| File name: | 15.msi |
| Full analysis: | https://app.any.run/tasks/399f1824-7a3e-4bd9-8619-8fd7e1bcdb9f |
| Verdict: | Malicious activity |
| Analysis date: | February 14, 2025, 02:29:18 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: Backstop, Author: Lummox Carbonado, Keywords: Installer, Comments: This installer database contains the logic and data required to install Backstop., Template: Intel;1033, Revision Number: {E74B25AD-2BC3-4BD0-A758-01B7052B048A}, Create Time/Date: Thu Feb 13 17:43:28 2025, Last Saved Time/Date: Thu Feb 13 17:43:28 2025, Number of Pages: 500, Number of Words: 10, Name of Creating Application: WiX Toolset (4.0.0.0), Security: 2 |
| MD5: | C3F1E44CC3C9989E7B2565C9D94A783C |
| SHA1: | 163A046B4DA9A599742E3EBF2DC98F6B1BB8C8D8 |
| SHA256: | B6BF2F947B782BD0F30BC93F0F8CF4BDFD8B9F5F2D287731DA5D8F07CCB5D3DC |
| SSDEEP: | 98304:a7Pwr2DAqdmysudq1t8bWJ4r8V4dbCLG7GR6TaZnnkQYGtx2MGTIjcyHKtq2ByXz:qnKkn8ijLannOX2hNZEGbf4Aomk |
MALICIOUS
GENERIC has been found (auto)
- msiexec.exe (PID: 6468)
- Ahnenblatt4.exe (PID: 4592)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 6720)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 6604)
Executable content was dropped or overwritten
- Ahnenblatt4.exe (PID: 4592)
- cmd.exe (PID: 2756)
Starts itself from another location
- Ahnenblatt4.exe (PID: 4592)
Starts CMD.EXE for commands execution
- Ahnenblatt4.exe (PID: 5200)
Reads the date of Windows installation
- Chromewizard_test_v2.exe (PID: 1476)
The executable file from the user directory is run by the CMD process
- Chromewizard_test_v2.exe (PID: 1476)
INFO
Reads the computer name
- msiexec.exe (PID: 6604)
- Ahnenblatt4.exe (PID: 4592)
- Ahnenblatt4.exe (PID: 5200)
- Chromewizard_test_v2.exe (PID: 1476)
The sample compiled with english language support
- msiexec.exe (PID: 6468)
- msiexec.exe (PID: 6604)
- Ahnenblatt4.exe (PID: 4592)
Manages system restore points
- SrTasks.exe (PID: 5432)
Checks supported languages
- msiexec.exe (PID: 6604)
- Ahnenblatt4.exe (PID: 4592)
- Ahnenblatt4.exe (PID: 5200)
- Chromewizard_test_v2.exe (PID: 1476)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6604)
Creates files or folders in the user directory
- msiexec.exe (PID: 6604)
- Ahnenblatt4.exe (PID: 4592)
Creates a software uninstall entry
- msiexec.exe (PID: 6604)
Create files in a temporary directory
- Ahnenblatt4.exe (PID: 5200)
Checks proxy server information
- Chromewizard_test_v2.exe (PID: 1476)
Reads the machine GUID from the registry
- Chromewizard_test_v2.exe (PID: 1476)
Reads the software policy settings
- Chromewizard_test_v2.exe (PID: 1476)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Installer (100) |
|---|
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
| Subject: | Backstop |
| Author: | Lummox Carbonado |
| Keywords: | Installer |
| Comments: | This installer database contains the logic and data required to install Backstop. |
| Template: | Intel;1033 |
| RevisionNumber: | {E74B25AD-2BC3-4BD0-A758-01B7052B048A} |
| CreateDate: | 2025:02:13 17:43:28 |
| ModifyDate: | 2025:02:13 17:43:28 |
| Pages: | 500 |
| Words: | 10 |
| Software: | WiX Toolset (4.0.0.0) |
| Security: | Read-only recommended |
Total processes
138
Monitored processes
10
Malicious processes
2
Suspicious processes
1
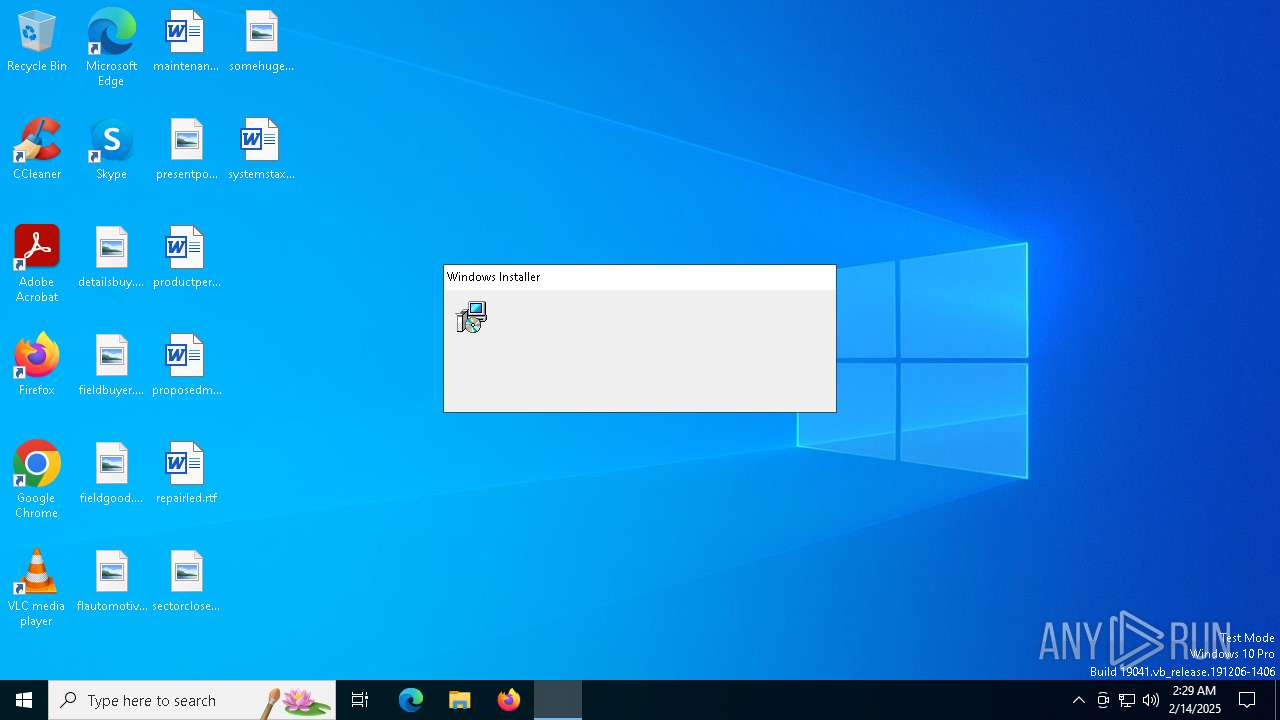
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1476 | C:\Users\admin\AppData\Local\Temp\Chromewizard_test_v2.exe | C:\Users\admin\AppData\Local\Temp\Chromewizard_test_v2.exe | cmd.exe | ||||||||||||
User: admin Company: Nenad Hrg (SoftwareOK.com) Integrity Level: MEDIUM Description: Q-Dir Version: 11,4,4,0 Modules
| |||||||||||||||
| 2756 | C:\WINDOWS\SysWOW64\cmd.exe | C:\Windows\SysWOW64\cmd.exe | Ahnenblatt4.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4388 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4592 | "C:\Users\admin\AppData\Roaming\Galleria\Ahnenblatt4.exe" | C:\Users\admin\AppData\Roaming\Galleria\Ahnenblatt4.exe | msiexec.exe | ||||||||||||
User: admin Company: Dirk Böttcher Integrity Level: MEDIUM Description: Ahnenblatt Exit code: 0 Version: 4.20.0.4 Modules
| |||||||||||||||
| 5200 | C:\Users\admin\AppData\Roaming\validservice_yc\Ahnenblatt4.exe | C:\Users\admin\AppData\Roaming\validservice_yc\Ahnenblatt4.exe | — | Ahnenblatt4.exe | |||||||||||
User: admin Company: Dirk Böttcher Integrity Level: MEDIUM Description: Ahnenblatt Exit code: 1 Version: 4.20.0.4 Modules
| |||||||||||||||
| 5432 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6468 | "C:\Windows\System32\msiexec.exe" /i C:\Users\admin\AppData\Local\Temp\15.msi | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6604 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6720 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 432
Read events
3 168
Write events
246
Delete events
18
Modification events
| (PID) Process: | (6604) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000C0E1D745887EDB01CC190000F0190000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6604) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000C0E1D745887EDB01CC190000F0190000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6604) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000D5496046887EDB01CC190000F0190000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6604) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000D5496046887EDB01CC190000F0190000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6604) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 480000000000000045746746887EDB01CC190000F0190000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6604) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000B73B6C46887EDB01CC190000F0190000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6604) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (6604) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000CCB71047887EDB01CC190000F0190000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6604) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000147F1547887EDB01CC190000E41A0000E8030000010000000000000000000000A7332AA04650564B953295A3FC6F6F5700000000000000000000000000000000 | |||
| (PID) Process: | (6720) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000B0712147887EDB01401A0000901A0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
7
Suspicious files
21
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6604 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 6604 | msiexec.exe | C:\Windows\Installer\13f0cc.msi | — | |
MD5:— | SHA256:— | |||
| 6604 | msiexec.exe | C:\Users\admin\AppData\Roaming\Galleria\torchlight.mkv | — | |
MD5:— | SHA256:— | |||
| 6604 | msiexec.exe | C:\Windows\Installer\13f0ce.msi | — | |
MD5:— | SHA256:— | |||
| 6604 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{a02a33a7-5046-4b56-9532-95a3fc6f6f57}_OnDiskSnapshotProp | binary | |
MD5:39F52EF4BEE0A64D474CC8CF7103AAC2 | SHA256:17DF03E20DC4B1C2F5BEA65F2D017FA7B1A8E60E6B35F7163223A4536C61673E | |||
| 6604 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:39F52EF4BEE0A64D474CC8CF7103AAC2 | SHA256:17DF03E20DC4B1C2F5BEA65F2D017FA7B1A8E60E6B35F7163223A4536C61673E | |||
| 6604 | msiexec.exe | C:\Users\admin\AppData\Roaming\Galleria\cc32290mt.dll | executable | |
MD5:A5A2A06E37069BF91326C8231F427B3A | SHA256:1B5870E925FB5C43B49F24F2A174DA1359CE753BD888277746F62A132749FC55 | |||
| 6604 | msiexec.exe | C:\Users\admin\AppData\Roaming\Galleria\Ahnenblatt4.exe | executable | |
MD5:950F3BEBB7563EE8354B21EF9CBEA4A2 | SHA256:8F4F53BC02348A549F3437444AACEC43EAE5F90875EA3C5EC96600BA1CB4A061 | |||
| 6604 | msiexec.exe | C:\Windows\Installer\MSIF35C.tmp | binary | |
MD5:8BA7CC92016443EEF594B8B0EF1A957A | SHA256:DFCEE153199E7E797007132798291BFEFCA269C336AFD1CE185C836D8649CB4D | |||
| 6604 | msiexec.exe | C:\Windows\Temp\~DFA407EDCEA1A1C596.TMP | binary | |
MD5:BF619EAC0CDF3F68D496EA9344137E8B | SHA256:076A27C79E5ACE2A3D47F9DD2E83E4FF6EA8872B3C2218F66C92B89B55F36560 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
31
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4328 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4912 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4912 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6708 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4328 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1076 | svchost.exe | 23.35.238.131:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
1176 | svchost.exe | 20.190.159.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 184.30.131.245:80 | — | AKAMAI-AS | US | unknown |
5064 | SearchApp.exe | 2.19.96.120:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4912 | SIHClient.exe | 20.109.210.53:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
www.bing.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |