| File name: | HashCheckInstall-2.1.11.exe |
| Full analysis: | https://app.any.run/tasks/b8954651-2172-4eba-bec3-77f7429ee2c2 |
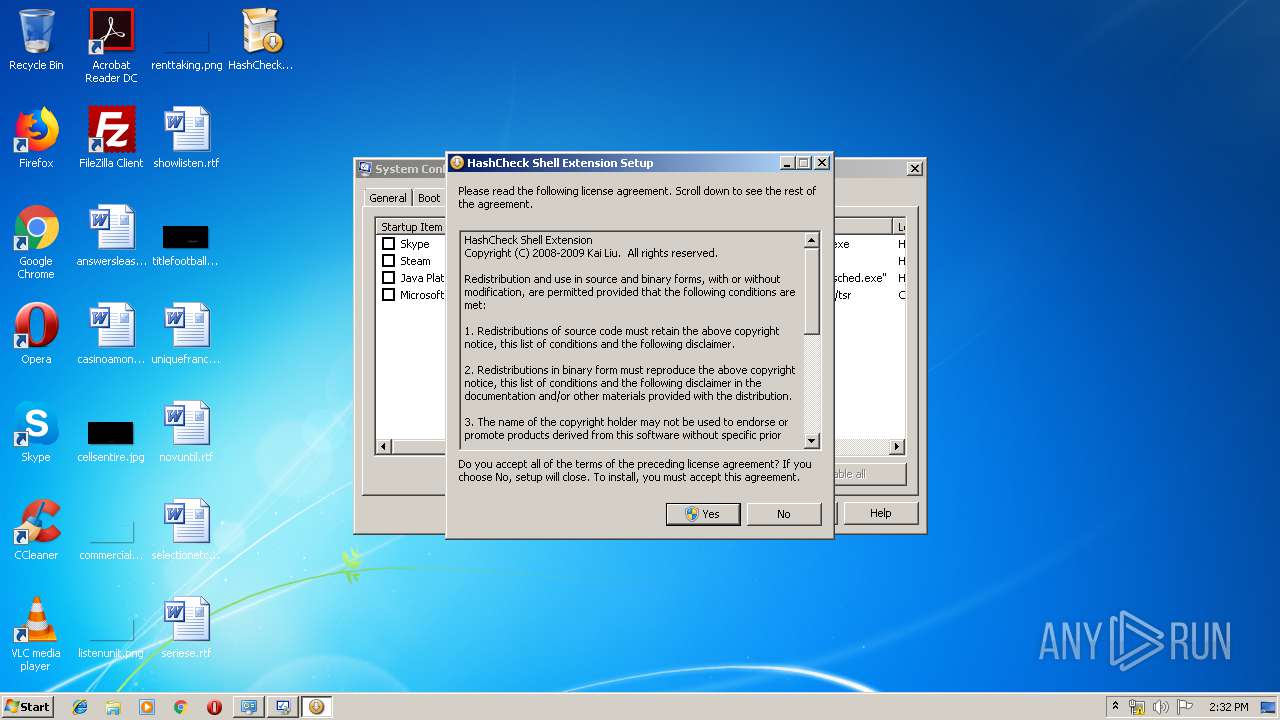
| Verdict: | Malicious activity |
| Analysis date: | September 06, 2019, 13:31:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B99FF61DEF8125E2178CE6F1F7D6D8C0 |
