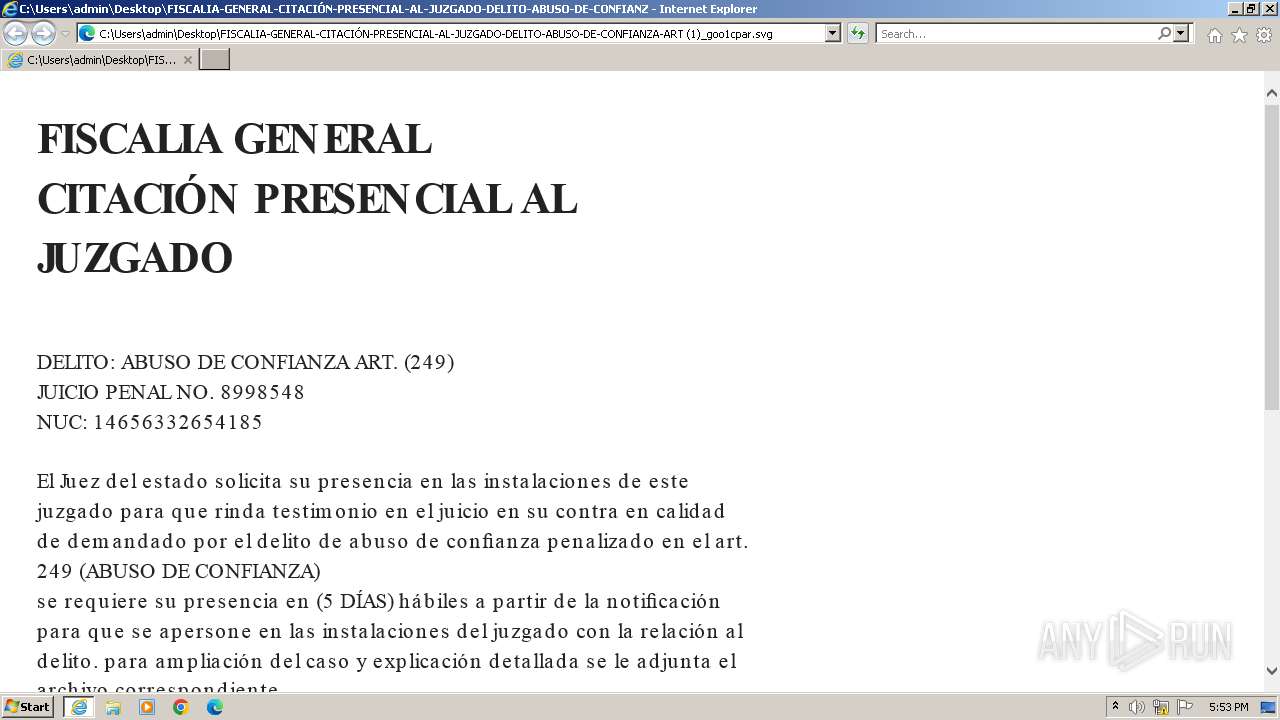
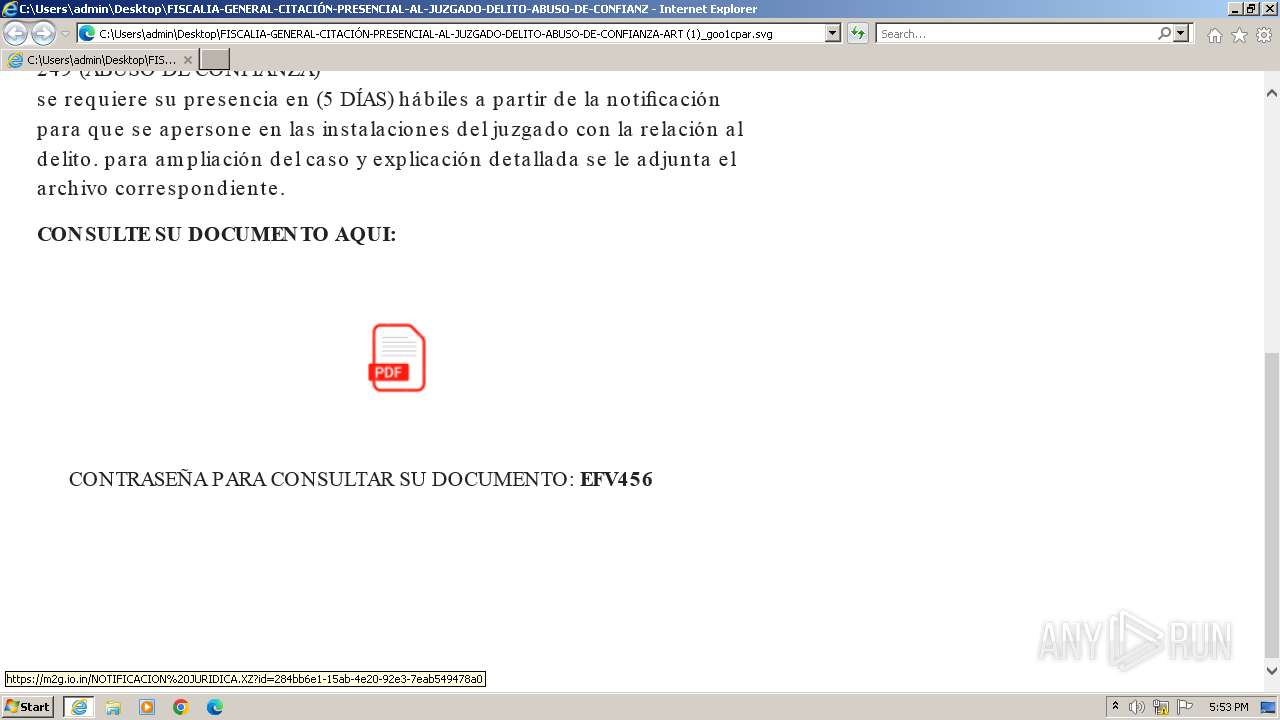
| File name: | FISCALIA-GENERAL-CITACIÓN-PRESENCIAL-AL-JUZGADO-DELITO-ABUSO-DE-CONFIANZA-ART (1)_goo1cpar.svg |
| Full analysis: | https://app.any.run/tasks/701ed91e-86d3-472e-b1ac-f681f854f871 |
| Verdict: | Malicious activity |
| Analysis date: | January 10, 2025, 17:53:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | image/svg+xml |
| File info: | SVG Scalable Vector Graphics image |
| MD5: | 7BB7CE3A47595BEE5A5D8F2019026798 |
| SHA1: | 25F09A3240AEFFDFD0845C044281A96F09828B65 |
| SHA256: | B7B0F4AA48372BC0E3630613B7D062EDE8E01D4D52A077840BA72D7220A4A486 |
| SSDEEP: | 768:62uGMpnHzuh5HTejuyJVJaSCzjPyHl35NuGMpnHzuh5HTejuyJVJaSCzjPyHl35U:63GMROqqHaFpMGMROqqHaFpU |
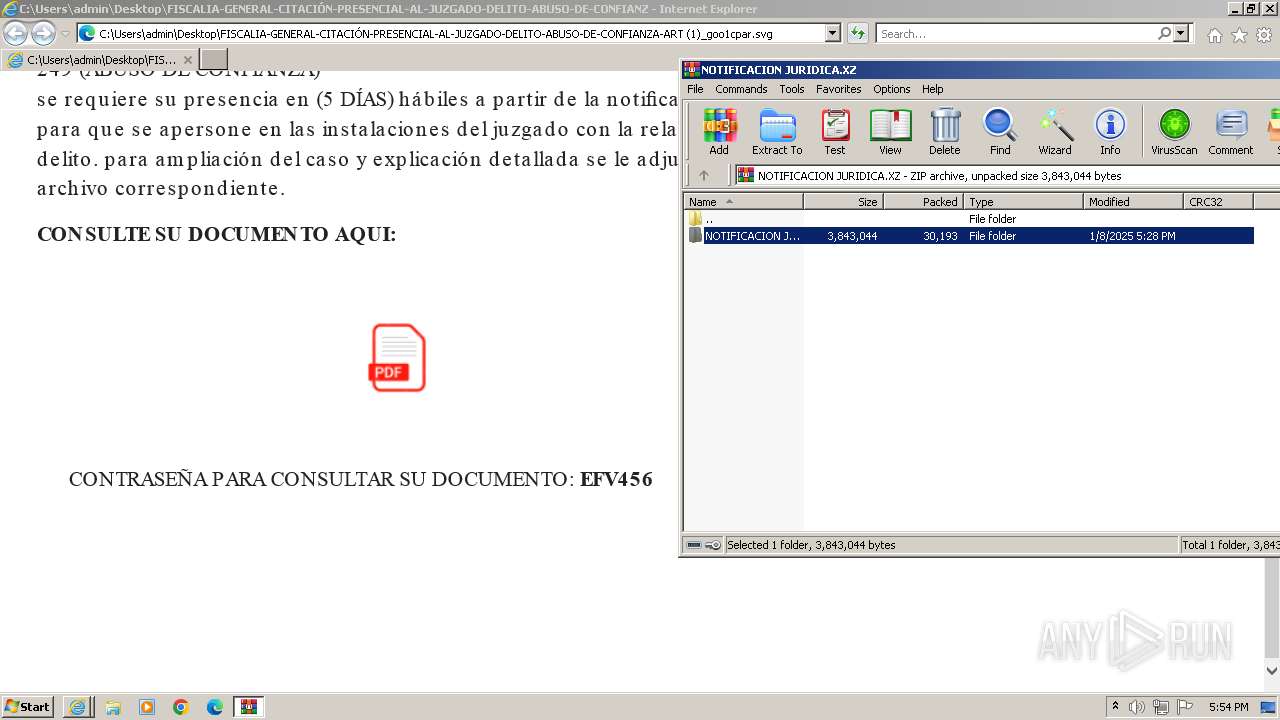
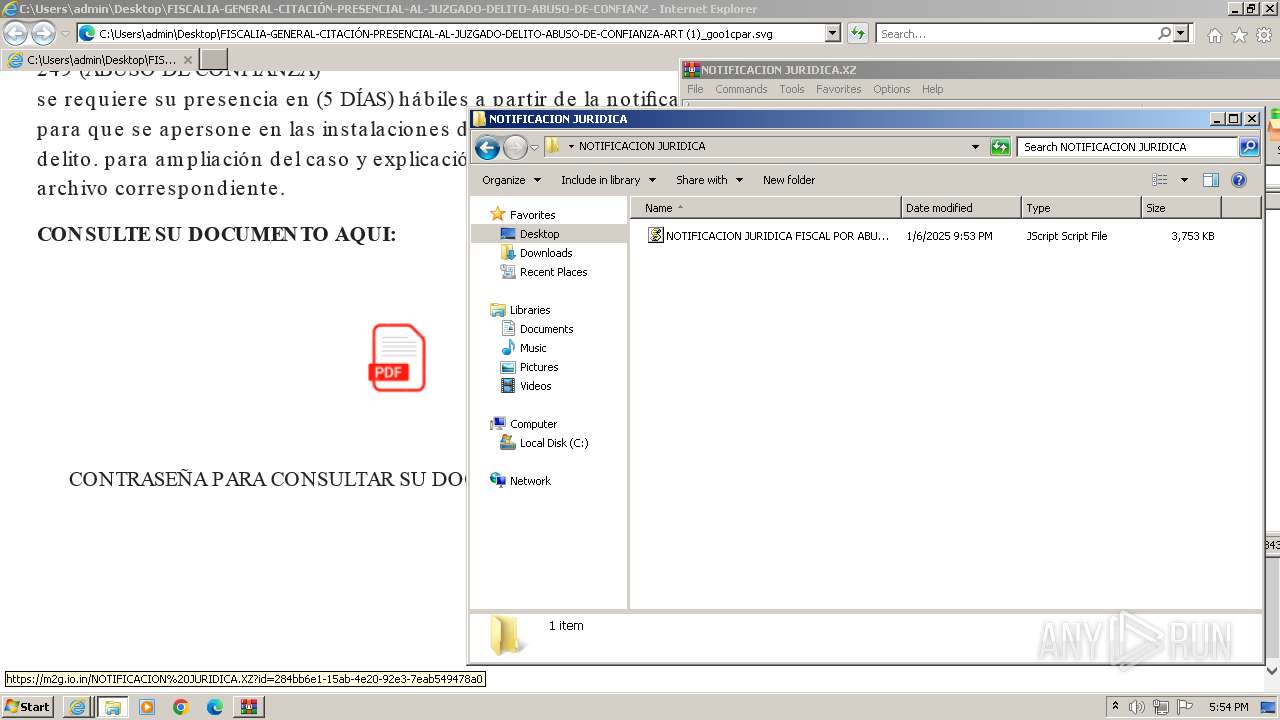
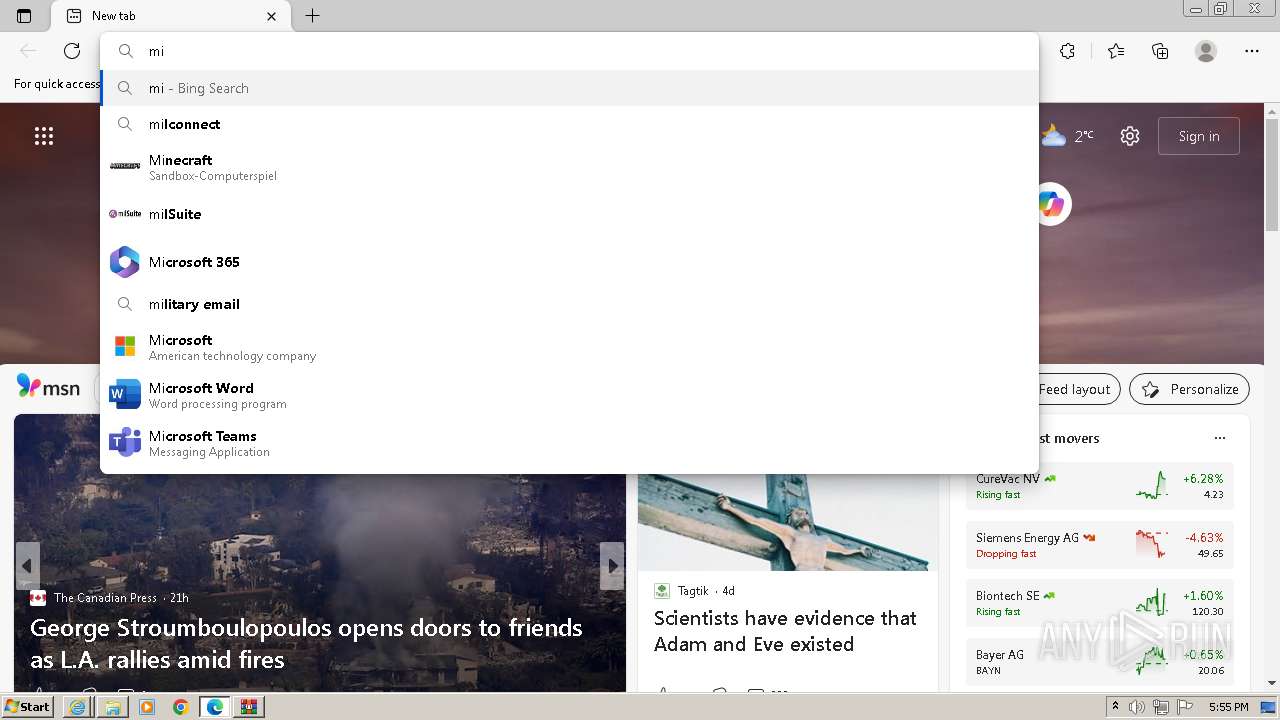
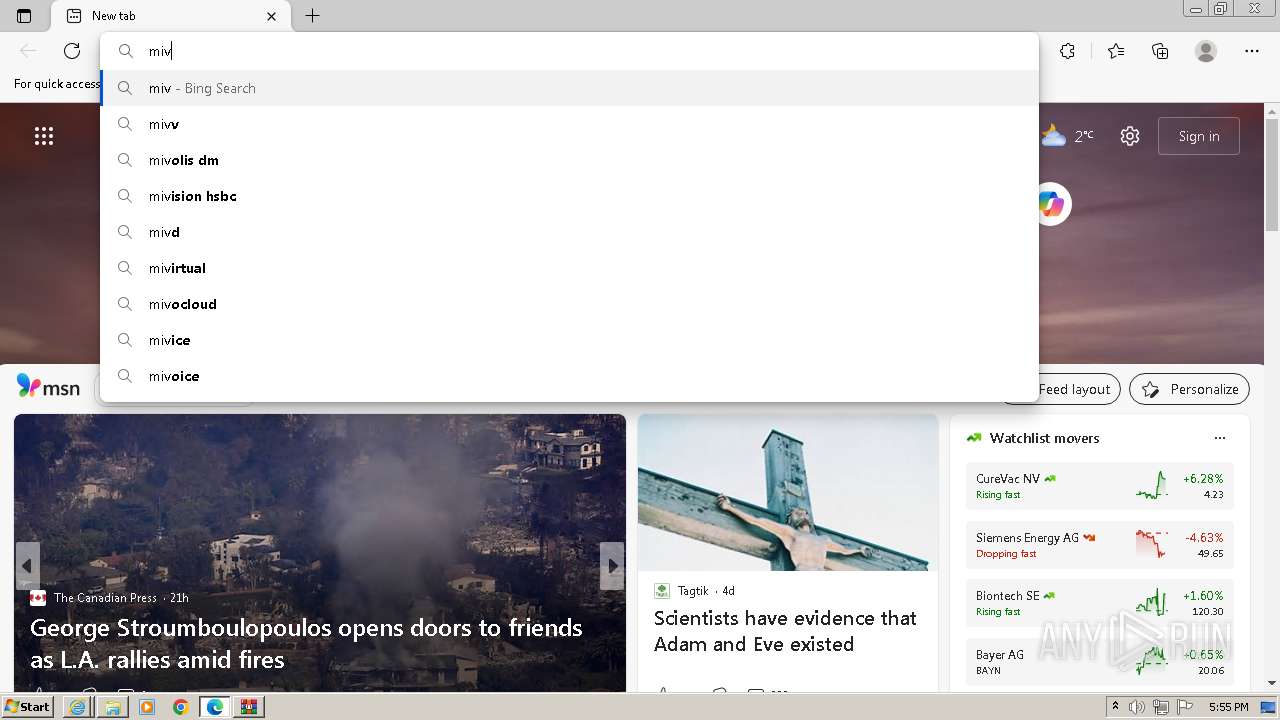
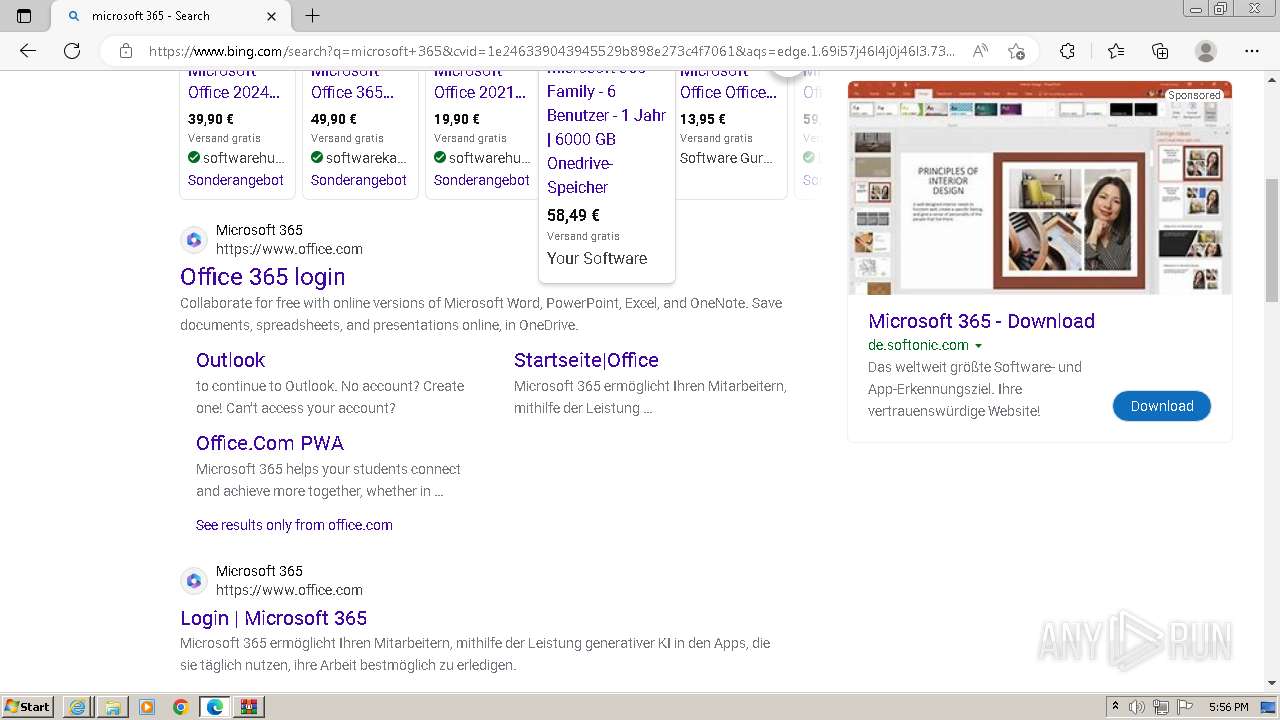
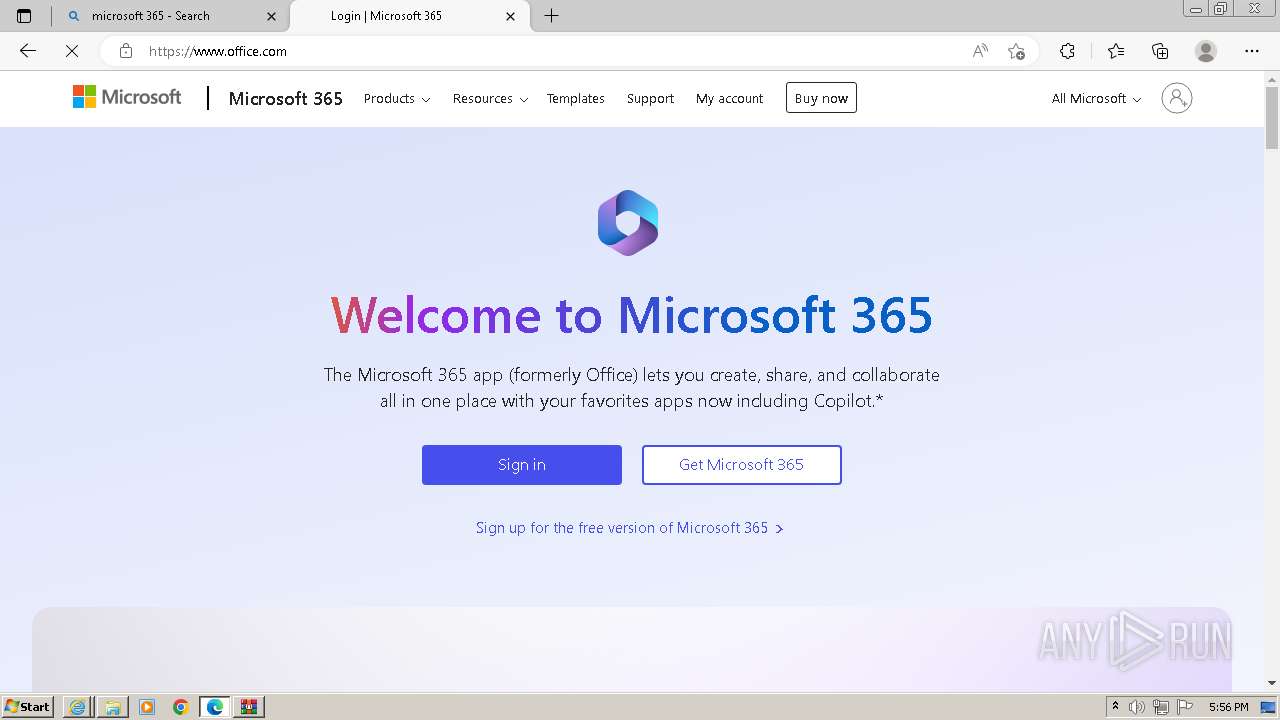
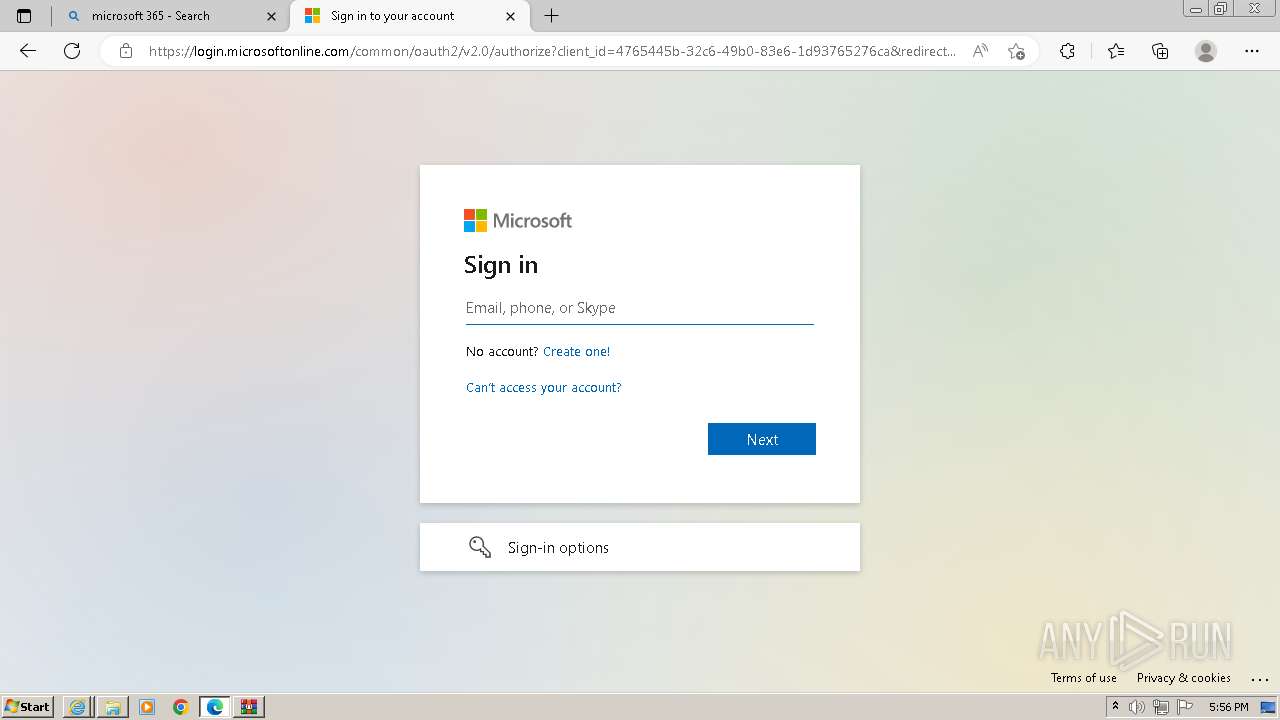
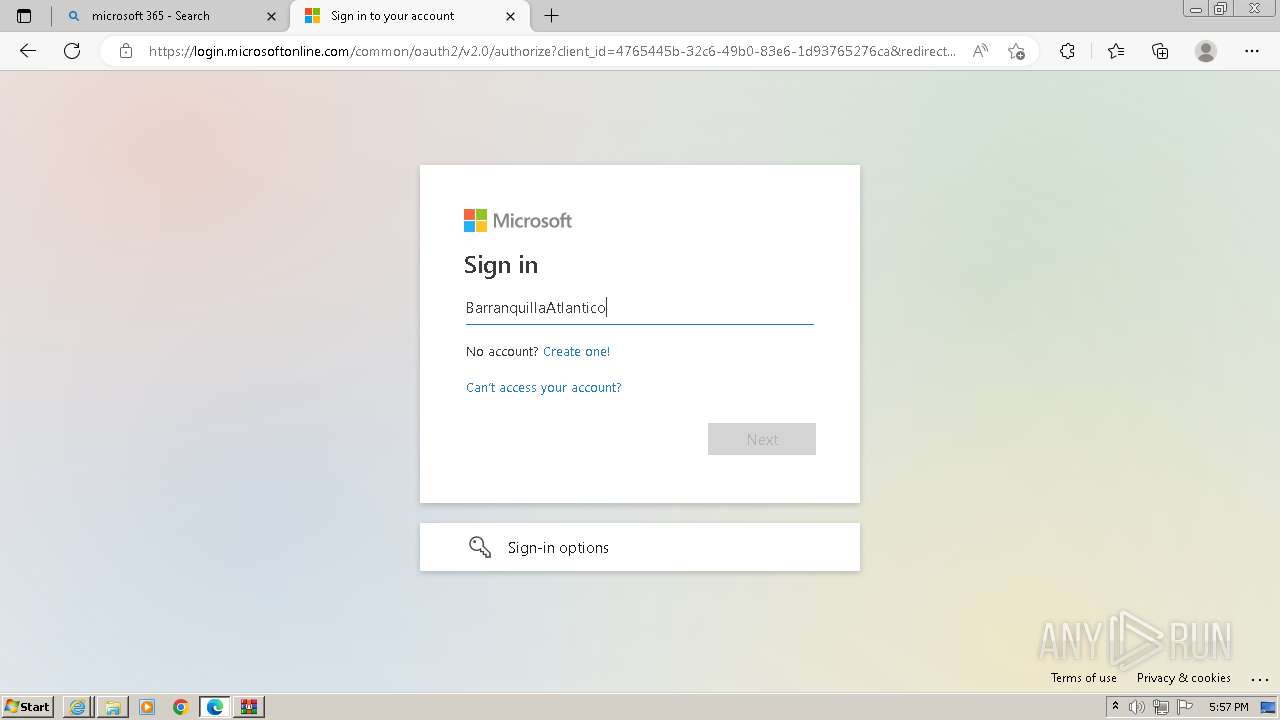
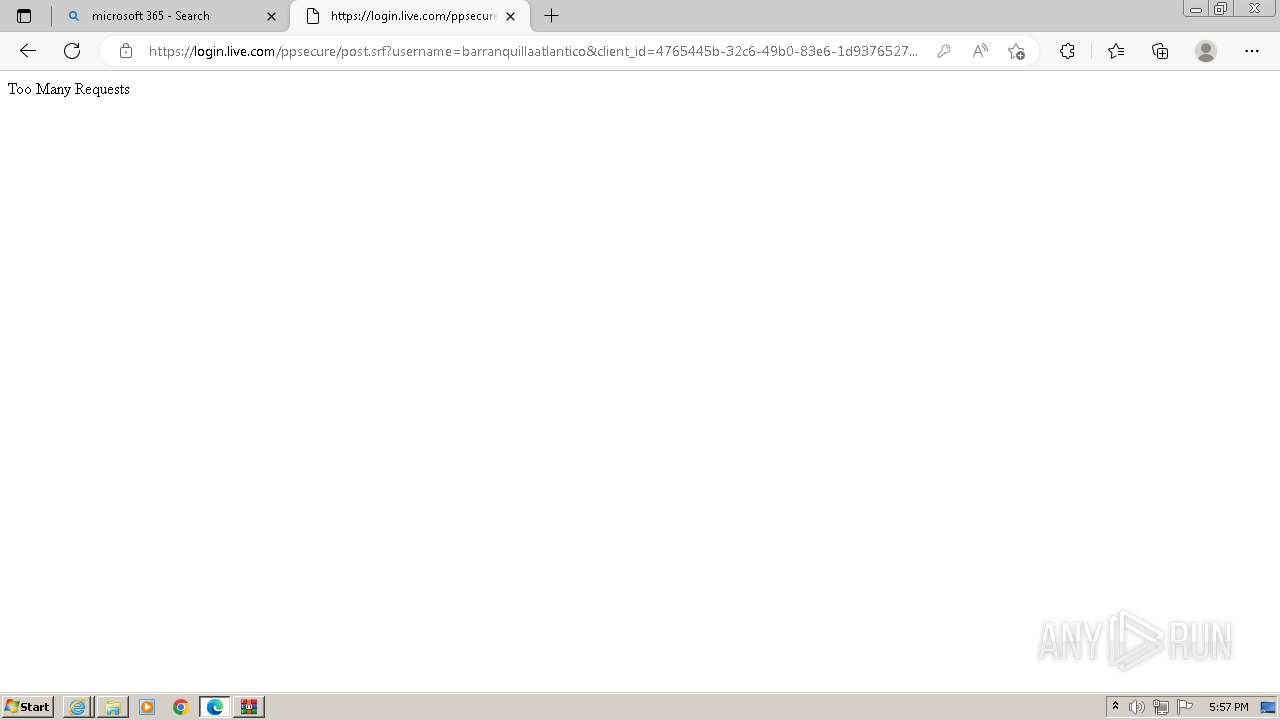
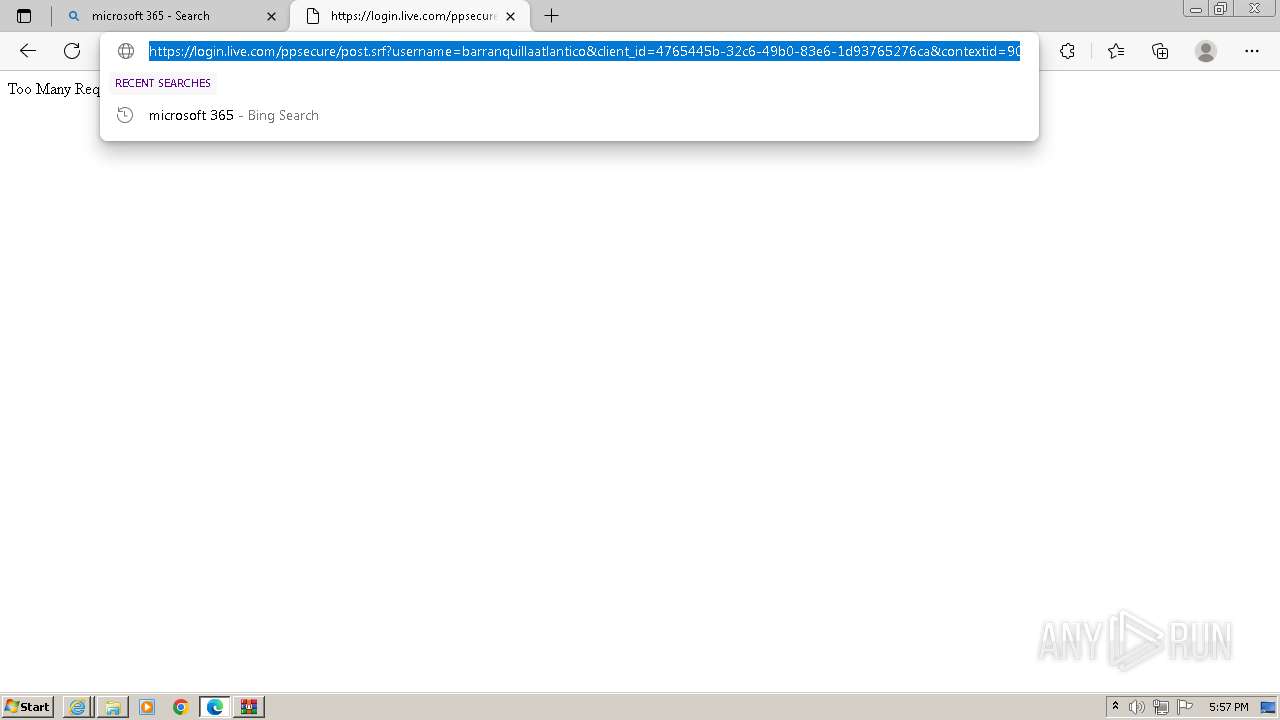
MALICIOUS
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 3212)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 3212)
Gets path to any of the special folders (SCRIPT)
- wscript.exe (PID: 3212)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 3212)
Bypass execution policy to execute commands
- powershell.exe (PID: 3524)
Changes powershell execution policy (Bypass)
- wscript.exe (PID: 3212)
SUSPICIOUS
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 3212)
Adds, changes, or deletes HTTP request header (SCRIPT)
- wscript.exe (PID: 3212)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 3212)
Adds/modifies Windows certificates
- wscript.exe (PID: 3212)
Runs shell command (SCRIPT)
- wscript.exe (PID: 3212)
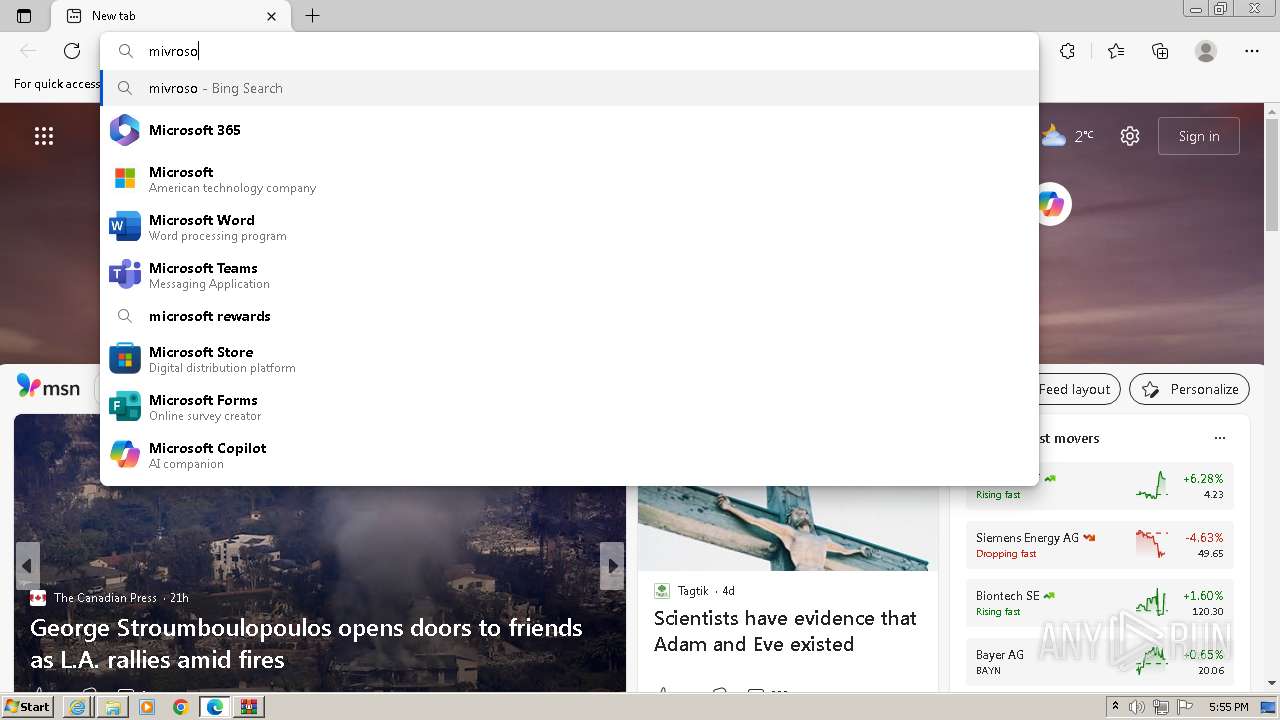
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 3212)
The process bypasses the loading of PowerShell profile settings
- wscript.exe (PID: 3212)
The process executes Powershell scripts
- wscript.exe (PID: 3212)
Reads the Internet Settings
- wscript.exe (PID: 3212)
- powershell.exe (PID: 3524)
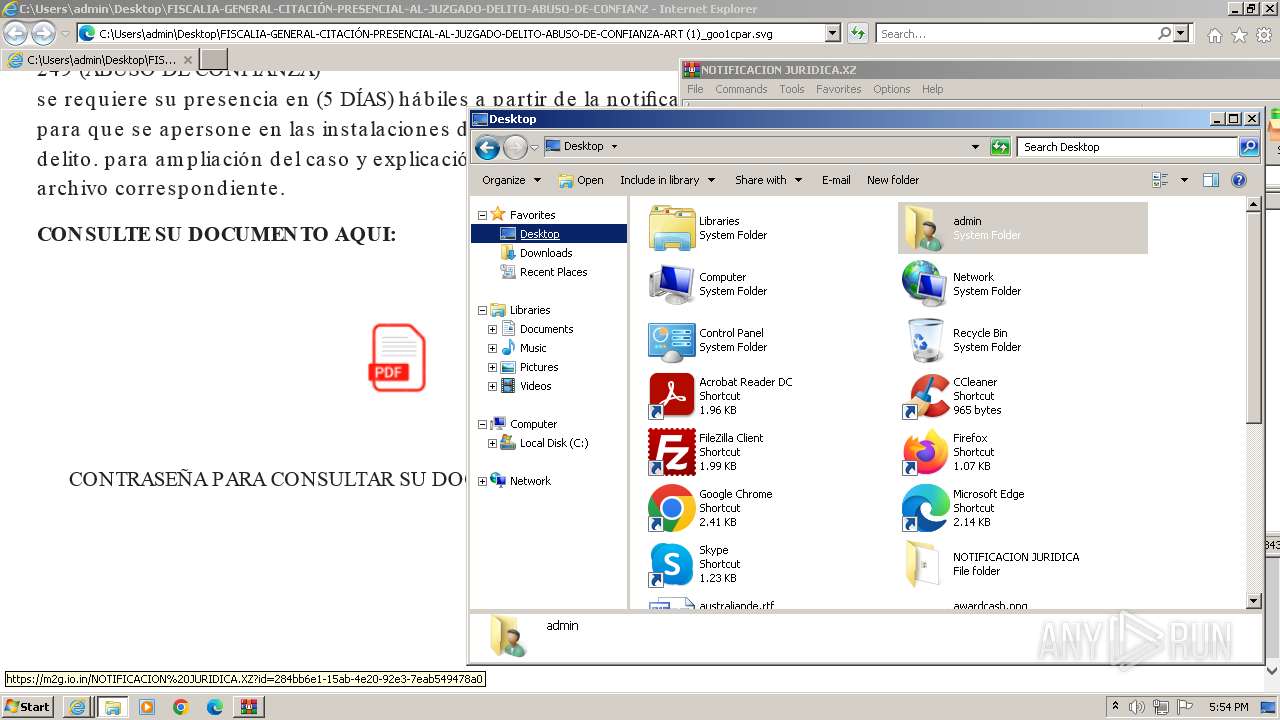
Executable content was dropped or overwritten
- powershell.exe (PID: 3524)
The process creates files with name similar to system file names
- powershell.exe (PID: 3524)
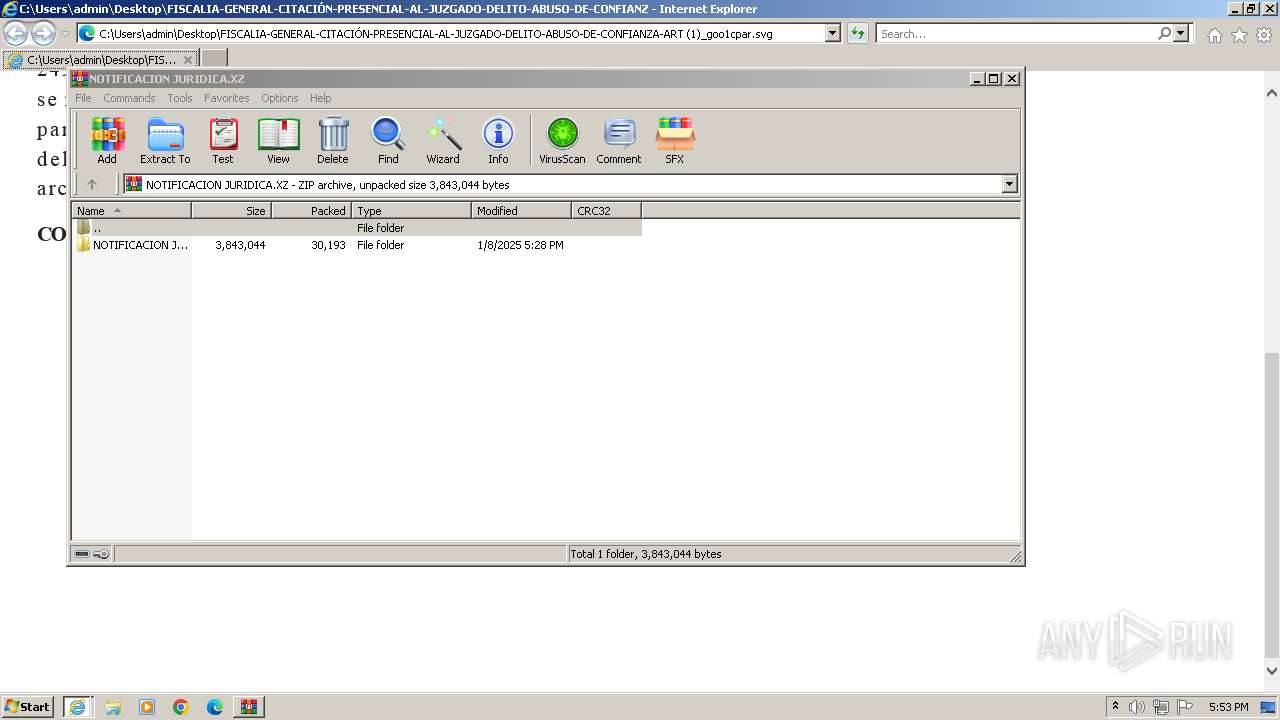
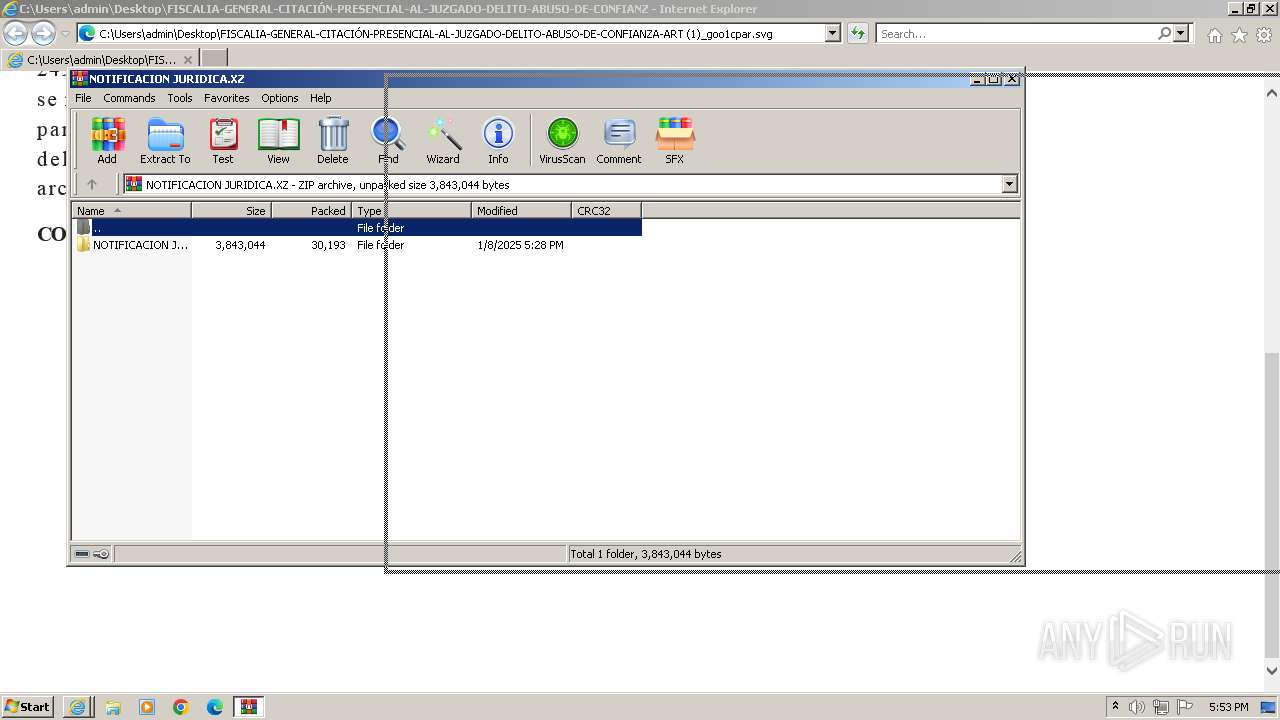
Extracts files to a directory (POWERSHELL)
- powershell.exe (PID: 3524)
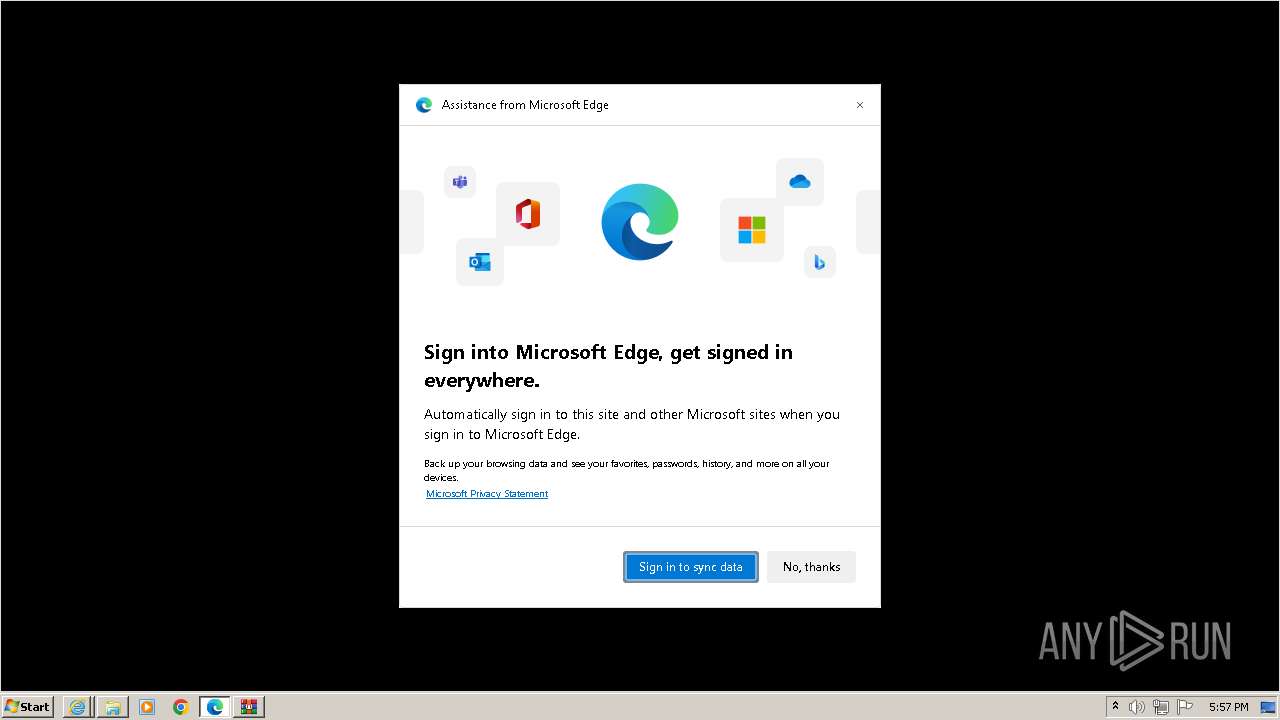
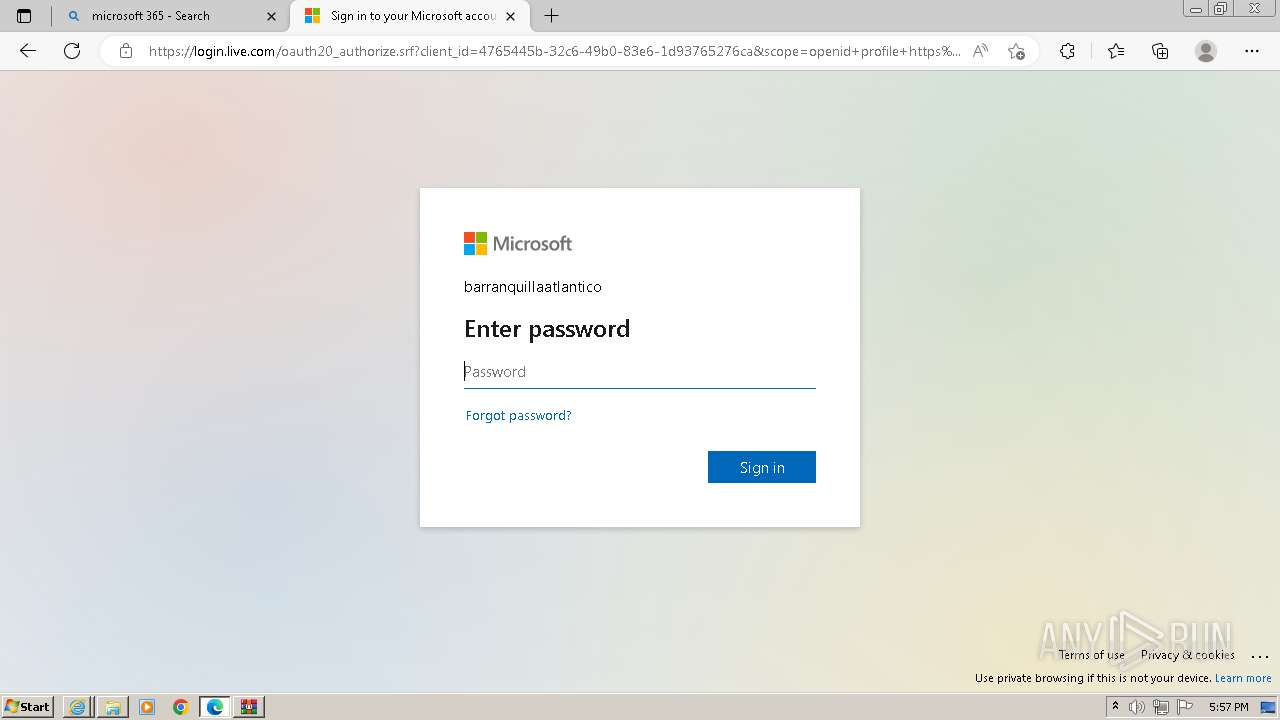
Reads Internet Explorer settings
- msedge.exe (PID: 3752)
INFO
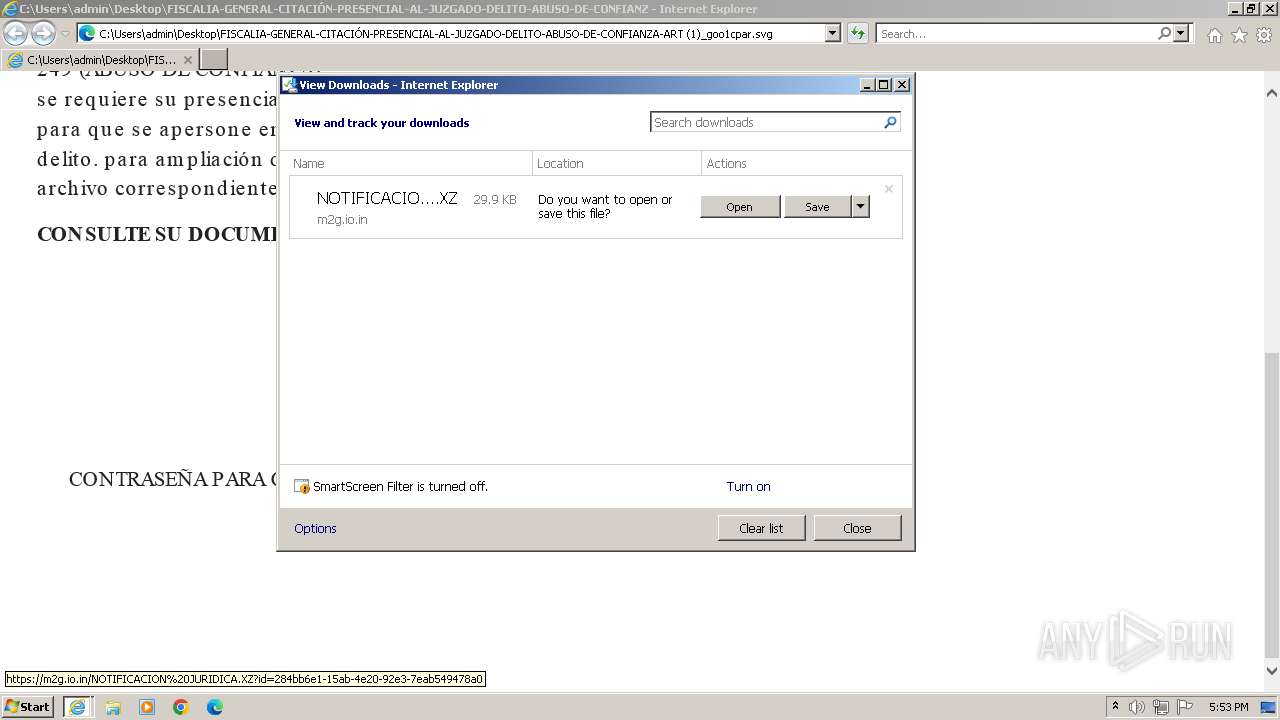
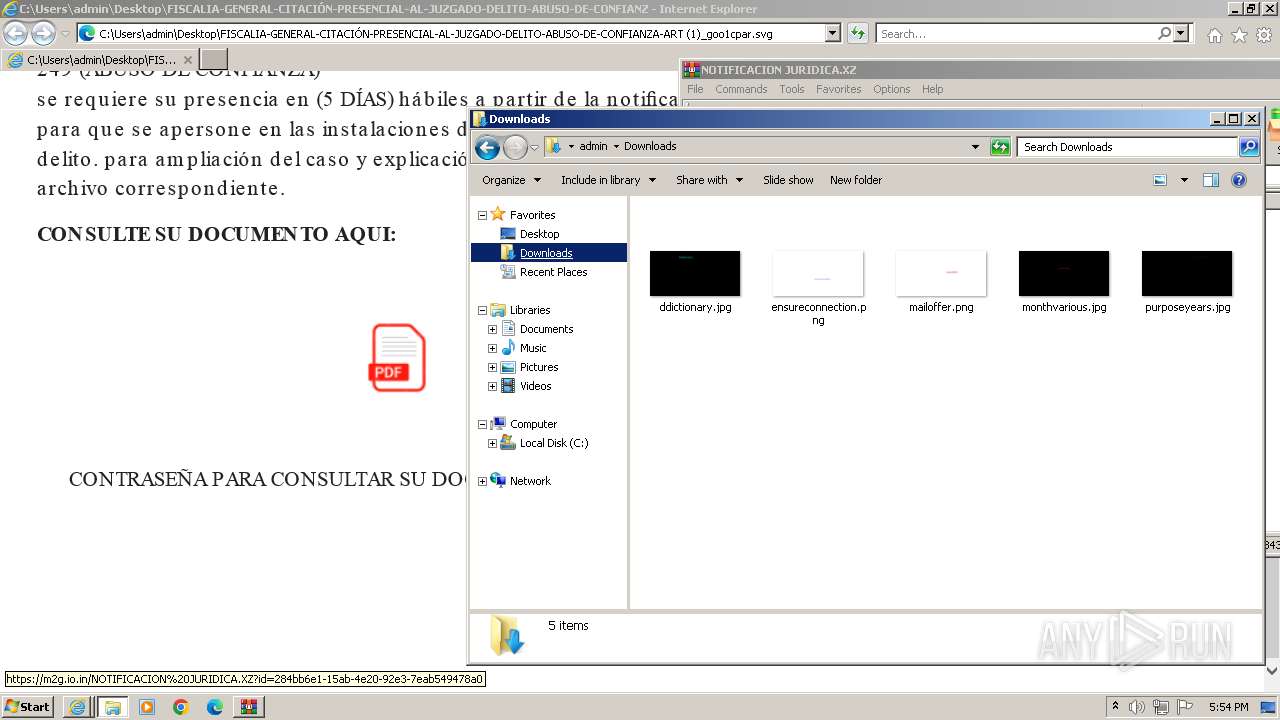
The process uses the downloaded file
- iexplore.exe (PID: 116)
- iexplore.exe (PID: 1828)
- WinRAR.exe (PID: 952)
- wscript.exe (PID: 3212)
Application launched itself
- iexplore.exe (PID: 116)
- iexplore.exe (PID: 1828)
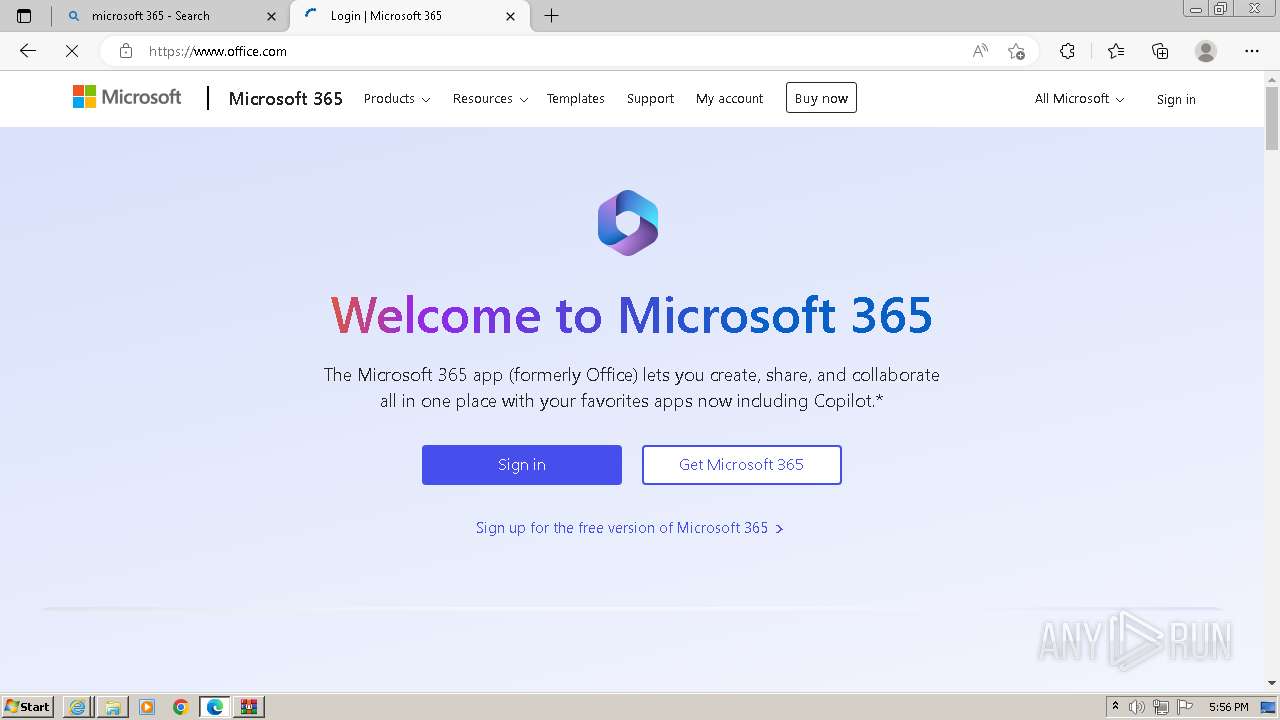
- msedge.exe (PID: 3752)
Manual execution by a user
- wmpnscfg.exe (PID: 3296)
- wscript.exe (PID: 3212)
- explorer.exe (PID: 1396)
- msedge.exe (PID: 3752)
Modifies the phishing filter of IE
- iexplore.exe (PID: 116)
Checks supported languages
- wmpnscfg.exe (PID: 3296)
Reads the computer name
- wmpnscfg.exe (PID: 3296)
Self-termination (SCRIPT)
- wscript.exe (PID: 3212)
Disables trace logs
- powershell.exe (PID: 3524)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 3524)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rdf | | | Resource Description Framework (48.6) |
|---|---|---|
| .svg | | | Scalable Vector Graphics (var.3) (38.1) |
| .xml | | | Generic XML (ASCII) (13.1) |
EXIF
SVG
| Xmlns: | http://www.w3.org/2000/svg |
|---|---|
| ViewBox: | 0 0 794 1122.5601 |
| ImageHeight: | 1122.5601 |
| ImageWidth: | 794 |
| ID: | svg2 |
| SVGVersion: | 1.1 |
| Data-unique-id: | 661c0583-9e92-449a-96e3-e44c05f2a9fe |
| MetadataID: | metadata8 |
| Data-random: | ugyyu |
XMP
| WorkFormatData-random: | puizo |
|---|---|
| WorkFormat: | image/svg+xml |
| WorkTypeData-random: | vxiia |
| WorkType: | http://purl.org/dc/dcmitype/StillImage |
Composite
| ImageSize: | 794x1122.5601 |
|---|---|
| Megapixels: | 0.891 |
Total processes
84
Monitored processes
45
Malicious processes
2
Suspicious processes
1
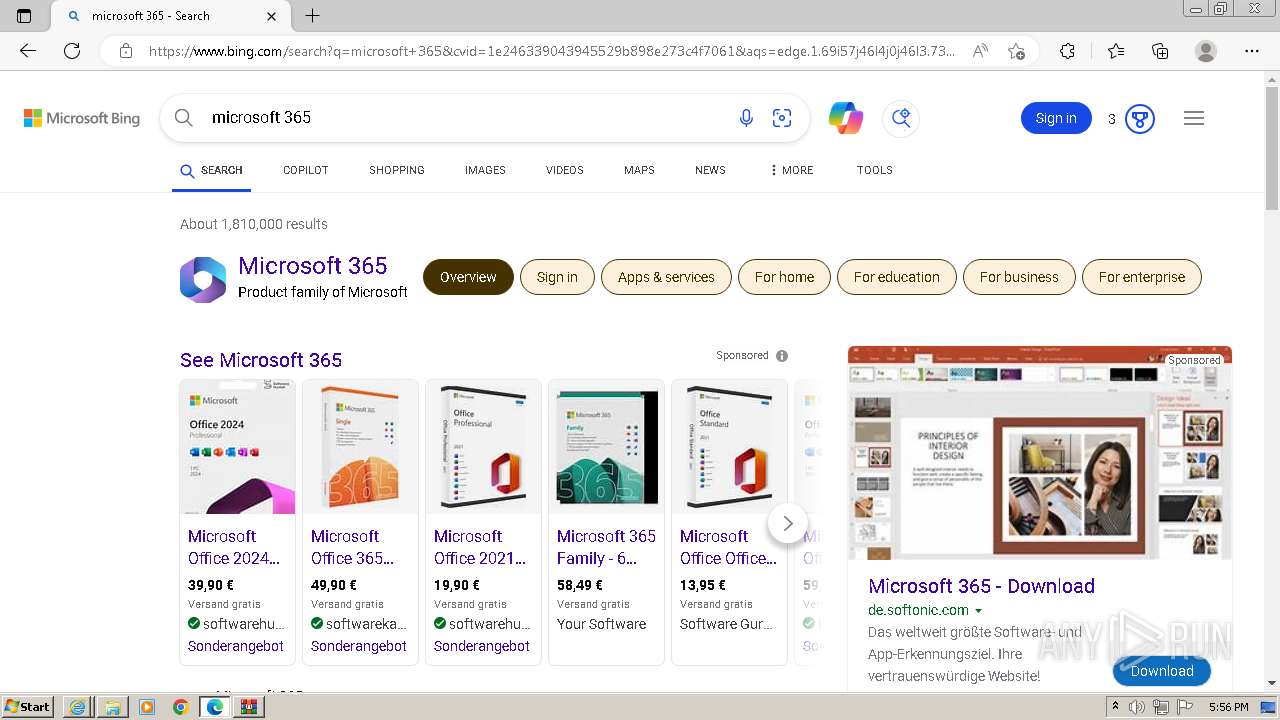
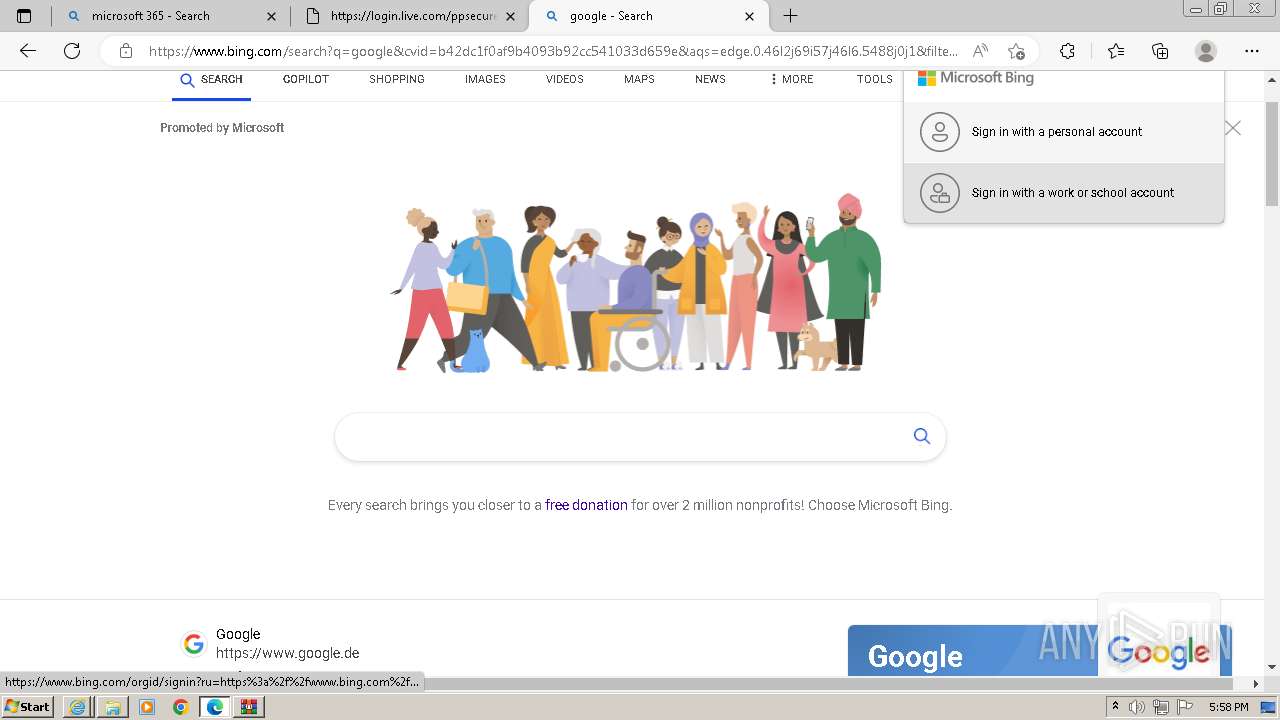
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Internet Explorer\iexplore.exe" "C:\Users\admin\Desktop\FISCALIA-GENERAL-CITACIÓN-PRESENCIAL-AL-JUZGADO-DELITO-ABUSO-DE-CONFIANZA-ART (1)_goo1cpar.svg" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 688 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --mojo-platform-channel-handle=5904 --field-trial-handle=1296,i,6399301416012993434,10697344804003695733,131072 --enable-features=msMicrosoftRootStoreUsed /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
| 848 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --mojo-platform-channel-handle=5736 --field-trial-handle=1296,i,6399301416012993434,10697344804003695733,131072 --enable-features=msMicrosoftRootStoreUsed /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 912 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1392 --field-trial-handle=1296,i,6399301416012993434,10697344804003695733,131072 --enable-features=msMicrosoftRootStoreUsed /prefetch:3 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
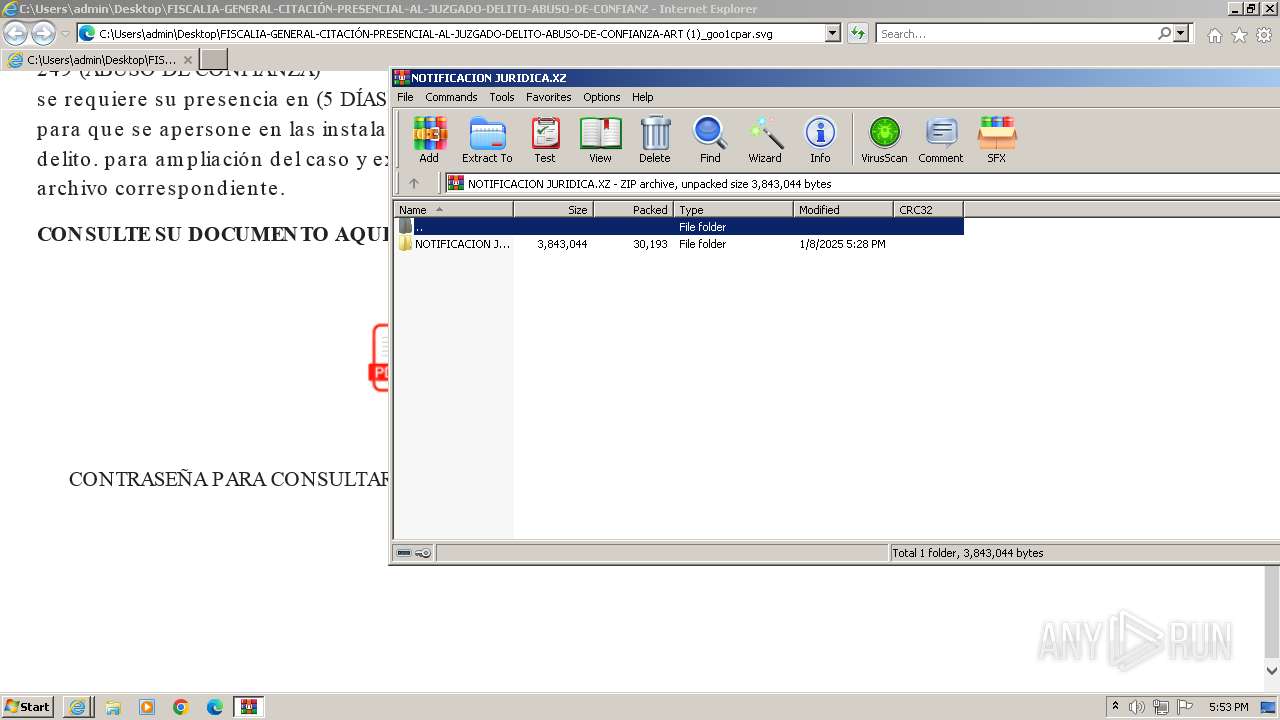
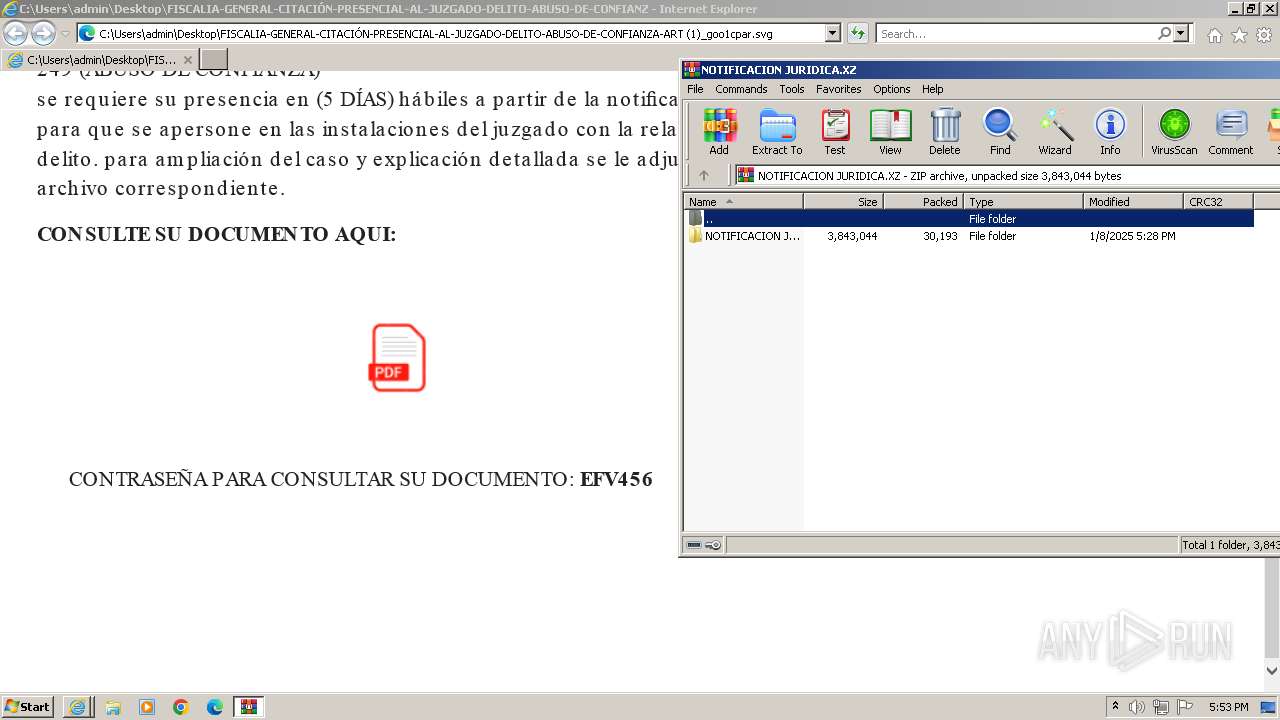
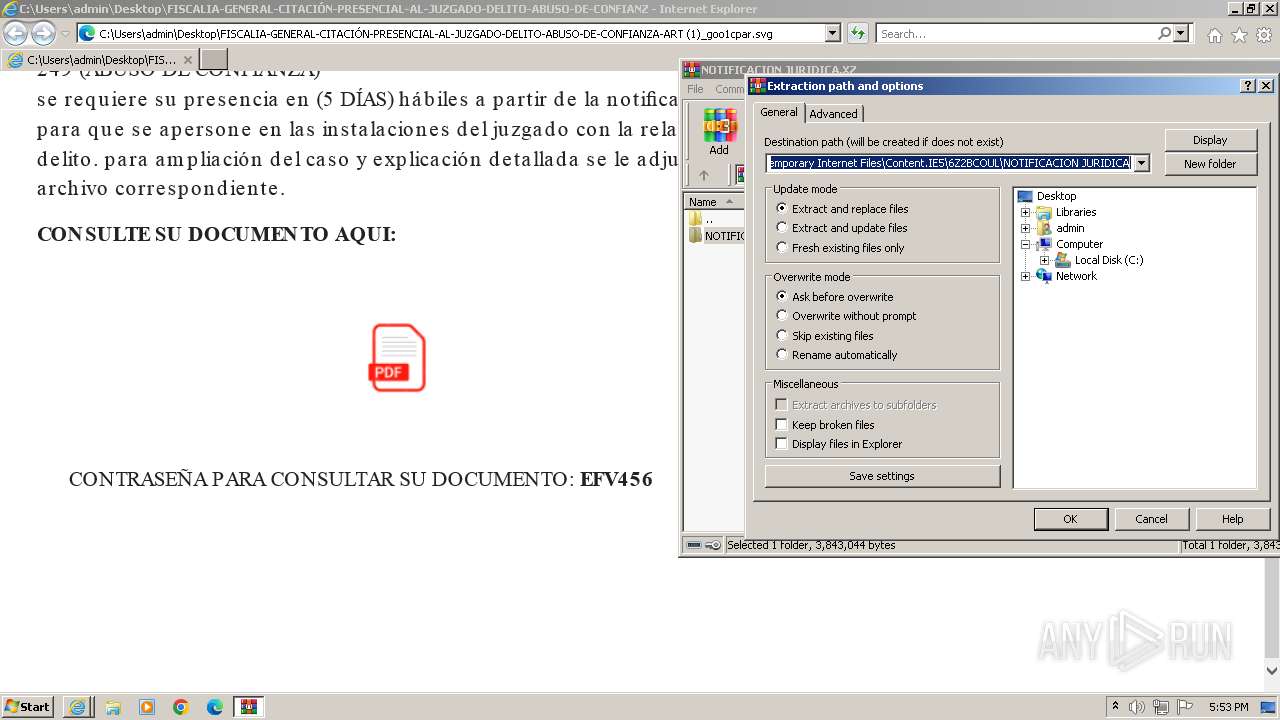
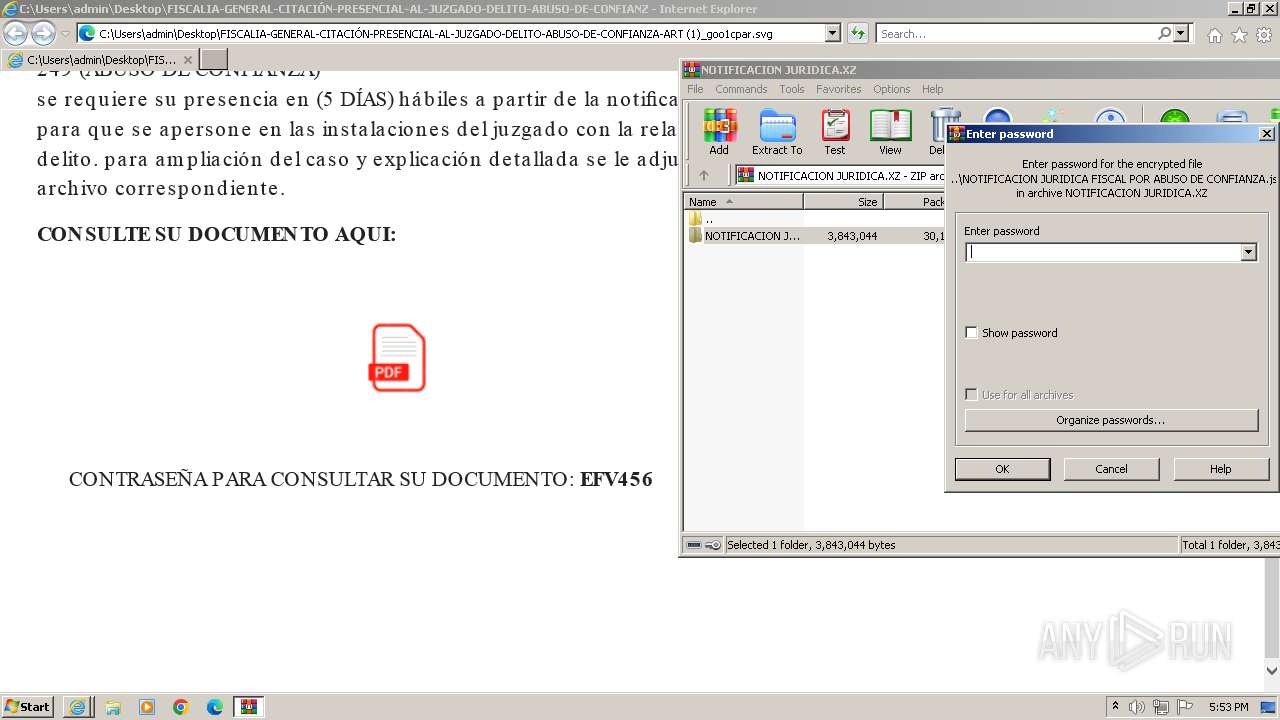
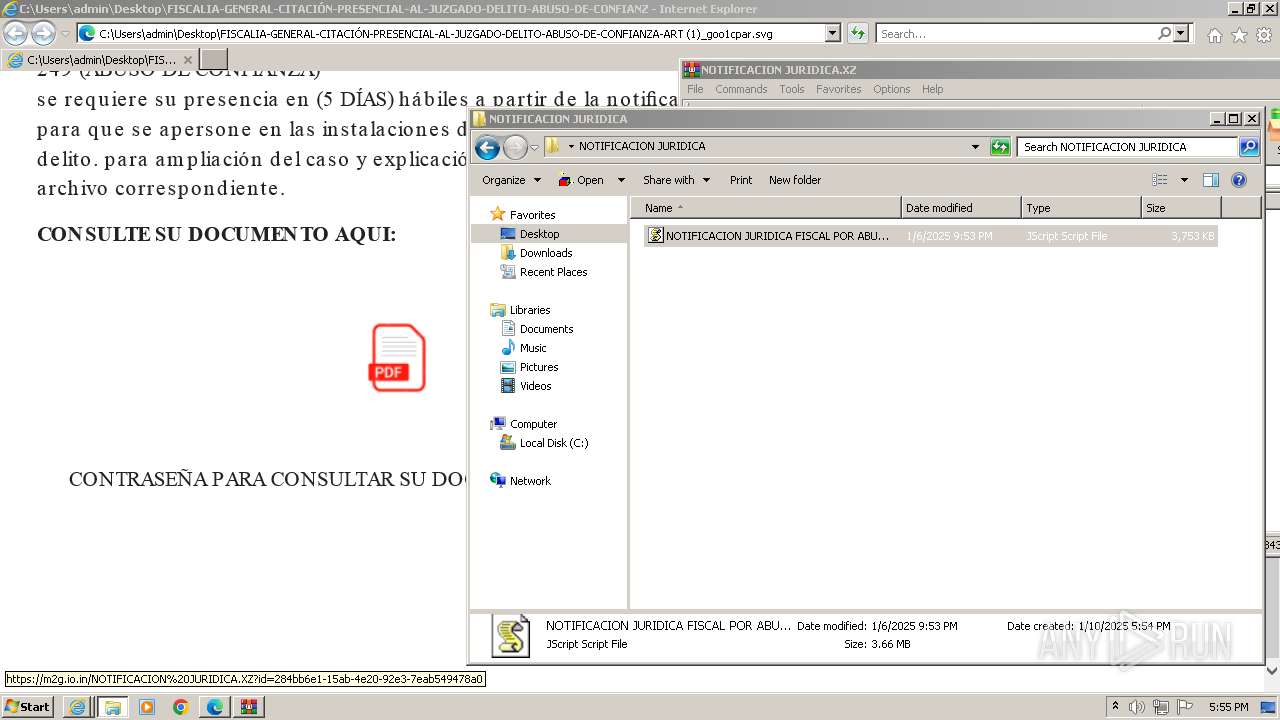
| 952 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\NOTIFICACION JURIDICA.XZ" | C:\Program Files\WinRAR\WinRAR.exe | — | iexplore.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 992 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=34 --mojo-platform-channel-handle=2328 --field-trial-handle=1296,i,6399301416012993434,10697344804003695733,131072 --enable-features=msMicrosoftRootStoreUsed /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1396 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1396 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=5228 --field-trial-handle=1296,i,6399301416012993434,10697344804003695733,131072 --enable-features=msMicrosoftRootStoreUsed /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1652 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --instant-process --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2176 --field-trial-handle=1296,i,6399301416012993434,10697344804003695733,131072 --enable-features=msMicrosoftRootStoreUsed /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1732 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=5396 --field-trial-handle=1296,i,6399301416012993434,10697344804003695733,131072 --enable-features=msMicrosoftRootStoreUsed /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
Total events
41 334
Read events
40 939
Write events
323
Delete events
72
Modification events
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31155080 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31155080 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
38
Suspicious files
714
Text files
161
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 116 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 116 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | der | |
MD5:89BB2767A3E7E6B9F5DF10671199B917 | SHA256:CAE75111C18FAC99EF65BF0FC90A04CB3F65E21D04681C4FA3660C92F87014E7 | |||
| 116 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:258D978F0399DC17330CE828F326481F | SHA256:3118AC436FFD4B7F10DC9FFD77B1A26B9B710C420395A993C089E7C6E302BE89 | |||
| 116 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:77B20B5CD41BC6BB475CCA3F91AE6E3C | SHA256:5511A9B9F9144ED7BDE4CCB074733B7C564D918D2A8B10D391AFC6BE5B3B1509 | |||
| 116 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\favicon[2].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 116 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:90E7EBE2C9B8DEC0EB5E1E15894AD31D | SHA256:8C5683BCC8AE4EAC62811A5554055EF413BF56F7A62D857D6D540996BCFF06CC | |||
| 116 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{CC40E7F0-CF7B-11EF-AC60-12A9866C77DE}.dat | binary | |
MD5:5A0C81AEFC970DB3D652B77581B82EBD | SHA256:78315E82A1D6AE7F2DC3C0CD352279F1E768E25D2E5A91E8E1EDD05715C1C055 | |||
| 116 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF67943908521C4952.TMP | binary | |
MD5:7E06D75B0E7BBB3FE517F50E5EF2CFE8 | SHA256:B05075FC360BF1B65BFDA281FFC09AB396B0BFD098B77CF1EBF49A551970A1B7 | |||
| 116 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:E8D4784EAE2F5609B287C2EA9DA80803 | SHA256:ECC3AAD6844A15C1EF86EFC7C2F6A6AE8944FDD16581B9D05CE13C97A592A047 | |||
| 116 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:9BF51918A12F03CA4F26D83E99645740 | SHA256:C04F101C94199D3B225AD950B34B6A4D7E1D5392E01B01FDE11ADEBFAE33AA5E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
137
DNS requests
247
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
116 | iexplore.exe | GET | 200 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?5e22539541d96f8b | unknown | — | — | whitelisted |
116 | iexplore.exe | GET | 200 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?999c28cf29202038 | unknown | — | — | whitelisted |
116 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2604 | iexplore.exe | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
2604 | iexplore.exe | GET | 200 | 184.24.77.79:80 | http://r11.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBQaUrm0WeTDM5ghfoZtS72KO9ZnzgQUCLkRO6XQhRi06g%2BgrZ%2BGHo78OCcCEgR2s6w3Dgfv51%2FIOQkQllJo4A%3D%3D | unknown | — | — | whitelisted |
116 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
116 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
116 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
912 | msedge.exe | GET | 200 | 69.192.161.44:80 | http://x1.i.lencr.org/ | unknown | — | — | whitelisted |
912 | msedge.exe | GET | 200 | 69.192.161.44:80 | http://r3.i.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1108 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
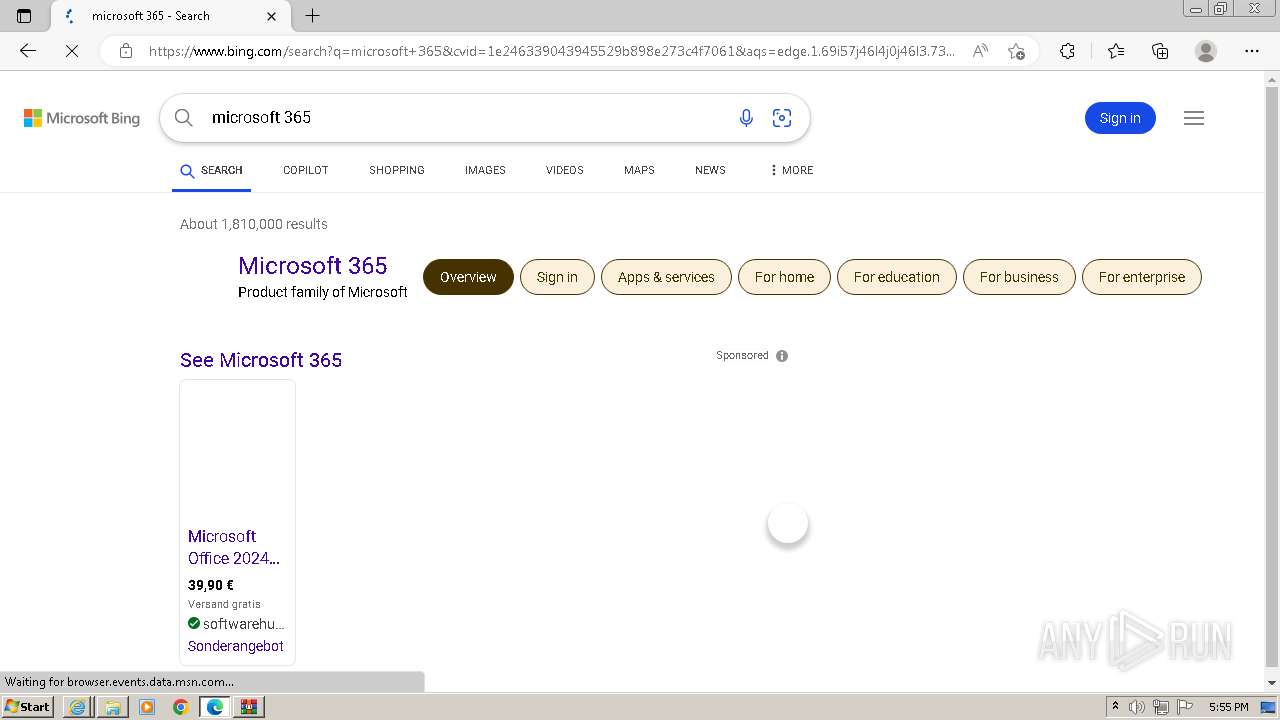
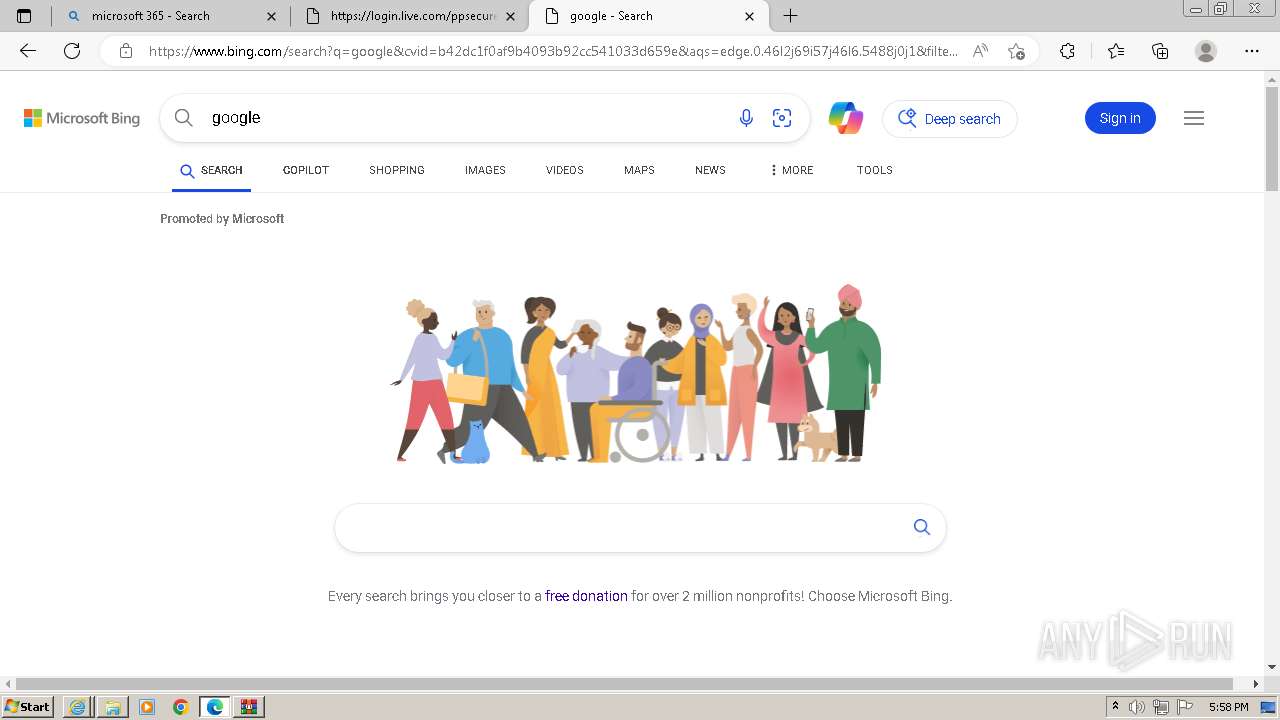
116 | iexplore.exe | 92.123.104.38:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
116 | iexplore.exe | 199.232.214.172:80 | ctldl.windowsupdate.com | FASTLY | US | whitelisted |
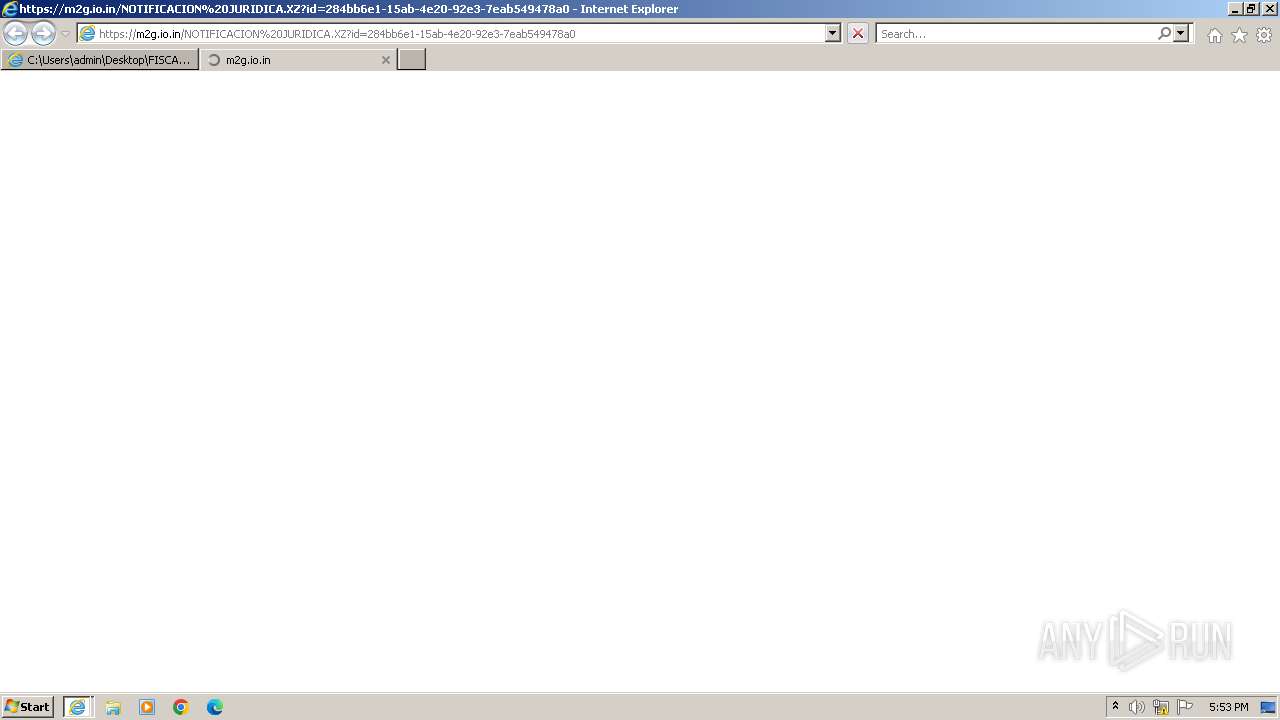
2604 | iexplore.exe | 103.160.107.178:443 | m2g.io.in | Web Werks India Pvt. Ltd. | IN | unknown |
116 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2604 | iexplore.exe | 69.192.161.44:80 | x1.c.lencr.org | AKAMAI-AS | DE | whitelisted |
2604 | iexplore.exe | 184.24.77.79:80 | r11.o.lencr.org | Akamai International B.V. | DE | whitelisted |
116 | iexplore.exe | 152.199.19.161:443 | r20swj13mr.microsoft.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
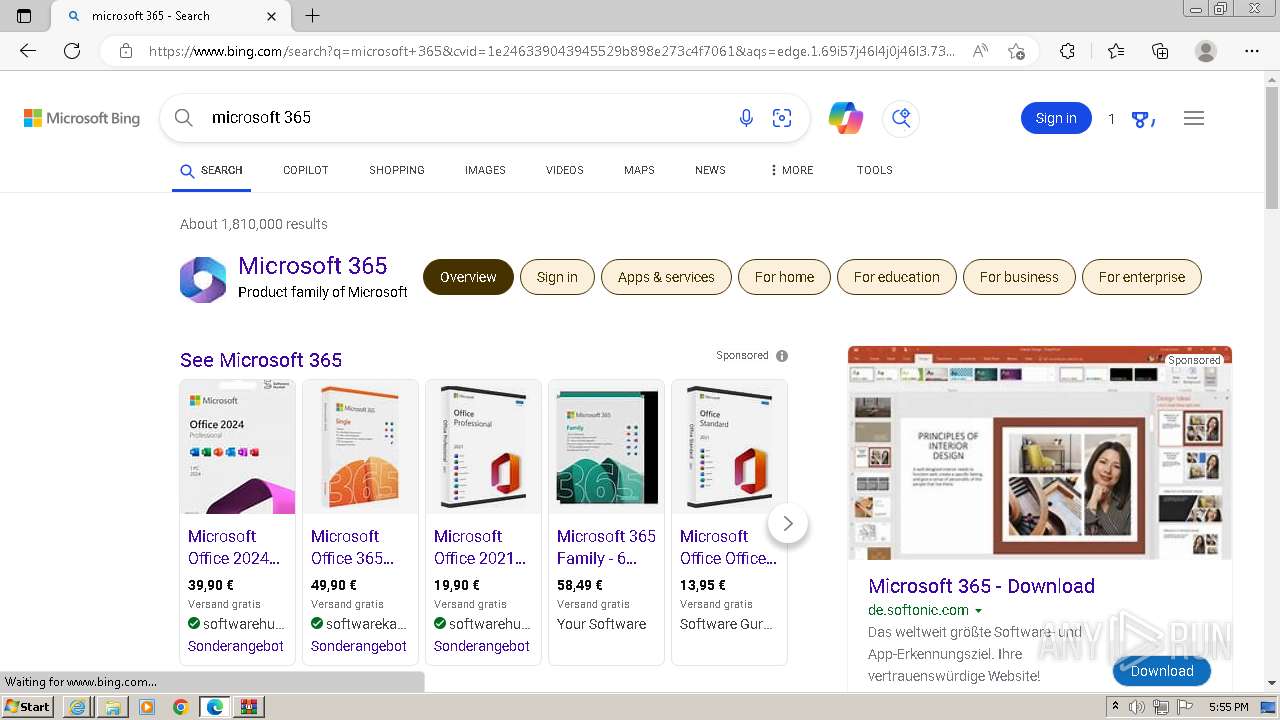
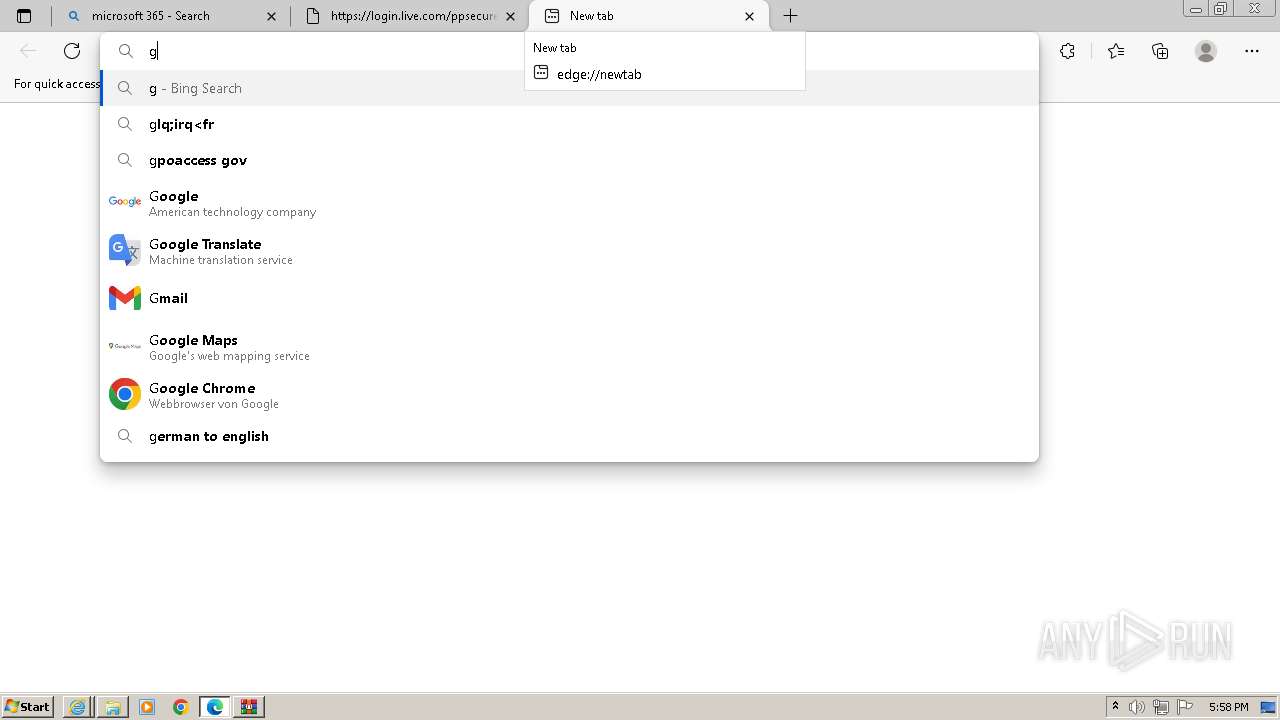
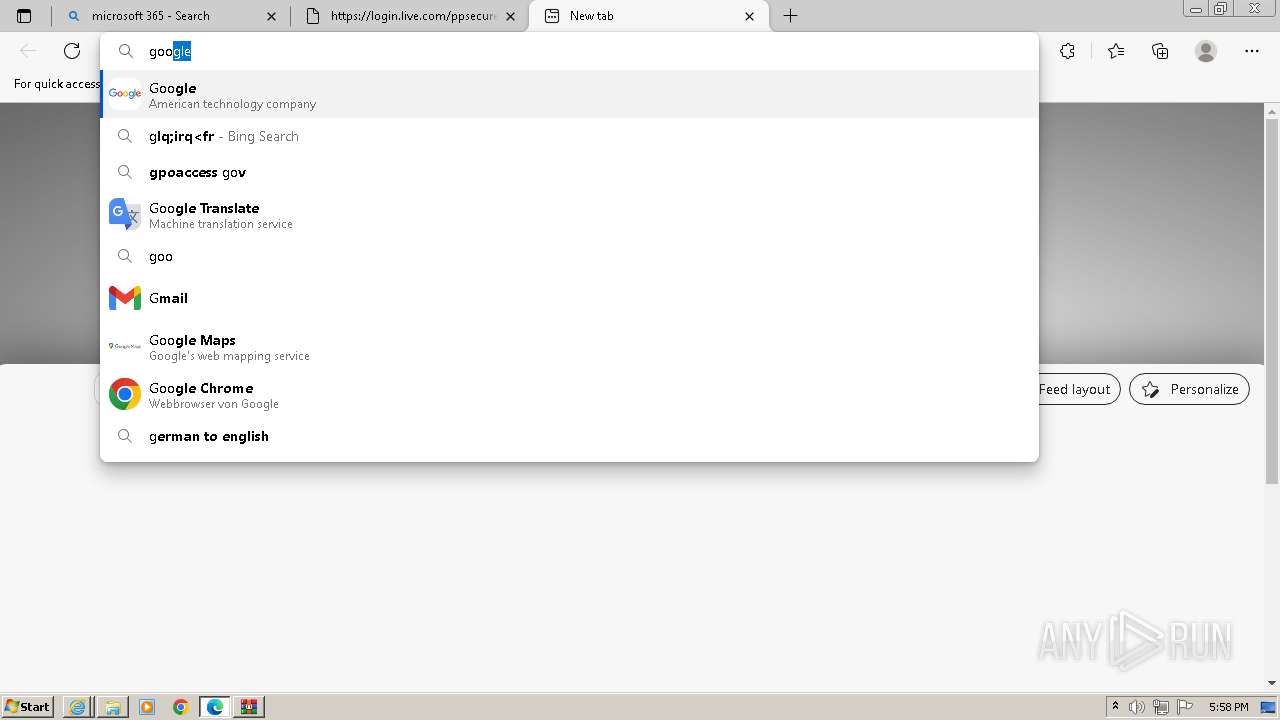
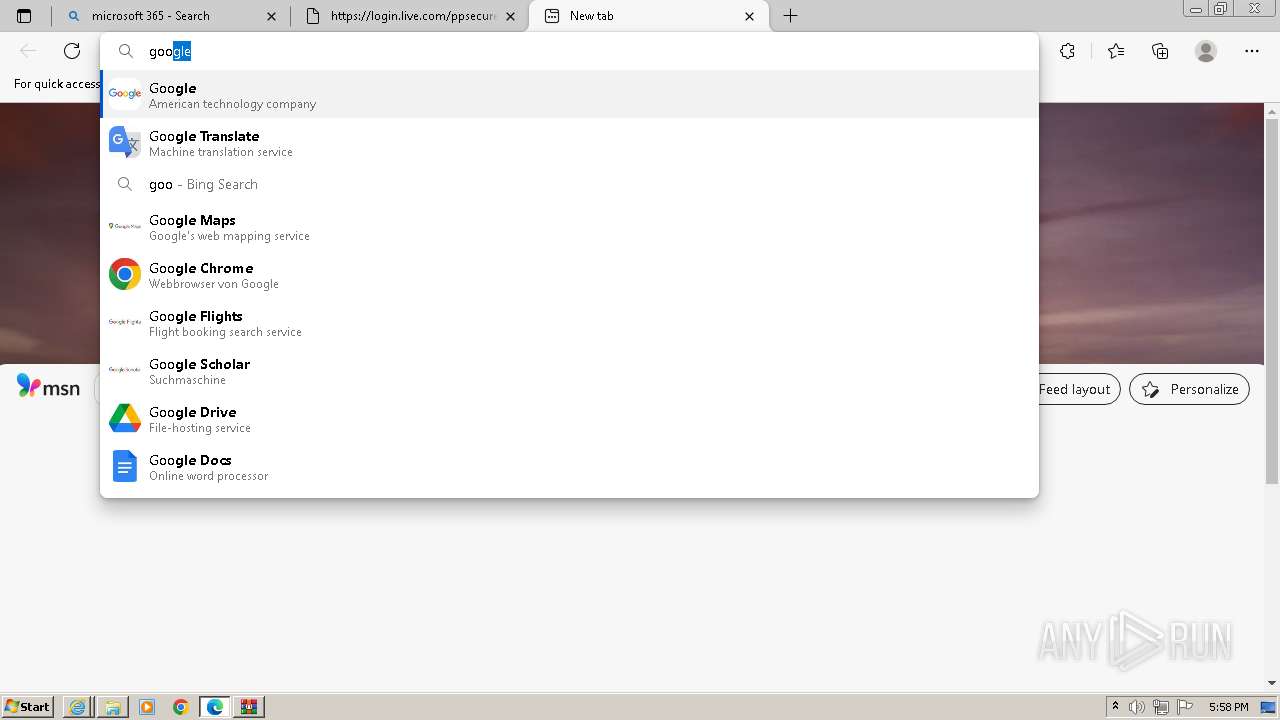
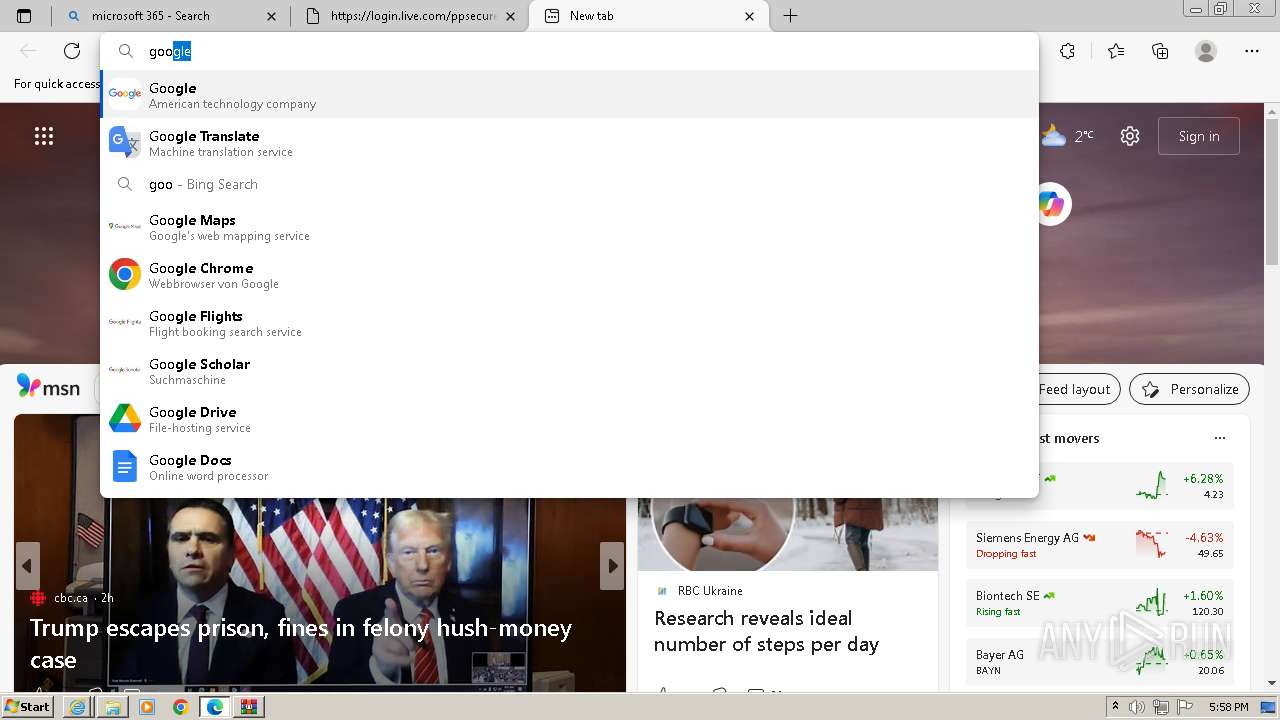
google.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
m2g.io.in |
| unknown |
ocsp.digicert.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r11.o.lencr.org |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
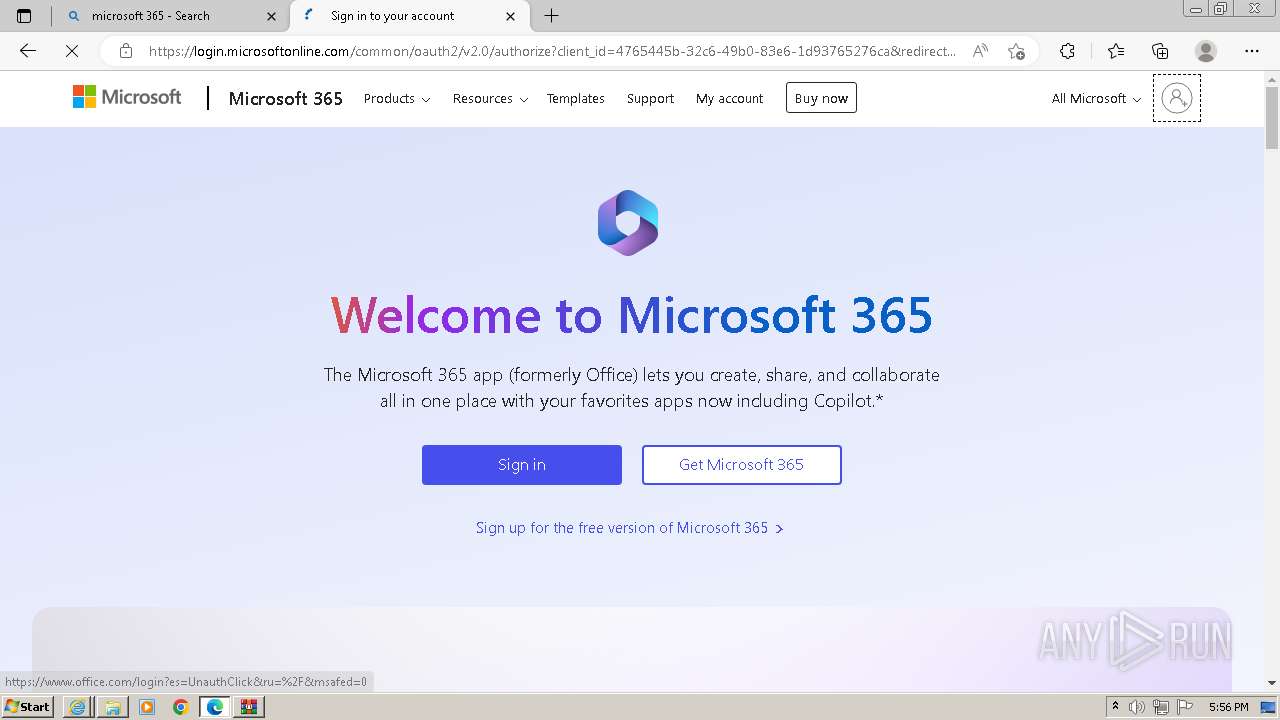
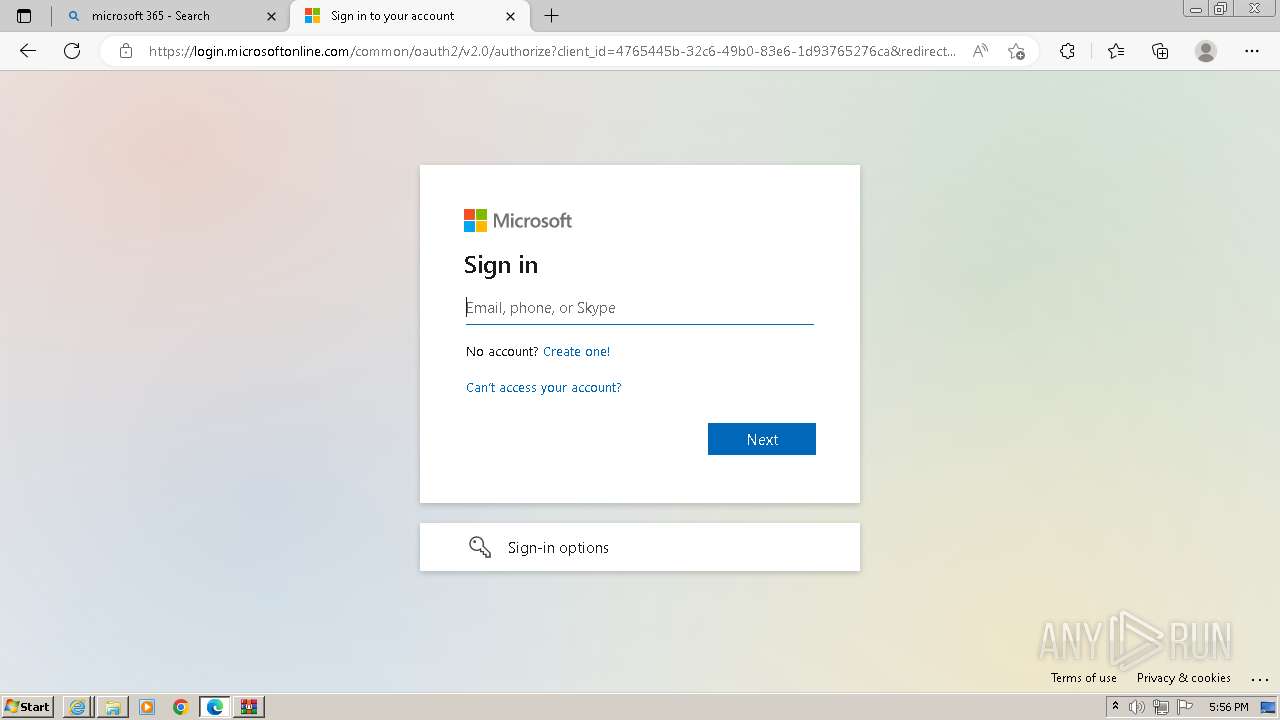
912 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
912 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
912 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
912 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
912 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
912 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
912 | msedge.exe | Misc activity | SUSPICIOUS [ANY.RUN] Tracking Service (.popin .cc) |
912 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
912 | msedge.exe | Misc activity | SUSPICIOUS [ANY.RUN] Tracking Service (.popin .cc) |
912 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |