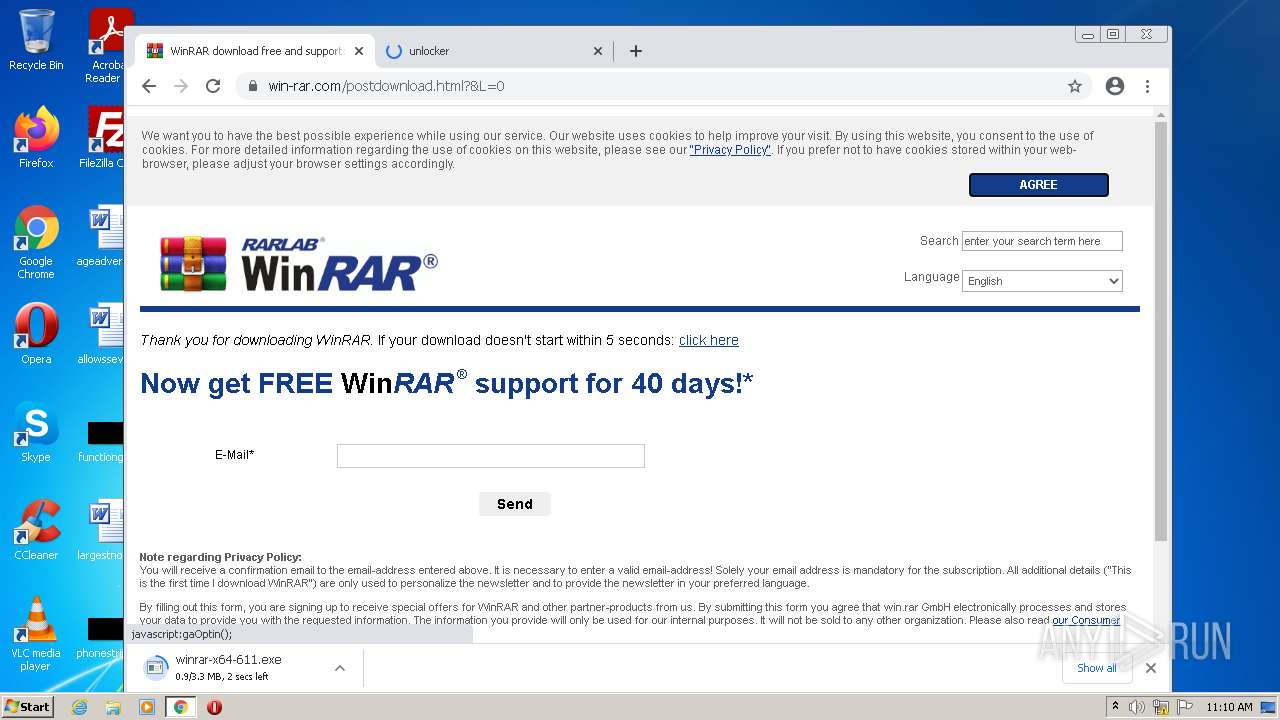
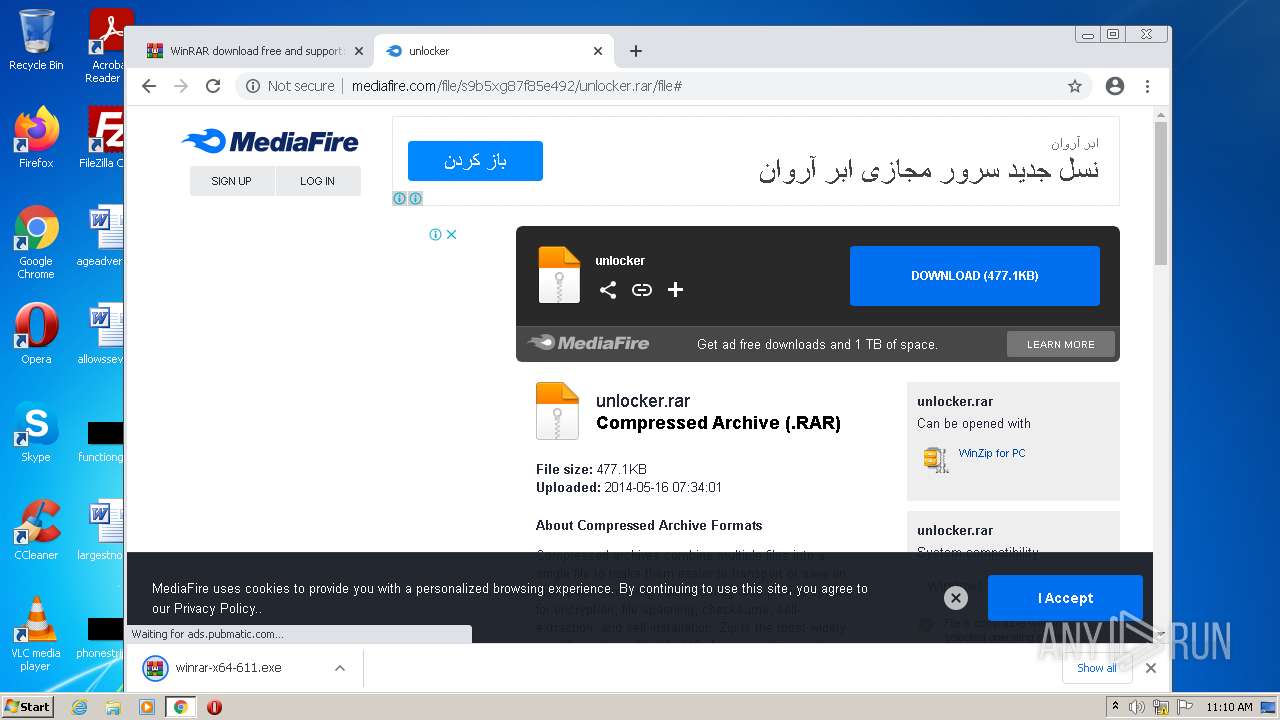
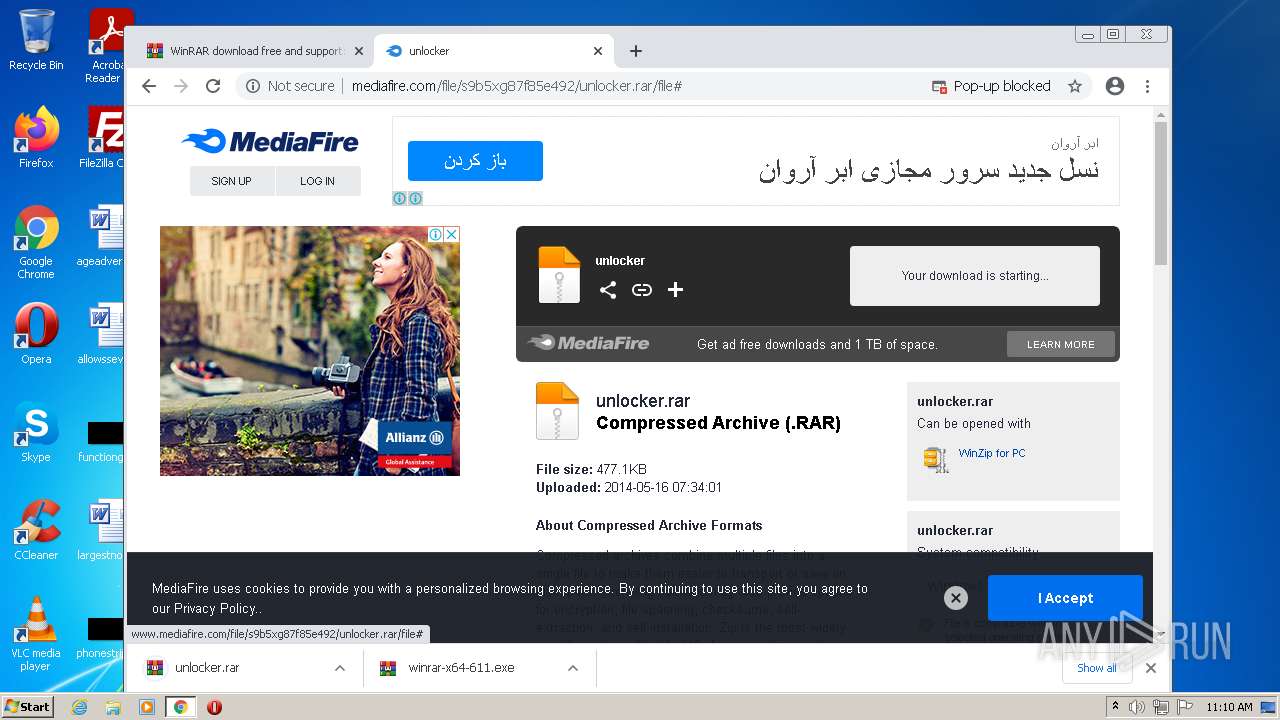
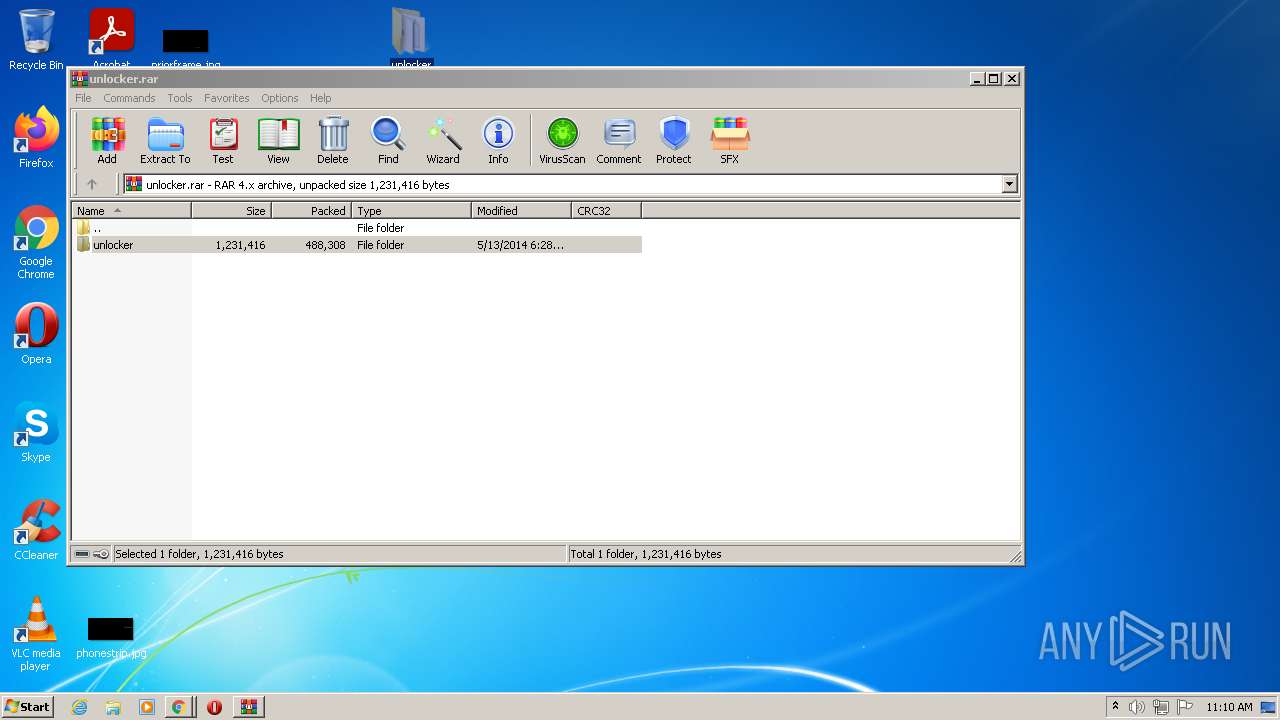
| URL: | http://www.mediafire.com/file/s9b5xg87f85e492/unlocker.rar/file# |
| Full analysis: | https://app.any.run/tasks/f6d4e862-3f6a-4212-87d4-1cd6e9df21b3 |
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2022, 10:09:58 |
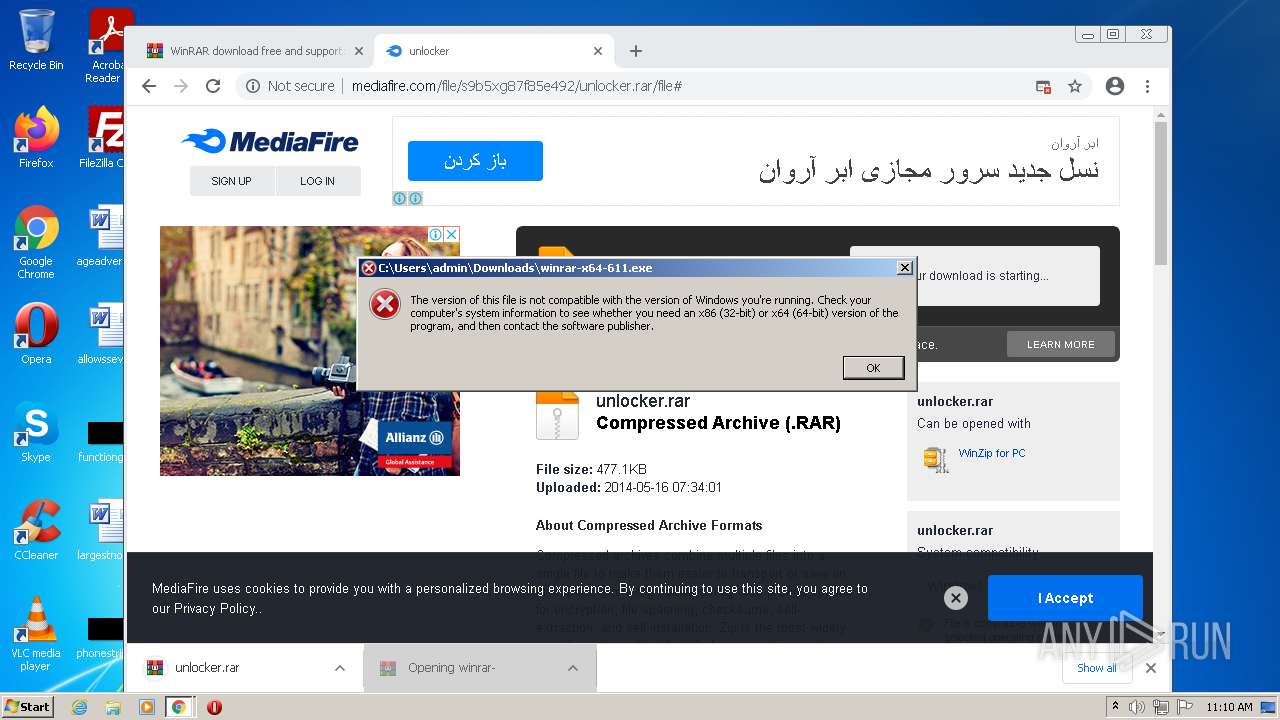
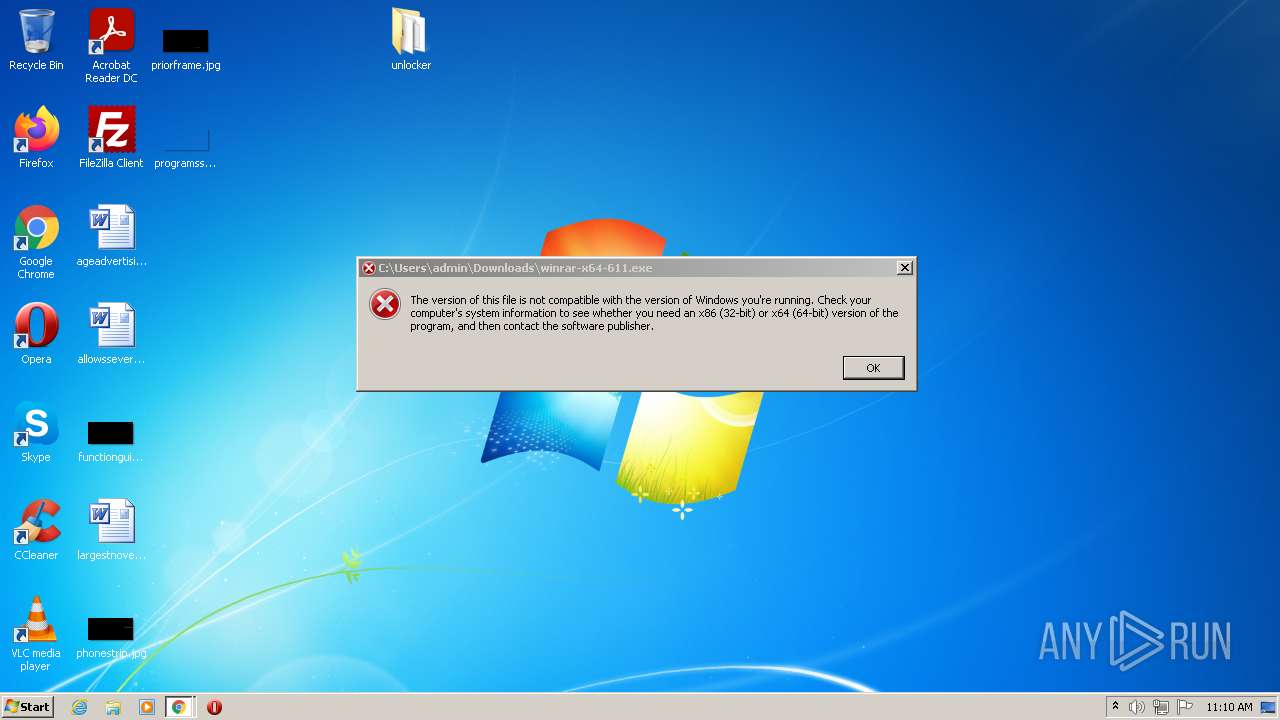
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 3619540C95722ADA71F9B9E2EAC5960B |
| SHA1: | 43747805F15A886E2CCEB6467F3A8604E3EEF4FB |
| SHA256: | B73DCDA756EE435AFC24B24948C3B92E3B41C251D4600E29AD9EC8F5A9C6275E |
| SSDEEP: | 3:N1KJS4w3eGUobwAWXUzaj:Cc4w3eGYrEGj |
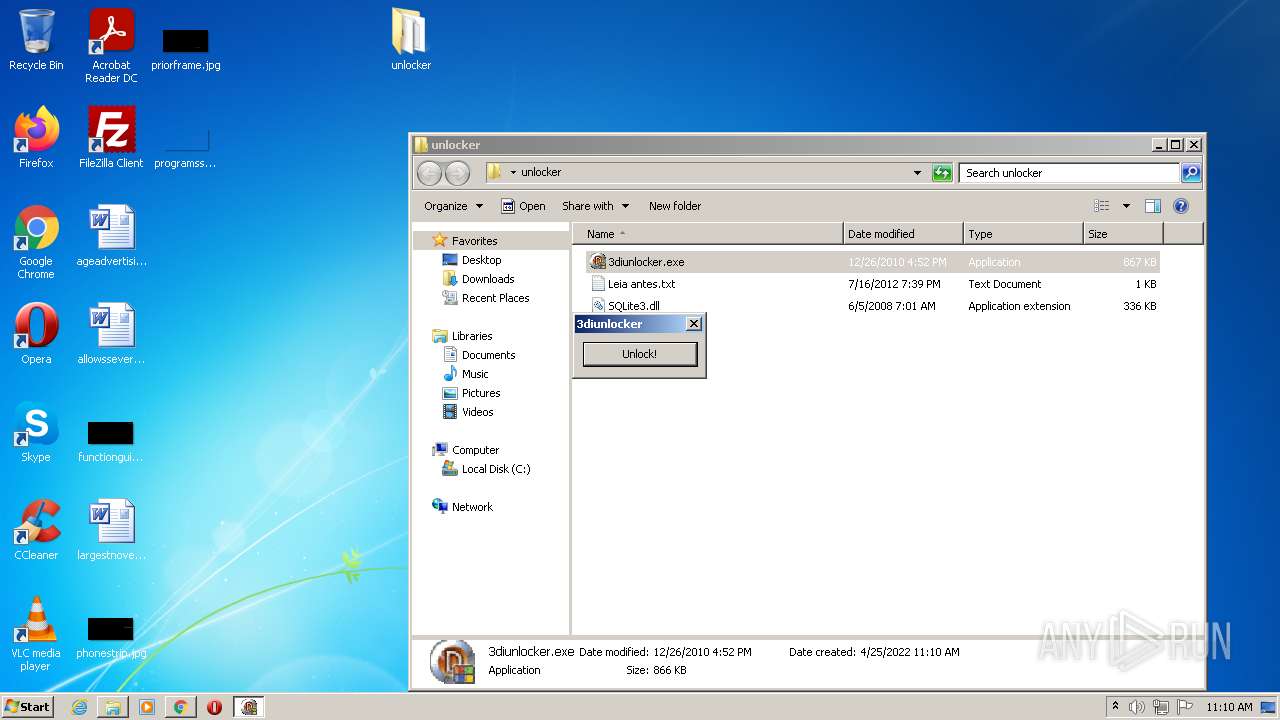
MALICIOUS
Drops executable file immediately after starts
- chrome.exe (PID: 2448)
- chrome.exe (PID: 3072)
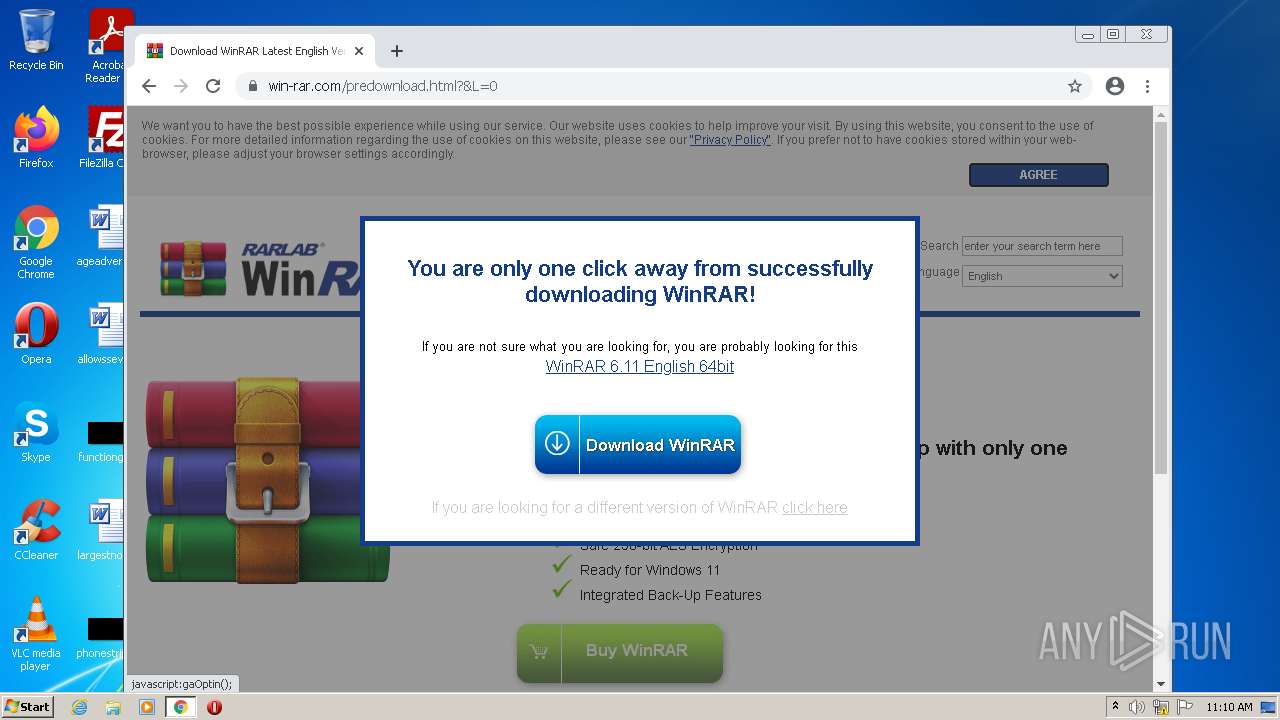
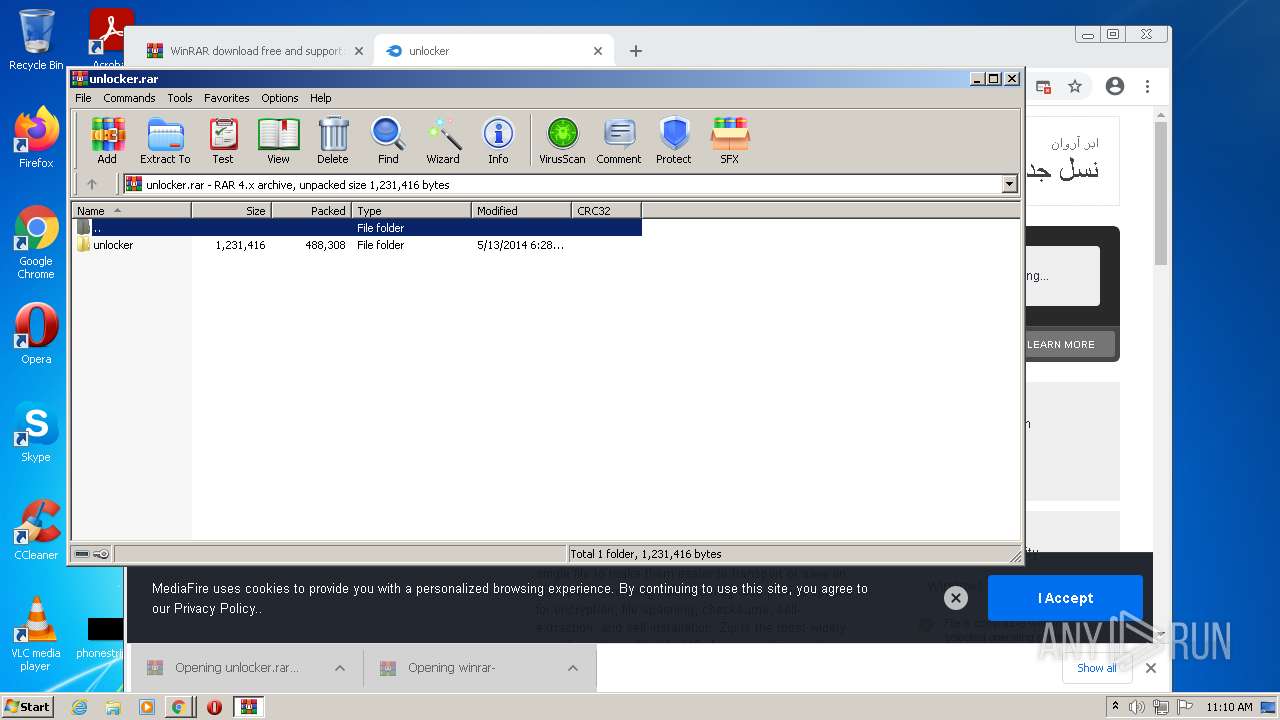
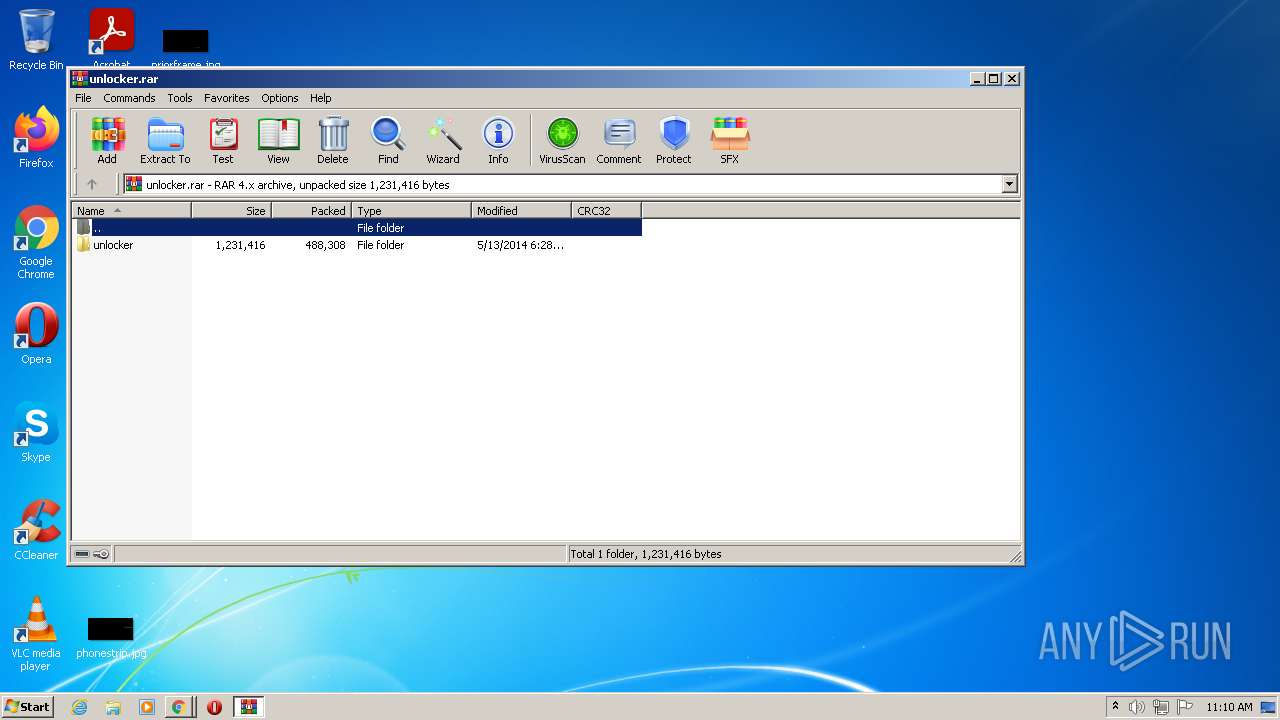
- WinRAR.exe (PID: 1972)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3540)
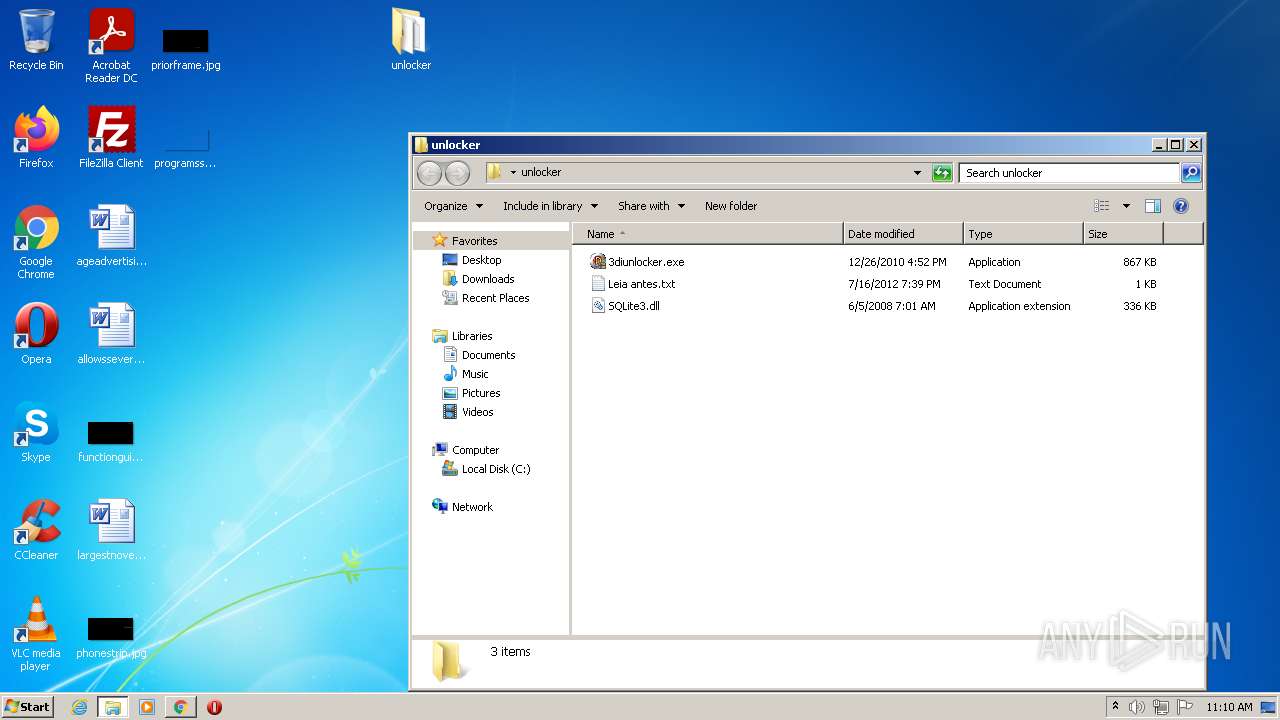
- 3diunlocker.exe (PID: 2484)
- 3diunlocker.exe (PID: 3972)
Application was dropped or rewritten from another process
- 3diunlocker.exe (PID: 2484)
- 3diunlocker.exe (PID: 3972)
SUSPICIOUS
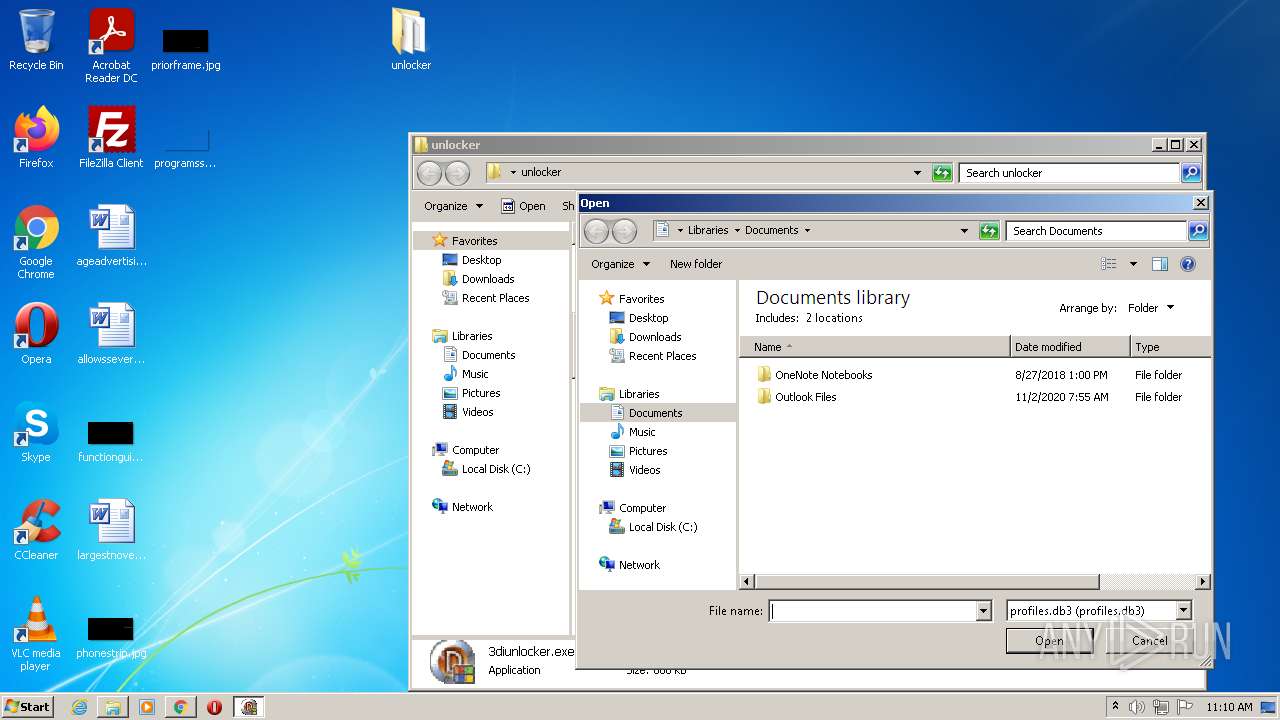
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 1988)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2448)
Drops a file with a compile date too recent
- chrome.exe (PID: 2448)
- chrome.exe (PID: 3072)
- WinRAR.exe (PID: 1972)
Executable content was dropped or overwritten
- chrome.exe (PID: 2448)
- chrome.exe (PID: 3072)
- WinRAR.exe (PID: 1972)
Checks supported languages
- WinRAR.exe (PID: 1972)
- 3diunlocker.exe (PID: 2484)
- 3diunlocker.exe (PID: 3972)
Reads the computer name
- WinRAR.exe (PID: 1972)
- 3diunlocker.exe (PID: 2484)
INFO
Checks supported languages
- iexplore.exe (PID: 2604)
- chrome.exe (PID: 2428)
- iexplore.exe (PID: 1988)
- chrome.exe (PID: 3072)
- chrome.exe (PID: 2988)
- chrome.exe (PID: 2448)
- chrome.exe (PID: 1868)
- chrome.exe (PID: 1292)
- chrome.exe (PID: 3680)
- chrome.exe (PID: 3740)
- chrome.exe (PID: 916)
- chrome.exe (PID: 1832)
- chrome.exe (PID: 4044)
- chrome.exe (PID: 3244)
- chrome.exe (PID: 3872)
- chrome.exe (PID: 736)
- chrome.exe (PID: 2216)
- chrome.exe (PID: 3428)
- chrome.exe (PID: 2272)
- chrome.exe (PID: 1768)
- chrome.exe (PID: 2988)
- chrome.exe (PID: 2648)
- chrome.exe (PID: 1640)
- chrome.exe (PID: 3640)
- chrome.exe (PID: 2536)
- chrome.exe (PID: 2216)
- chrome.exe (PID: 3756)
- chrome.exe (PID: 2168)
- chrome.exe (PID: 3548)
- chrome.exe (PID: 2288)
- chrome.exe (PID: 3432)
- chrome.exe (PID: 2652)
- chrome.exe (PID: 772)
- chrome.exe (PID: 1656)
- chrome.exe (PID: 2480)
- chrome.exe (PID: 1928)
- chrome.exe (PID: 3464)
- chrome.exe (PID: 3780)
- chrome.exe (PID: 2160)
- chrome.exe (PID: 3672)
- chrome.exe (PID: 2788)
- chrome.exe (PID: 2720)
- chrome.exe (PID: 3384)
- chrome.exe (PID: 2616)
- chrome.exe (PID: 1376)
- chrome.exe (PID: 2812)
- chrome.exe (PID: 3336)
- chrome.exe (PID: 2636)
- chrome.exe (PID: 3836)
- chrome.exe (PID: 1584)
- chrome.exe (PID: 3512)
- chrome.exe (PID: 2192)
- chrome.exe (PID: 3576)
- chrome.exe (PID: 2340)
- chrome.exe (PID: 1828)
- chrome.exe (PID: 1556)
Application launched itself
- iexplore.exe (PID: 2604)
- chrome.exe (PID: 2448)
Reads settings of System Certificates
- iexplore.exe (PID: 2604)
- chrome.exe (PID: 3072)
- chrome.exe (PID: 2448)
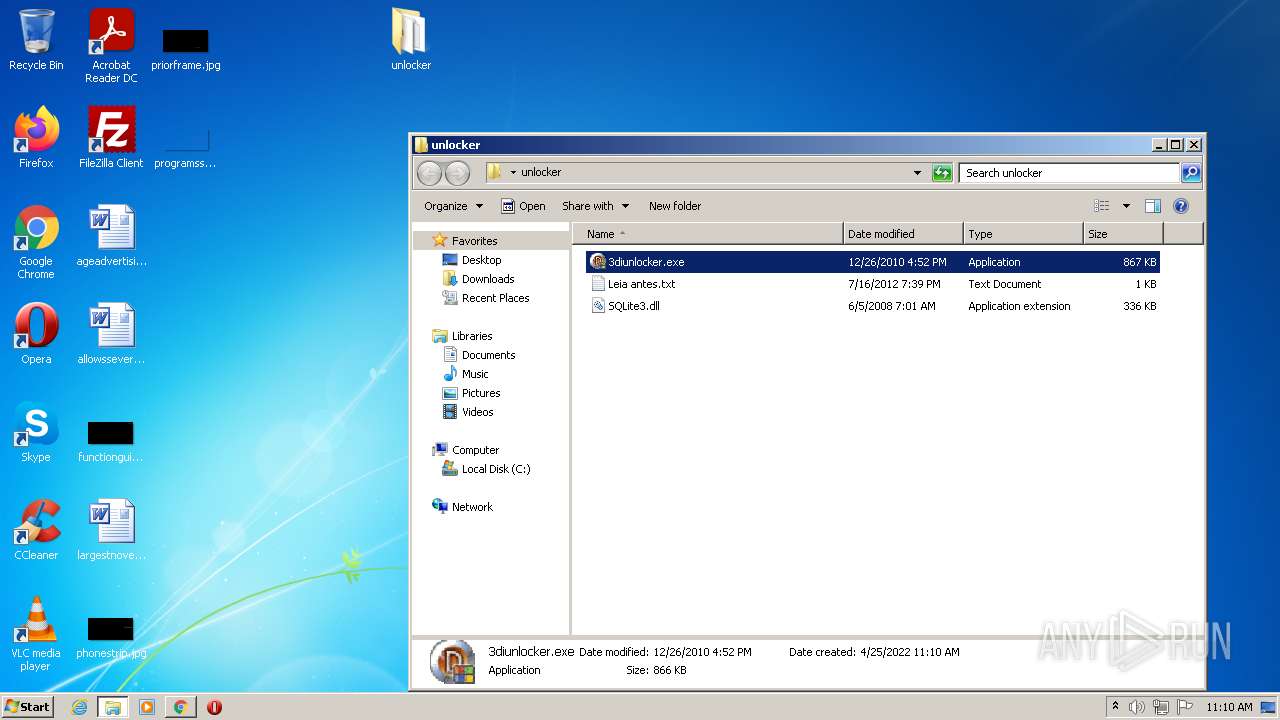
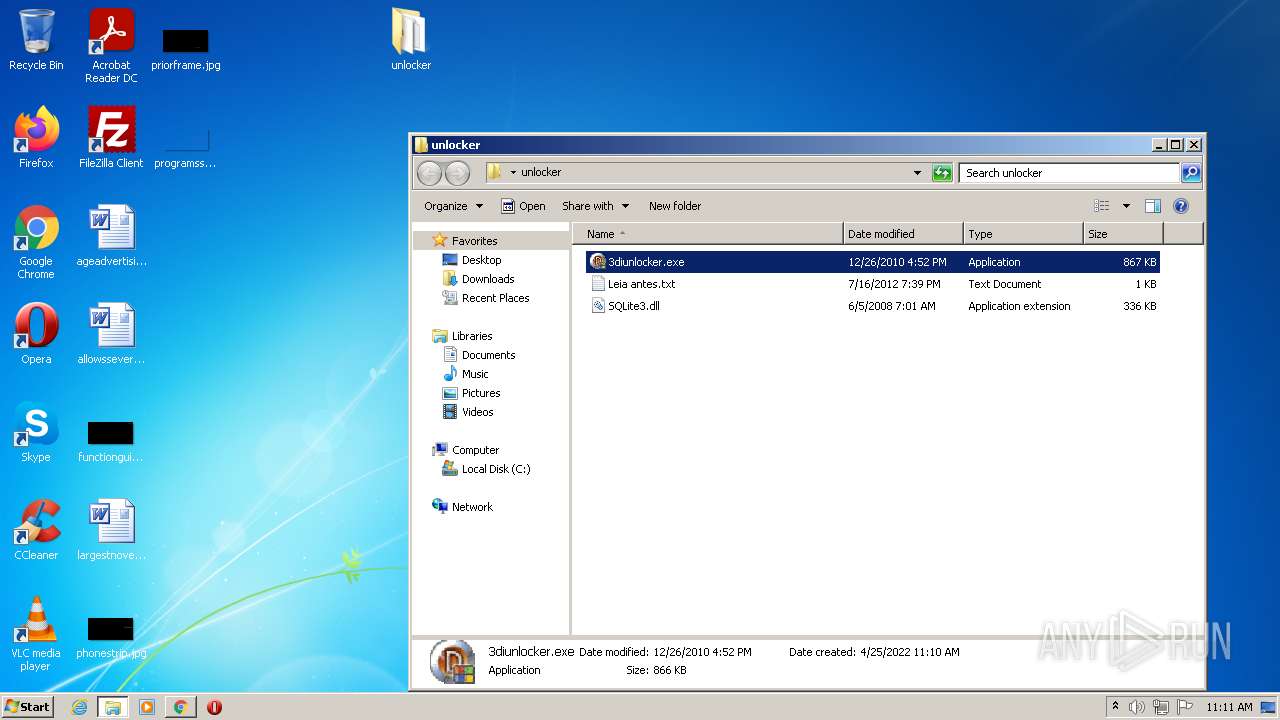
Manual execution by user
- chrome.exe (PID: 2448)
- 3diunlocker.exe (PID: 2484)
- 3diunlocker.exe (PID: 3972)
Reads the computer name
- iexplore.exe (PID: 2604)
- iexplore.exe (PID: 1988)
- chrome.exe (PID: 2988)
- chrome.exe (PID: 2448)
- chrome.exe (PID: 3072)
- chrome.exe (PID: 3740)
- chrome.exe (PID: 1832)
- chrome.exe (PID: 3756)
- chrome.exe (PID: 2652)
- chrome.exe (PID: 1376)
- chrome.exe (PID: 3336)
- chrome.exe (PID: 2636)
- chrome.exe (PID: 3836)
- chrome.exe (PID: 2192)
Changes internet zones settings
- iexplore.exe (PID: 2604)
Checks Windows Trust Settings
- iexplore.exe (PID: 2604)
- chrome.exe (PID: 2448)
Reads the hosts file
- chrome.exe (PID: 3072)
- chrome.exe (PID: 2448)
Reads the date of Windows installation
- iexplore.exe (PID: 2604)
- chrome.exe (PID: 3836)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
96
Monitored processes
60
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=996,11353002554443945829,12316075080992226633,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3012 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,11353002554443945829,12316075080992226633,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=32 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4800 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=996,11353002554443945829,12316075080992226633,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2956 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,11353002554443945829,12316075080992226633,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2340 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --field-trial-handle=996,11353002554443945829,12316075080992226633,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=5088 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=996,11353002554443945829,12316075080992226633,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=4176 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,11353002554443945829,12316075080992226633,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=49 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4340 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1640 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=996,11353002554443945829,12316075080992226633,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2992 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1656 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,11353002554443945829,12316075080992226633,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=33 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4868 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,11353002554443945829,12316075080992226633,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2056 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
37 728
Read events
37 365
Write events
358
Delete events
5
Modification events
| (PID) Process: | (2604) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2604) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2604) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30955660 | |||
| (PID) Process: | (2604) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2604) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30955660 | |||
| (PID) Process: | (2604) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2604) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2604) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2604) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2604) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
6
Suspicious files
223
Text files
145
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-62667380-990.pma | — | |
MD5:— | SHA256:— | |||
| 2604 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\2c1a2973-c47c-4516-96fb-393a046af700.tmp | text | |
MD5:— | SHA256:— | |||
| 3072 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\index | binary | |
MD5:— | SHA256:— | |||
| 2448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 2604 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 2448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF1063dc.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 2448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 2448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF1063ad.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 2428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
185
DNS requests
123
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3072 | chrome.exe | GET | 301 | 142.250.184.238:80 | http://translate.google.com/translate_a/element.js?cb=googFooterTranslate | US | — | — | whitelisted |
3072 | chrome.exe | GET | 200 | 104.17.167.186:80 | http://6.adsco.re/ | US | — | — | whitelisted |
3072 | chrome.exe | GET | 302 | 142.250.185.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 554 b | whitelisted |
2604 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3072 | chrome.exe | GET | 200 | 8.248.139.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?bedab0ab33b8a871 | US | compressed | 59.5 Kb | whitelisted |
3072 | chrome.exe | GET | 200 | 104.16.203.237:80 | http://www.mediafire.com/file/s9b5xg87f85e492/unlocker.rar/file | US | html | 84.0 Kb | shared |
3072 | chrome.exe | GET | 200 | 104.16.203.237:80 | http://www.mediafire.com/js/prebid5.17.0.js | US | text | 78.0 Kb | shared |
3072 | chrome.exe | GET | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | text | 37 b | whitelisted |
3072 | chrome.exe | GET | 200 | 104.16.202.237:80 | http://static.mediafire.com/images/filetype/file-zip-v3.png | US | image | 1.83 Kb | shared |
2604 | iexplore.exe | GET | 200 | 8.248.139.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?119636c2c31f8bf1 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2604 | iexplore.exe | 131.253.33.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1988 | iexplore.exe | 104.16.202.237:80 | www.mediafire.com | Cloudflare Inc | US | unknown |
2604 | iexplore.exe | 8.248.139.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
2604 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3072 | chrome.exe | 142.250.184.237:443 | accounts.google.com | Google Inc. | US | suspicious |
3072 | chrome.exe | 142.250.181.238:443 | clients2.google.com | Google Inc. | US | whitelisted |
3072 | chrome.exe | 142.250.74.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3072 | chrome.exe | 142.250.181.228:443 | www.google.com | Google Inc. | US | whitelisted |
3072 | chrome.exe | 142.250.185.129:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3072 | chrome.exe | 142.250.184.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.mediafire.com |
| shared |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
www.google.com |
| malicious |
accounts.google.com |
| shared |
clients2.googleusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3072 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
3072 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |