| File name: | b78b162232ed3eb495de8fc553e32cf93098ca9bca17ee791956555b5042b72c |
| Full analysis: | https://app.any.run/tasks/129eada2-4b83-45ad-b255-03a36fed9907 |
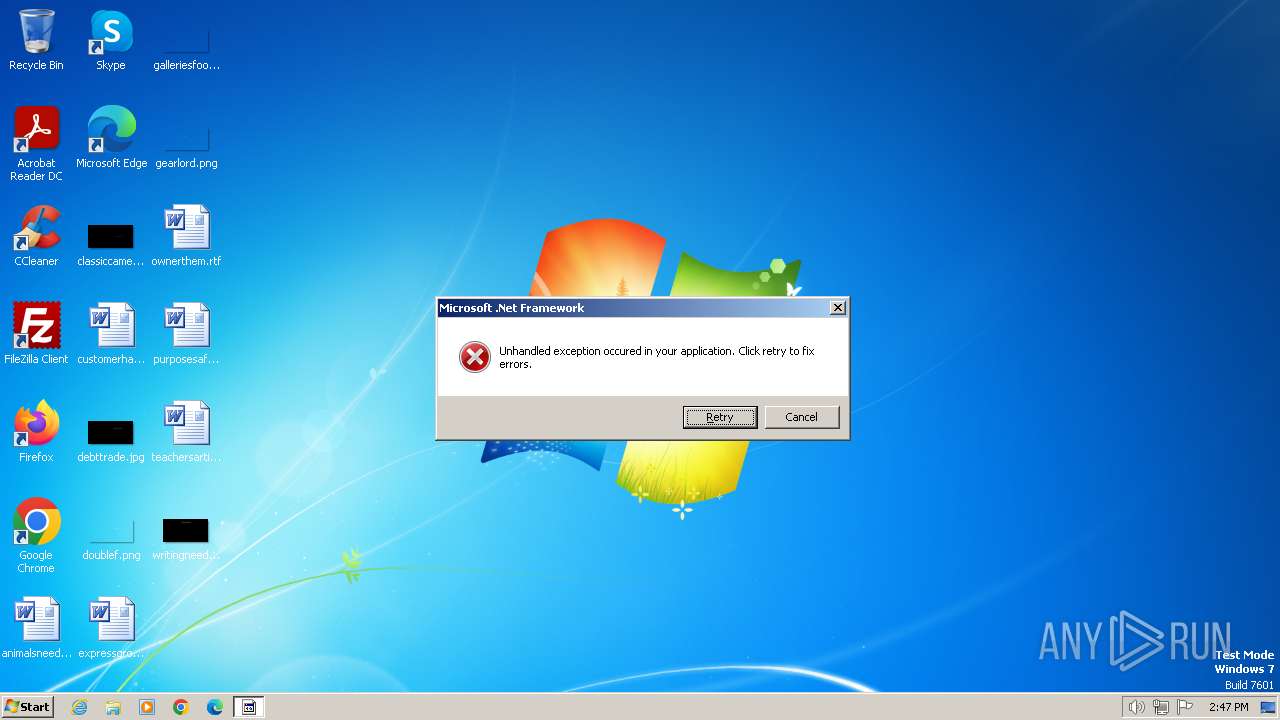
| Verdict: | Malicious activity |
| Analysis date: | December 20, 2023, 14:47:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 7C711EA527DECE150C377BA6EA303173 |
| SHA1: | 3624262B051B9A570C150ADE6826DC6C2DFD5B2C |
| SHA256: | B78B162232ED3EB495DE8FC553E32CF93098CA9BCA17EE791956555B5042B72C |
| SSDEEP: | 6144:o7FLOFmOyoHzl6d6XHr92iScE+vzBMBLM1xK:j1h6dRctz6BCE |
MALICIOUS
Drops the executable file immediately after the start
- b78b162232ed3eb495de8fc553e32cf93098ca9bca17ee791956555b5042b72c.exe (PID: 2040)
SUSPICIOUS
Starts itself from another location
- b78b162232ed3eb495de8fc553e32cf93098ca9bca17ee791956555b5042b72c.exe (PID: 2040)
Reads the Internet Settings
- b78b162232ed3eb495de8fc553e32cf93098ca9bca17ee791956555b5042b72c.exe (PID: 2040)
INFO
Creates files or folders in the user directory
- b78b162232ed3eb495de8fc553e32cf93098ca9bca17ee791956555b5042b72c.exe (PID: 2040)
Checks supported languages
- b78b162232ed3eb495de8fc553e32cf93098ca9bca17ee791956555b5042b72c.exe (PID: 2040)
- br.exe (PID: 1432)
Reads the computer name
- b78b162232ed3eb495de8fc553e32cf93098ca9bca17ee791956555b5042b72c.exe (PID: 2040)
- br.exe (PID: 1432)
Reads the machine GUID from the registry
- br.exe (PID: 1432)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:08:22 16:56:46+02:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 111616 |
| InitializedDataSize: | 53248 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9ae1 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
34
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1432 | "C:\Users\admin\AppData\Roaming\SysDiagnosticsServices\br.exe" | C:\Users\admin\AppData\Roaming\SysDiagnosticsServices\br.exe | b78b162232ed3eb495de8fc553e32cf93098ca9bca17ee791956555b5042b72c.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2040 | "C:\Users\admin\AppData\Local\Temp\b78b162232ed3eb495de8fc553e32cf93098ca9bca17ee791956555b5042b72c.exe" | C:\Users\admin\AppData\Local\Temp\b78b162232ed3eb495de8fc553e32cf93098ca9bca17ee791956555b5042b72c.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
1 720
Read events
1 712
Write events
8
Delete events
0
Modification events
| (PID) Process: | (2040) b78b162232ed3eb495de8fc553e32cf93098ca9bca17ee791956555b5042b72c.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2040) b78b162232ed3eb495de8fc553e32cf93098ca9bca17ee791956555b5042b72c.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2040) b78b162232ed3eb495de8fc553e32cf93098ca9bca17ee791956555b5042b72c.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2040) b78b162232ed3eb495de8fc553e32cf93098ca9bca17ee791956555b5042b72c.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2040 | b78b162232ed3eb495de8fc553e32cf93098ca9bca17ee791956555b5042b72c.exe | C:\Users\admin\AppData\Roaming\SysDiagnosticsServices\br.exe | executable | |
MD5:7C711EA527DECE150C377BA6EA303173 | SHA256:B78B162232ED3EB495DE8FC553E32CF93098CA9BCA17EE791956555B5042B72C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
65
TCP/UDP connections
69
DNS requests
148
Threats
342
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1432 | br.exe | POST | 404 | 49.13.77.253:80 | http://forgeplux.tk/gate.php | DE | xml | 341 b | unknown |
1432 | br.exe | POST | 404 | 49.13.77.253:80 | http://forgeplux.tk/gate.php | DE | xml | 341 b | unknown |
1432 | br.exe | POST | 404 | 49.13.77.253:80 | http://forgeplux.tk/gate.php | DE | xml | 341 b | unknown |
1432 | br.exe | POST | 404 | 49.13.77.253:80 | http://forgeplux.tk/gate.php | DE | xml | 341 b | unknown |
1432 | br.exe | POST | 404 | 49.13.77.253:80 | http://forgeplux.tk/gate.php | DE | xml | 341 b | unknown |
1432 | br.exe | POST | 404 | 49.13.77.253:80 | http://forgeplux.tk/gate.php | DE | xml | 341 b | unknown |
1432 | br.exe | POST | 404 | 49.13.77.253:80 | http://forgeplux.tk/gate.php | DE | xml | 341 b | unknown |
1432 | br.exe | POST | 404 | 49.13.77.253:80 | http://forgeplux.tk/gate.php | DE | xml | 341 b | unknown |
1432 | br.exe | POST | 404 | 49.13.77.253:80 | http://forgeplux.tk/gate.php | DE | xml | 341 b | unknown |
1432 | br.exe | POST | 404 | 49.13.77.253:80 | http://forgeplux.tk/gate.php | DE | xml | 341 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1432 | br.exe | 49.13.77.253:80 | forgeplux.tk | Hetzner Online GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
forgeplux.tk |
| unknown |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a .tk domain - Likely Hostile |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a .tk domain - Likely Hostile |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a .tk domain - Likely Hostile |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a .tk domain - Likely Hostile |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a .tk domain - Likely Hostile |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a .tk domain - Likely Hostile |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a .tk domain - Likely Hostile |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a .tk domain - Likely Hostile |
1432 | br.exe | A Network Trojan was detected | ET MALWARE Trojan Generic - POST To gate.php with no referer |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a .tk domain - Likely Hostile |