| File name: | upacked.exe |
| Full analysis: | https://app.any.run/tasks/ae67389d-cadd-47f9-8955-068cfd2af75e |
| Verdict: | Malicious activity |
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
| Analysis date: | February 11, 2019, 12:05:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 2CEC5A980C694D850E9BBBB0D03BDD0F |
| SHA1: | C2F11A6FF3AF83B2EE96246C640E8CA7CD481CB7 |
| SHA256: | B6AD652A3259130E5B71144F718F99402B30D098DD9DEA8877AE09BC0B8B169F |
| SSDEEP: | 3072:4ViGkEvvHqkEsQ3vkpUSBzdIYWi1wnznrMFf9a6/9IwLq5p+9h/jFWymPXvn:4VlrXFED3vdAzCYLbeOaY9hOPX |
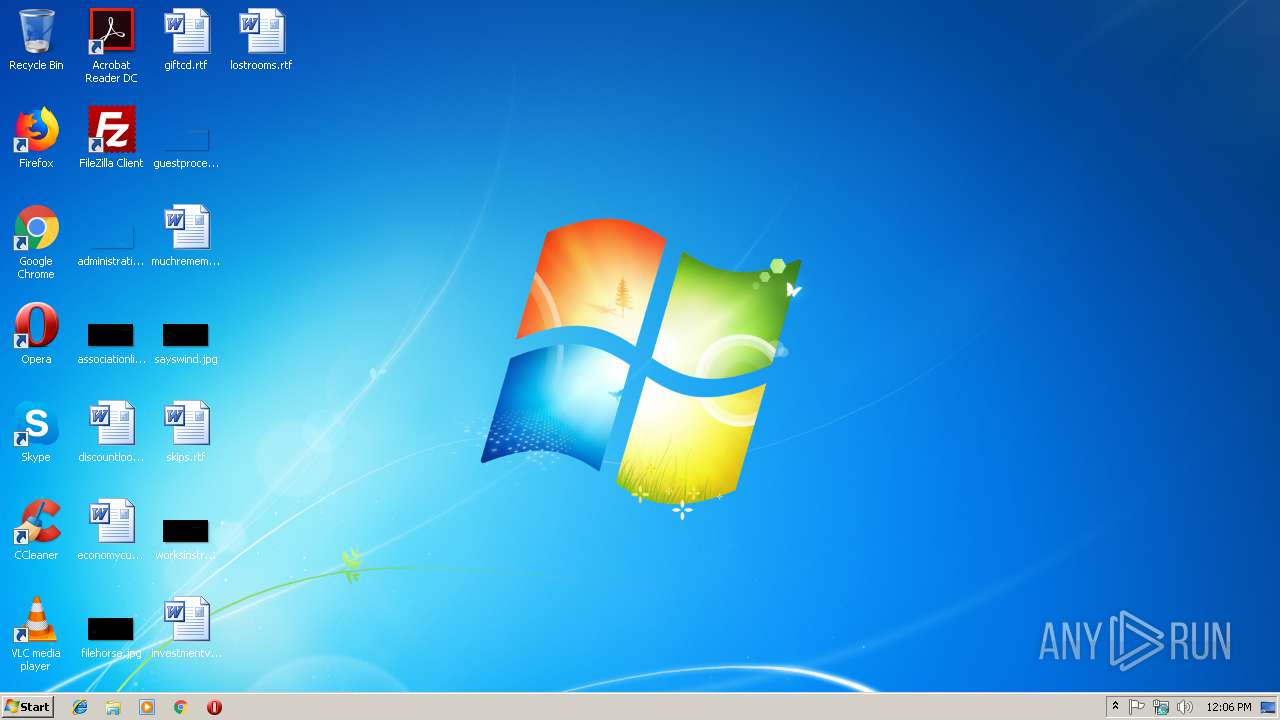
MALICIOUS
GandCrab keys found
- upacked.exe (PID: 3092)
Writes file to Word startup folder
- upacked.exe (PID: 3092)
Deletes shadow copies
- upacked.exe (PID: 3092)
Renames files like Ransomware
- upacked.exe (PID: 3092)
Changes settings of System certificates
- upacked.exe (PID: 3092)
Dropped file may contain instructions of ransomware
- upacked.exe (PID: 3092)
Connects to CnC server
- upacked.exe (PID: 3092)
Actions looks like stealing of personal data
- upacked.exe (PID: 3092)
SUSPICIOUS
Reads the cookies of Mozilla Firefox
- upacked.exe (PID: 3092)
Creates files in the program directory
- upacked.exe (PID: 3092)
Adds / modifies Windows certificates
- upacked.exe (PID: 3092)
Creates files like Ransomware instruction
- upacked.exe (PID: 3092)
Creates files in the user directory
- upacked.exe (PID: 3092)
INFO
Dropped object may contain TOR URL's
- upacked.exe (PID: 3092)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:08:14 17:56:13+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 67584 |
| InitializedDataSize: | 236032 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x59ce |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x004f |
| FileFlags: | (none) |
| FileOS: | Unknown (0x40534) |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Unknown (557D) |
| CharacterSet: | Unknown (F56C) |
| FileVersion: | 4.8.5.34 |
| InternalName: | fapuhebopi.exe |
| LegalCopyright: | Copyright (C) 2018, vemeluzuboguweg |
| ProductVersion: | 4.8.5.34 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Aug-2018 15:56:13 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 14-Aug-2018 15:56:13 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000107C2 | 0x00010800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.63442 |
.rdata | 0x00012000 | 0x00004BA4 | 0x00004C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.92085 |
.data | 0x00017000 | 0x000254F0 | 0x00023600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.94282 |
.version\x04 | 0x0003D000 | 0x00000004 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 0.0611629 |
.version\x0a\x10 | 0x0003E000 | 0x0000100A | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.0111738 |
.rsrc | 0x00040000 | 0x0000D260 | 0x0000D400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.45722 |
.reloc | 0x0004E000 | 0x00001D0E | 0x00001E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0 |
Imports
GDI32.dll |
KERNEL32.DLL |
USER32.dll |
Total processes
36
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2304 | "C:\Windows\system32\wbem\wmic.exe" shadowcopy delete | C:\Windows\system32\wbem\wmic.exe | upacked.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3092 | "C:\Users\admin\AppData\Local\Temp\upacked.exe" | C:\Users\admin\AppData\Local\Temp\upacked.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3416 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
129
Read events
95
Write events
34
Delete events
0
Modification events
| (PID) Process: | (3092) upacked.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\ex_data\data |
| Operation: | write | Name: | ext |
Value: 2E00740074006900690079000000 | |||
| (PID) Process: | (3092) upacked.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\keys_data\data |
| Operation: | write | Name: | public |
Value: 0602000000A40000525341310008000001000100BB2EB76149B93D6629981CA3DB3AFD16FD74EDF845C25CF0D7E2A37485B5DC8A1014F538A72BAA82BA78E20D4F4695373574110396E7FF371255CDAE24893899F619A2AA5A91374D82D96DBFEA510C688662E9E9B63262EB23727B4DB62D361AB70030B755D4CE27429DD3B736565E48BE5D16908D2DDC725B52A031717E254FC6B7D494C709403481BE81AEEC526CFF678E78E63A08CFF60F0F9EBB6A65A0C5963FDB3CD5AEC42BB4854DFDD9A697E13AB07C4E2C074AC8893003206C94864B5A670714994EBAD8D4572A32BB04DD41D5E273AB88EAA4DEA9E5B37D6C565B5872E01367E43C45BC712DF6182A6EE0A2A1FFCBFC33E4AC6F74D4562D8F283FF3 | |||
| (PID) Process: | (3092) upacked.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\keys_data\data |
| Operation: | write | Name: | private |
Value: 94040000AD7C60C8C4C5F1E9AB6D9569A27D32BB471EDE6510075AA7B5C4DA31A9BD501A845B657C111C7E86F54813DA1AA07374E47DCED71DCC68211550424B96BD623BF2B79A4325BD5292EE3FD72CC6BDB1F26E454CA77A3F60ADC1776546F2D7C60D6308349A4405B17619D1D7307B4079693EE76D73F961B152DFF3253E567C1CB57678C2486AF146FA45F78E333269EFB6306687D97036812B019257B5C3C67B4D55575796C8FB4B39F1C8BC12AEE19775CEB18E2EAFB92260C3DF0E73C286E42E9E26C03F7E18A62E99695879F95329D5B9524D31AA5C9881FCE979B264C53CC12B4260D289B75AFBDCF43DCF3CB39E77A756D2C2BB868016E11BC9FD19E4D3213F7C45863851C7FF38AB7C38EE863E4F7257AACA2212159472C35F215A64807D49C86C806F59D4121C8D625A3DAC0956D5D6D7B76197D636893BA5B246387D7186B89AF7E67C79A7B9484F95E958BBD028B13163C2504A2B50A4F0949EF8A63F6300FF555717927E02F6CDD88F19047611593226B44C5E292ADBBCE9E250FFA3515B052A88B7BD2EC804917C3A58D2B0F35A57EE6D2B549AAE23BD7BE8AB81E00EEEFB9F085DDEC72E8D82A9D29FAE3B6526B8DDC93225BEE3A62CA19B2A6E4D885AE2C684B75701B2A3C2A468ADA64661F9A3DFA3DCD85DFC53FBFC048E8DD2BD165D946316DC0654DF8F90E1DC82C23157910FADC1052D94951C48397EA68C30786ADEE4AC3616A33AFB2A5E29D7B760C60629CF718F2EC0C08D95181DFD8275704FF4B328D8B2391F397017D4AE18071BFD12ABFBD3A898FAB094E0CDBF42061BCA1E0CFB6457622715548C6D6459E8DD57A35EF7B491F1651DBE54B22B8D26351BD14B21F2B09B95F4ECAEED6BE9EF5E6042A89DE40C494F37C96634FFCB7190CEC1DC807967C2DB55387E9F4961F14FA997759F5423922AEF25C39CE01A695BC7B9FA976EECD59B62B5834FA8F850D3672DDA29AD6FBAB6652A0793ABECFBBBABC4831EF82C6CE88D407BB9383D0B00C039AE3E1D83CF10F5AE6817B9C2F2EF6684D4196735D3E50133C3C9AD77DA0186BFB04D5892B452A5A14807E4085ACC701B4272D5C82D052A99471B3DFC54CB2BA776543A34CCC9E6C040D9B4DD37C05FEF0DCD450A1F9EE64F51023D00D984B8ADECC175464D452B571AF9EBA2A70C2DE8D33218C91C844D314698A8C217E529AD13250B6C12D0C0420D302AB862DD5B1787B54BD89B4395134430C5134D0E6B1C2EC72E2DF1FA7EB13B3BAA5EBB92F7277F7CC53187C7846FBDC3290646488BF179D971D4355D42FFCDE5C77753F12E2CC8A09A8BC897AC021259BFADF8EB0066140E3E1C539DEAD3FAD51ACCBAD62BEA427408A3244C857937B02E7B8066B748F117E9694E9DCB3D2E608ADC697B0E922845AB6362CC5626CB01DF46470592369419EC05F4239F52F3BDFEC415D9F25404E8C08203A0AC24749FC3883B69202A4B296D31AD556B1CFA25EF44DC1D002B1EFF411A01B90A129215EF868743156C34E3990A45E47639DD047E813C3911A81D9CD9783DE23772AE6E4ECEA1AD71FB7D7A773B49BBEDC8F518446F65333DA40C65FD57A713523011E6BD204030A8D184917FAAC9B20FE6B393BD70C75E3D2854F1F001B36960BC996B5CBC3D2F737660F000FF684A5E42FBCE7FE2BC43A88EE7D698FFC3F20045BC3BEC8F20A6D8A72E6020F7781F723D0CB210FD2917DEF0CF33150B33DAA7978DAD1D868702B78258BEAAD5485388BF1913D8253DD1FE70F3FE1EC1602B31742B2B64A19F1F3D0D8072D185C6C63CBF062075EEECF71C213CE2B7EF19521DDDA8946C5100F15531EC217F48D5EBEE5C0DAC1F496613188F9DDFFED0E16E9D8CF42447466DDF5B8D2EA71E59796B574D55225BD06B11D210EF60065A7CED63660908FF34E17222A61CDCF3A34F4F667E30DC72AE34D8A18B3031228215A7DA5320DC391212AECED91C4240644E8A7228F7E50F92A9F5760A383C46270FF7B108DC4F15AAA7A09F95A387671430BEED567E1B497B2E8A07A73FDFE6A914B5CAF1AA096D6093666861EB3590755282990F8863B19C51D6383EE6ECEEE7A7C57C27EE7B0716976F0BB39865F9F9884ECDD1512539E5C249BF59BB27240259D354C3C84A402C587A2A197E97B81707E7A77806C9941A8031F319A8C85D288B8B9F369A10E6F04A507F36953443611F7C3722CA7482E27B731A76BF85AD70D0E6DF4DB3512F99B7FF7898E97452477B74313CF34DAF177C28FDAEA5EA8FFB233724B1298FDB3B06E2ECF41264DF3EE3D9848B0C00924E3B81426D1E5C38D82DC5EC041CFC708DE1F9209C2CFA8FD8E3730A4308B9B0C704322772638E8CF7465864B903AA3D7FCF8A1C63 | |||
| (PID) Process: | (3092) upacked.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3092) upacked.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3092) upacked.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\upacked_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3092) upacked.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\upacked_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3092) upacked.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\upacked_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3092) upacked.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\upacked_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3092) upacked.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\upacked_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
0
Suspicious files
429
Text files
319
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3092 | upacked.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\boot.sdi | — | |
MD5:— | SHA256:— | |||
| 3092 | upacked.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim.ttiiy | — | |
MD5:— | SHA256:— | |||
| 3092 | upacked.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim | — | |
MD5:— | SHA256:— | |||
| 3092 | upacked.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{05ed3515-06b3-48f6-8cf2-bf24b1bf0727}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 3092 | upacked.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{16d74681-6bc3-4c44-97f0-8b8dfefe2355}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 3092 | upacked.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{38e8535f-27d0-4352-aa3a-ce4178930102}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 3092 | upacked.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{3cc0f82b-873a-4e59-b89f-689fbdf88af9}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 3092 | upacked.exe | C:\$Recycle.Bin\TTIIY-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
| 3092 | upacked.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{5c4beaff-a038-4df7-9b35-072a18f8e3d6}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 3092 | upacked.exe | C:\TTIIY-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
1
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3092 | upacked.exe | GET | 301 | 185.52.2.154:80 | http://www.kakaocorp.link/ | NL | html | 162 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3092 | upacked.exe | 185.52.2.154:80 | www.kakaocorp.link | RouteLabel V.O.F. | NL | suspicious |
3092 | upacked.exe | 185.52.2.154:443 | www.kakaocorp.link | RouteLabel V.O.F. | NL | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.kakaocorp.link |
| malicious |
Threats
2 ETPRO signatures available at the full report