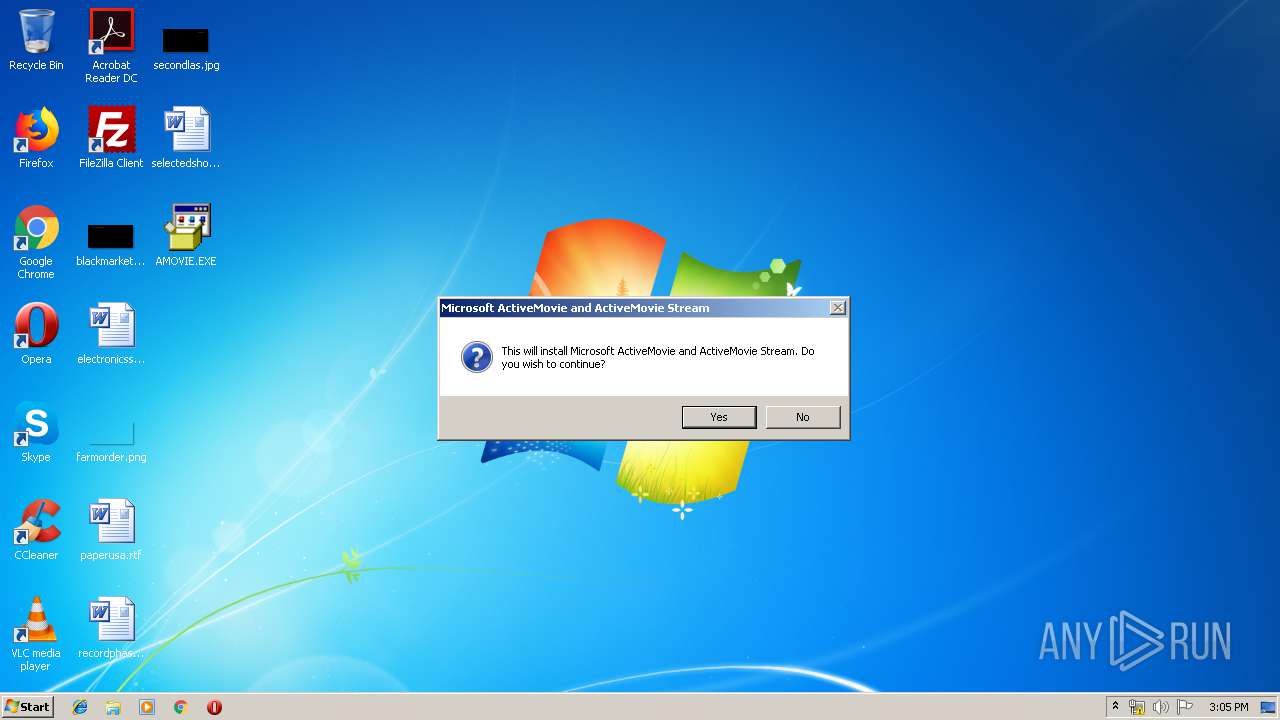
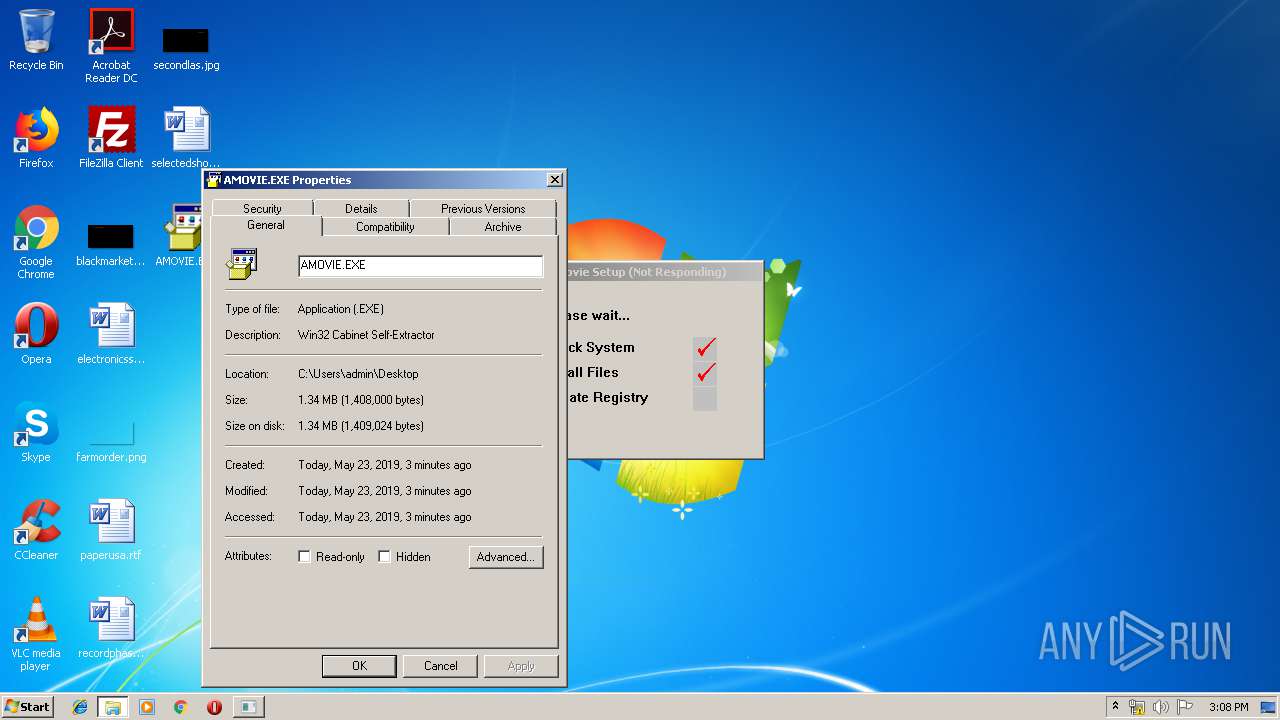
| File name: | AMOVIE.EXE |
| Full analysis: | https://app.any.run/tasks/06c768c7-ad7e-4233-843f-0ac7445907fc |
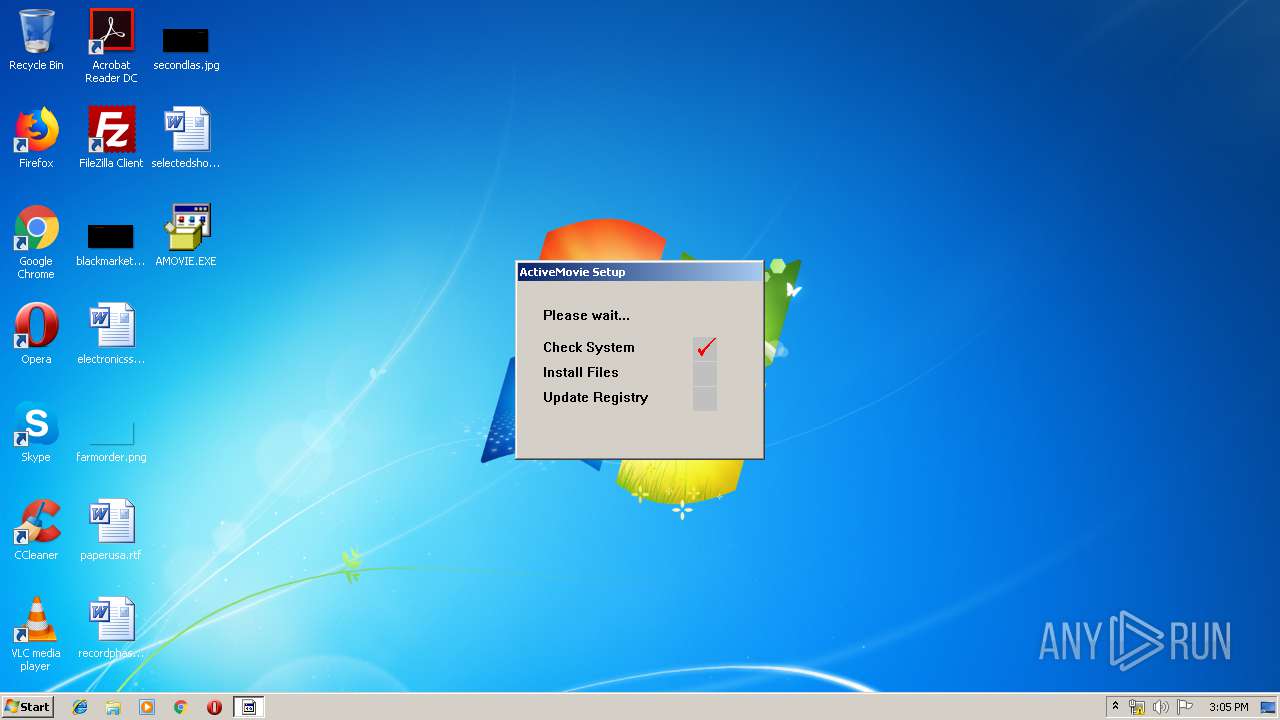
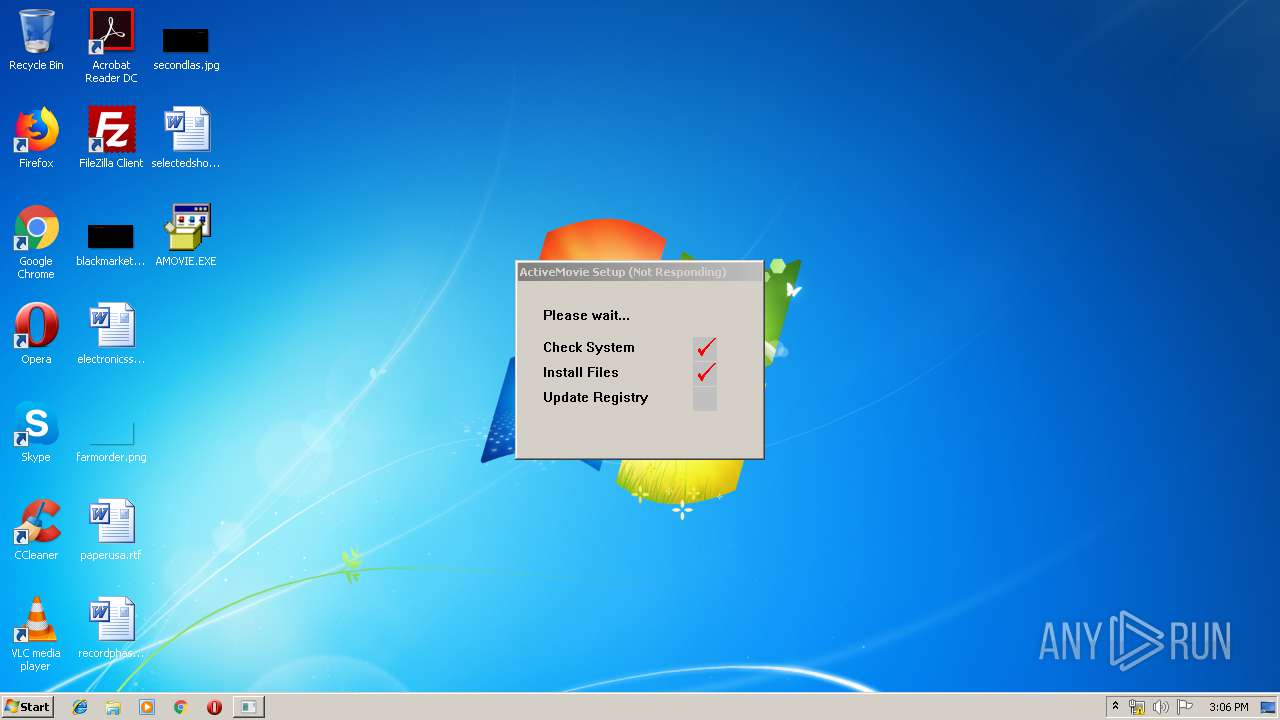
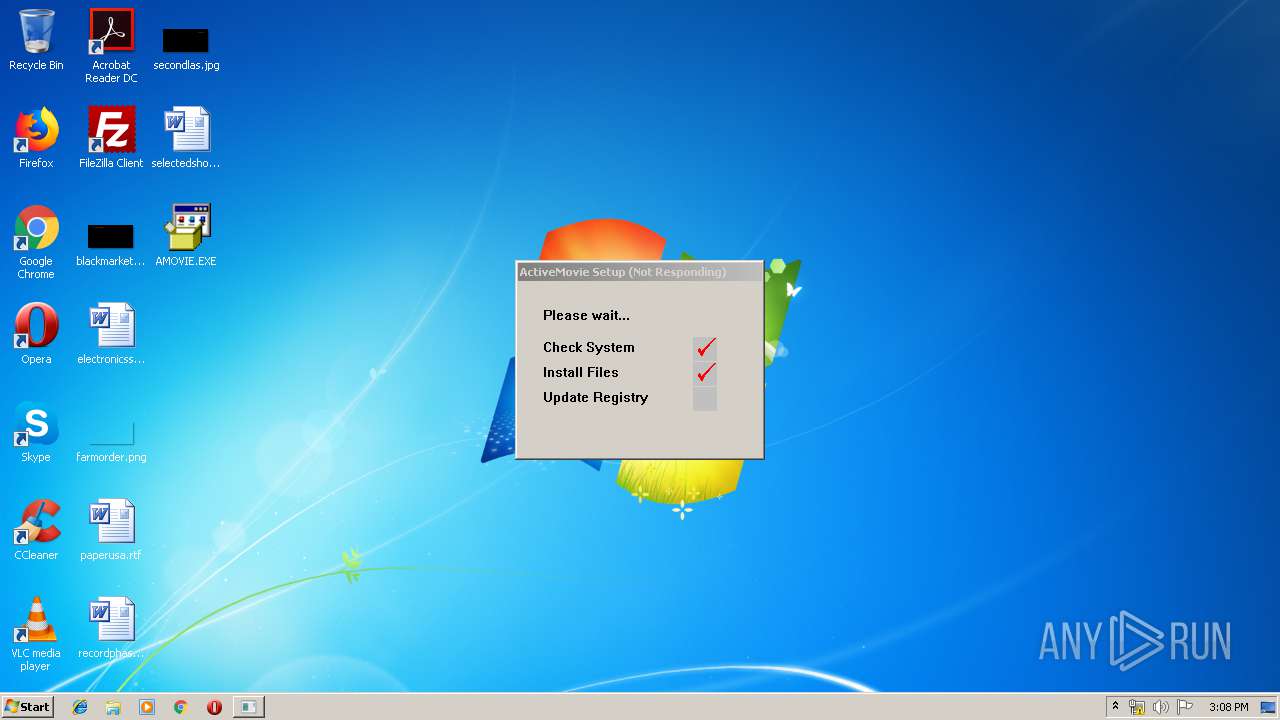
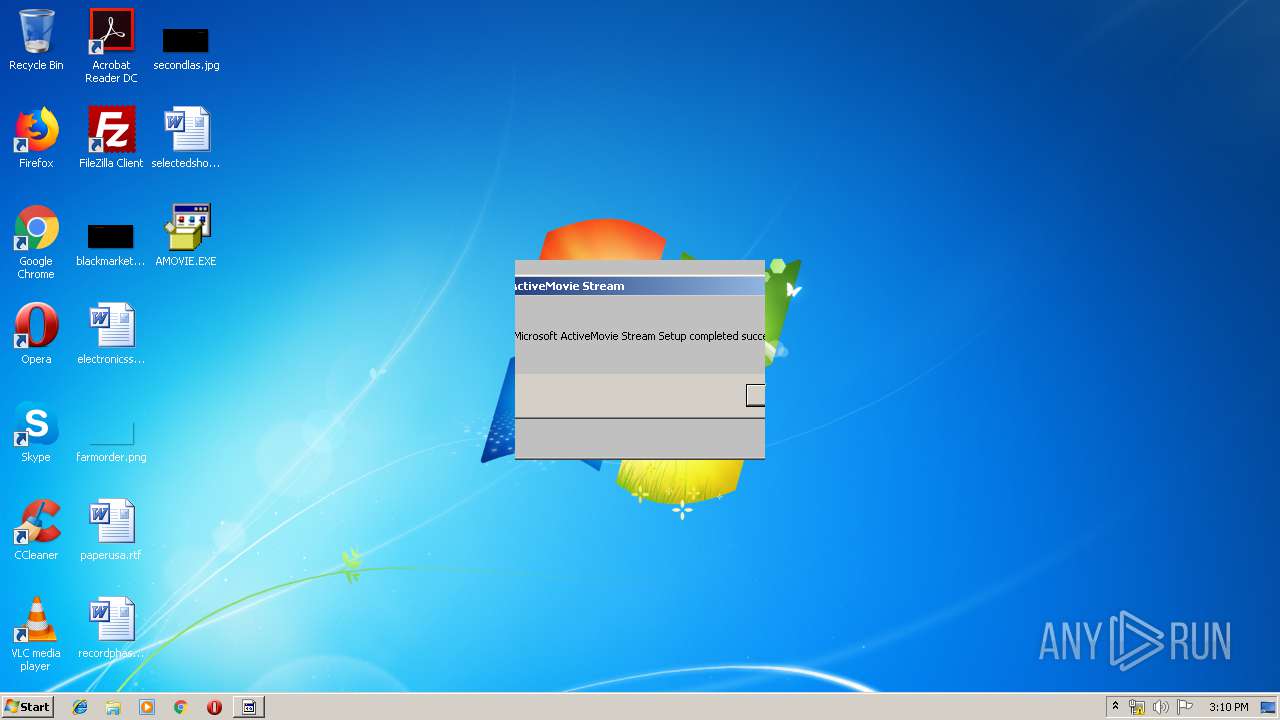
| Verdict: | Malicious activity |
| Analysis date: | May 23, 2019, 14:04:46 |
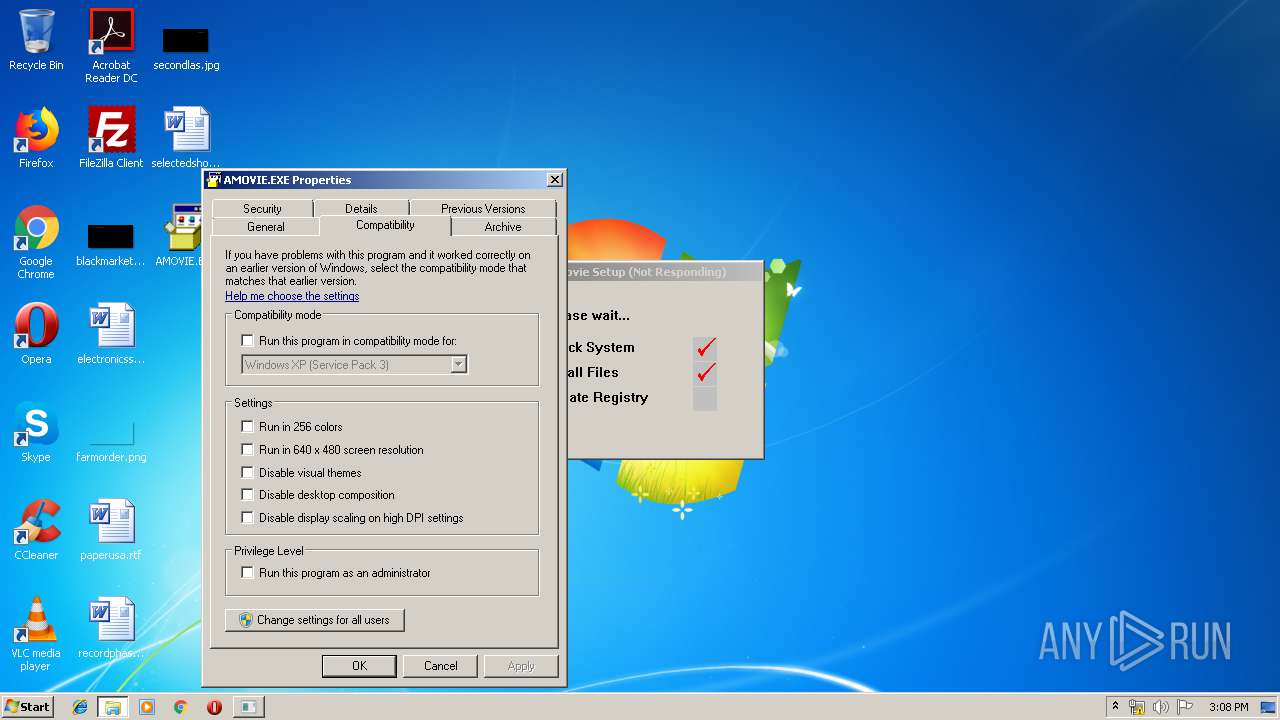
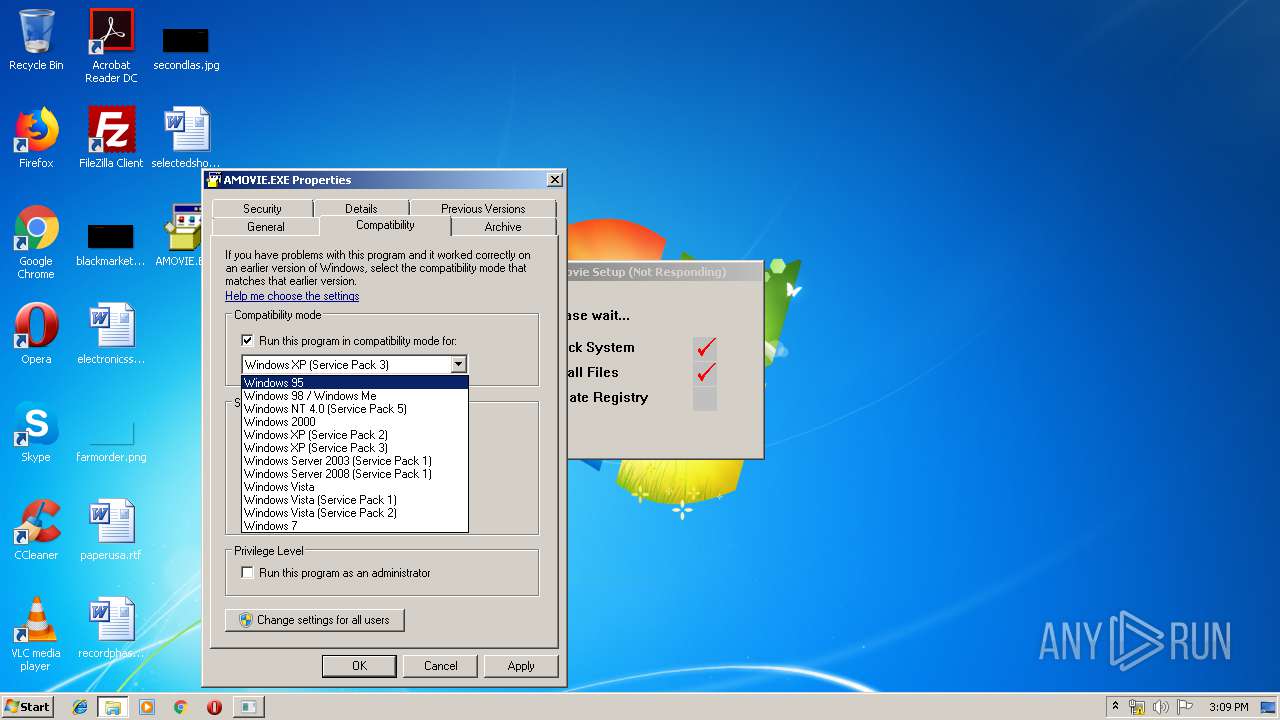
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 3FB053FFD52FE8ABEB96C8B6BA68FB30 |
| SHA1: | CAFA9637523878699AA830A0A157B54E6E58632E |
| SHA256: | B79397B8BE1E1A2A0D48C749AFE2E52296EEE53213E152CCC0C58FDDE2D9EB9C |
| SSDEEP: | 24576:QeDywLnpYBWy0OCuOKG/5ZHXoiMpC+MzNCt9cJGVR0zrfLjTnd71FUgQxMsW:lPNYBHp8oBpdMzm9cJM0vfLnd71+Md |
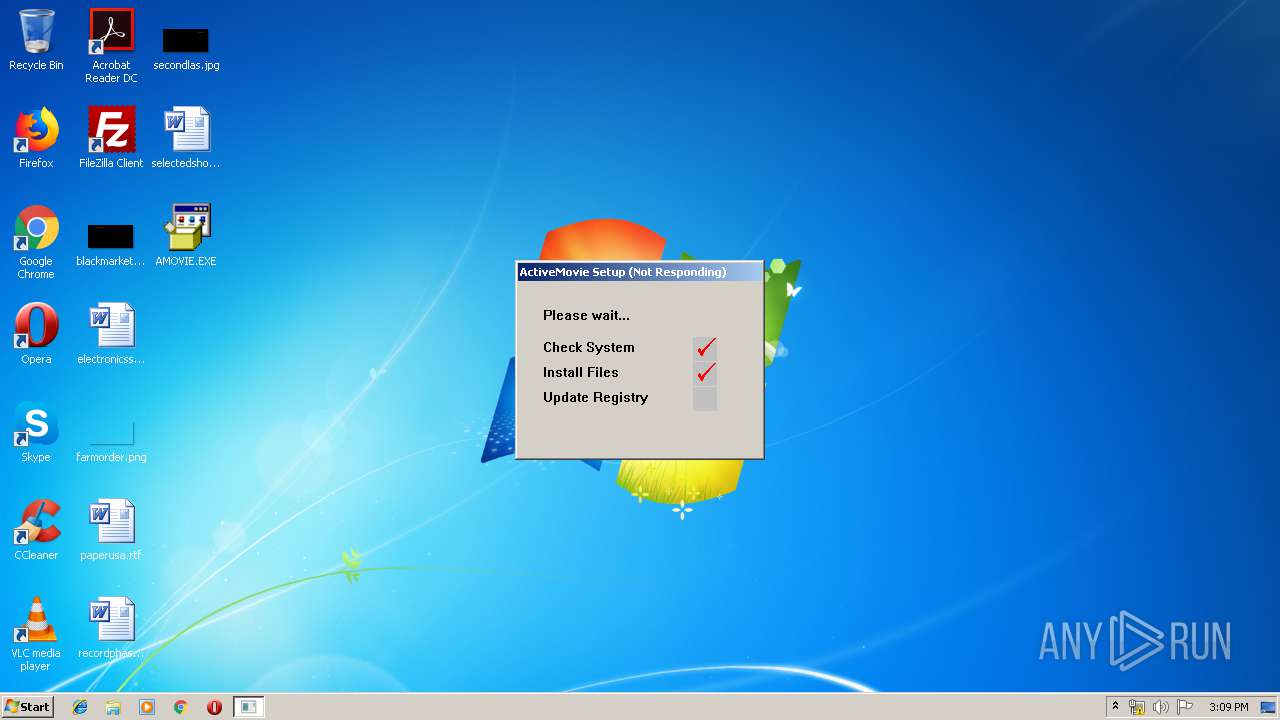
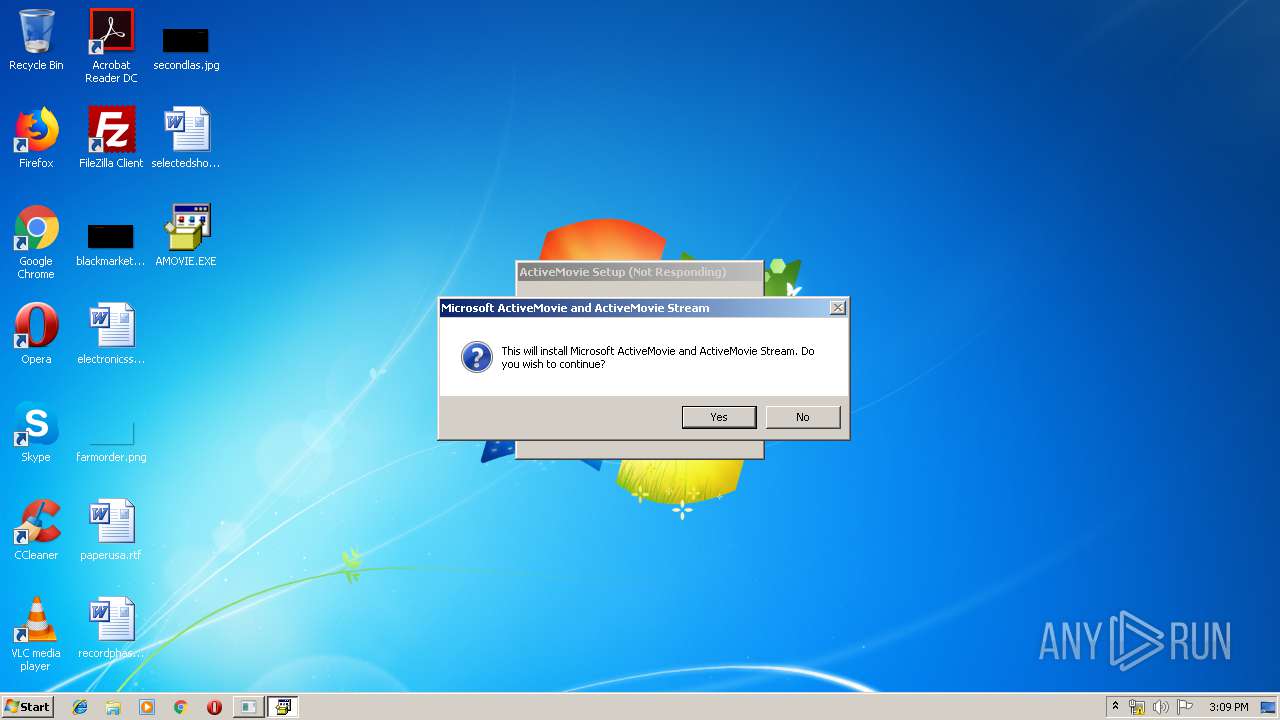
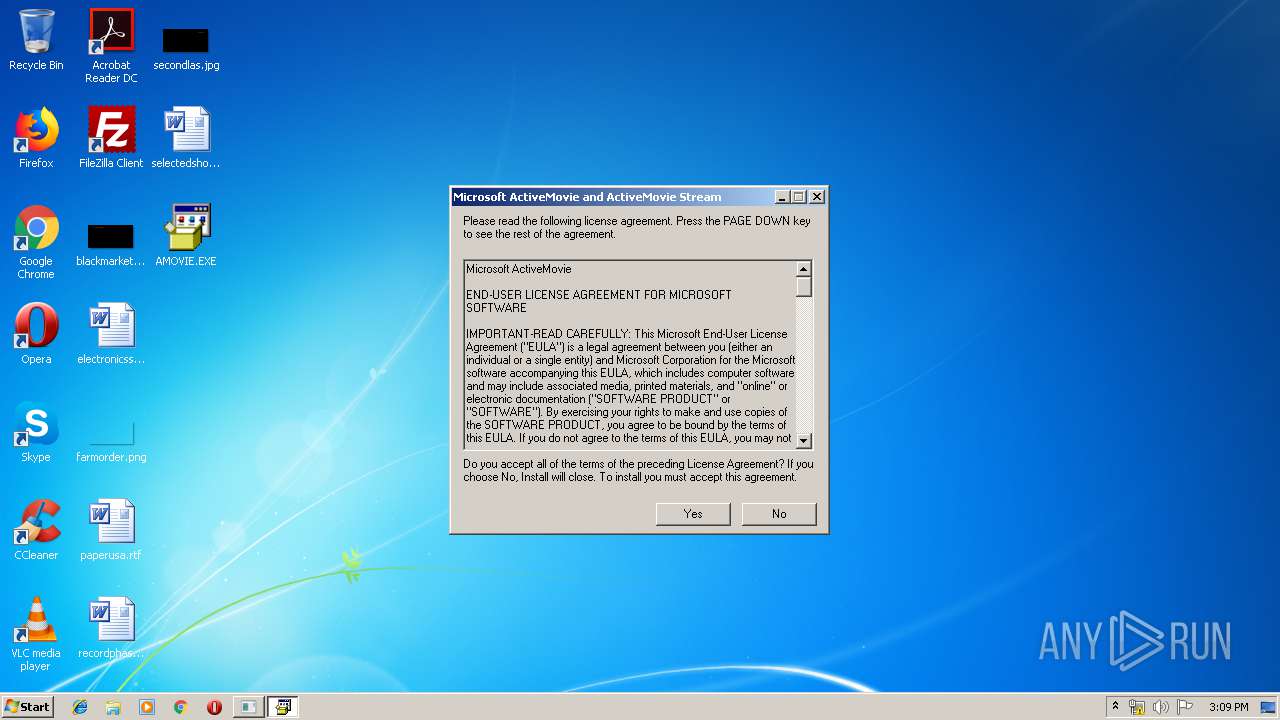
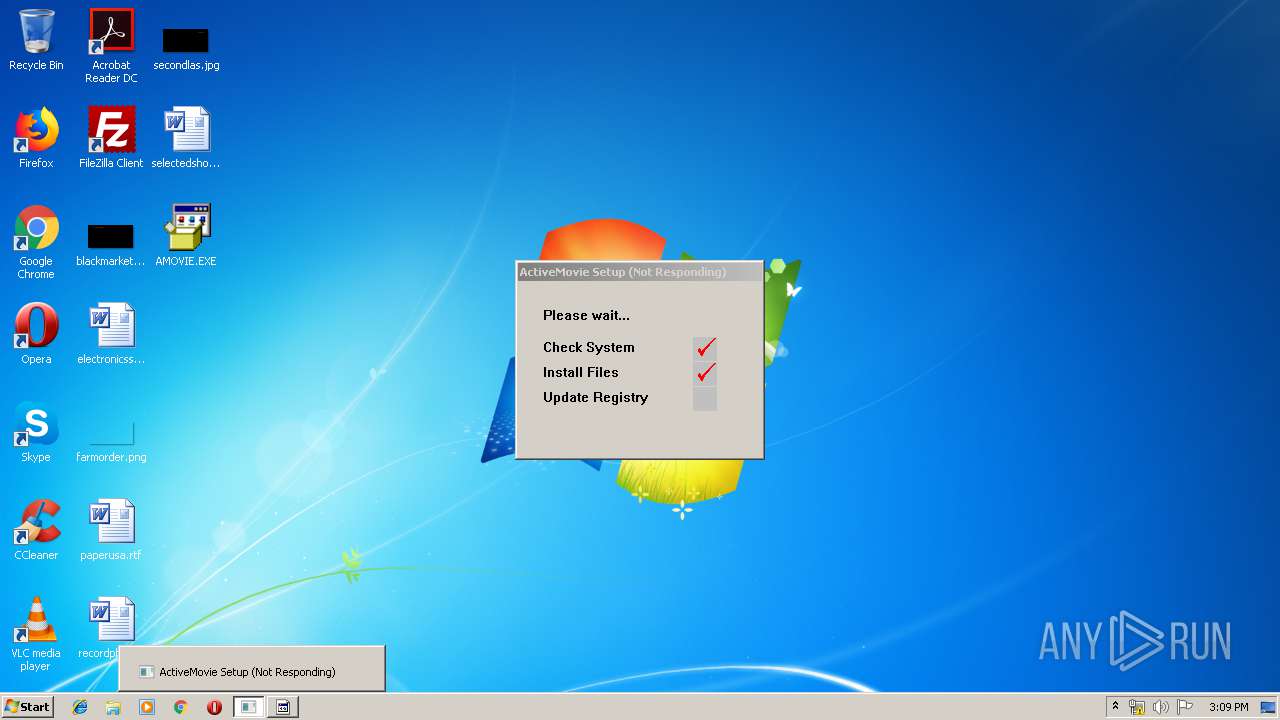
MALICIOUS
Changes the autorun value in the registry
- AMOVIE.EXE (PID: 3200)
- amovie.exe (PID: 3580)
- AMOVIE.EXE (PID: 1940)
- amovie.exe (PID: 2156)
- AMclient.exe (PID: 2388)
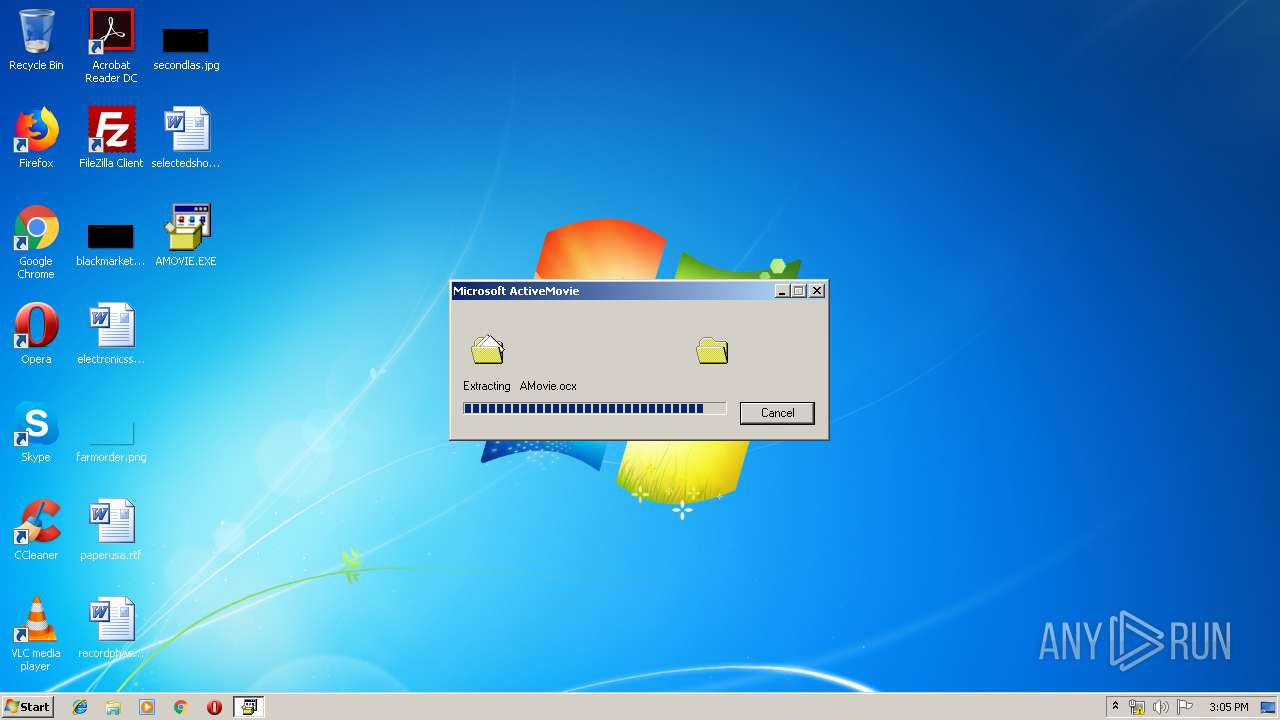
Application was dropped or rewritten from another process
- amovie.exe (PID: 3580)
- setupam.exe (PID: 3204)
- setupam.exe (PID: 2972)
- amovie.exe (PID: 2156)
- setupam.exe (PID: 2200)
- AMclient.exe (PID: 2388)
- Setup.exe (PID: 2992)
- Setup.exe (PID: 3568)
- asfclsid.exe (PID: 3780)
Loads dropped or rewritten executable
- setupam.exe (PID: 2972)
- setupam.exe (PID: 2200)
SUSPICIOUS
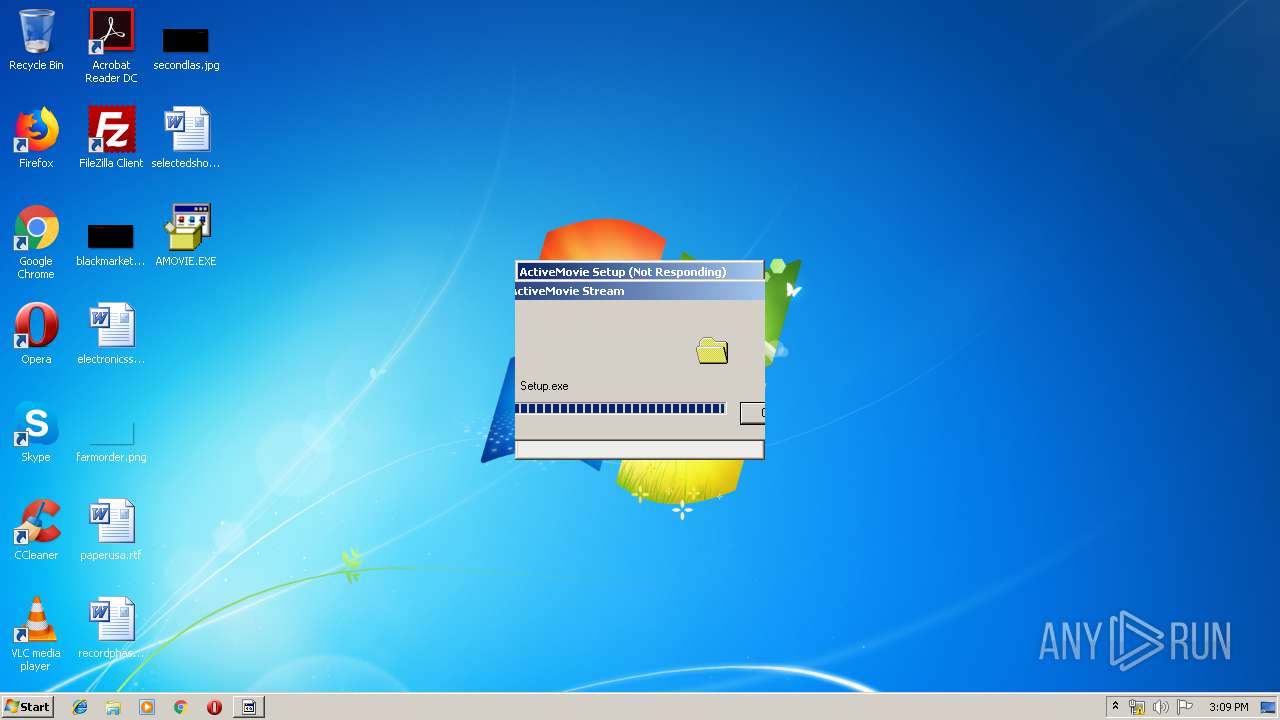
Executable content was dropped or overwritten
- amovie.exe (PID: 3580)
- AMOVIE.EXE (PID: 3200)
- setupam.exe (PID: 2972)
- AMOVIE.EXE (PID: 1940)
- amovie.exe (PID: 2156)
- AMclient.exe (PID: 2388)
- setupam.exe (PID: 2200)
- Setup.exe (PID: 3568)
Creates files in the Windows directory
- setupam.exe (PID: 2972)
- Setup.exe (PID: 3568)
- setupam.exe (PID: 2200)
Removes files from Windows directory
- setupam.exe (PID: 2200)
Modifies the open verb of a shell class
- Setup.exe (PID: 3568)
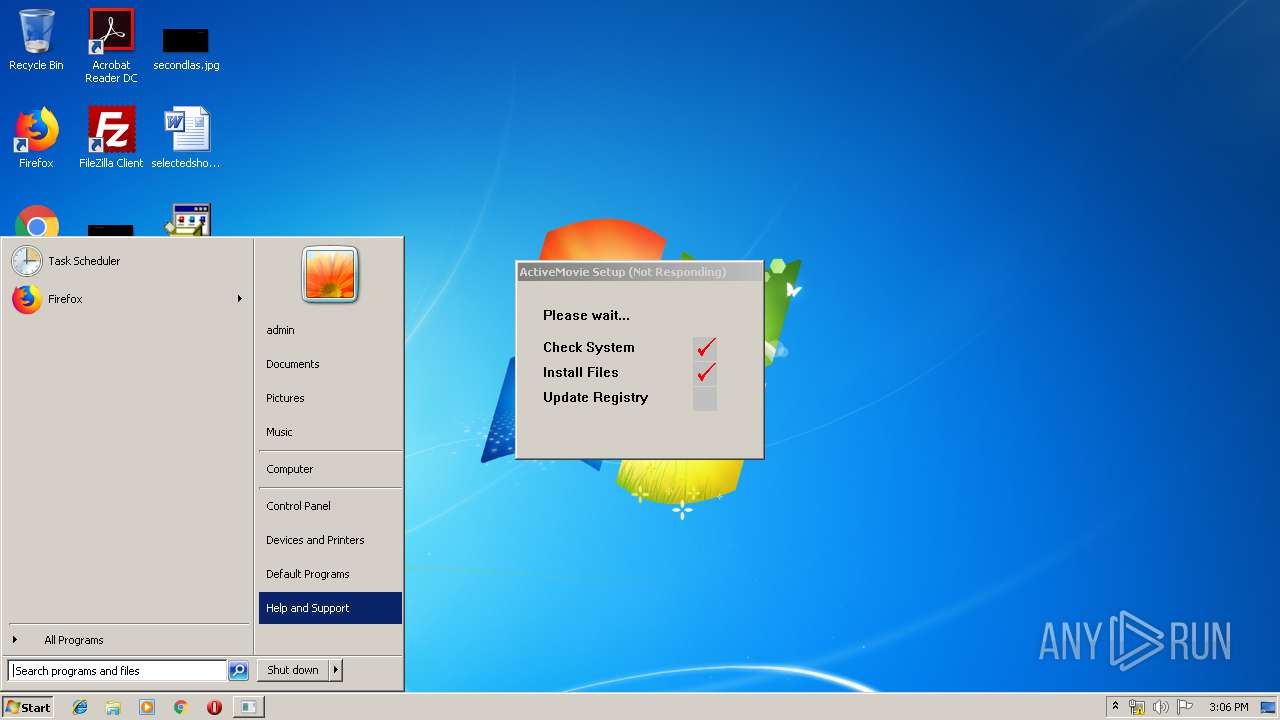
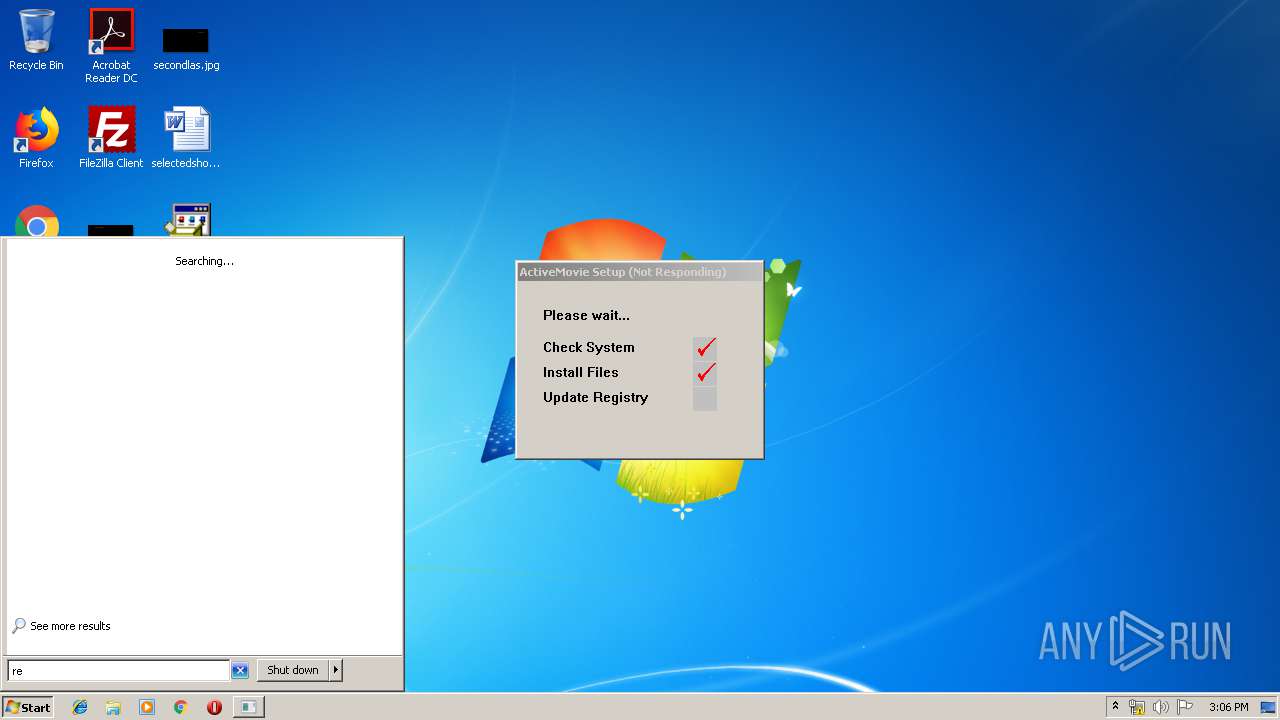
INFO
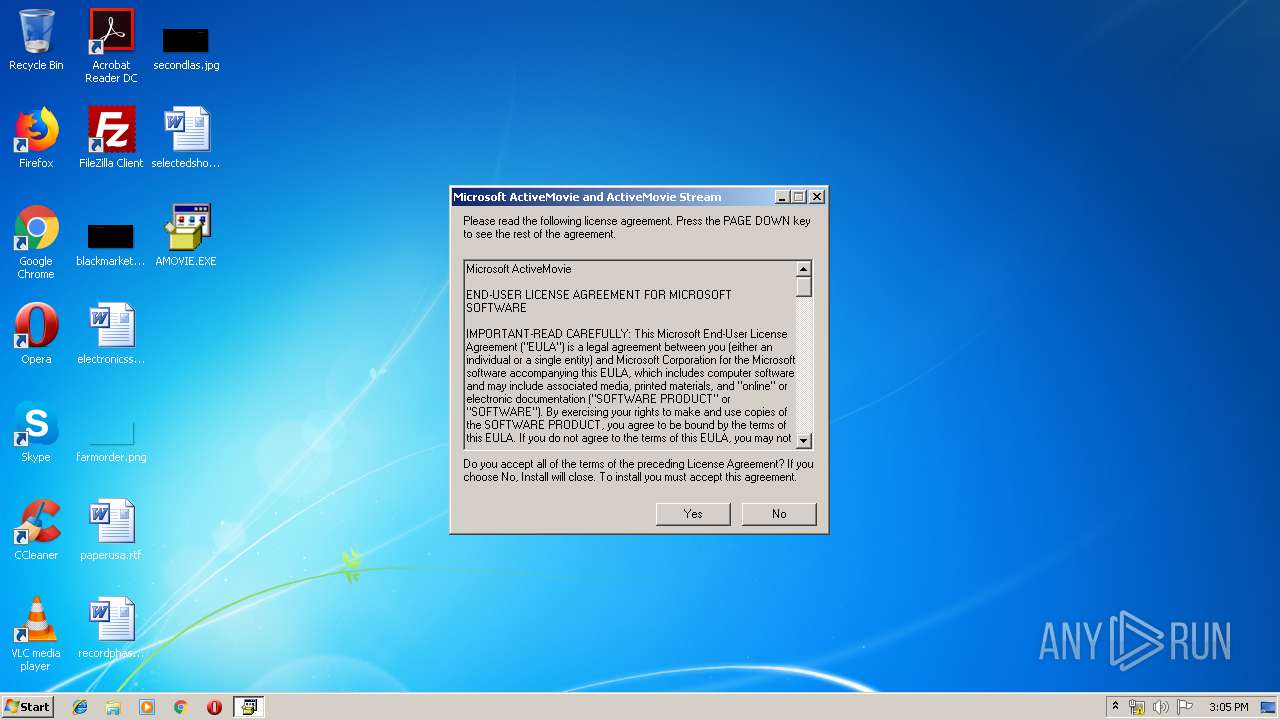
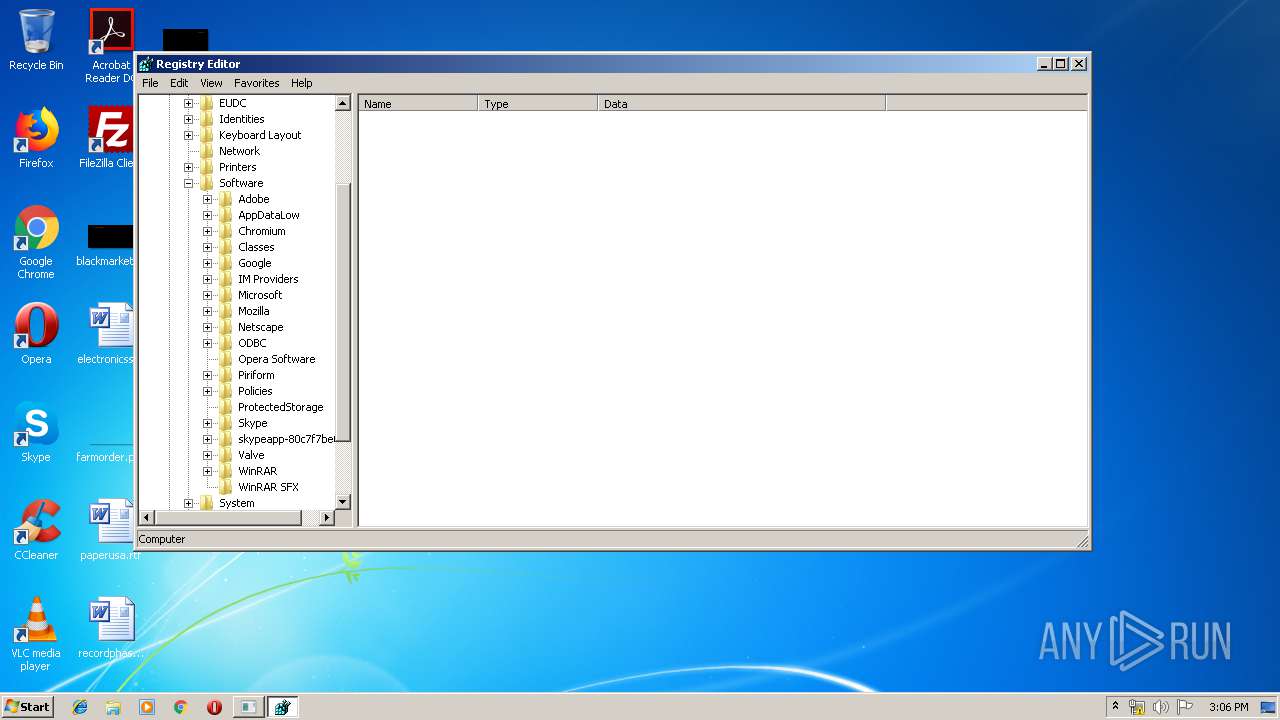
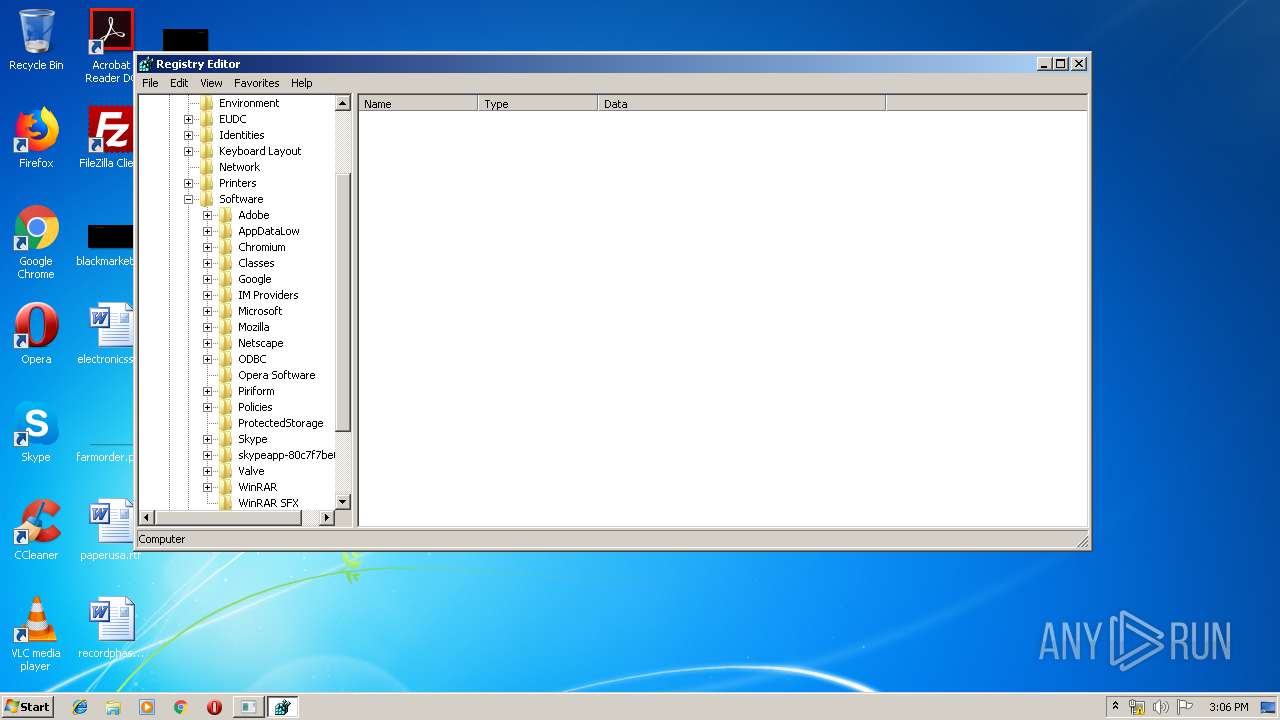
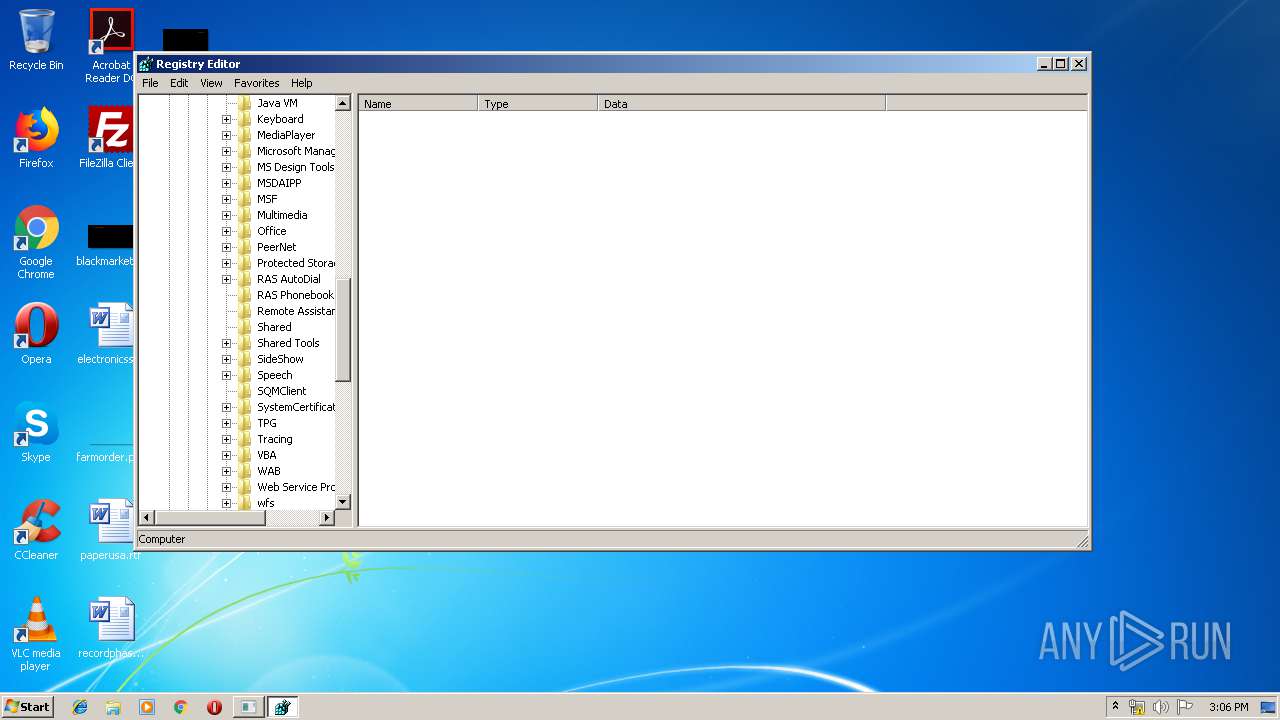
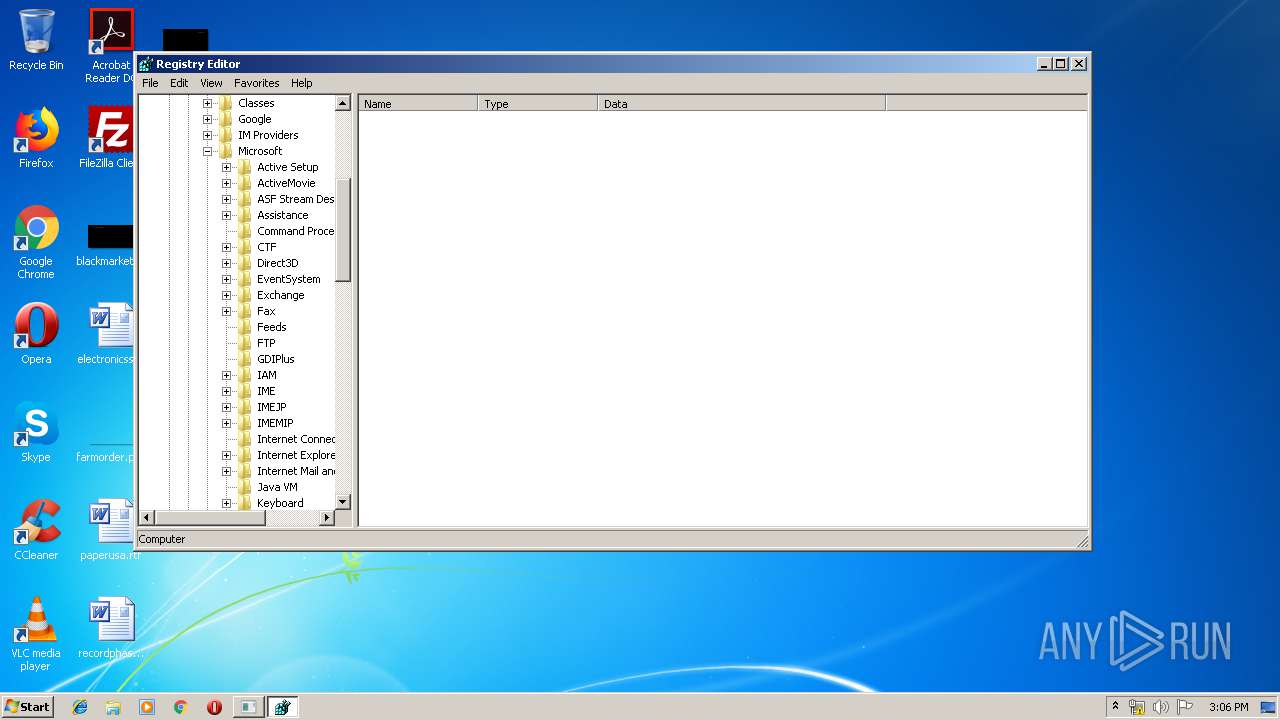
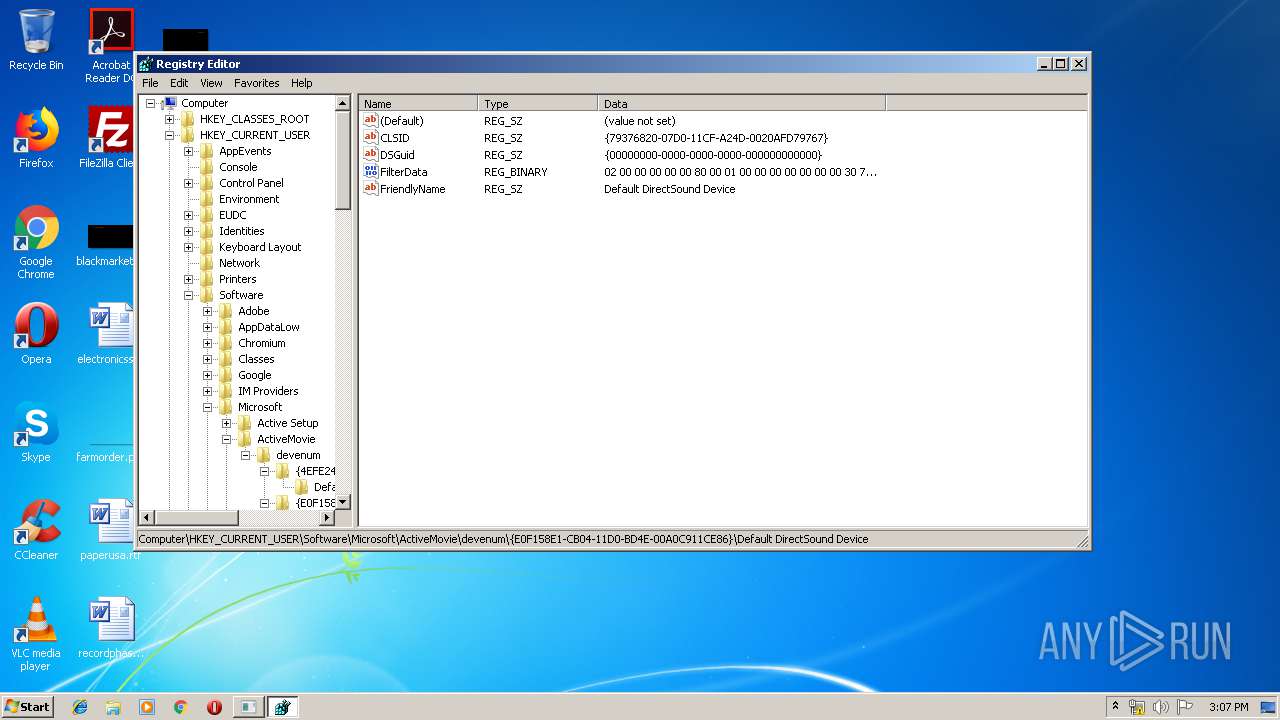
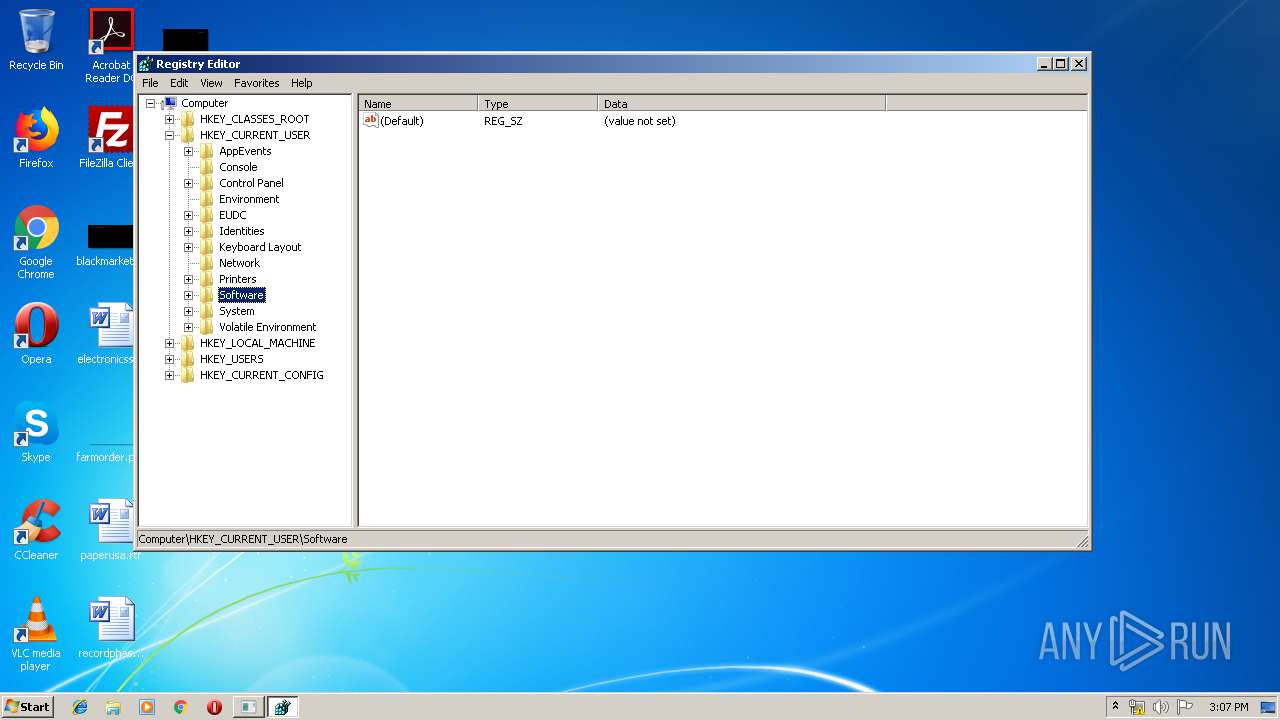
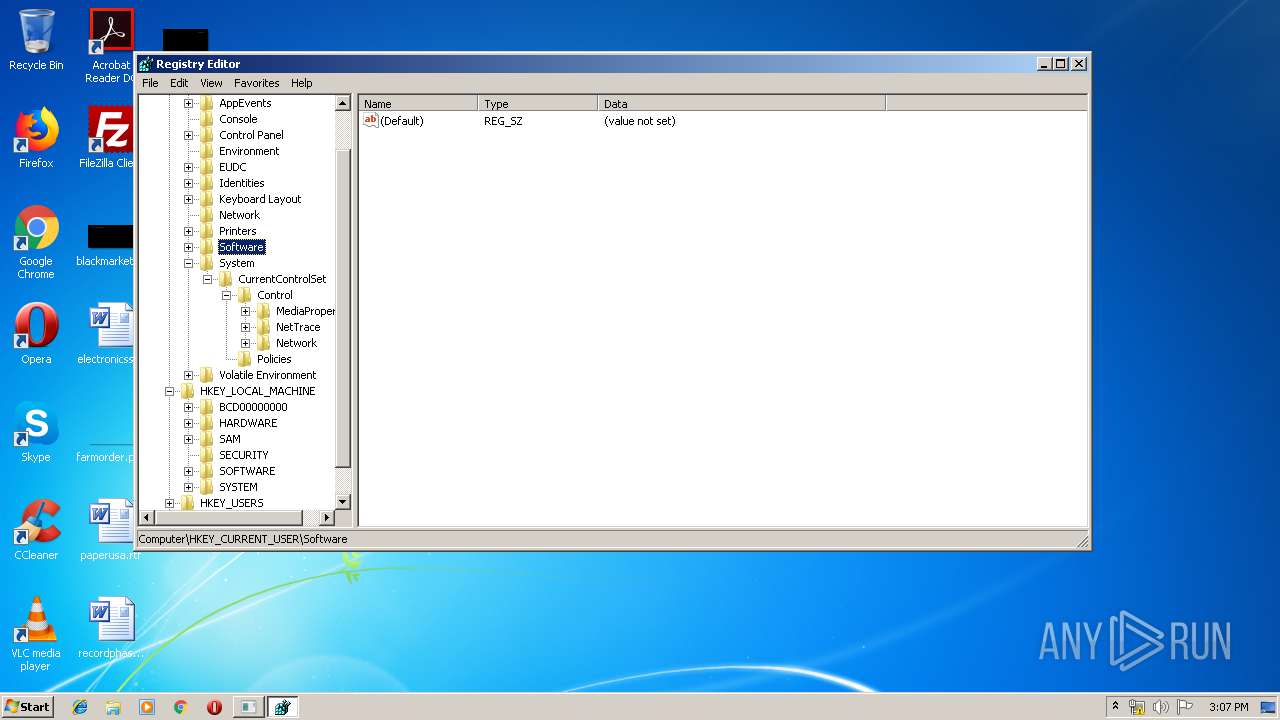
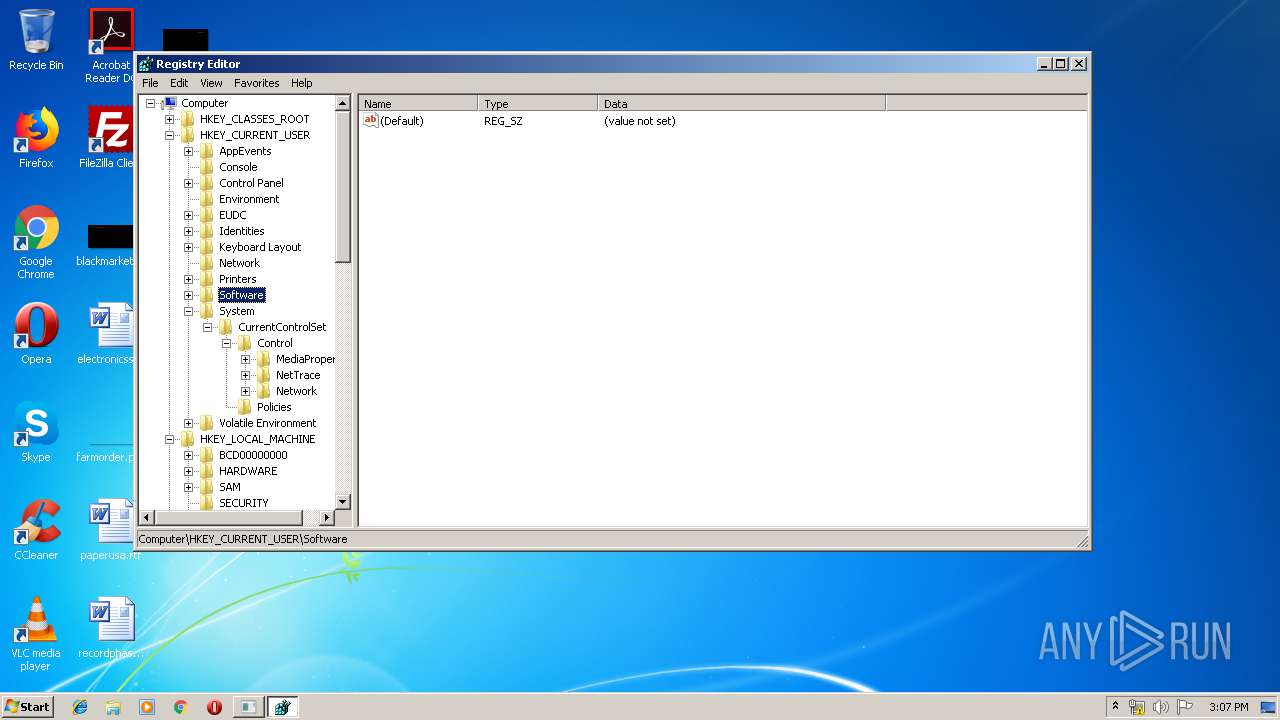
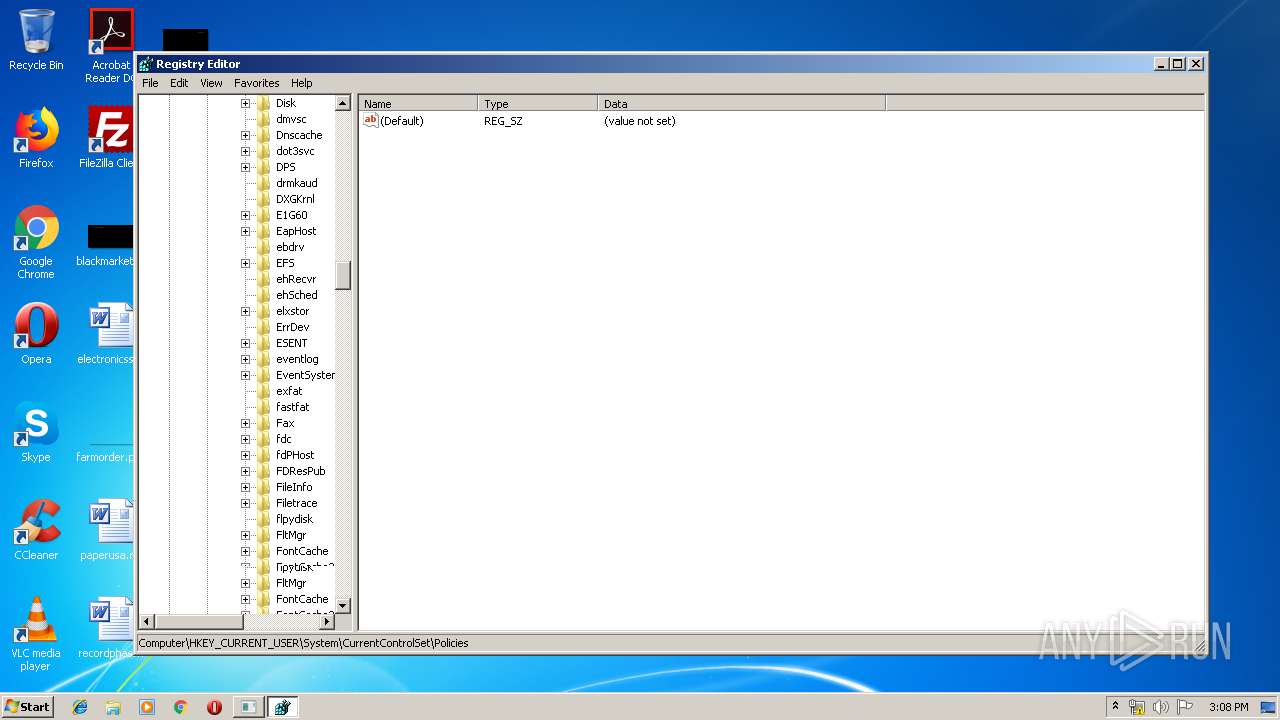
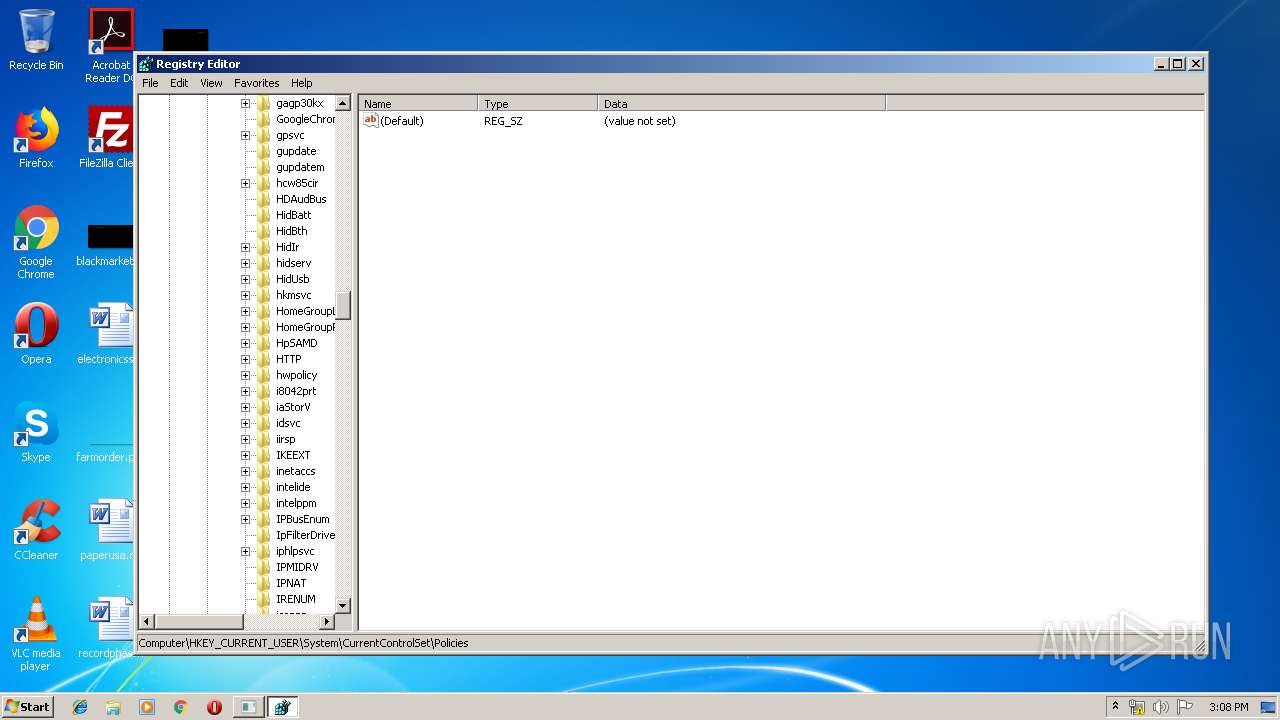
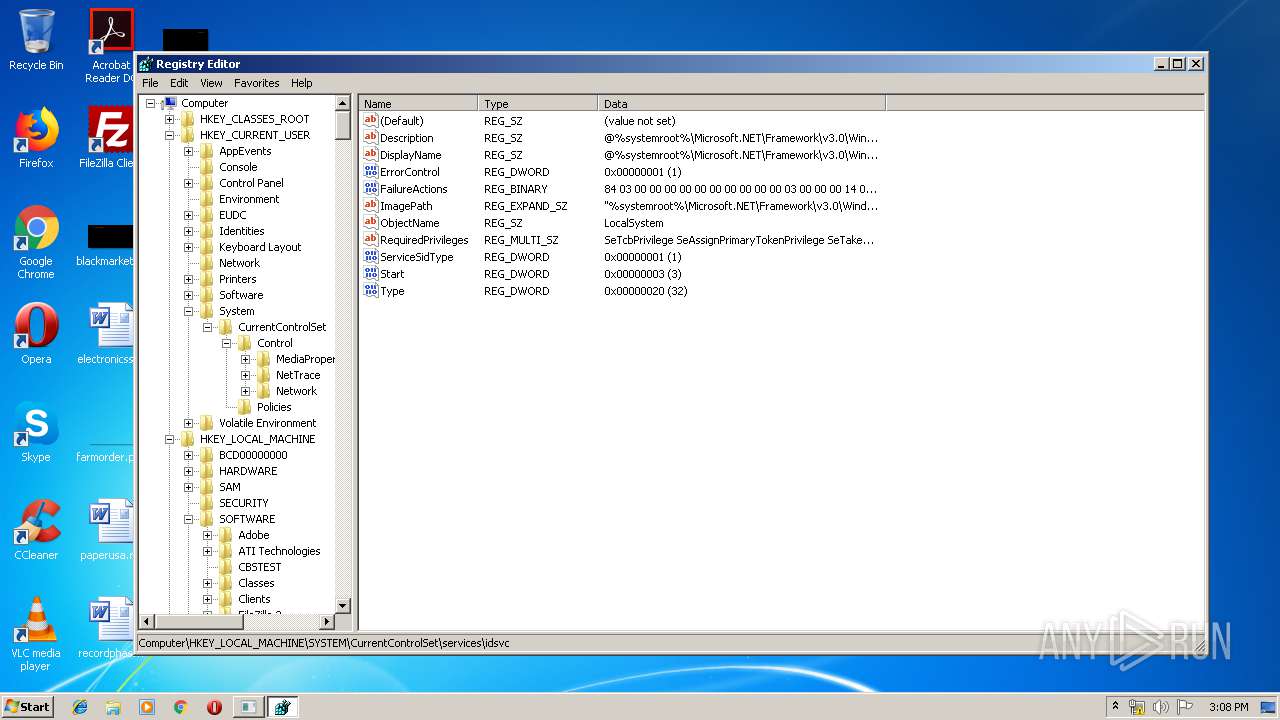
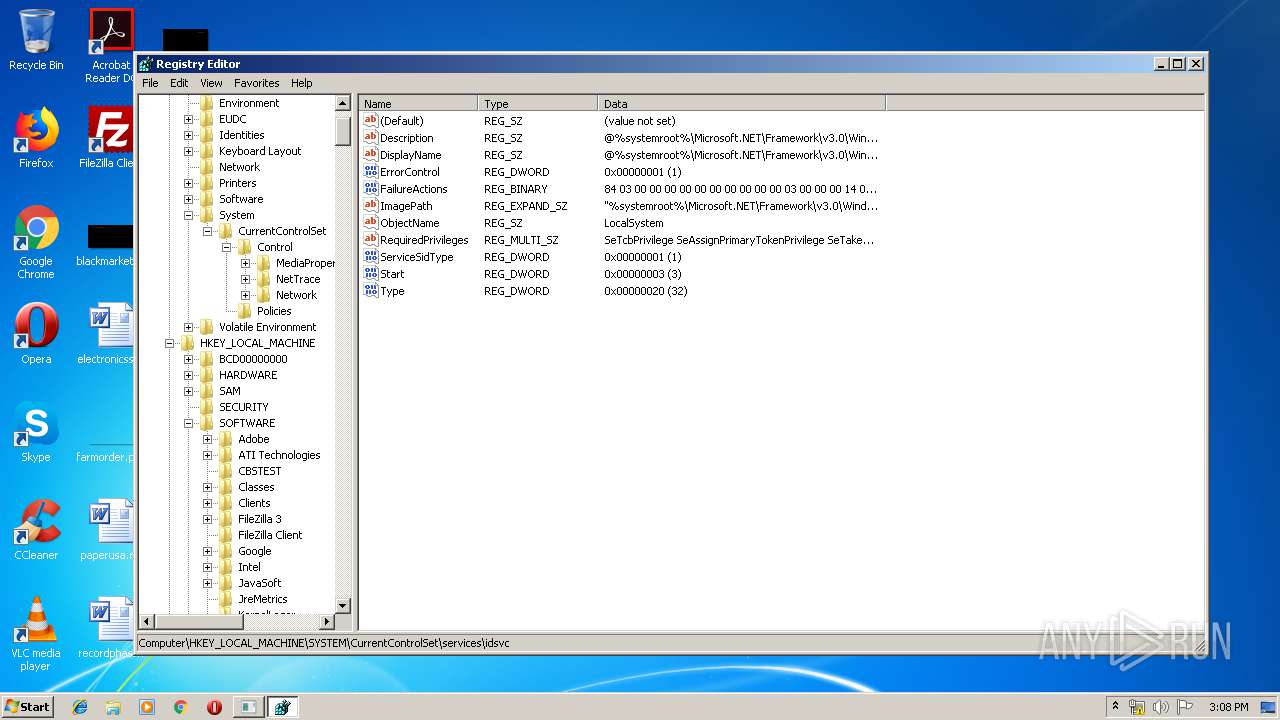
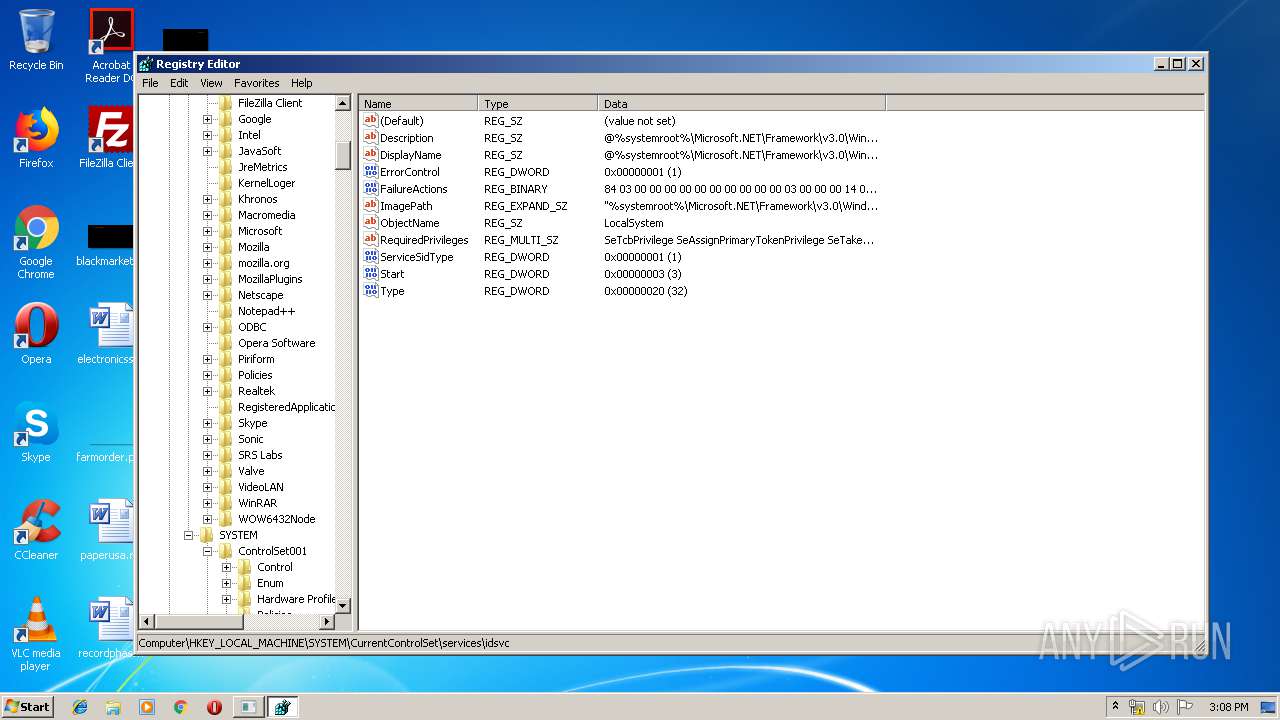
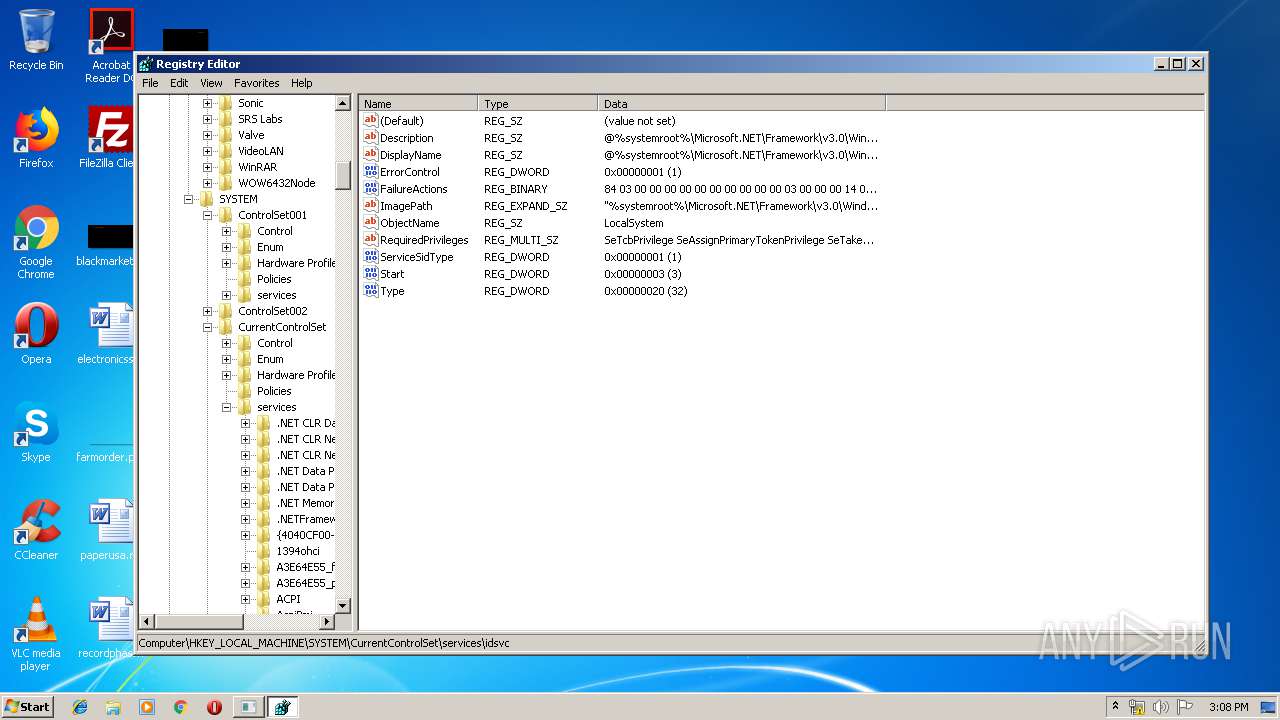
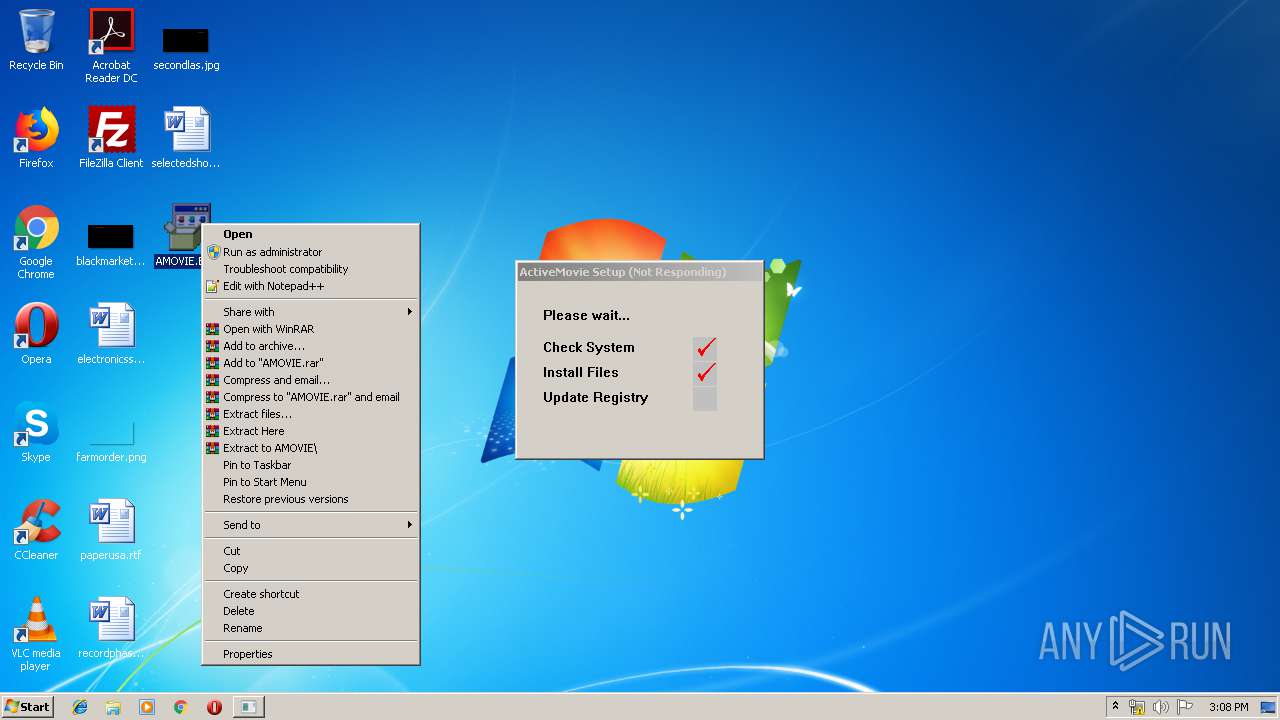
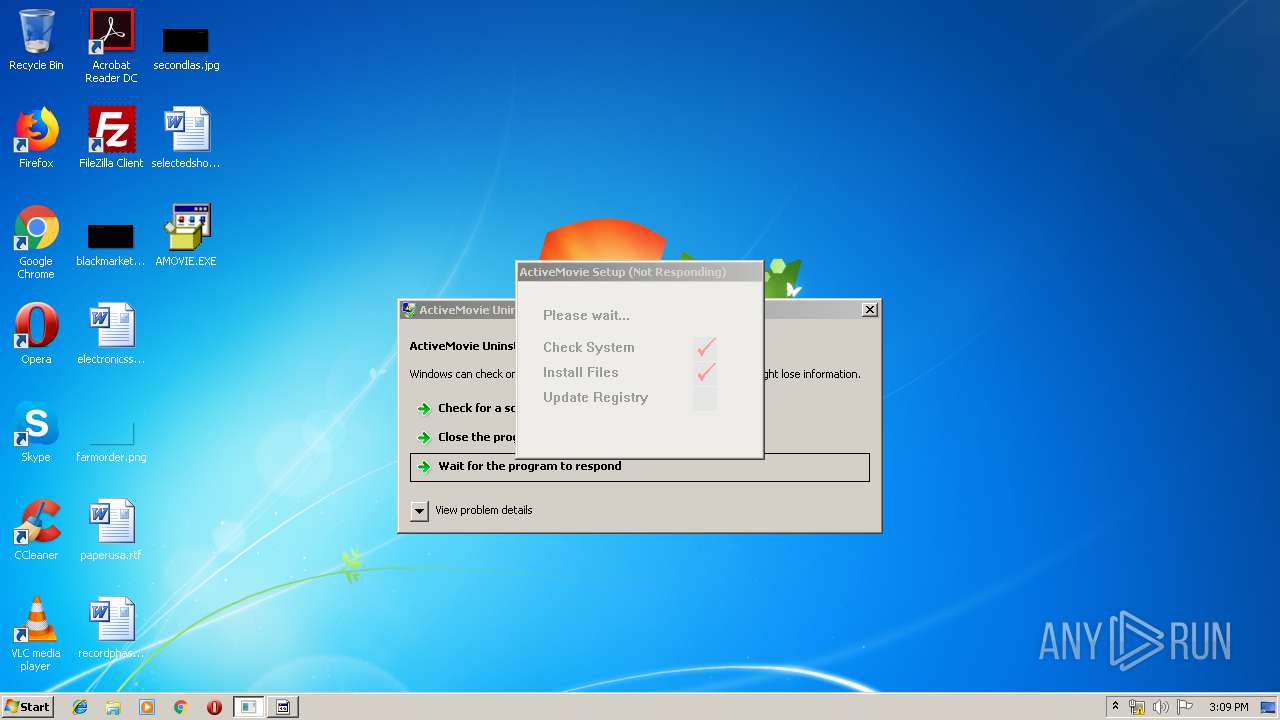
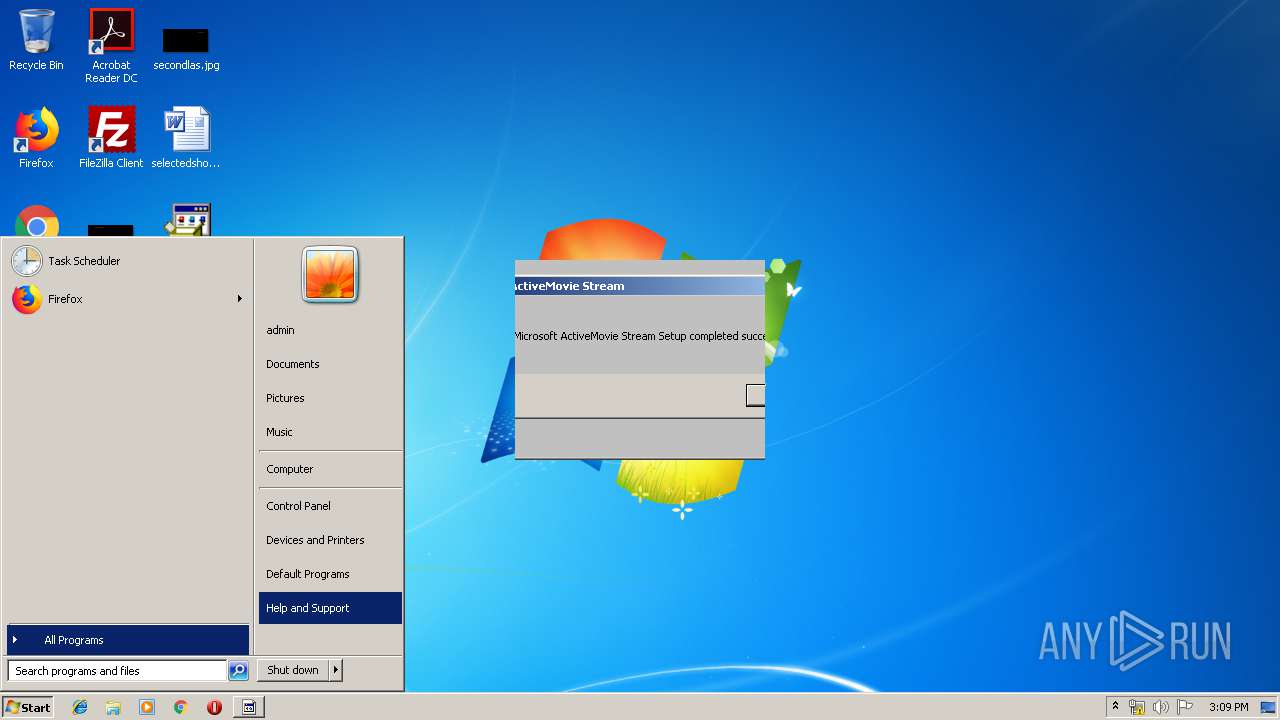
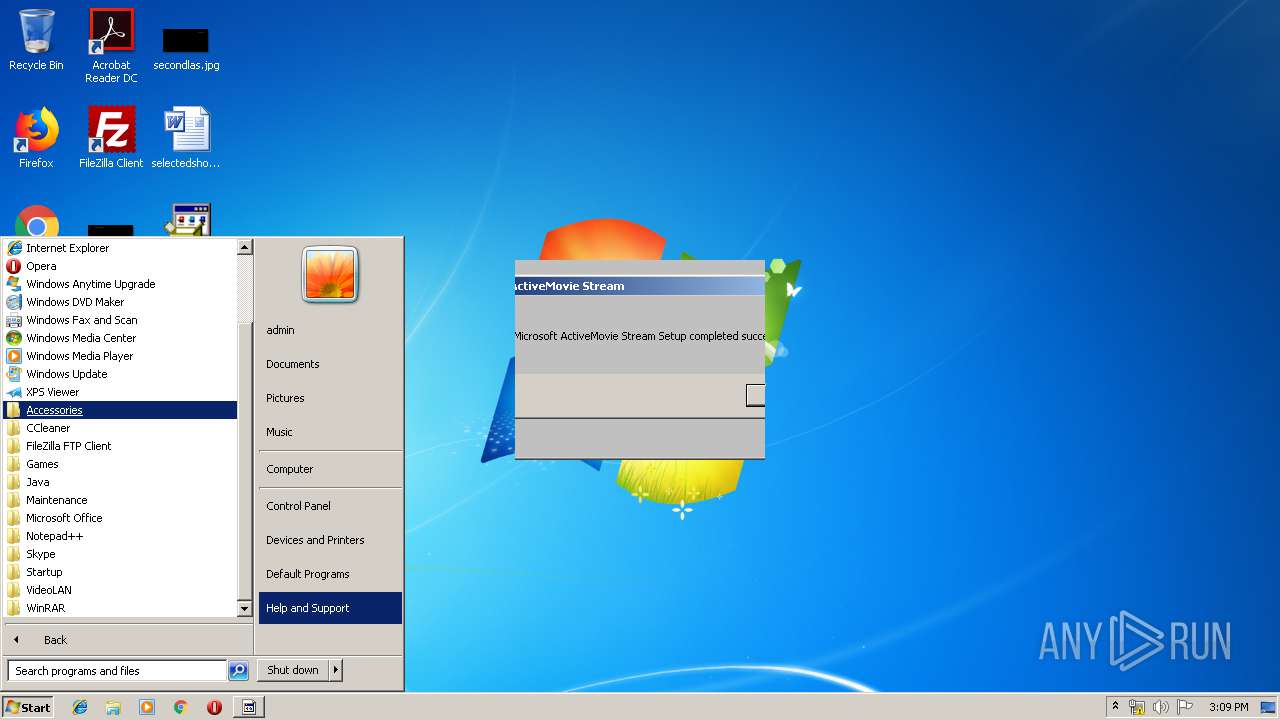
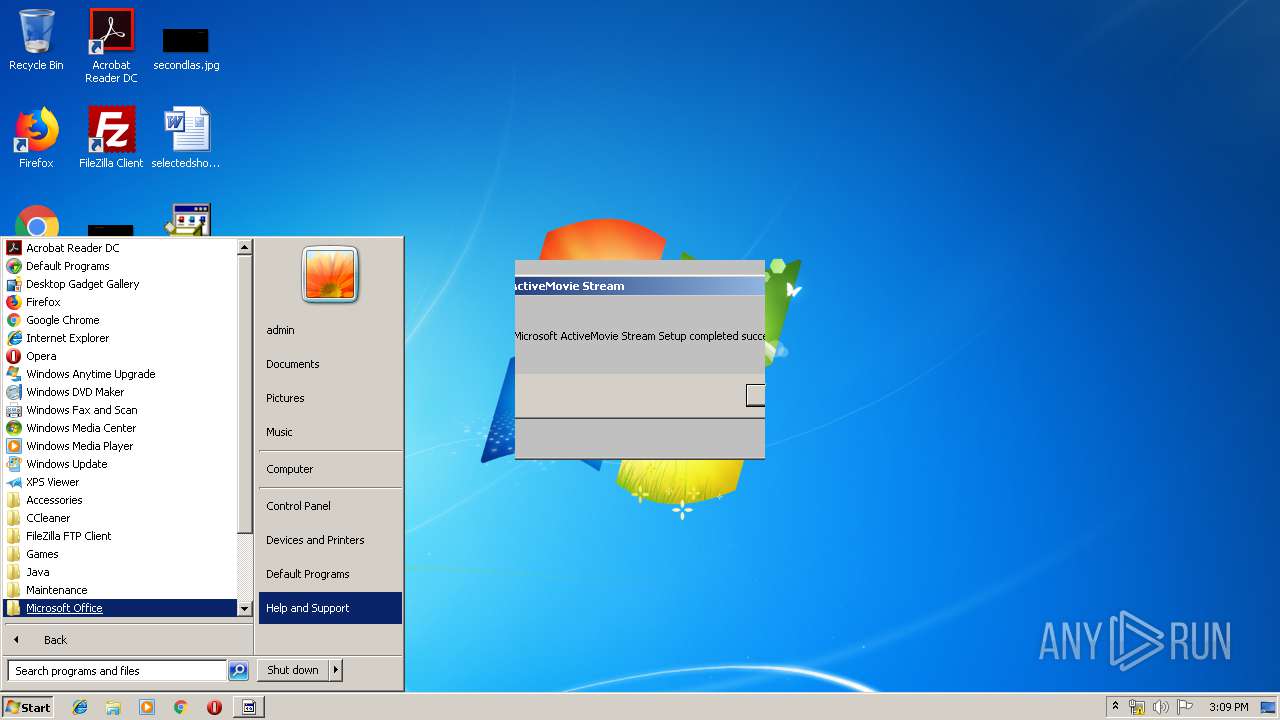
Manual execution by user
- regedit.exe (PID: 2720)
- regedit.exe (PID: 3748)
- wermgr.exe (PID: 3560)
- AMOVIE.EXE (PID: 1940)
- AMOVIE.EXE (PID: 1940)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 MS Cabinet Self-Extractor (WExtract stub) (71.8) |
|---|---|---|
| .exe | | | InstallShield setup (10.1) |
| .exe | | | Win32 Executable MS Visual C++ (generic) (7.3) |
| .exe | | | Win64 Executable (generic) (6.5) |
| .dll | | | Win32 Dynamic Link Library (generic) (1.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1996:08:03 01:30:40+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 3.1 |
| CodeSize: | 50176 |
| InitializedDataSize: | 1349632 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9c90 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.70.0.1153 |
| ProductVersionNumber: | 4.70.0.1153 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Pre-release, Private build |
| FileOS: | Windows 16-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Win32 Cabinet Self-Extractor |
| FileVersion: | 4.70.1153 |
| InternalName: | Wextract |
| LegalCopyright: | Copyright © Microsoft Corp. 1995 |
| OriginalFileName: | WEXTRACT.EXE |
| ProductName: | Microsoft® Plus! for Windows® 95 |
| ProductVersion: | 4.70.1153 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Aug-1996 23:30:40 |
| Detected languages: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | Win32 Cabinet Self-Extractor |
| FileVersion: | 4.70.1153 |
| InternalName: | Wextract |
| LegalCopyright: | Copyright © Microsoft Corp. 1995 |
| OriginalFilename: | WEXTRACT.EXE |
| ProductName: | Microsoft® Plus! for Windows® 95 |
| ProductVersion: | 4.70.1153 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 02-Aug-1996 23:30:40 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000C208 | 0x0000C400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.28141 |
.rdata | 0x0000E000 | 0x000000D5 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.1931 |
.data | 0x0000F000 | 0x00008470 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.59853 |
.idata | 0x00018000 | 0x00000EB6 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.1836 |
.rsrc | 0x00019000 | 0x00146000 | 0x00145A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.98966 |
.reloc | 0x0015F000 | 0x00007000 | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_NOT_CACHED, IMAGE_SCN_MEM_NOT_PAGED, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.21748 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.37346 | 976 | Latin 1 / Western European | English - United States | RT_VERSION |
2 | 3.53793 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
63 | 2.53204 | 146 | Latin 1 / Western European | English - United States | RT_STRING |
66 | 1.7646 | 64 | Latin 1 / Western European | English - United States | RT_STRING |
76 | 3.23884 | 1438 | Latin 1 / Western European | English - United States | RT_STRING |
77 | 3.30764 | 1524 | Latin 1 / Western European | English - United States | RT_STRING |
80 | 3.11064 | 320 | Latin 1 / Western European | English - United States | RT_STRING |
82 | 3.24912 | 792 | Latin 1 / Western European | English - United States | RT_STRING |
83 | 3.30387 | 1086 | Latin 1 / Western European | English - United States | RT_STRING |
85 | 3.10473 | 938 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
USER32.dll |
Total processes
65
Monitored processes
15
Malicious processes
8
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1940 | "C:\Users\admin\Desktop\AMOVIE.EXE" | C:\Users\admin\Desktop\AMOVIE.EXE | explorer.exe | ||||||||||||
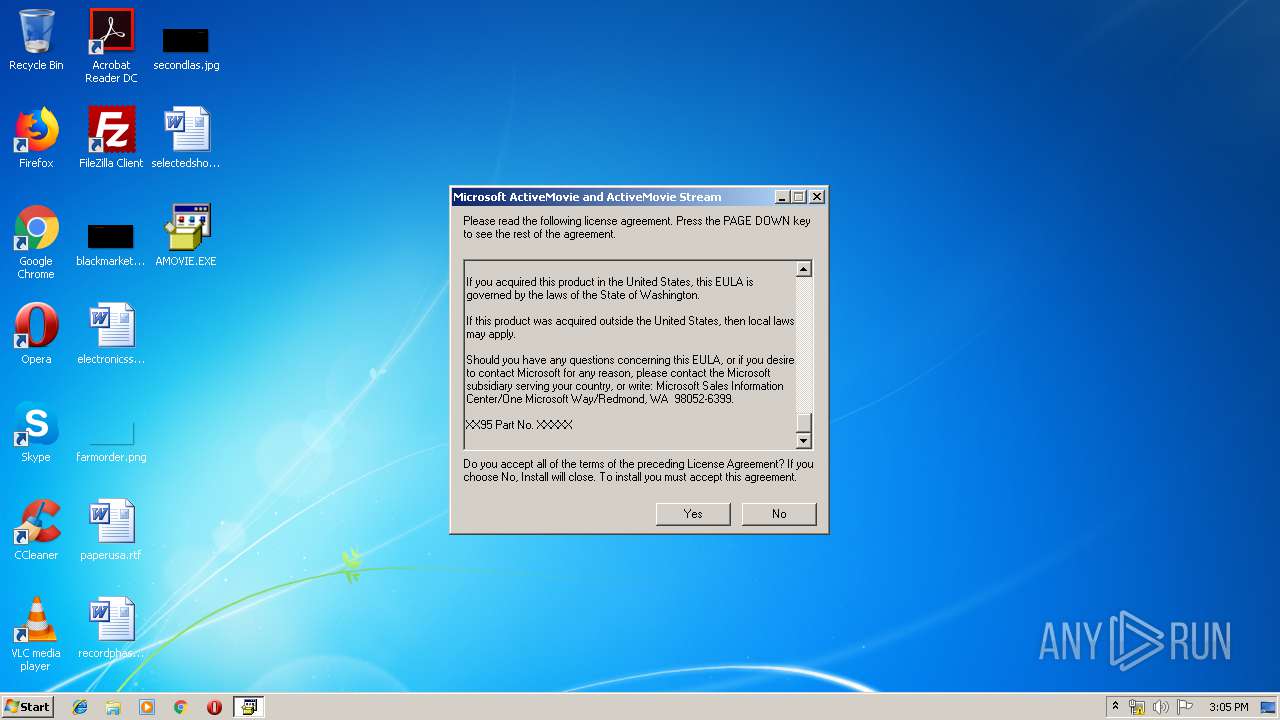
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 4.70.1153 Modules
| |||||||||||||||
| 1940 | "C:\Users\admin\Desktop\AMOVIE.EXE" | C:\Users\admin\Desktop\AMOVIE.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Exit code: 3221226540 Version: 4.70.1153 Modules
| |||||||||||||||
| 2156 | C:\Users\admin\AppData\Local\Temp\MSEB281.tmp\amovie.exe /Q:1 | C:\Users\admin\AppData\Local\Temp\MSEB281.tmp\amovie.exe | AMOVIE.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 4.70.1145 Modules
| |||||||||||||||
| 2200 | C:\Users\admin\AppData\Local\Temp\MSEB3B9.tmp\setupam.exe | C:\Users\admin\AppData\Local\Temp\MSEB3B9.tmp\setupam.exe | amovie.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: ActiveMovie Uninstall Exit code: 0 Version: 4.00.96.0729 Modules
| |||||||||||||||
| 2388 | C:\Users\admin\AppData\Local\Temp\MSE32D0.tmp\AMclient.exe /Q:1 | C:\Users\admin\AppData\Local\Temp\MSE32D0.tmp\AMclient.exe | AMOVIE.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 4.70.1153 Modules
| |||||||||||||||
| 2720 | "C:\Windows\regedit.exe" | C:\Windows\regedit.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Editor Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2972 | C:\Users\admin\AppData\Local\Temp\MSE339B.tmp\setupam.exe | C:\Users\admin\AppData\Local\Temp\MSE339B.tmp\setupam.exe | amovie.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: ActiveMovie Uninstall Exit code: 3489660927 Version: 4.00.96.0729 Modules
| |||||||||||||||
| 2992 | C:\Users\admin\AppData\Local\Temp\MSE92C.tmp\Setup.exe | C:\Users\admin\AppData\Local\Temp\MSE92C.tmp\Setup.exe | — | AMclient.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Cougar SETUP Application Exit code: 3221226540 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3200 | "C:\Users\admin\Desktop\AMOVIE.EXE" | C:\Users\admin\Desktop\AMOVIE.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 4.70.1153 Modules
| |||||||||||||||
| 3204 | C:\Users\admin\AppData\Local\Temp\MSE339B.tmp\setupam.exe | C:\Users\admin\AppData\Local\Temp\MSE339B.tmp\setupam.exe | — | amovie.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: ActiveMovie Uninstall Exit code: 3221226540 Version: 4.00.96.0729 Modules
| |||||||||||||||
Total events
76
Read events
37
Write events
37
Delete events
2
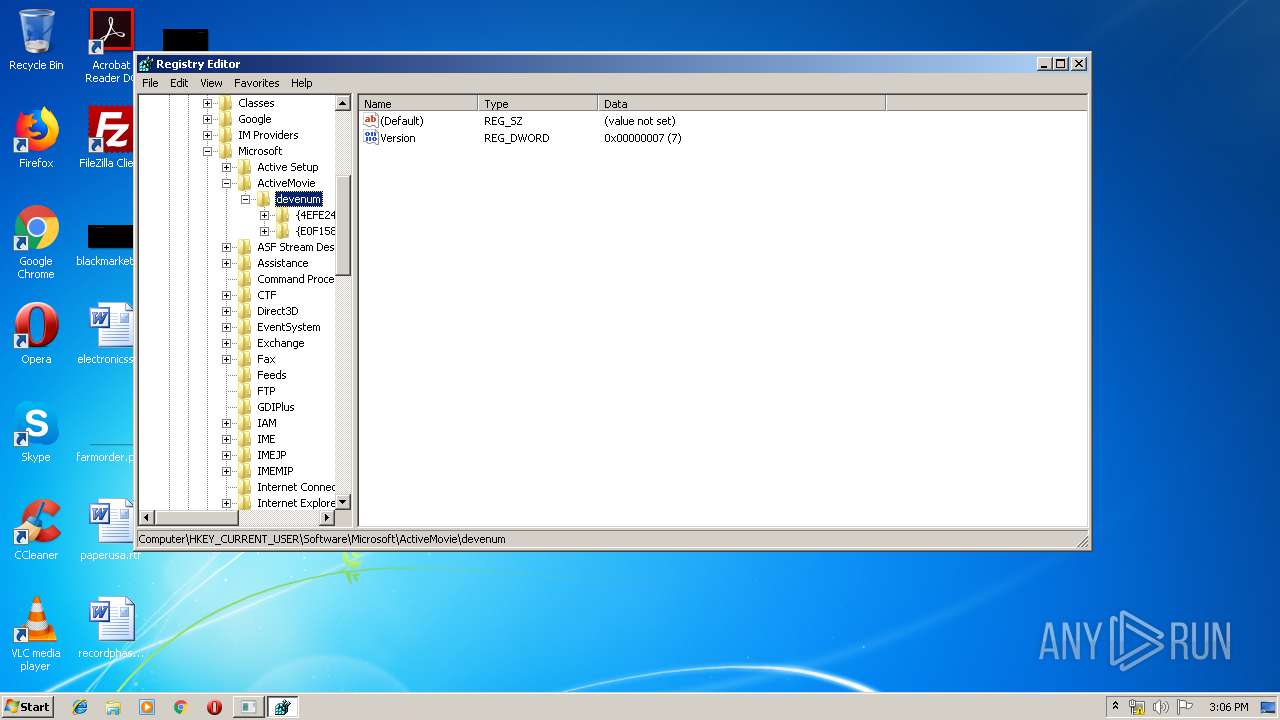
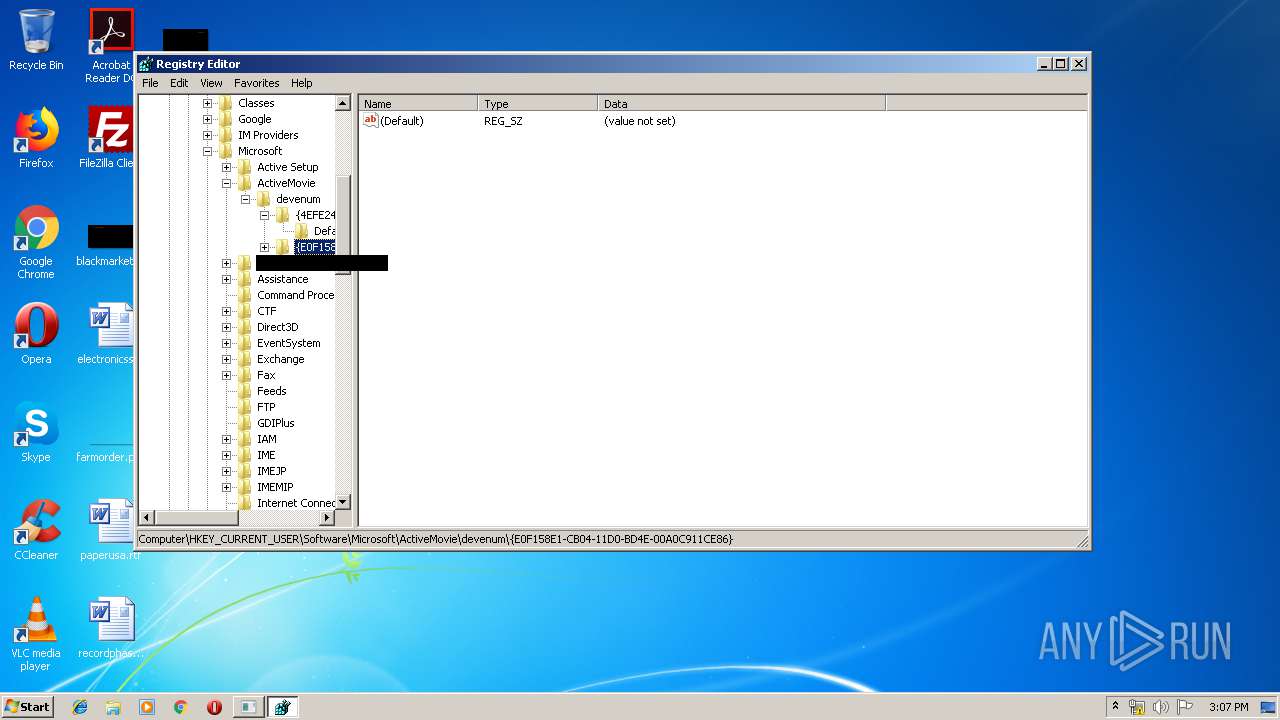
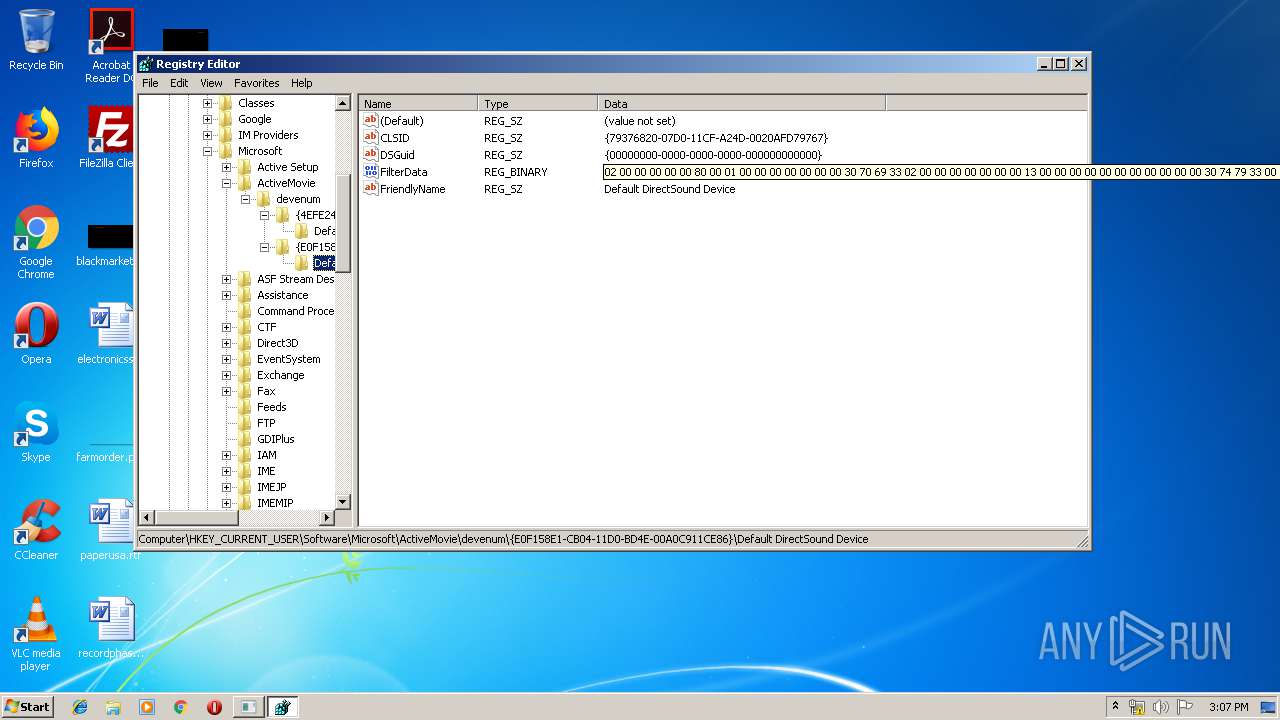
Modification events
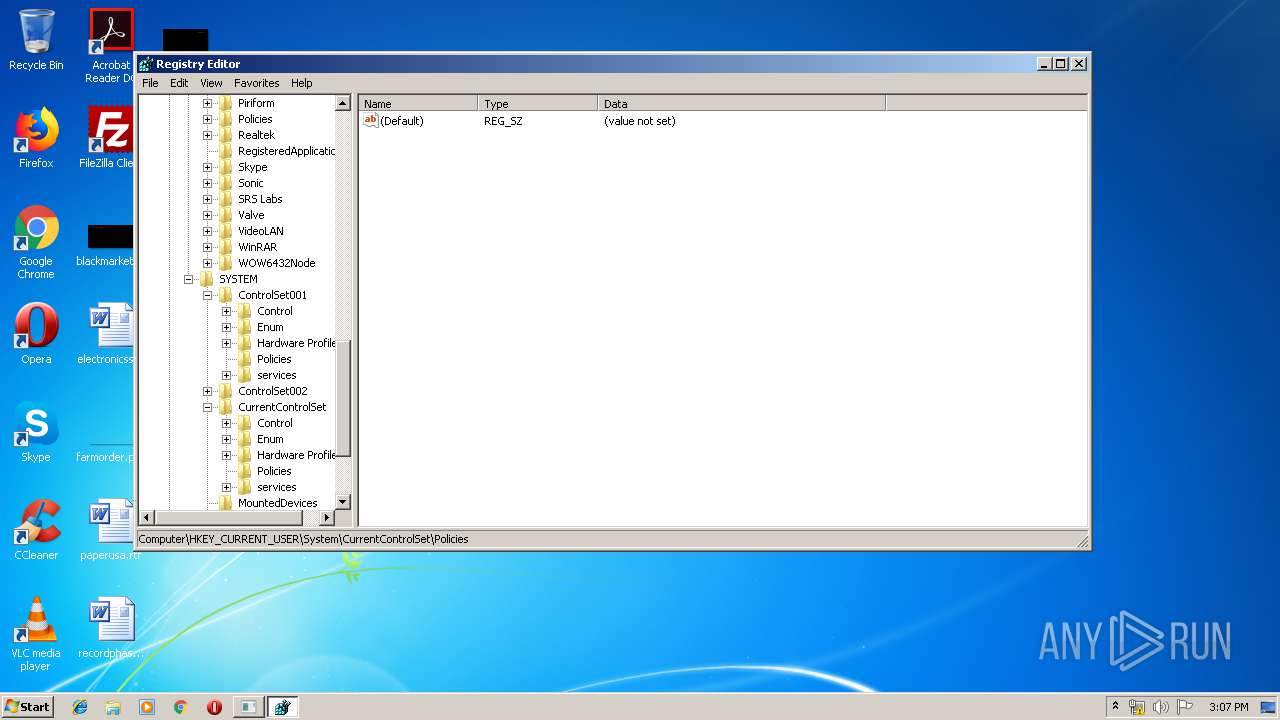
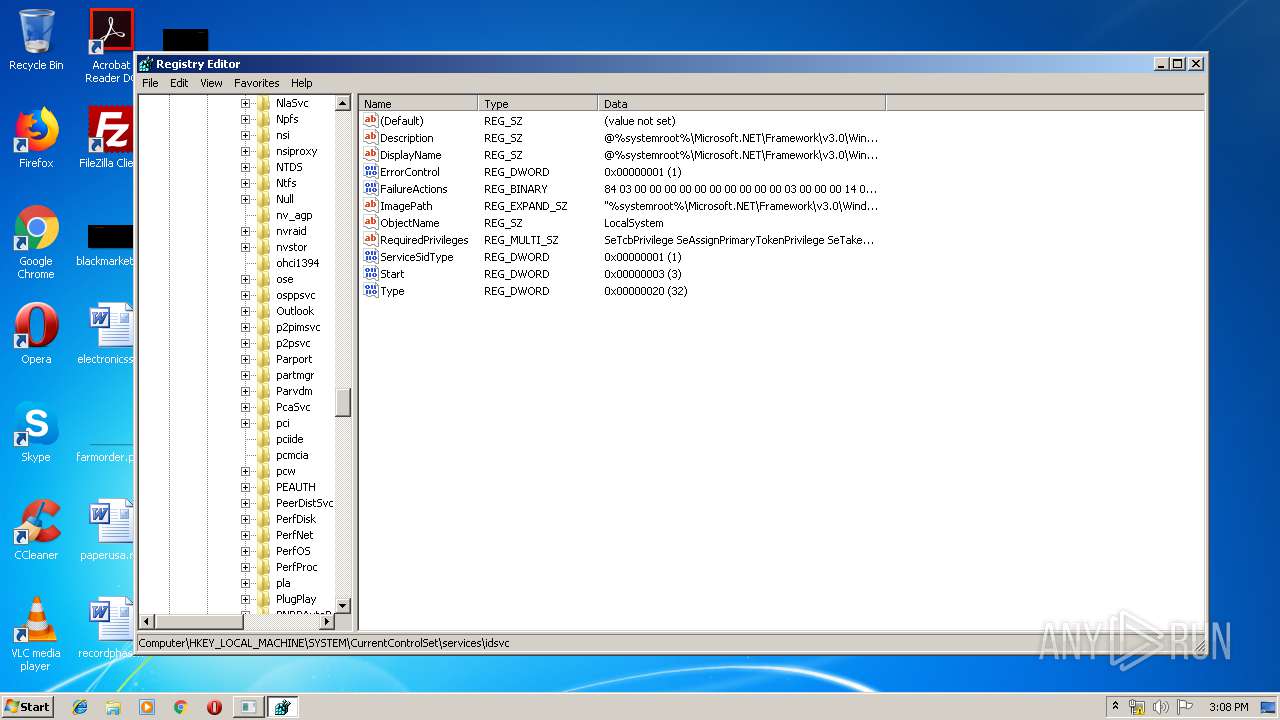
| (PID) Process: | (3200) AMOVIE.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | wextract_cleanup0 |
Value: C:\Users\admin\Desktop\AMOVIE.EXE /D:C:\Users\admin\AppData\Local\Temp\MSE32D0.tmp\ | |||
| (PID) Process: | (3580) amovie.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | wextract_cleanup0 |
Value: C:\Users\admin\AppData\Local\Temp\MSE32D0.tmp\amovie.exe /D:C:\Users\admin\AppData\Local\Temp\MSE339B.tmp\ | |||
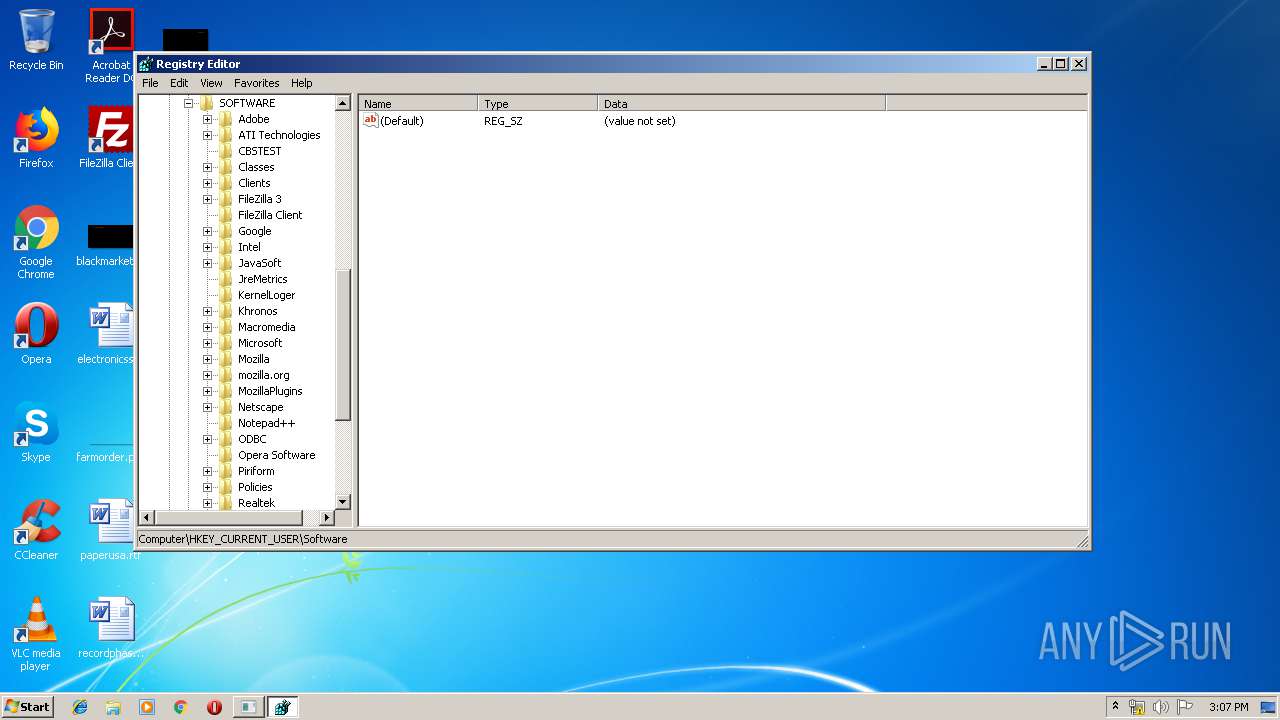
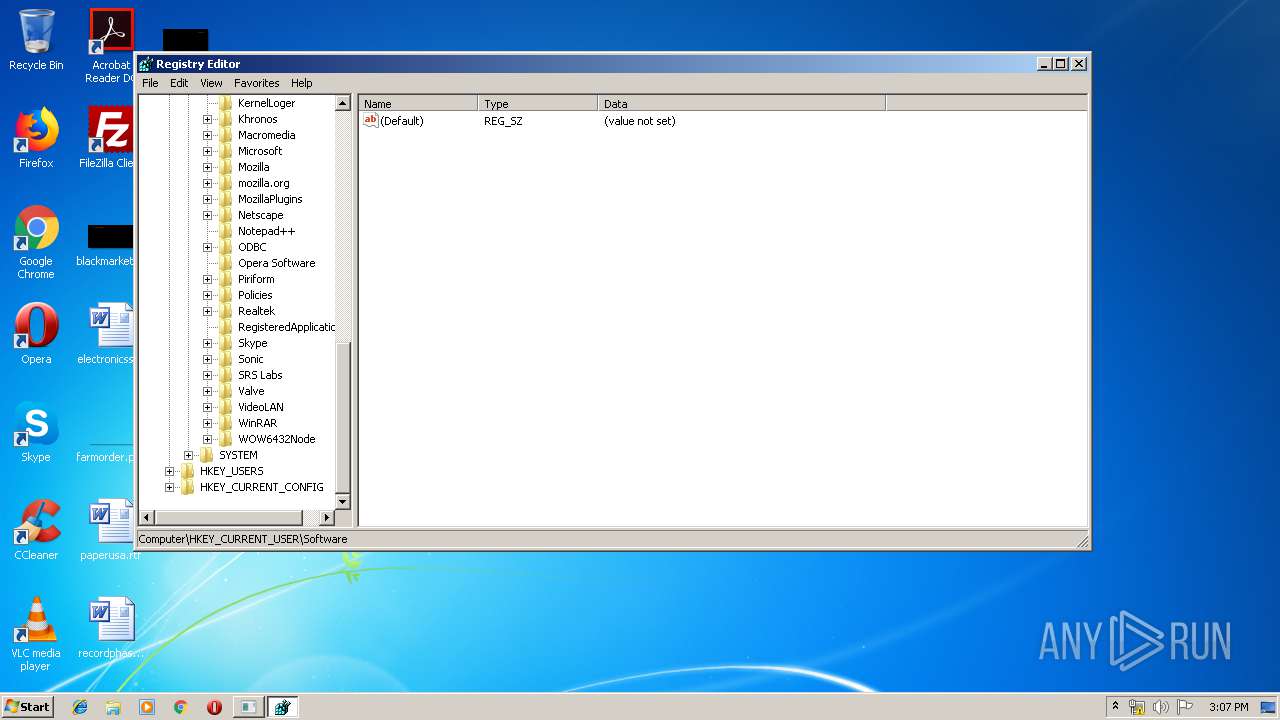
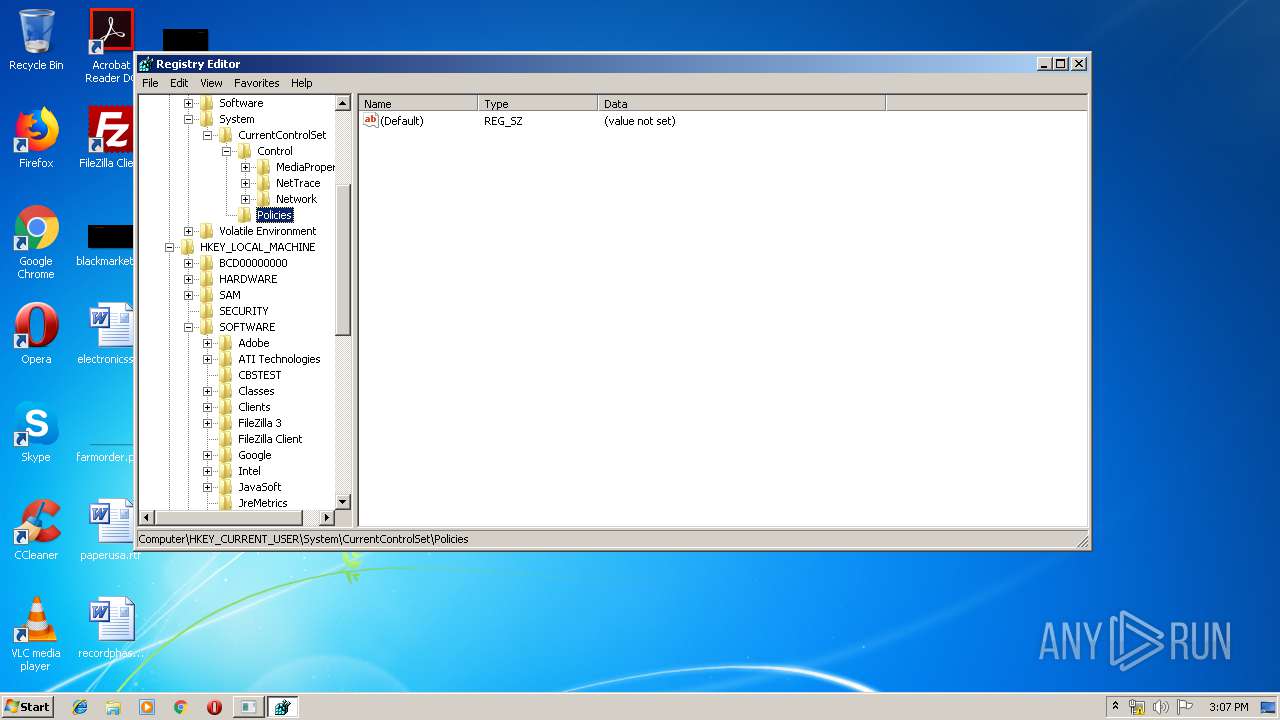
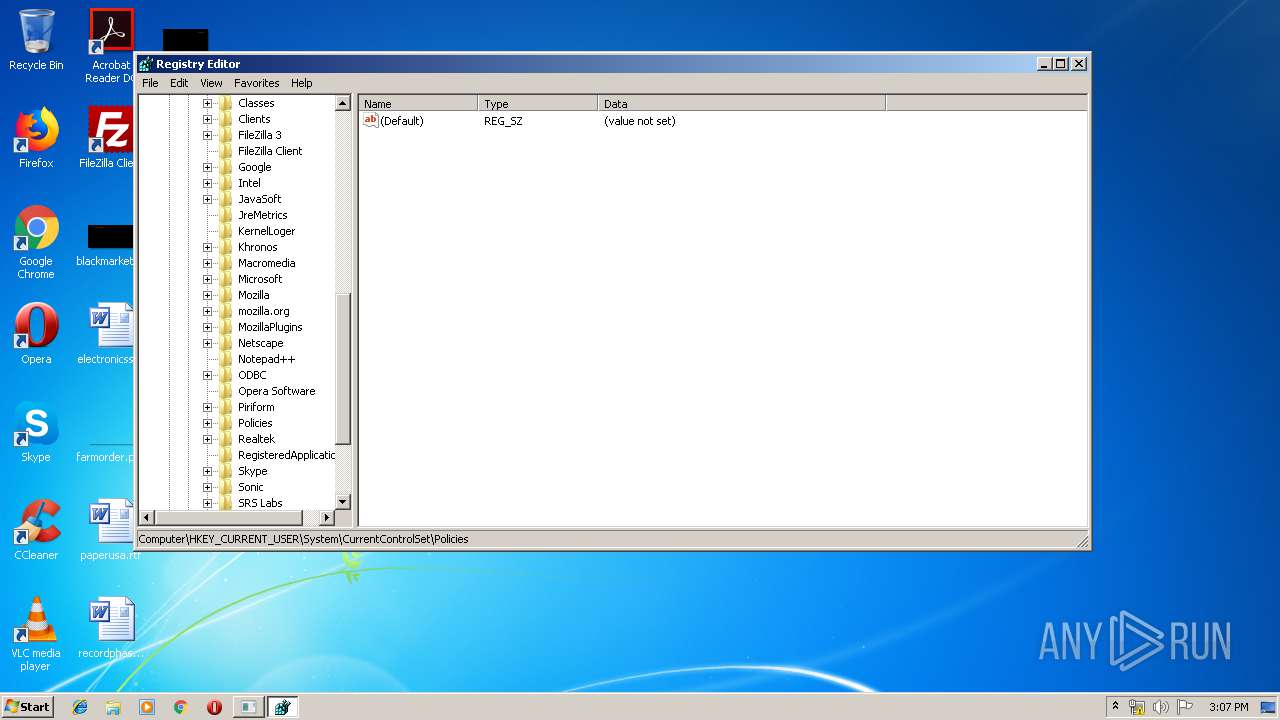
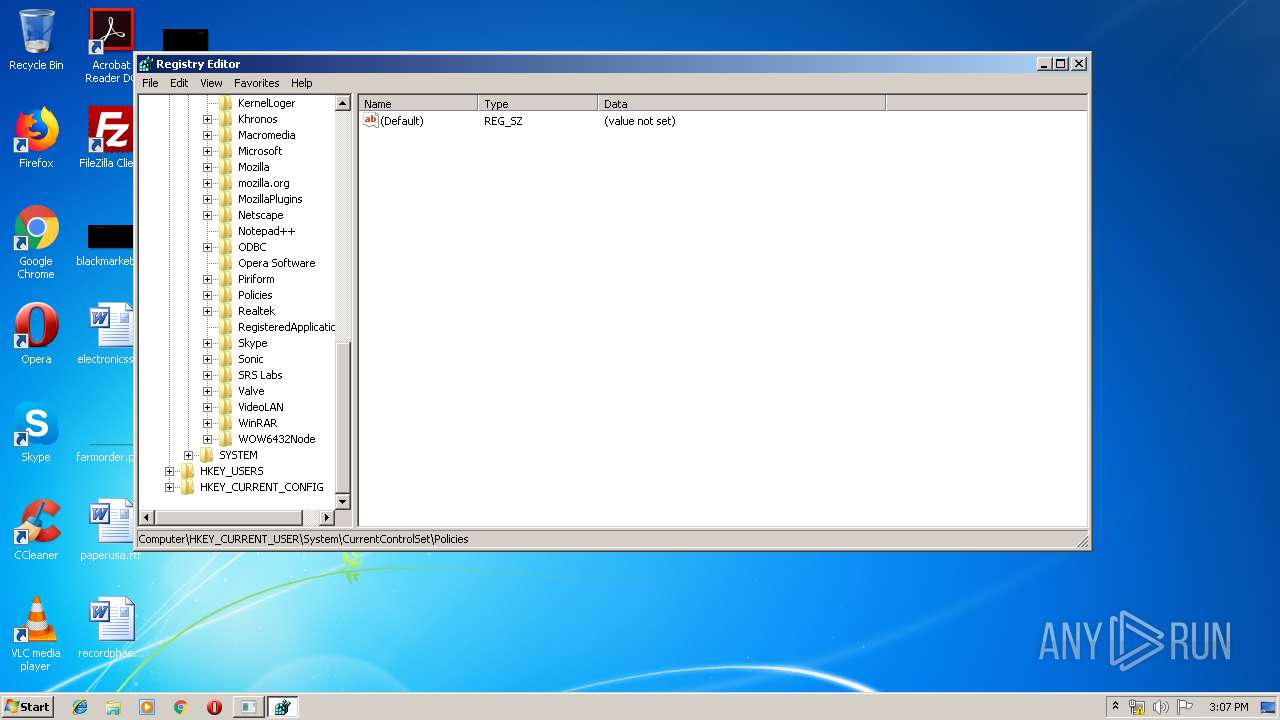
| (PID) Process: | (2720) regedit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Applets\Regedit |
| Operation: | write | Name: | View |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF8500000033000000BA04000090020000D800000078000000780000002001000001000000 | |||
| (PID) Process: | (2720) regedit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Applets\Regedit |
| Operation: | write | Name: | FindFlags |
Value: 14 | |||
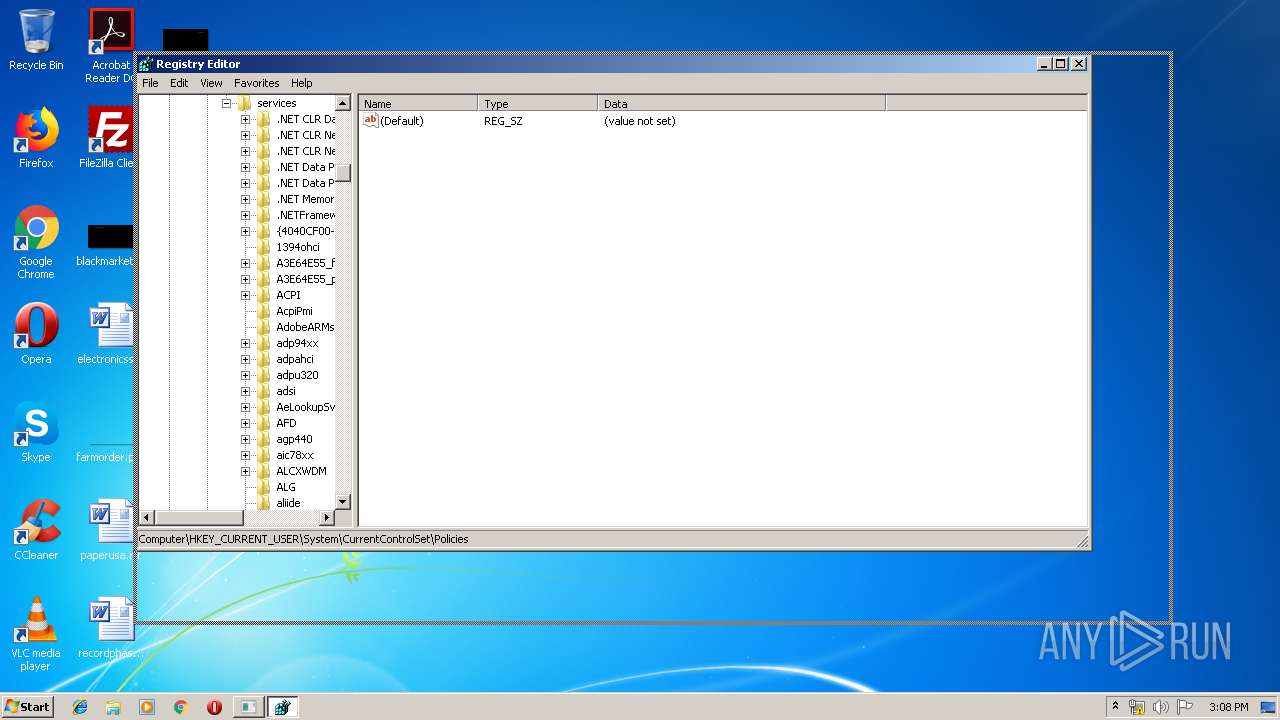
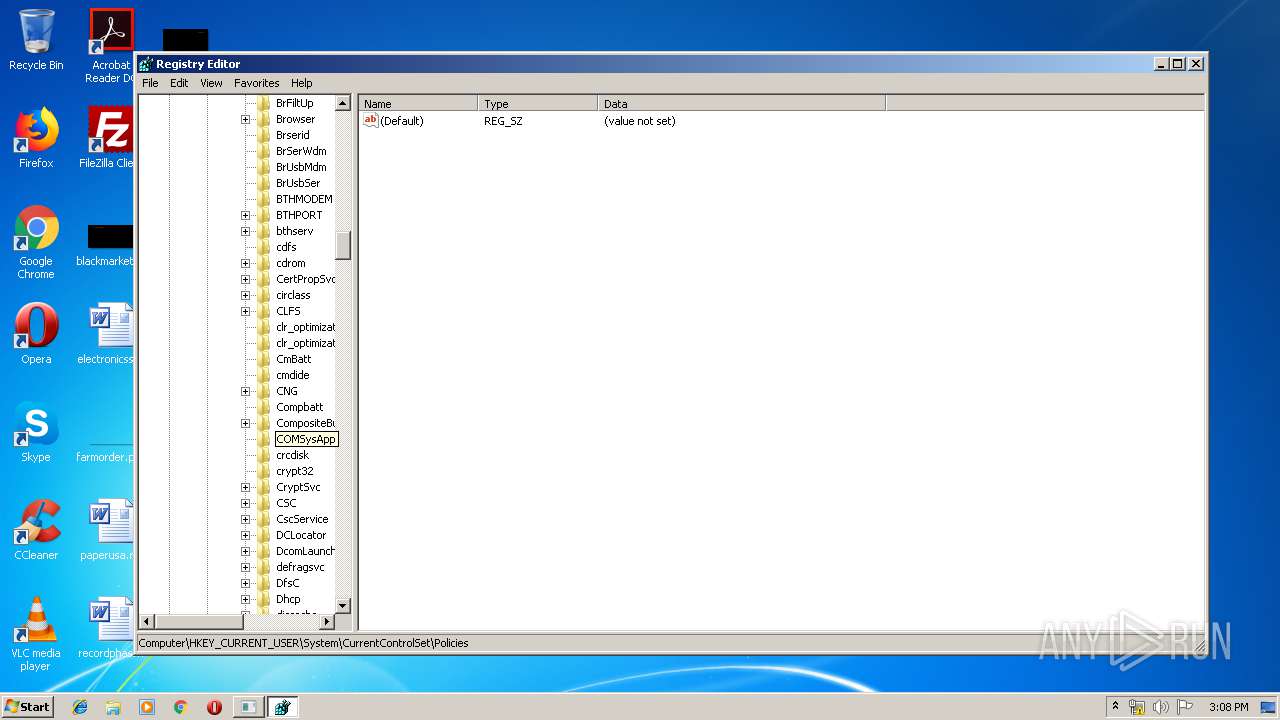
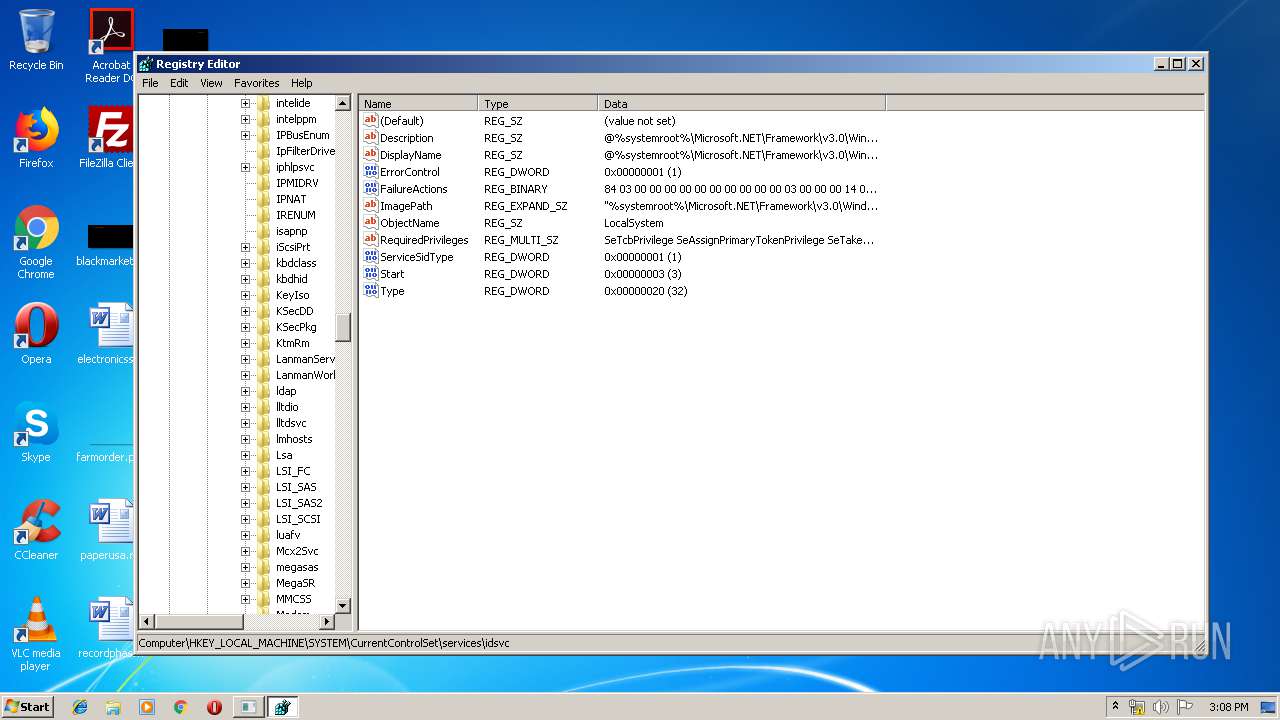
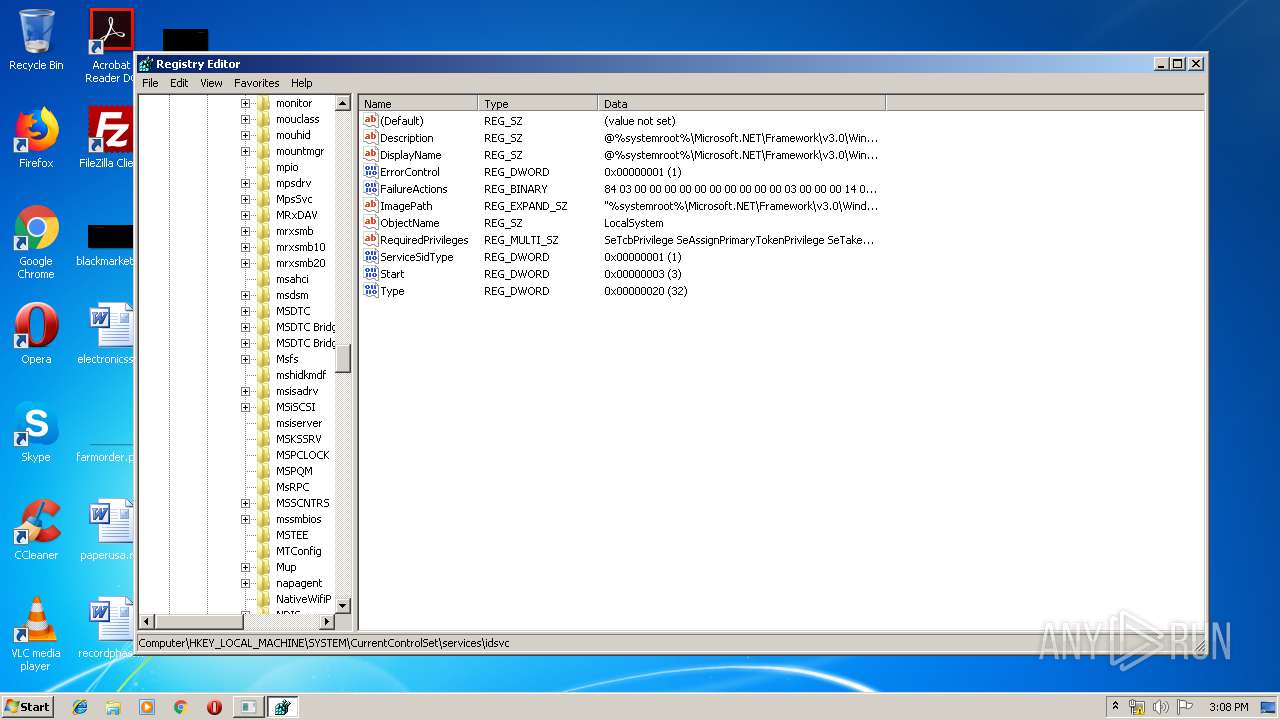
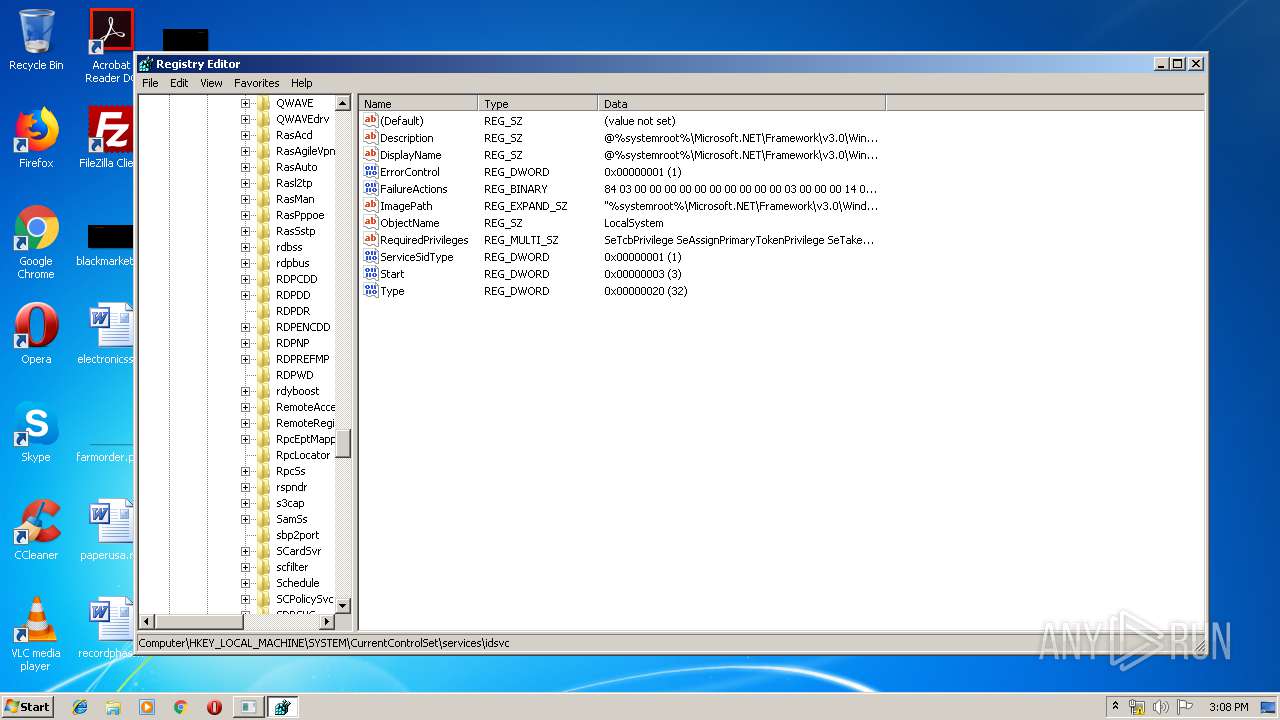
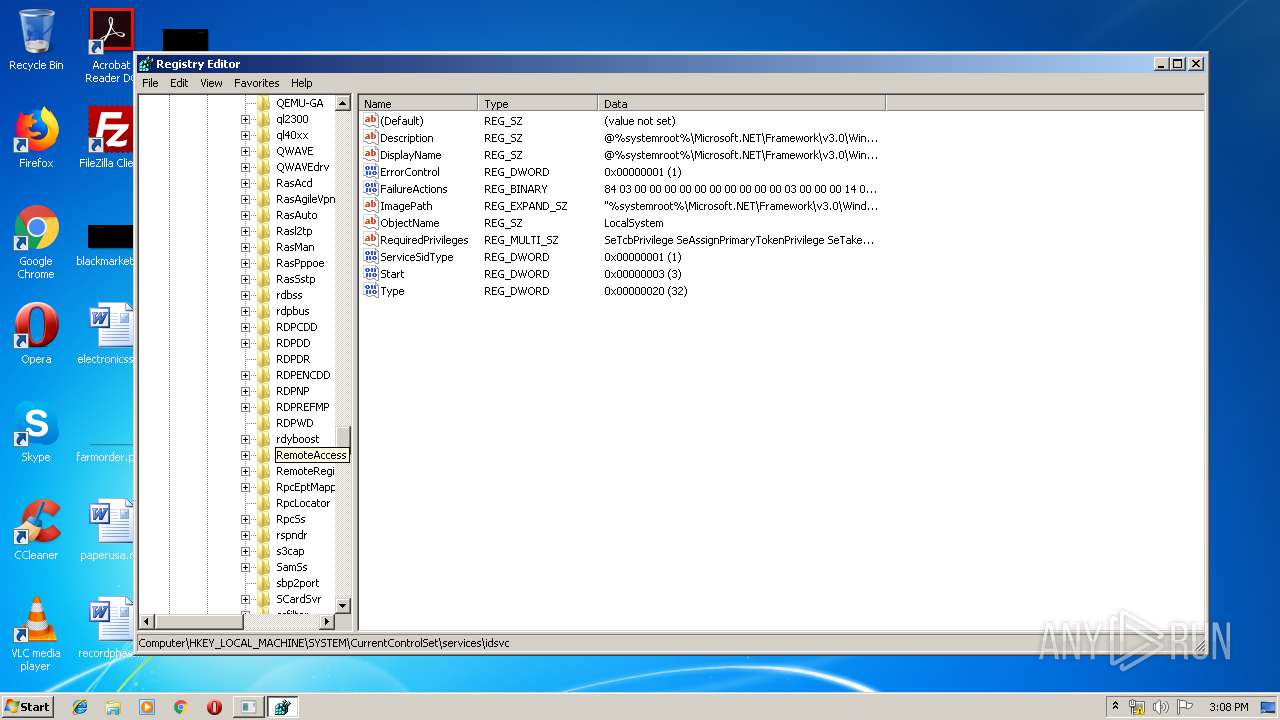
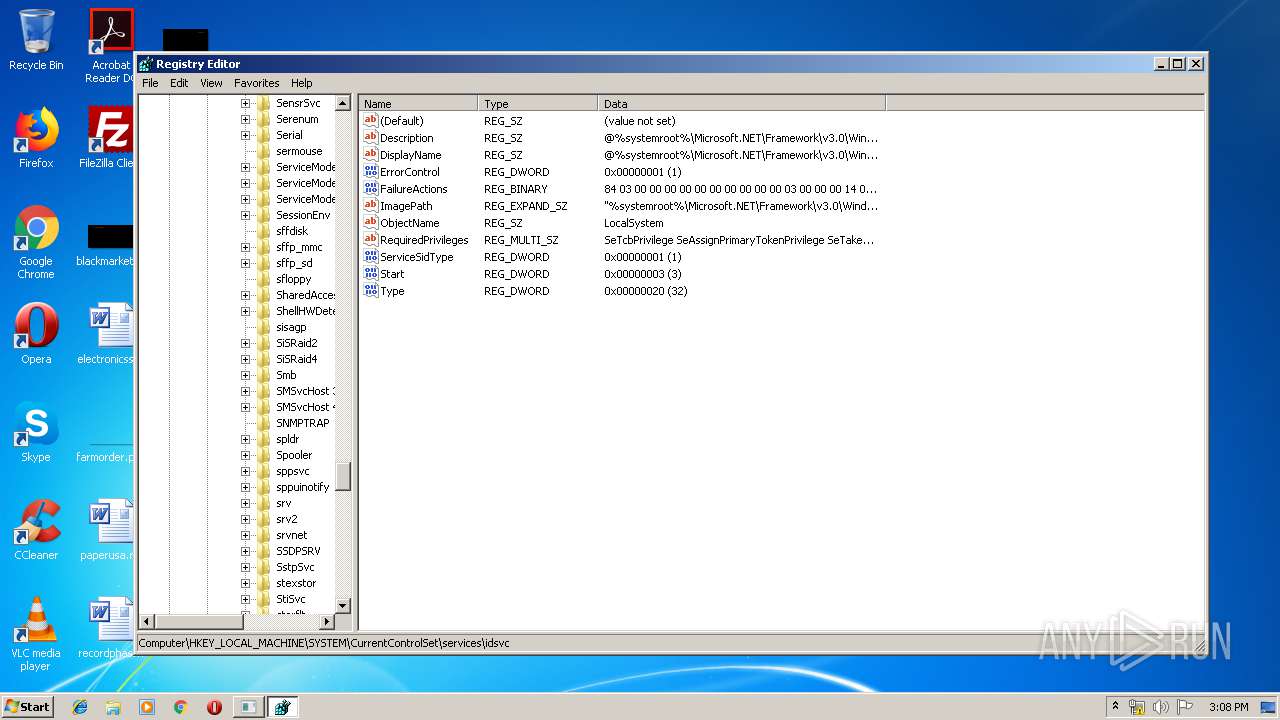
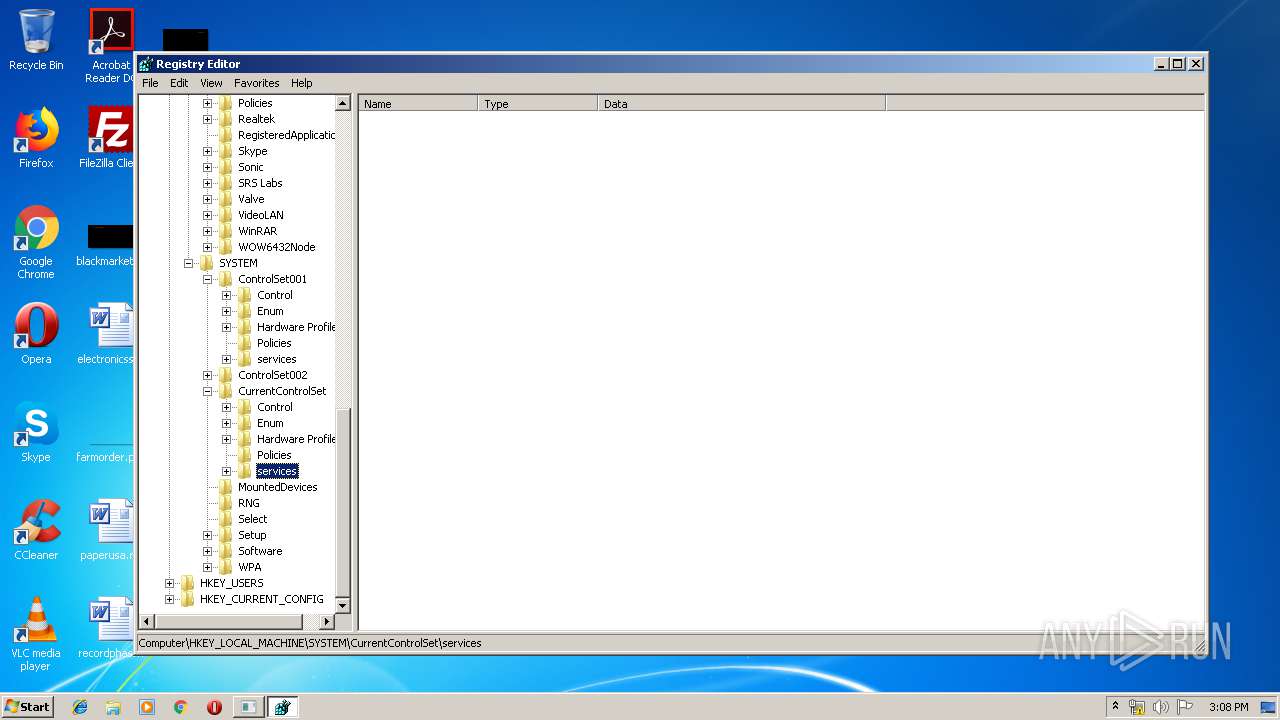
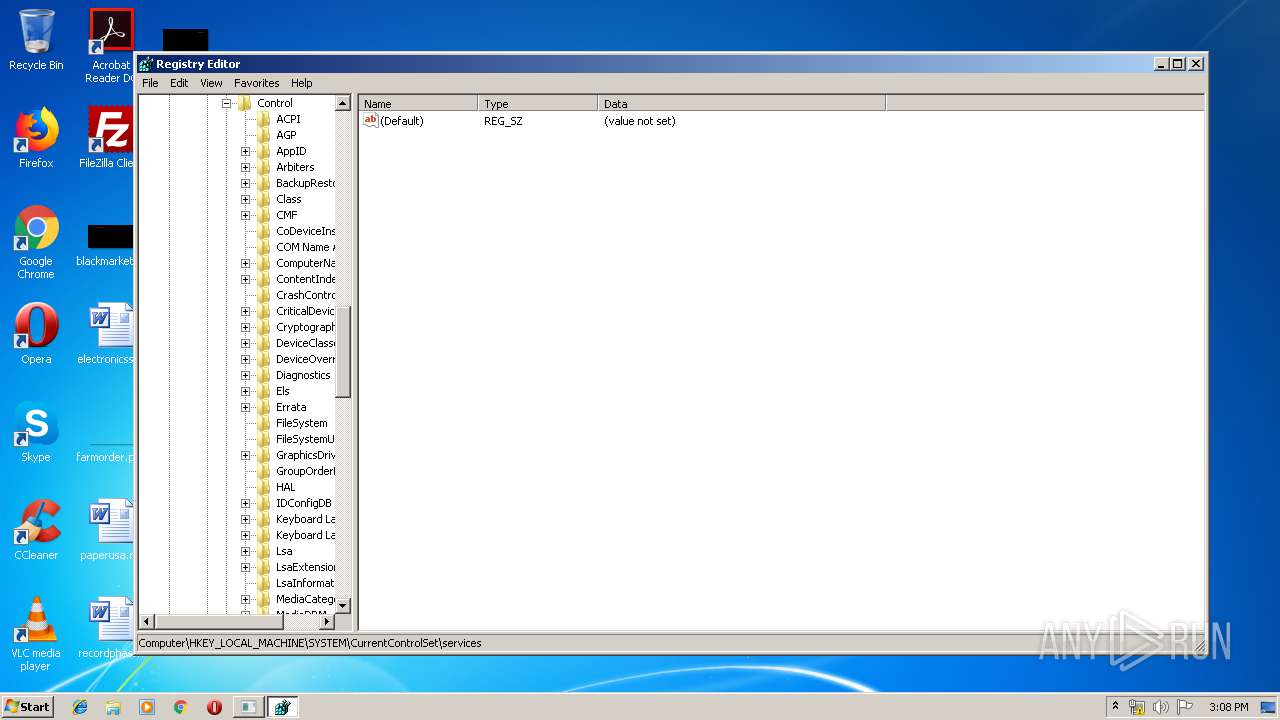
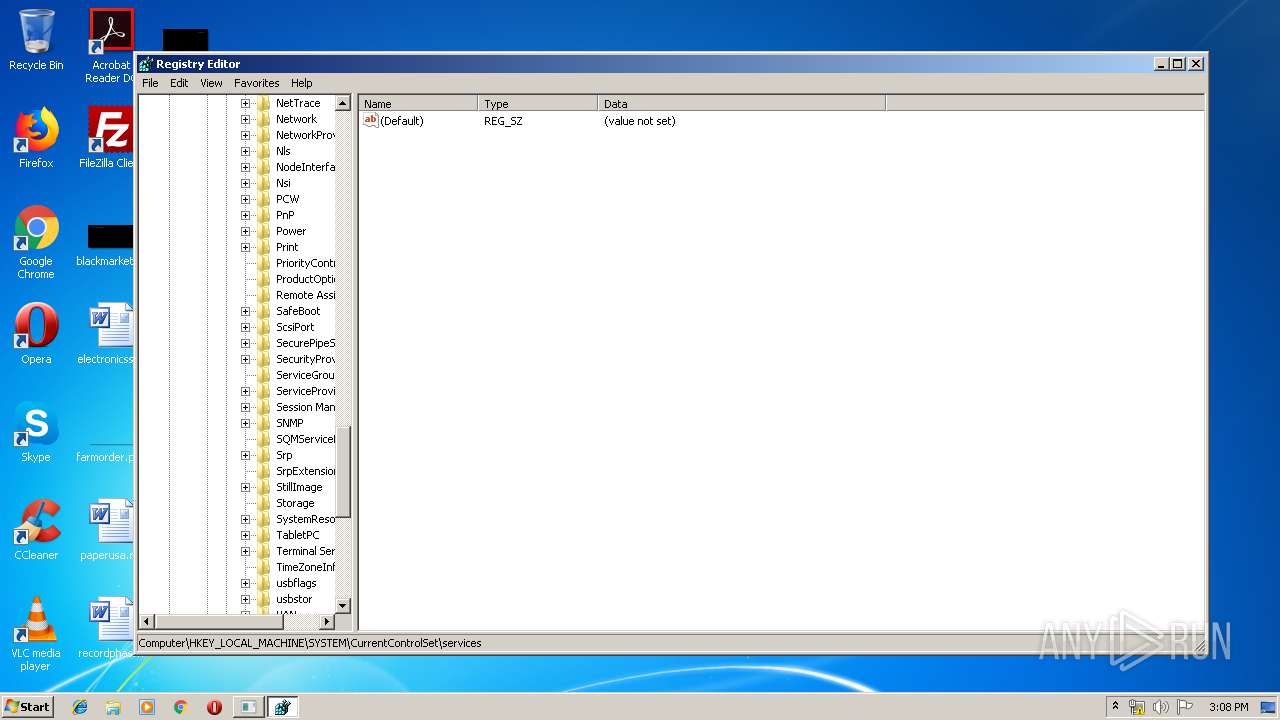
| (PID) Process: | (2720) regedit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Applets\Regedit |
| Operation: | write | Name: | LastKey |
Value: Computer\HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services | |||
| (PID) Process: | (1940) AMOVIE.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | wextract_cleanup0 |
Value: C:\Users\admin\Desktop\AMOVIE.EXE /D:C:\Users\admin\AppData\Local\Temp\MSEB281.tmp\ | |||
| (PID) Process: | (2156) amovie.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | wextract_cleanup1 |
Value: C:\Users\admin\AppData\Local\Temp\MSEB281.tmp\amovie.exe /D:C:\Users\admin\AppData\Local\Temp\MSEB3B9.tmp\ | |||
| (PID) Process: | (3580) amovie.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | delete value | Name: | wextract_cleanup0 |
Value: C:\Users\admin\Desktop\AMOVIE.EXE /D:C:\Users\admin\AppData\Local\Temp\MSEB281.tmp\ | |||
| (PID) Process: | (2388) AMclient.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | wextract_cleanup2 |
Value: C:\Users\admin\AppData\Local\Temp\MSE32D0.tmp\AMclient.exe /D:C:\Users\admin\AppData\Local\Temp\MSE92C.tmp\ | |||
| (PID) Process: | (3200) AMOVIE.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | wextract_cleanup2 |
Value: C:\Users\admin\Desktop\AMOVIE.EXE /D:C:\Users\admin\AppData\Local\Temp\MSE32D0.tmp\ | |||
Executable files
59
Suspicious files
1
Text files
8
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3580 | amovie.exe | C:\Users\admin\AppData\Local\Temp\MSE339B.tmp\quartz.vxd | executable | |
MD5:— | SHA256:— | |||
| 3580 | amovie.exe | C:\Users\admin\AppData\Local\Temp\MSE339B.tmp\mciqtz.drv | executable | |
MD5:— | SHA256:— | |||
| 3580 | amovie.exe | C:\Users\admin\AppData\Local\Temp\MSE339B.tmp\amsetup.dll | executable | |
MD5:— | SHA256:— | |||
| 3200 | AMOVIE.EXE | C:\Users\admin\AppData\Local\Temp\MSE32D0.tmp\AMclient.exe | executable | |
MD5:— | SHA256:— | |||
| 3200 | AMOVIE.EXE | C:\Users\admin\AppData\Local\Temp\MSE32D0.tmp\AMovie.exe | executable | |
MD5:— | SHA256:— | |||
| 3580 | amovie.exe | C:\Users\admin\AppData\Local\Temp\MSE339B.tmp\rundll32.exe | executable | |
MD5:180F801AEB40E227293AD194904AD32B | SHA256:18FA0327A4EE53F5B2B42E14A1F5284D6D299FCA0F1D18EB418DF06A958E5109 | |||
| 3580 | amovie.exe | C:\Users\admin\AppData\Local\Temp\MSE339B.tmp\eula.txt | text | |
MD5:F2F1CA4B7C917DFDAA38EBD620C69132 | SHA256:0F76C20F4CF734356ED96B74F2AEACFB8D9BAFD14F7BB610E90B4372B59A9E73 | |||
| 3580 | amovie.exe | C:\Users\admin\AppData\Local\Temp\MSE339B.tmp\mciqtz32.dll | executable | |
MD5:7ADEE115548FDA6511B94B22DF25169F | SHA256:8921B98B34DFE4385279CEFE9A2C685CDC16C64C0EB4E2EA71C5420354A7275A | |||
| 3580 | amovie.exe | C:\Users\admin\AppData\Local\Temp\MSE339B.tmp\msvcrt40.dll | executable | |
MD5:7B2CB61D924A56654A27C9B5FD747D51 | SHA256:65D5FD6B24C12734897DA9A7A036936CA038E799D87A8012E6DD0D1509445DE0 | |||
| 3580 | amovie.exe | C:\Users\admin\AppData\Local\Temp\MSE339B.tmp\AMovie.ocx | executable | |
MD5:— | SHA256:— | |||
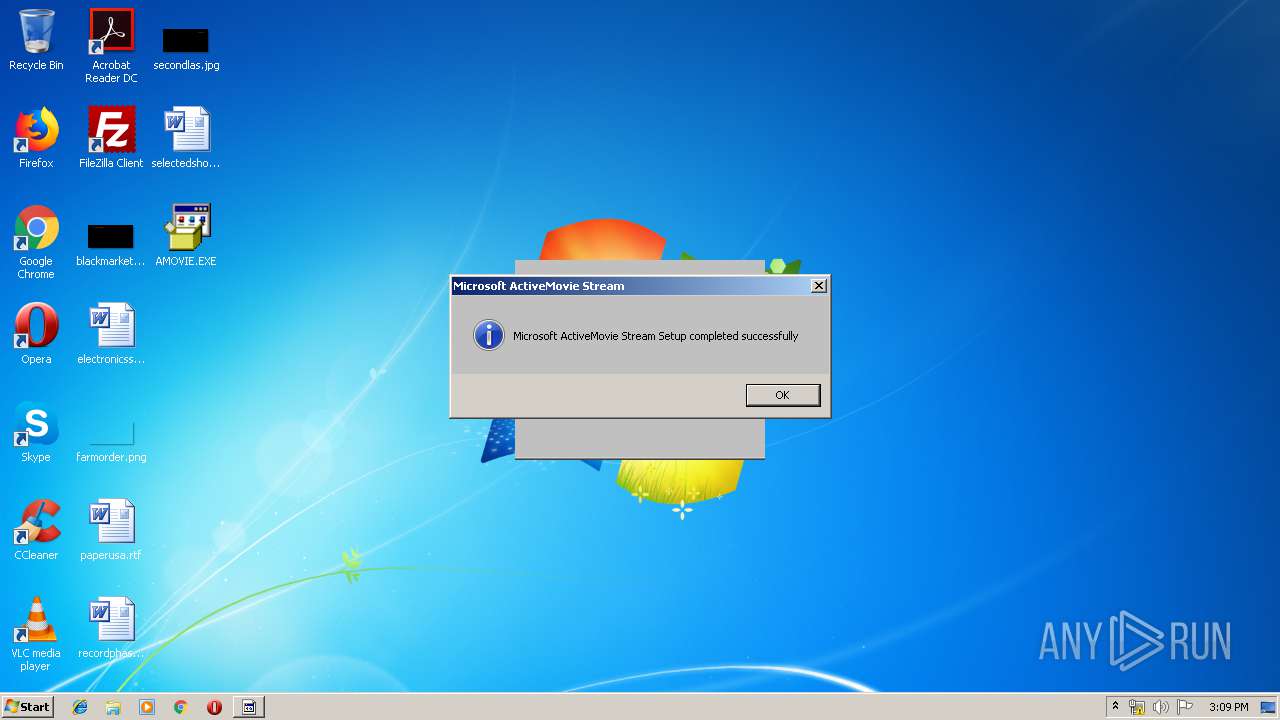
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
AMOVIE.EXE | FTH: (1940): *** Fault tolerant heap shim applied to current process. This is usually due to previous crashes. ***
|
amovie.exe | FTH: (2156): *** Fault tolerant heap shim applied to current process. This is usually due to previous crashes. ***
|
setupam.exe | FTH: (2200): *** Fault tolerant heap shim applied to current process. This is usually due to previous crashes. ***
|