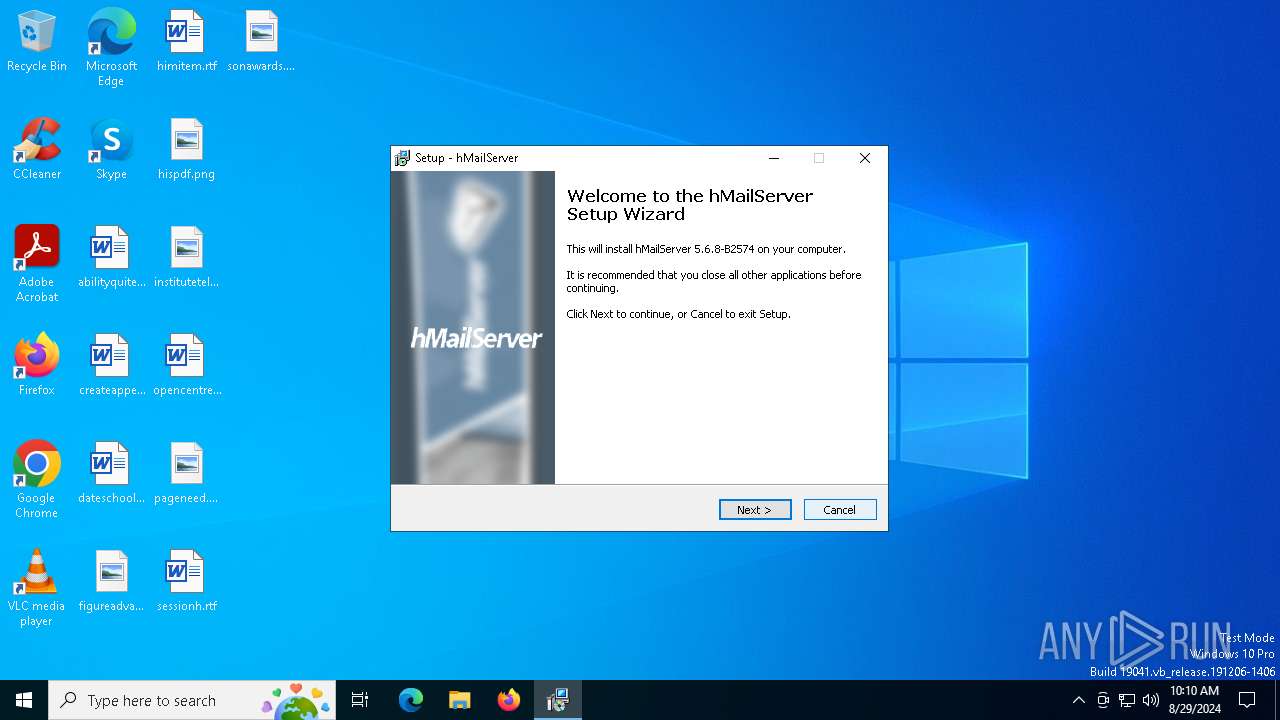
| File name: | hMailServer-5.6.8-B2574.exe |
| Full analysis: | https://app.any.run/tasks/dfdbf4b9-c625-41c6-90ef-65d00f420338 |
| Verdict: | Malicious activity |
| Analysis date: | August 29, 2024, 10:09:52 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | C8444C5EE87FC53003ECD6443209CA93 |
| SHA1: | 395CC0AFC3A1F4737BC42AC0FED1E747572D4CA0 |
| SHA256: | B7239676CD5EB9F21BF49C9AE170E7004B8ABECB7EEA08108930866A37D72659 |
| SSDEEP: | 98304:Y9peoM9NSmjBQEn1JjiSrS9q1tejXoAR4uEmkj2pfeGAOSIatAJqFT8IpWlEv7Fh:pANlS |
MALICIOUS
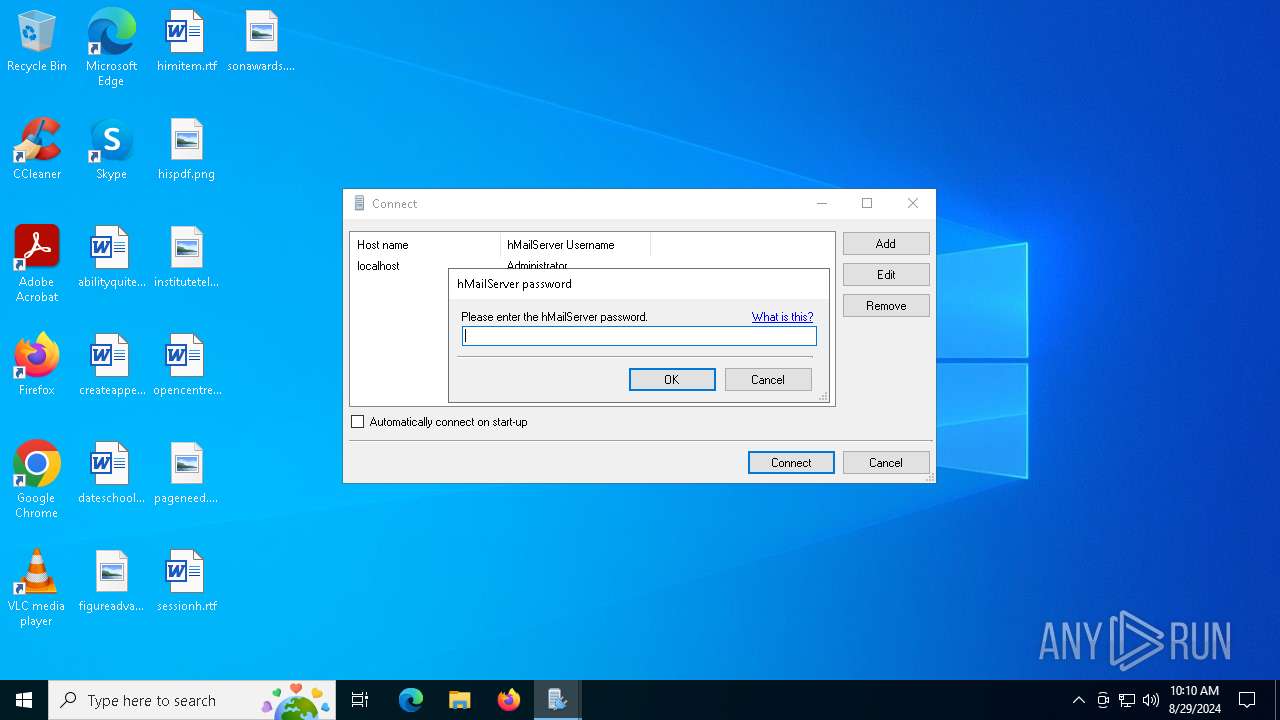
Starts NET.EXE for service management
- net.exe (PID: 5148)
- hMailServer-5.6.8-B2574.tmp (PID: 5708)
Starts Visual C# compiler
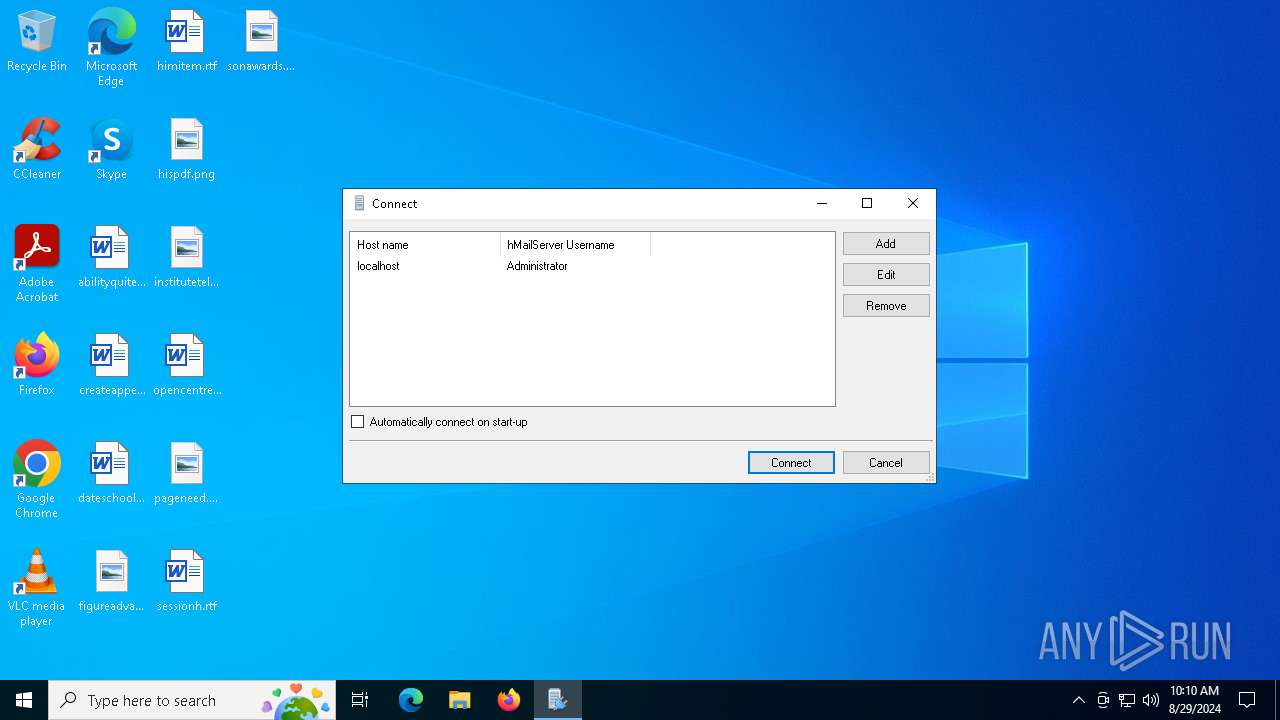
- hMailAdmin.exe (PID: 7088)
SUSPICIOUS
Drops the executable file immediately after the start
- hMailServer-5.6.8-B2574.exe (PID: 6156)
- hMailServer-5.6.8-B2574.exe (PID: 488)
- hMailServer-5.6.8-B2574.tmp (PID: 5708)
- csc.exe (PID: 5656)
- msiexec.exe (PID: 1020)
Reads the date of Windows installation
- hMailServer-5.6.8-B2574.tmp (PID: 6172)
- hMailServer-5.6.8-B2574.tmp (PID: 5708)
Executable content was dropped or overwritten
- hMailServer-5.6.8-B2574.exe (PID: 6156)
- hMailServer-5.6.8-B2574.tmp (PID: 5708)
- hMailServer-5.6.8-B2574.exe (PID: 488)
- csc.exe (PID: 5656)
Reads security settings of Internet Explorer
- hMailServer-5.6.8-B2574.tmp (PID: 6172)
- hMailServer-5.6.8-B2574.tmp (PID: 5708)
Reads the Windows owner or organization settings
- hMailServer-5.6.8-B2574.tmp (PID: 5708)
- msiexec.exe (PID: 1020)
Process drops legitimate windows executable
- hMailServer-5.6.8-B2574.tmp (PID: 5708)
- msiexec.exe (PID: 1020)
Drops 7-zip archiver for unpacking
- hMailServer-5.6.8-B2574.tmp (PID: 5708)
The process drops C-runtime libraries
- hMailServer-5.6.8-B2574.tmp (PID: 5708)
Checks Windows Trust Settings
- msiexec.exe (PID: 1020)
Creates/Modifies COM task schedule object
- hMailServer.exe (PID: 7004)
- msiexec.exe (PID: 1020)
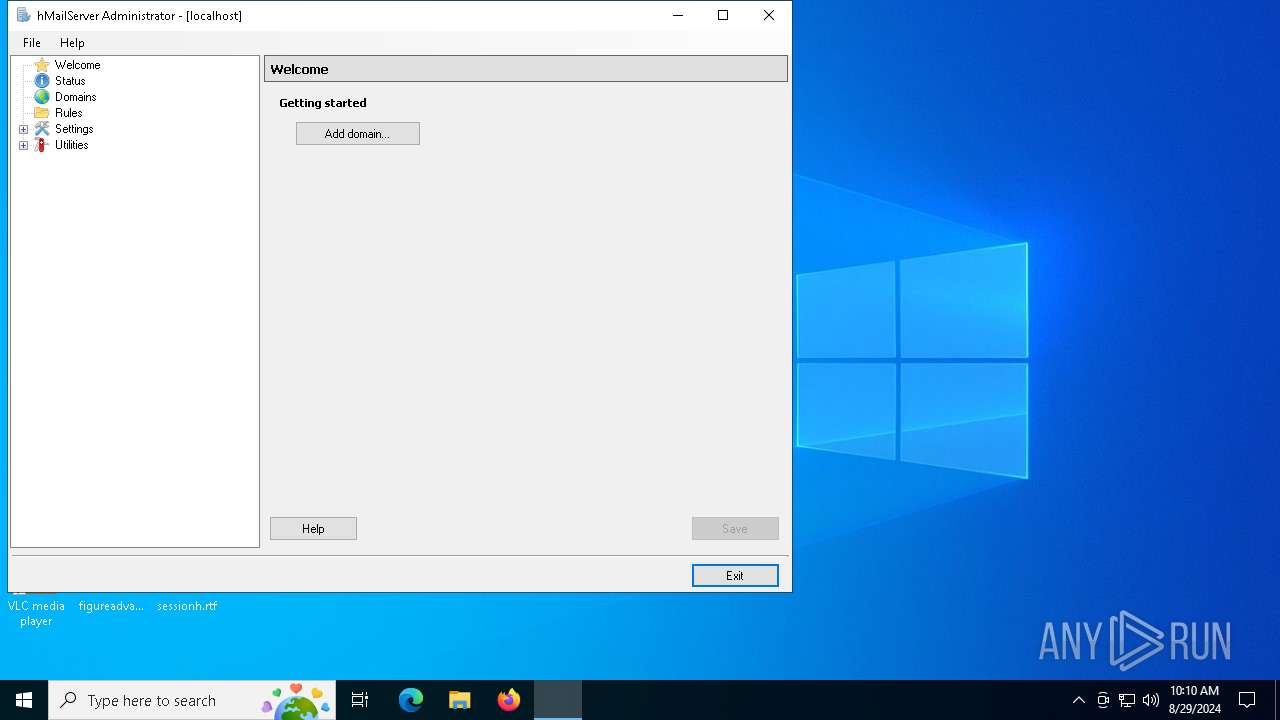
Uses .NET C# to load dll
- hMailAdmin.exe (PID: 7088)
Reads Internet Explorer settings
- hMailAdmin.exe (PID: 7088)
Executes as Windows Service
- hMailServer.exe (PID: 6796)
INFO
Create files in a temporary directory
- hMailServer-5.6.8-B2574.exe (PID: 6156)
- hMailServer-5.6.8-B2574.exe (PID: 488)
- hMailServer-5.6.8-B2574.tmp (PID: 5708)
- hMailAdmin.exe (PID: 7088)
- csc.exe (PID: 5656)
- cvtres.exe (PID: 7152)
Checks supported languages
- hMailServer-5.6.8-B2574.exe (PID: 6156)
- hMailServer-5.6.8-B2574.tmp (PID: 6172)
- hMailServer-5.6.8-B2574.exe (PID: 488)
- msiexec.exe (PID: 1020)
- msiexec.exe (PID: 6504)
- msiexec.exe (PID: 5464)
- hMailServer.exe (PID: 7004)
- DBSetupQuick.exe (PID: 5104)
- hMailServer.exe (PID: 6796)
- hMailAdmin.exe (PID: 7088)
- csc.exe (PID: 5656)
- hMailServer-5.6.8-B2574.tmp (PID: 5708)
- cvtres.exe (PID: 7152)
Reads the computer name
- hMailServer-5.6.8-B2574.tmp (PID: 6172)
- hMailServer-5.6.8-B2574.tmp (PID: 5708)
- msiexec.exe (PID: 1020)
- msiexec.exe (PID: 5464)
- msiexec.exe (PID: 6504)
- hMailServer.exe (PID: 7004)
- DBSetupQuick.exe (PID: 5104)
- hMailServer.exe (PID: 6796)
- hMailAdmin.exe (PID: 7088)
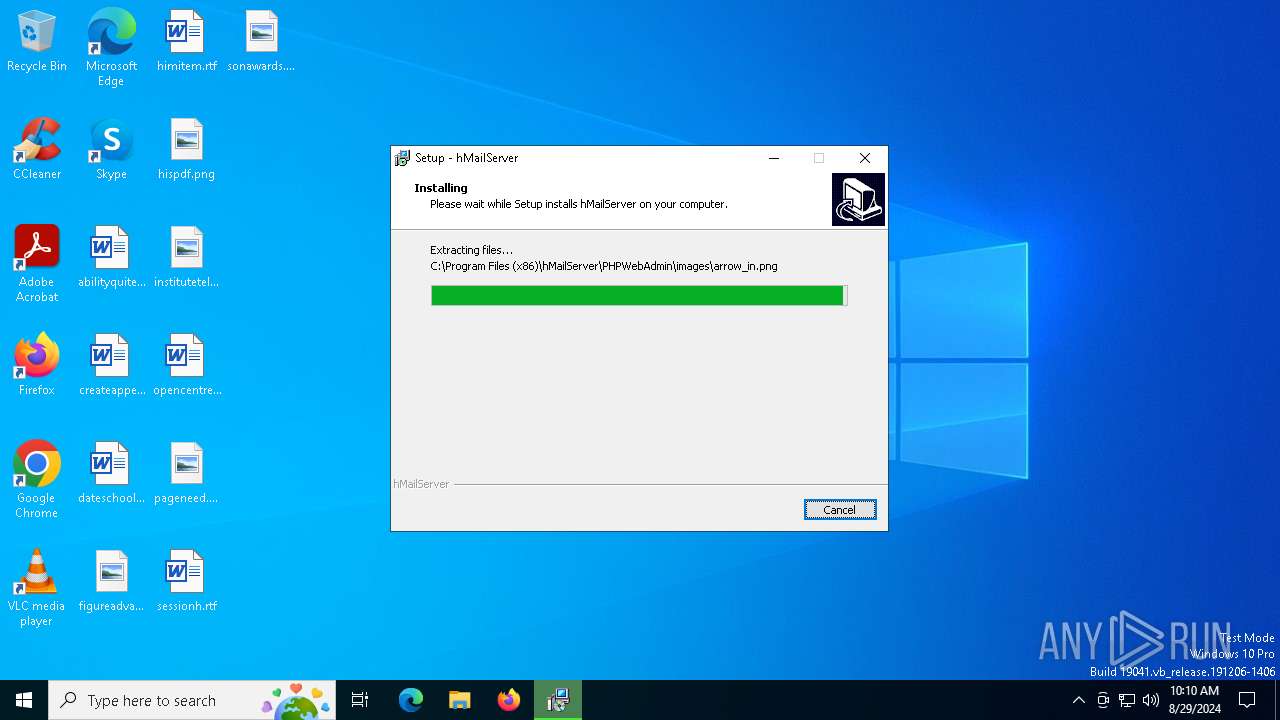
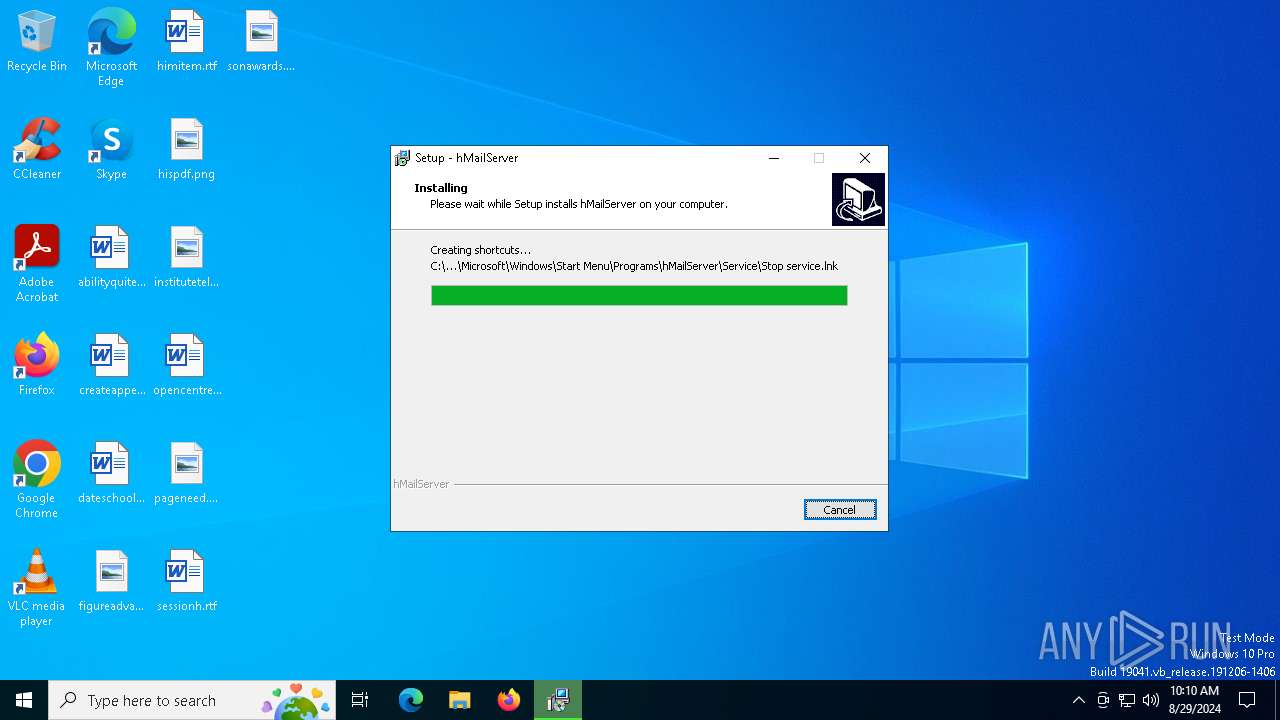
Creates files in the program directory
- hMailServer-5.6.8-B2574.tmp (PID: 5708)
- hMailServer.exe (PID: 6796)
Process checks computer location settings
- hMailServer-5.6.8-B2574.tmp (PID: 5708)
- hMailServer-5.6.8-B2574.tmp (PID: 6172)
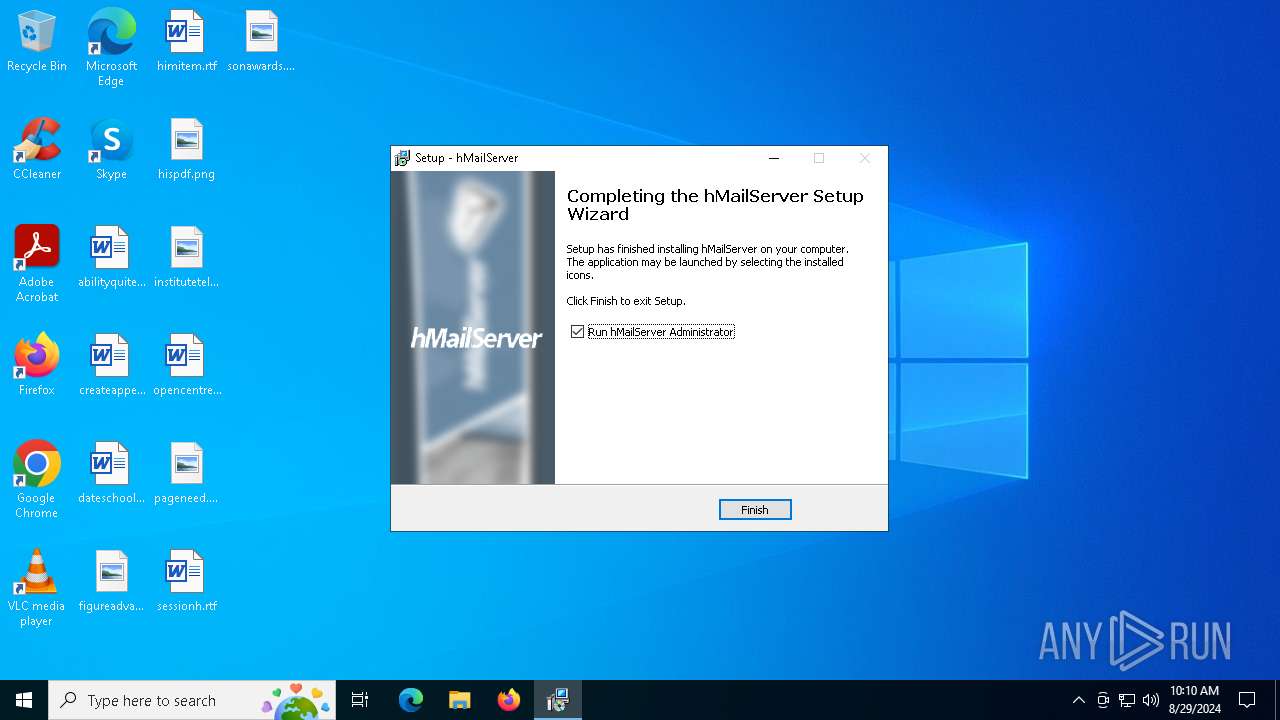
Creates a software uninstall entry
- hMailServer-5.6.8-B2574.tmp (PID: 5708)
- msiexec.exe (PID: 1020)
Executable content was dropped or overwritten
- msiexec.exe (PID: 1020)
Creates files or folders in the user directory
- msiexec.exe (PID: 1020)
- hMailAdmin.exe (PID: 7088)
Reads the software policy settings
- msiexec.exe (PID: 1020)
- slui.exe (PID: 7020)
Reads the machine GUID from the registry
- hMailServer.exe (PID: 6796)
- hMailAdmin.exe (PID: 7088)
- csc.exe (PID: 5656)
- cvtres.exe (PID: 7152)
- msiexec.exe (PID: 1020)
Reads Environment values
- hMailServer.exe (PID: 6796)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
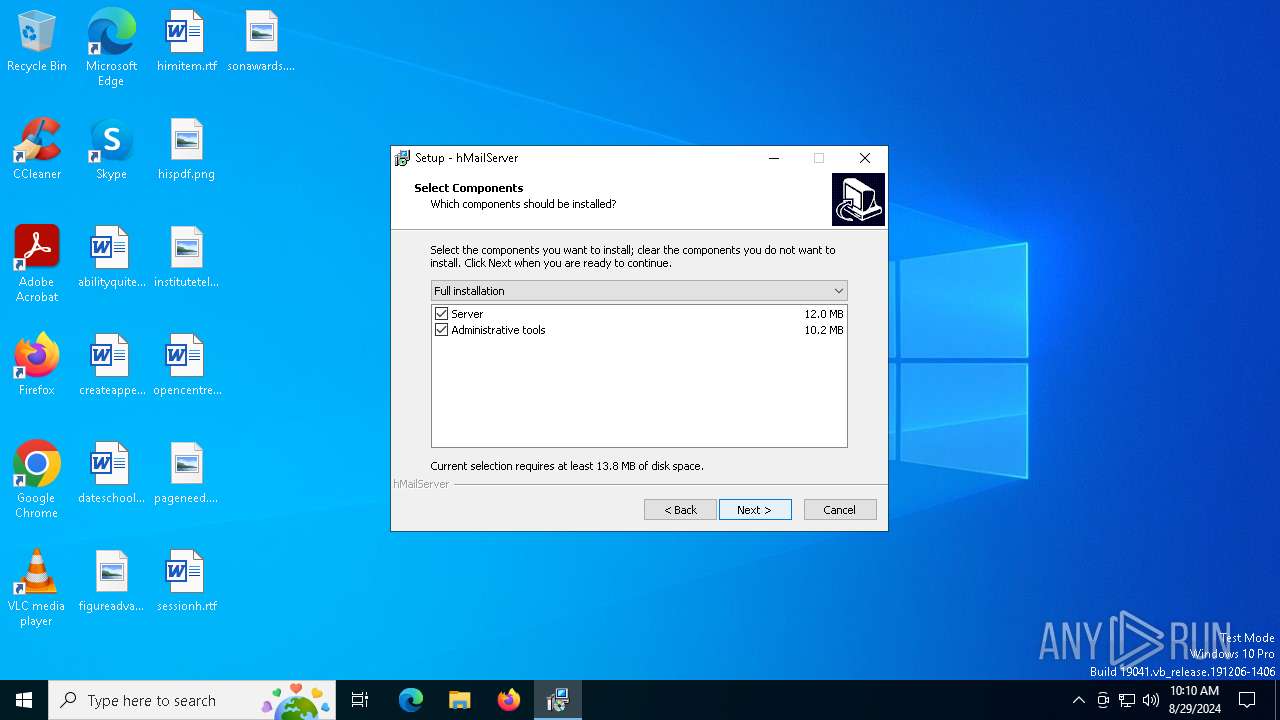
| .exe | | | Inno Setup installer (71.1) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (9.1) |
| .scr | | | Windows screen saver (8.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.2) |
| .exe | | | Win32 Executable (generic) (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 40448 |
| InitializedDataSize: | 17920 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa5f8 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | |
| FileDescription: | hMailServer Setup |
| FileVersion: | |
| LegalCopyright: | Copyright © 2008 |
| ProductName: | hMailServer |
| ProductVersion: |
Total processes
152
Monitored processes
21
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 488 | "C:\Users\admin\AppData\Local\Temp\hMailServer-5.6.8-B2574.exe" /SPAWNWND=$7034C /NOTIFYWND=$8033E | C:\Users\admin\AppData\Local\Temp\hMailServer-5.6.8-B2574.exe | hMailServer-5.6.8-B2574.tmp | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: hMailServer Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 1020 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2008 | C:\WINDOWS\system32\net1 START hMailServer | C:\Windows\SysWOW64\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2456 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2636 | "C:\WINDOWS\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\is-4HG0L.tmp\SSCERuntime-ENU.msi" /qn | C:\Windows\SysWOW64\msiexec.exe | — | hMailServer-5.6.8-B2574.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
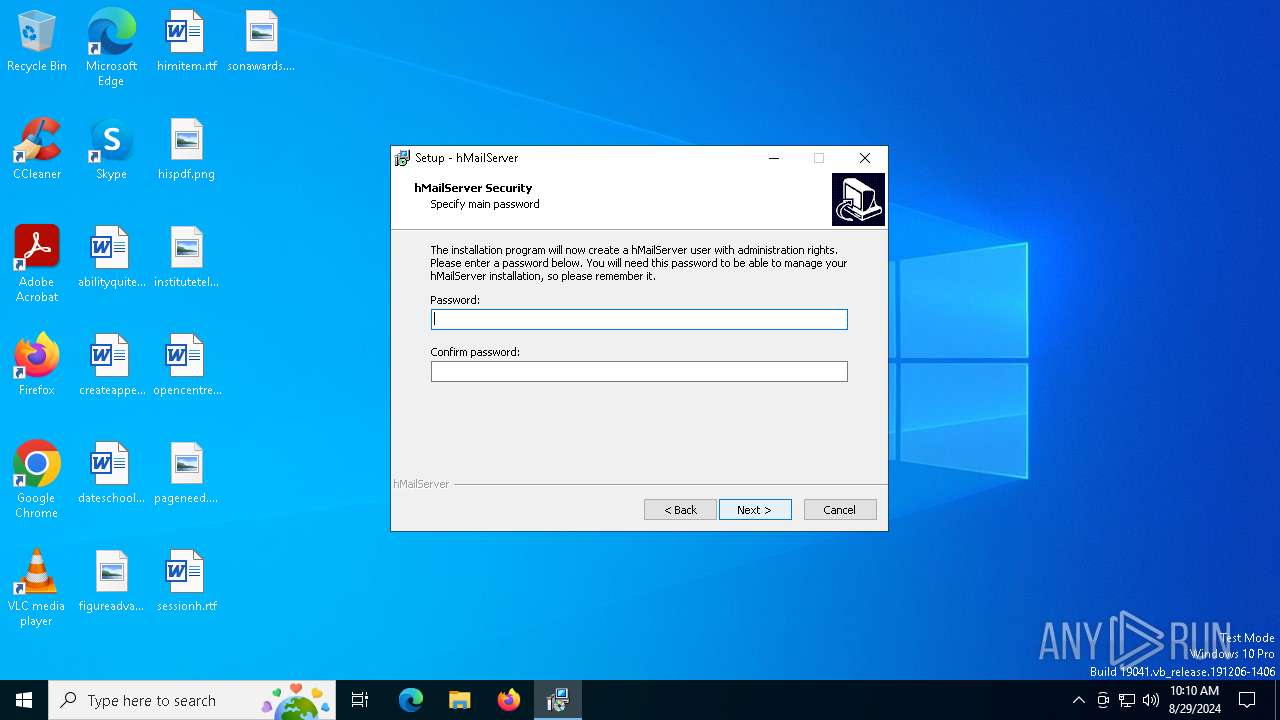
| 5104 | "C:\Program Files (x86)\hMailServer\Bin\DBSetupQuick.exe" password:tester | C:\Program Files (x86)\hMailServer\Bin\DBSetupQuick.exe | — | hMailServer-5.6.8-B2574.tmp | |||||||||||
User: admin Company: HI Integrity Level: HIGH Description: DBSetupQuick Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 5112 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5148 | "C:\WINDOWS\system32\net.exe" START hMailServer | C:\Windows\SysWOW64\net.exe | — | hMailServer-5.6.8-B2574.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5388 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5464 | C:\Windows\syswow64\MsiExec.exe -Embedding 3124F047B6A4DD43D76C47CC0771D98B | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
18 309
Read events
17 831
Write events
461
Delete events
17
Modification events
| (PID) Process: | (5708) hMailServer-5.6.8-B2574.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 4C160000A3834C9BFBF9DA01 | |||
| (PID) Process: | (5708) hMailServer-5.6.8-B2574.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 9025E60D9ED668DF3FA23C26B68A2B76046D74B9A026450AF6933E0FDA8EC07E | |||
| (PID) Process: | (5708) hMailServer-5.6.8-B2574.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (5708) hMailServer-5.6.8-B2574.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\WINDOWS\system32\atl70.dll | |||
| (PID) Process: | (5708) hMailServer-5.6.8-B2574.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: C1E51614B226650AD5BC0ED337D6102F798D41E509679B4332B5FF7C10973D17 | |||
| (PID) Process: | (5708) hMailServer-5.6.8-B2574.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\hMailServer_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.5.4 (a) | |||
| (PID) Process: | (5708) hMailServer-5.6.8-B2574.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\hMailServer_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
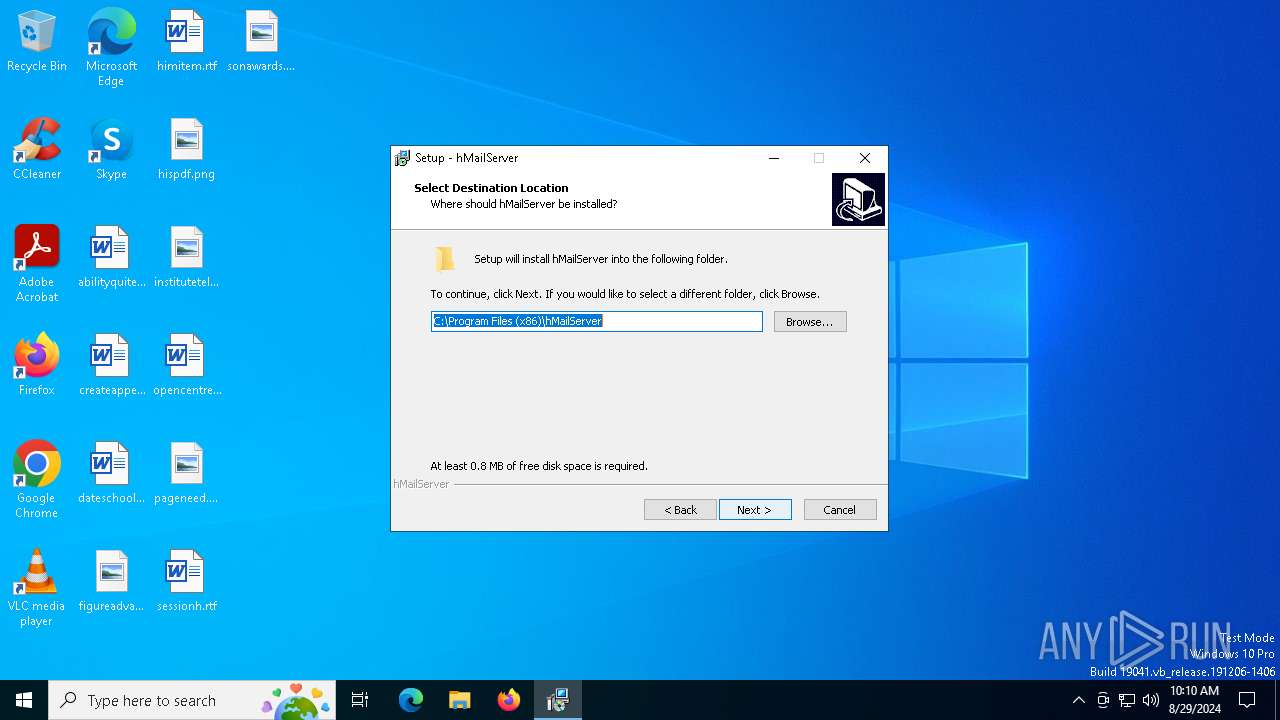
Value: C:\Program Files (x86)\hMailServer | |||
| (PID) Process: | (5708) hMailServer-5.6.8-B2574.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\hMailServer_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files (x86)\hMailServer\ | |||
| (PID) Process: | (5708) hMailServer-5.6.8-B2574.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\hMailServer_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: hMailServer | |||
| (PID) Process: | (5708) hMailServer-5.6.8-B2574.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\hMailServer_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
Executable files
68
Suspicious files
27
Text files
590
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5708 | hMailServer-5.6.8-B2574.tmp | C:\Users\admin\AppData\Local\Temp\is-4HG0L.tmp\_isetup\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
| 5708 | hMailServer-5.6.8-B2574.tmp | C:\Program Files (x86)\hMailServer\is-EFVIE.tmp | executable | |
MD5:DF679C1A9B6C251B7F9FB2E8F17BEFEF | SHA256:24B9DDBA6424CCB901ABDA25E7F5B0106867CF8F3CC7295CCBEBCFF7B55FB731 | |||
| 5708 | hMailServer-5.6.8-B2574.tmp | C:\Program Files (x86)\hMailServer\unins000.exe | executable | |
MD5:DF679C1A9B6C251B7F9FB2E8F17BEFEF | SHA256:24B9DDBA6424CCB901ABDA25E7F5B0106867CF8F3CC7295CCBEBCFF7B55FB731 | |||
| 5708 | hMailServer-5.6.8-B2574.tmp | C:\Program Files (x86)\hMailServer\Bin\License.rtf | text | |
MD5:67DA419790DB8E161B6F566B42277A85 | SHA256:97EEB485005171627A6A0A115F42282049D8FF55C8DE394C70000AA5BF973614 | |||
| 5708 | hMailServer-5.6.8-B2574.tmp | C:\Program Files (x86)\hMailServer\Bin\is-C9N21.tmp | executable | |
MD5:A751580637365B2BE8EF90E8C8229294 | SHA256:85135756921C74635BD5566499212BC10A3890A6F4844498F12ABEFDB2F76EB6 | |||
| 5708 | hMailServer-5.6.8-B2574.tmp | C:\Users\admin\AppData\Local\Temp\is-4HG0L.tmp\is-3QKPJ.tmp | executable | |
MD5:81802B011FA0F84E62C3967101E756D3 | SHA256:9E1594BC762F10109EB08334DFC889982FB3F2BDC6F585A80BC58037F9242DAF | |||
| 5708 | hMailServer-5.6.8-B2574.tmp | C:\Program Files (x86)\hMailServer\Bin\7za.exe | executable | |
MD5:42BADC1D2F03A8B1E4875740D3D49336 | SHA256:C136B1467D669A725478A6110EBAAAB3CB88A3D389DFA688E06173C066B76FCF | |||
| 5708 | hMailServer-5.6.8-B2574.tmp | C:\Users\admin\AppData\Local\Temp\is-4HG0L.tmp\isxdl.dll | executable | |
MD5:792620390AAE5305220283F2CE33CA68 | SHA256:21BC620515EBBDEB125D273C2D8DB45577D05408EF624464AF26AFCFECFD201A | |||
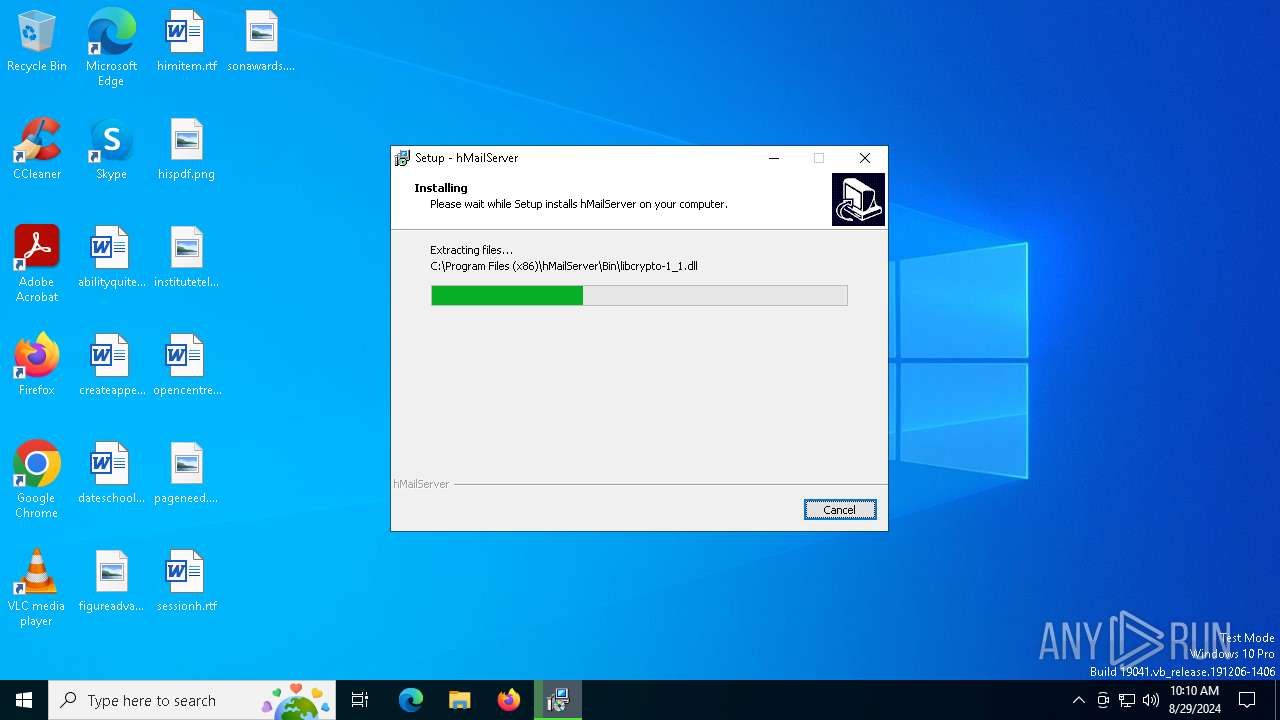
| 5708 | hMailServer-5.6.8-B2574.tmp | C:\Program Files (x86)\hMailServer\Bin\libcrypto-1_1.dll | executable | |
MD5:8A284A5D0C7BBB549EB829173D7D3D5A | SHA256:1FE1681A2A56047BE2E299A574457BC2A2444C545F342CFE011BF542D2407618 | |||
| 5708 | hMailServer-5.6.8-B2574.tmp | C:\Program Files (x86)\hMailServer\Bin\libssl-1_1.dll | executable | |
MD5:A751580637365B2BE8EF90E8C8229294 | SHA256:85135756921C74635BD5566499212BC10A3890A6F4844498F12ABEFDB2F76EB6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
28
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1780 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4576 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4576 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1020 | msiexec.exe | GET | 200 | 23.48.23.166:80 | http://crl.microsoft.com/pki/crl/products/CSPCA.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4132 | svchost.exe | 52.140.118.28:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IN | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6256 | RUXIMICS.exe | 52.140.118.28:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IN | whitelisted |
2120 | MoUsoCoreWorker.exe | 52.140.118.28:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IN | whitelisted |
4132 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1780 | svchost.exe | 40.126.31.67:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1780 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3260 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |