analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
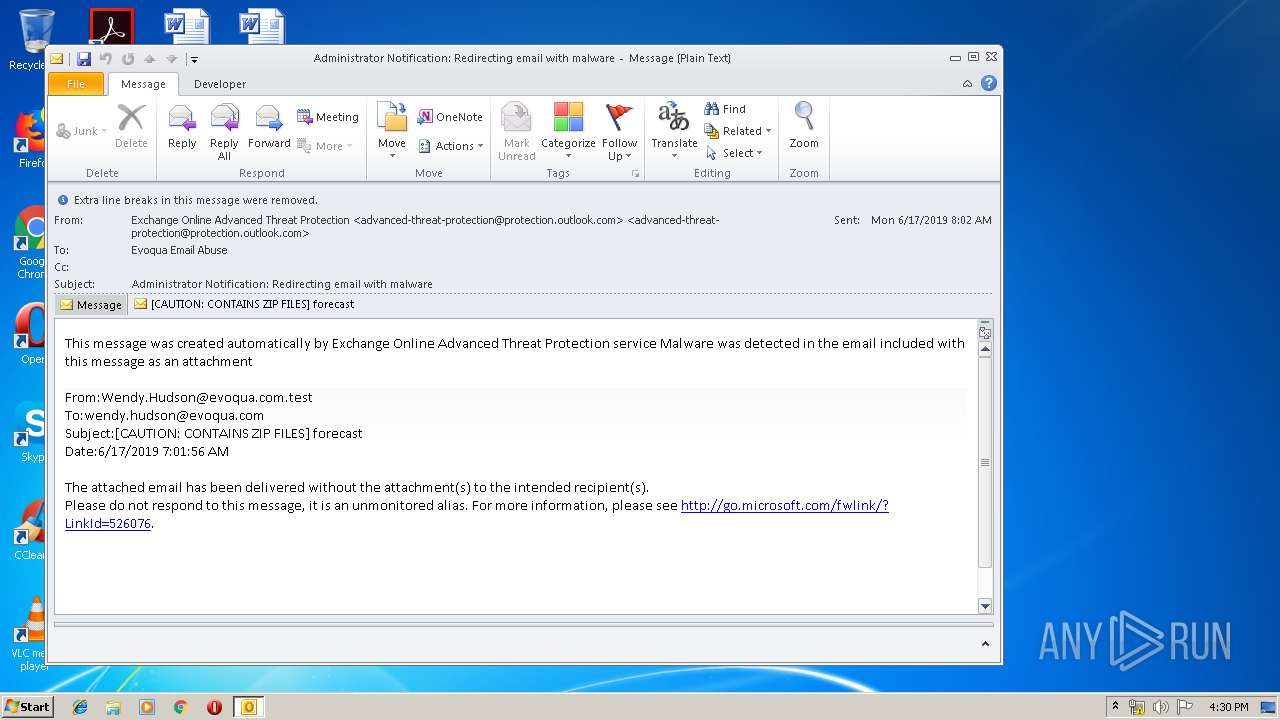
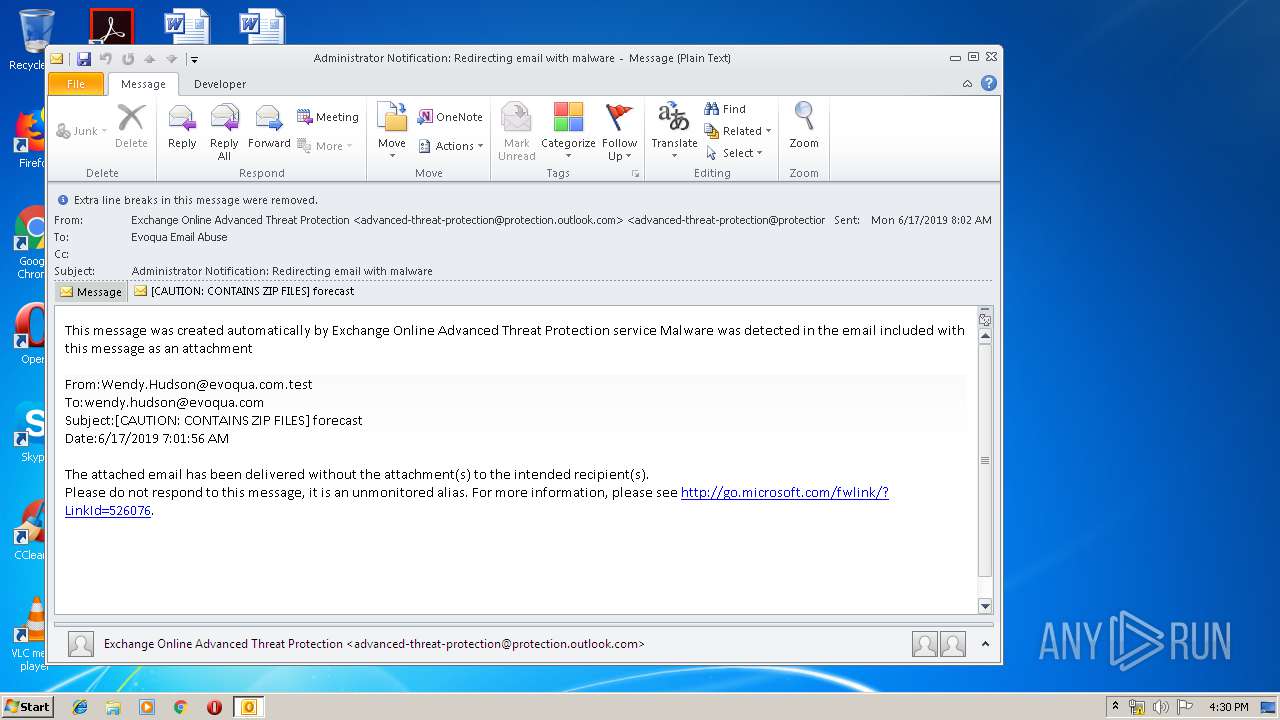
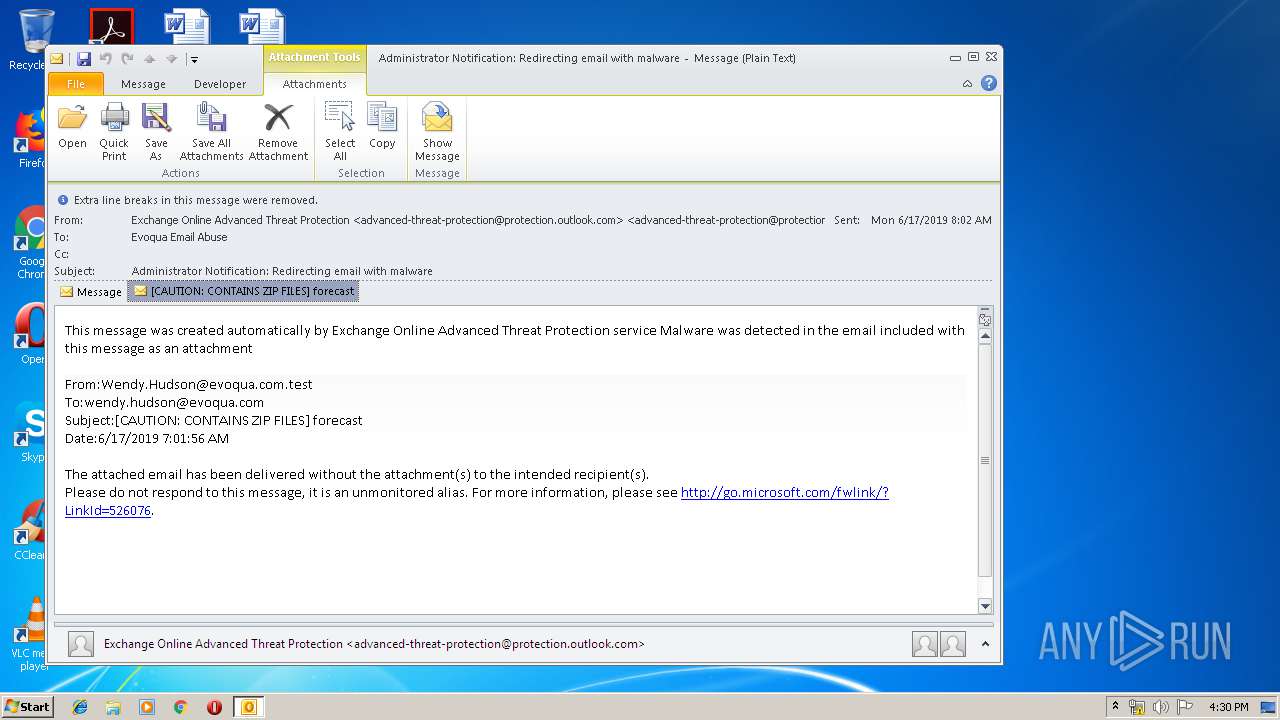
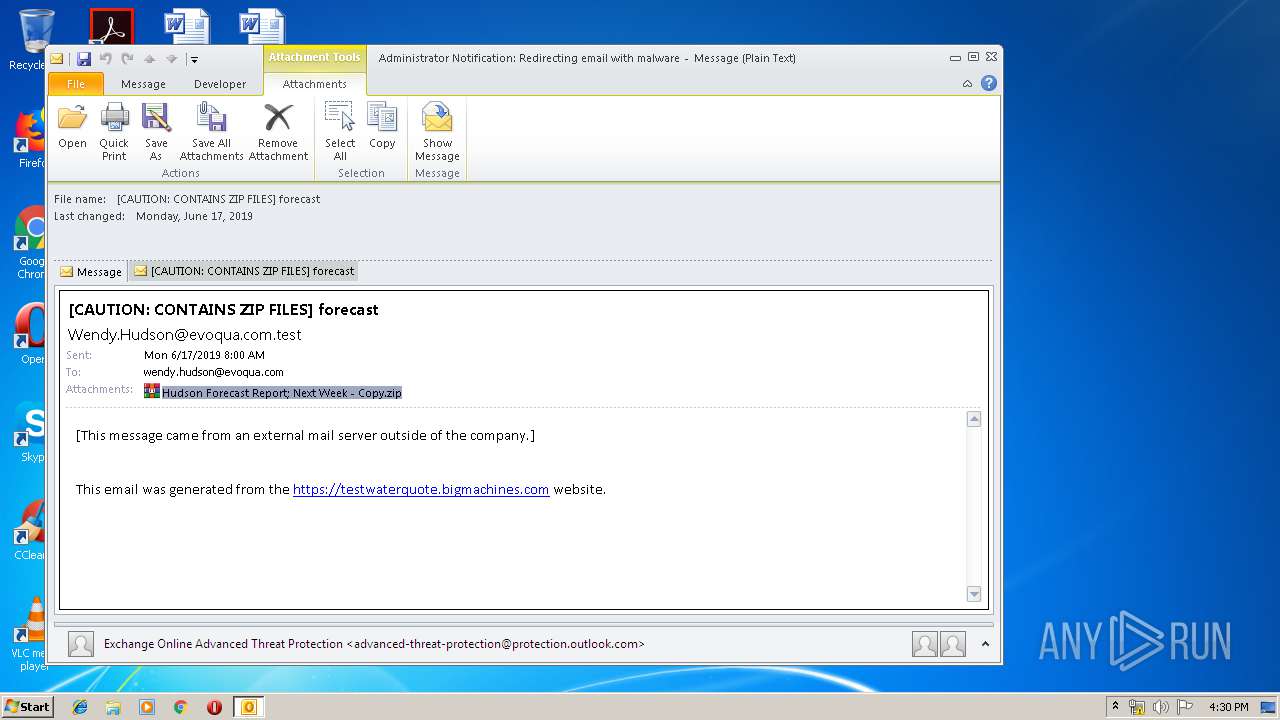
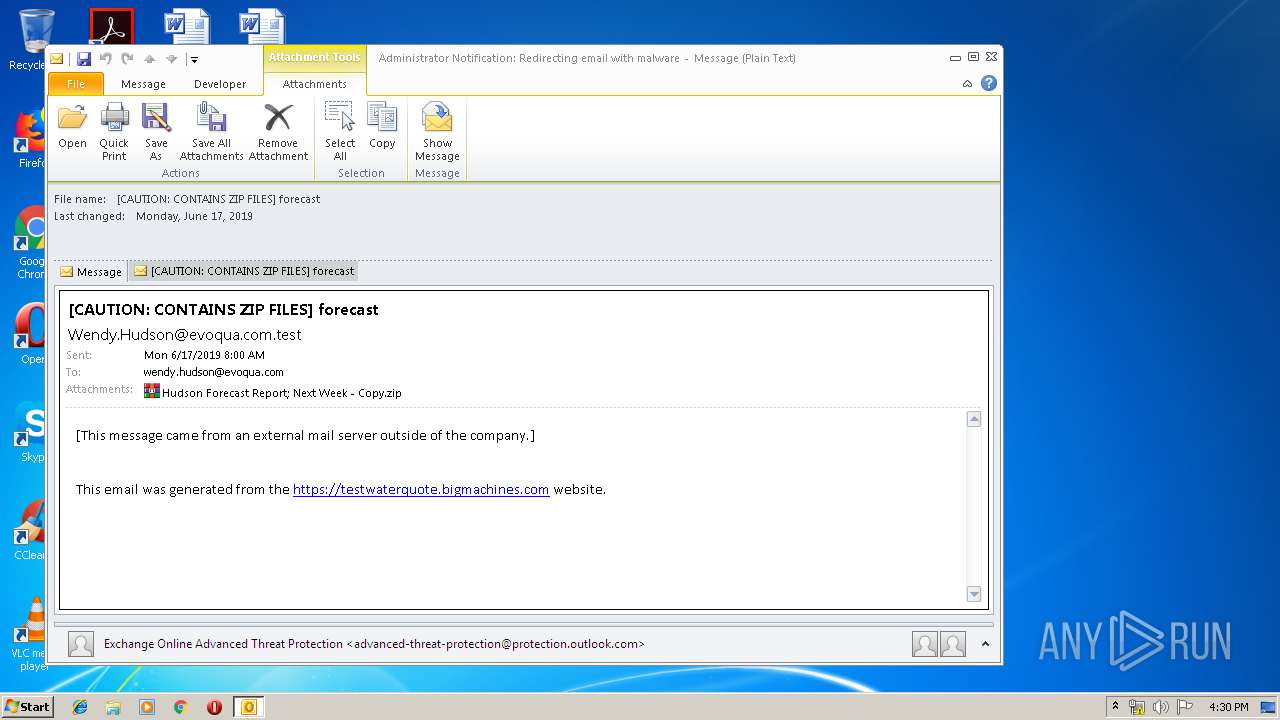
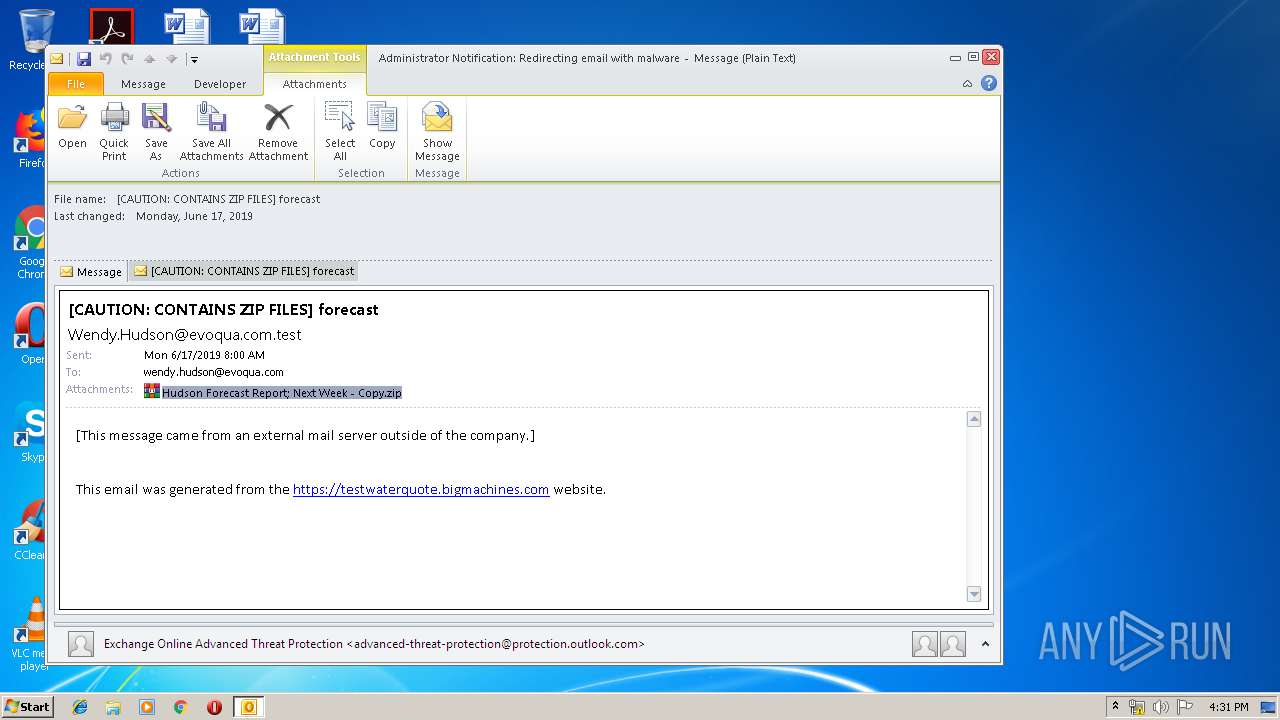
| File name: | Administrator Notification_ Redirecting email with malware.msg |
| Full analysis: | https://app.any.run/tasks/d201631e-7e1f-4246-abdf-4bbe17592772 |
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2019, 15:29:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 8E8021F3949C1B51CC76D7963654CC23 |
| SHA1: | B7EBF2F7BCB45E0DAF6D1BA002460572DD0A8628 |
| SHA256: | B749D25773BCE61E56F1DC674134DF65F2F9B52513BC897C88778493FFA6AE45 |
| SSDEEP: | 1536:JuWTW+S+iBTv1Hxb0mCWUWQfyas7y05G/0UGRqCvuOl1b9JR:J1SFBTdxIkZ5R |
MALICIOUS
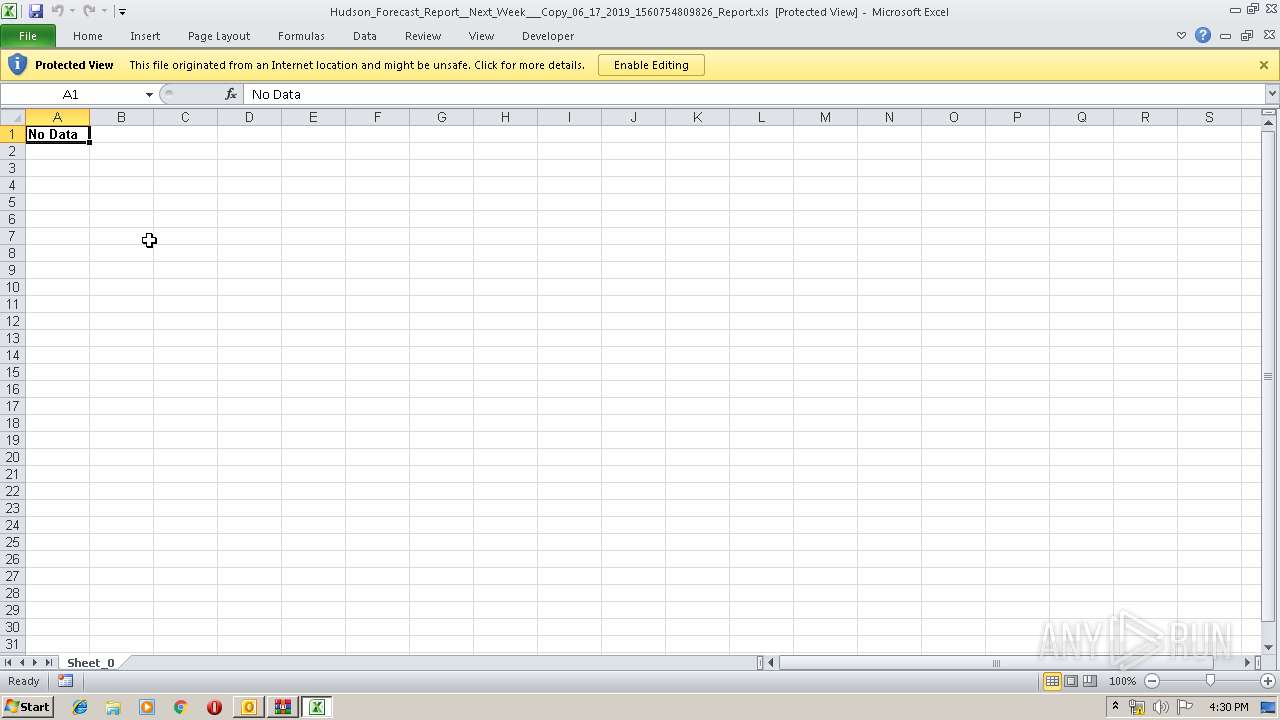
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 3316)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 3316)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 3316)
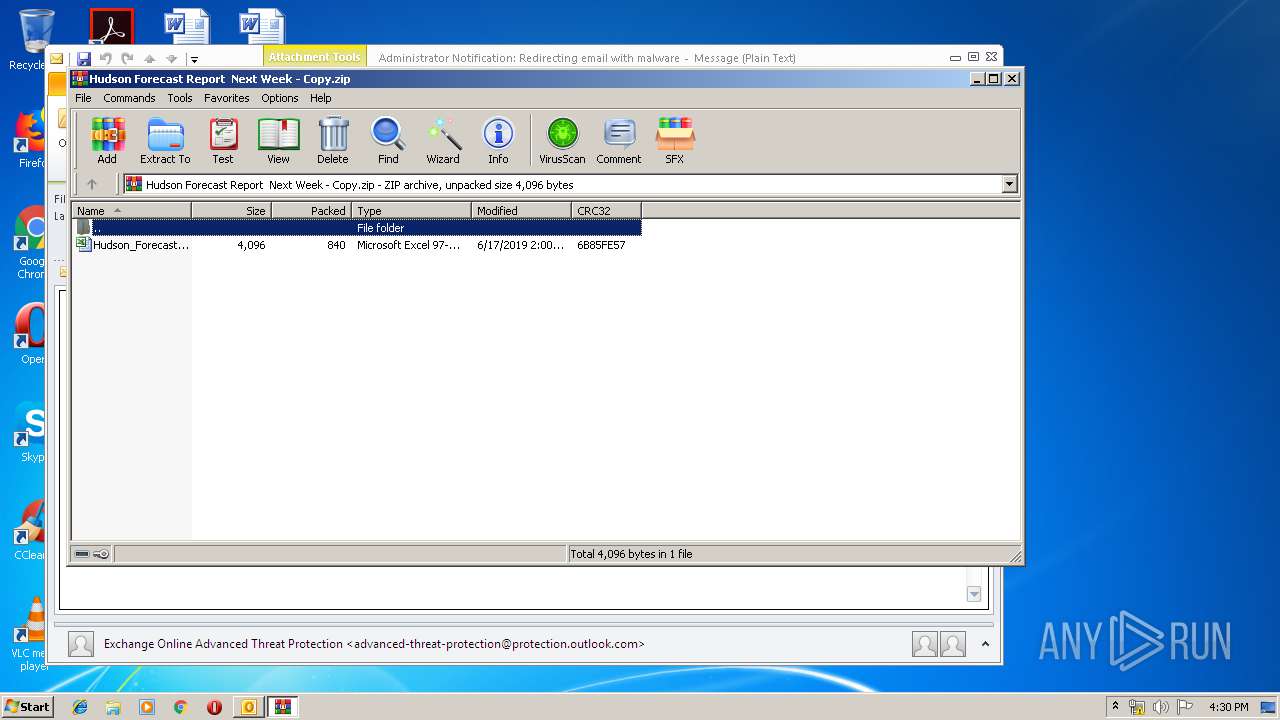
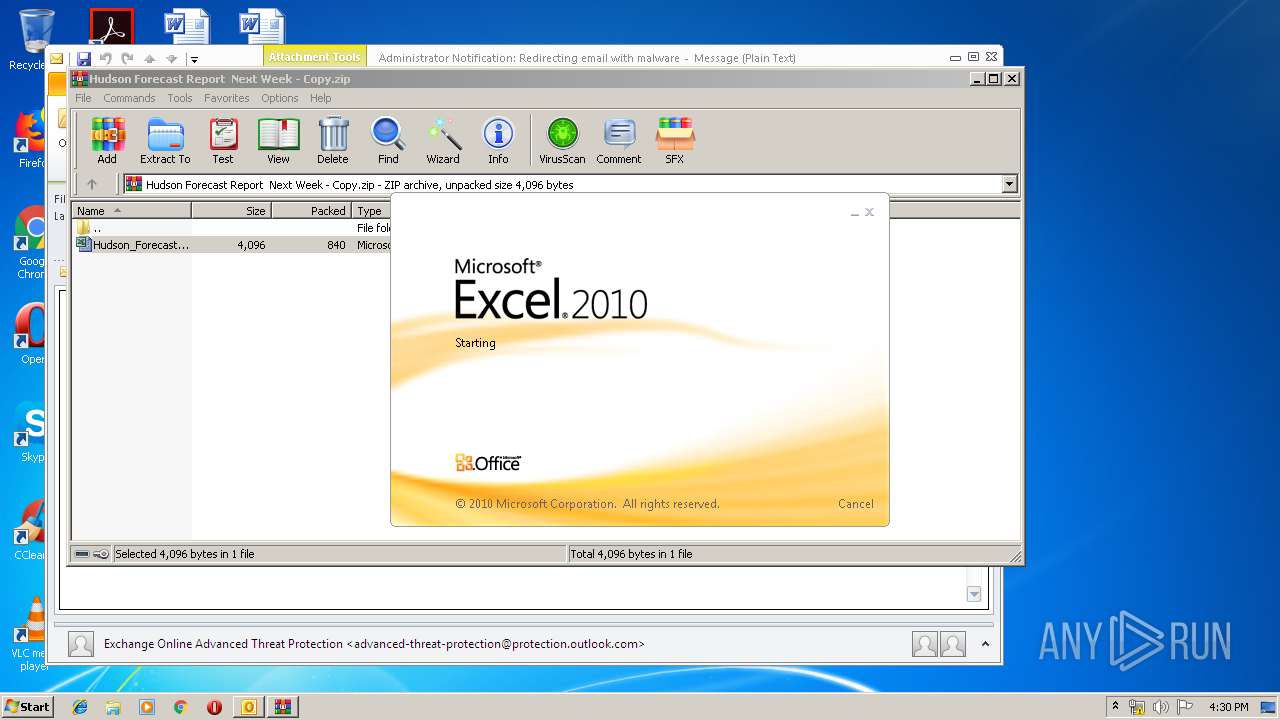
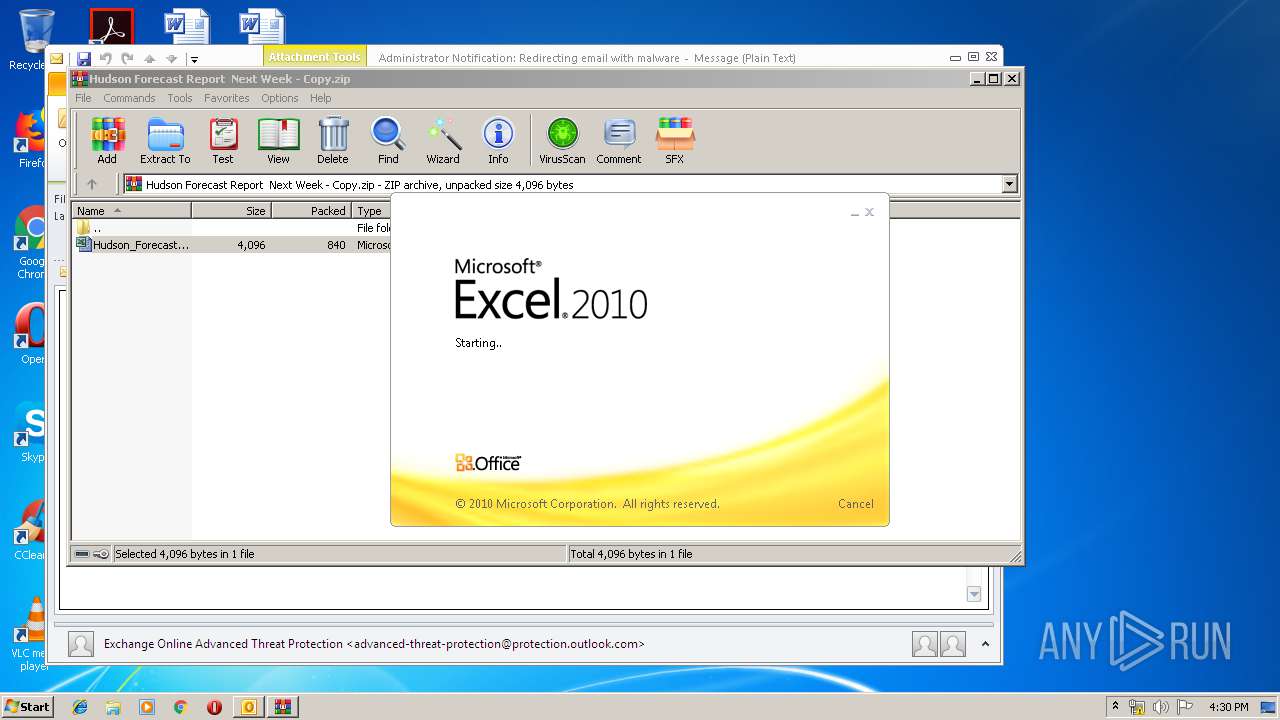
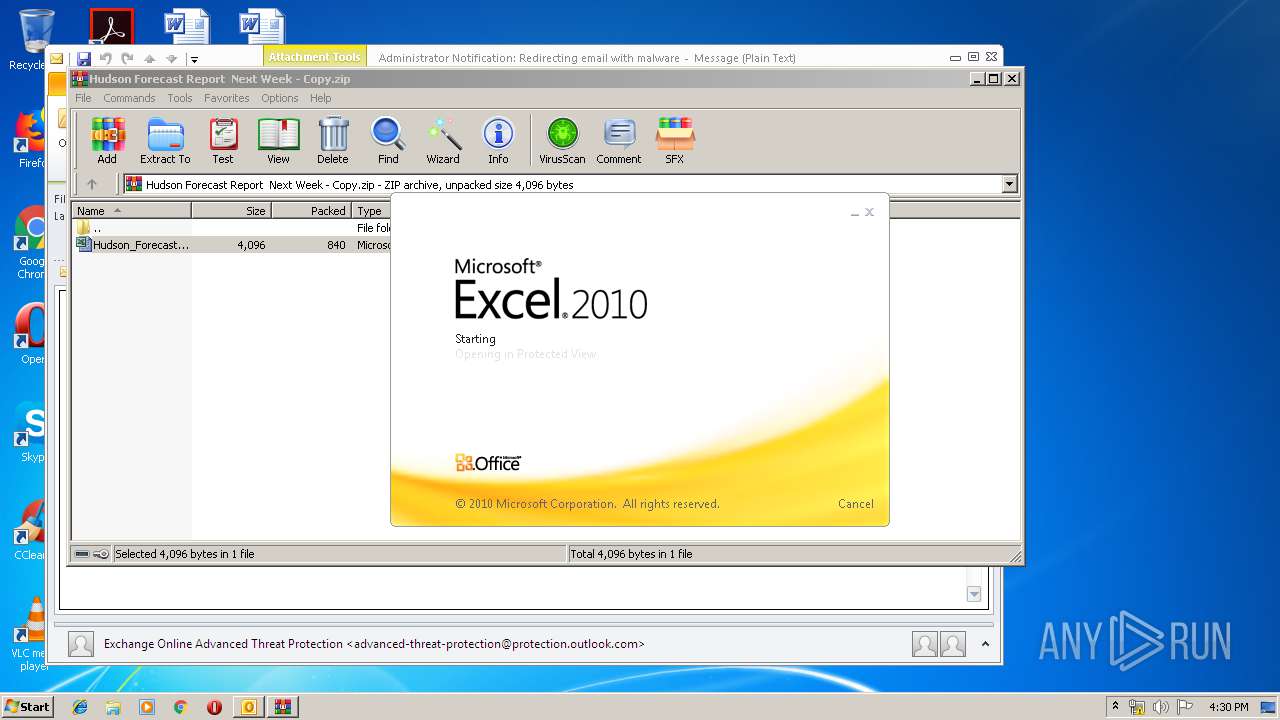
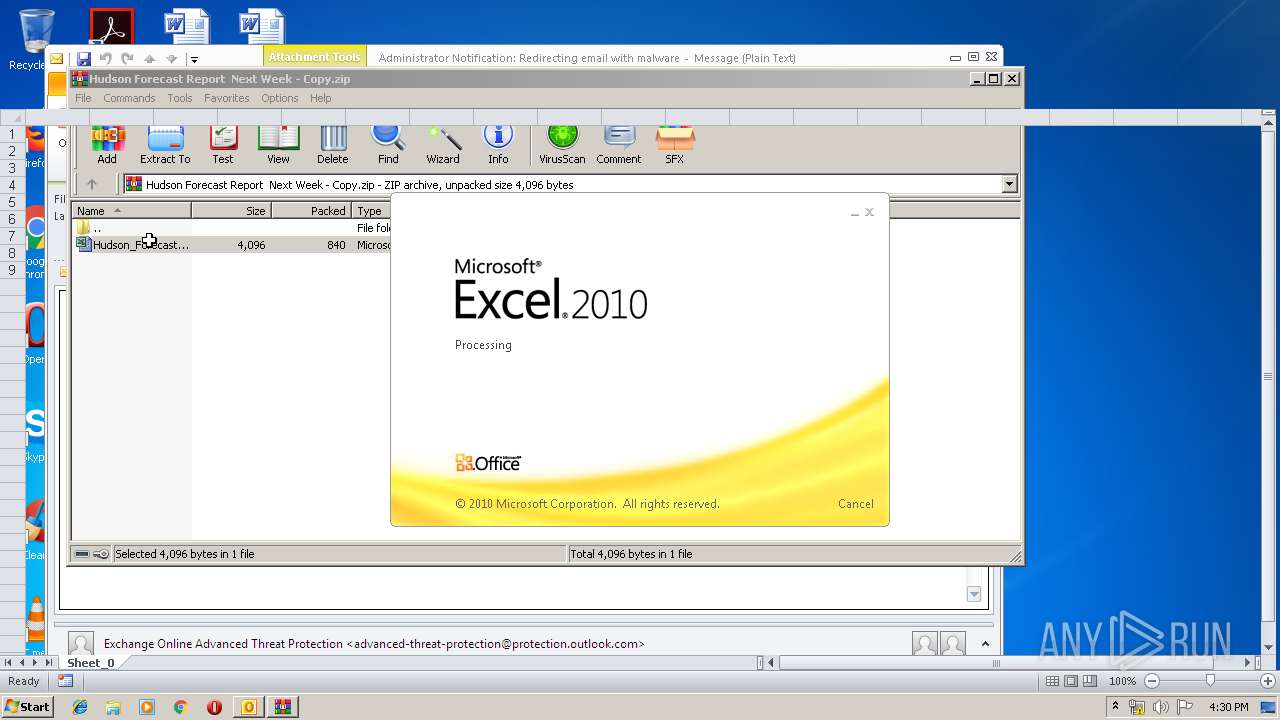
Starts Microsoft Office Application
- WinRAR.exe (PID: 2112)
- EXCEL.EXE (PID: 2636)
Application launched itself
- EXCEL.EXE (PID: 2636)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 3276)
- EXCEL.EXE (PID: 2636)
- OUTLOOK.EXE (PID: 3316)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
37
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
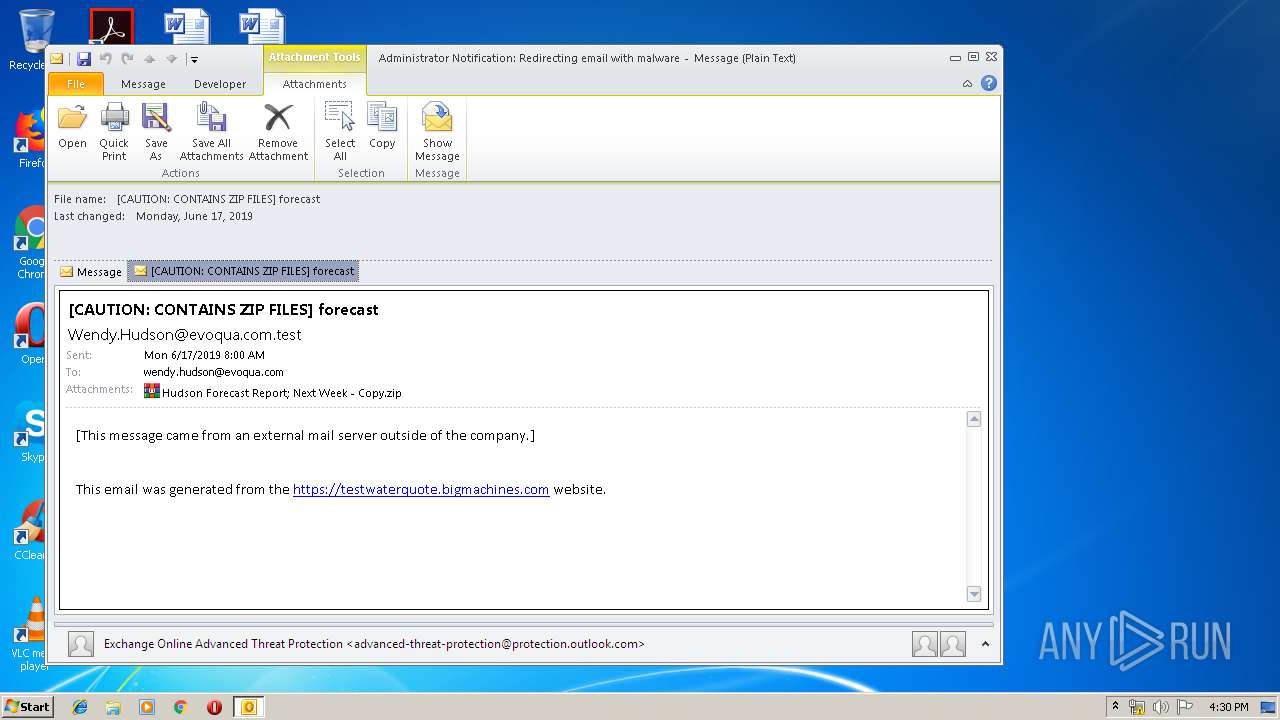
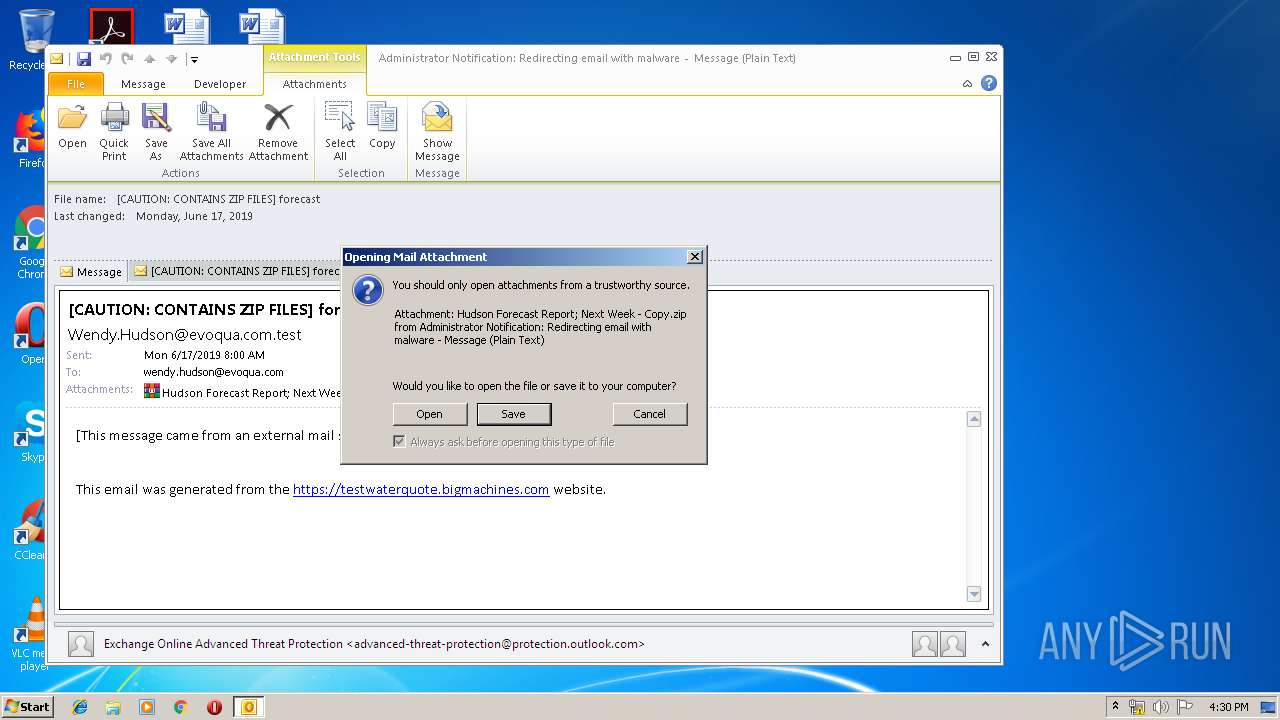
| 3316 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Administrator Notification_ Redirecting email with malware.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 | ||||
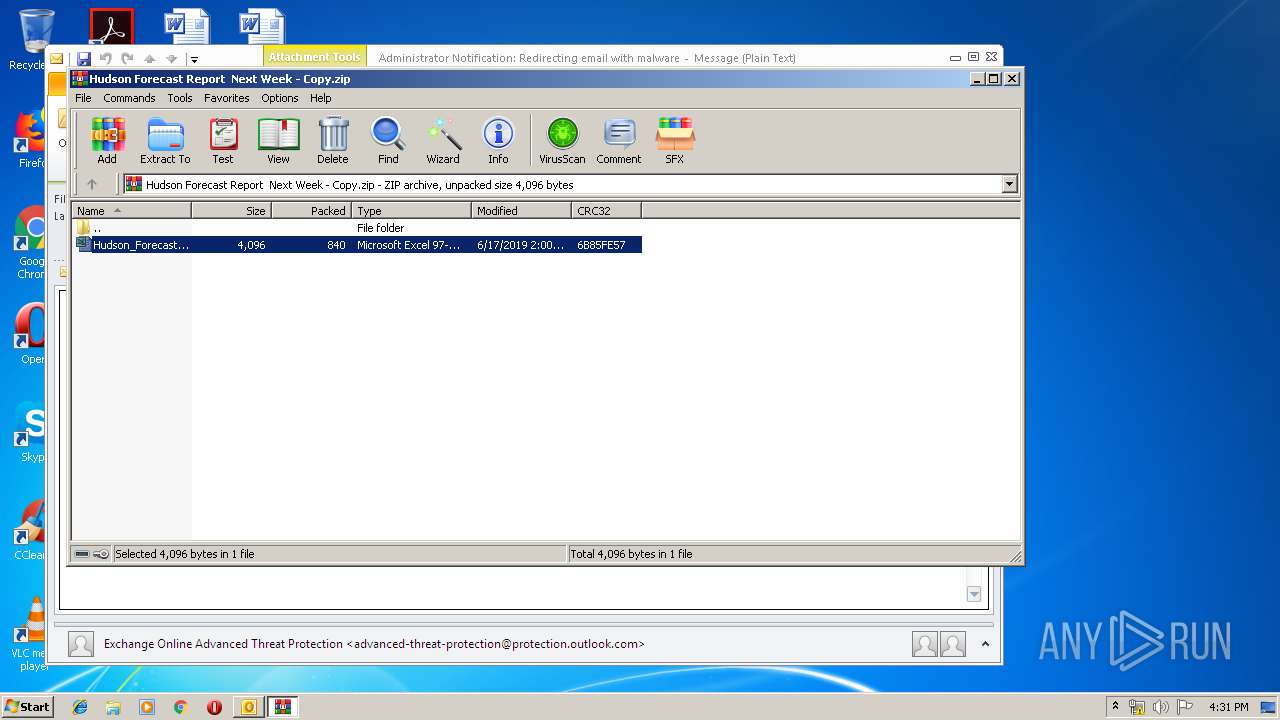
| 2112 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\QRD19XO1\Hudson Forecast Report Next Week - Copy.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | OUTLOOK.EXE |
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 | ||||
| 2636 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | WinRAR.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 | ||||
| 3276 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | EXCEL.EXE |
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 | ||||
Total events
3 129
Read events
2 626
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
7
Text files
26
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3316 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRECAF.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3316 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DFE4A7EA43BF152CCD.TMP | — | |
MD5:— | SHA256:— | |||
| 3316 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\QRD19XO1\Hudson Forecast Report Next Week - Copy (2).zip\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2636 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR5C12.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2636 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DF900F65A45E4F4BC1.TMP | — | |
MD5:— | SHA256:— | |||
| 2636 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\OICE_30030A6B-C76D-4C7A-B954-A0C7C0B283C0.0\2C60C38D.xls\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3316 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:53A4E1E2B105A1908FA1CF2D49B3084A | SHA256:19A75587A000660C8D10CCEB430EF78D273B35A047127793F4E2B1CE275A5FAC | |||
| 3276 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\OICE_30030A6B-C76D-4C7A-B954-A0C7C0B283C0.0\~DF7E5CFBCF67551E39.TMP | — | |
MD5:— | SHA256:— | |||
| 3276 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\OICE_30030A6B-C76D-4C7A-B954-A0C7C0B283C0.0\~DF7ACB6EB9A51E71FA.TMP | — | |
MD5:— | SHA256:— | |||
| 3316 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DF676F69B6AD756BFA.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3316 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3316 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |