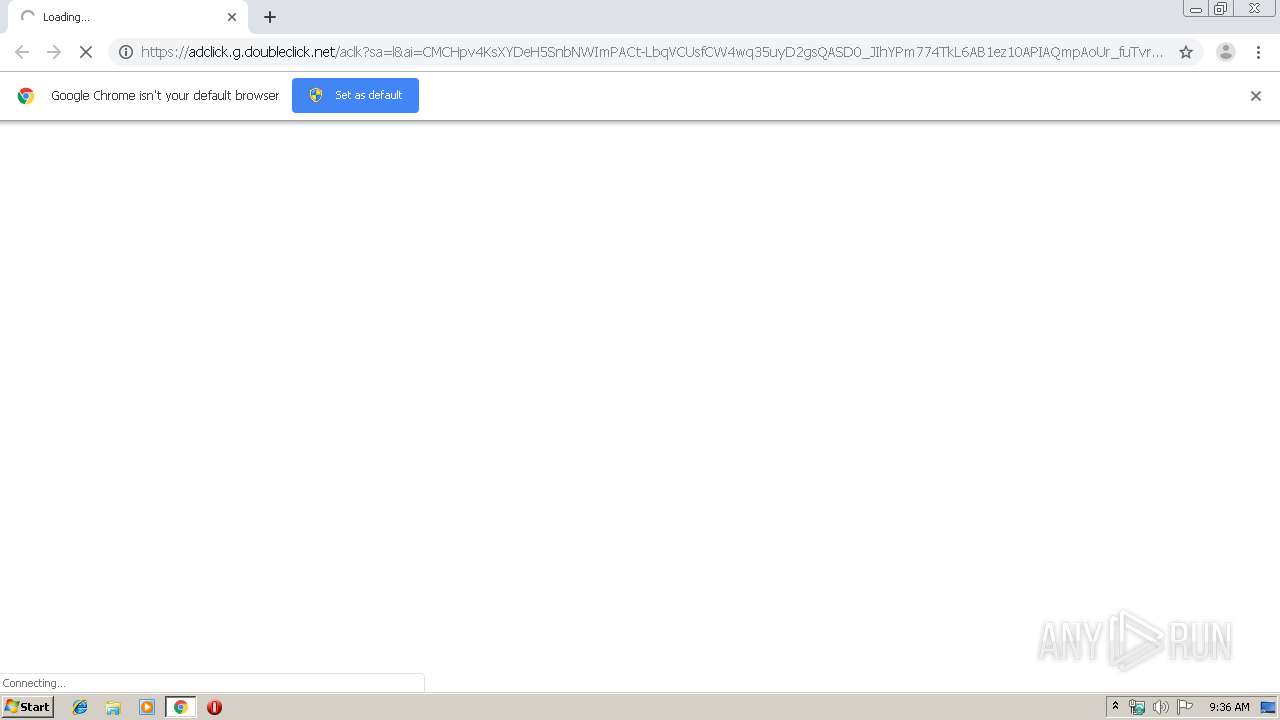
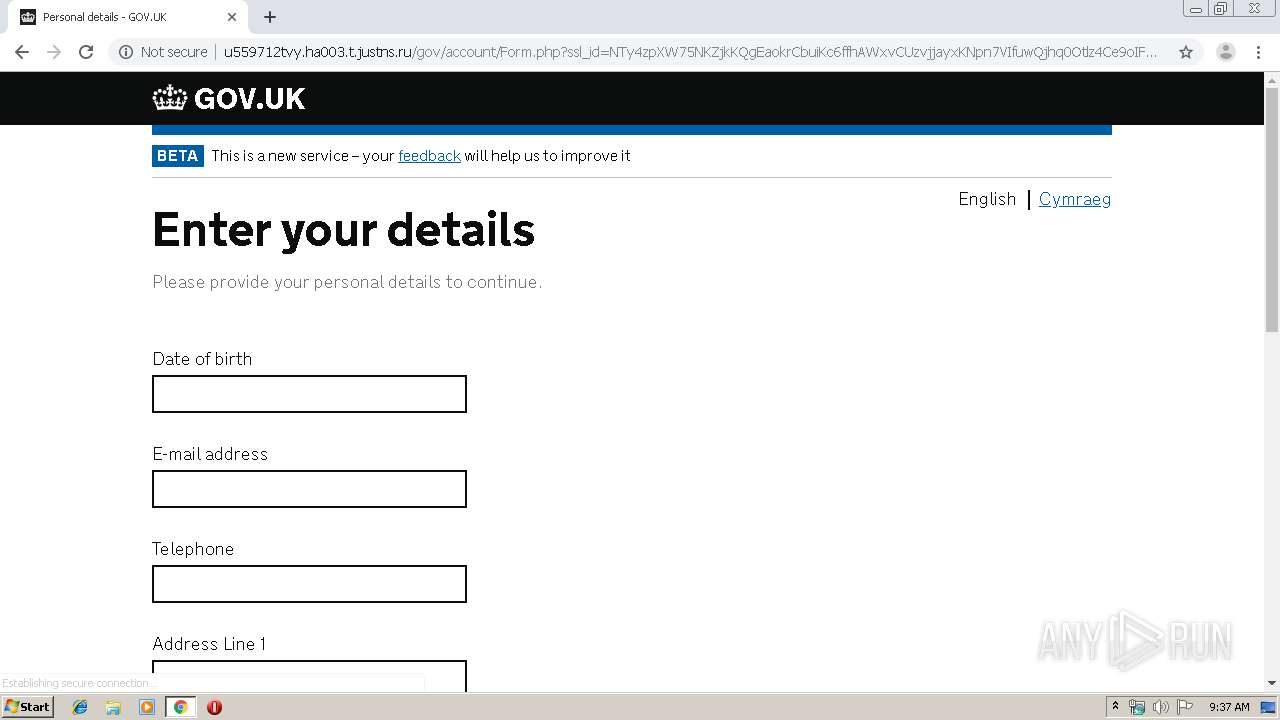
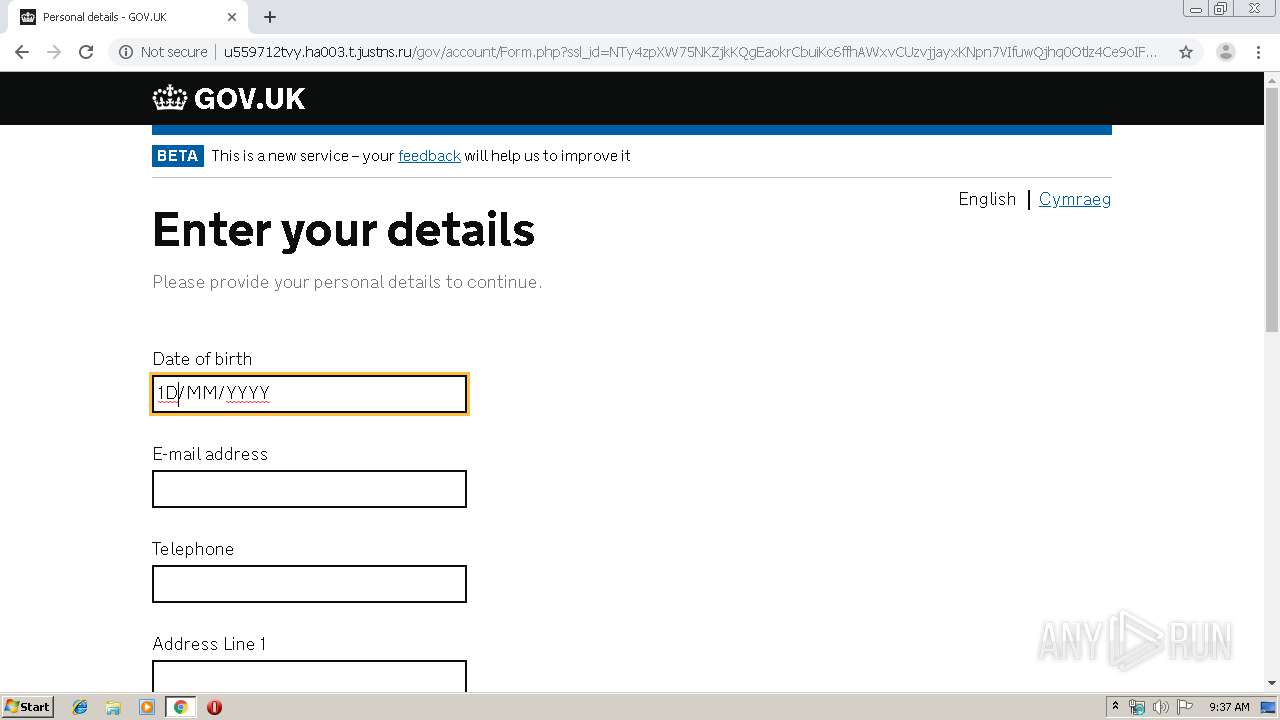
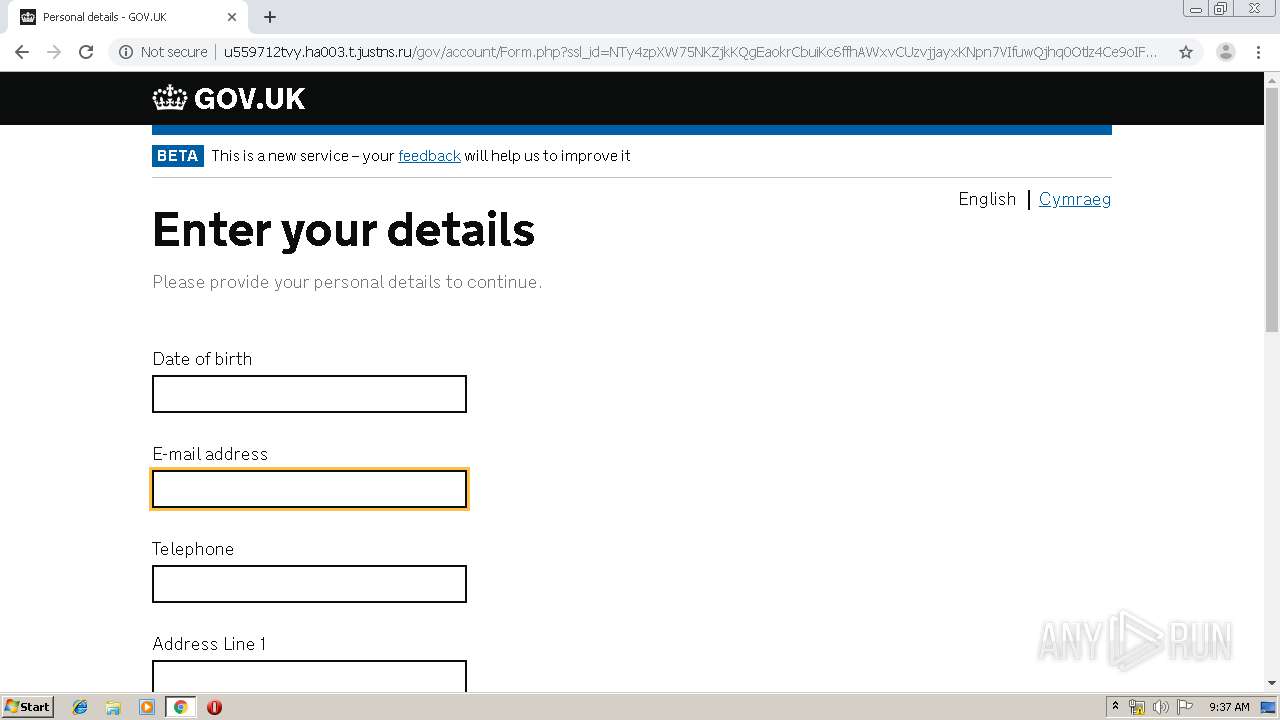
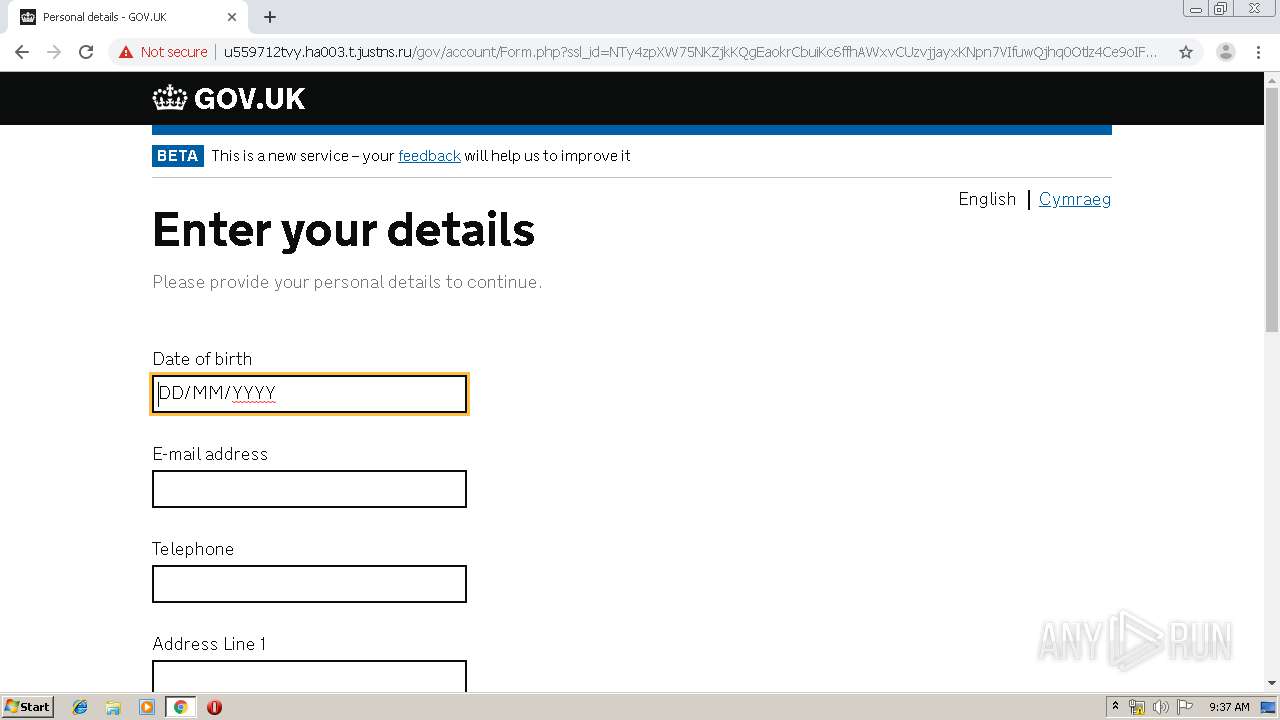
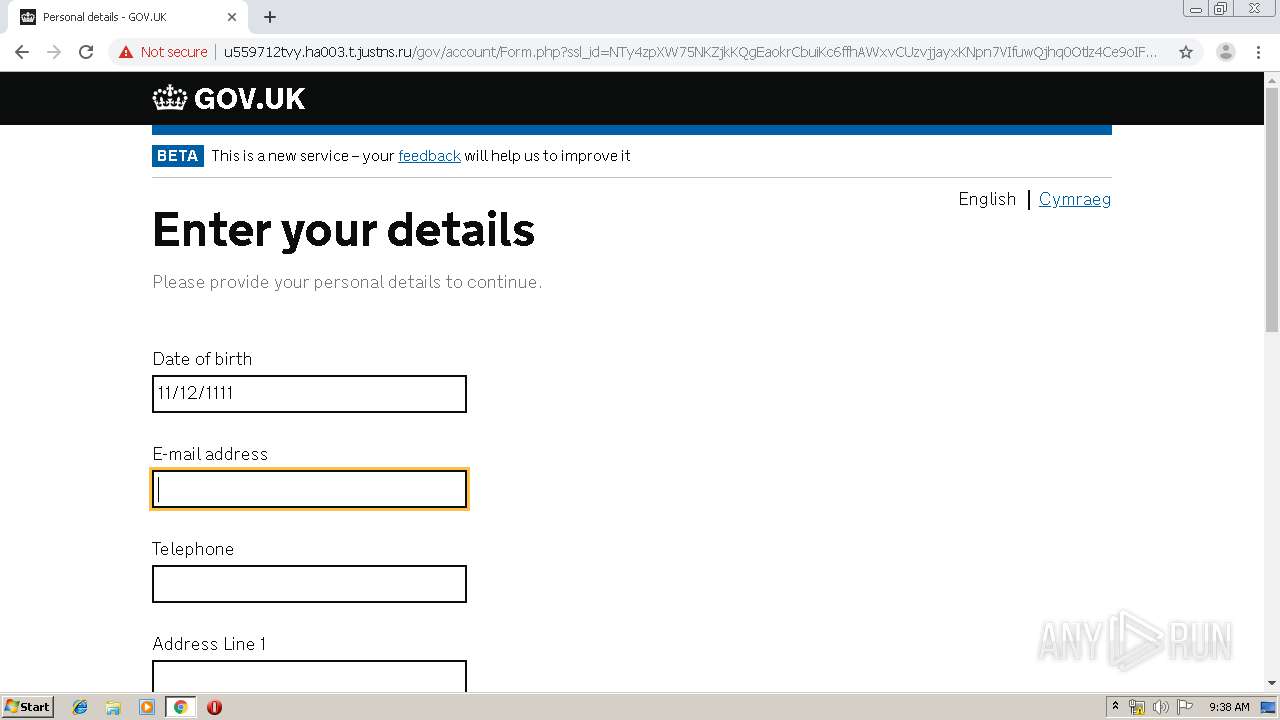
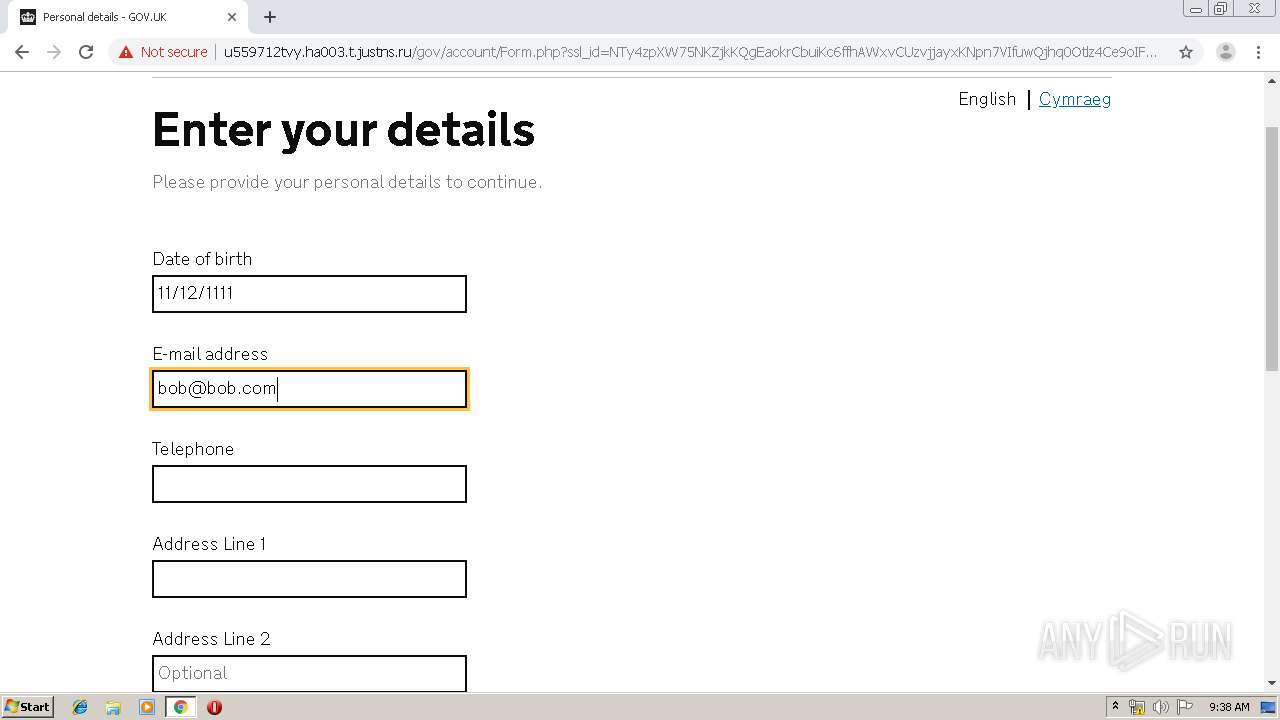
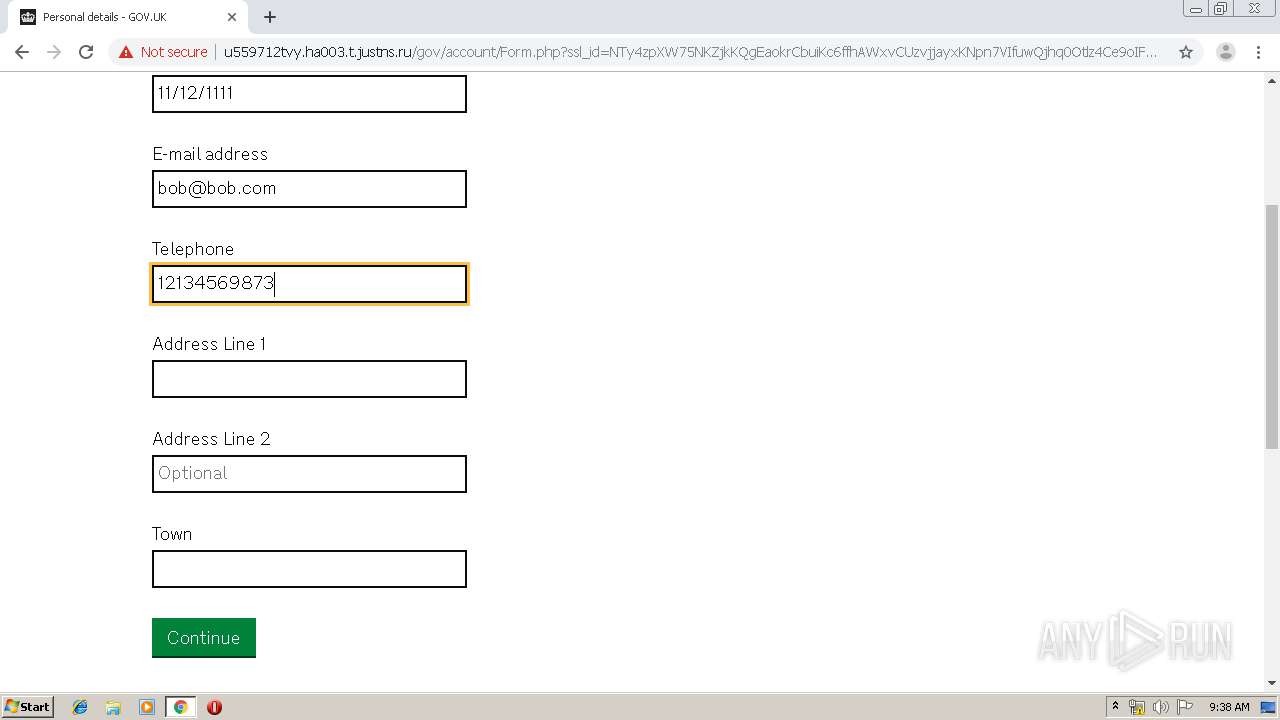
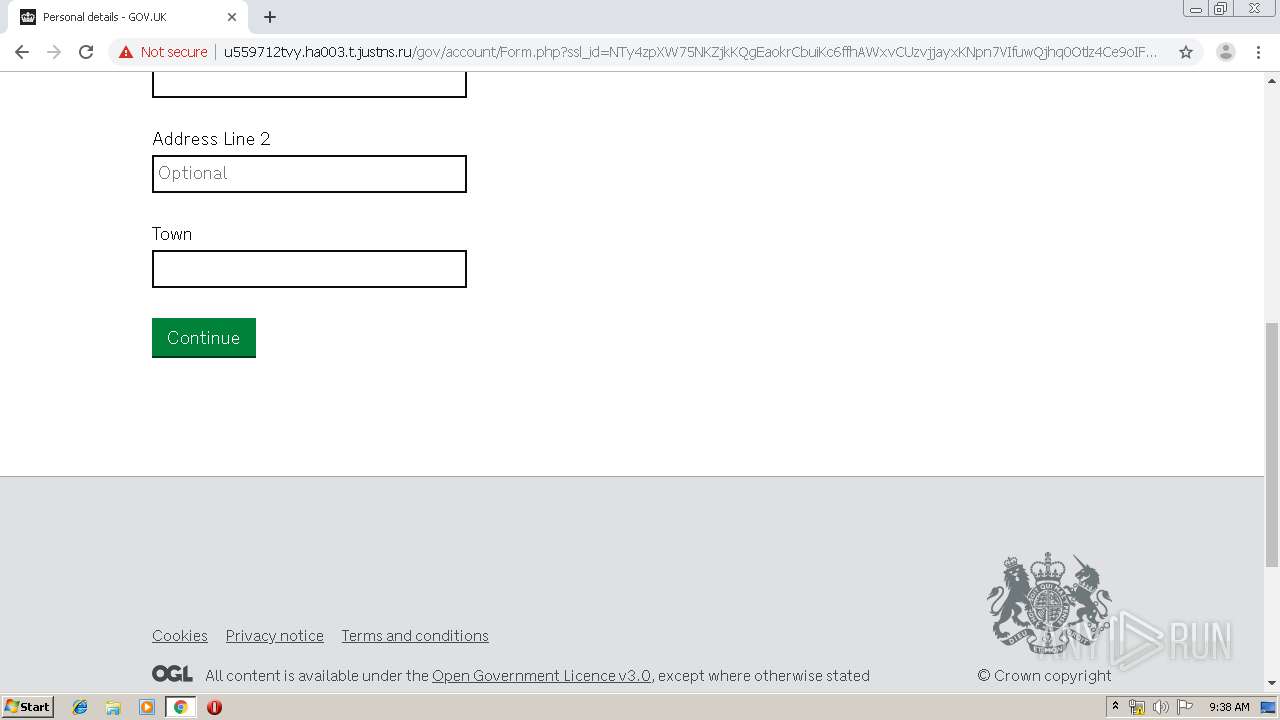
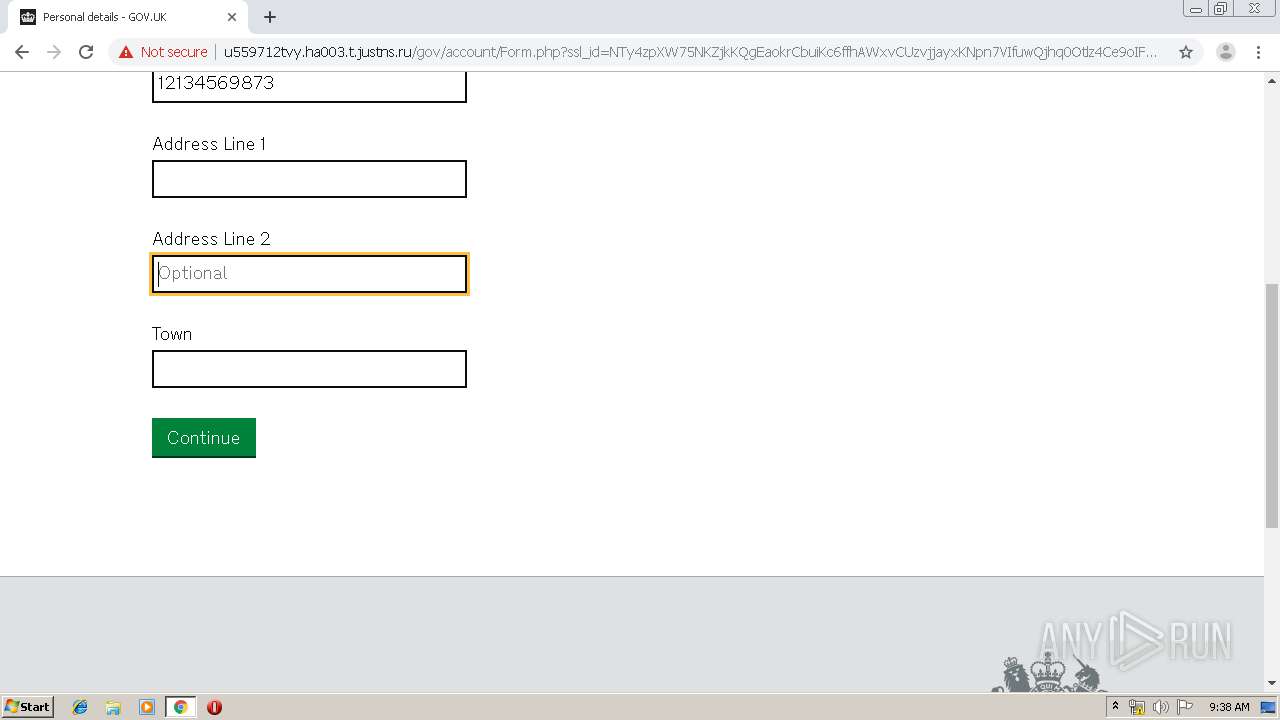
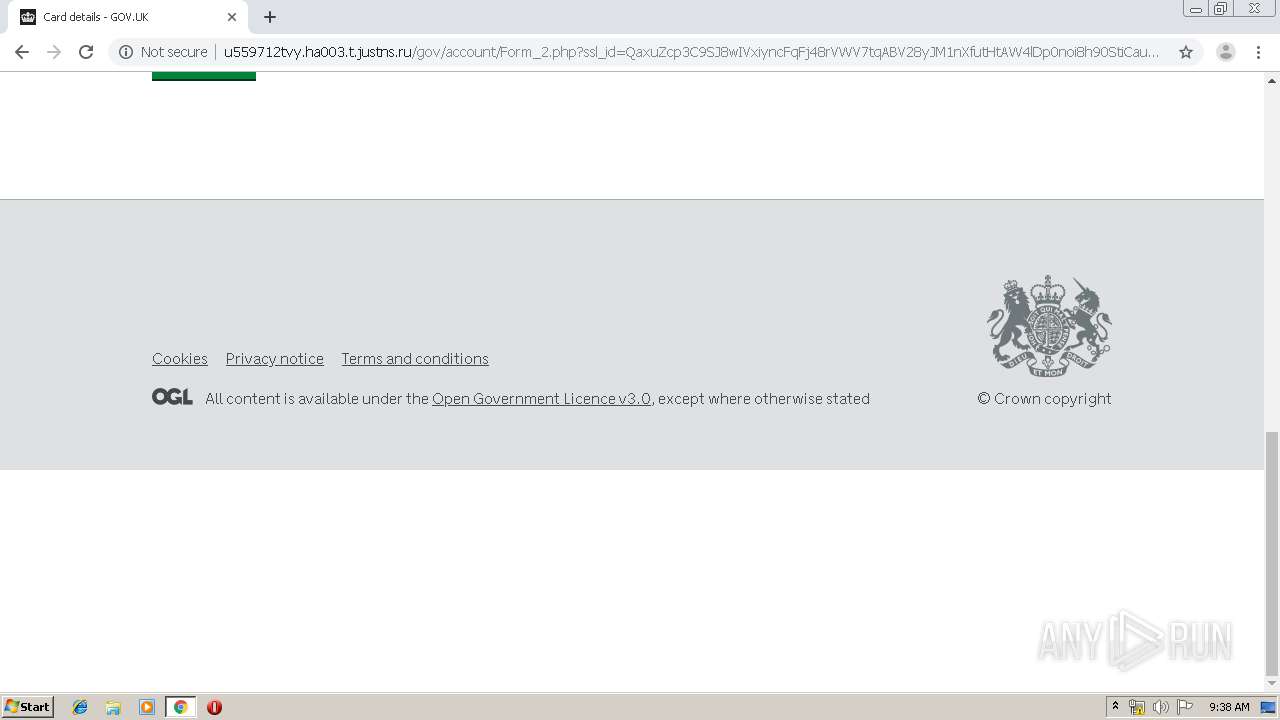
| URL: | https://adclick.g.doubleclick.net/aclk?sa=l&ai=CMCHpv4KsXYDeH5SnbNWImPACt-LbqVCUsfCW4wq35uyD2gsQASD0_JIhYPm774TkL6AB1ez10APIAQmpAoUr_fuTvrI-qAMByANKqgSxAU_QtPuf445l8BODGCyah2HxqvKtHUCkG-HsICT9go-gJrng4u7DZ6208aeecdz1ZdIcWD7gM5ztzGjLEmKe9nvKqWJxxi6Spid8K-4GhpP-BEcgDyVdox5ner9jeO3kG6sJop4SvW0RPpbYHNqqFySmiOeitMvZjDr5hwfV8kY1ifsUmnA4FiV3j8jqzrvmyRzFquQCdlqQV_n3Eir30Z7hqWVAEo3FNxB80Cs1WODDOfoFBgglEAEYAKAGLoAHn6CfA6gHjs4bqAfB0xuoB4XUG6gHgdQbqAeC1BuoB4bUG6gHhNQbqAeT2BuoB-DTG6gHugaoB9nLG6gHz8wbqAemvhuoB_PRG6gH7NUb2AcAwAgB0ggHCIxjEAEYHfIIG2FkeC1zdWJzeW4tMjg4NTA0NzgyMTkzNDQyNoAKA5ALA9gTDA&ae=1&num=1&sig=AOD64_1JPVhfUJ81qz4RxGgP80bE7u0qPw&client=ca-pub-8929667634210480&adurl=http://u559712tvy.ha003.t.justns.ru/gov/account/?url=https://www.google.com/search?q=messi&rlz=1C1CHBD_enMA745MA745&oq=messi&aqs=chrome..69i57j0l5.1496j0j7&sourceid=chrome&ie=U |
| Full analysis: | https://app.any.run/tasks/c6b5d925-e38d-4110-8ff9-fdc9466ae339 |
| Verdict: | Malicious activity |
| Analysis date: | January 03, 2020, 09:36:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1480FA1BA05CCE14136A900CCF943D07 |
| SHA1: | 7EA3CAA90E84BC9ADB1169ACAB4AB182F11C087C |
| SHA256: | B6FB0943171E5E87C51F4749F5E414FEC58B7B07F559B5BE12809BECF20EC8E6 |
| SSDEEP: | 24:2gixHGD2NwIGQ7G9KnNKIASLJgfgpWr3osOd92:xixmNIhimASVEgpWr4sOd92 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2896)
INFO
Reads the hosts file
- chrome.exe (PID: 2896)
- chrome.exe (PID: 3792)
Application launched itself
- chrome.exe (PID: 2896)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
62
Monitored processes
27
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1004,13327520542302318643,14185662005431868472,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=13903309300760929672 --mojo-platform-channel-handle=4616 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,13327520542302318643,14185662005431868472,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5859877622634285751 --renderer-client-id=23 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2328 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 640 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,13327520542302318643,14185662005431868472,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18160422115442095713 --mojo-platform-channel-handle=4112 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 792 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,13327520542302318643,14185662005431868472,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5750305037957302062 --mojo-platform-channel-handle=4108 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1044 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,13327520542302318643,14185662005431868472,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8816938428252392665 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3740 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,13327520542302318643,14185662005431868472,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6939193944565802323 --mojo-platform-channel-handle=4396 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,13327520542302318643,14185662005431868472,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16760720894829625049 --mojo-platform-channel-handle=4192 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,13327520542302318643,14185662005431868472,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=9709573864303325570 --mojo-platform-channel-handle=2840 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1904 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,13327520542302318643,14185662005431868472,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10182884767384525846 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2224 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,13327520542302318643,14185662005431868472,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7182945042401759147 --mojo-platform-channel-handle=3544 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
622
Read events
523
Write events
94
Delete events
5
Modification events
| (PID) Process: | (2896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2520) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2896-13222517787885375 |
Value: 259 | |||
| (PID) Process: | (2896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2896) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
50
Text files
207
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\5d3e3494-6a4f-484f-b4e4-4cf6d6b02da2.tmp | — | |
MD5:— | SHA256:— | |||
| 2896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF3998fe.TMP | text | |
MD5:A519780ED0A2F4336DB4F5651D79C369 | SHA256:DA5B71BD0075B55757BF757BF5F4D4A1DCBCF0762CDA5B31B28680963E068C75 | |||
| 2896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:454106CCF080F3E3795C229FC73350D4 | SHA256:9974DC611BE9E20BDFA7B8D939CB913AD23859DEA5F52EBB8D10CEAD9AB5B4FA | |||
| 2896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF39991e.TMP | text | |
MD5:3D551B6E929CF62F7AA66091E718704B | SHA256:1698A1B1BC3E86676392FB8BD4C712438302A5A2220503C08F290ED4B1790404 | |||
| 2896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:3D551B6E929CF62F7AA66091E718704B | SHA256:1698A1B1BC3E86676392FB8BD4C712438302A5A2220503C08F290ED4B1790404 | |||
| 2896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:C4D6CBB269C626168A5D6D0D8CCE6C30 | SHA256:B62CDBB758278A0C2E50593357390119441D8DE09428EB29027F3DFD1332E348 | |||
| 2896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
39
DNS requests
17
Threats
35
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3792 | chrome.exe | GET | 302 | 216.58.210.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 512 b | whitelisted |
3792 | chrome.exe | GET | 200 | 84.15.64.13:80 | http://r2---sn-cpux-8ovs.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=85.206.175.219&mm=28&mn=sn-cpux-8ovs&ms=nvh&mt=1578044119&mv=m&mvi=1&pl=21&shardbypass=yes | LT | crx | 293 Kb | whitelisted |
3792 | chrome.exe | GET | 302 | 216.58.210.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 533 b | whitelisted |
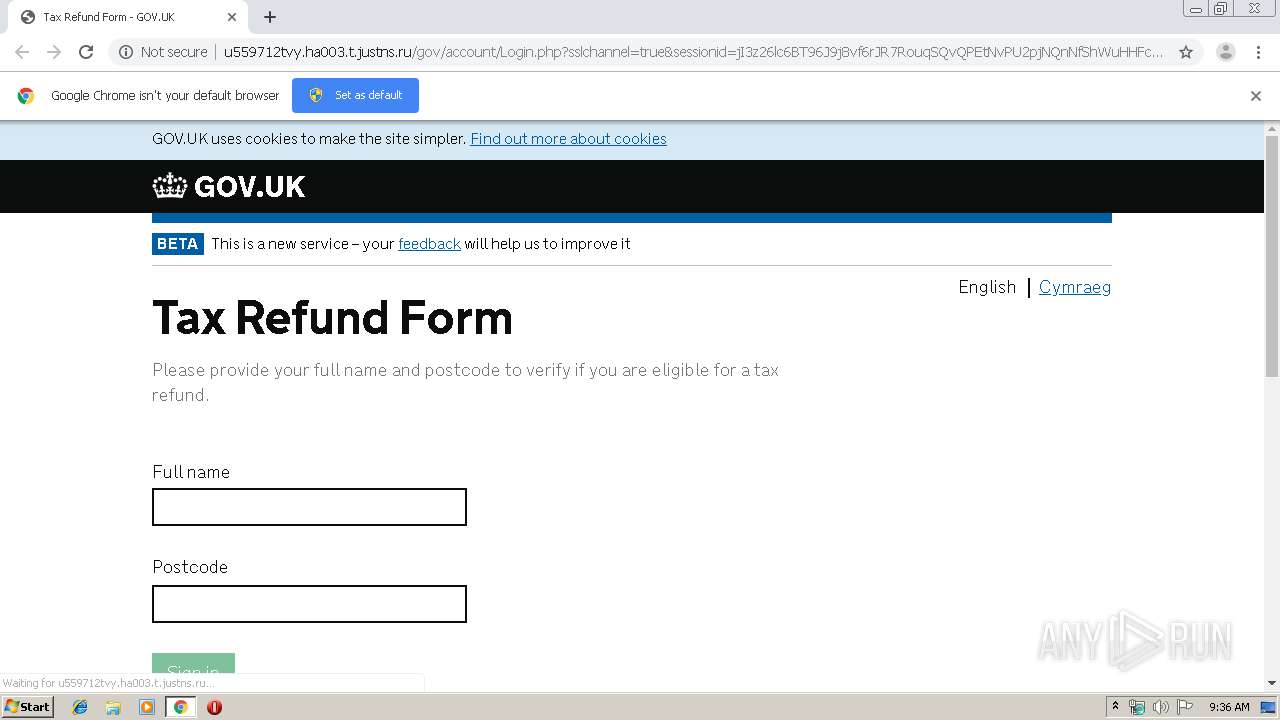
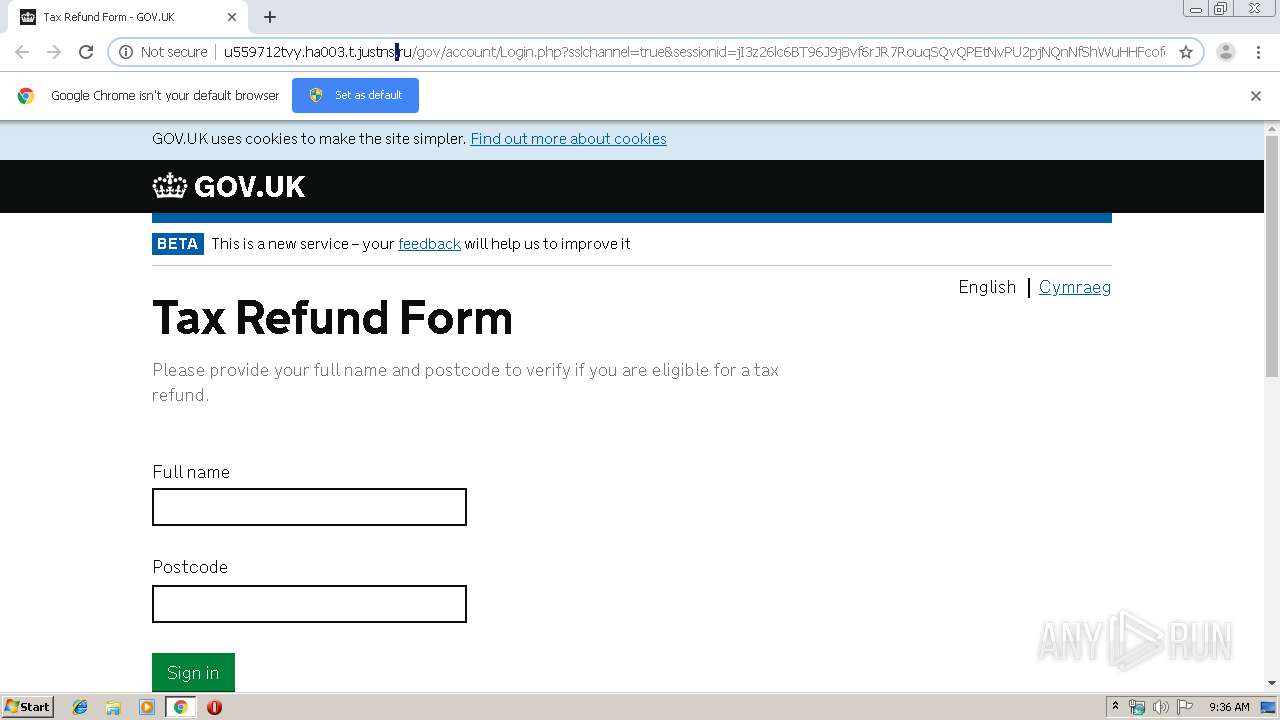
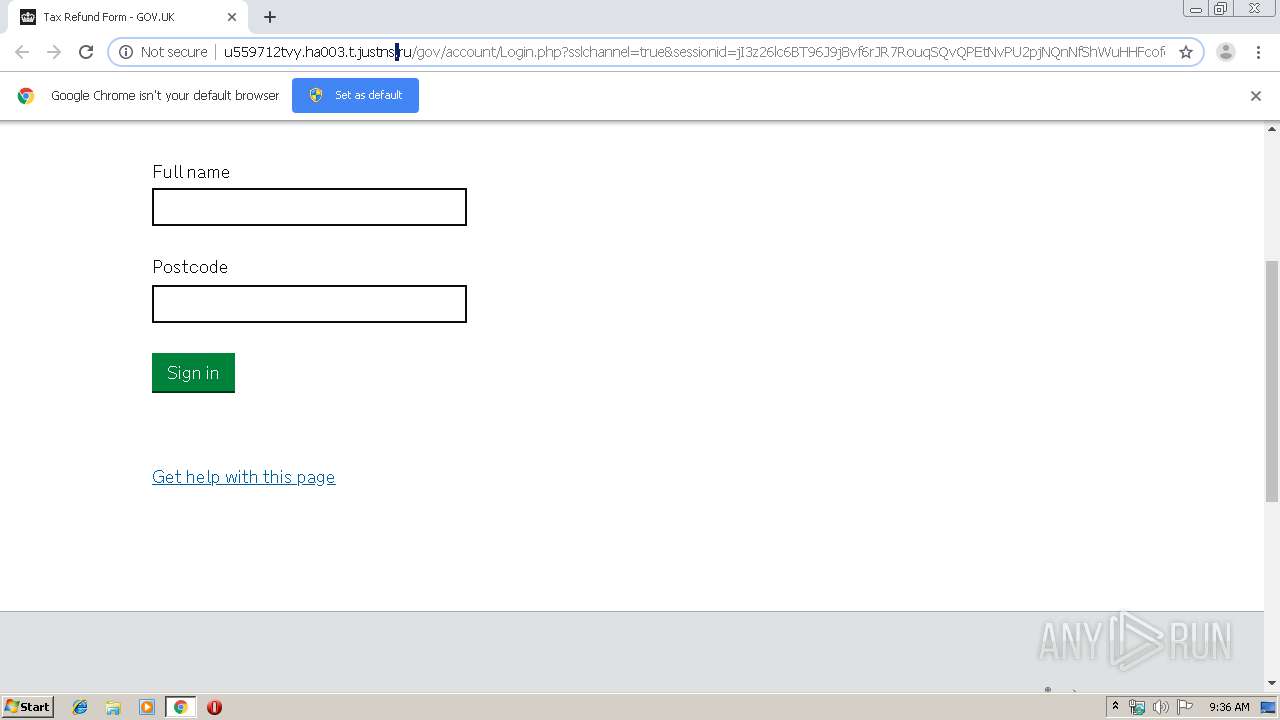
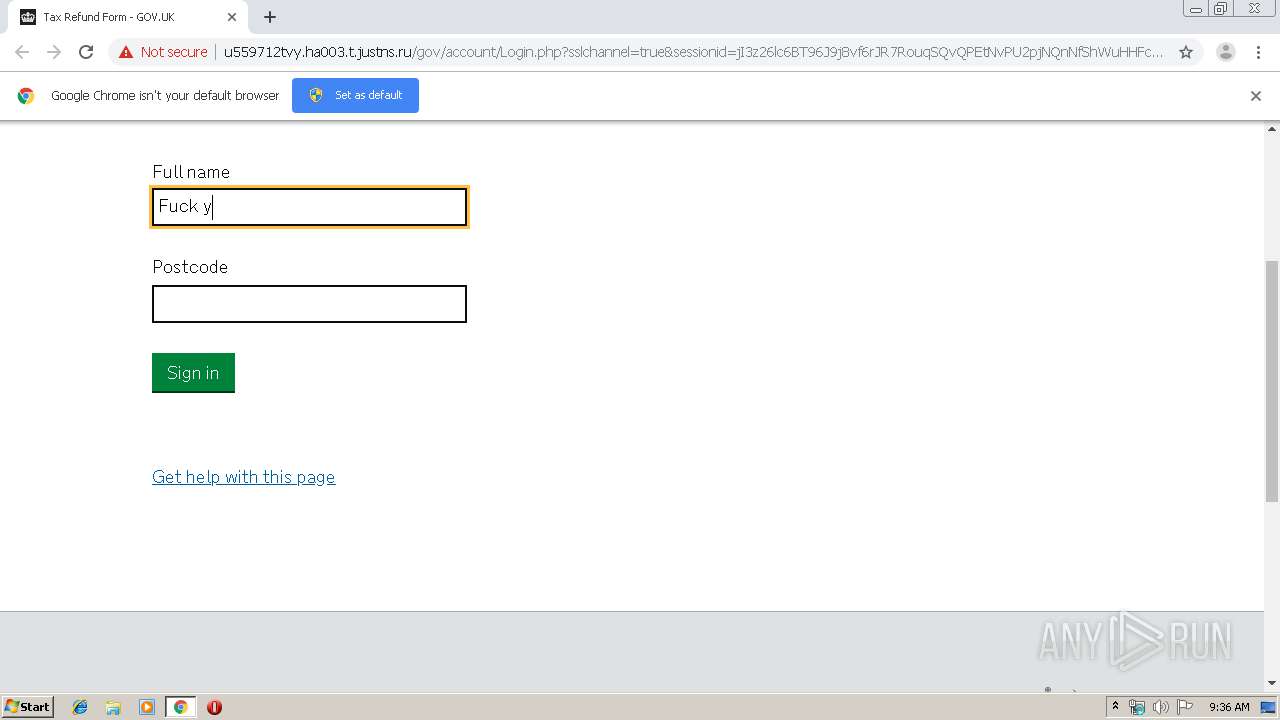
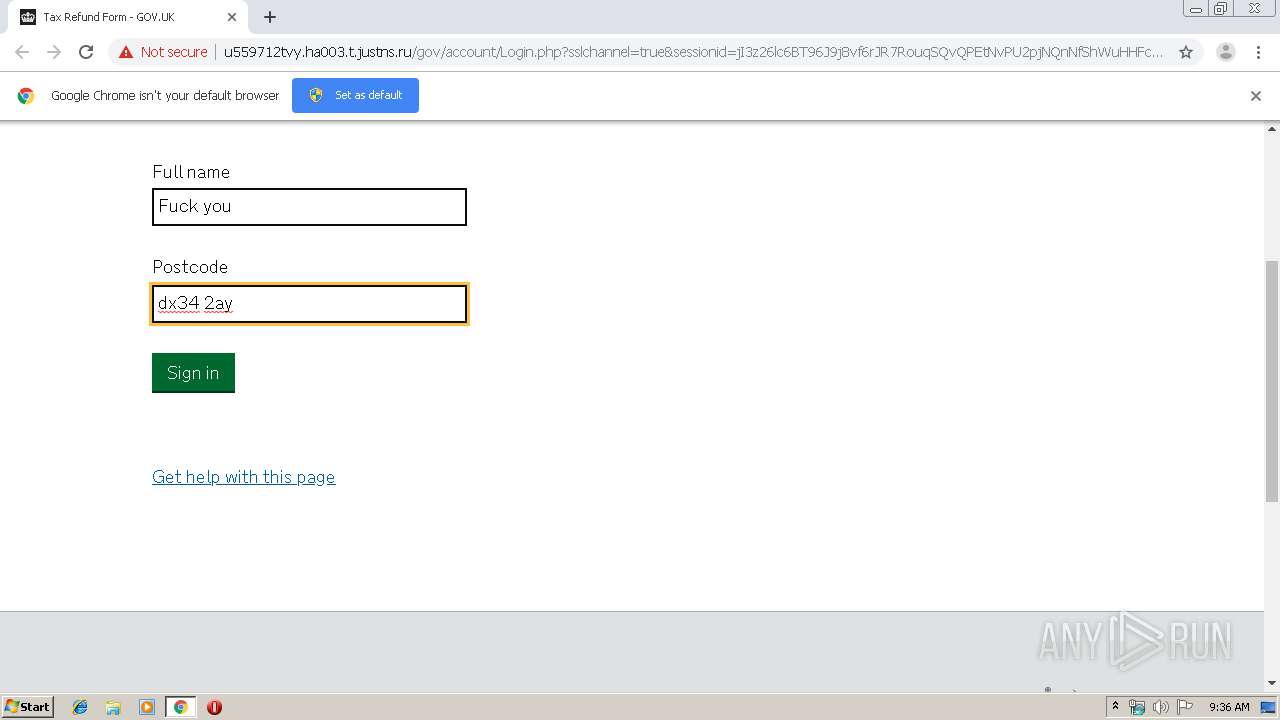
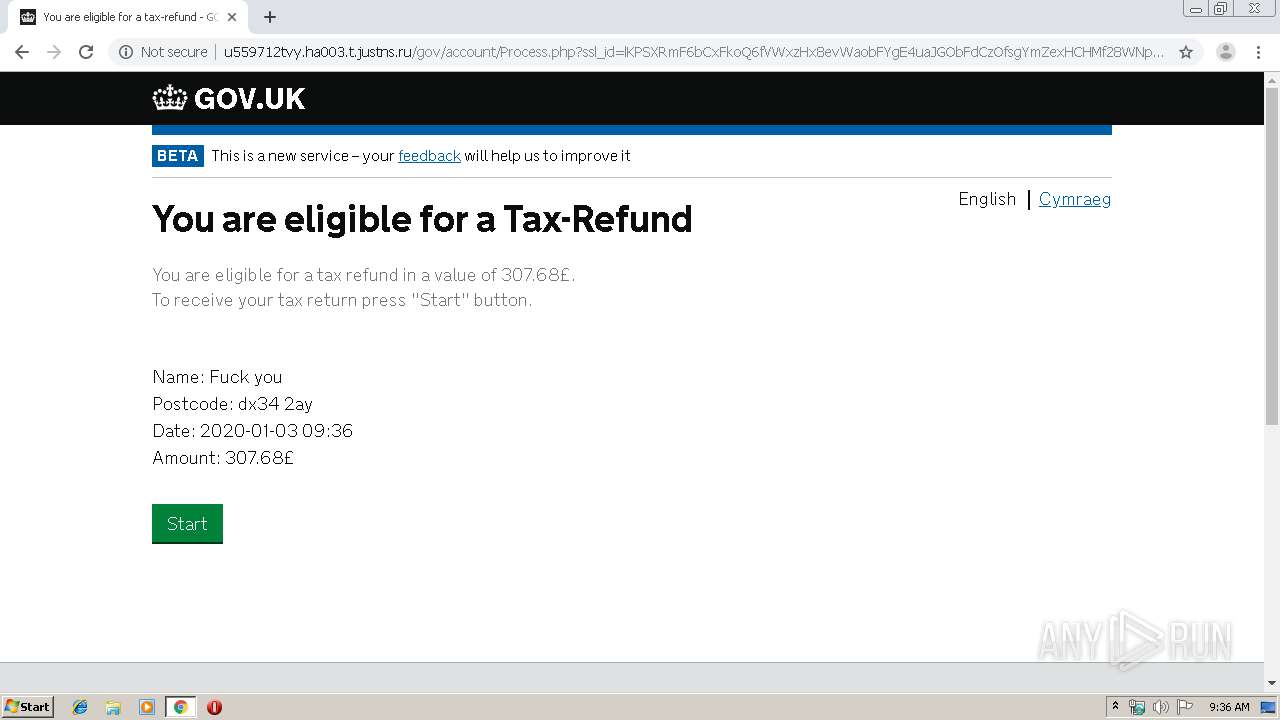
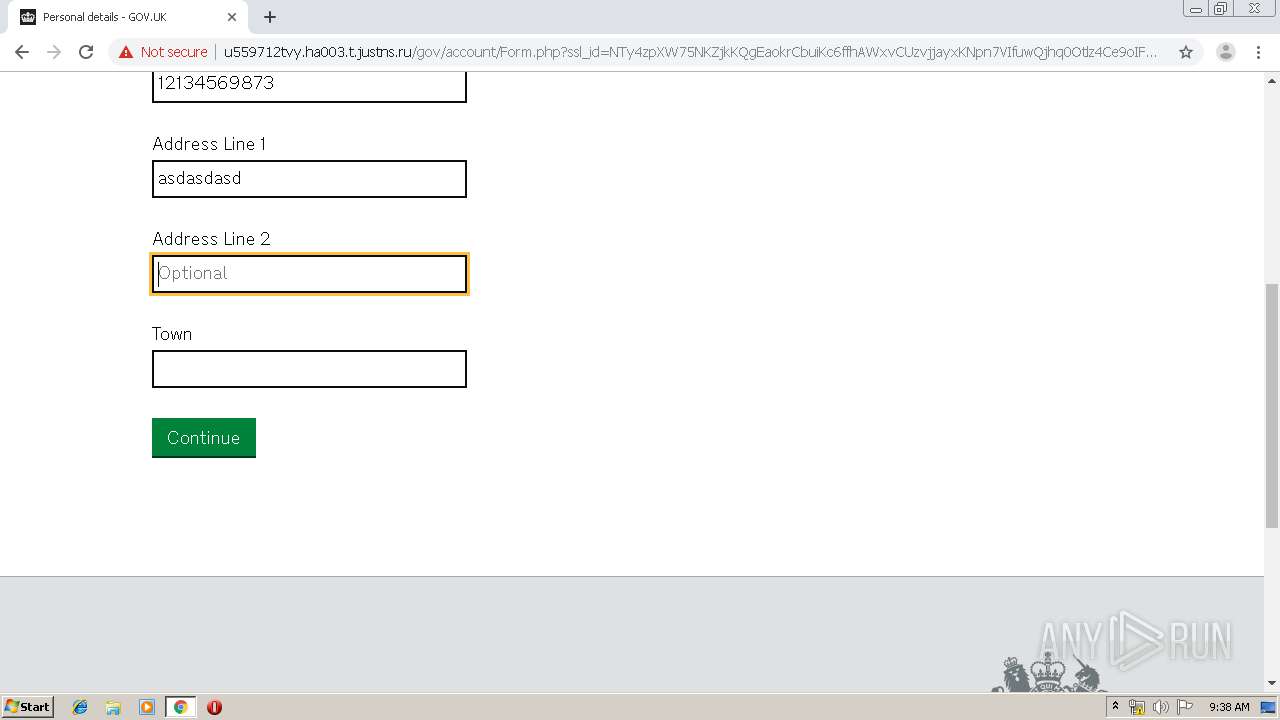
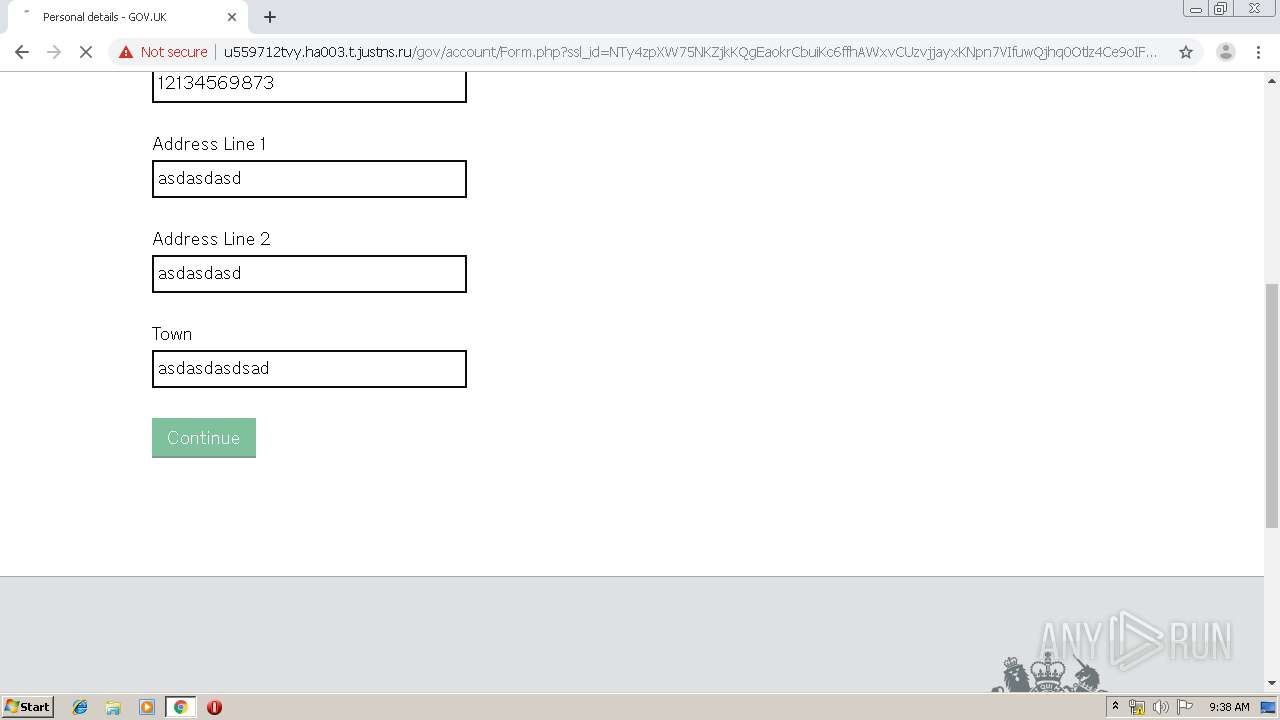
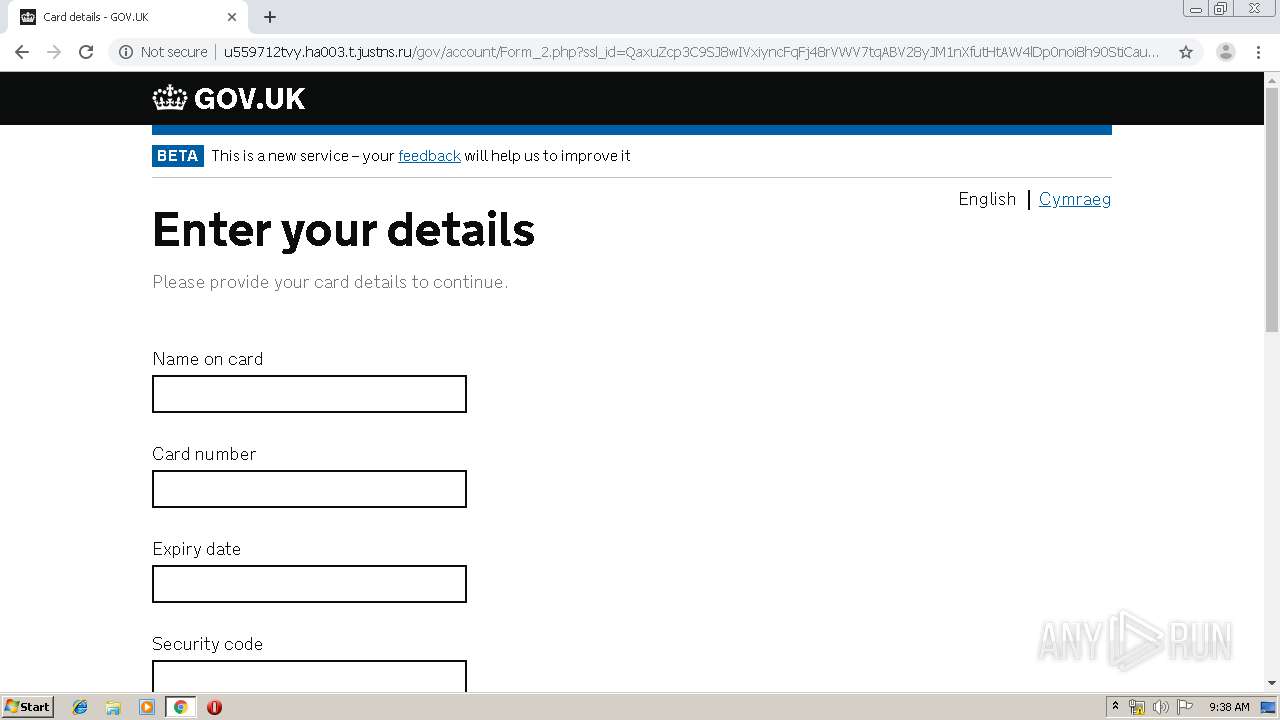
3792 | chrome.exe | GET | 200 | 185.22.155.27:80 | http://u559712tvy.ha003.t.justns.ru/gov/account/?url=https://www.google.com/search?q=messi&gclid=EAIaIQobChMIwLm78Jir5QIVlBMbCh1VBAYuEAEYASABEgK2z_D_BwE | RU | html | 239 b | suspicious |
3792 | chrome.exe | GET | 200 | 185.22.155.27:80 | http://u559712tvy.ha003.t.justns.ru/gov/account/Login.php?sslchannel=true&sessionid=jI3z26lc6BT96J9j8vf6rJR7RouqSQvQPEtNvPU2pjNQnNfShWuHHFcofq6TvCTwkyAaS8TdVORD7TiPSOJK6tEGHyQFblLzSniUPcRMzQYnFUEE5HqpUdr5Hz0QiEU1Hr | RU | html | 3.77 Kb | suspicious |
3792 | chrome.exe | GET | 200 | 185.22.155.27:80 | http://u559712tvy.ha003.t.justns.ru/gov/account/assets/files/template.css | RU | text | 3.79 Kb | suspicious |
3792 | chrome.exe | GET | 200 | 185.22.155.27:80 | http://u559712tvy.ha003.t.justns.ru/gov/account/assets/files/elements.css | RU | text | 7.04 Kb | suspicious |
3792 | chrome.exe | GET | 200 | 185.22.155.27:80 | http://u559712tvy.ha003.t.justns.ru/gov/account/assets/files/local-overrides.css | RU | text | 1.47 Kb | suspicious |
3792 | chrome.exe | GET | 200 | 185.22.155.27:80 | http://u559712tvy.ha003.t.justns.ru/gov/account/assets/files/fonts.css | RU | text | 194 Kb | suspicious |
3792 | chrome.exe | GET | 200 | 185.22.155.27:80 | http://u559712tvy.ha003.t.justns.ru/gov/account/assets/files/gov.png | RU | image | 1.02 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3792 | chrome.exe | 172.217.18.98:443 | adclick.g.doubleclick.net | Google Inc. | US | whitelisted |
3792 | chrome.exe | 216.58.205.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3792 | chrome.exe | 172.217.18.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
3792 | chrome.exe | 172.217.16.194:443 | www.googleadservices.com | Google Inc. | US | whitelisted |
3792 | chrome.exe | 172.217.18.4:443 | www.google.com | Google Inc. | US | whitelisted |
3792 | chrome.exe | 185.22.155.27:80 | u559712tvy.ha003.t.justns.ru | LLC Baxet | RU | malicious |
3792 | chrome.exe | 172.217.21.206:443 | clients1.google.com | Google Inc. | US | whitelisted |
3792 | chrome.exe | 54.172.47.69:3478 | stun.services.mozilla.com | Amazon.com, Inc. | US | whitelisted |
3792 | chrome.exe | 216.58.205.238:443 | clients2.google.com | Google Inc. | US | whitelisted |
3792 | chrome.exe | 172.217.16.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
adclick.g.doubleclick.net |
| whitelisted |
accounts.google.com |
| shared |
www.googleadservices.com |
| whitelisted |
u559712tvy.ha003.t.justns.ru |
| suspicious |
www.google.com |
| malicious |
clients1.google.com |
| whitelisted |
stun.services.mozilla.com |
| whitelisted |
clients2.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3792 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3792 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3792 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3792 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3792 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3792 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3792 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3792 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3792 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3792 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3 ETPRO signatures available at the full report