| File name: | 0c97d7f6a1835a3fe64c1c625ea109ed.doc |
| Full analysis: | https://app.any.run/tasks/6e6c18c8-1eea-4aec-8a2e-69111c0ebff1 |
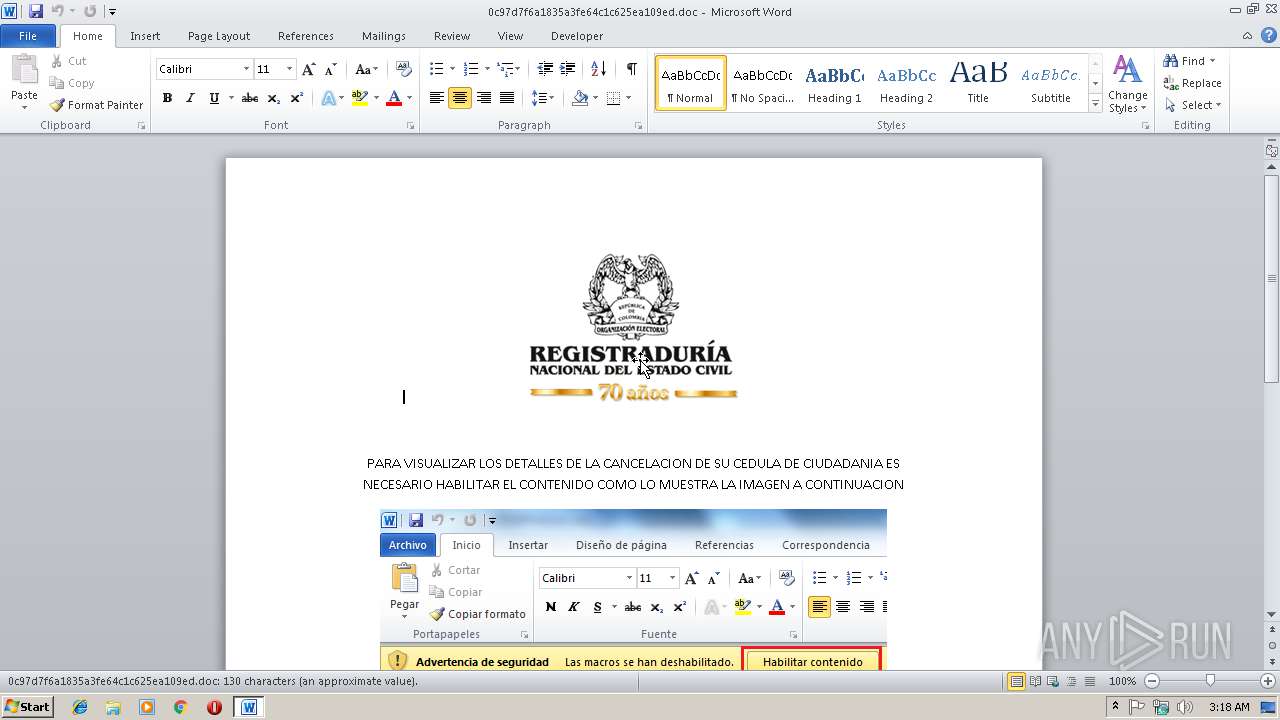
| Verdict: | Malicious activity |
| Analysis date: | February 19, 2019, 03:18:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | MIME entity, ISO-8859 text, with CRLF line terminators |
| MD5: | 0C97D7F6A1835A3FE64C1C625EA109ED |
| SHA1: | C76584AF95F3CDADD17E5A5C08F03EFC10E8E2F6 |
| SHA256: | B763D7F59864AACC9B4AF6C74FEE1CAAFD950B66DB667082E84A787C32B983DE |
| SSDEEP: | 3072:DRwXYUcUK1TQZXgSUmVKngNG4wvjbQTrhhC+6B+V974:DR+NcUK1TmXCcKnR4wvQTFA+Vy |
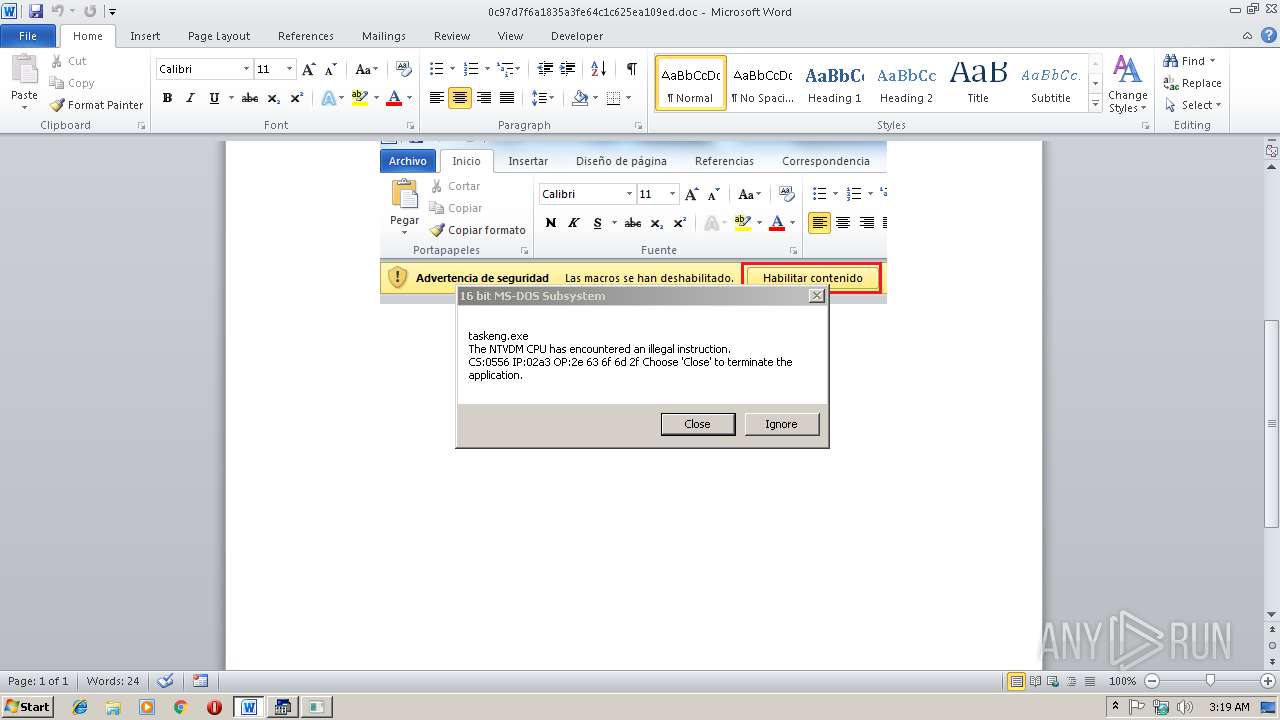
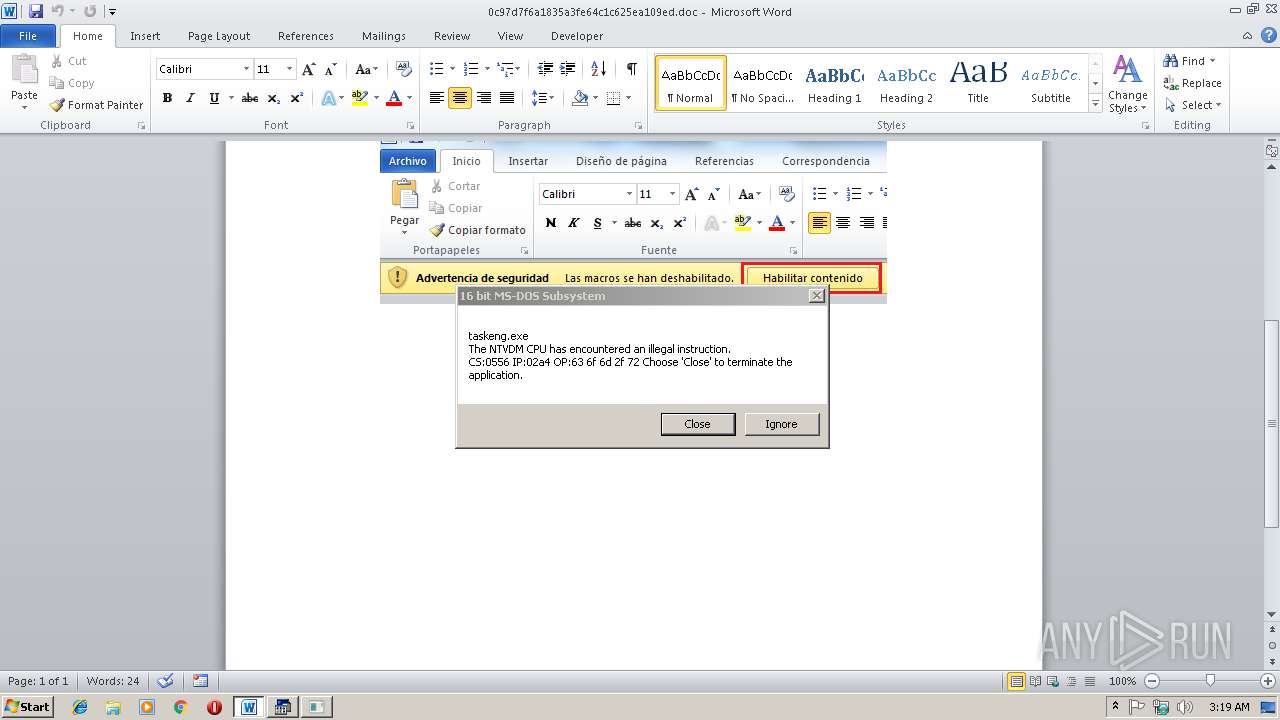
MALICIOUS
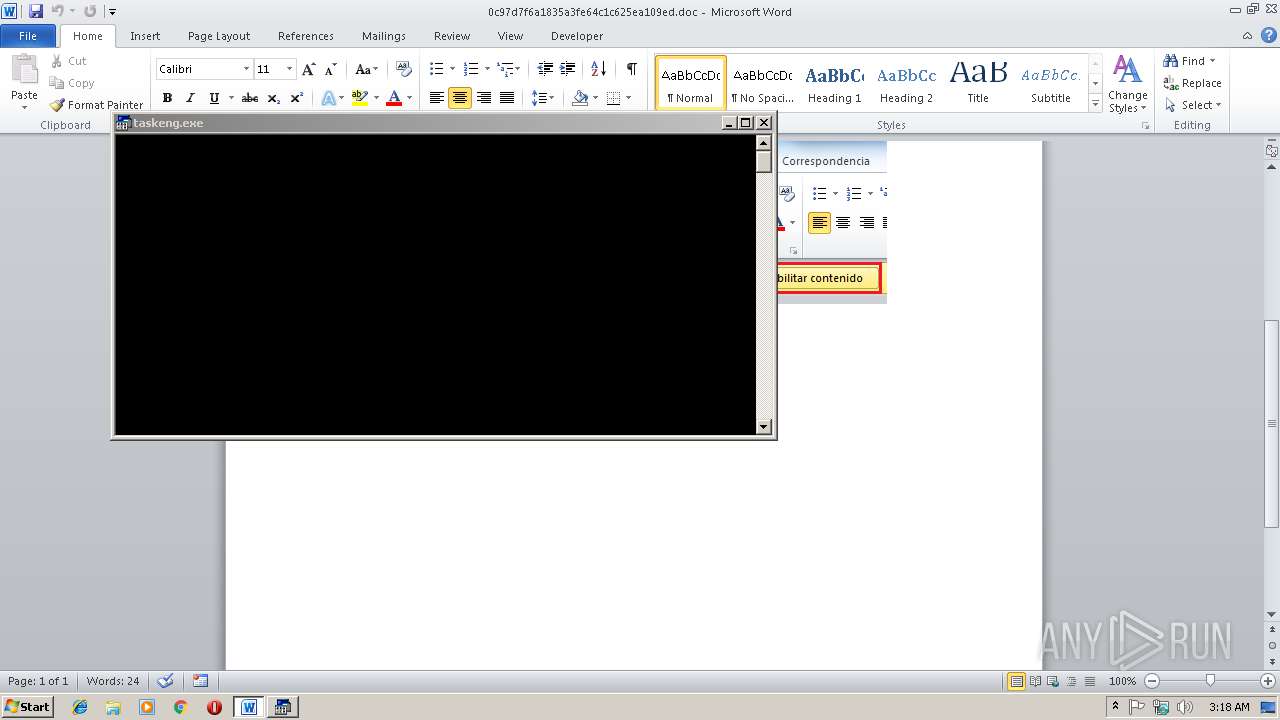
Loads the Task Scheduler COM API
- WINWORD.EXE (PID: 2964)
SUSPICIOUS
Reads Internet Cache Settings
- WINWORD.EXE (PID: 2964)
Unusual connect from Microsoft Office
- WINWORD.EXE (PID: 2964)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2964)
Creates files in the user directory
- WINWORD.EXE (PID: 2964)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .mht/mhtml | | | MIME HTML archive format (var 2) (100) |
|---|
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
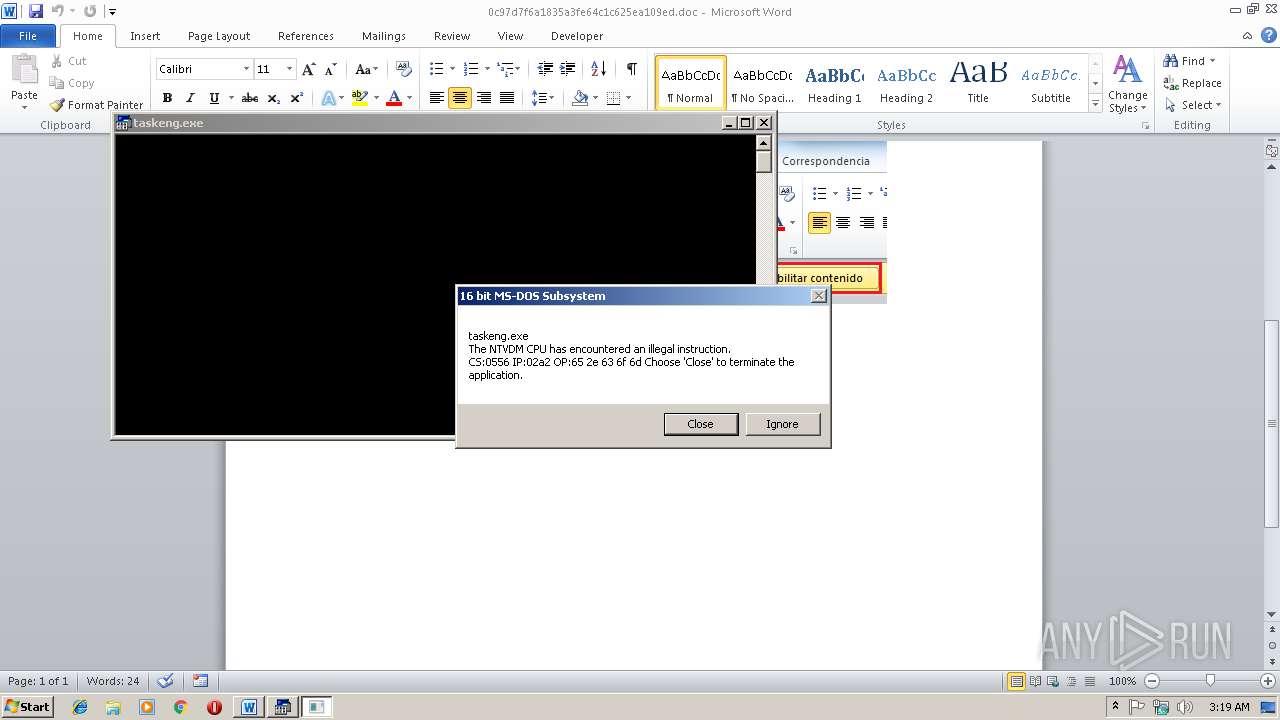
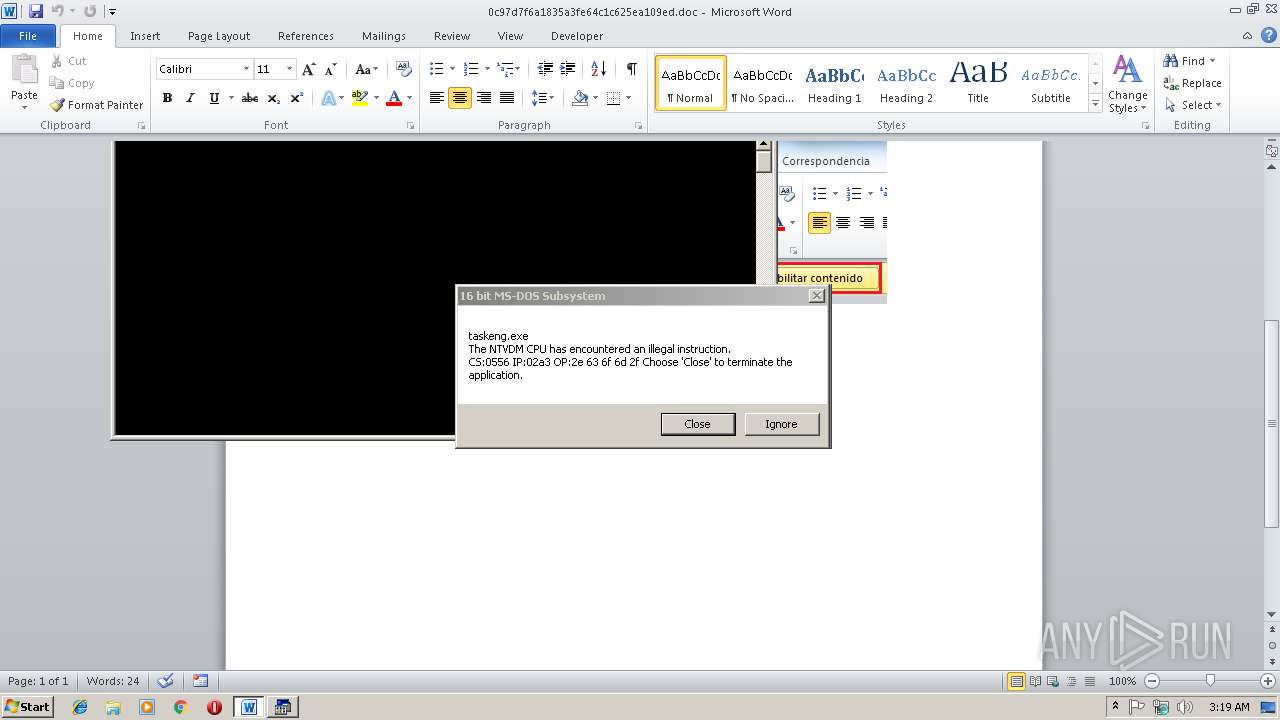
| 2268 | "C:\Windows\system32\ntvdm.exe" -i1 | C:\Windows\system32\ntvdm.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 3221225477 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2964 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\0c97d7f6a1835a3fe64c1c625ea109ed.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 083
Read events
747
Write events
331
Delete events
5
Modification events
| (PID) Process: | (2964) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | l~, |
Value: 6C7E2C00940B0000010000000000000000000000 | |||
| (PID) Process: | (2964) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2964) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2964) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1314062359 | |||
| (PID) Process: | (2964) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1314062480 | |||
| (PID) Process: | (2964) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1314062481 | |||
| (PID) Process: | (2964) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 940B0000A6B3A6CD01C8D40100000000 | |||
| (PID) Process: | (2964) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | %, |
Value: 257F2C00940B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2964) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | %, |
Value: 257F2C00940B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2964) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
4
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2964 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRE66C.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2964 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\21D9C36C.png | — | |
MD5:— | SHA256:— | |||
| 2964 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\EB6385A.png | — | |
MD5:— | SHA256:— | |||
| 2964 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2964 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$97d7f6a1835a3fe64c1c625ea109ed.doc | pgc | |
MD5:— | SHA256:— | |||
| 2268 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs3FB8.tmp | text | |
MD5:8CF6DDB5AA59B49F34B967CD46F013B6 | SHA256:EE06792197C3E025B84860A72460EAF628C66637685F8C52C5A08A9CC35D376C | |||
| 2964 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\suspendedpage[1].htm | html | |
MD5:AFC83AE7C4EA82B533D9B8731AAB3E80 | SHA256:FDF900267092BC67BD7786B86C462E69F9ED52BED838809B6BA28B298BE879F6 | |||
| 2964 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\l.exe | html | |
MD5:AFC83AE7C4EA82B533D9B8731AAB3E80 | SHA256:FDF900267092BC67BD7786B86C462E69F9ED52BED838809B6BA28B298BE879F6 | |||
| 2268 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs4084.tmp | text | |
MD5:4C361DEA398F7AEEF49953BDC0AB4A9B | SHA256:06D61C23E6CA59B9DDAD1796ECCC42C032CD8F6F424AF6CFEE5D085D36FF7DFD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2964 | WINWORD.EXE | GET | 302 | 198.54.116.50:80 | http://diangovcomuiscia.com/media/a.jpg | US | html | 237 b | malicious |
2964 | WINWORD.EXE | GET | 200 | 198.54.116.50:80 | http://diangovcomuiscia.com/cgi-sys/suspendedpage.cgi | US | html | 3.89 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2964 | WINWORD.EXE | 198.54.116.50:80 | diangovcomuiscia.com | Namecheap, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
diangovcomuiscia.com |
| malicious |