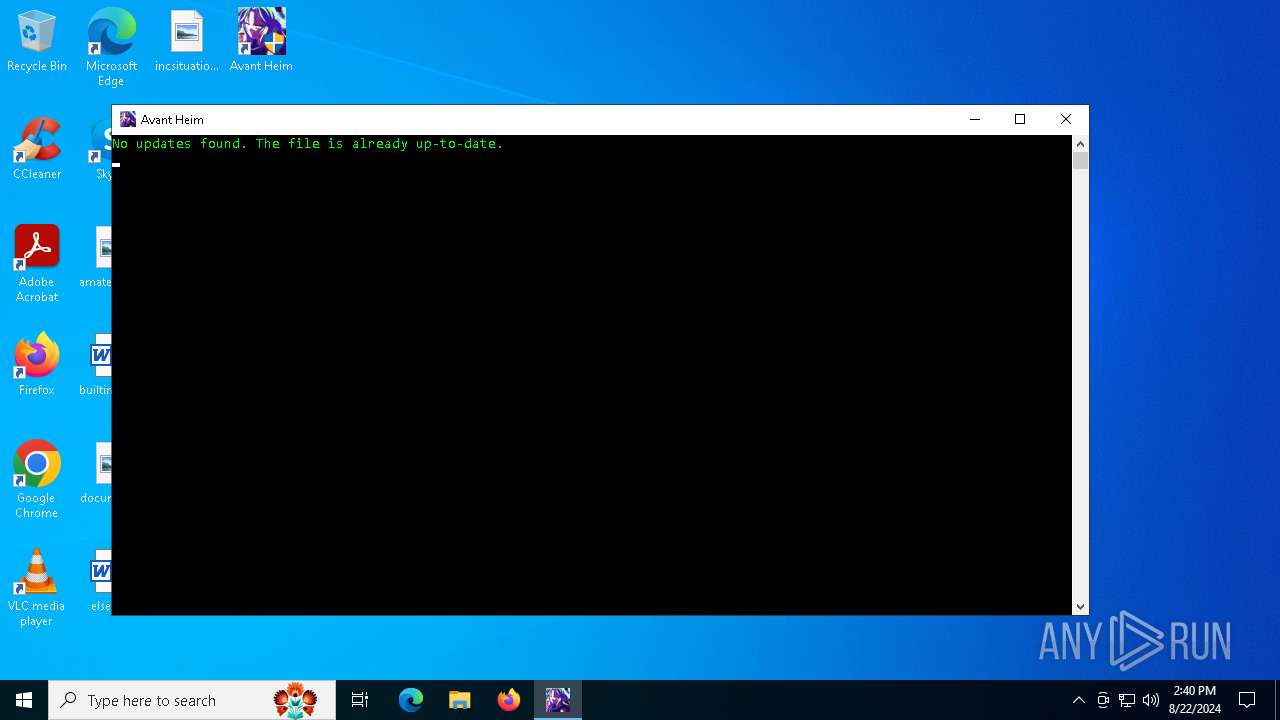
| File name: | Avant Heim.exe |
| Full analysis: | https://app.any.run/tasks/99de320f-cff2-496b-9a45-cb5ee4a6d268 |
| Verdict: | Malicious activity |
| Analysis date: | August 22, 2024, 14:38:36 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, RAR self-extracting archive |
| MD5: | 1B443253B83A46738846633D6B2B285B |
| SHA1: | A5F9F3AAB8C71CDE80A1D925738CF341CF05DE10 |
| SHA256: | B72DDB642160CF1276C9FD92D9C6ED1CF8FF823CAE09E86AD1C2500876EDF715 |
| SSDEEP: | 98304:gjPc/0cnmesVKHtrQCkUz113KUopAMB+S1GQp8lkW1UL9rsAVMm5cc0+ghlgn2pO:7HXp/o2E |
MALICIOUS
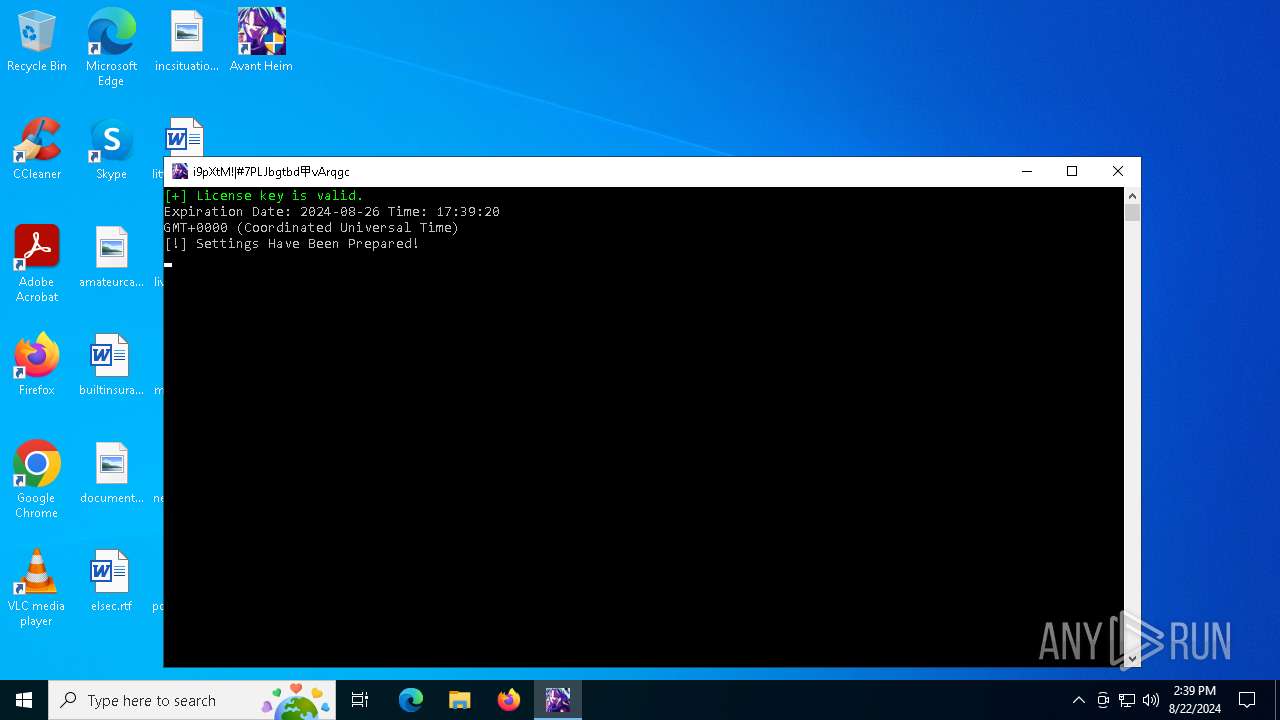
PHISHING has been detected (SURICATA)
- Avant Heim Hax.exe (PID: 6168)
- Avant Heim Hax.exe (PID: 3960)
XORed URL has been found (YARA)
- Avant Heim Hax.exe (PID: 6168)
SUSPICIOUS
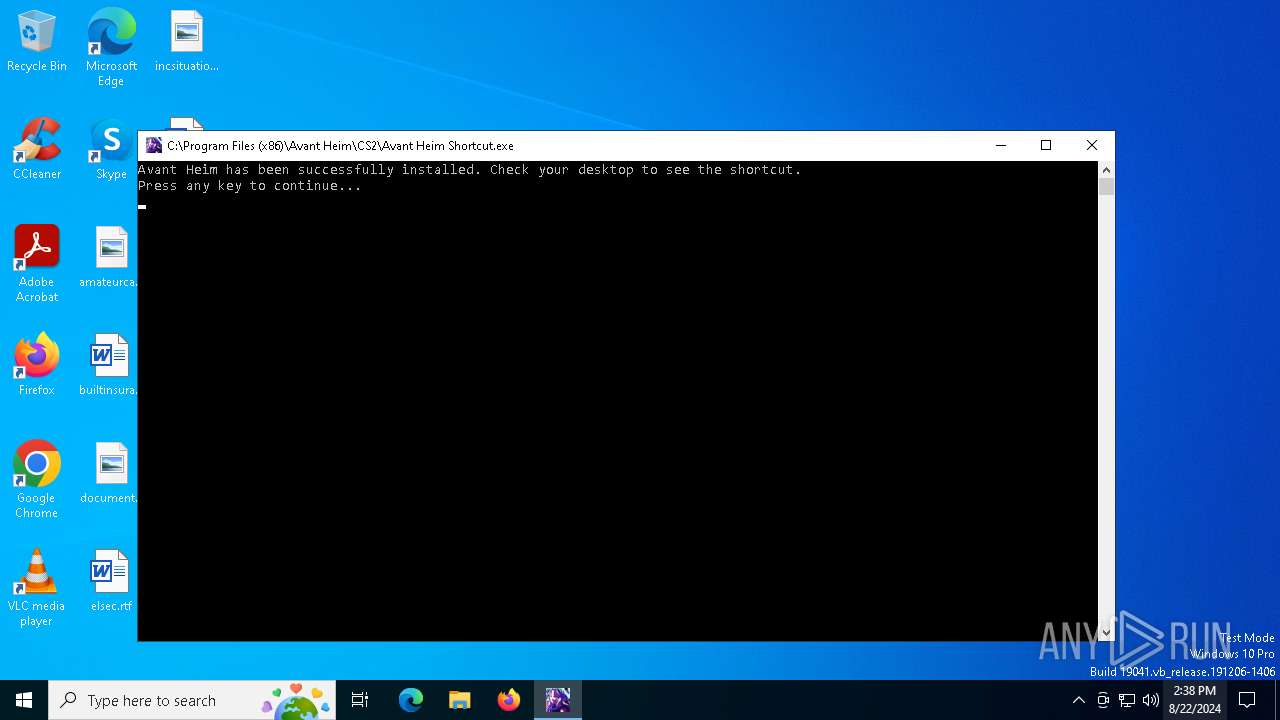
Drops the executable file immediately after the start
- Avant Heim.exe (PID: 6796)
- kdu.exe (PID: 5276)
- Avant Heim Hax.exe (PID: 3960)
Reads security settings of Internet Explorer
- Avant Heim.exe (PID: 6796)
Reads the date of Windows installation
- Avant Heim.exe (PID: 6796)
Executable content was dropped or overwritten
- Avant Heim.exe (PID: 6796)
- Avant Heim Hax.exe (PID: 3960)
- kdu.exe (PID: 5276)
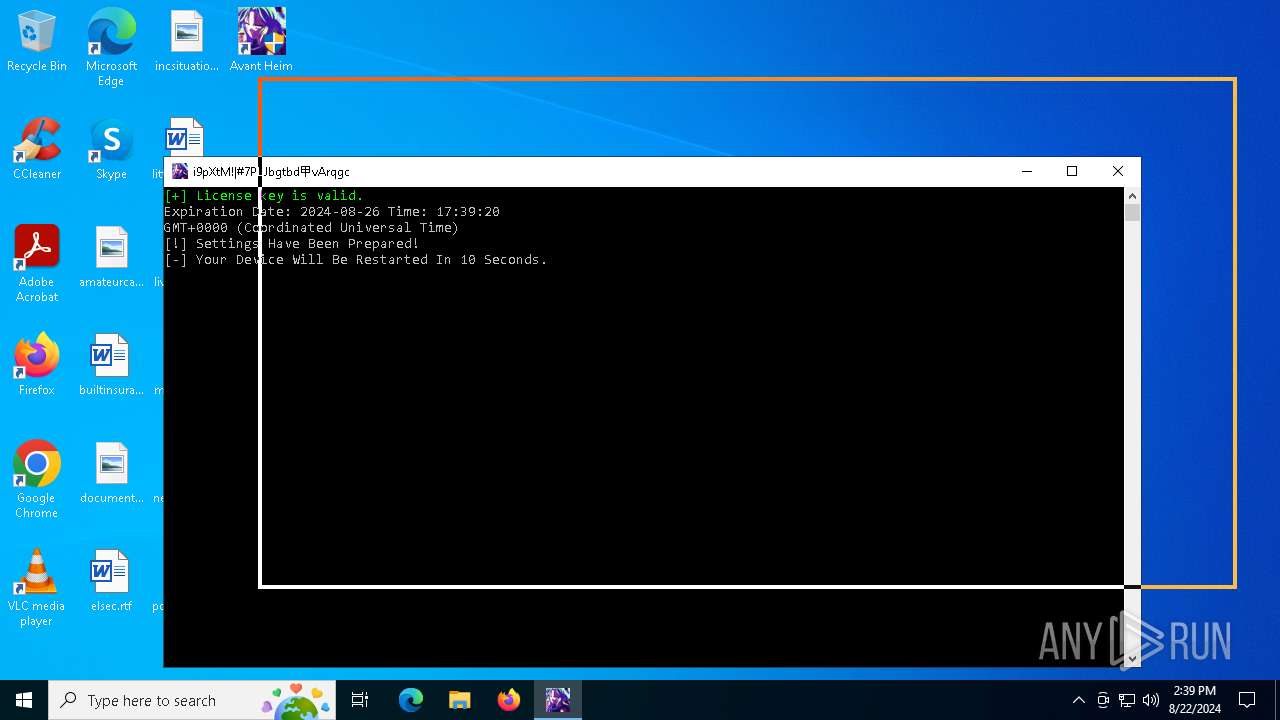
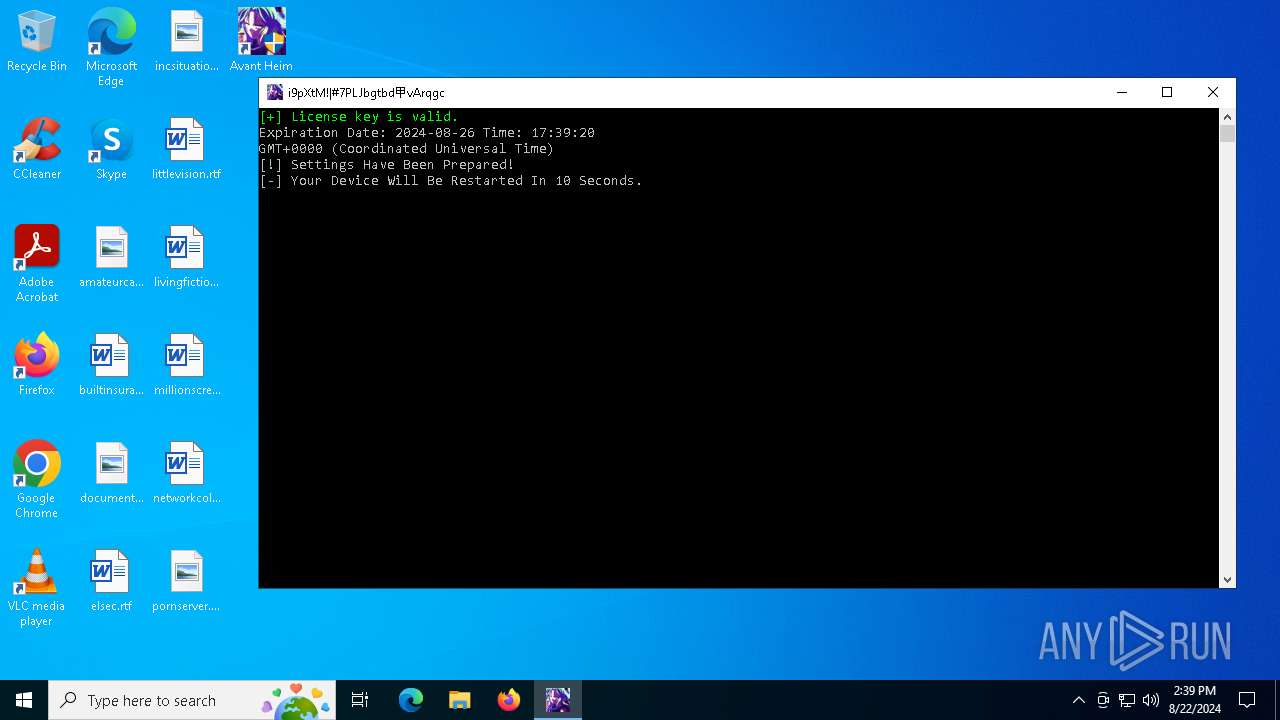
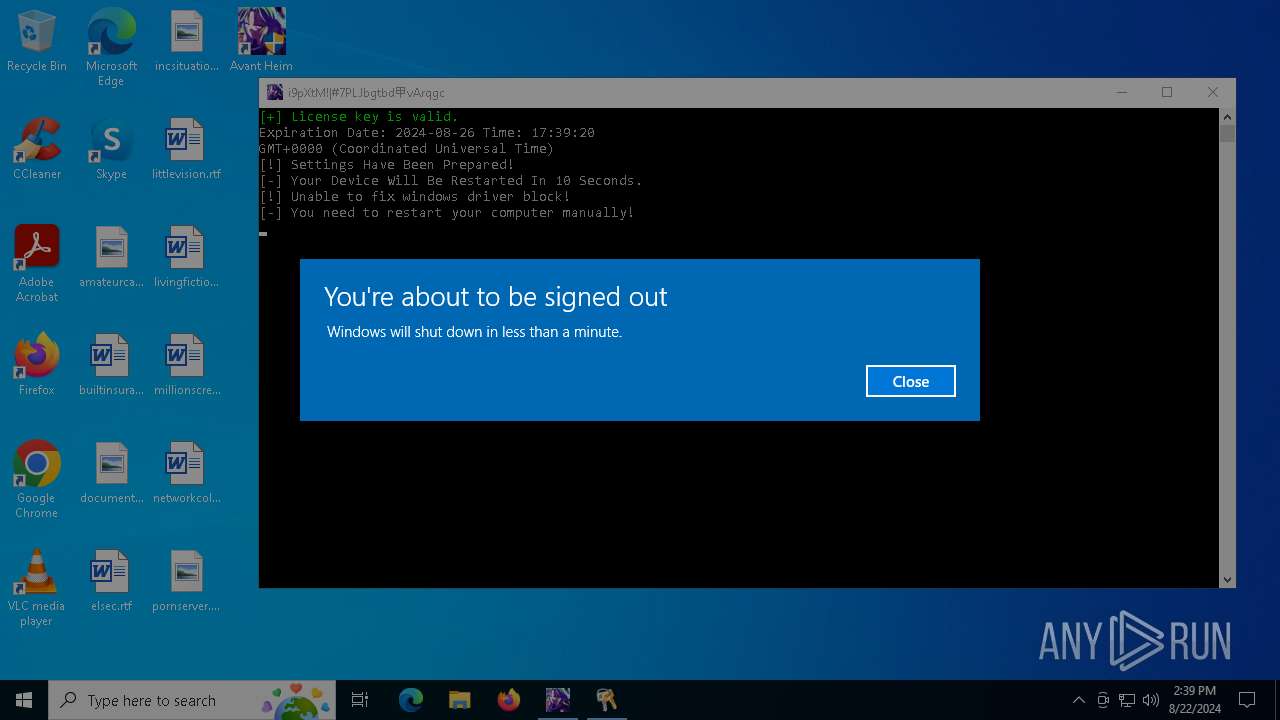
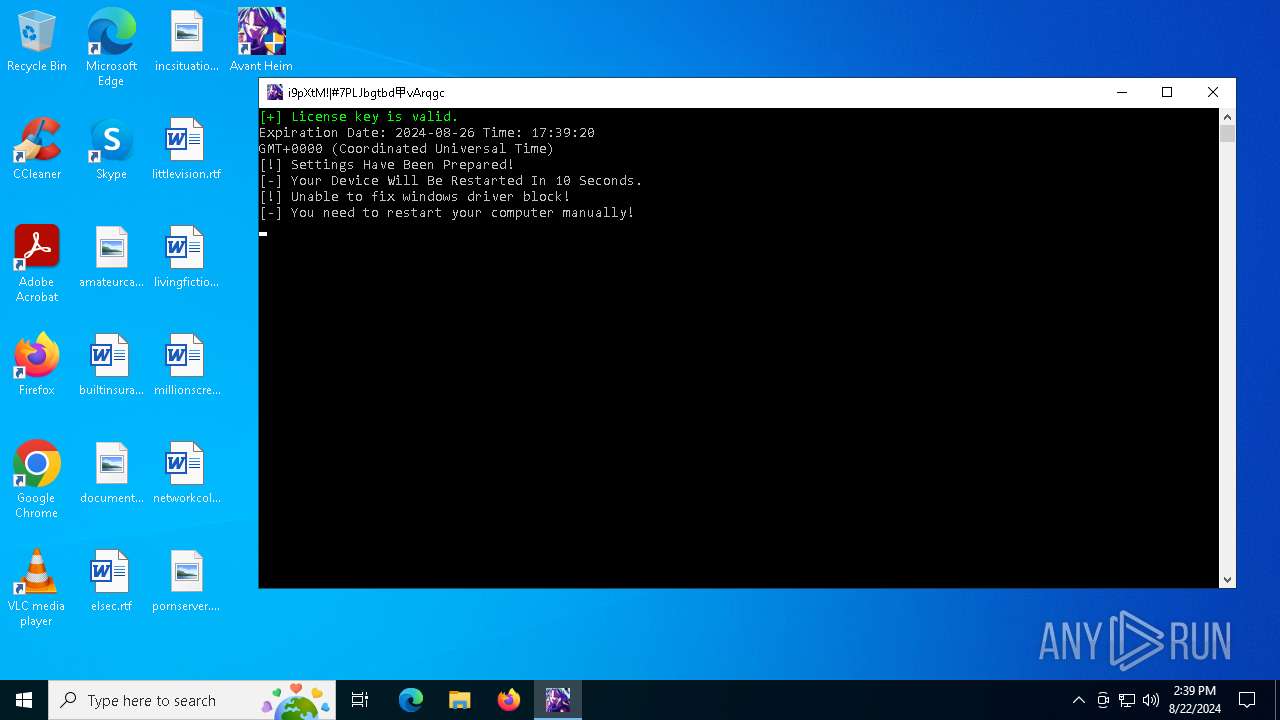
Starts CMD.EXE for commands execution
- Avant Heim Hax.exe (PID: 6168)
- Avant Heim Hax.exe (PID: 3960)
The system shut down or reboot
- cmd.exe (PID: 3208)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 884)
Creates or modifies Windows services
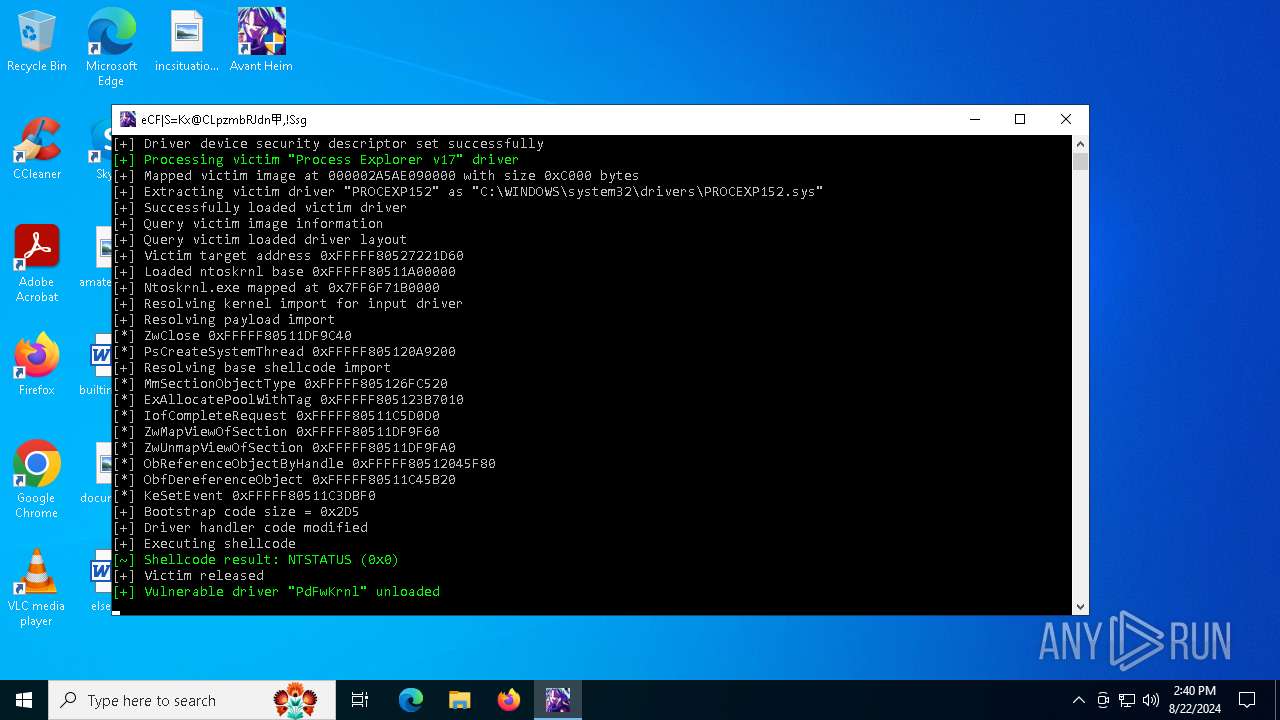
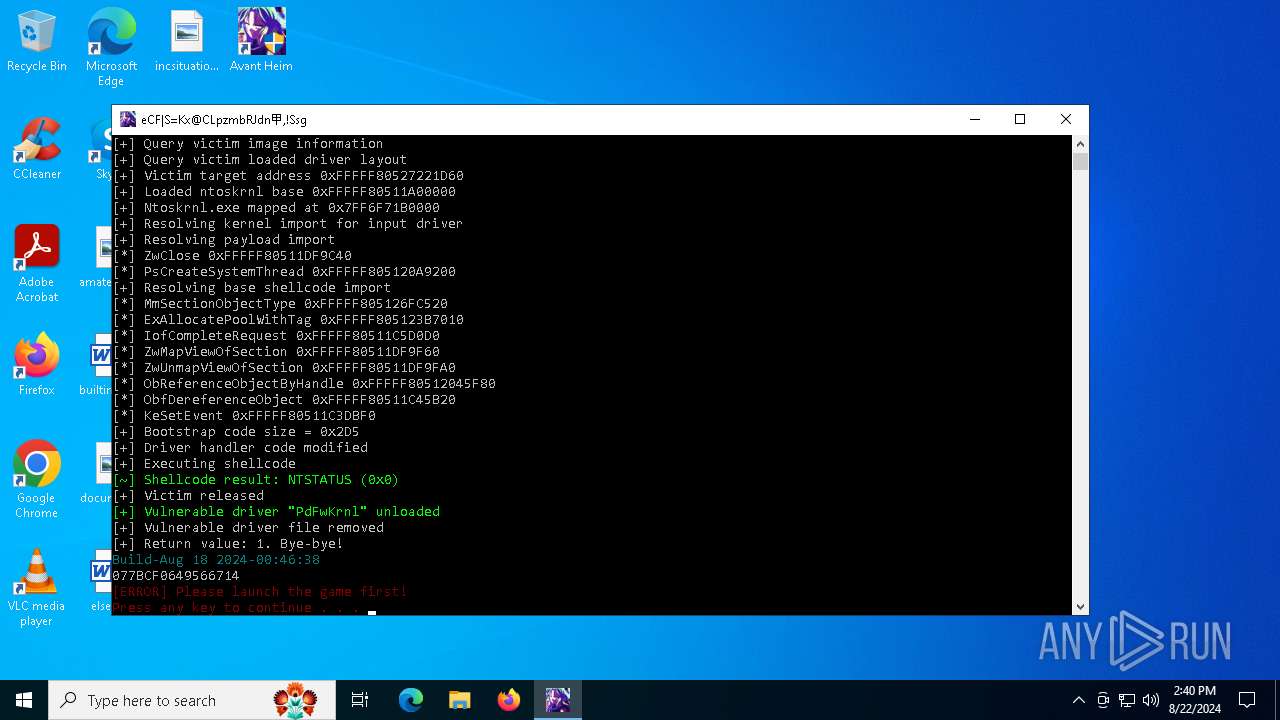
- kdu.exe (PID: 5276)
Drops a system driver (possible attempt to evade defenses)
- kdu.exe (PID: 5276)
- Avant Heim Hax.exe (PID: 3960)
Creates files in the driver directory
- kdu.exe (PID: 5276)
Checks for external IP
- Avant Heim Hax.exe (PID: 3960)
- Avant Heim Hax.exe (PID: 6168)
INFO
Reads the computer name
- Avant Heim.exe (PID: 6796)
- Avant Heim Shortcut.exe (PID: 7092)
- Avant Heim Hax.exe (PID: 6168)
- PLUGScheduler.exe (PID: 884)
- Avant Heim Hax.exe (PID: 3960)
Creates files in the program directory
- Avant Heim.exe (PID: 6796)
- Avant Heim Hax.exe (PID: 6168)
- PLUGScheduler.exe (PID: 884)
- Avant Heim Hax.exe (PID: 3960)
- kdu.exe (PID: 5276)
Checks supported languages
- Avant Heim Shortcut.exe (PID: 7092)
- Avant Heim.exe (PID: 6796)
- Avant Heim Hax.exe (PID: 6168)
- PLUGScheduler.exe (PID: 884)
- Avant Heim Hax.exe (PID: 3960)
- kdu.exe (PID: 5276)
Dropped object may contain TOR URL's
- Avant Heim.exe (PID: 6796)
Process checks computer location settings
- Avant Heim.exe (PID: 6796)
- Avant Heim Hax.exe (PID: 6168)
- Avant Heim Hax.exe (PID: 3960)
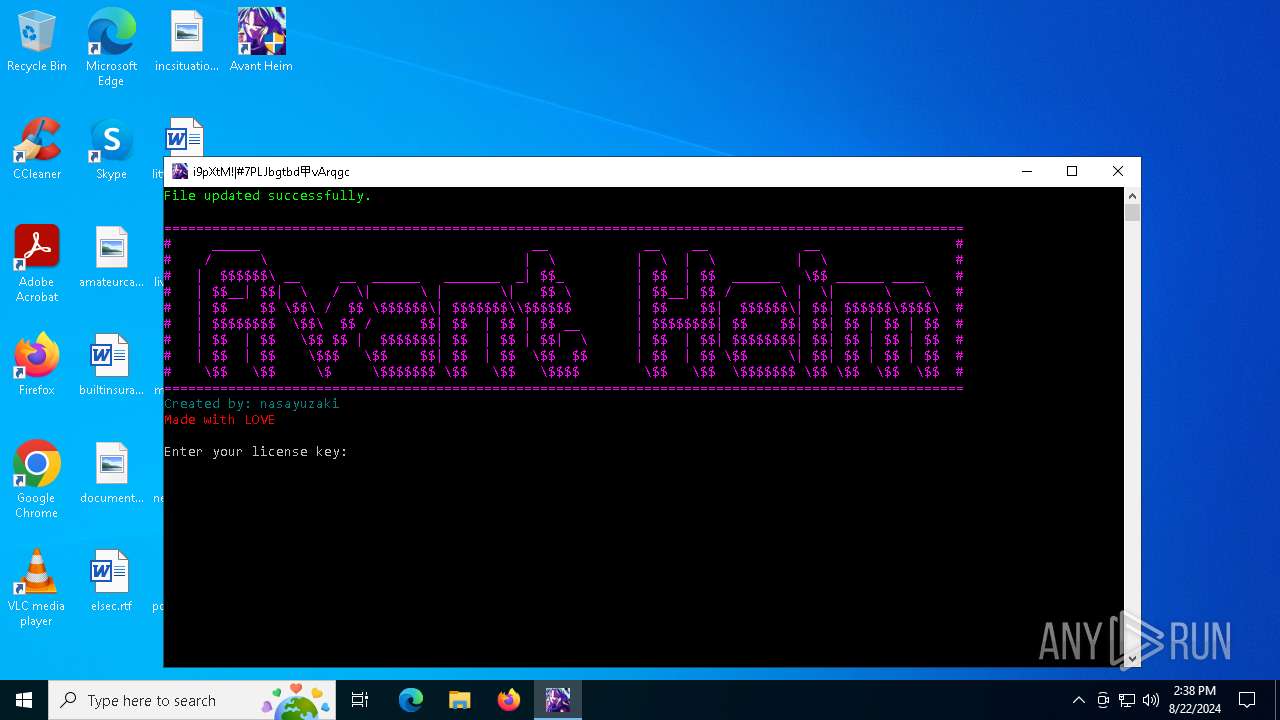
Manual execution by a user
- Avant Heim Hax.exe (PID: 4672)
- Avant Heim Hax.exe (PID: 6168)
- Avant Heim Hax.exe (PID: 5000)
- Avant Heim Hax.exe (PID: 3960)
Attempting to use instant messaging service
- Avant Heim Hax.exe (PID: 6168)
- Avant Heim Hax.exe (PID: 3960)
Reads the machine GUID from the registry
- kdu.exe (PID: 5276)
UPX packer has been detected
- Avant Heim Hax.exe (PID: 6168)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
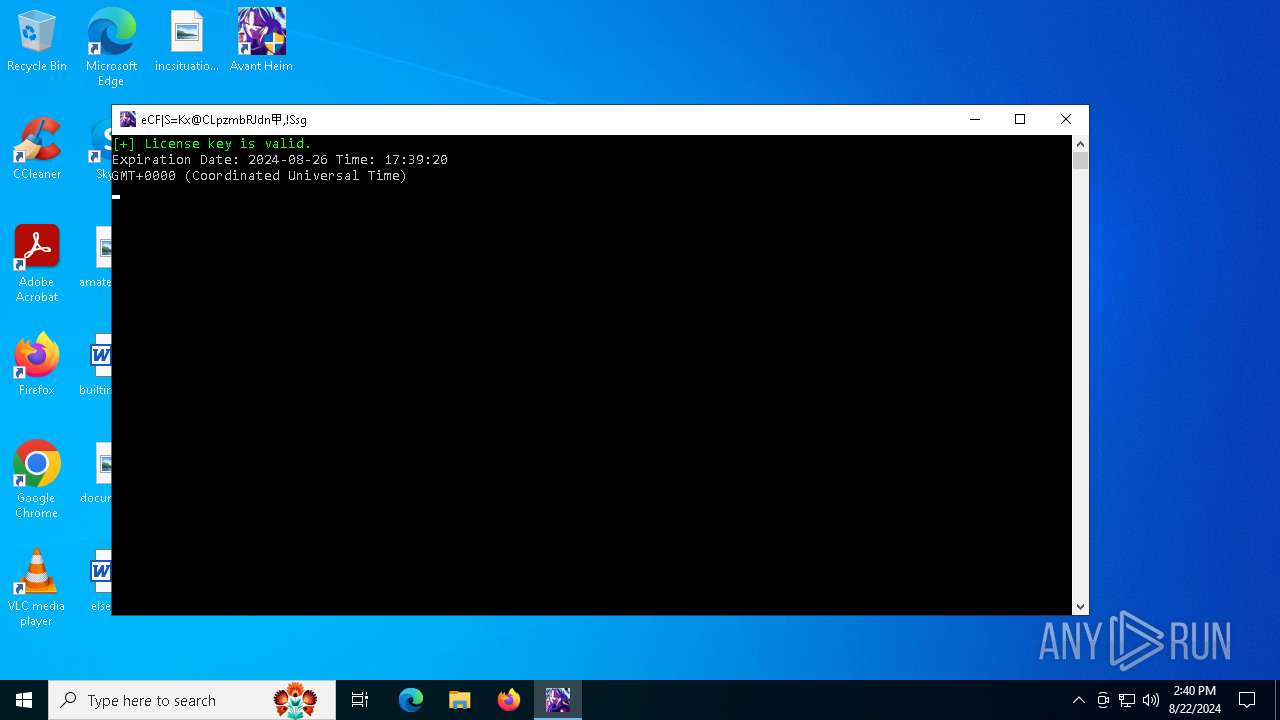
xor-url
(PID) Process(6168) Avant Heim Hax.exe
Decrypted-URLs (2)https://www.bilibili.com/video/D
https://www.gov.cn/guoqing/2023
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:12:01 08:08:23+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 153088 |
| InitializedDataSize: | 524800 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1d728 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Total processes
289
Monitored processes
19
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 884 | "C:\Program Files\RUXIM\PLUGscheduler.exe" | C:\Program Files\RUXIM\PLUGScheduler.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Update LifeCycle Component Scheduler Exit code: 0 Version: 10.0.19041.3623 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1748 | shutdown /r | C:\Windows\System32\shutdown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Shutdown and Annotation Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3208 | C:\WINDOWS\system32\cmd.exe /c shutdown /r | C:\Windows\System32\cmd.exe | — | Avant Heim Hax.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3960 | "C:\Program Files (x86)\Avant Heim\CS2\Avant Heim Hax.exe" | C:\Program Files (x86)\Avant Heim\CS2\Avant Heim Hax.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 4016 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Avant Heim Hax.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4672 | "C:\Program Files (x86)\Avant Heim\CS2\Avant Heim Hax.exe" | C:\Program Files (x86)\Avant Heim\CS2\Avant Heim Hax.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 4680 | C:\WINDOWS\system32\cmd.exe /c cls | C:\Windows\System32\cmd.exe | — | Avant Heim Hax.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5000 | "C:\Program Files (x86)\Avant Heim\CS2\Avant Heim Hax.exe" | C:\Program Files (x86)\Avant Heim\CS2\Avant Heim Hax.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 5276 | C:\WINDOWS\system32\cmd.exe /c cls | C:\Windows\System32\cmd.exe | — | Avant Heim Hax.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5276 | kdu -prv 44 -map AHDriver.sys | C:\Program Files (x86)\Avant Heim\CS2\kdu.exe | cmd.exe | ||||||||||||
User: admin Company: UG North Integrity Level: HIGH Description: Kernel Driver Utility Exit code: 1 Version: 1.4.1.2312 Modules
| |||||||||||||||
Total events
4 037
Read events
4 007
Write events
28
Delete events
2
Modification events
| (PID) Process: | (6796) Avant Heim.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR SFX |
| Operation: | write | Name: | C%%Program Files (x86)%Avant Heim%CS2 |
Value: C:\Program Files (x86)\Avant Heim\CS2 | |||
| (PID) Process: | (6796) Avant Heim.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6796) Avant Heim.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6796) Avant Heim.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6796) Avant Heim.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6168) Avant Heim Hax.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\DeviceGuard |
| Operation: | write | Name: | RequireMicrosoftSignedBootChain |
Value: 0 | |||
| (PID) Process: | (6168) Avant Heim Hax.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\DeviceGuard\Scenarios |
| Operation: | write | Name: | HypervisorEnforcedCodeIntegrity |
Value: 0 | |||
| (PID) Process: | (3960) Avant Heim Hax.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\DeviceGuard\Scenarios |
| Operation: | write | Name: | HypervisorEnforcedCodeIntegrity |
Value: 0 | |||
| (PID) Process: | (5276) kdu.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\PdFwKrnl |
| Operation: | write | Name: | ErrorControl |
Value: 1 | |||
| (PID) Process: | (5276) kdu.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\PdFwKrnl |
| Operation: | write | Name: | Type |
Value: 1 | |||
Executable files
9
Suspicious files
25
Text files
3
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6796 | Avant Heim.exe | C:\Program Files (x86)\Avant Heim\CS2\zlib1.dll | executable | |
MD5:3A75B6D4A3B51843EF65D8F3D44A615D | SHA256:75DF33EE57C6EB007A17E45D6F2913F29A102C9A7F744B9618087D6638B25F14 | |||
| 884 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.031.etl | etl | |
MD5:868E79A00A8204448B2FFC4F4D5C08EA | SHA256:148FE324431CB4C826BCF0436147D946AC389A877732612CF40629048B8517DC | |||
| 884 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.030.etl | etl | |
MD5:44A0E917AD0C126931B1BCD959285A9A | SHA256:DDFBE47E7DFD6D8B7517F2F6FF9808ECF3C0A25F588A9F96D04F4E2B4A578573 | |||
| 884 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.036.etl | etl | |
MD5:FA358BFEE9B4E1FFB7394D13CBBC4898 | SHA256:6FF97BBF8A56286A4C71623829514CC14B7F8CBBCF09748D939F733968478A22 | |||
| 884 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.025.etl | etl | |
MD5:FED961067F664B5381B65A534B7AB728 | SHA256:652F31A8284AE812D1D9D24192BC800976BF74C240591C6AC443A28C4709FB7C | |||
| 884 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.028.etl | etl | |
MD5:C8834D365FAE073DEDE1F1620454CE71 | SHA256:C6DD793EEE1D5551CA507A3C5BFFECA82DD3E29C63C2C6DD218A7D4BFB37046B | |||
| 884 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.027.etl | binary | |
MD5:5EA68411BF8E9EAF4621BAF73F61449E | SHA256:9D4CA5A1D871F819C139A498BB910A63576C2FE6367853544F8D172D8B6EBFF7 | |||
| 6796 | Avant Heim.exe | C:\Program Files (x86)\Avant Heim\CS2\imgui.ini | text | |
MD5:D496977E9DB4BCB7E187E73B23200BB4 | SHA256:4472DB2A16FBBE99913BE4DE722799C78E1F51B597A9017F57F92251F5A910BC | |||
| 884 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.032.etl | etl | |
MD5:2F36C598EBFF5B5CDD898C9691D6BCCB | SHA256:8900C5931ED8E0D1B68082B45CF2F4E8C1025D36825508E0804C916D781B9F50 | |||
| 884 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.026.etl | binary | |
MD5:A23907B6FDD47DCABFDFD7CF2FCD7671 | SHA256:0C9C33FE9E984A2E5A70EBA51F36B9929A86199E424AF2F8080E1267B87DC970 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
82
DNS requests
43
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
768 | lsass.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | unknown | — | — | whitelisted |
768 | lsass.exe | GET | 200 | 142.250.185.227:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
768 | lsass.exe | GET | 200 | 142.250.185.227:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
768 | lsass.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | unknown | — | — | whitelisted |
1116 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7164 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
768 | lsass.exe | GET | 200 | 142.250.185.227:80 | http://c.pki.goog/r/r1.crl | unknown | — | — | whitelisted |
768 | lsass.exe | GET | 200 | 142.250.185.227:80 | http://o.pki.goog/s/wr3/CGU/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQSq0i5t2Pafi2Gw9uzwnc7KTctWgQUx4H1%2FY6I2QA8TWOiUDEkoM4j%2FiMCEAhl9OBG7IWSCYGkdB6XM1w%3D | unknown | — | — | whitelisted |
2584 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4476 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1432 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5400 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1432 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6168 | Avant Heim Hax.exe | 185.199.111.133:443 | gist.githubusercontent.com | FASTLY | US | unknown |
768 | lsass.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
6168 | Avant Heim Hax.exe | 162.159.134.233:443 | cdn.discordapp.com | CLOUDFLARENET | — | shared |
6168 | Avant Heim Hax.exe | 172.67.74.152:443 | api.ipify.org | CLOUDFLARENET | US | unknown |
768 | lsass.exe | 142.250.185.227:80 | c.pki.goog | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
gist.githubusercontent.com |
| shared |
ocsp.digicert.com |
| whitelisted |
cdn.discordapp.com |
| shared |
api.ipify.org |
| shared |
c.pki.goog |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
arc.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
6168 | Avant Heim Hax.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
2256 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
6168 | Avant Heim Hax.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
6168 | Avant Heim Hax.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Phishing domain has been detected (replit .app) |
6168 | Avant Heim Hax.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Phishing domain has been detected (replit .app) |
3960 | Avant Heim Hax.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
2184 | svchost.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
2184 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
3960 | Avant Heim Hax.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |