| File name: | LOIC-1.0.8-binary.zip |
| Full analysis: | https://app.any.run/tasks/8324a472-fc6d-48a7-83f9-fed28fbbb1df |
| Verdict: | Malicious activity |
| Analysis date: | January 24, 2022, 21:05:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | C615DA1584CF050CF81A08D40309D735 |
| SHA1: | FF00F68B03F7BBC785284ABD95A54D5B98F7DB9B |
| SHA256: | B6D6E0D1DCE867836A684A0AF278E46ED4A50BE49A784AB7BFCB3ED59841C9D0 |
| SSDEEP: | 3072:n1sQ9BKWms487f1j/XjSGrJmjJ7cAs1QRls:nuQ9Tmd41jfD0lgXQRG |
MALICIOUS
Application was dropped or rewritten from another process
- LOIC.exe (PID: 4064)
SUSPICIOUS
Checks supported languages
- WinRAR.exe (PID: 2984)
- LOIC.exe (PID: 4064)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 2984)
Reads Microsoft Outlook installation path
- LOIC.exe (PID: 4064)
Reads the computer name
- WinRAR.exe (PID: 2984)
- LOIC.exe (PID: 4064)
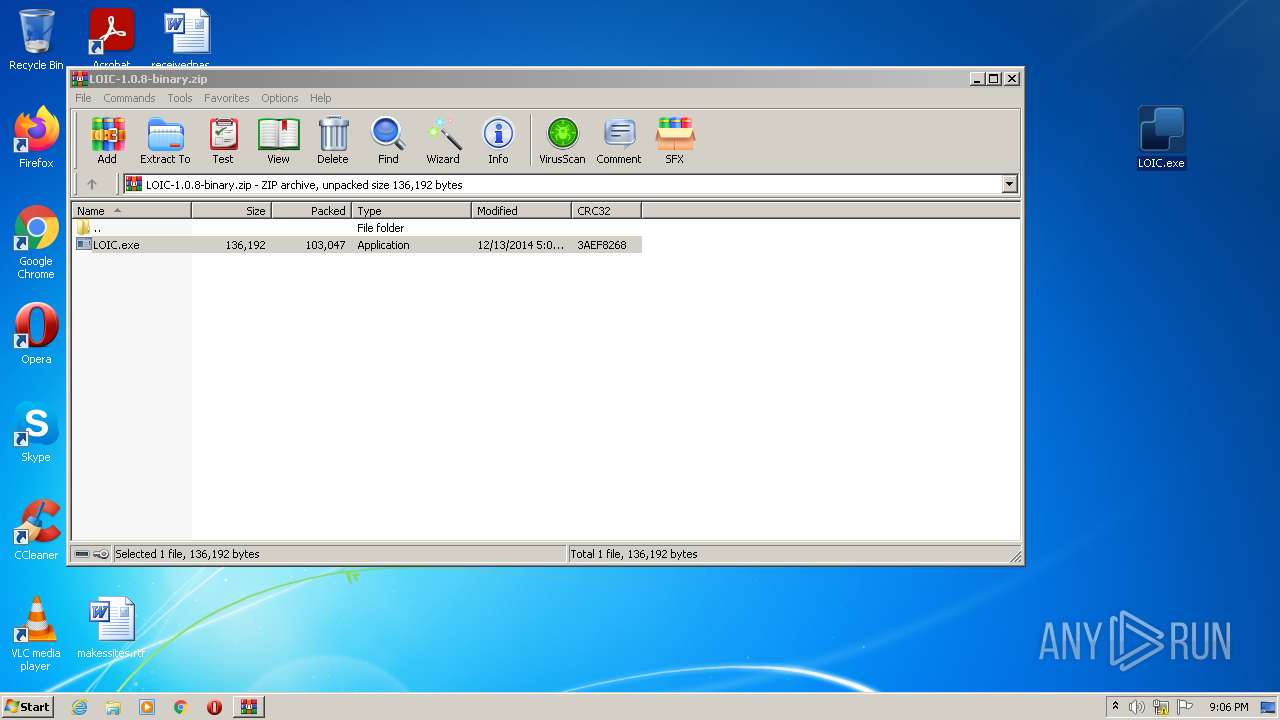
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2984)
Creates files in the user directory
- LOIC.exe (PID: 4064)
Reads internet explorer settings
- LOIC.exe (PID: 4064)
Reads CPU info
- LOIC.exe (PID: 4064)
INFO
Manual execution by user
- LOIC.exe (PID: 4064)
Reads settings of System Certificates
- LOIC.exe (PID: 4064)
Checks Windows Trust Settings
- LOIC.exe (PID: 4064)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
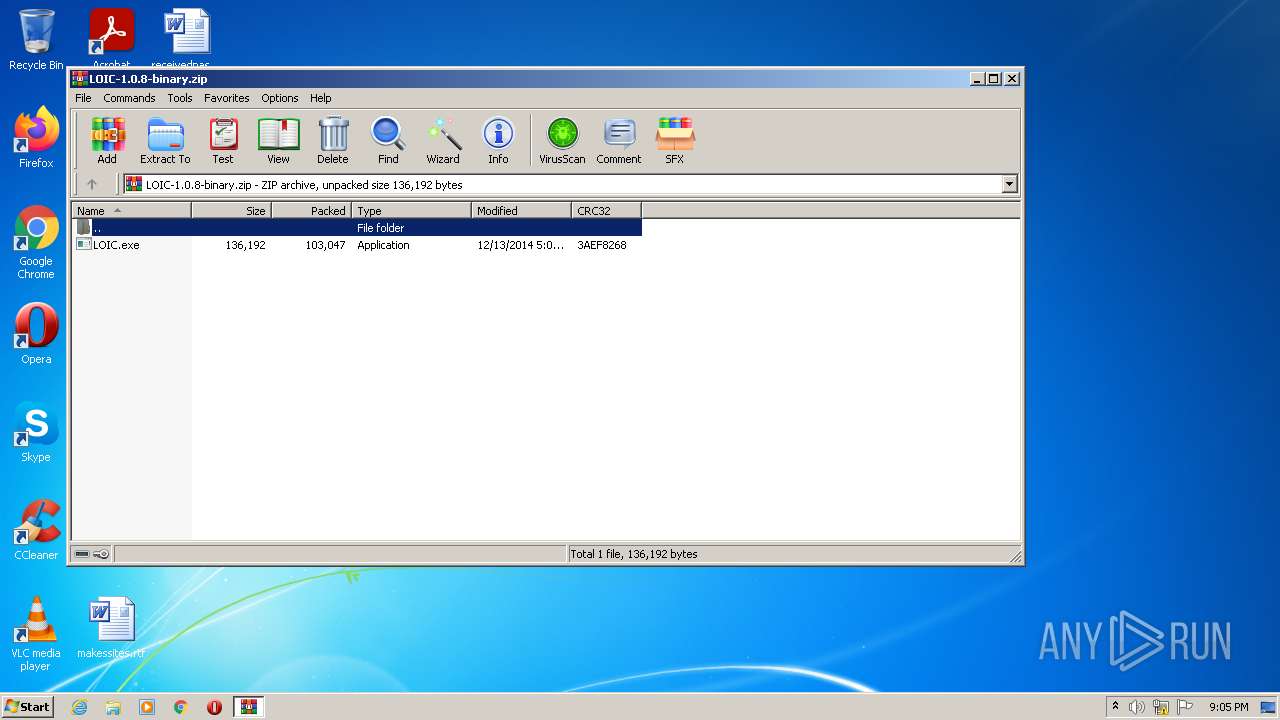
| ZipFileName: | LOIC.exe |
|---|---|
| ZipUncompressedSize: | 136192 |
| ZipCompressedSize: | 103047 |
| ZipCRC: | 0x3aef8268 |
| ZipModifyDate: | 2014:12:12 21:09:00 |
| ZipCompression: | Deflated |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 20 |
Total processes
37
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2984 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\LOIC-1.0.8-binary.zip" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
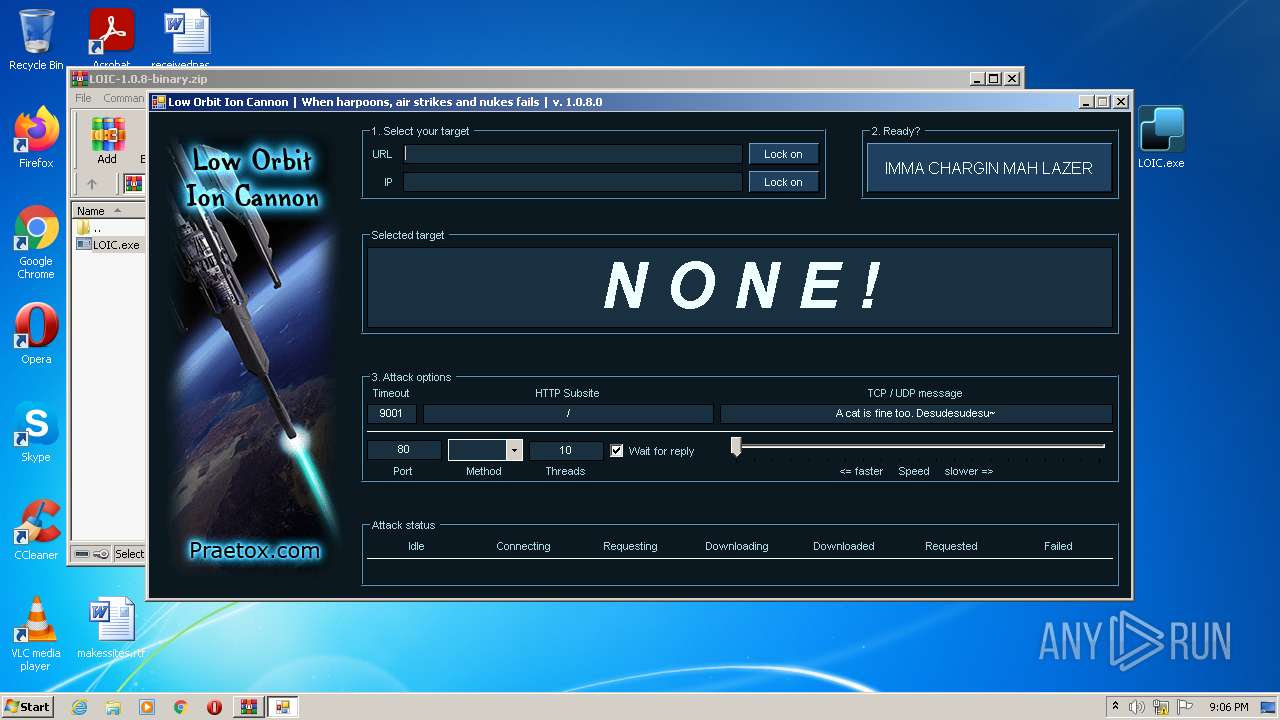
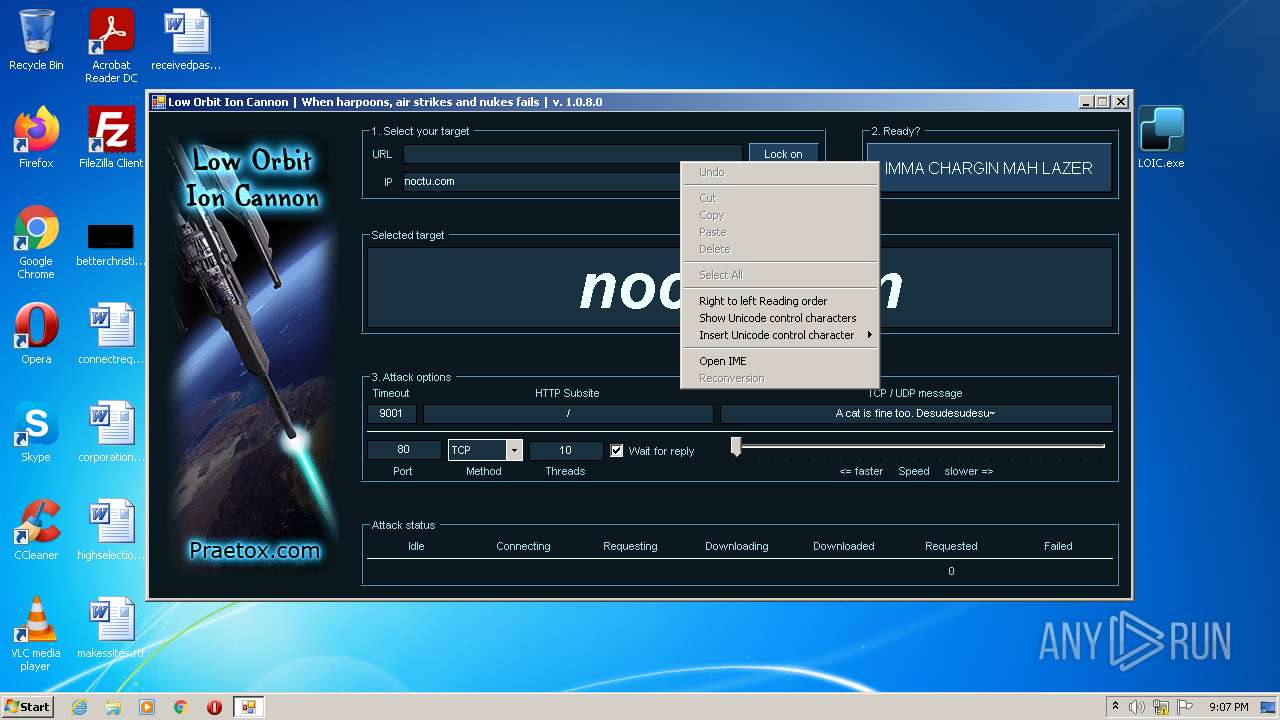
| 4064 | "C:\Users\admin\Desktop\LOIC.exe" | C:\Users\admin\Desktop\LOIC.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Low Orbit Ion Cannon Exit code: 0 Version: 1.0.8.0 Modules
| |||||||||||||||
Total events
6 380
Read events
6 315
Write events
65
Delete events
0
Modification events
| (PID) Process: | (2984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2984) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\LOIC-1.0.8-binary.zip | |||
| (PID) Process: | (2984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
1
Suspicious files
9
Text files
9
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4064 | LOIC.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 4064 | LOIC.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_D975BBA8033175C8D112023D8A7A8AD6 | binary | |
MD5:— | SHA256:— | |||
| 4064 | LOIC.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | der | |
MD5:— | SHA256:— | |||
| 4064 | LOIC.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E573CDF4C6D731D56A665145182FD759_6B24471AF7D42D8A96573B48B6B5FC54 | der | |
MD5:— | SHA256:— | |||
| 4064 | LOIC.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E573CDF4C6D731D56A665145182FD759_6B24471AF7D42D8A96573B48B6B5FC54 | binary | |
MD5:— | SHA256:— | |||
| 4064 | LOIC.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | binary | |
MD5:— | SHA256:— | |||
| 4064 | LOIC.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | der | |
MD5:— | SHA256:— | |||
| 4064 | LOIC.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | binary | |
MD5:— | SHA256:— | |||
| 4064 | LOIC.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_D975BBA8033175C8D112023D8A7A8AD6 | der | |
MD5:— | SHA256:— | |||
| 4064 | LOIC.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22 405
TCP/UDP connections
24 132
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4064 | LOIC.exe | GET | — | 104.143.9.210:80 | http://104.143.9.210:80/ | US | — | — | malicious |
4064 | LOIC.exe | GET | — | 104.143.9.210:80 | http://104.143.9.210:80/ | US | — | — | malicious |
4064 | LOIC.exe | GET | — | 104.143.9.210:80 | http://104.143.9.210:80/ | US | — | — | malicious |
4064 | LOIC.exe | GET | — | 104.143.9.210:80 | http://104.143.9.210:80/ | US | — | — | malicious |
4064 | LOIC.exe | GET | — | 104.143.9.210:80 | http://104.143.9.210:80/ | US | — | — | malicious |
4064 | LOIC.exe | GET | — | 104.143.9.210:80 | http://104.143.9.210:80/ | US | — | — | malicious |
4064 | LOIC.exe | GET | — | 104.143.9.210:80 | http://104.143.9.210:80/ | US | — | — | malicious |
4064 | LOIC.exe | GET | — | 104.143.9.210:80 | http://104.143.9.210:80/ | US | — | — | malicious |
4064 | LOIC.exe | GET | — | 104.143.9.210:80 | http://104.143.9.210:80/ | US | — | — | malicious |
4064 | LOIC.exe | GET | — | 104.143.9.210:80 | http://104.143.9.210:80/ | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4064 | LOIC.exe | 67.199.248.16:443 | j.mp | Bitly Inc | US | shared |
4064 | LOIC.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
4064 | LOIC.exe | 142.250.186.67:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
4064 | LOIC.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
4064 | LOIC.exe | 104.143.9.210:80 | noctu.com | VegasNAP, LLC | US | malicious |
4064 | LOIC.exe | 52.179.188.206:443 | loicweb.azurewebsites.net | Microsoft Corporation | US | unknown |
4064 | LOIC.exe | 216.58.212.174:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
4064 | LOIC.exe | 152.199.21.175:443 | az416426.vo.msecnd.net | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 104.143.9.210:80 | noctu.com | VegasNAP, LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
j.mp |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
loicweb.azurewebsites.net |
| whitelisted |
az416426.vo.msecnd.net |
| whitelisted |
www.google-analytics.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
noctu.com |
| unknown |