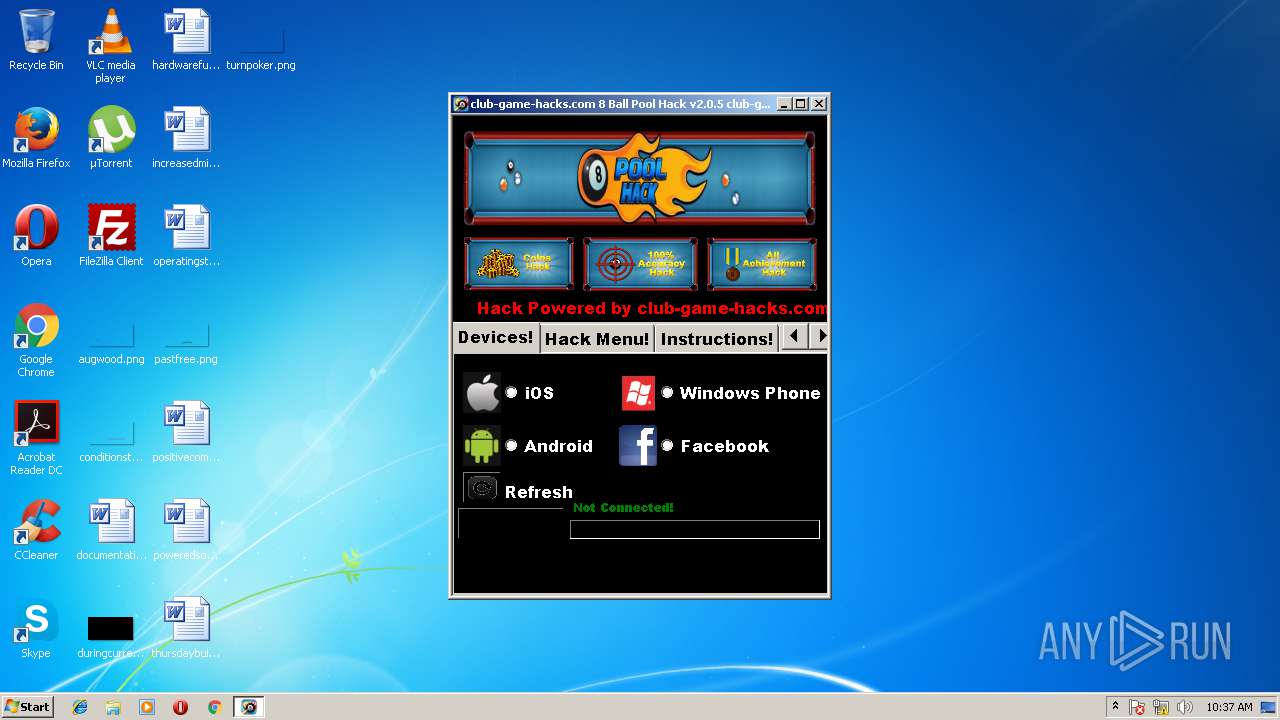
| File name: | 8 Ball Pool Hack Tool.exe |
| Full analysis: | https://app.any.run/tasks/2c88751e-1a12-4c44-8a90-858e3436d47c |
| Verdict: | Malicious activity |
| Analysis date: | June 08, 2018, 09:37:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 42318B3DF4A7D8BB0ABC50213D00CEFD |
| SHA1: | 6179428E4E42ECCA107B2E92A5FF6D1B0320EA44 |
| SHA256: | B6F6C32D567B6D4184555CDCDA3A9D668021CEE9044B8334B252764073921BE3 |
| SSDEEP: | 24576:Nyd+ZM2A4dyd+BeZj9lRkmuyUtzmYp9+AjEeiwg2jrYEUzEEhrum2008id3yd+:WLJz/loTddiIjrVFd6 |
MALICIOUS
No malicious indicators.SUSPICIOUS
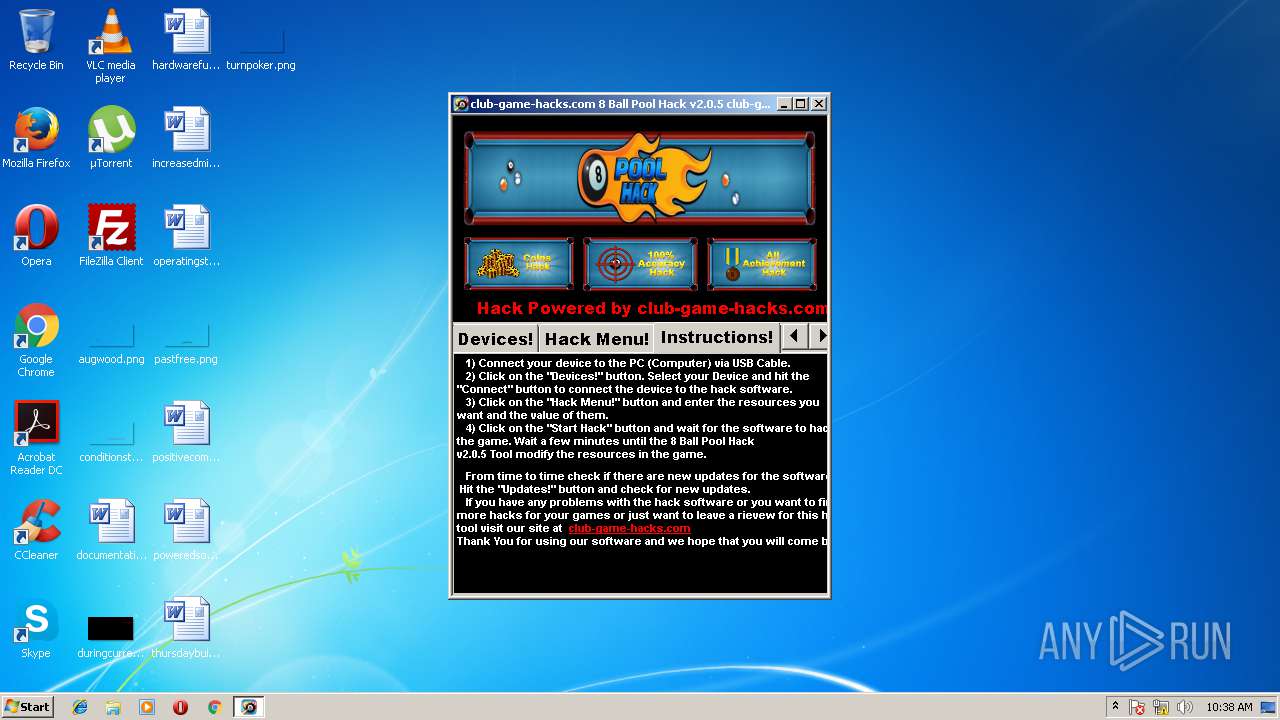
Starts Internet Explorer
- 8 Ball Pool Hack Tool.exe (PID: 3348)
INFO
Application launched itself
- iexplore.exe (PID: 2092)
Creates files in the user directory
- iexplore.exe (PID: 3516)
Reads Internet Cache Settings
- iexplore.exe (PID: 3516)
Dropped object may contain URL's
- iexplore.exe (PID: 3516)
- iexplore.exe (PID: 2092)
Reads internet explorer settings
- iexplore.exe (PID: 3516)
Changes internet zones settings
- iexplore.exe (PID: 2092)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (55.8) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21) |
| .scr | | | Windows screen saver (9.9) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:02:07 20:24:08+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 1550336 |
| InitializedDataSize: | 127488 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x17c71e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | New Hack Template |
| FileVersion: | 1.0.0.0 |
| InternalName: | New Hack Template.exe |
| LegalCopyright: | Copyright © 2014 |
| OriginalFileName: | New Hack Template.exe |
| ProductName: | New Hack Template |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 07-Feb-2015 19:24:08 |
| Debug artifacts: |
|
| FileDescription: | New Hack Template |
| FileVersion: | 1.0.0.0 |
| InternalName: | New Hack Template.exe |
| LegalCopyright: | Copyright © 2014 |
| OriginalFilename: | New Hack Template.exe |
| ProductName: | New Hack Template |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 07-Feb-2015 19:24:08 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x0017A724 | 0x0017A800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.95119 |
.sdata | 0x0017E000 | 0x00000091 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.08831 |
.rsrc | 0x00180000 | 0x0001ECEE | 0x0001EE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.89875 |
.reloc | 0x001A0000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 6.54627 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 6.74725 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 6.75207 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 6.70806 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.67841 | 76 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
37
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2092 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | 8 Ball Pool Hack Tool.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3348 | "C:\Users\admin\AppData\Local\Temp\8 Ball Pool Hack Tool.exe" | C:\Users\admin\AppData\Local\Temp\8 Ball Pool Hack Tool.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: New Hack Template Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3516 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2092 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
409
Read events
343
Write events
63
Delete events
3
Modification events
| (PID) Process: | (2092) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2092) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2092) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2092) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2092) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2092) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000006B000000010000000000000000000000000000000000000000000000400C35B347C7D301000000000000000000000000020000001700000000000000FE80000000000000D45917EAB3ED3D860B000000000000001700000000000000FE80000000000000D45917EAB3ED3D860B000000000000001C00000000000000000000000000000000000000000000000000000000000000170000000000000000000000000000000000FFFFC0A8640B000000000000000002000000C0A801640000000000000000000000000000000000000000000000000C00000C37D0000010A73800D8703600000000000000000000000000000000000000000000000000000000000000000000000000000000000000000081F800009000230090002300380023000000000000702C000A00000000000000F8412C00 | |||
| (PID) Process: | (2092) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {A803AFC1-6AFF-11E8-B27F-5254004AAD21} |
Value: 0 | |||
| (PID) Process: | (2092) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2092) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 5 | |||
| (PID) Process: | (2092) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E207060005000800090026000B00D501 | |||
Executable files
0
Suspicious files
2
Text files
7
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2092 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\2LKO8ICX\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2092 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3516 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\WF2FXMJU\club-game-hacks_com[1].txt | — | |
MD5:— | SHA256:— | |||
| 2092 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFA375A53C4F51FE88.TMP | — | |
MD5:— | SHA256:— | |||
| 2092 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF7B604D535C71D2C6.TMP | — | |
MD5:— | SHA256:— | |||
| 2092 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFF445E3EF061146EC.TMP | — | |
MD5:— | SHA256:— | |||
| 2092 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{A803AFC2-6AFF-11E8-B27F-5254004AAD21}.dat | — | |
MD5:— | SHA256:— | |||
| 2092 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF421B61E277B60197.TMP | — | |
MD5:— | SHA256:— | |||
| 2092 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{A803AFC1-6AFF-11E8-B27F-5254004AAD21}.dat | — | |
MD5:— | SHA256:— | |||
| 3516 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\7W7KPD6U\club-game-hacks_com[1].htm | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
6
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3516 | iexplore.exe | GET | 200 | 72.52.4.90:80 | http://sedoparking.com/frmpark/club-game-hacks.com/Skenzor6/park.js | US | html | 631 b | whitelisted |
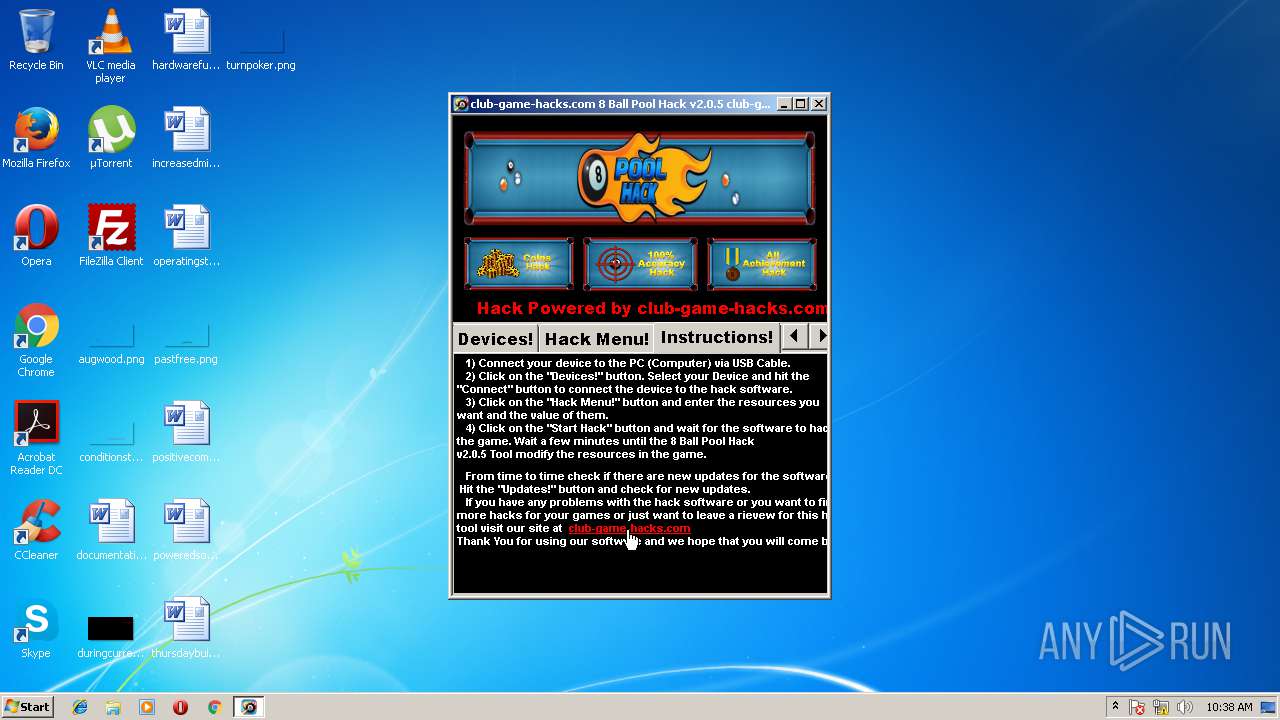
3516 | iexplore.exe | GET | 200 | 204.11.56.48:80 | http://club-game-hacks.com/ | VG | html | 545 b | malicious |
3516 | iexplore.exe | GET | 200 | 204.11.56.48:80 | http://club-game-hacks.com/ | VG | html | 545 b | malicious |
3516 | iexplore.exe | GET | 200 | 72.52.4.90:80 | http://sedoparking.com/frmpark/club-game-hacks.com/Skenzor6/park.js | US | html | 631 b | whitelisted |
2092 | iexplore.exe | GET | 404 | 204.11.56.48:80 | http://club-game-hacks.com/favicon.ico | VG | text | 30 b | malicious |
3516 | iexplore.exe | GET | — | 204.11.56.48:80 | http://club-game-hacks.com/ | VG | — | — | malicious |
2092 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2092 | iexplore.exe | GET | 404 | 204.11.56.48:80 | http://club-game-hacks.com/favicon.ico | VG | text | 30 b | malicious |
3516 | iexplore.exe | GET | 200 | 172.217.21.226:80 | http://pagead2.googlesyndication.com/apps/domainpark/show_afd_ads.js | US | text | 1.44 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2092 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3516 | iexplore.exe | 204.11.56.48:80 | club-game-hacks.com | Confluence Networks Inc | VG | malicious |
3516 | iexplore.exe | 172.217.21.226:80 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
3516 | iexplore.exe | 72.52.4.90:80 | sedoparking.com | Akamai Technologies, Inc. | US | whitelisted |
2092 | iexplore.exe | 204.11.56.48:80 | club-game-hacks.com | Confluence Networks Inc | VG | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
club-game-hacks.com |
| malicious |
sedoparking.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |