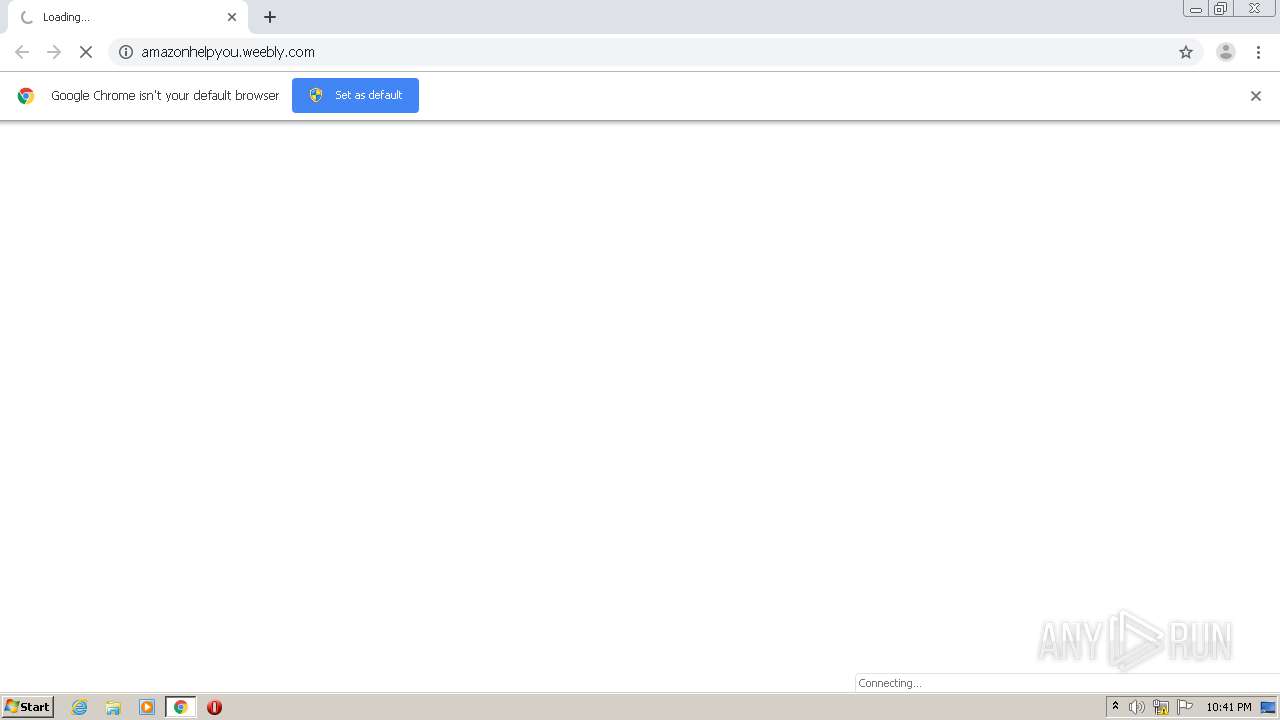
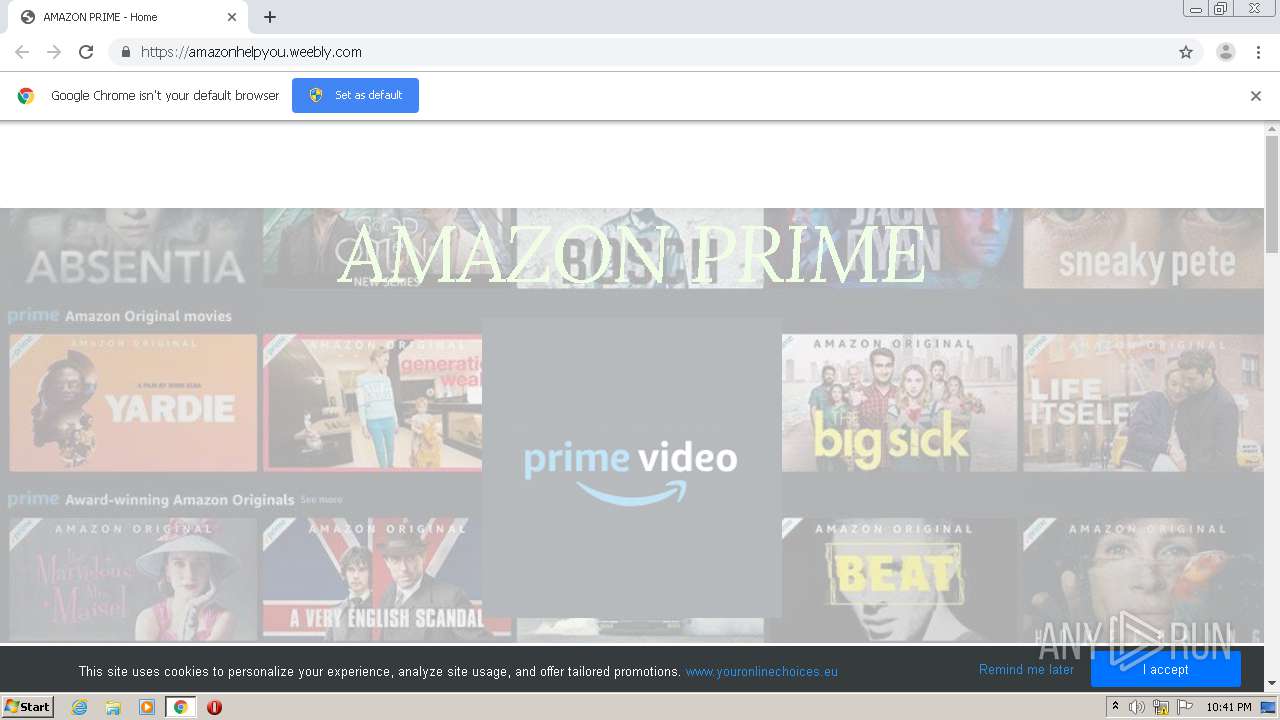
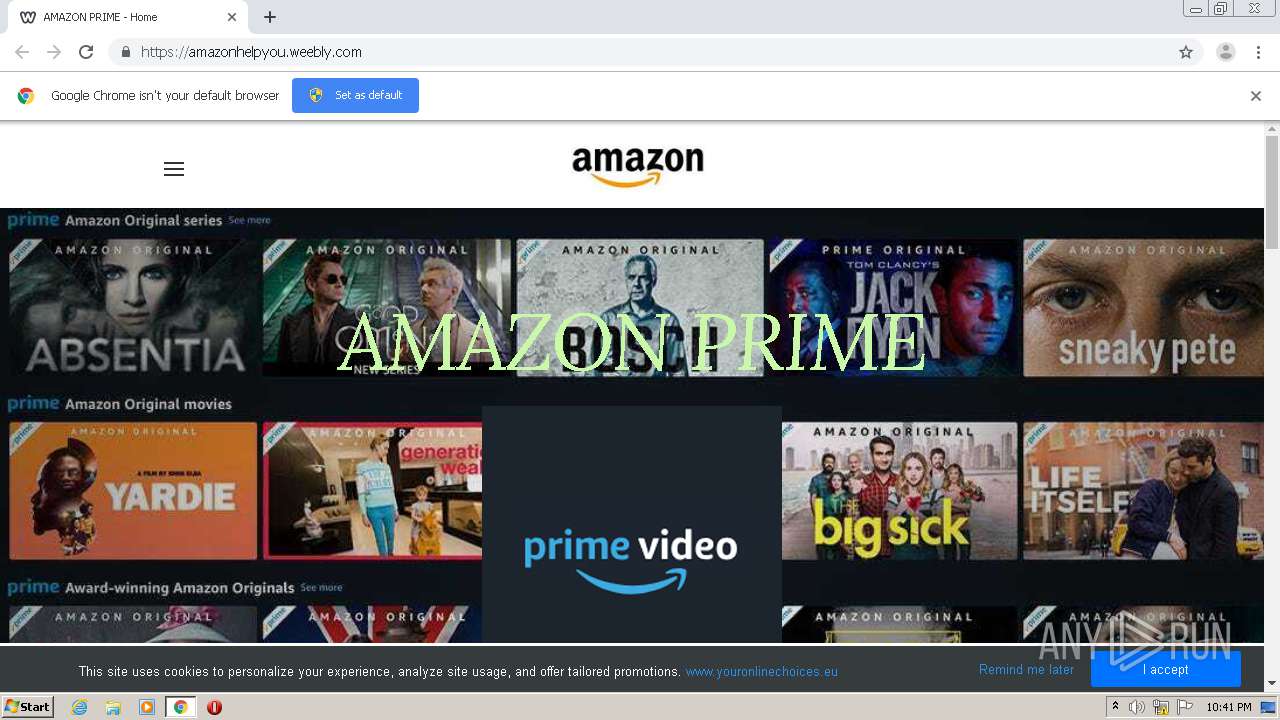
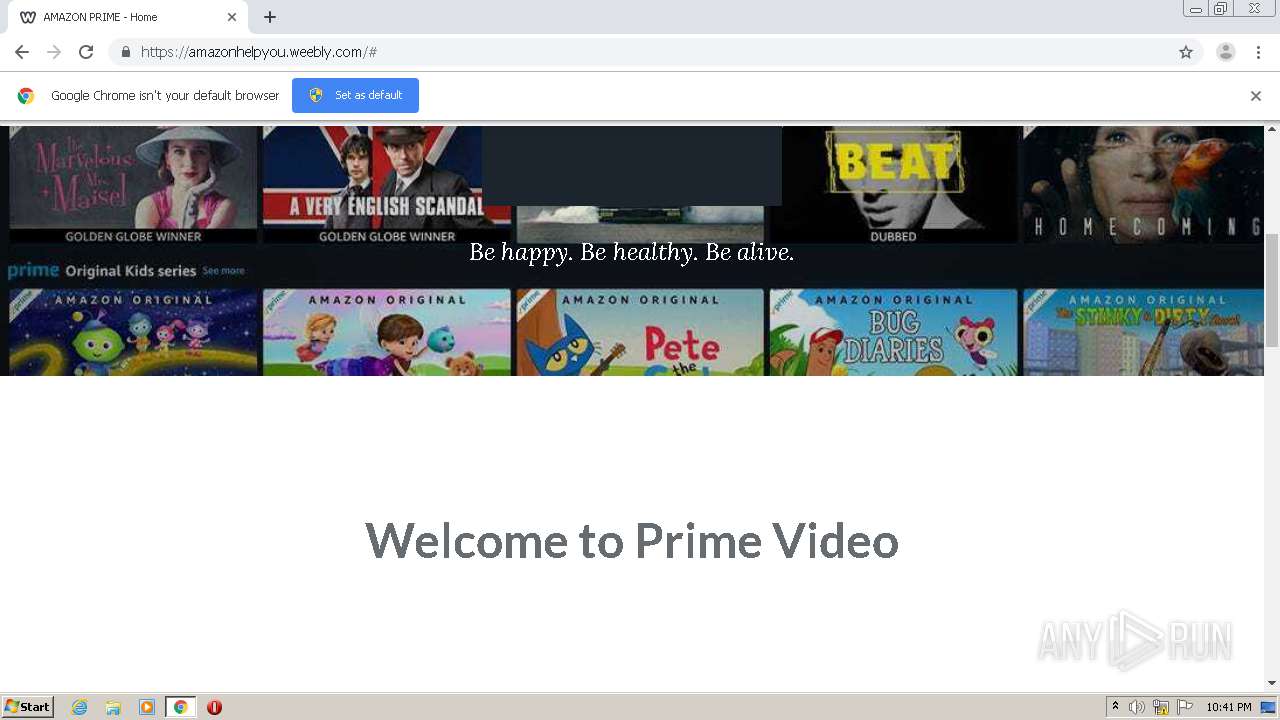
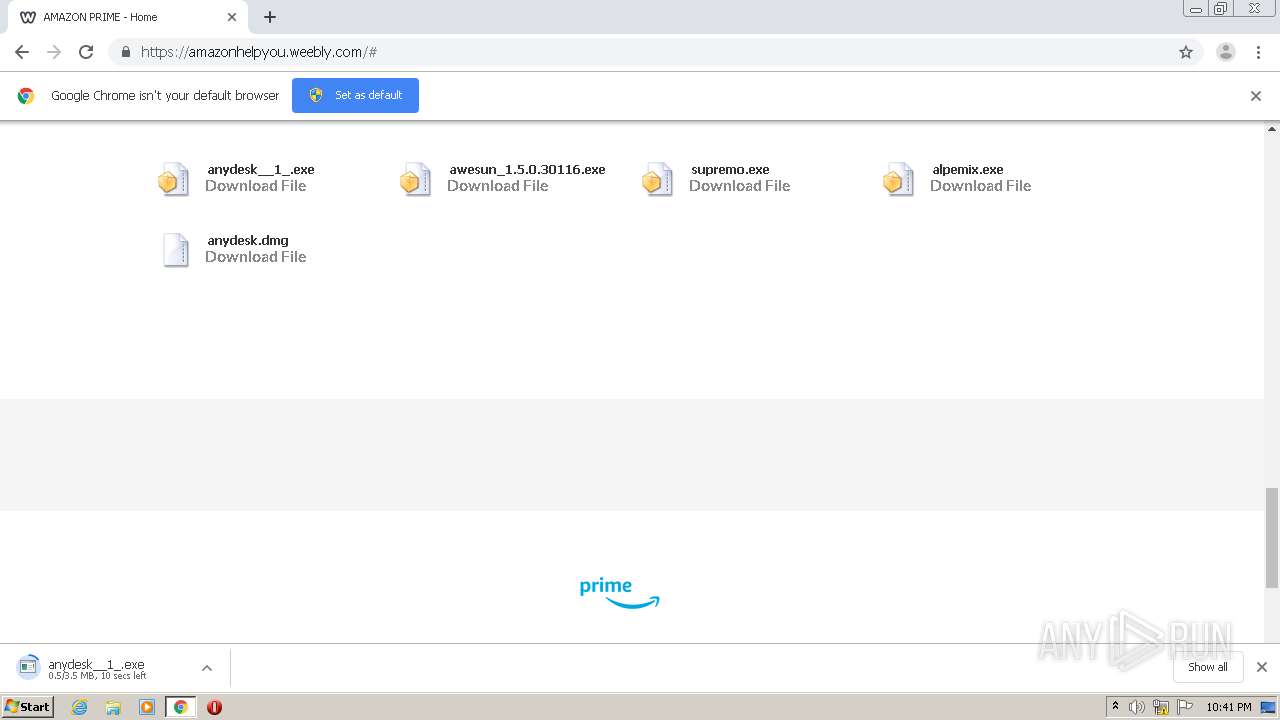
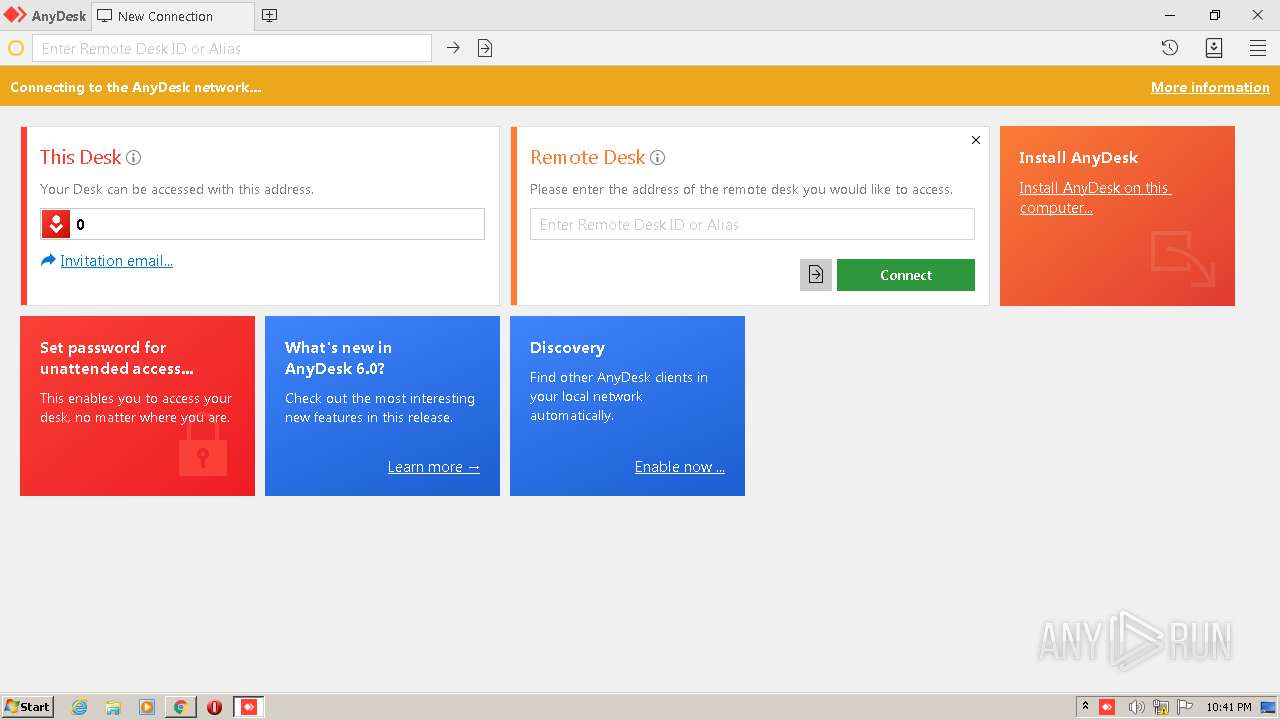
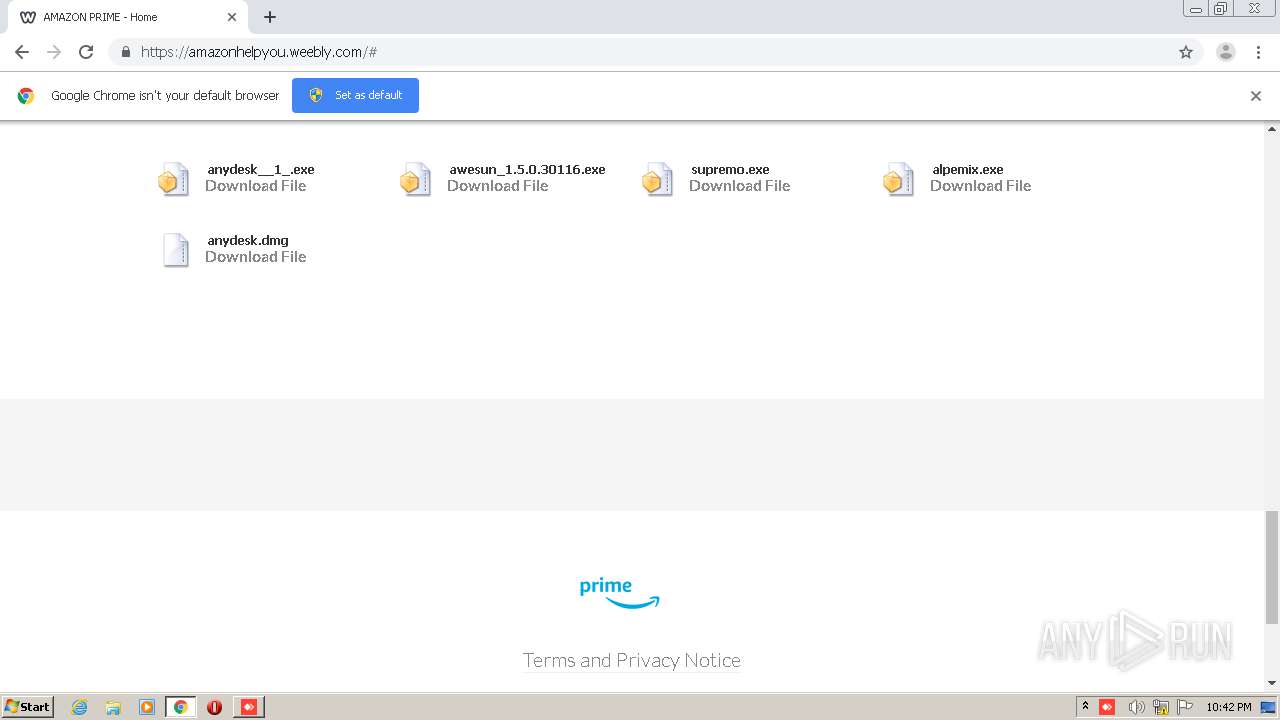
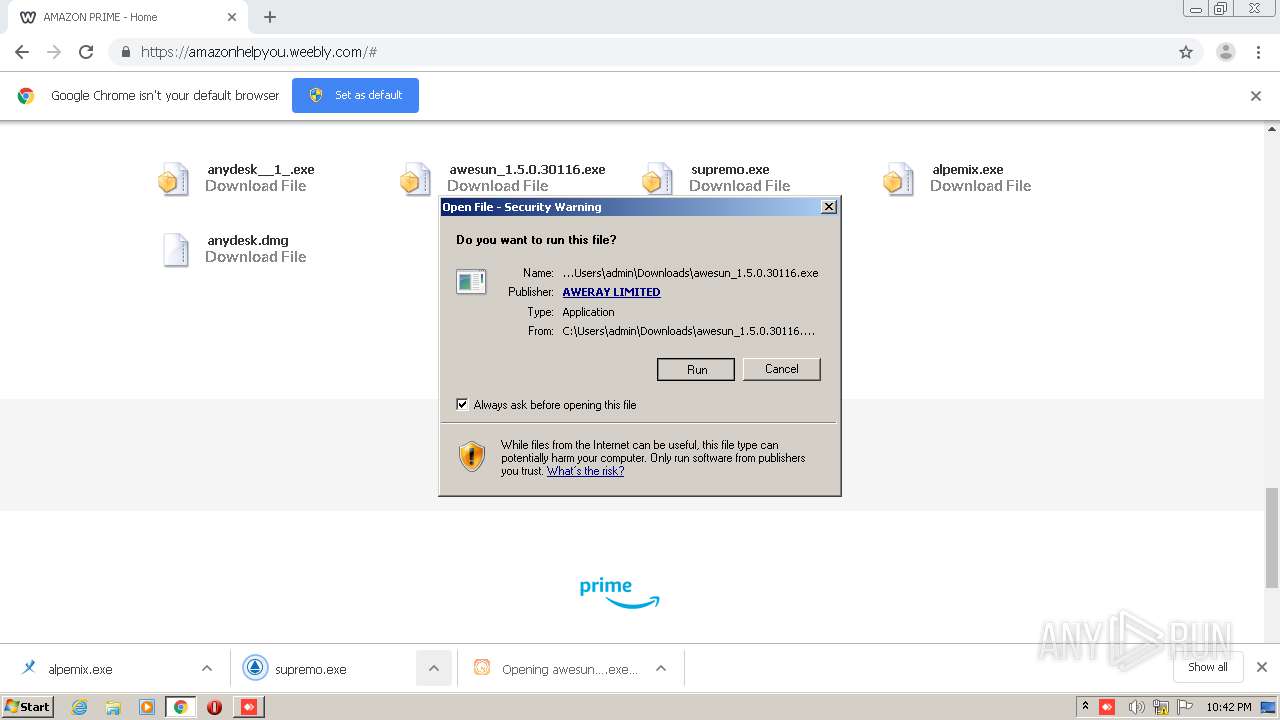
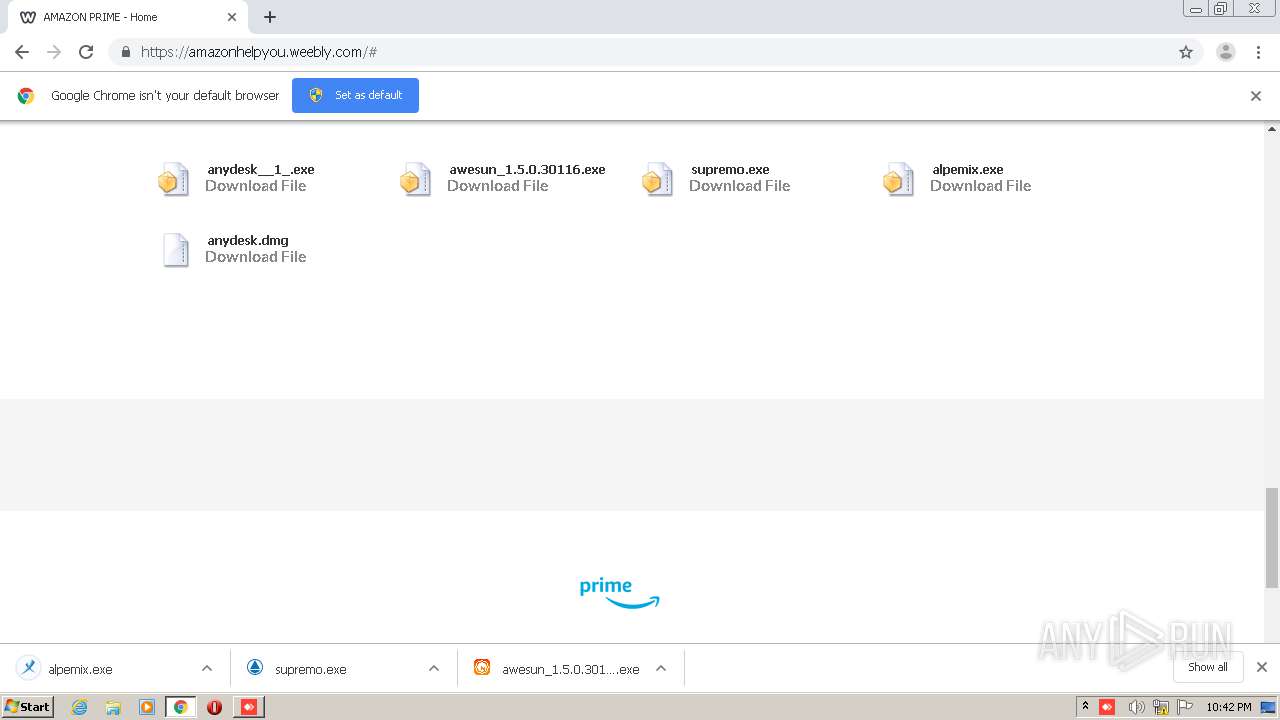
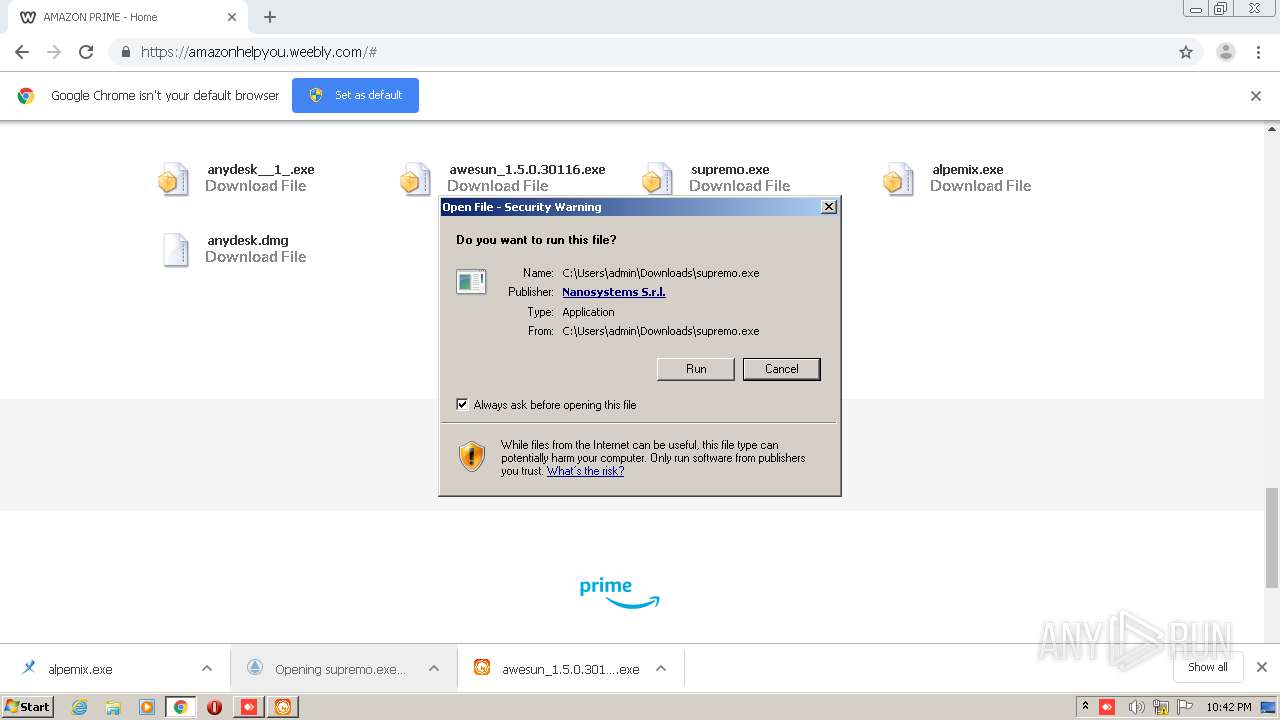
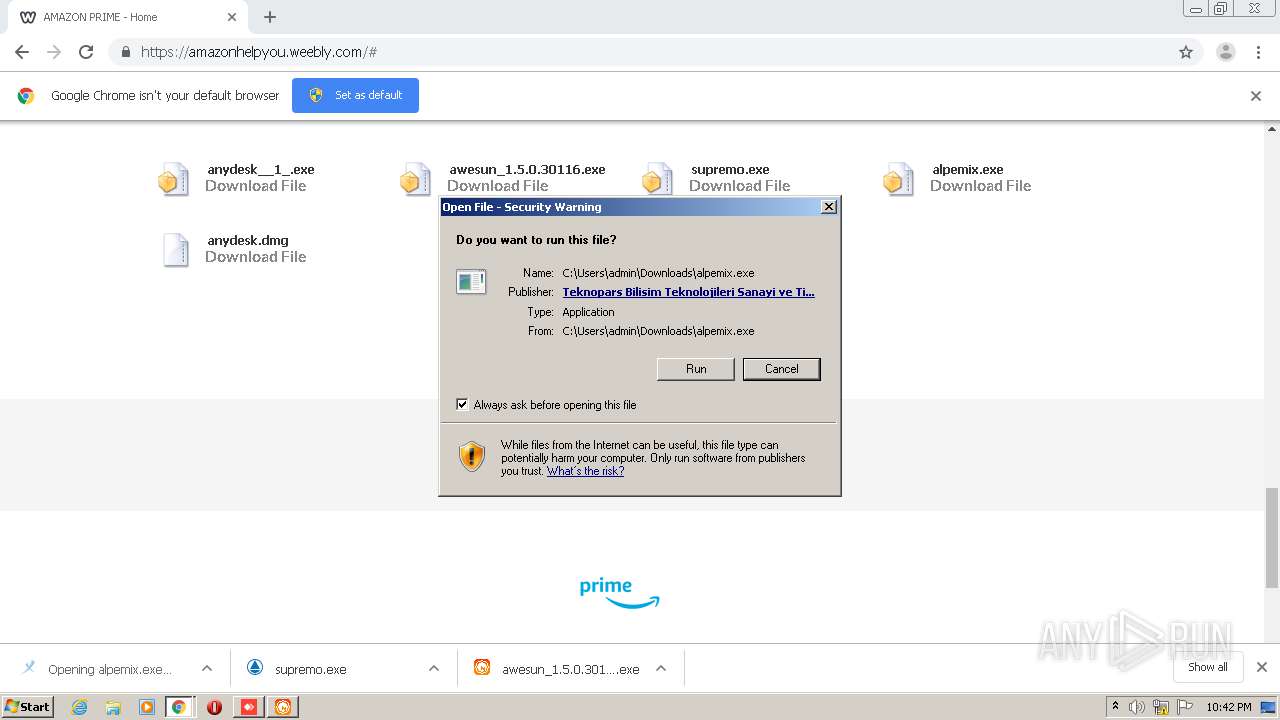
| URL: | http://amazonhelpyou.weebly.com |
| Full analysis: | https://app.any.run/tasks/cfd9b96c-d1fa-403b-8422-7c43c890c744 |
| Verdict: | Malicious activity |
| Analysis date: | October 19, 2020, 21:40:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 108D347C2287291460BD6ED3C9F68825 |
| SHA1: | FC9A7F71567B915721327D003282D4819AB9EB8A |
| SHA256: | B6A5B184CE9F704A615AF9D003255ECBF8532CD3E7E95D9DA848F7FD9BBE26C4 |
| SSDEEP: | 3:N1Kf3SApcLdI:CLpcZI |
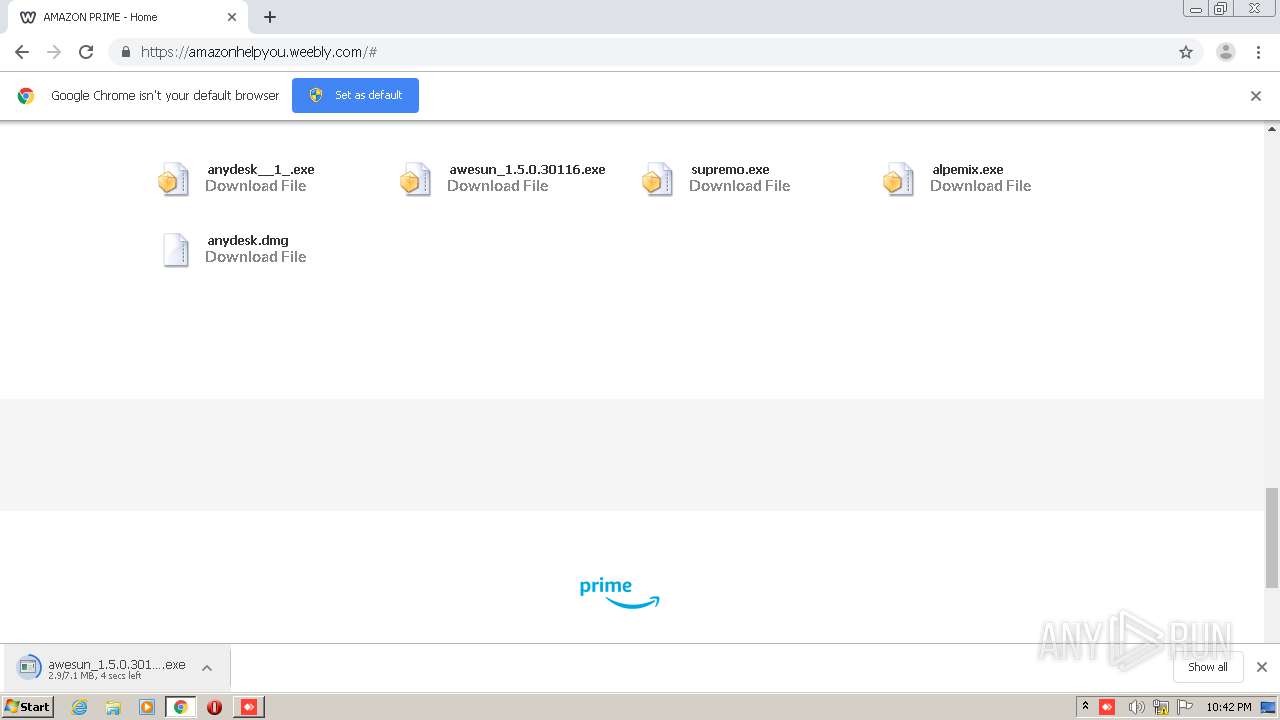
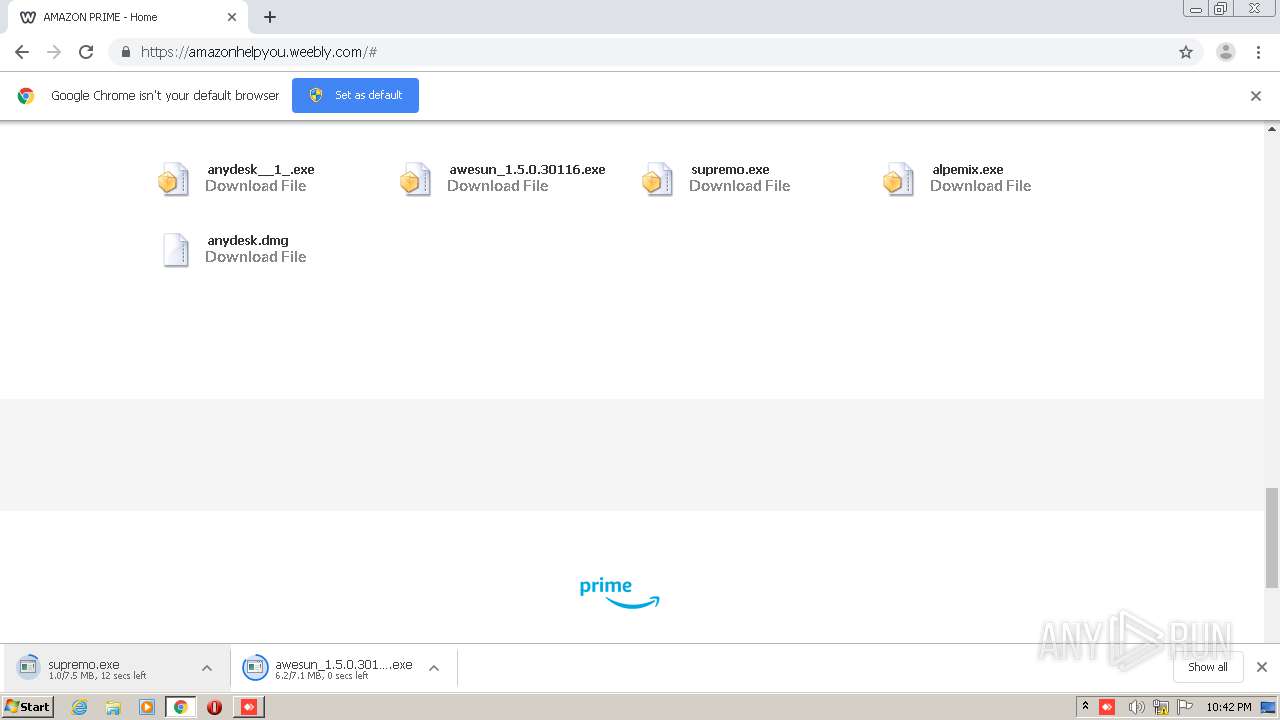
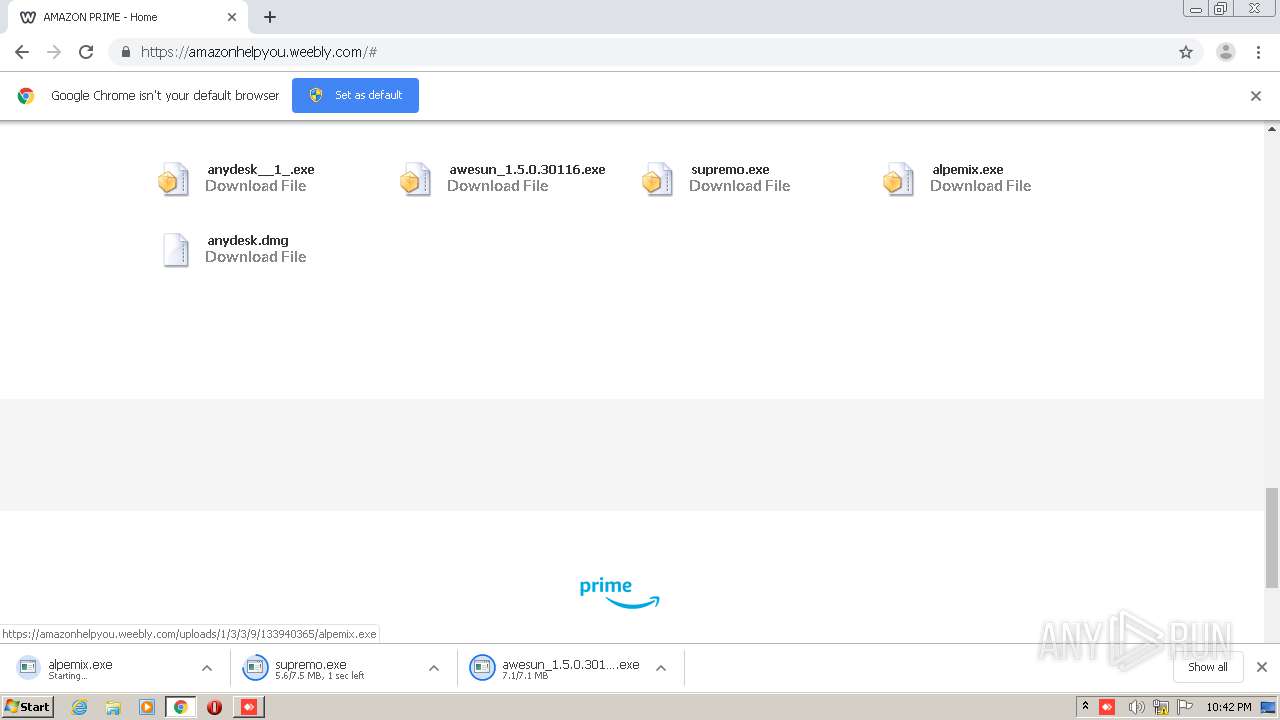
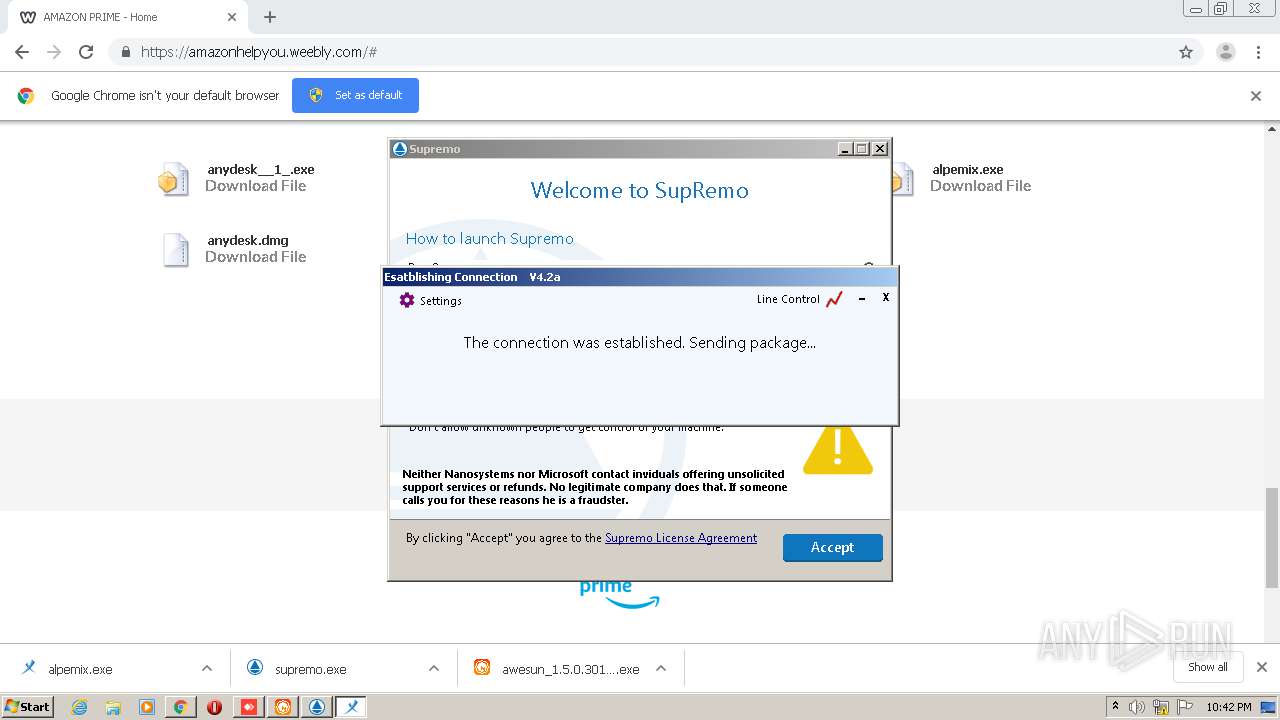
MALICIOUS
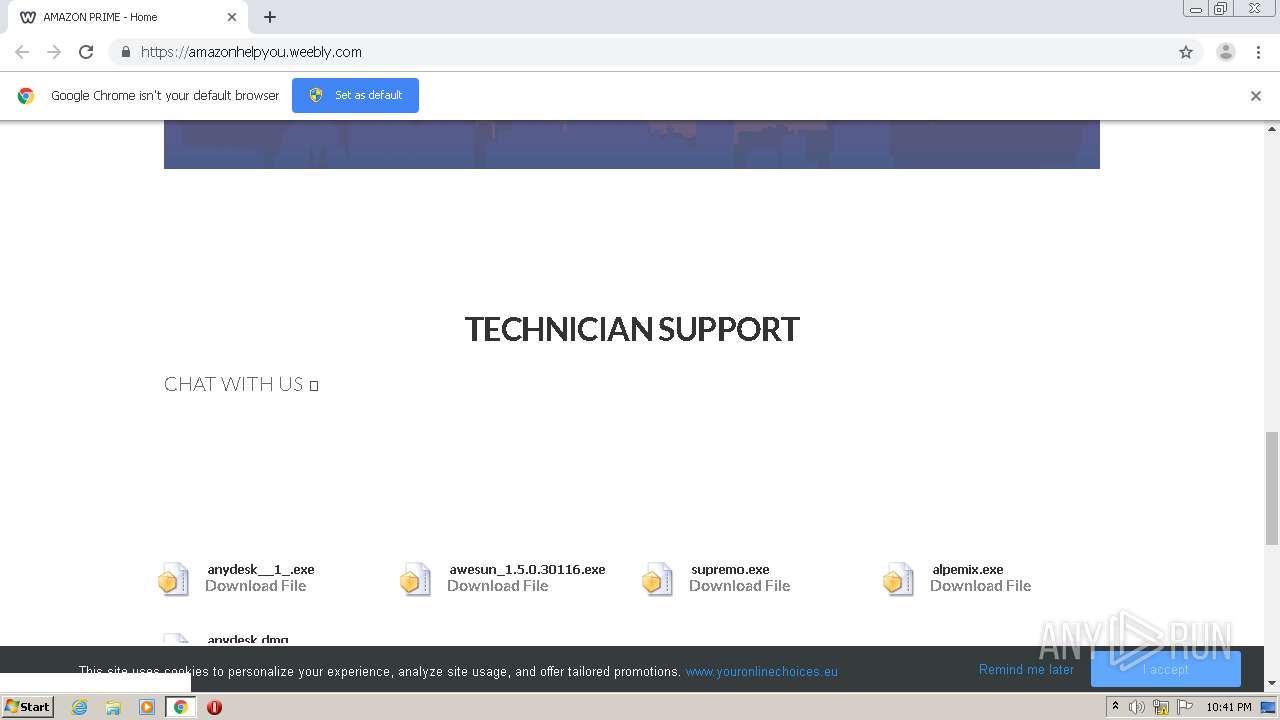
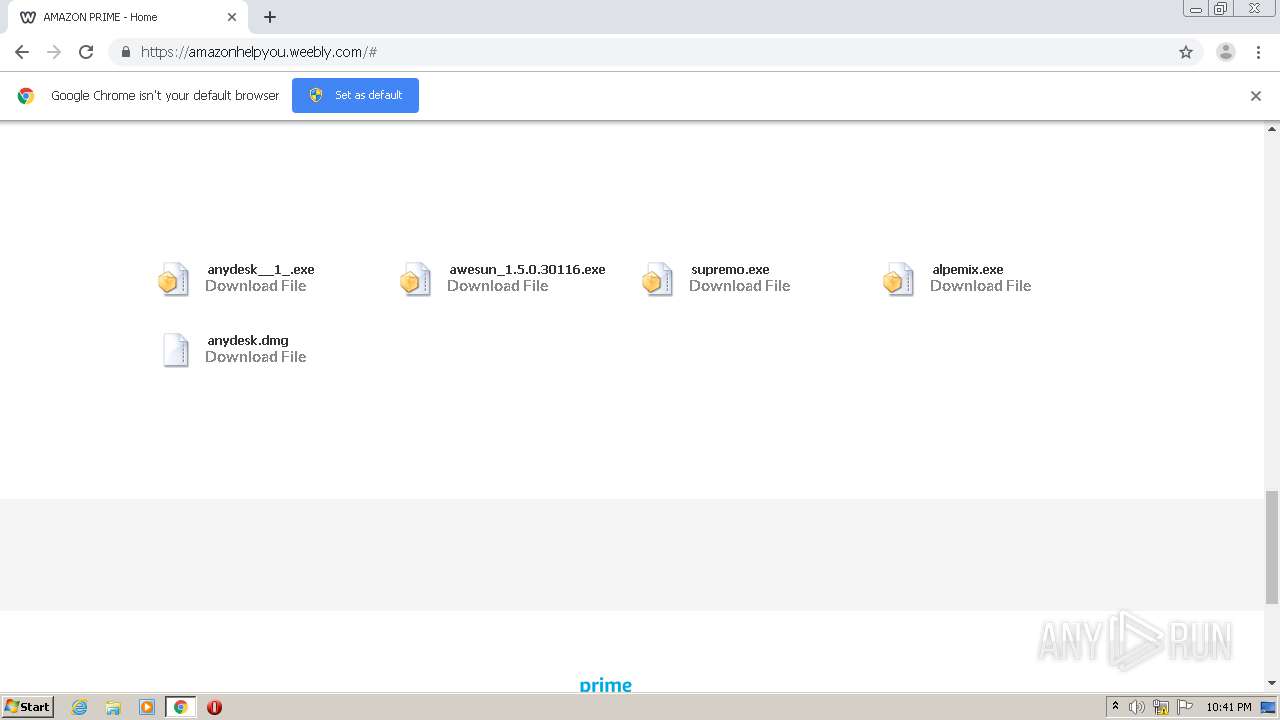
Application was dropped or rewritten from another process
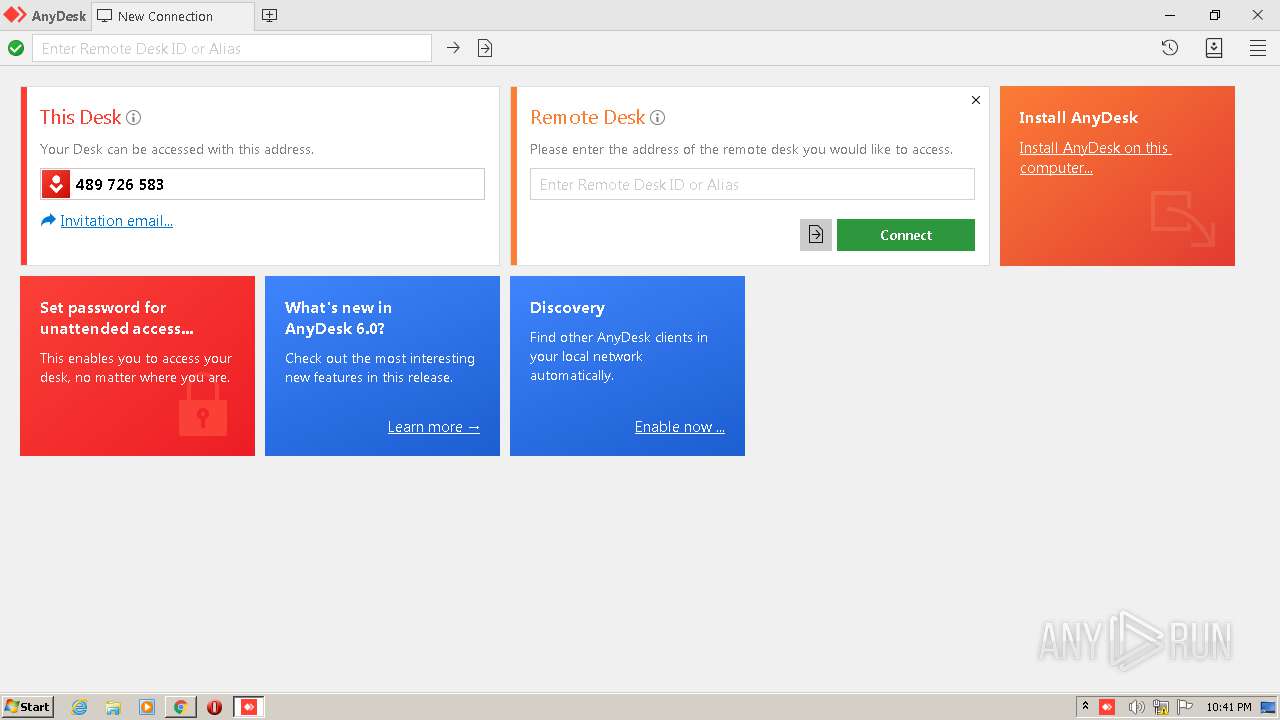
- anydesk__1_.exe (PID: 1252)
- anydesk__1_.exe (PID: 2472)
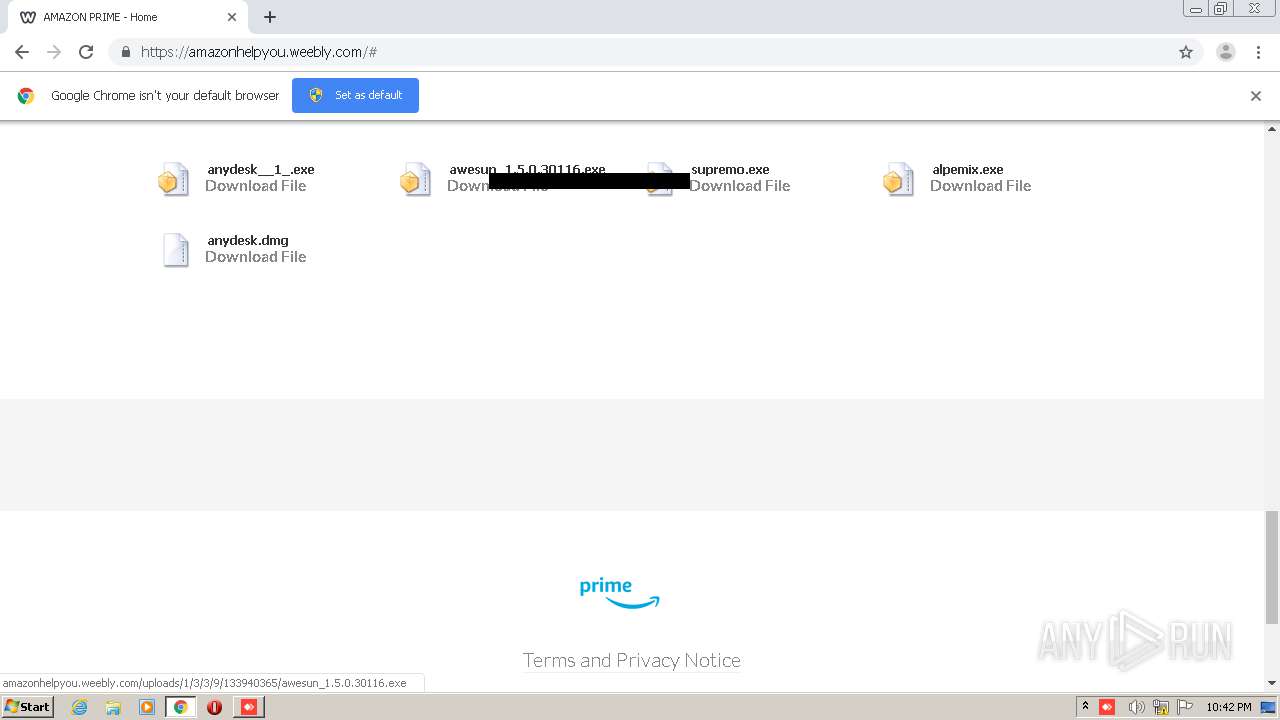
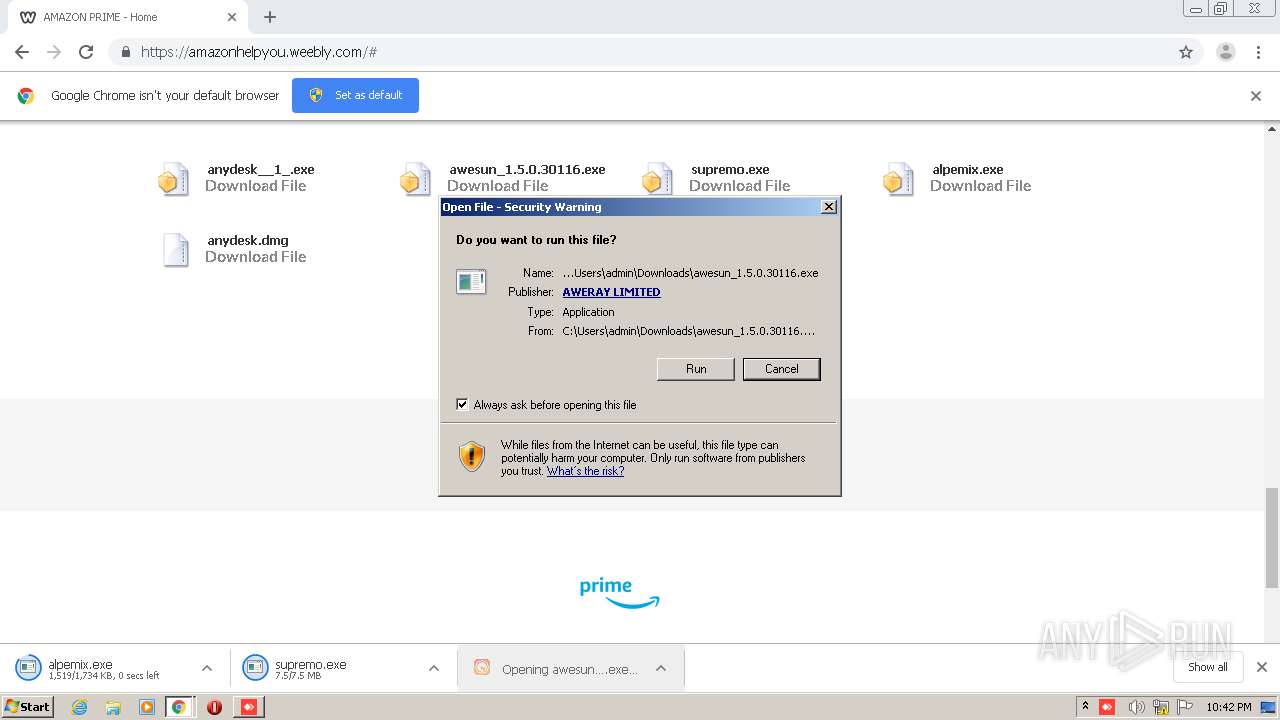
- awesun_1.5.0.30116.exe (PID: 3492)
