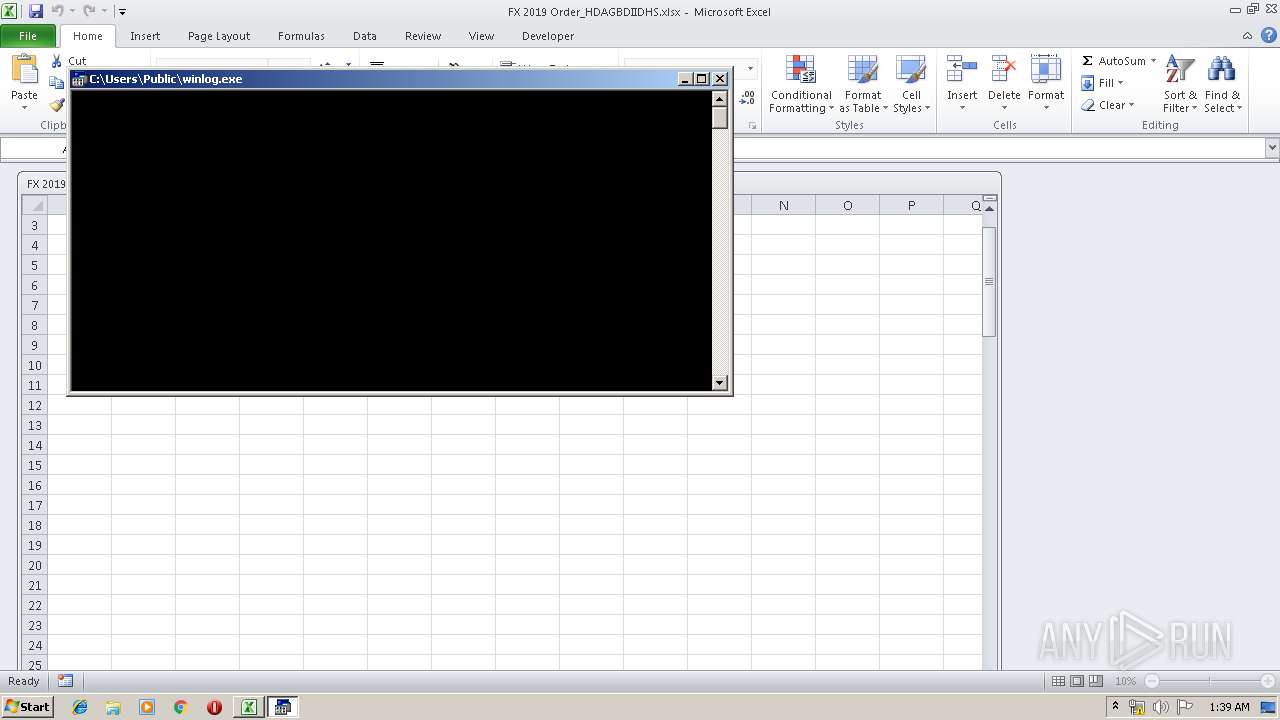
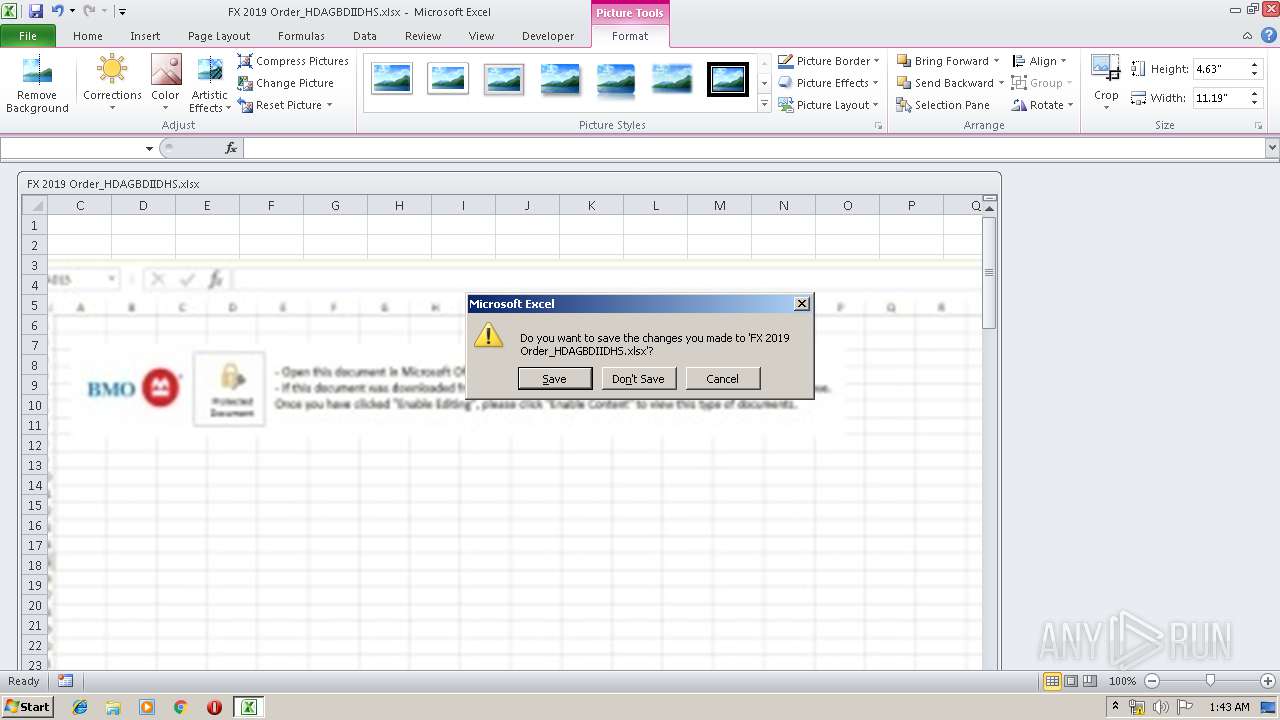
| File name: | FX 2019 Order_HDAGBDIIDHS.xlsx |
| Full analysis: | https://app.any.run/tasks/958d76df-aa9f-4fd4-a648-80a32aeea869 |
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2019, 00:38:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/encrypted |
| File info: | CDFV2 Encrypted |
| MD5: | 9502D12BA2124686F72AE98E122F891D |
| SHA1: | E80EE87D5FCCF8B91F1DD38794FB7067A991AA4F |
| SHA256: | B75D1C4A1C0782A6C9168DC2D73A0065B88E462EBF7356D3F9EDF8E3DB389216 |
| SSDEEP: | 768:IoowjRhSrTOsO+1FLtbPD2YeO2OJ0JsWocAS:ljPSr6qxblHUJeS |
MALICIOUS
Equation Editor starts application (CVE-2017-11882)
- EQNEDT32.EXE (PID: 2128)
SUSPICIOUS
Executes application which crashes
- EQNEDT32.EXE (PID: 2128)
Executed via COM
- EQNEDT32.EXE (PID: 2128)
INFO
Manual execution by user
- WINWORD.EXE (PID: 1180)
Creates files in the user directory
- WINWORD.EXE (PID: 1180)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1180)
- EXCEL.EXE (PID: 3156)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1180 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2128 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
| 3156 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 4036 | "C:\Windows\system32\ntvdm.exe" -i1 | C:\Windows\system32\ntvdm.exe | — | EQNEDT32.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 134
Read events
1 050
Write events
68
Delete events
16
Modification events
| (PID) Process: | (3156) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | (8> |
Value: 28383E00540C0000010000000000000000000000 | |||
| (PID) Process: | (3156) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3156) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3156) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel |
| Operation: | write | Name: | MTTT |
Value: 540C0000CA0413713726D50100000000 | |||
| (PID) Process: | (3156) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete value | Name: | (8> |
Value: 28383E00540C0000010000000000000000000000 | |||
| (PID) Process: | (3156) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3156) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3156) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3156) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3156) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\DocumentRecovery\11FF3E |
| Operation: | write | Name: | 11FF3E |
Value: 04000000540C00004000000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C00460058002000320030003100390020004F0072006400650072005F00480044004100470042004400490049004400480053002E0078006C0073007800000000002200000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C0001000000000000003045BB723726D5013EFF11003EFF110000000000AC020000001000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3156 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRF828.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 4036 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs930.tmp | — | |
MD5:— | SHA256:— | |||
| 4036 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs940.tmp | — | |
MD5:— | SHA256:— | |||
| 3156 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\C18CD03.jpeg | — | |
MD5:— | SHA256:— | |||
| 3156 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DF1ABF203D9630C41D.TMP | — | |
MD5:— | SHA256:— | |||
| 3156 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~$FX 2019 Order_HDAGBDIIDHS.xlsx | — | |
MD5:— | SHA256:— | |||
| 1180 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR58F2.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1180 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2128 | EQNEDT32.EXE | C:\Users\Public\winlog.exe | binary | |
MD5:— | SHA256:— | |||
| 2128 | EQNEDT32.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\kabzzy[1].exe | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
0
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2128 | EQNEDT32.EXE | GET | 200 | 216.170.122.22:80 | http://216.170.122.22/kabzzy.exe | US | binary | 620 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2128 | EQNEDT32.EXE | 216.170.122.22:80 | — | ColoCrossing | US | suspicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
2128 | EQNEDT32.EXE | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |