| File name: | unionreturns.rtf.exe |
| Full analysis: | https://app.any.run/tasks/1321a3f5-2389-482e-a4d2-e82b9611603d |
| Verdict: | Malicious activity |
| Analysis date: | December 02, 2023, 21:26:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 4C2ED6148F7E4787FD8D1017BD81CC11 |
| SHA1: | 6ACF9A455C5CABE93D4AA625E7B70BC42200A533 |
| SHA256: | B73C950CCC87F4C49A9A5AC1B5E28936B07F40CEF46CFAC60C0ED43D15F2D994 |
| SSDEEP: | 24576:1oFbrcrnIxMfzcayo389j1GwZlZ/Zvi4z/v6HsEnWeonu2NAz1tsliem9B:1oFbrcrnIxMfzcayo389j1GwZlZ/ZviL |
MALICIOUS
Changes appearance of the Explorer extensions
- unionreturns.rtf.exe (PID: 124)
REVENGERAT has been detected (YARA)
- admtools.exe (PID: 3676)
Drops the executable file immediately after the start
- devenv.exe (PID: 2184)
- unionreturns.rtf.exe (PID: 124)
SUSPICIOUS
Reads the Internet Settings
- unionreturns.rtf.exe (PID: 124)
- devenv.exe (PID: 2184)
Connects to unusual port
- admtools.exe (PID: 3676)
INFO
Reads the computer name
- unionreturns.rtf.exe (PID: 124)
- admtools.exe (PID: 3676)
- devenv.exe (PID: 2184)
Checks supported languages
- unionreturns.rtf.exe (PID: 124)
- devenv.exe (PID: 2184)
- admtools.exe (PID: 3676)
Reads the machine GUID from the registry
- unionreturns.rtf.exe (PID: 124)
- devenv.exe (PID: 2184)
- admtools.exe (PID: 3676)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (62) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.5) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Win16/32 Executable Delphi generic (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2105:05:31 07:12:31+02:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 80 |
| CodeSize: | 558080 |
| InitializedDataSize: | 117248 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x8a2ce |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.2.51.0 |
| ProductVersionNumber: | 4.2.51.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 4.2.51.0 |
| InternalName: | -.exe |
| LegalCopyright: | © Microsoft Corporation |
| LegalTrademarks: | - |
| OriginalFileName: | -.exe |
| ProductName: | - |
| ProductVersion: | 4.2.51.0 |
| AssemblyVersion: | 4.2.51.0 |
Total processes
45
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
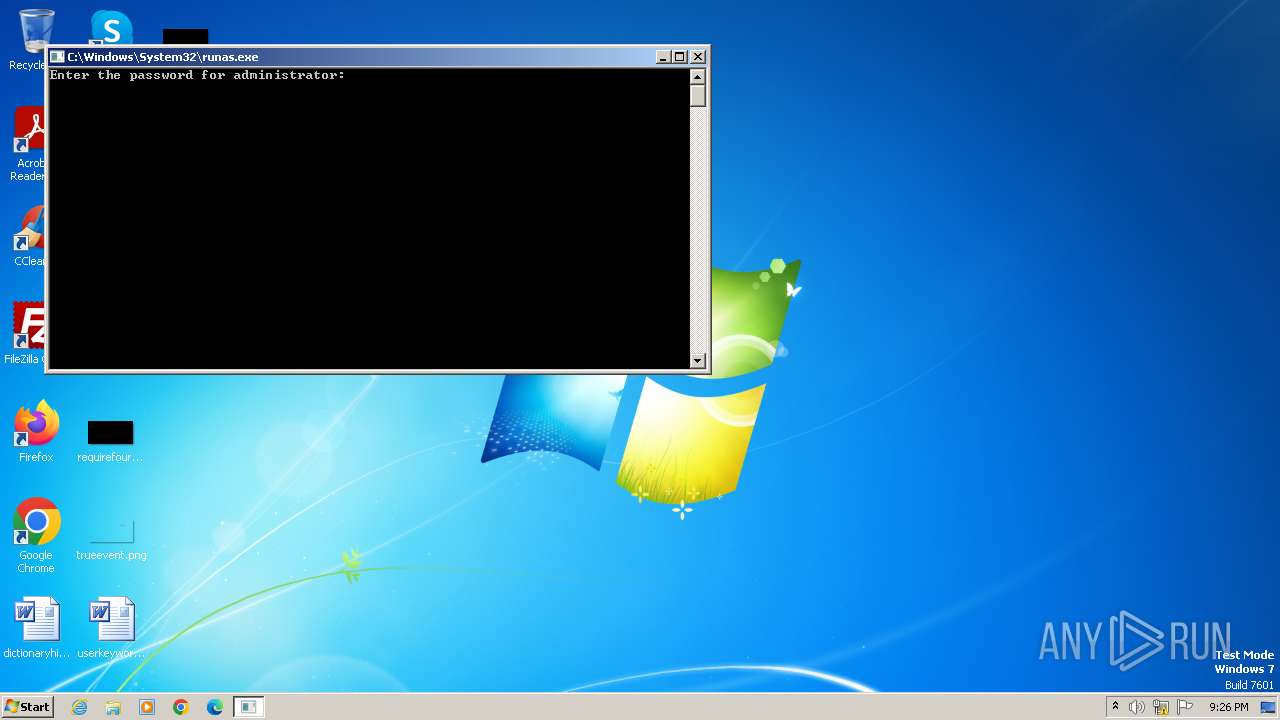
| 124 | C:\Users\admin\Desktop\unionreturns.rtf.exe | C:\Users\admin\Desktop\unionreturns.rtf.exe | runas.exe | ||||||||||||
User: Administrator Integrity Level: HIGH Exit code: 0 Version: 4.2.51.0 Modules
| |||||||||||||||
| 2184 | "C:\Users\Public\Documents\devenv.exe" | C:\Users\Public\Documents\devenv.exe | — | unionreturns.rtf.exe | |||||||||||
User: Administrator Integrity Level: HIGH Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 2644 | "C:\Windows\System32\runas.exe" /user:administrator C:\Users\admin\Desktop\unionreturns.rtf.exe | C:\Windows\System32\runas.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Run As Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3676 | "C:\Users\Public\Documents\admtools.exe" | C:\Users\Public\Documents\admtools.exe | unionreturns.rtf.exe | ||||||||||||
User: Administrator Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
1 830
Read events
1 814
Write events
14
Delete events
2
Modification events
| (PID) Process: | (124) unionreturns.rtf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | delete value | Name: | ProxyBypass |
Value: 0 | |||
| (PID) Process: | (124) unionreturns.rtf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | delete value | Name: | IntranetName |
Value: 0 | |||
| (PID) Process: | (124) unionreturns.rtf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (124) unionreturns.rtf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (124) unionreturns.rtf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced |
| Operation: | write | Name: | Hidden |
Value: 2 | |||
| (PID) Process: | (124) unionreturns.rtf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced |
| Operation: | write | Name: | HideFileExt |
Value: 1 | |||
| (PID) Process: | (2184) devenv.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2184) devenv.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2184) devenv.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2184) devenv.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
844
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 124 | unionreturns.rtf.exe | C:\RCX7874.tmp | executable | |
MD5:4EEDC4536048ABEB736AE6AB020B4743 | SHA256:34A1A5366023F397416DC562BBE25723E39FF36540364E7A454DF38ED0EE8047 | |||
| 124 | unionreturns.rtf.exe | C:\RCX78F4.tmp | executable | |
MD5:E4C2D7117EF556AAD5B57E9D91D02524 | SHA256:2F1733A517FF45EC0E11F64835727241CAD3B495875A224383140E4AF8BDE319 | |||
| 124 | unionreturns.rtf.exe | C:\RCX77B5.tmp | executable | |
MD5:9623330DF18B3F8514F29CC79EF72EA0 | SHA256:FCD22C1C7245F6D5C77C0B595A9C613FE6722064078EF41F9135E27A826A92EE | |||
| 124 | unionreturns.rtf.exe | C:\Users\Administrator\ntuser.dat.LOG1.exe | executable | |
MD5:4C2ED6148F7E4787FD8D1017BD81CC11 | SHA256:B73C950CCC87F4C49A9A5AC1B5E28936B07F40CEF46CFAC60C0ED43D15F2D994 | |||
| 124 | unionreturns.rtf.exe | C:\Users\Administrator\ntuser.dat.LOG2.exe | executable | |
MD5:4C2ED6148F7E4787FD8D1017BD81CC11 | SHA256:B73C950CCC87F4C49A9A5AC1B5E28936B07F40CEF46CFAC60C0ED43D15F2D994 | |||
| 124 | unionreturns.rtf.exe | C:\RCX7894.tmp | executable | |
MD5:F2F2067064CCB40B93BCBABD0AA3059E | SHA256:29811DC066C655E669FCFED88B8F8E370D3C4A1E86D196F39AD40B5E33008EAC | |||
| 124 | unionreturns.rtf.exe | C:\RCX78D4.tmp | executable | |
MD5:4C2ED6148F7E4787FD8D1017BD81CC11 | SHA256:B73C950CCC87F4C49A9A5AC1B5E28936B07F40CEF46CFAC60C0ED43D15F2D994 | |||
| 124 | unionreturns.rtf.exe | C:\Users\Public\Documents\devenv.exe | executable | |
MD5:3FE2B1337F824DFCBF545CCFFB5454F3 | SHA256:001D3941132DD30110E1A650ABBC4DD49D352F06D08D491A4F6503ACFF875E67 | |||
| 2184 | devenv.exe | C:\Users\Public\Documents\p2p.dll | executable | |
MD5:6CFFF9C292A1BB84D395AF36A514B969 | SHA256:A3967A0CC27A52334C159387BE84DBA99EC5F5F2978260F6B1E3AFA648A060DB | |||
| 124 | unionreturns.rtf.exe | C:\Users\Public\Documents\admtools.exe | executable | |
MD5:86CA40FFE87618AD86BD49E5A9B6DA69 | SHA256:9BD3D486E541B5C7E9EEC713B6162FAF97B21C0CF61A56A996F838A6F4F0BE59 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
7
DNS requests
3
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3676 | admtools.exe | 45.84.227.157:50 | pex.0x01.cf | Beget LLC | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pex.0x01.cf |
| unknown |
api.peer2profit.com |
| unknown |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Misc activity | ET INFO DNS Query for Suspicious .cf Domain |