| File name: | crss.exe |
| Full analysis: | https://app.any.run/tasks/cc4e3d29-5ffe-4220-bbe7-88e02085c032 |
| Verdict: | Malicious activity |
| Analysis date: | October 29, 2024, 16:22:37 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 6 sections |
| MD5: | F3BB8CF06F10DD217E03FDBC59469133 |
| SHA1: | 0C502245D752A6025706E77D67BD20815C8534E4 |
| SHA256: | B7A5D160E405DD03C501272FFBD4D0B8C33FEA67FE357C3362AAEA1B49B820D4 |
| SSDEEP: | 98304:s6ClazeJu8M+J4tqaOFHhwIsRjKOVWjtKxgA5evnaY8g2XpNpZM/xiLEDKIbjQrc:47rbyLh6YCU3pIwWm1bUe |
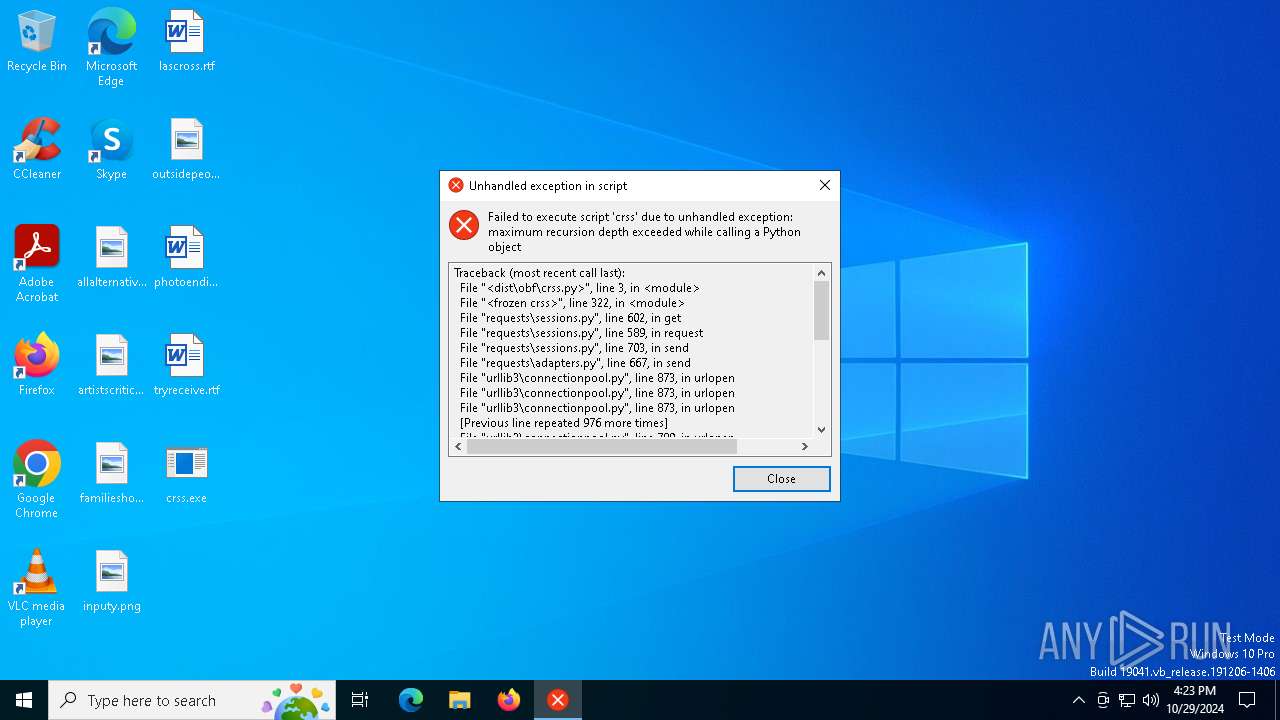
MALICIOUS
Changes the autorun value in the registry
- crss.exe (PID: 2648)
SUSPICIOUS
Executable content was dropped or overwritten
- crss.exe (PID: 5832)
Application launched itself
- crss.exe (PID: 5832)
Process drops legitimate windows executable
- crss.exe (PID: 5832)
The process drops C-runtime libraries
- crss.exe (PID: 5832)
Process drops python dynamic module
- crss.exe (PID: 5832)
Starts CMD.EXE for commands execution
- crss.exe (PID: 2648)
Potential Corporate Privacy Violation
- crss.exe (PID: 2648)
INFO
Reads the computer name
- crss.exe (PID: 5832)
- crss.exe (PID: 2648)
Checks supported languages
- crss.exe (PID: 2648)
- crss.exe (PID: 5832)
Reads the machine GUID from the registry
- crss.exe (PID: 2648)
Checks operating system version
- crss.exe (PID: 2648)
Create files in a temporary directory
- crss.exe (PID: 5832)
Checks proxy server information
- crss.exe (PID: 2648)
PyInstaller has been detected (YARA)
- crss.exe (PID: 5832)
- crss.exe (PID: 2648)
Application based on Rust
- crss.exe (PID: 2648)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:10:29 16:21:28+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.4 |
| CodeSize: | 172032 |
| InitializedDataSize: | 93184 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xcdb0 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
125
Monitored processes
4
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2648 | "C:\Users\admin\Desktop\crss.exe" | C:\Users\admin\Desktop\crss.exe | crss.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 3648 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5832 | "C:\Users\admin\Desktop\crss.exe" | C:\Users\admin\Desktop\crss.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 5920 | C:\WINDOWS\system32\cmd.exe /c "ver" | C:\Windows\System32\cmd.exe | — | crss.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
348
Read events
347
Write events
1
Delete events
0
Modification events
| (PID) Process: | (2648) crss.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | козляк |
Value: C:\Users\admin\Desktop\crss.exe | |||
Executable files
33
Suspicious files
1
Text files
122
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5832 | crss.exe | C:\Users\admin\AppData\Local\Temp\_MEI58322\_cffi_backend.cp310-win_amd64.pyd | executable | |
MD5:2BAAA98B744915339AE6C016B17C3763 | SHA256:4F1CE205C2BE986C9D38B951B6BCB6045EB363E06DACC069A41941F80BE9068C | |||
| 5832 | crss.exe | C:\Users\admin\AppData\Local\Temp\_MEI58322\_hashlib.pyd | executable | |
MD5:D4674750C732F0DB4C4DD6A83A9124FE | SHA256:CAA4D2F8795E9A55E128409CC016E2CC5C694CB026D7058FC561E4DD131ED1C9 | |||
| 5832 | crss.exe | C:\Users\admin\AppData\Local\Temp\_MEI58322\VCRUNTIME140.dll | executable | |
MD5:F34EB034AA4A9735218686590CBA2E8B | SHA256:9D2B40F0395CC5D1B4D5EA17B84970C29971D448C37104676DB577586D4AD1B1 | |||
| 5832 | crss.exe | C:\Users\admin\AppData\Local\Temp\_MEI58322\_socket.pyd | executable | |
MD5:819166054FEC07EFCD1062F13C2147EE | SHA256:E6DEB751039CD5424A139708475CE83F9C042D43E650765A716CB4A924B07E4F | |||
| 5832 | crss.exe | C:\Users\admin\AppData\Local\Temp\_MEI58322\_lzma.pyd | executable | |
MD5:7447EFD8D71E8A1929BE0FAC722B42DC | SHA256:60793C8592193CFBD00FD3E5263BE4315D650BA4F9E4FDA9C45A10642FD998BE | |||
| 5832 | crss.exe | C:\Users\admin\AppData\Local\Temp\_MEI58322\_queue.pyd | executable | |
MD5:D8C1B81BBC125B6AD1F48A172181336E | SHA256:925F05255F4AAE0997DC4EC94D900FD15950FD840685D5B8AA755427C7422B14 | |||
| 5832 | crss.exe | C:\Users\admin\AppData\Local\Temp\_MEI58322\_overlapped.pyd | executable | |
MD5:FDF8663B99959031780583CCE98E10F5 | SHA256:2EBBB0583259528A5178DD37439A64AFFCB1AB28CF323C6DC36A8C30362AA992 | |||
| 5832 | crss.exe | C:\Users\admin\AppData\Local\Temp\_MEI58322\_pytransform.dll | executable | |
MD5:23376A4DF02C2BB0B770930449355ACB | SHA256:E999F10F53A09DDD5C6E05AD8BD3635C43D1035EB70AFD32463875A1AEF030CD | |||
| 5832 | crss.exe | C:\Users\admin\AppData\Local\Temp\_MEI58322\_multiprocessing.pyd | executable | |
MD5:A9A0588711147E01EED59BE23C7944A9 | SHA256:7581EDEA33C1DB0A49B8361E51E6291688601640E57D75909FB2007B2104FA4C | |||
| 5832 | crss.exe | C:\Users\admin\AppData\Local\Temp\_MEI58322\_decimal.pyd | executable | |
MD5:20C77203DDF9FF2FF96D6D11DEA2EDCF | SHA256:9AAC010A424C757C434C460C3C0A6515D7720966AB64BAD667539282A17B4133 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
1 000
DNS requests
9
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1248 | RUXIMICS.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1248 | RUXIMICS.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2648 | crss.exe | GET | 200 | 142.250.184.228:80 | http://www.google.com/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1248 | RUXIMICS.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1248 | RUXIMICS.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1248 | RUXIMICS.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5488 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.google.com |
| whitelisted |
raw.githubusercontent.com |
| shared |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2172 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
1 ETPRO signatures available at the full report