- awesun_1.5.0.30116.exe (PID: 2608)
- AweSun.exe (PID: 1772)
- AweSun.exe (PID: 3700)
- devcon.exe (PID: 1452)
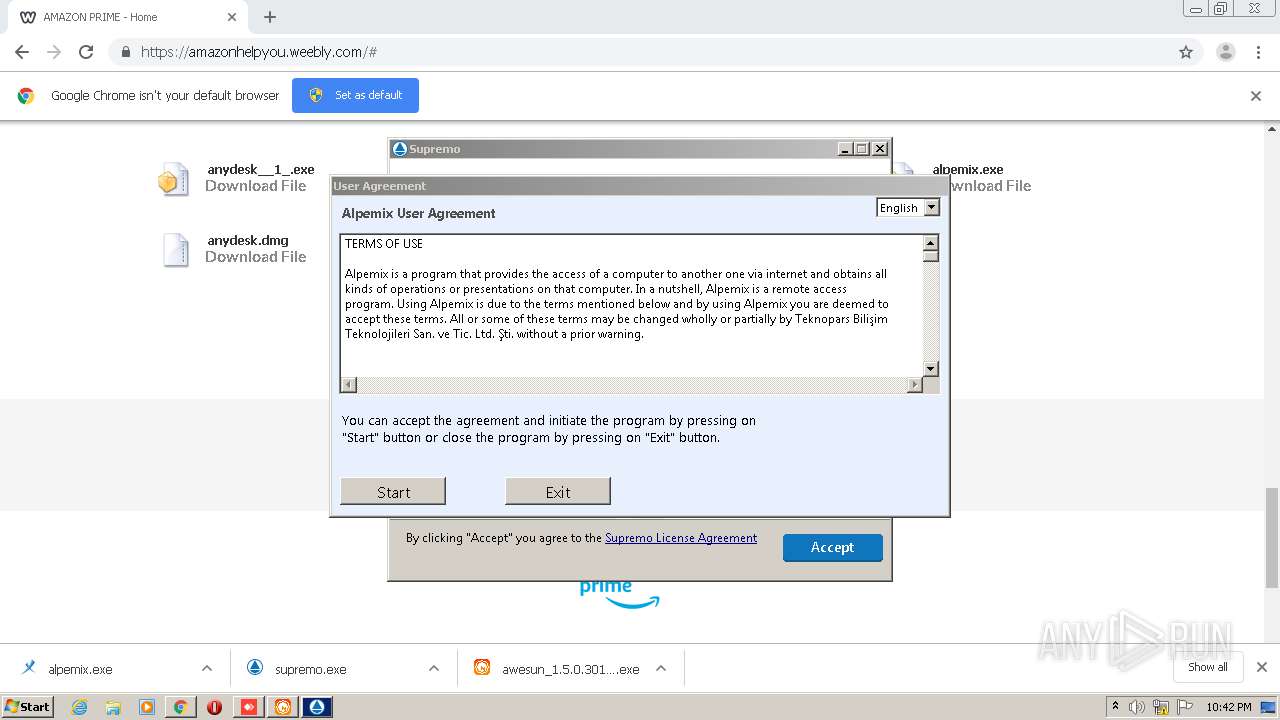
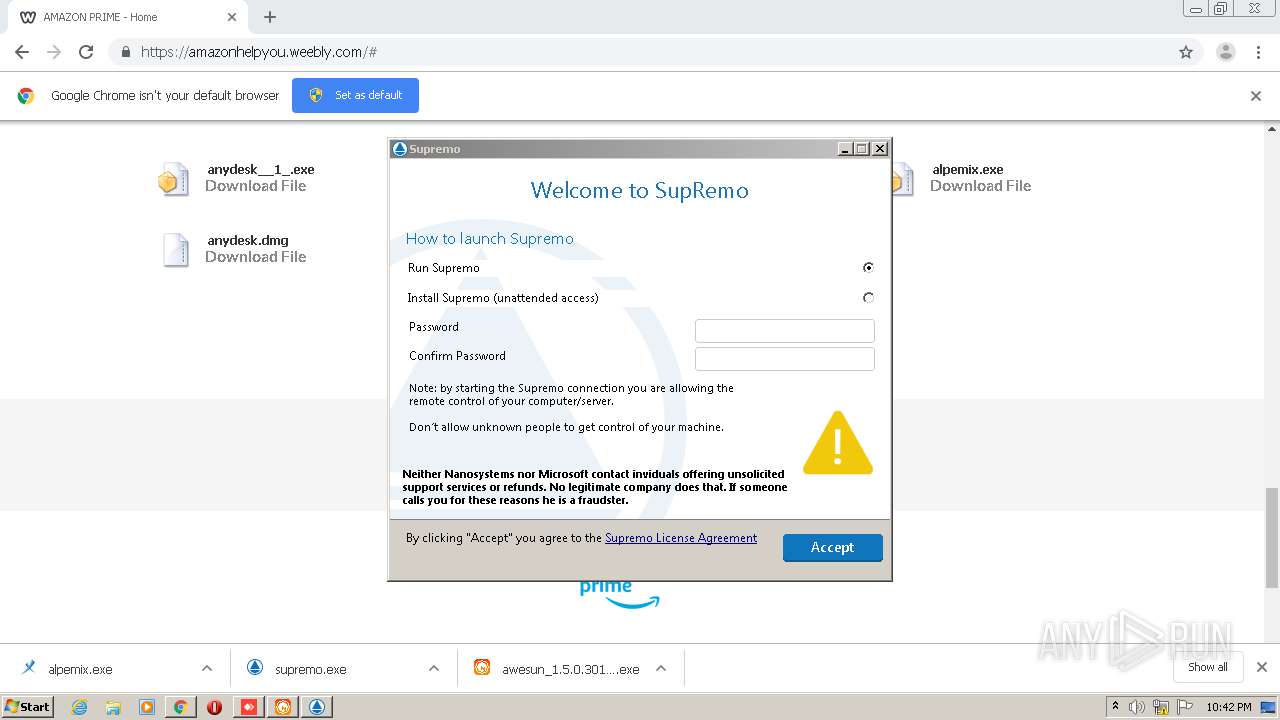
- supremo.exe (PID: 2072)
- SupremoSystem.exe (PID: 3480)
- SupremoSystem.exe (PID: 2260)
- supremo.exe (PID: 2884)
- AweSun.exe (PID: 2680)
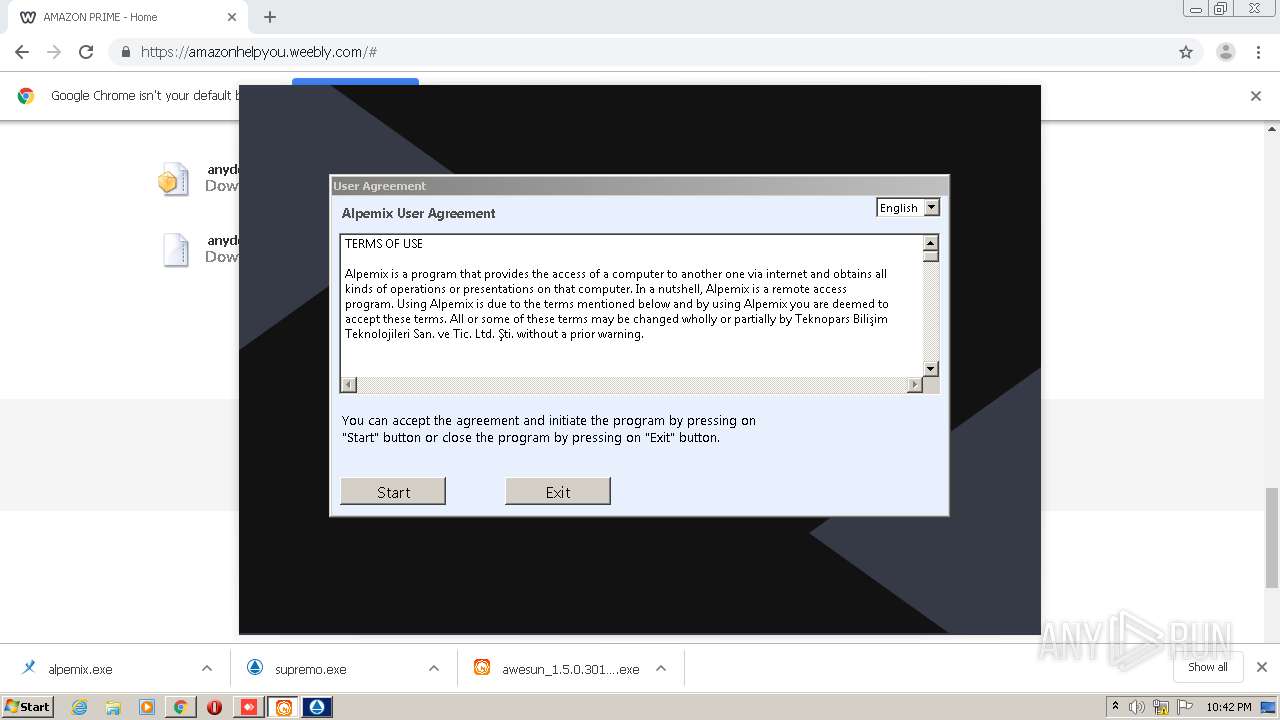
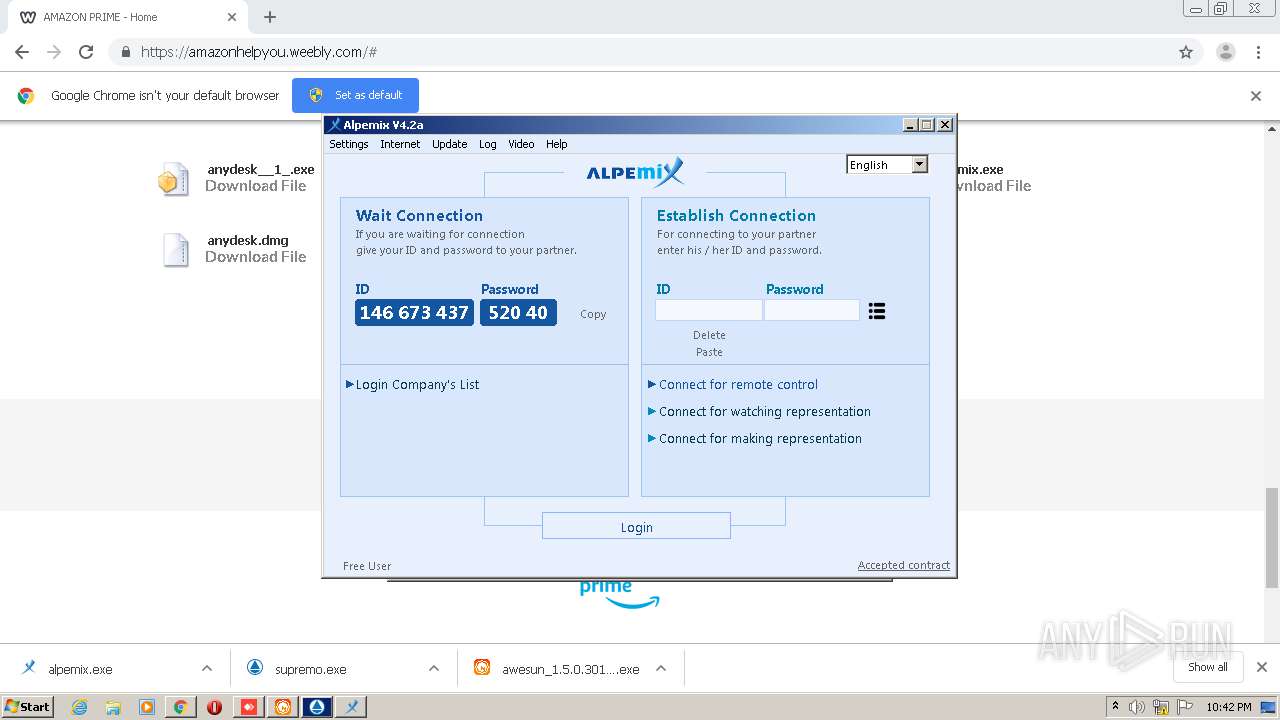
- alpemix.exe (PID: 2352)
- AweSun.exe (PID: 2360)
- alpemix.exe (PID: 2912)
- alpemix.exe (PID: 3864)
- alpemix.exe (PID: 3560)
- SupremoHelper.exe (PID: 3840)
- anydesk__1_.exe (PID: 1516)
Loads dropped or rewritten executable
- anydesk__1_.exe (PID: 2472)
- anydesk__1_.exe (PID: 1516)
- supremo.exe (PID: 2884)
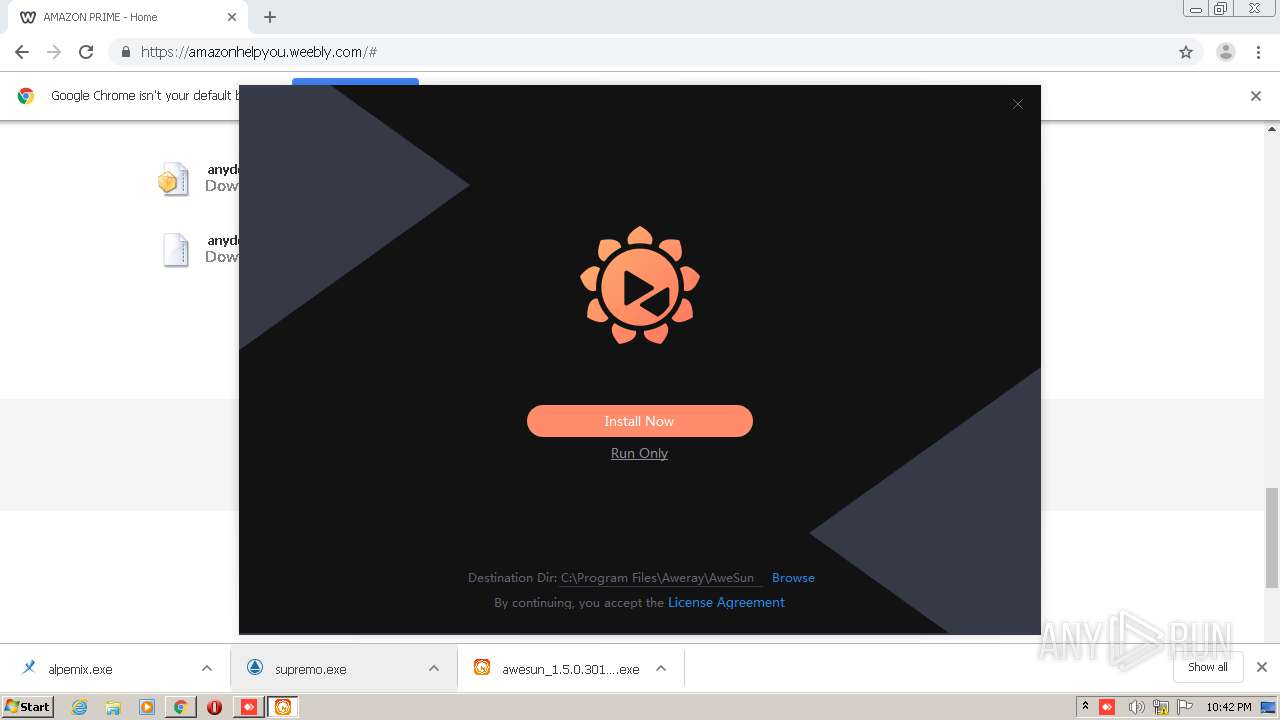
Changes the autorun value in the registry
- awesun_1.5.0.30116.exe (PID: 3492)
- AweSun.exe (PID: 3700)
Changes settings of System certificates
- devcon.exe (PID: 1452)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 3460)
- chrome.exe (PID: 2544)
- anydesk__1_.exe (PID: 1516)
- awesun_1.5.0.30116.exe (PID: 3492)
- supremo.exe (PID: 2072)
- devcon.exe (PID: 1452)
- DrvInst.exe (PID: 3444)
- DrvInst.exe (PID: 3036)
- supremo.exe (PID: 2884)
- alpemix.exe (PID: 3560)
Creates files in the user directory
- anydesk__1_.exe (PID: 1252)
- anydesk__1_.exe (PID: 1516)
Cleans NTFS data-stream (Zone Identifier)
- anydesk__1_.exe (PID: 1252)
- awesun_1.5.0.30116.exe (PID: 2608)
Application launched itself
- anydesk__1_.exe (PID: 1252)
- cmd.exe (PID: 2264)
- AweSun.exe (PID: 3700)
- alpemix.exe (PID: 2352)
- alpemix.exe (PID: 3864)
- awesun_1.5.0.30116.exe (PID: 2608)
Starts CMD.EXE for commands execution
- awesun_1.5.0.30116.exe (PID: 3492)
- cmd.exe (PID: 2264)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 776)
Uses NETSH.EXE for network configuration
- cmd.exe (PID: 1860)
- cmd.exe (PID: 2840)
- cmd.exe (PID: 1480)
- cmd.exe (PID: 2128)
- cmd.exe (PID: 3868)
- cmd.exe (PID: 1764)
- cmd.exe (PID: 3232)
Creates files in the program directory
- supremo.exe (PID: 2072)
- awesun_1.5.0.30116.exe (PID: 3492)
- AweSun.exe (PID: 3700)
- AweSun.exe (PID: 2680)
- supremo.exe (PID: 2884)
Starts itself from another location
- awesun_1.5.0.30116.exe (PID: 3492)
Creates a software uninstall entry
- awesun_1.5.0.30116.exe (PID: 3492)
Executed as Windows Service
- SupremoSystem.exe (PID: 2260)
- AweSun.exe (PID: 3700)
- alpemix.exe (PID: 3864)
Adds / modifies Windows certificates
- devcon.exe (PID: 1452)
Executed via COM
- DrvInst.exe (PID: 3444)
- DrvInst.exe (PID: 3036)
Removes files from Windows directory
- DrvInst.exe (PID: 3444)
- supremo.exe (PID: 2884)
- DrvInst.exe (PID: 3036)
Creates files in the Windows directory
- DrvInst.exe (PID: 3444)
- DrvInst.exe (PID: 3036)
- supremo.exe (PID: 2884)
Creates files in the driver directory
- DrvInst.exe (PID: 3444)
- DrvInst.exe (PID: 3036)
Modifies the open verb of a shell class
- supremo.exe (PID: 2884)
Reads Internet Cache Settings
- alpemix.exe (PID: 2352)
INFO
Reads the hosts file
- chrome.exe (PID: 2544)
- chrome.exe (PID: 3460)
Reads Internet Cache Settings
- chrome.exe (PID: 2544)
Reads settings of System Certificates
- chrome.exe (PID: 3460)
Application launched itself
- chrome.exe (PID: 2544)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
104
Monitored processes
57
Malicious processes
11
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 560 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,3908618913888703686,6117652162698556669,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9403773545956922229 --mojo-platform-channel-handle=2012 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 776 | "C:\Windows\System32\cmd.exe" cmd.exe /c TASKKILL /PID 0 /PID 0 /F | C:\Windows\System32\cmd.exe | — | awesun_1.5.0.30116.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 128 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1044 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,3908618913888703686,6117652162698556669,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5683375962063264957 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2236 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1204 | TASKKILL /PID 0 /PID 0 /F | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
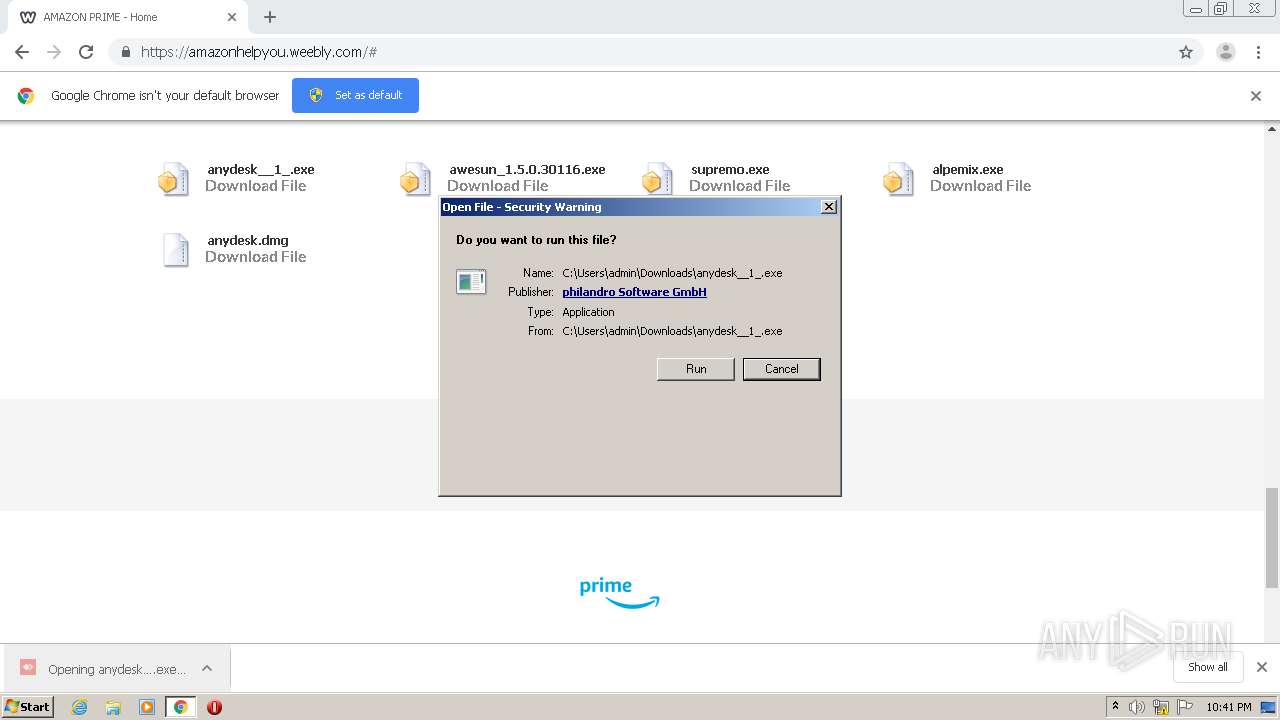
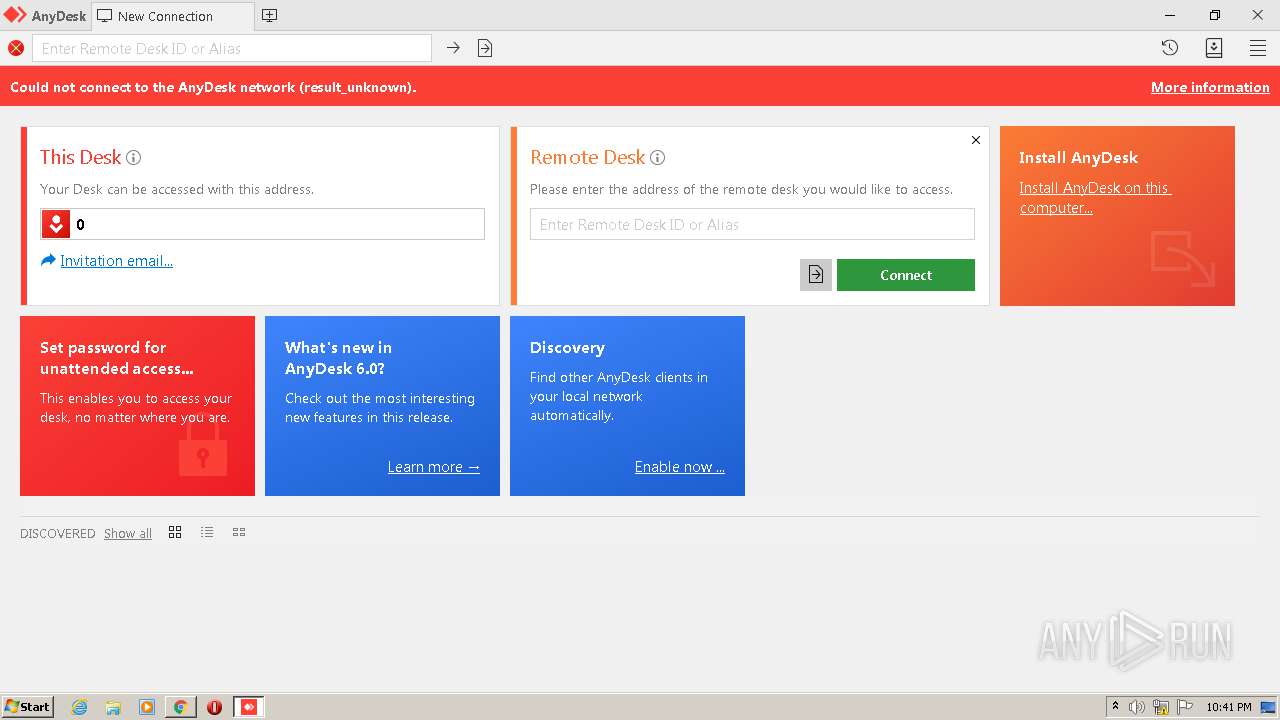
| 1252 | "C:\Users\admin\Downloads\anydesk__1_.exe" | C:\Users\admin\Downloads\anydesk__1_.exe | — | chrome.exe | |||||||||||
User: admin Company: philandro Software GmbH Integrity Level: MEDIUM Description: AnyDesk Exit code: 0 Version: 6.0.8.0 Modules
| |||||||||||||||
| 1440 | netsh advfirewall firewall add rule name="AweSun" dir=in action=allow program="C:\Program Files\Aweray\AweSun\AweSun.exe" protocol=tcp enable=yes profile=domain | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1452 | "C:\Program Files\Aweray\AweSun\Driver\Mirror\devcon.exe" reinstall "C:\Program Files\Aweray\AweSun\Driver\Mirror\OrayMir.inf" C50B00D7-AE62-4936-8BC8-20E0B9F0BEFB | C:\Program Files\Aweray\AweSun\Driver\Mirror\devcon.exe | AweSun.exe | ||||||||||||
User: admin Company: Windows (R) Server 2003 DDK provider Integrity Level: HIGH Description: Windows Setup API Exit code: 0 Version: 5.2.3790.1830 built by: WinDDK Modules
| |||||||||||||||
| 1480 | cmd /c netsh advfirewall firewall add rule name="AweSun" dir=in action=allow program="C:\Program Files\Aweray\AweSun\AweSun.exe" protocol=tcp enable=yes profile=private | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1516 | "C:\Users\admin\Downloads\anydesk__1_.exe" --local-service | C:\Users\admin\Downloads\anydesk__1_.exe | anydesk__1_.exe | ||||||||||||
User: admin Company: philandro Software GmbH Integrity Level: MEDIUM Description: AnyDesk Exit code: 0 Version: 6.0.8.0 Modules
| |||||||||||||||
| 1628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,3908618913888703686,6117652162698556669,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=13326575690023190931 --mojo-platform-channel-handle=3148 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 339
Read events
2 787
Write events
546
Delete events
6
Modification events
| (PID) Process: | (2120) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2544-13247617262224875 |
Value: 259 | |||
| (PID) Process: | (2544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2544) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
51
Suspicious files
70
Text files
323
Unknown types
23
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F8E07EE-9F0.pma | — | |
MD5:— | SHA256:— | |||
| 2544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\45fd7edd-e3b7-4419-87ef-79a41570d3f8.tmp | — | |
MD5:— | SHA256:— | |||
| 2544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 2544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF2d41e0.TMP | text | |
MD5:— | SHA256:— | |||
| 2544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF2d41ff.TMP | text | |
MD5:— | SHA256:— | |||
| 2544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
55
DNS requests
27
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3460 | chrome.exe | GET | 301 | 199.34.228.53:80 | http://amazonhelpyou.weebly.com/ | US | html | 376 b | suspicious |
1516 | anydesk__1_.exe | POST | 204 | 99.81.142.100:80 | http://api.playanext.com/httpapi | US | — | — | whitelisted |
3560 | alpemix.exe | GET | 200 | 77.92.134.180:80 | http://77.92.134.180/site/servers.htm | TR | html | 58 b | suspicious |
3560 | alpemix.exe | GET | 200 | 77.92.134.180:80 | http://alpemix.com/site/filecontrol.htm | TR | text | 2.56 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3460 | chrome.exe | 172.217.23.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3460 | chrome.exe | 216.58.212.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
3460 | chrome.exe | 199.34.228.54:80 | amazonhelpyou.weebly.com | Weebly, Inc. | US | suspicious |
3460 | chrome.exe | 199.34.228.53:80 | amazonhelpyou.weebly.com | Weebly, Inc. | US | suspicious |
3460 | chrome.exe | 199.34.228.54:443 | amazonhelpyou.weebly.com | Weebly, Inc. | US | suspicious |
3460 | chrome.exe | 216.58.207.67:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3460 | chrome.exe | 142.250.74.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3460 | chrome.exe | 172.217.22.10:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3460 | chrome.exe | 216.58.206.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3460 | chrome.exe | 74.115.50.109:443 | www.weebly.com | Weebly, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
amazonhelpyou.weebly.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
cdn2.editmysite.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.weebly.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1516 | anydesk__1_.exe | Potential Corporate Privacy Violation | ET POLICY SSL/TLS Certificate Observed (AnyDesk Remote Desktop Software) |
1516 | anydesk__1_.exe | Potential Corporate Privacy Violation | ET USER_AGENTS AnyDesk Remote Desktop Software User-Agent |
Process | Message |
|---|---|
awesun_1.5.0.30116.exe | 2020-10-19 22:42:28.711 = Debug = [monitor]PRIMARY, left=0, top=0
|
awesun_1.5.0.30116.exe | 2020-10-19 22:42:29.850 = Debug = [monitor]PRIMARY, left=0, top=0
|
awesun_1.5.0.30116.exe | 2020-10-19 22:42:33.383 = Debug = get_default_interface_ip ok with 192.168.100.242
|
awesun_1.5.0.30116.exe | 2020-10-19 22:42:33.383 - Info - [mac] mac address:12:A9:86:6C:77:DE
|
awesun_1.5.0.30116.exe | 2020-10-19 22:42:33.383 - Info - [mac] local ip:192.168.100.242
|
awesun_1.5.0.30116.exe | 2020-10-19 22:42:33.384 - Info - [http call3] new call id:1, url:https://asapi.aweray.net/feedback/install
|
awesun_1.5.0.30116.exe | 2020-10-19 22:42:33.386 - Info - [async dns] start resolve dns asapi.aweray.net
|
awesun_1.5.0.30116.exe | 2020-10-19 22:42:33.386 - Info - [http call3] id:1 create new connection : https://asapi.aweray.net:443
|
awesun_1.5.0.30116.exe | 2020-10-19 22:42:33.401 - Info - attempt to connect server asapi.aweray.net:443(34.85.64.198:443)
|
awesun_1.5.0.30116.exe | 2020-10-19 22:42:33.492 - Info - [Install] Create new you write info
|