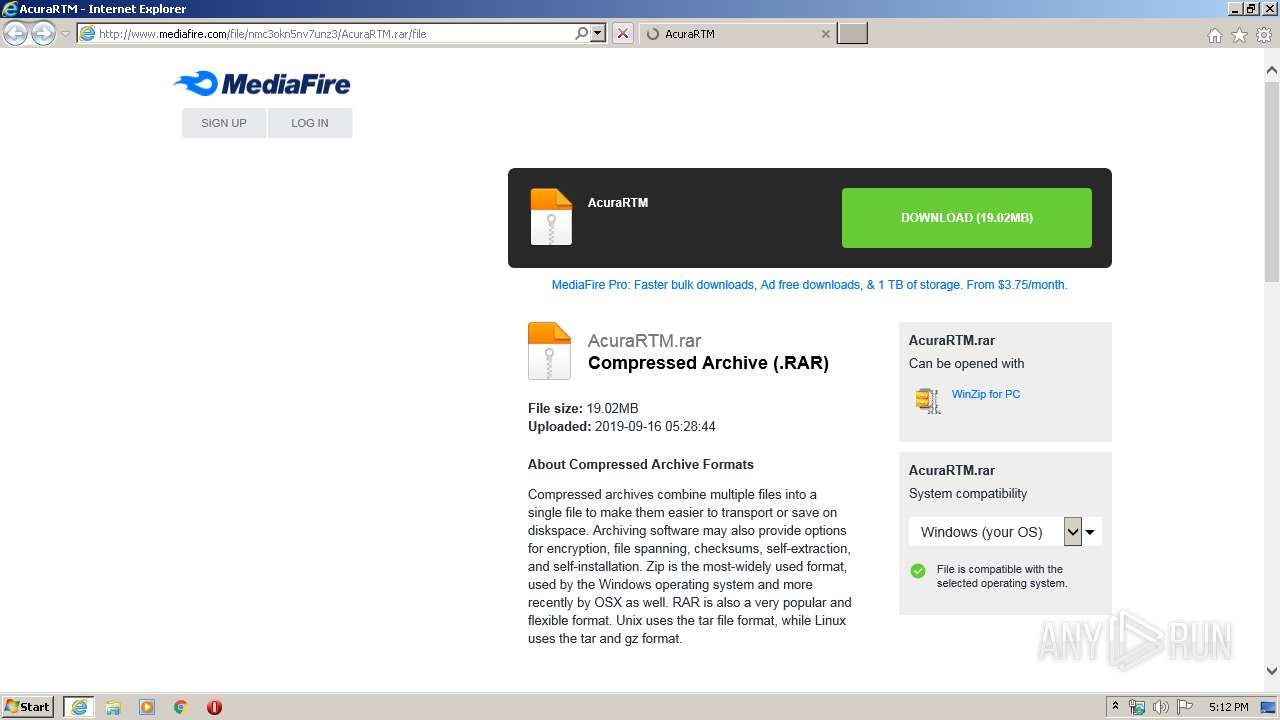
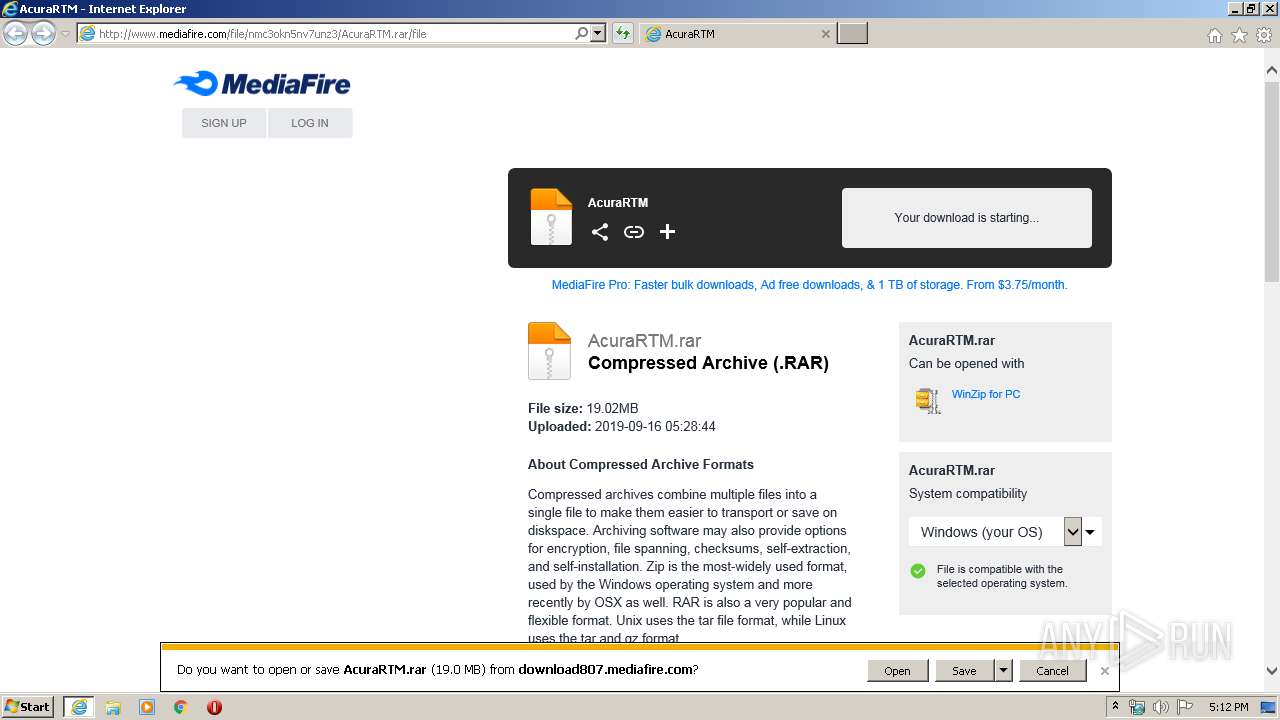
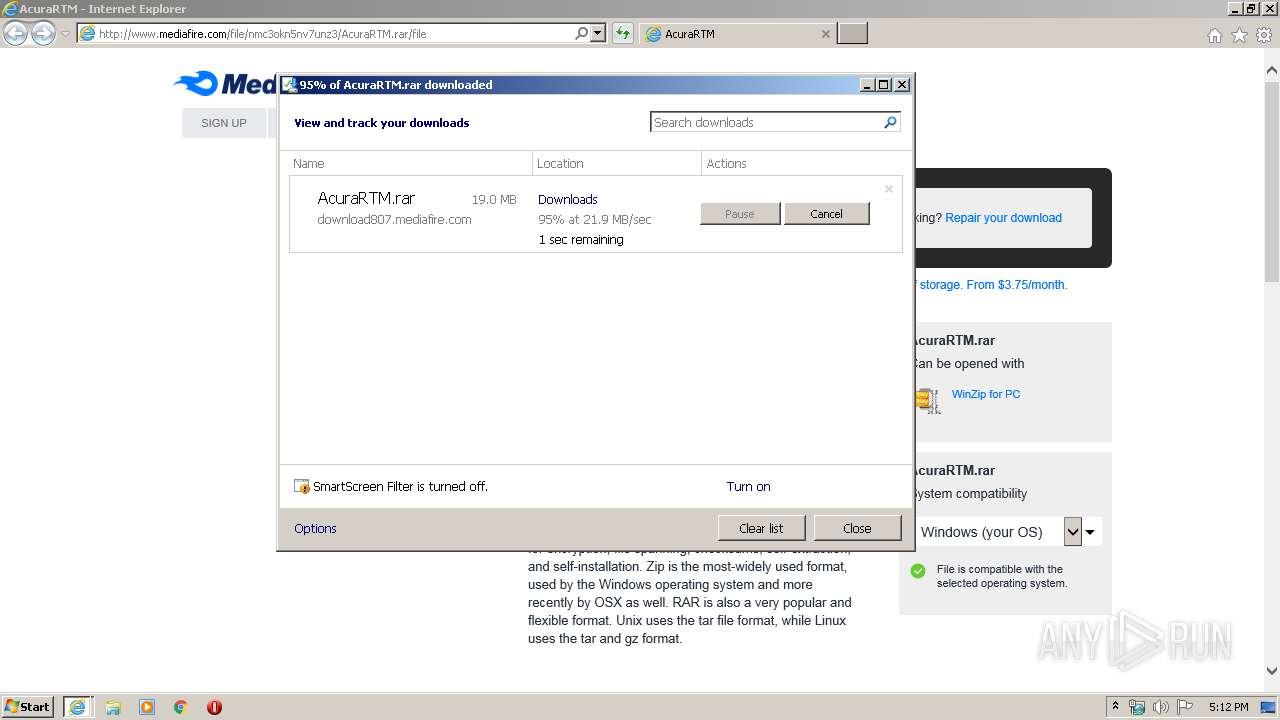
| URL: | http://www.mediafire.com/file/nmc3okn5nv7unz3/AcuraRTM.rar/file |
| Full analysis: | https://app.any.run/tasks/c65f27f4-7c6f-430a-972b-64e9865f0dc5 |
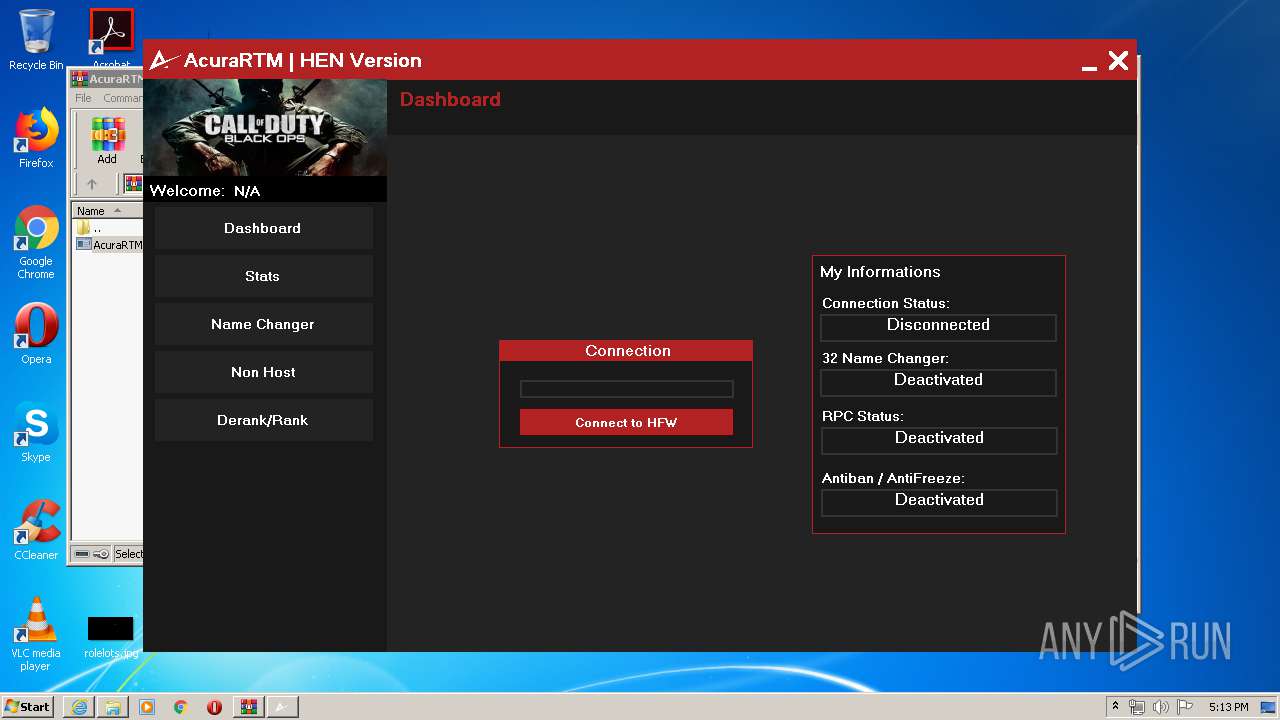
| Verdict: | Malicious activity |
| Analysis date: | February 03, 2020, 17:11:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | BF3673D3EB75B733439E768056E1509E |
| SHA1: | 61860C26DFC90C430EBD126FDD5B570DE288CABB |
| SHA256: | B723C01589C26FD894DE5FC34DA38B82940A928D25D5DA7C391134D76FE3296E |
| SSDEEP: | 3:N1KJS4w3eGUoGKOkjJk3njEXYIA:Cc4w3eGaVklk3nj+fA |
MALICIOUS
No malicious indicators.SUSPICIOUS
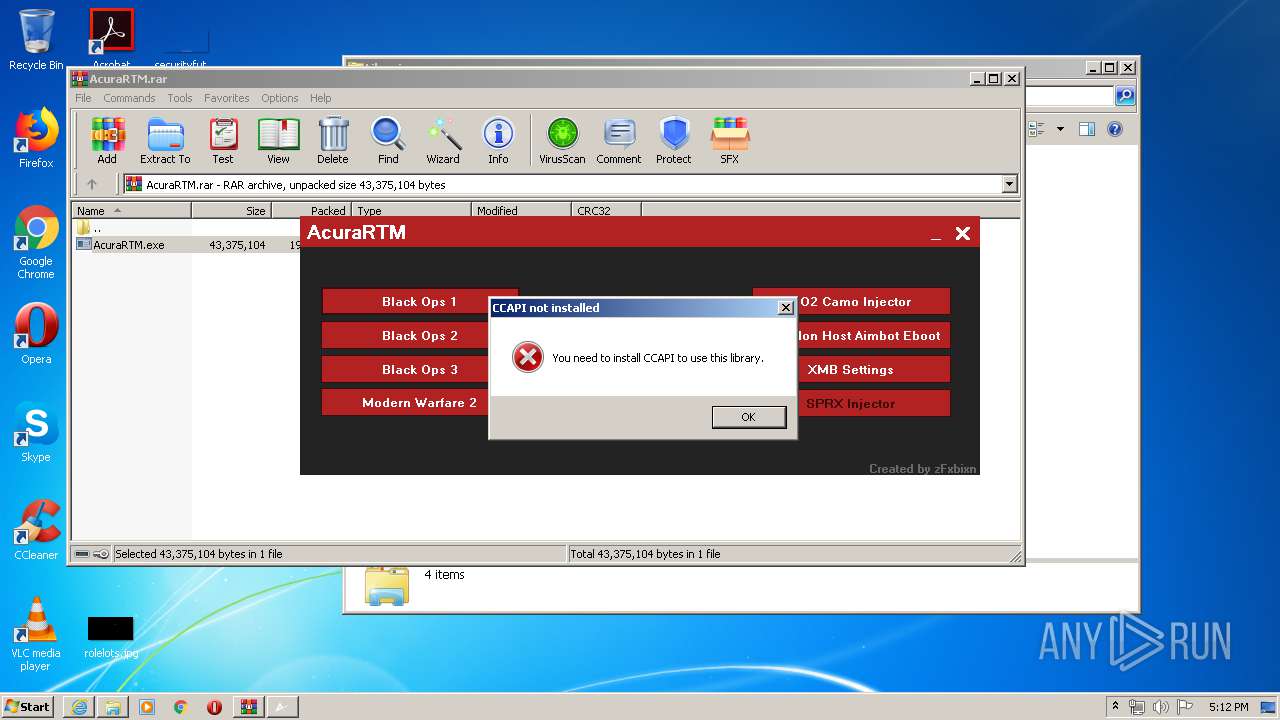
Creates files in the user directory
- AcuraRTM.exe (PID: 2944)
Connects to SMTP port
- AcuraRTM.exe (PID: 2944)
INFO
Application launched itself
- iexplore.exe (PID: 3376)
Changes internet zones settings
- iexplore.exe (PID: 3376)
Manual execution by user
- explorer.exe (PID: 3404)
Reads Internet Cache Settings
- iexplore.exe (PID: 3376)
- iexplore.exe (PID: 1944)
Creates files in the user directory
- iexplore.exe (PID: 1944)
Reads settings of System Certificates
- iexplore.exe (PID: 1944)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3376)
Reads internet explorer settings
- iexplore.exe (PID: 1944)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
5
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1944 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3376 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
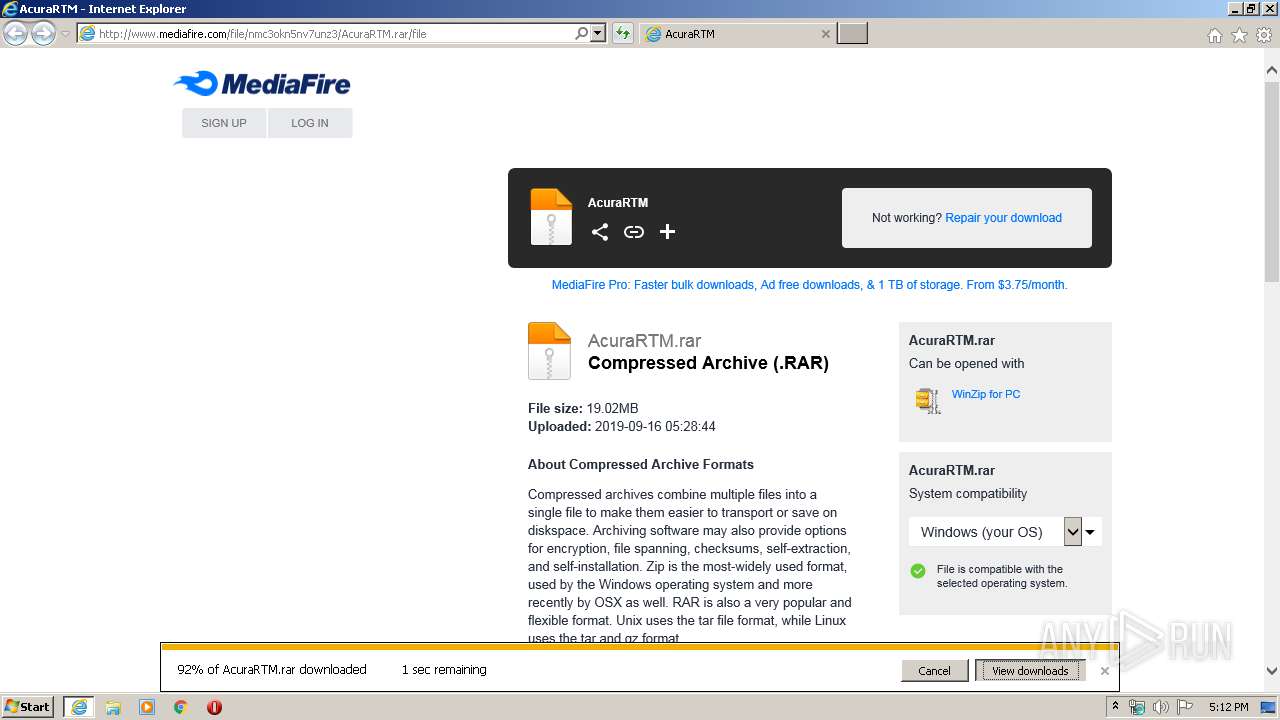
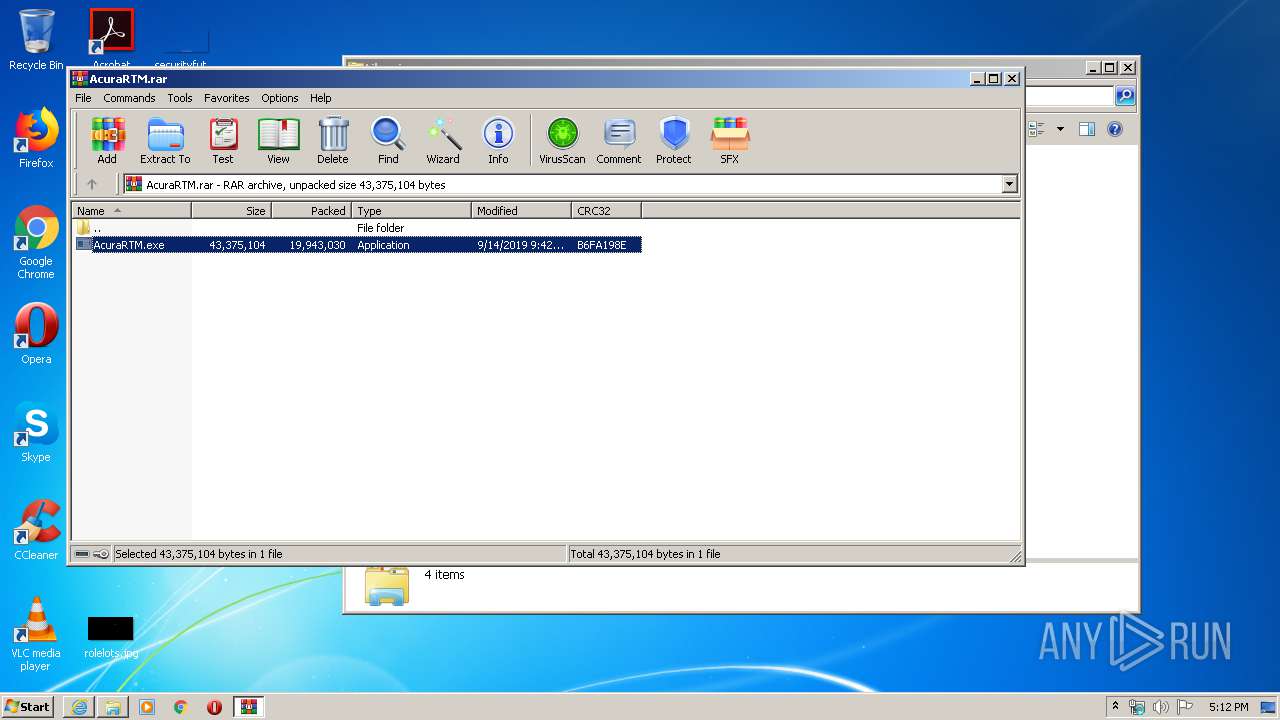
| 2820 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\AcuraRTM.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | iexplore.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
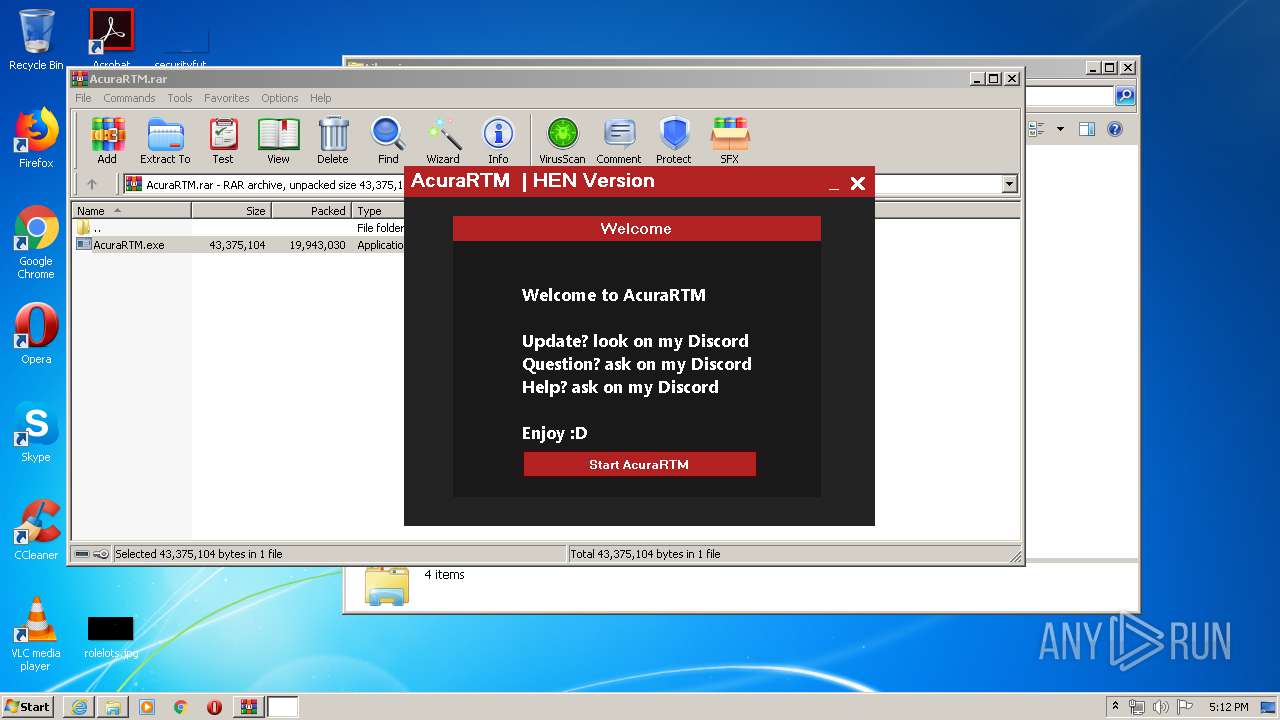
| 2944 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2820.46219\AcuraRTM.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2820.46219\AcuraRTM.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: AcuraRTM HEN Exit code: 0 Version: 2.2 Modules
| |||||||||||||||
| 3376 | "C:\Program Files\Internet Explorer\iexplore.exe" http://www.mediafire.com/file/nmc3okn5nv7unz3/AcuraRTM.rar/file | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3404 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 349
Read events
1 235
Write events
114
Delete events
0
Modification events
| (PID) Process: | (3376) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 549932842 | |||
| (PID) Process: | (3376) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30792373 | |||
| (PID) Process: | (3376) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3376) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3376) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3376) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3376) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3376) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3376) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3376) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
56
Text files
37
Unknown types
23
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1944 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\8QU1CQCK.txt | — | |
MD5:— | SHA256:— | |||
| 1944 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\0N7XOESD.txt | — | |
MD5:— | SHA256:— | |||
| 1944 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\239H7LYX.txt | — | |
MD5:— | SHA256:— | |||
| 1944 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\453HF2UZ.txt | — | |
MD5:— | SHA256:— | |||
| 1944 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\f[1].txt | text | |
MD5:— | SHA256:— | |||
| 1944 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\1UAOJV3W.txt | text | |
MD5:— | SHA256:— | |||
| 1944 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\apps_list_sprite-v4[1].png | image | |
MD5:— | SHA256:— | |||
| 1944 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar76CF.tmp | — | |
MD5:— | SHA256:— | |||
| 1944 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\footerIcons[1].png | image | |
MD5:E0ABC4FEA89D2C5153B73CD02AC5BA13 | SHA256:F917A9105C311331B1D40F4D2BDBF11233C1C465616C1A9C46232F451463B061 | |||
| 1944 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\file[1].htm | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
38
TCP/UDP connections
81
DNS requests
40
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1944 | iexplore.exe | GET | 200 | 104.16.203.237:80 | http://www.mediafire.com/file/nmc3okn5nv7unz3/AcuraRTM.rar/file | US | html | 82.0 Kb | shared |
1944 | iexplore.exe | GET | 200 | 104.122.154.243:80 | http://c.aaxads.com/aax.js?pub=AAX3221EY&hst=www.mediafire.com&ver=1.2 | US | text | 106 Kb | whitelisted |
1944 | iexplore.exe | GET | 200 | 104.16.203.237:80 | http://www.mediafire.com/images/icons/svg_light/icons_sprite.svg | US | image | 8.12 Kb | shared |
1944 | iexplore.exe | GET | 200 | 104.16.203.237:80 | http://www.mediafire.com/js/prebid2.44.1.js | US | text | 52.9 Kb | shared |
1944 | iexplore.exe | GET | 200 | 172.217.23.174:80 | http://translate.google.com/translate_a/element.js?cb=googFooterTranslate | US | text | 798 b | whitelisted |
1944 | iexplore.exe | GET | 200 | 104.16.203.237:80 | http://static.mediafire.com/images/backgrounds/download/apps_list_sprite-v4.png | US | image | 6.78 Kb | shared |
1944 | iexplore.exe | POST | 200 | 37.252.173.22:80 | http://ib.adnxs.com/ut/v3/prebid | unknown | text | 241 b | whitelisted |
1944 | iexplore.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCYUwbNjiYsAwgAAAAAKZZ%2F | US | der | 472 b | whitelisted |
1944 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
1944 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAVG%2Fhgj9%2BGUHaOfzhTEYXM%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1944 | iexplore.exe | 185.29.135.190:443 | sync.mathtag.com | MediaMath Inc | GB | unknown |
1944 | iexplore.exe | 172.217.21.226:443 | cm.g.doubleclick.net | Google Inc. | US | whitelisted |
1944 | iexplore.exe | 104.16.203.237:80 | www.mediafire.com | Cloudflare Inc | US | unknown |
1944 | iexplore.exe | 172.217.16.136:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
1944 | iexplore.exe | 104.122.154.243:80 | c.aaxads.com | Akamai Technologies, Inc. | US | unknown |
1944 | iexplore.exe | 216.58.205.226:443 | securepubads.g.doubleclick.net | Google Inc. | US | whitelisted |
1944 | iexplore.exe | 172.217.23.174:80 | translate.google.com | Google Inc. | US | whitelisted |
1944 | iexplore.exe | 172.217.18.106:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
1944 | iexplore.exe | 104.122.146.75:80 | aaxdetect.com | Akamai Technologies, Inc. | US | unknown |
1944 | iexplore.exe | 172.217.23.99:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.mediafire.com |
| shared |
www.googletagmanager.com |
| whitelisted |
securepubads.g.doubleclick.net |
| whitelisted |
c.aaxads.com |
| whitelisted |
translate.google.com |
| whitelisted |
static.mediafire.com |
| shared |
translate.googleapis.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
aaxdetect.com |
| whitelisted |
ib.adnxs.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1944 | iexplore.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
2944 | AcuraRTM.exe | Misc activity | SUSPICIOUS [PTsecurity] ipify.org External IP Check |
2944 | AcuraRTM.exe | Misc activity | SUSPICIOUS [PTsecurity] ipify.org External IP Check |
2944 | AcuraRTM.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
1 ETPRO signatures available at the full report