| File name: | vcredist_2015-2019_x64.exe |
| Full analysis: | https://app.any.run/tasks/8b75e4a0-09e3-4c02-b86c-04d47ce01545 |
| Verdict: | Malicious activity |
| Analysis date: | June 16, 2024, 13:59:56 |
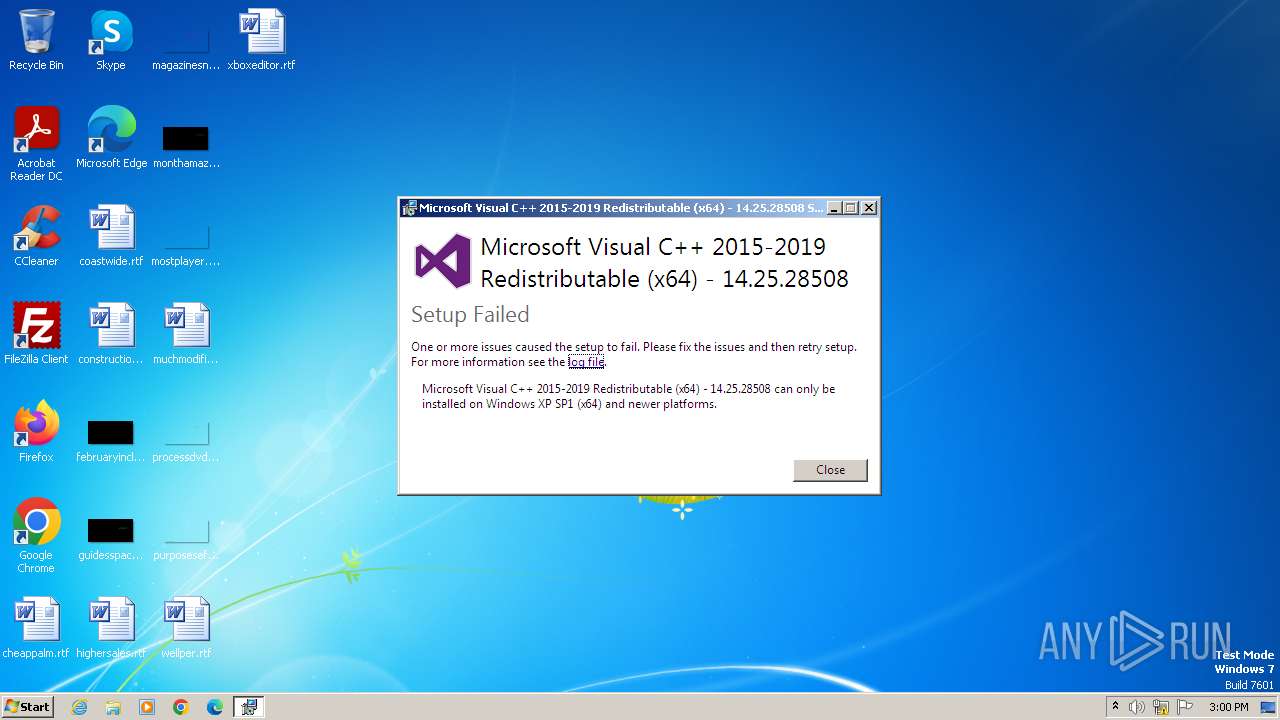
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | F0248D477E74687C5619AE16498B13D4 |
| SHA1: | 9ED4B091148C9B53F66B3F2C69BE7E60E74C486A |
| SHA256: | B6C82087A2C443DB859FDBEAAE7F46244D06C3F2A7F71C35E50358066253DE52 |
| SSDEEP: | 393216:q5lptVYmfr7yBG/4WoI+j6LTinXKSf0fzTDv8:q7pttD7yBG/uljIinXj0fQ |
MALICIOUS
Drops the executable file immediately after the start
- vcredist_2015-2019_x64.exe (PID: 3976)
- vcredist_2015-2019_x64.exe (PID: 3996)
SUSPICIOUS
Starts a Microsoft application from unusual location
- vcredist_2015-2019_x64.exe (PID: 3976)
- vcredist_2015-2019_x64.exe (PID: 3996)
Process drops legitimate windows executable
- vcredist_2015-2019_x64.exe (PID: 3976)
Executable content was dropped or overwritten
- vcredist_2015-2019_x64.exe (PID: 3976)
- vcredist_2015-2019_x64.exe (PID: 3996)
Searches for installed software
- vcredist_2015-2019_x64.exe (PID: 3996)
INFO
Checks supported languages
- vcredist_2015-2019_x64.exe (PID: 3976)
- vcredist_2015-2019_x64.exe (PID: 3996)
Create files in a temporary directory
- vcredist_2015-2019_x64.exe (PID: 3976)
- vcredist_2015-2019_x64.exe (PID: 3996)
Reads the computer name
- vcredist_2015-2019_x64.exe (PID: 3996)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:11:18 21:37:28+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit, Removable run from swap, Net run from swap |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 301056 |
| InitializedDataSize: | 161280 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2e06d |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 14.25.28508.3 |
| ProductVersionNumber: | 14.25.28508.3 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Microsoft Visual C++ 2015-2019 Redistributable (x64) - 14.25.28508 |
| FileVersion: | 14.25.28508.3 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) Microsoft Corporation. All rights reserved. |
| OriginalFileName: | VC_redist.x64.exe |
| ProductName: | Microsoft Visual C++ 2015-2019 Redistributable (x64) - 14.25.28508 |
| ProductVersion: | 14.25.28508.3 |
Total processes
33
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3976 | "C:\Users\admin\AppData\Local\Temp\vcredist_2015-2019_x64.exe" | C:\Users\admin\AppData\Local\Temp\vcredist_2015-2019_x64.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Visual C++ 2015-2019 Redistributable (x64) - 14.25.28508 Exit code: 1 Version: 14.25.28508.3 Modules
| |||||||||||||||
| 3996 | "C:\Users\admin\AppData\Local\Temp\{601F5EF8-6DFD-489F-8399-E95997C16654}\.cr\vcredist_2015-2019_x64.exe" -burn.clean.room="C:\Users\admin\AppData\Local\Temp\vcredist_2015-2019_x64.exe" -burn.filehandle.attached=152 -burn.filehandle.self=160 | C:\Users\admin\AppData\Local\Temp\{601F5EF8-6DFD-489F-8399-E95997C16654}\.cr\vcredist_2015-2019_x64.exe | vcredist_2015-2019_x64.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Visual C++ 2015-2019 Redistributable (x64) - 14.25.28508 Exit code: 1 Version: 14.25.28508.3 Modules
| |||||||||||||||
Total events
1 205
Read events
1 205
Write events
0
Delete events
0
Modification events
Executable files
2
Suspicious files
0
Text files
32
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3996 | vcredist_2015-2019_x64.exe | C:\Users\admin\AppData\Local\Temp\{89F3085B-7F10-4985-8133-A7C06A432730}\.ba\thm.xml | xml | |
MD5:F62729C6D2540015E072514226C121C7 | SHA256:F13BAE0EC08C91B4A315BB2D86EE48FADE597E7A5440DCE6F751F98A3A4D6916 | |||
| 3976 | vcredist_2015-2019_x64.exe | C:\Users\admin\AppData\Local\Temp\{601F5EF8-6DFD-489F-8399-E95997C16654}\.cr\vcredist_2015-2019_x64.exe | executable | |
MD5:843288FD72A1152B50B4E4B7344BB592 | SHA256:82C3E3423E48BAFCDD726624EB7FD3E00674E50E4B6ACDCAC408FE8FAE43B022 | |||
| 3996 | vcredist_2015-2019_x64.exe | C:\Users\admin\AppData\Local\Temp\{89F3085B-7F10-4985-8133-A7C06A432730}\.ba\1031\license.rtf | text | |
MD5:C2CFA4CE43DFF1FCD200EDD2B1212F0A | SHA256:F861DB23B972FAAA54520558810387D742878947057CF853DC74E5F6432E6A1B | |||
| 3996 | vcredist_2015-2019_x64.exe | C:\Users\admin\AppData\Local\Temp\{89F3085B-7F10-4985-8133-A7C06A432730}\.ba\1028\license.rtf | text | |
MD5:B7F65A3A169484D21FA075CCA79083ED | SHA256:32585B93E69272B6D42DAC718E04D954769FE31AC9217C6431510E9EEAD78C49 | |||
| 3996 | vcredist_2015-2019_x64.exe | C:\Users\admin\AppData\Local\Temp\{89F3085B-7F10-4985-8133-A7C06A432730}\.ba\license.rtf | text | |
MD5:2EABBB391ACB89942396DF5C1CA2BAD8 | SHA256:E3156D170014CED8D17A02B3C4FF63237615E5C2A8983B100A78CB1F881D6F38 | |||
| 3996 | vcredist_2015-2019_x64.exe | C:\Users\admin\AppData\Local\Temp\{89F3085B-7F10-4985-8133-A7C06A432730}\.ba\thm.wxl | xml | |
MD5:FBFCBC4DACC566A3C426F43CE10907B6 | SHA256:70400F181D00E1769774FF36BCD8B1AB5FBC431418067D31B876D18CC04EF4CE | |||
| 3996 | vcredist_2015-2019_x64.exe | C:\Users\admin\AppData\Local\Temp\{89F3085B-7F10-4985-8133-A7C06A432730}\.ba\1028\thm.wxl | xml | |
MD5:472ABBEDCBAD24DBA5B5F5E8D02C340F | SHA256:8E2E660DFB66CB453E17F1B6991799678B1C8B350A55F9EBE2BA0028018A15AD | |||
| 3996 | vcredist_2015-2019_x64.exe | C:\Users\admin\AppData\Local\Temp\{89F3085B-7F10-4985-8133-A7C06A432730}\.ba\1029\thm.wxl | xml | |
MD5:16343005D29EC431891B02F048C7F581 | SHA256:07FB3EC174F25DFBE532D9D739234D9DFDA8E9D34F01FE660C5B4D56989FA779 | |||
| 3996 | vcredist_2015-2019_x64.exe | C:\Users\admin\AppData\Local\Temp\{89F3085B-7F10-4985-8133-A7C06A432730}\.ba\1031\thm.wxl | xml | |
MD5:561F3F32DB2453647D1992D4D932E872 | SHA256:8E0DCA6E085744BFCBFF46F7DCBCFA6FBD722DFA52013EE8CEEAF682D7509581 | |||
| 3996 | vcredist_2015-2019_x64.exe | C:\Users\admin\AppData\Local\Temp\{89F3085B-7F10-4985-8133-A7C06A432730}\.ba\1041\thm.wxl | xml | |
MD5:DC81ED54FD28FC6DB6F139C8DA1BDED6 | SHA256:6B9BBF90D75CFA7D943F036C01602945FE2FA786C6173E22ACB7AFE18375C7EA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |