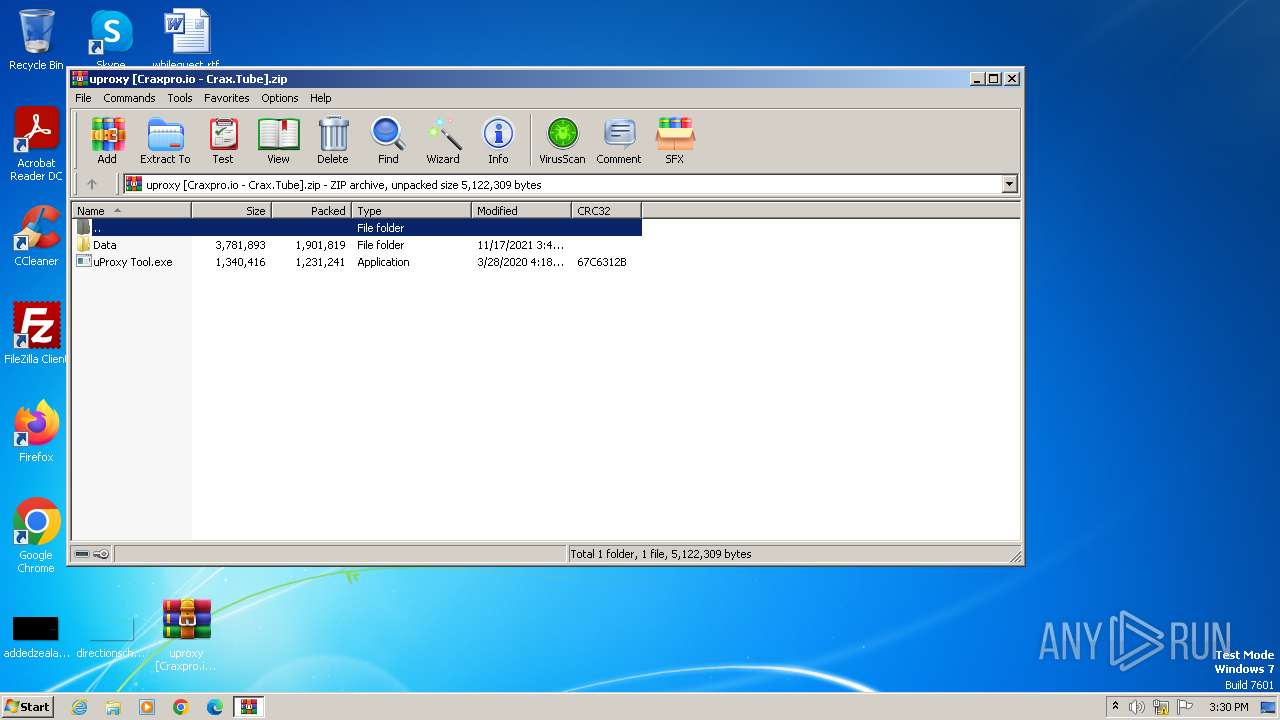
| File name: | uproxy [Craxpro.io - Crax.Tube].zip |
| Full analysis: | https://app.any.run/tasks/3b15b731-8d40-4ec9-84f3-49f23ce2a086 |
| Verdict: | Malicious activity |
| Analysis date: | November 12, 2023, 15:29:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | A9D84DA9B06FBCE05C32BD18FA98382B |
| SHA1: | 4BD809FBCBDC5DCDFF851D4371C6FDEA26B4C9DA |
| SHA256: | B777526250F7D616B6738229A5AFE52E0F61837B4F8632F8BFA145F492FAA0E6 |
| SSDEEP: | 98304:p3mCVAPL/ojOpSHP6oLB14AJCJI08Mx9yEi4HARFW62WzFSA7u50ASre8eIoC02x:6s7KQHClM |
MALICIOUS
No malicious indicators.SUSPICIOUS
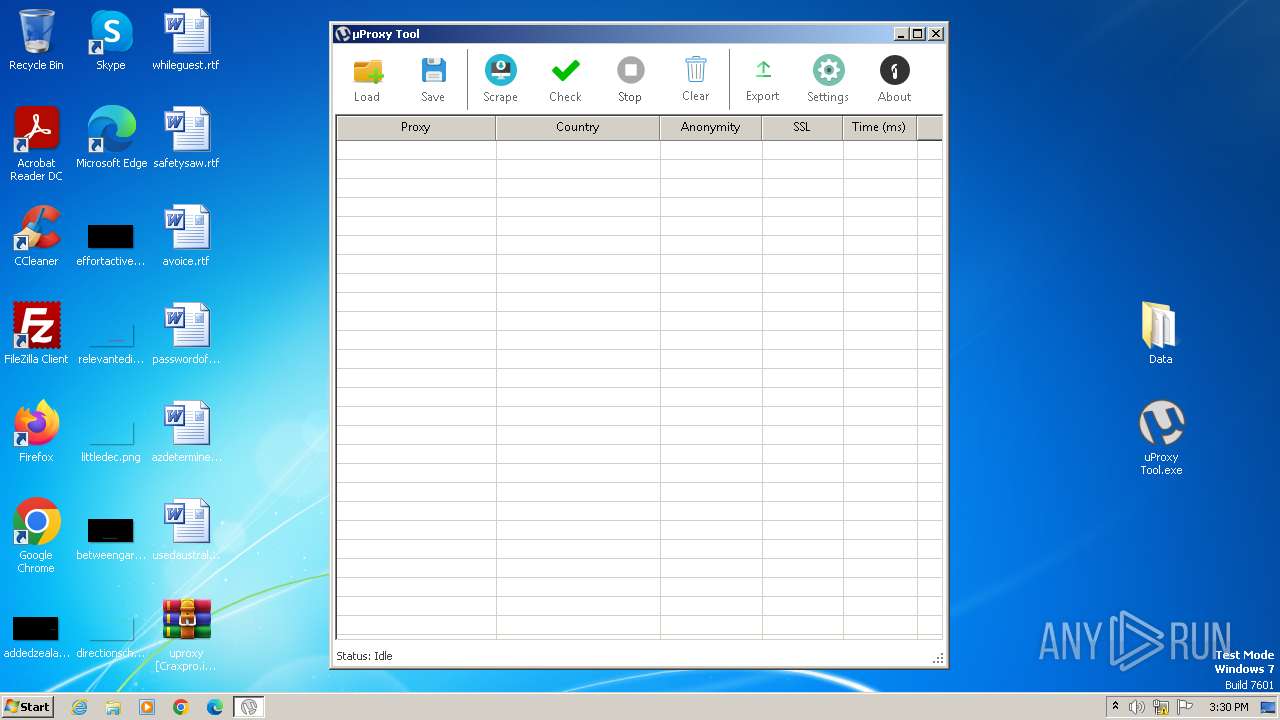
Reads settings of System Certificates
- uProxy Tool.exe (PID: 3228)
Reads the Internet Settings
- uProxy Tool.exe (PID: 3228)
INFO
Manual execution by a user
- uProxy Tool.exe (PID: 3228)
- wmpnscfg.exe (PID: 3580)
Reads the machine GUID from the registry
- uProxy Tool.exe (PID: 3228)
- wmpnscfg.exe (PID: 3580)
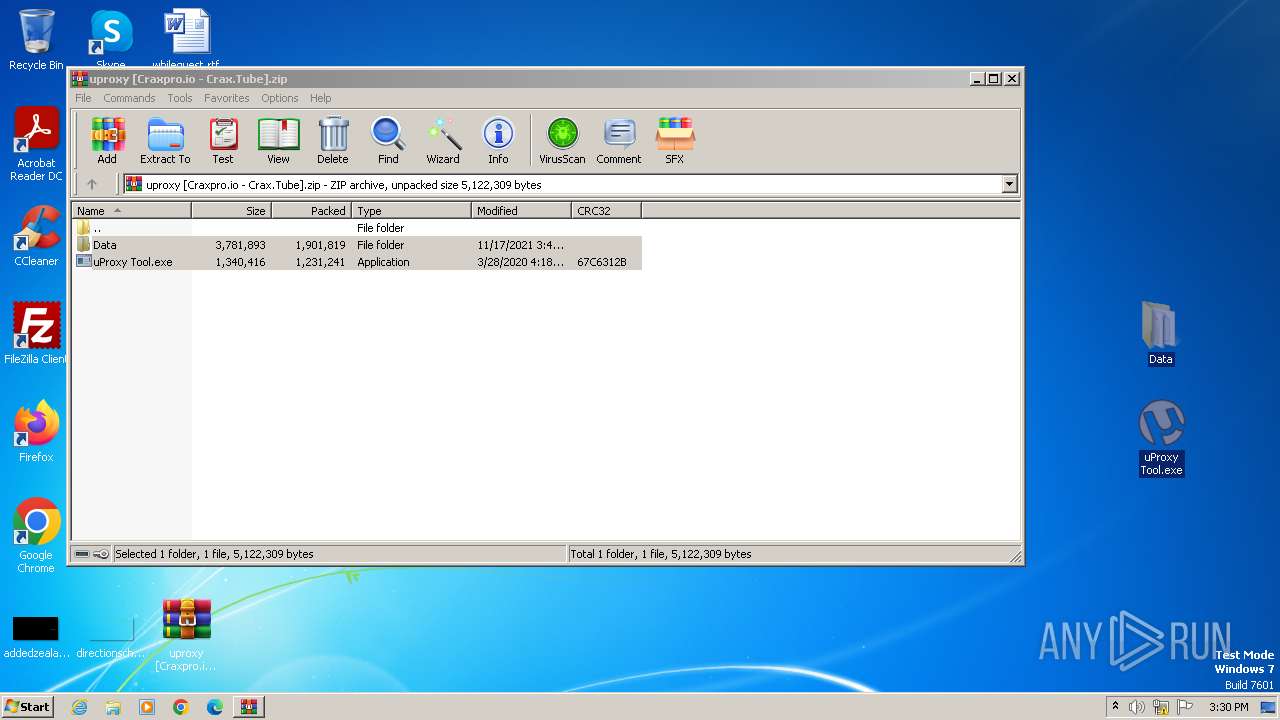
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3440)
Checks supported languages
- uProxy Tool.exe (PID: 3228)
- wmpnscfg.exe (PID: 3580)
Reads the computer name
- uProxy Tool.exe (PID: 3228)
- wmpnscfg.exe (PID: 3580)
Reads Environment values
- uProxy Tool.exe (PID: 3228)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2021:11:17 15:47:54 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Data/ |
Total processes
37
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3228 | "C:\Users\admin\Desktop\uProxy Tool.exe" | C:\Users\admin\Desktop\uProxy Tool.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: uProxy Tool Exit code: 0 Version: 2.1 Modules
| |||||||||||||||
| 3440 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\uproxy [Craxpro.io - Crax.Tube].zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3580 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 783
Read events
3 741
Write events
39
Delete events
3
Modification events
| (PID) Process: | (3440) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17A\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3440) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (3440) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3440) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3440) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3440) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3440) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3440) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3440) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (3440) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\Desktop | |||
Executable files
1
Suspicious files
1
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3440 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3440.49283\Data\Source.txt | text | |
MD5:414DC3B8FFA0DBCE4DE75BC2ACB2CE70 | SHA256:09AB8EF07742A1E6643D2E581ABCF99A8E529716A879DF4CB5085D5FA1879D39 | |||
| 3440 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3440.49283\Data\Country.mmdb | binary | |
MD5:917FA457274651B5F23DFECBC9286A6D | SHA256:588FF7098075F0B3823300C2DE9B5C670552E7E43A0D9BBD23B2B46BA0F85A49 | |||
| 3440 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3440.49283\uProxy Tool.exe | executable | |
MD5:D381C9079AF8DC8E11F08FC1C4BB5D21 | SHA256:8F781DAD2CD705D6BA672CF6B50CBEB8029157F130AE5096FA0756484AC6722D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3228 | uProxy Tool.exe | 185.199.108.133:443 | raw.githubusercontent.com | FASTLY | US | unknown |
868 | svchost.exe | 23.35.228.137:80 | armmf.adobe.com | AKAMAI-AS | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
raw.githubusercontent.com |
| shared |
armmf.adobe.com |
| whitelisted |