| SHA1: | D3CB884C8FC3F04720D176777508C4F5DD2DF40C |
| SHA256: | B6A43DC0F8F296F933F736DF99689395E5B36E65CDCDBAF1C644C65E42ACCC54 |
| SSDEEP: | 1536:nSFvCJIzL+BCAX7NeYRNsKyjrDW26MzzYylDnnpjB95/u4a6NeAss1G:nqvCJIzL+BC2eqsKyjrq26ScylDnnpjo |
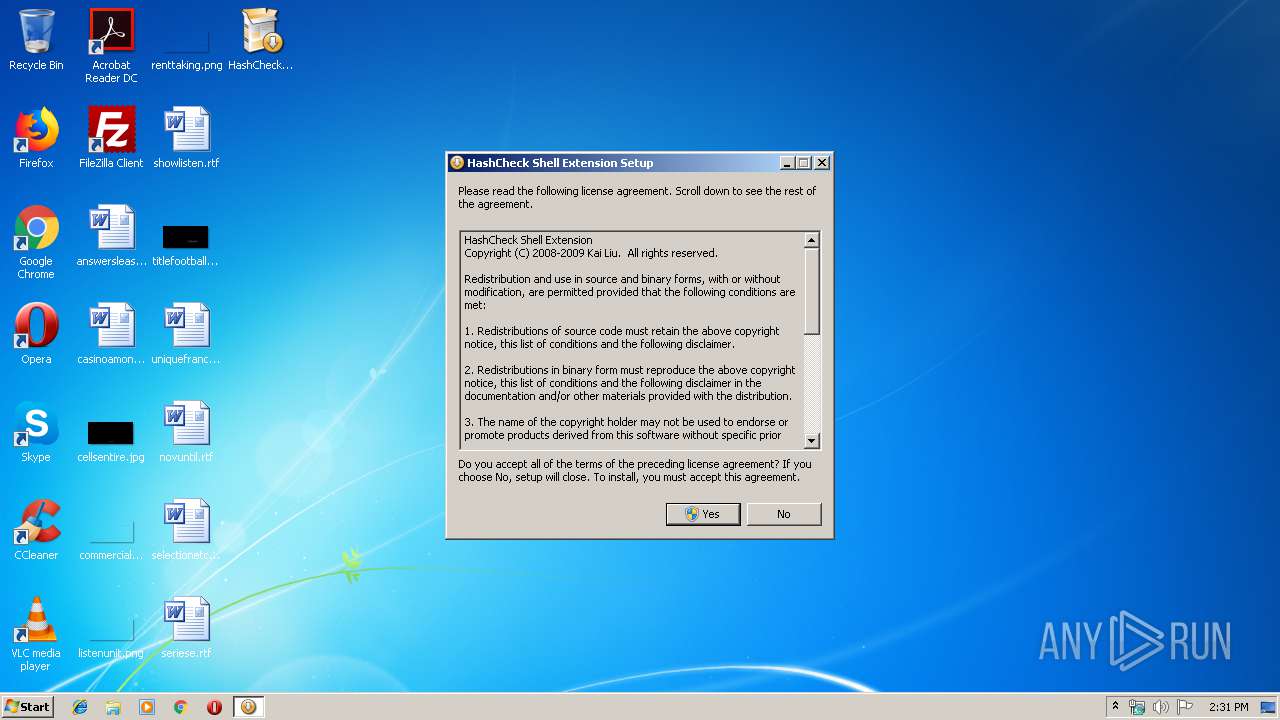
MALICIOUS
Loads dropped or rewritten executable
- HashCheckInstall-2.1.11.exe (PID: 3476)
- explorer.exe (PID: 276)
SUSPICIOUS
Executable content was dropped or overwritten
- HashCheckInstall-2.1.11.exe (PID: 3476)
Application launched itself
- HashCheckInstall-2.1.11.exe (PID: 2920)
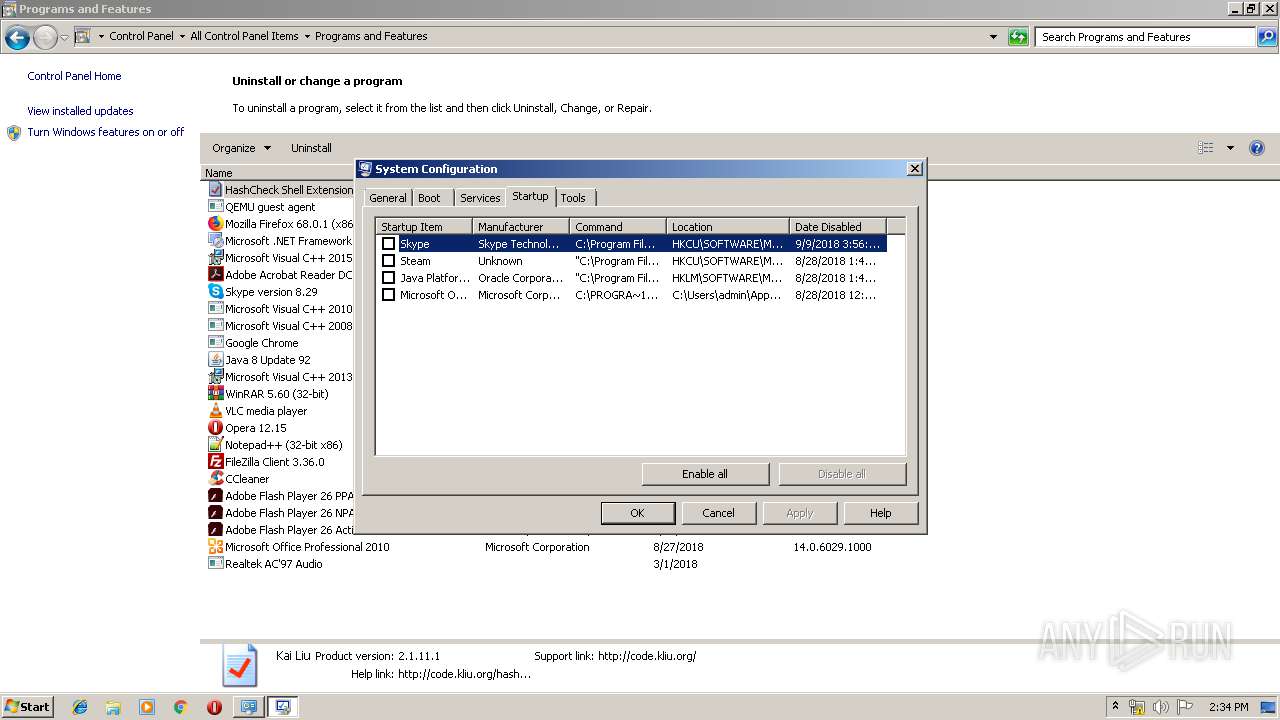
Creates COM task schedule object
- HashCheckInstall-2.1.11.exe (PID: 3476)
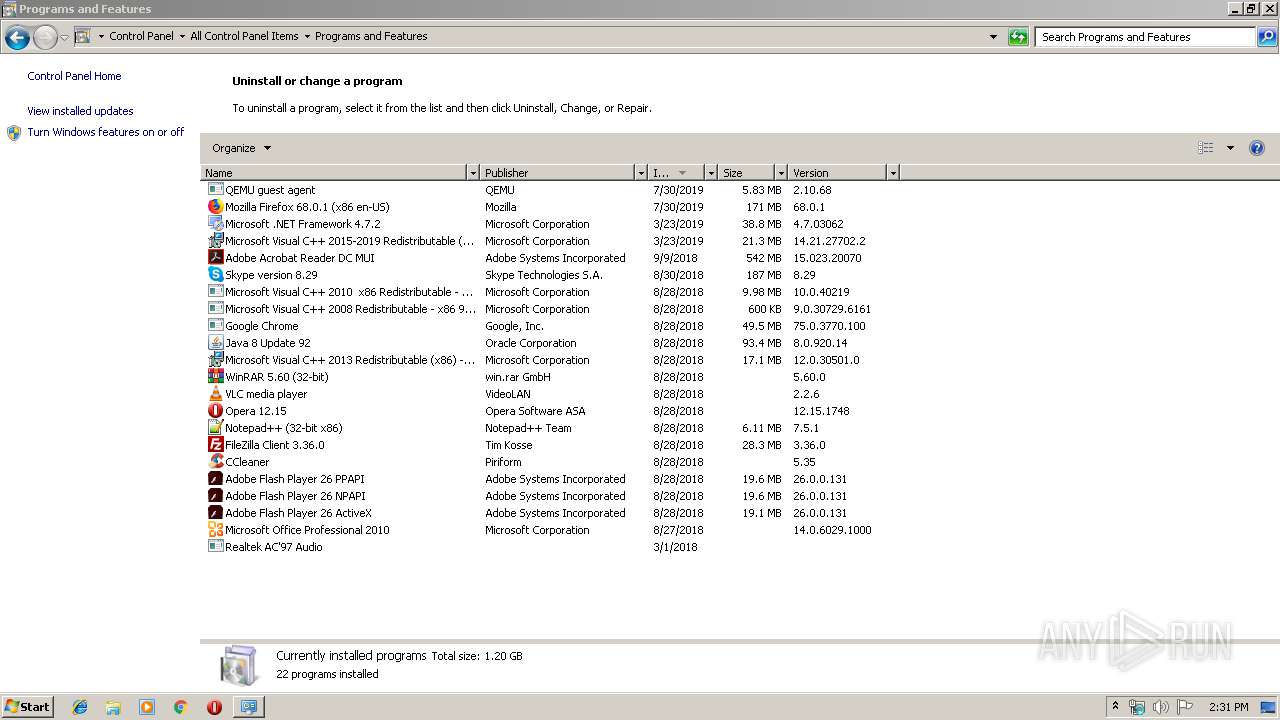
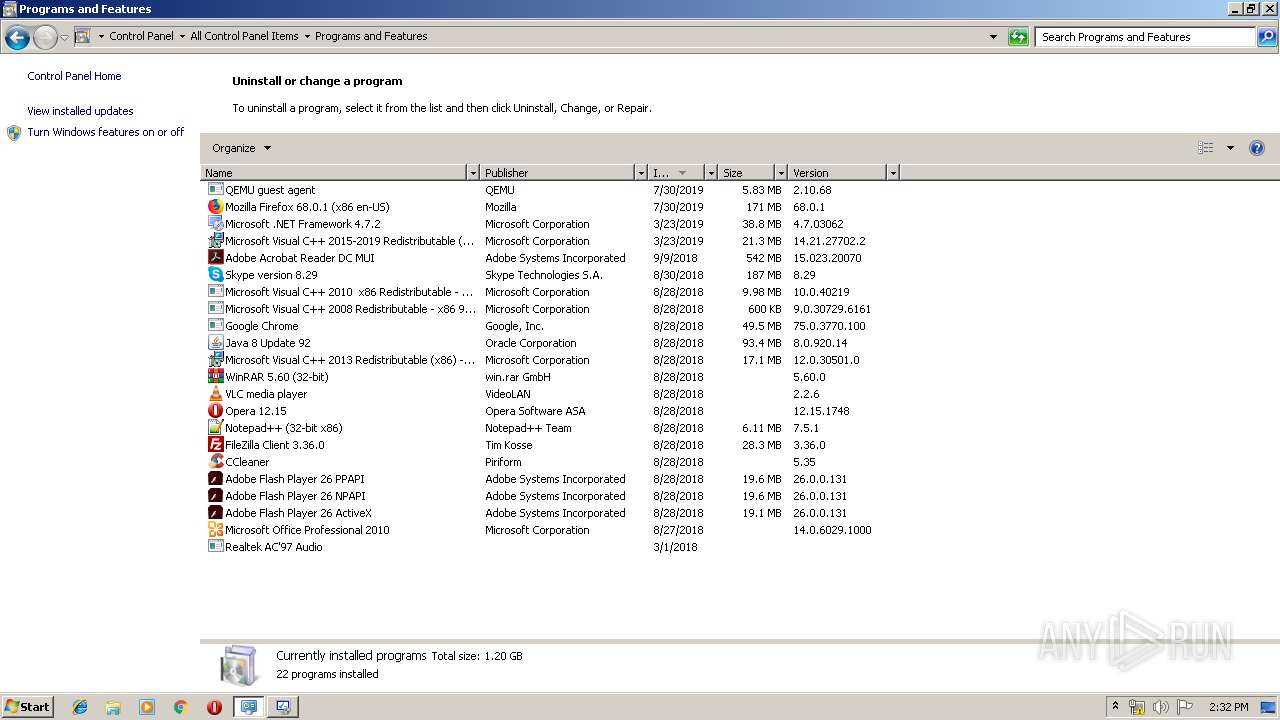
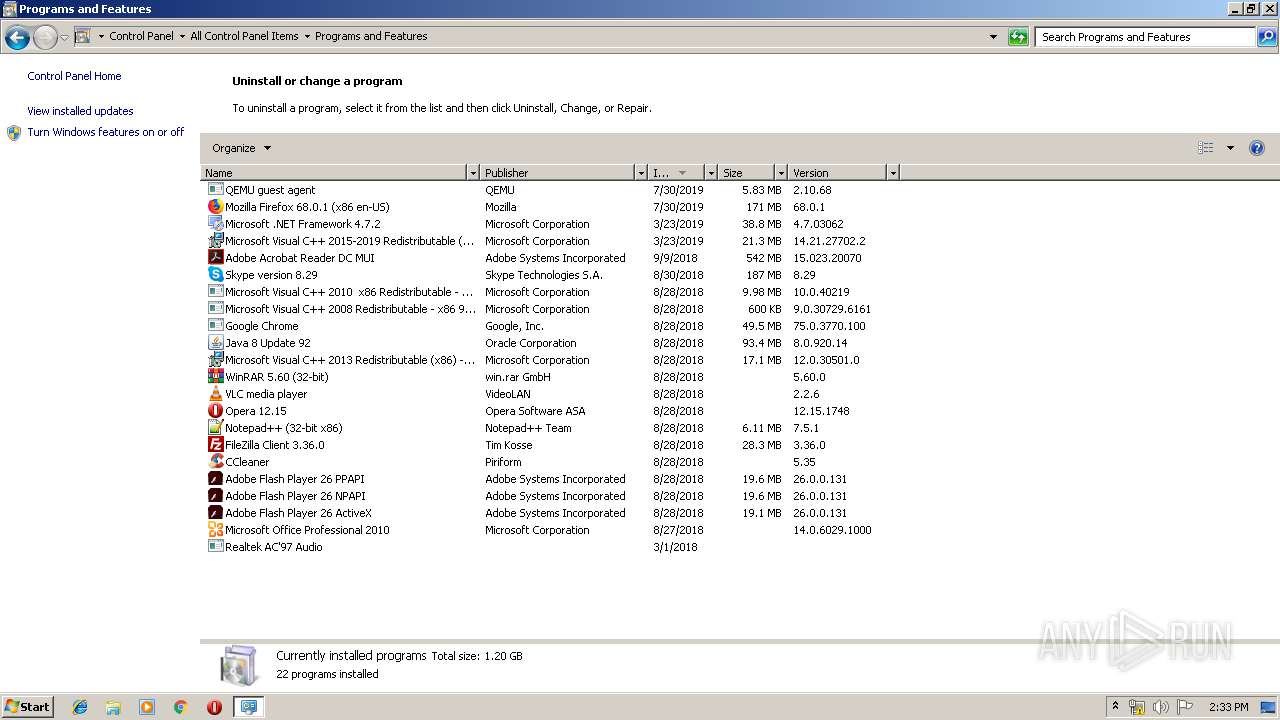
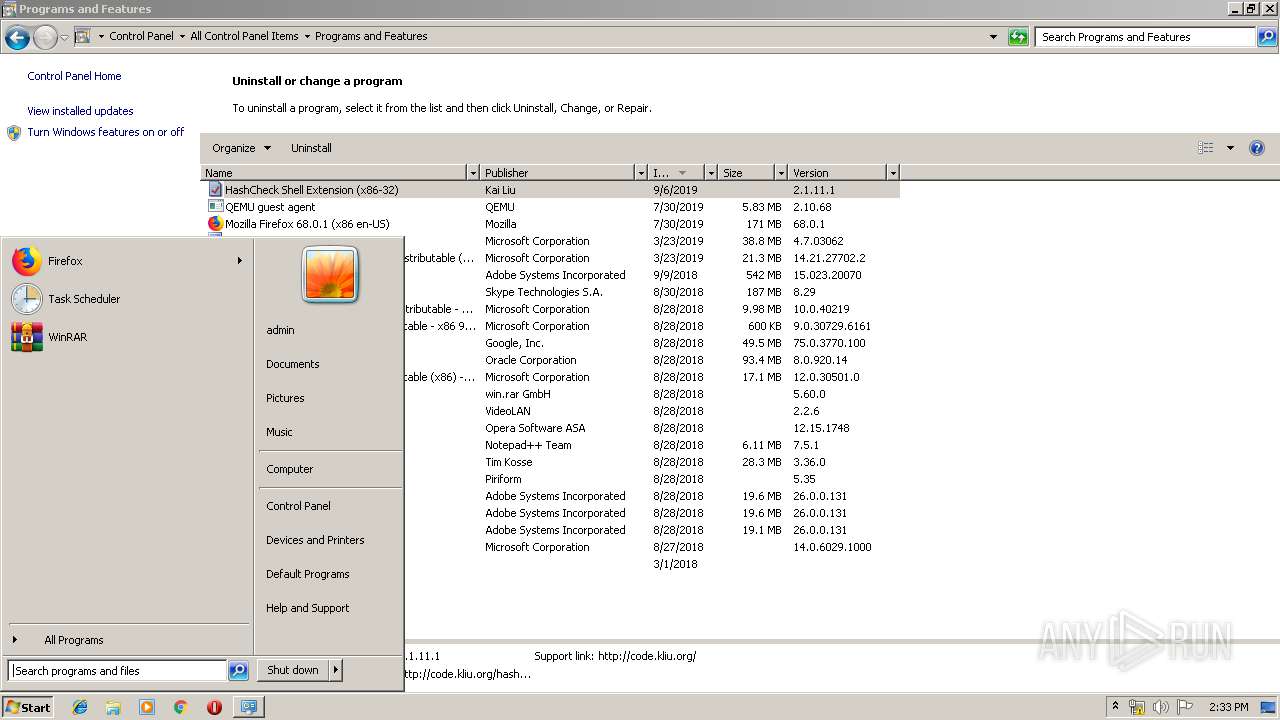
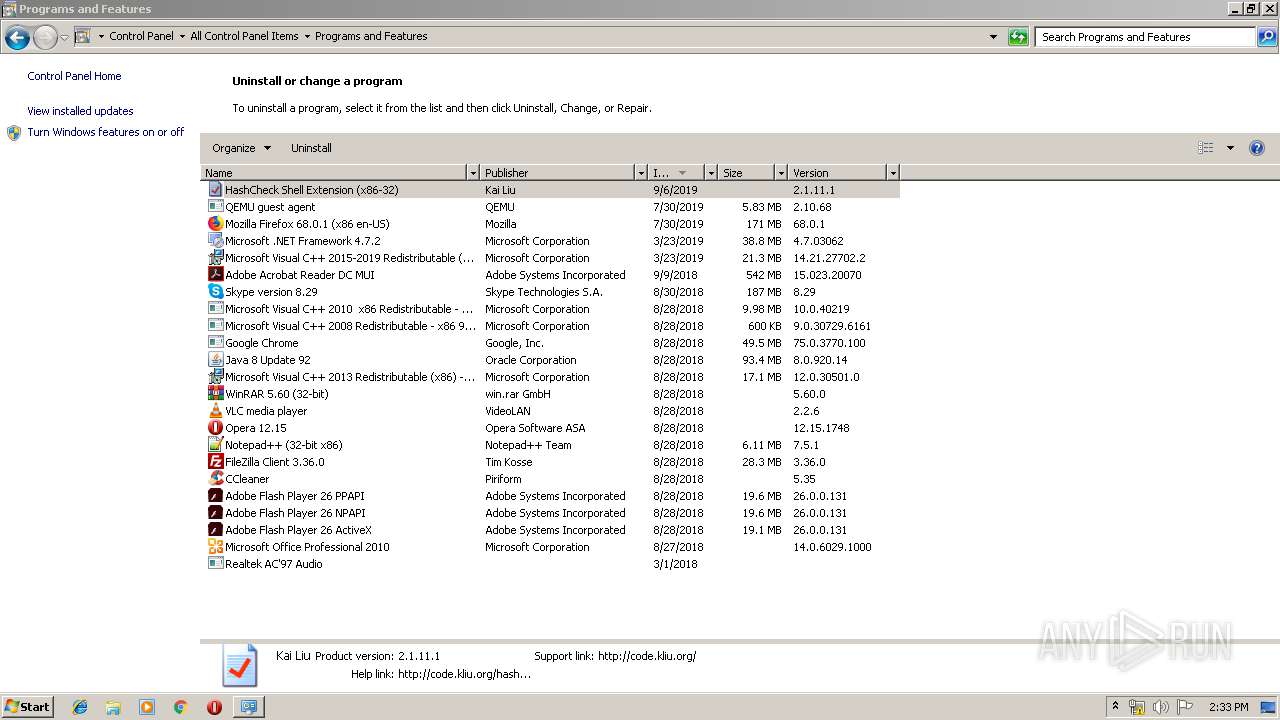
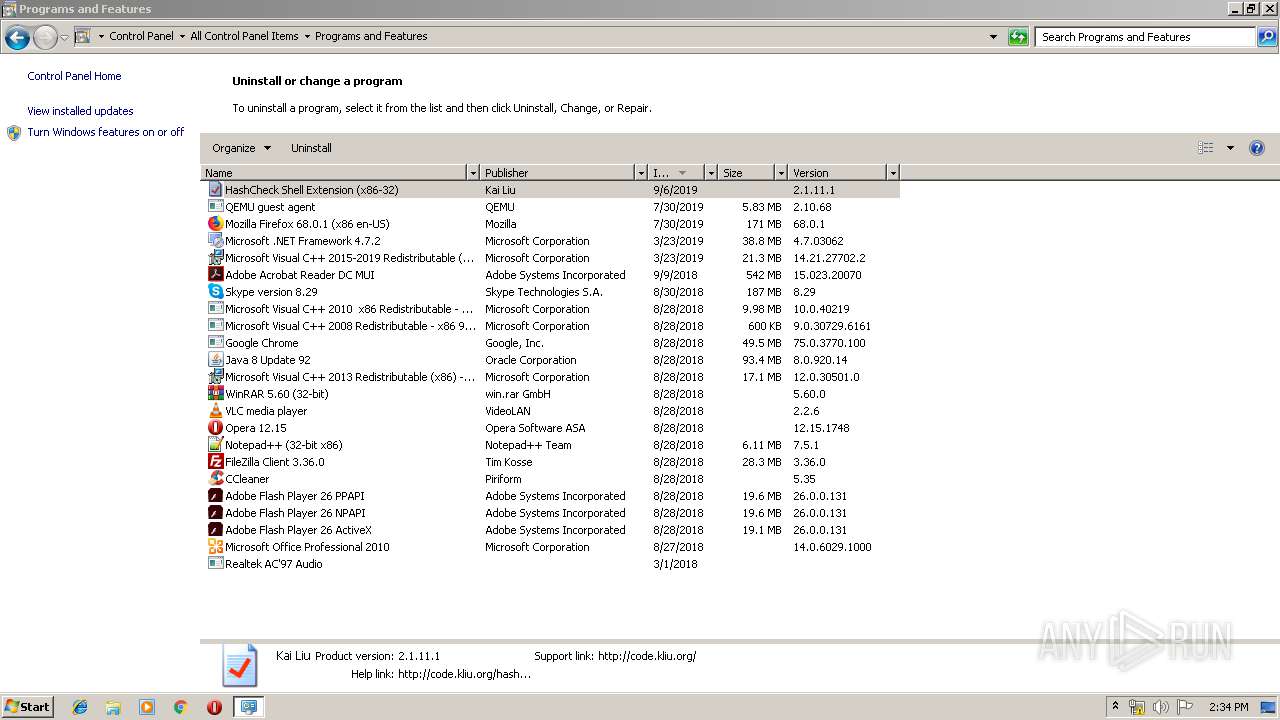
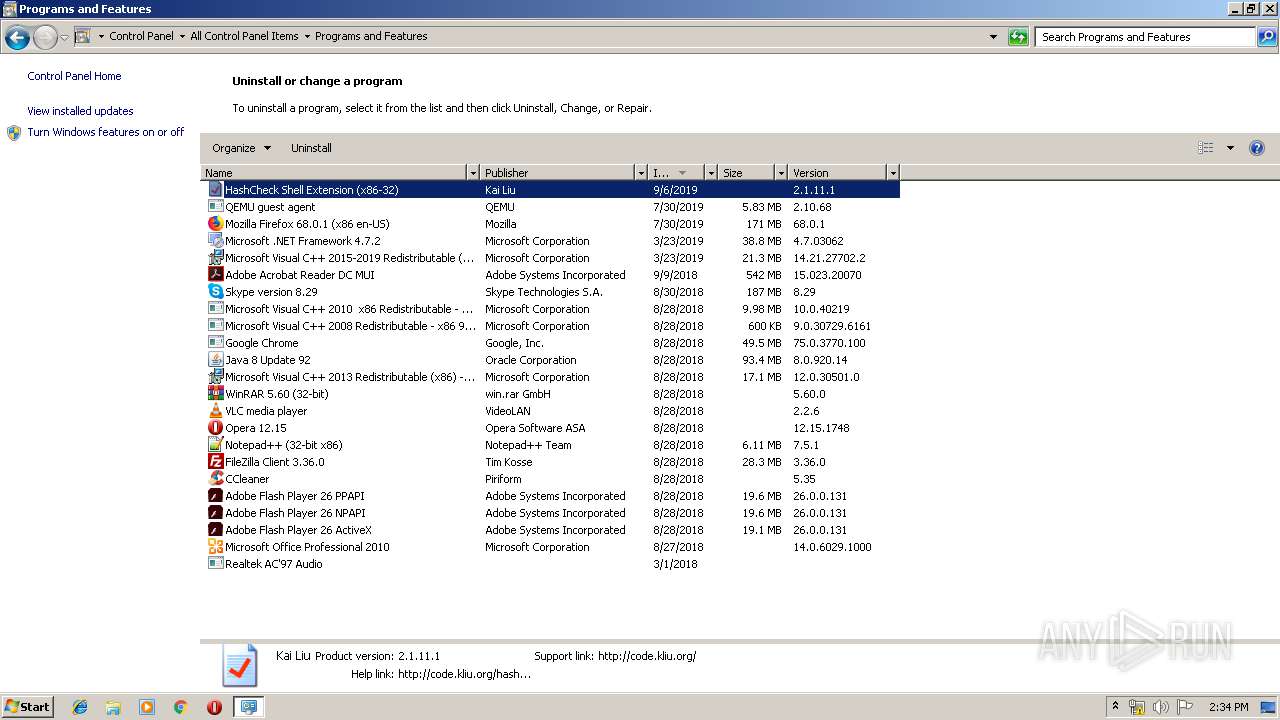
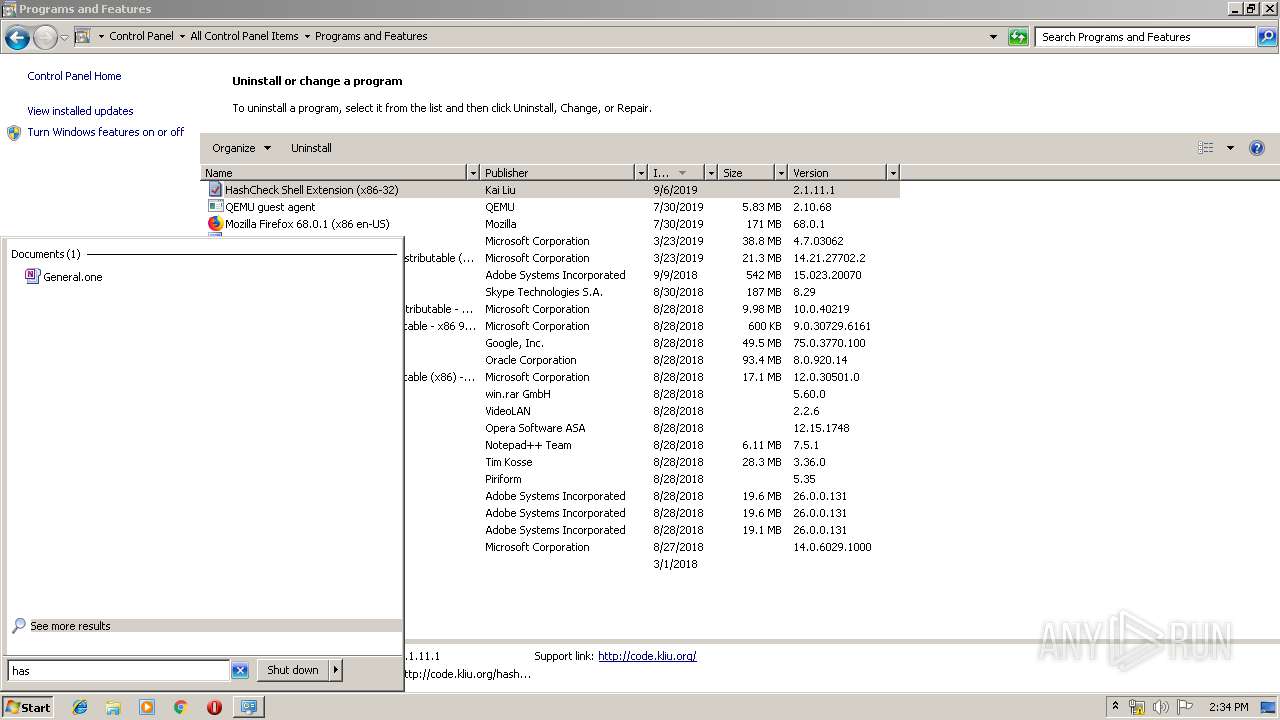
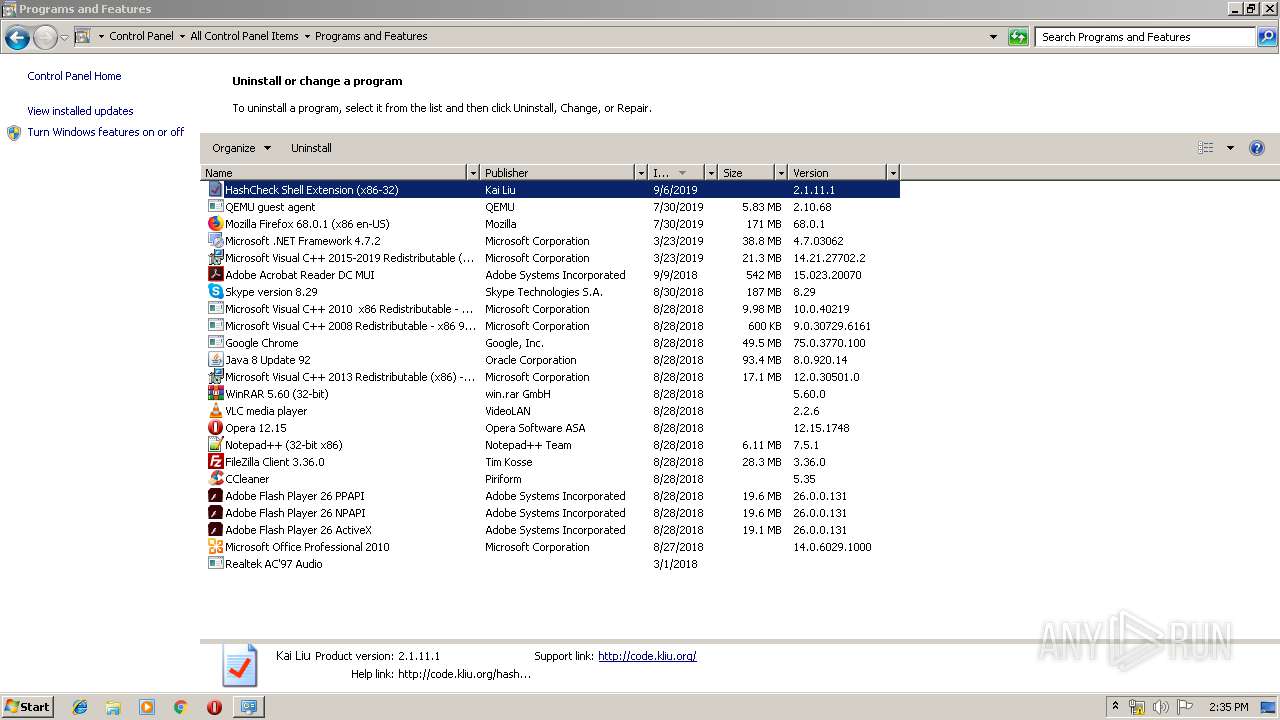
Creates a software uninstall entry
- HashCheckInstall-2.1.11.exe (PID: 3476)
Modifies the open verb of a shell class
- HashCheckInstall-2.1.11.exe (PID: 3476)
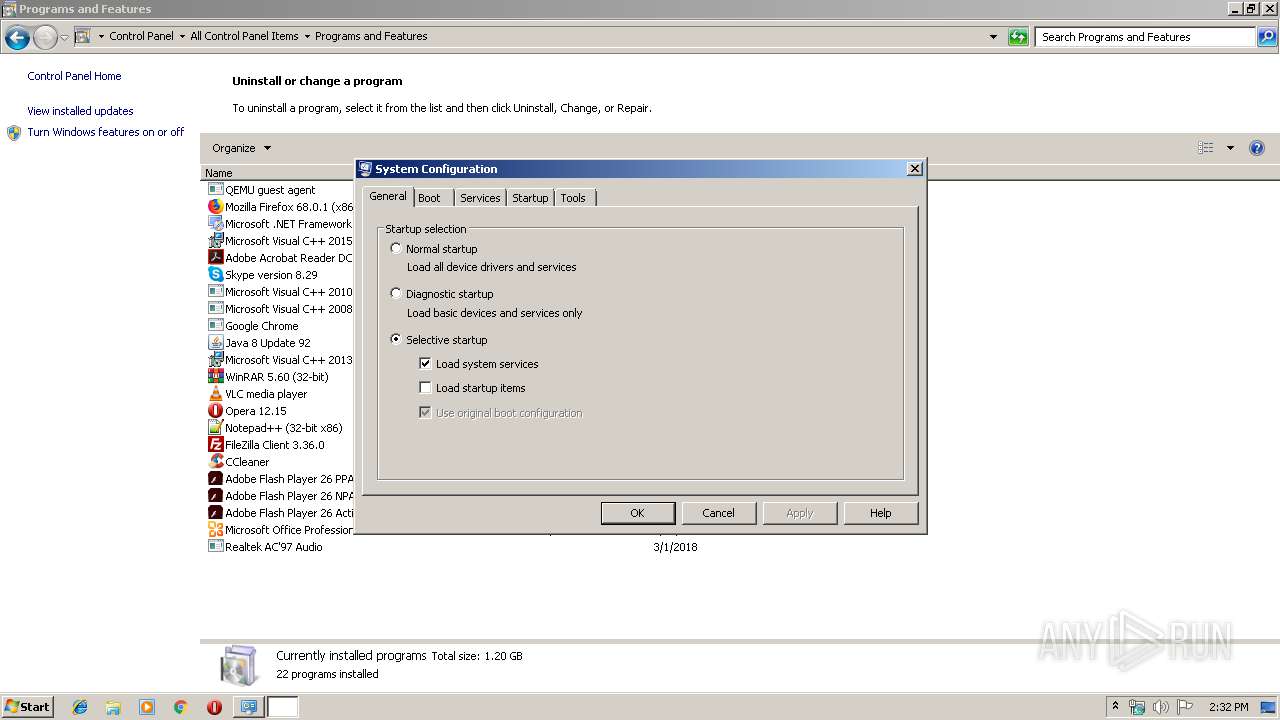
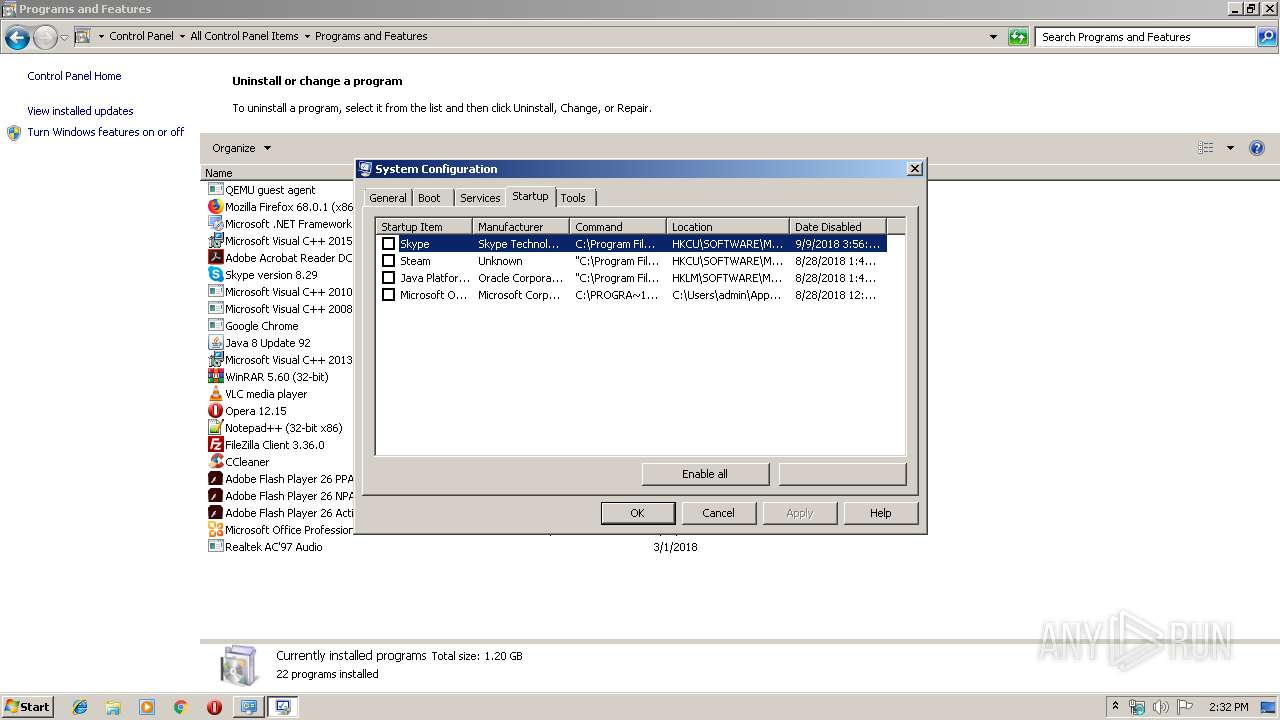
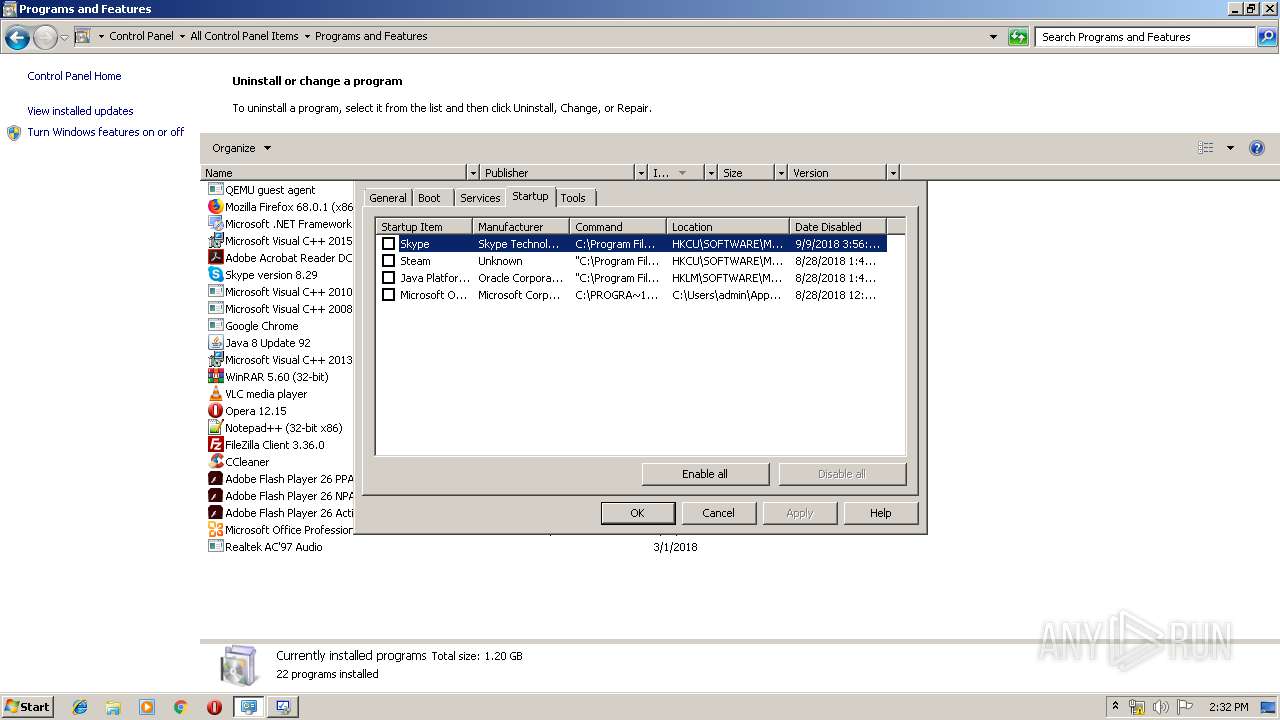
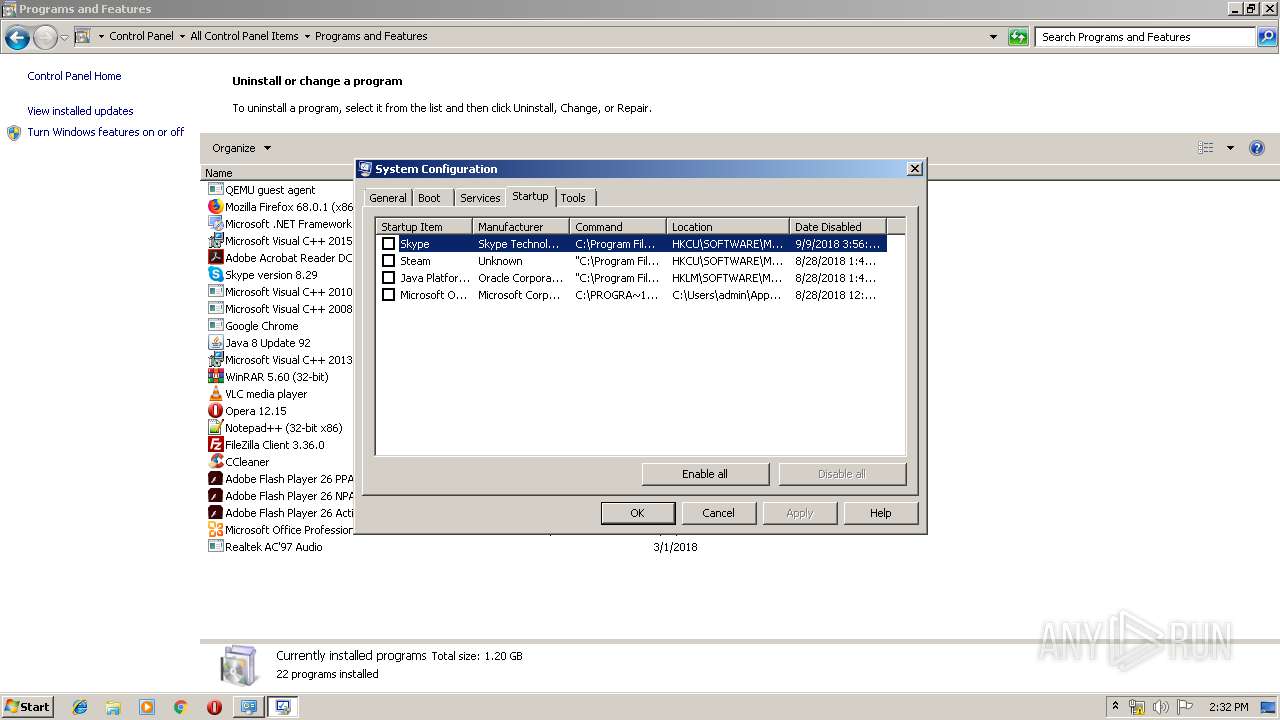
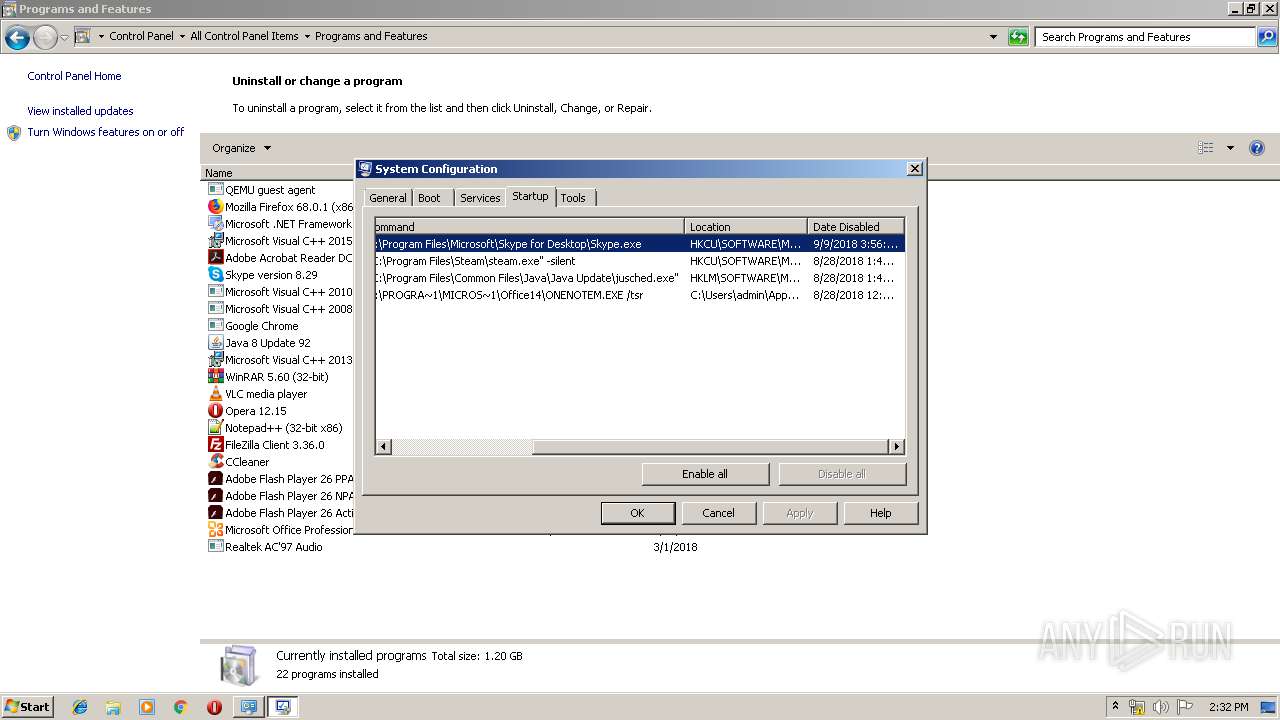
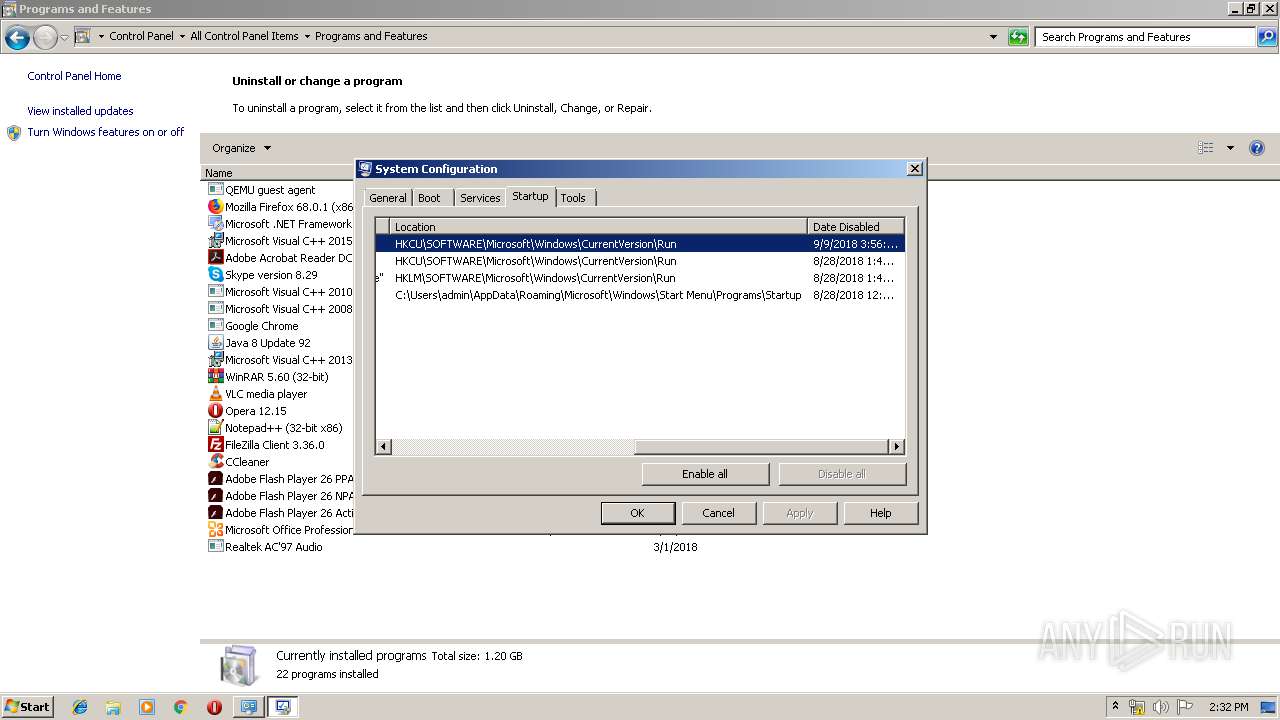
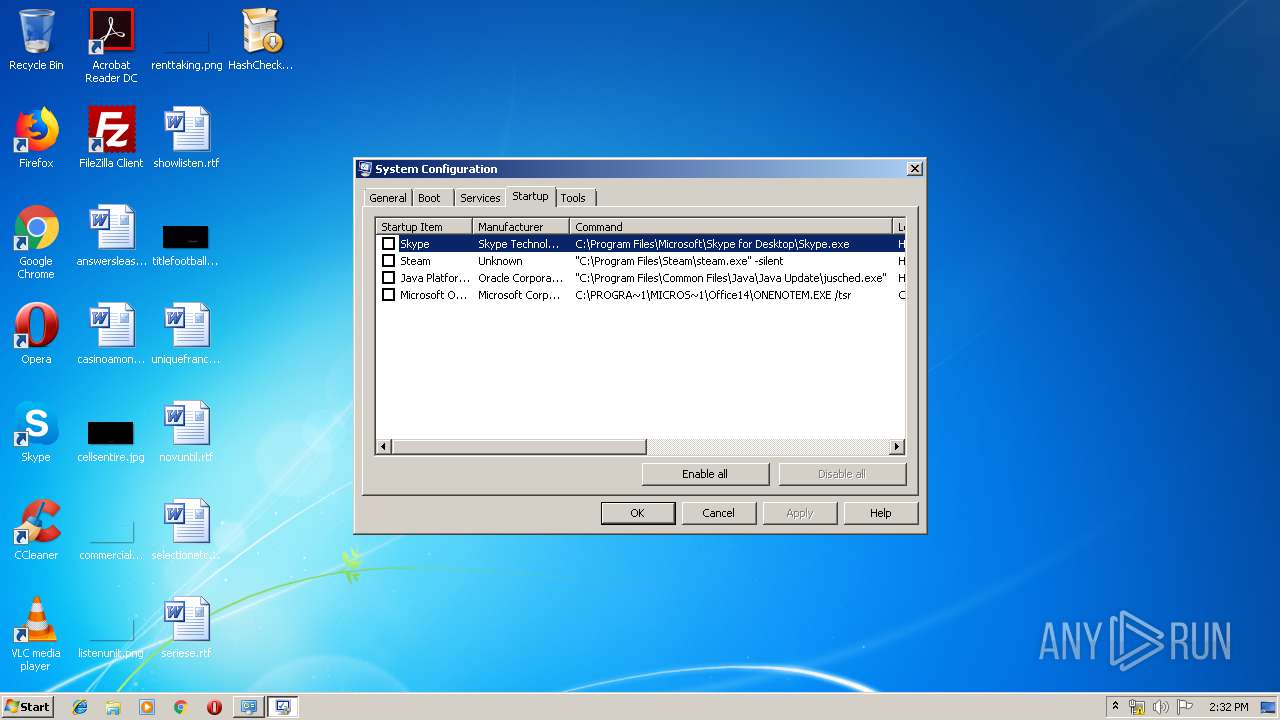
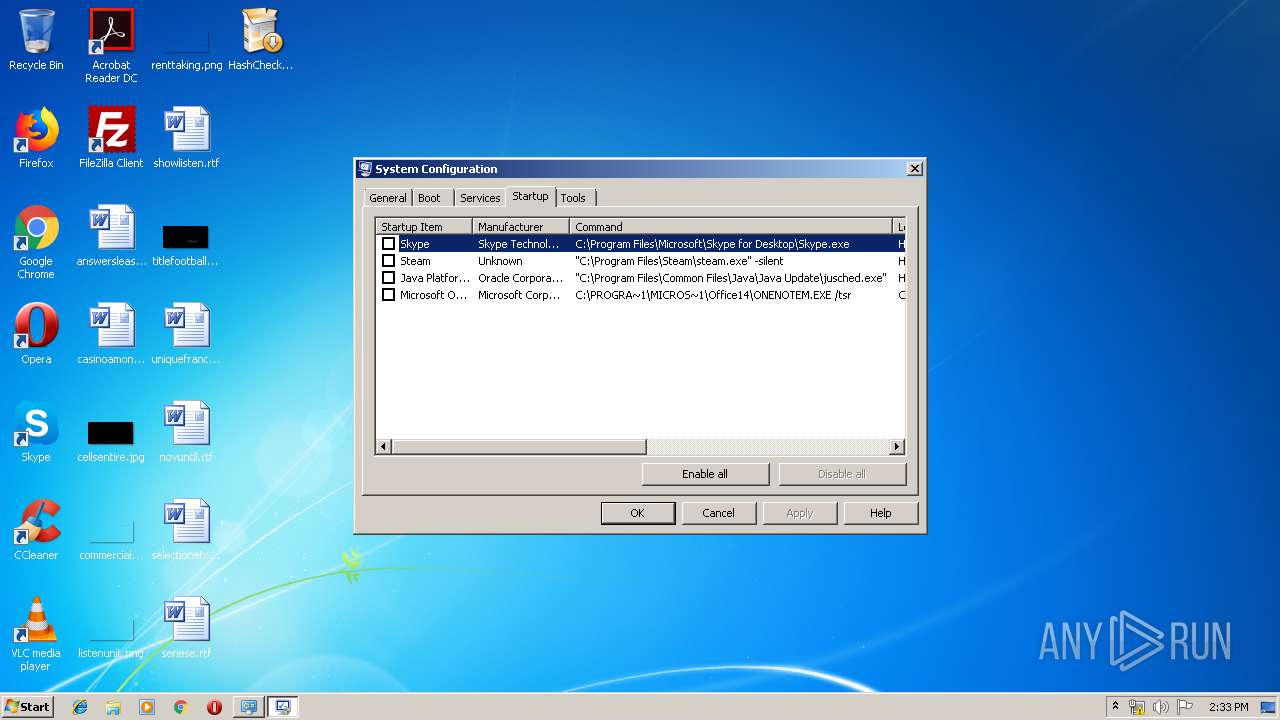
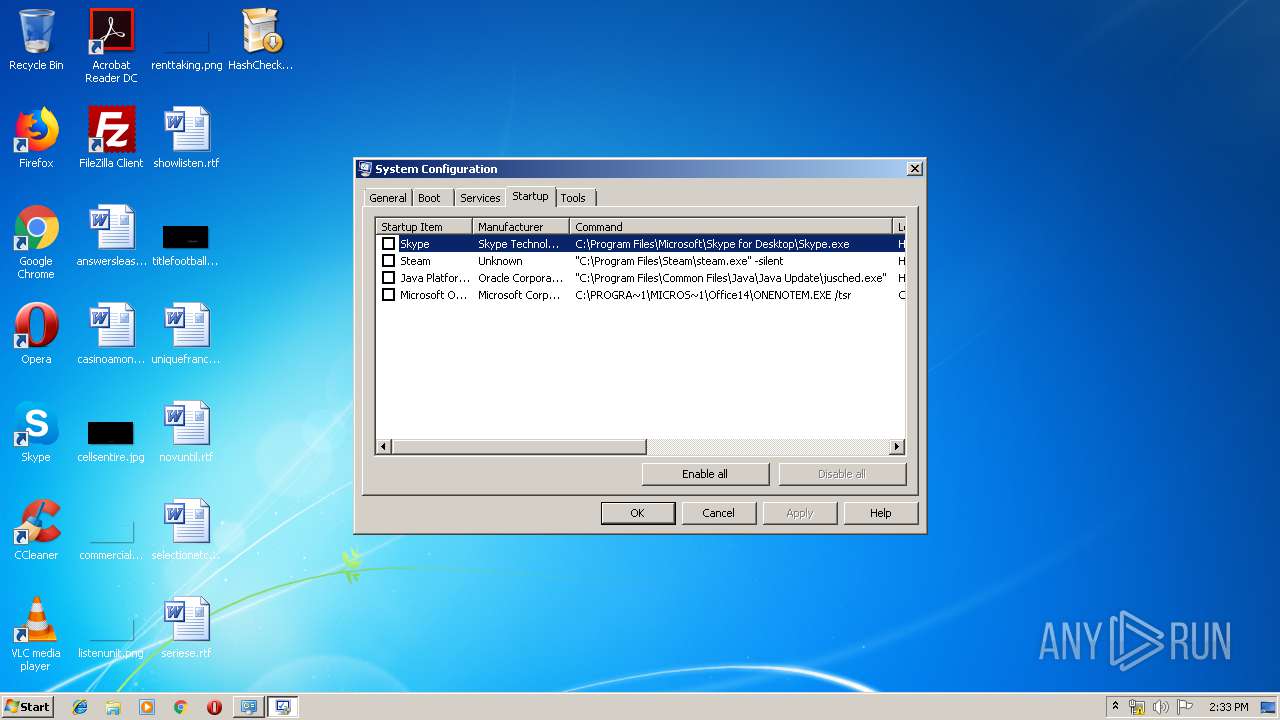
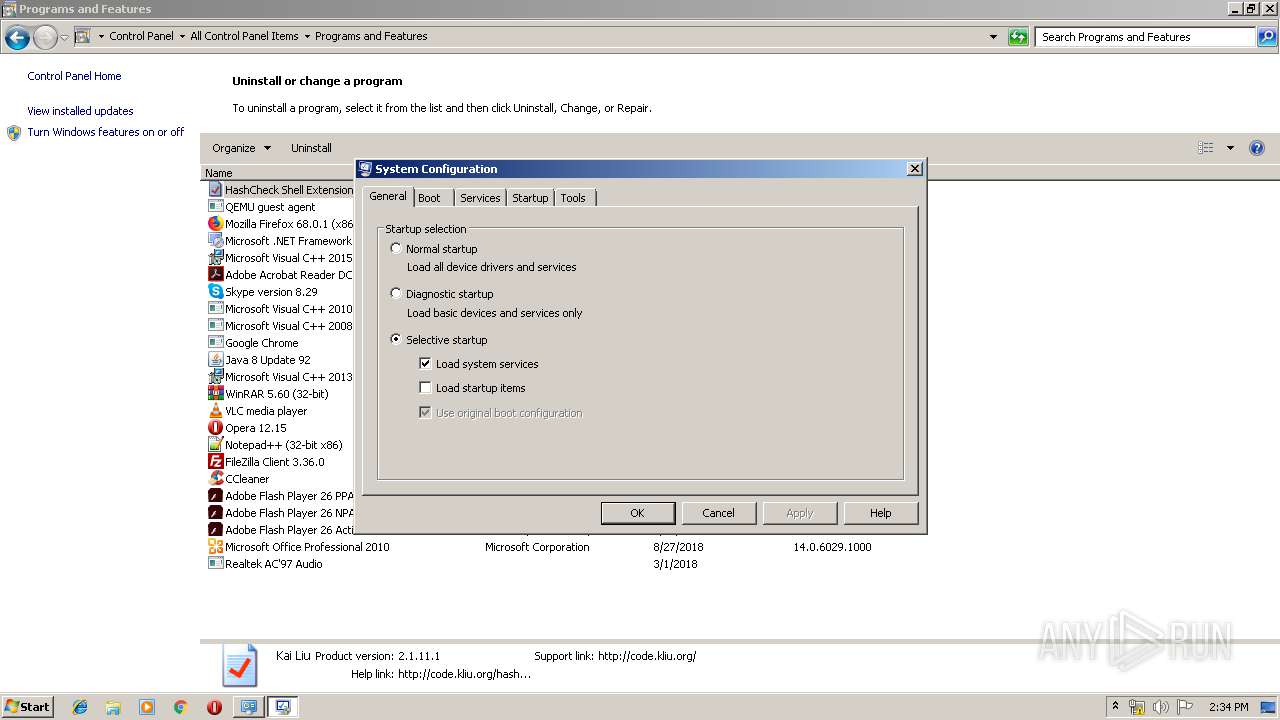
Low-level read access rights to disk partition
- msconfig.exe (PID: 2872)
- msconfig.exe (PID: 2452)
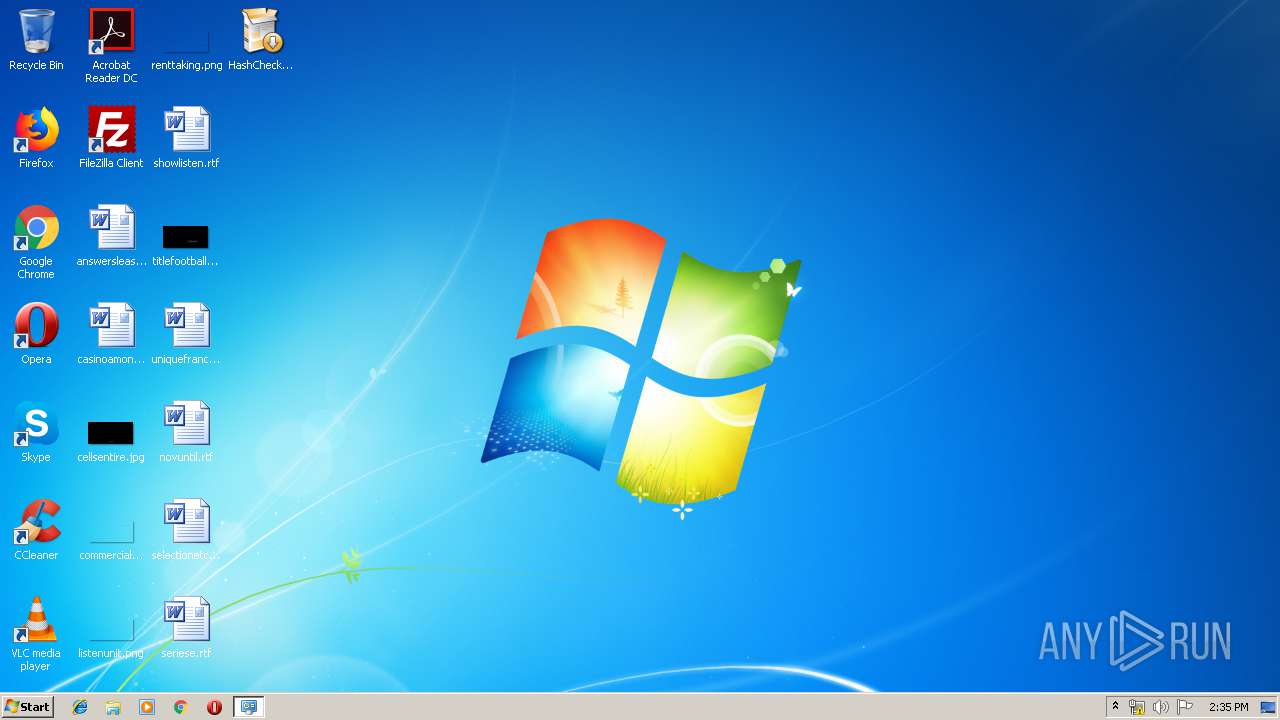
Creates files in the user directory
- explorer.exe (PID: 276)
Creates files in the Windows directory
- HashCheckInstall-2.1.11.exe (PID: 3476)
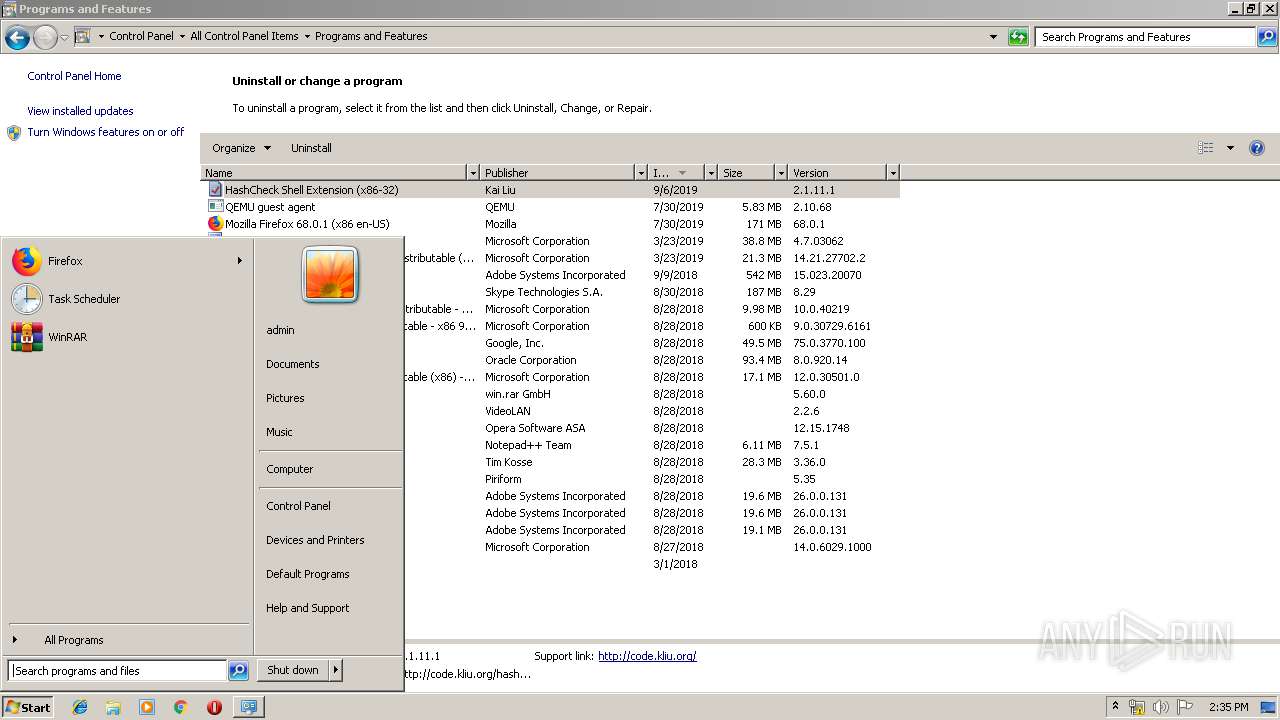
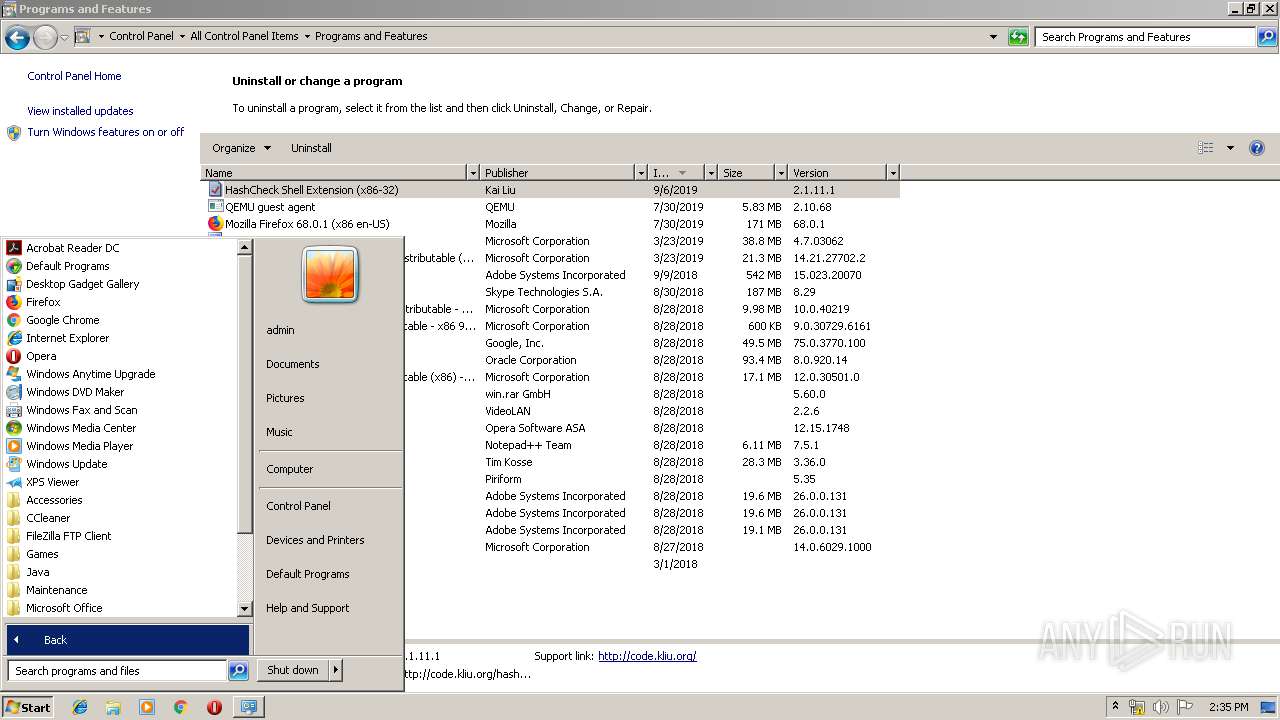
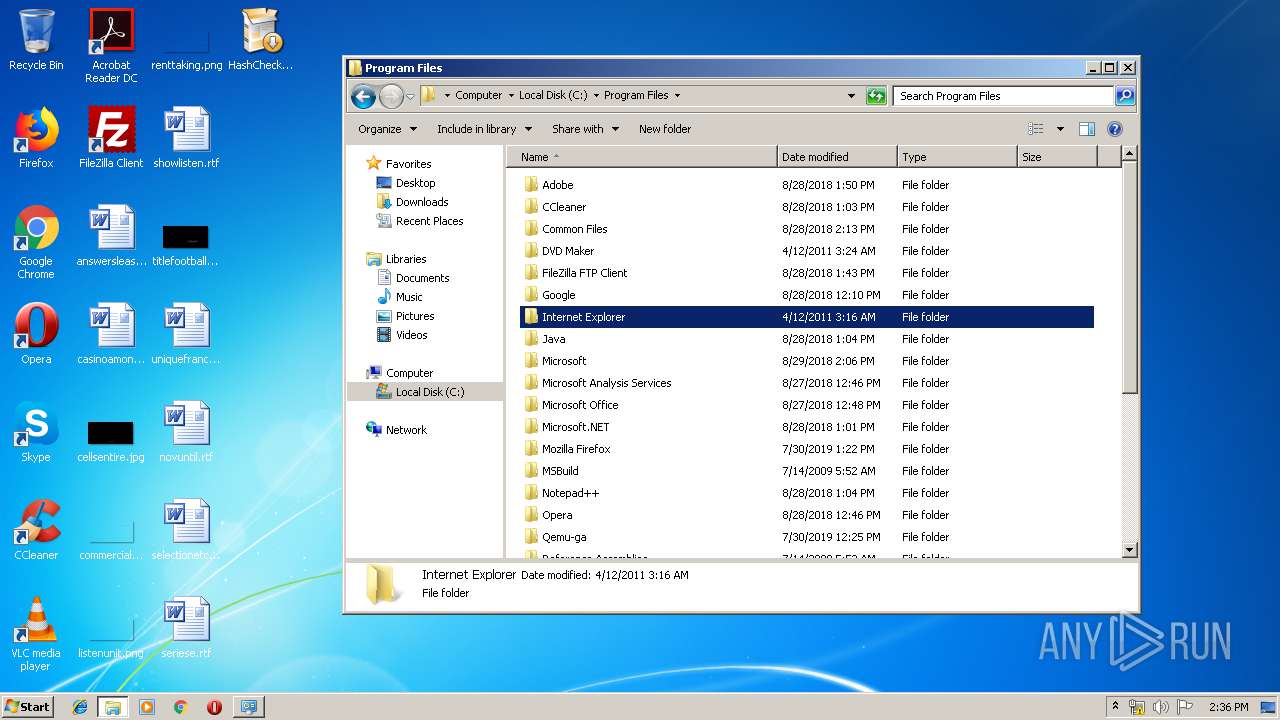
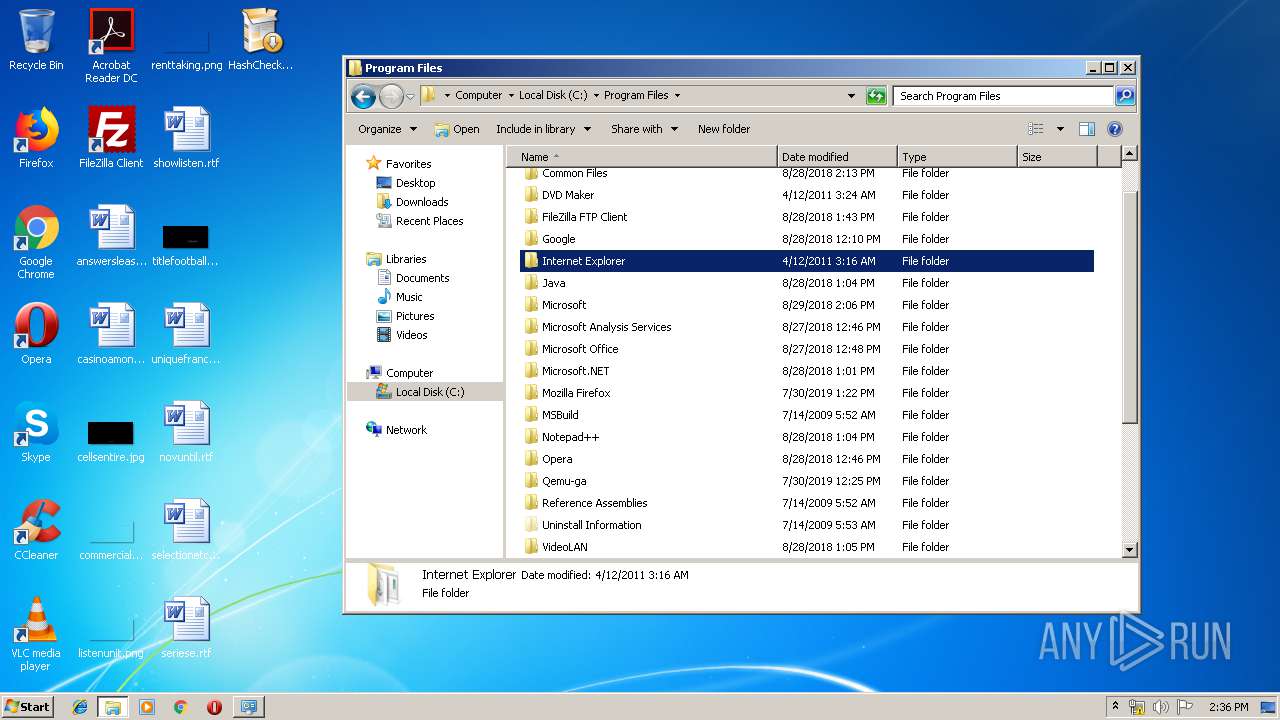
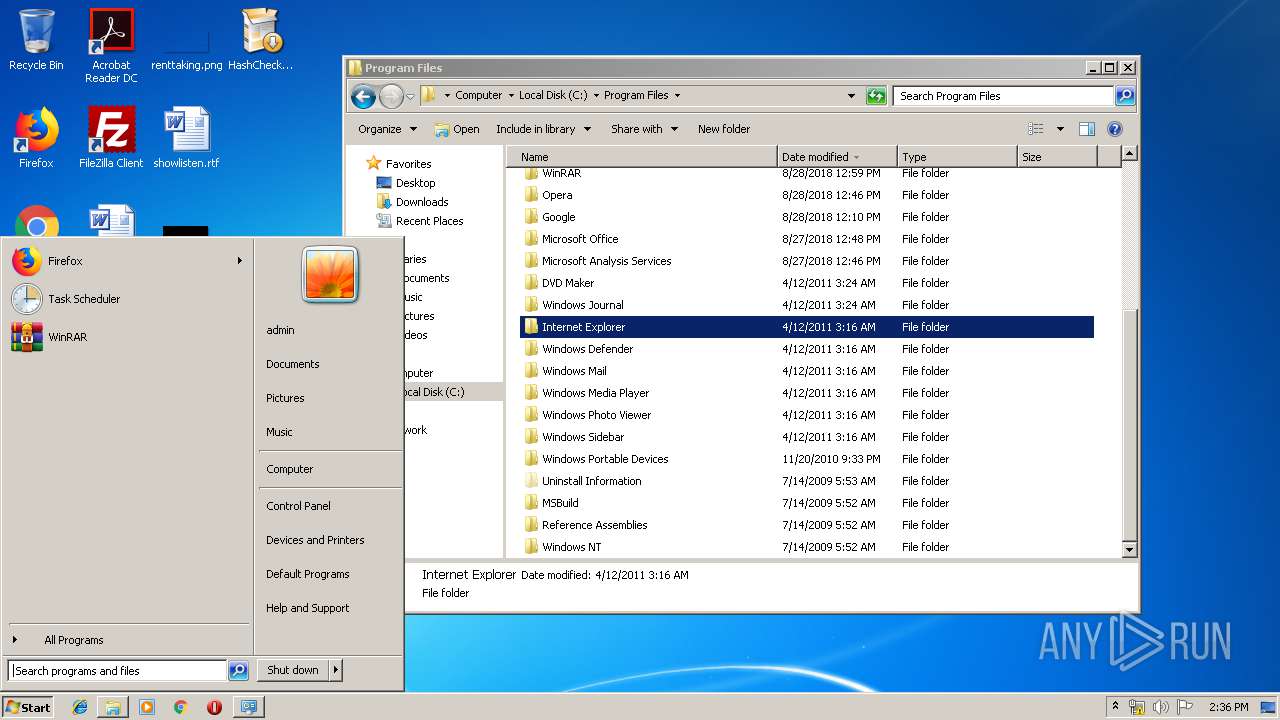
Starts Internet Explorer
- explorer.exe (PID: 276)
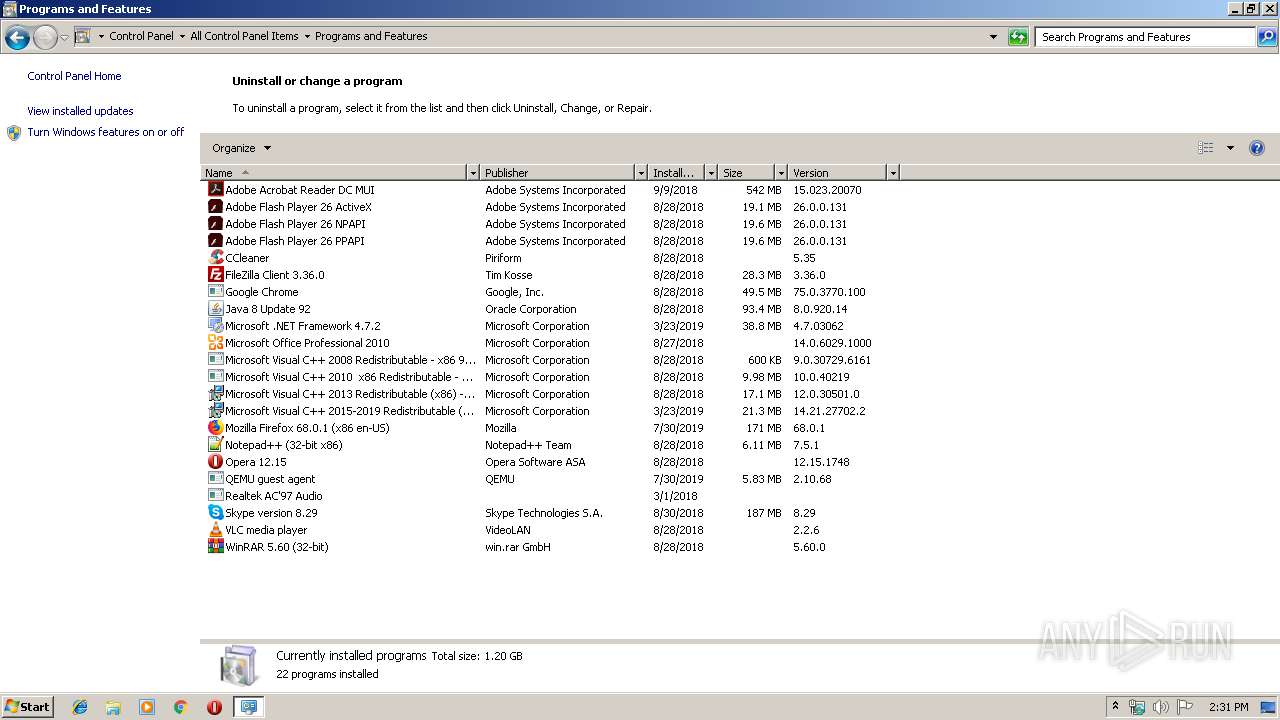
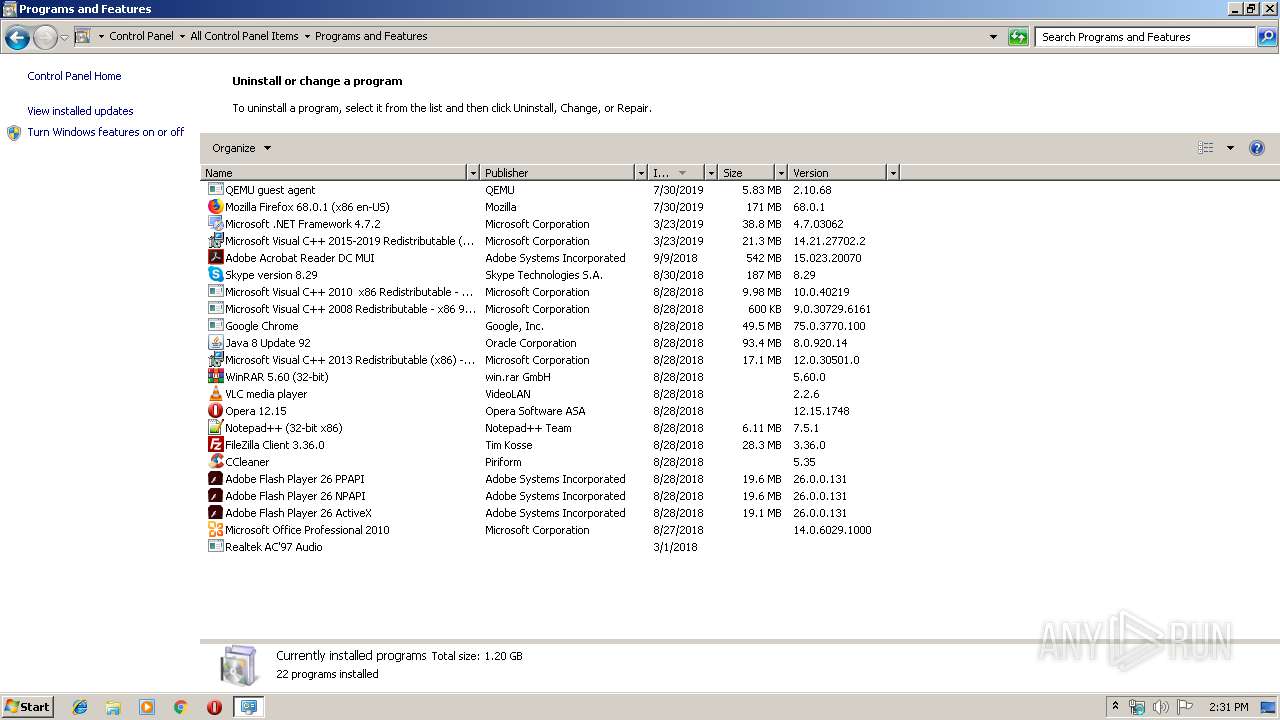
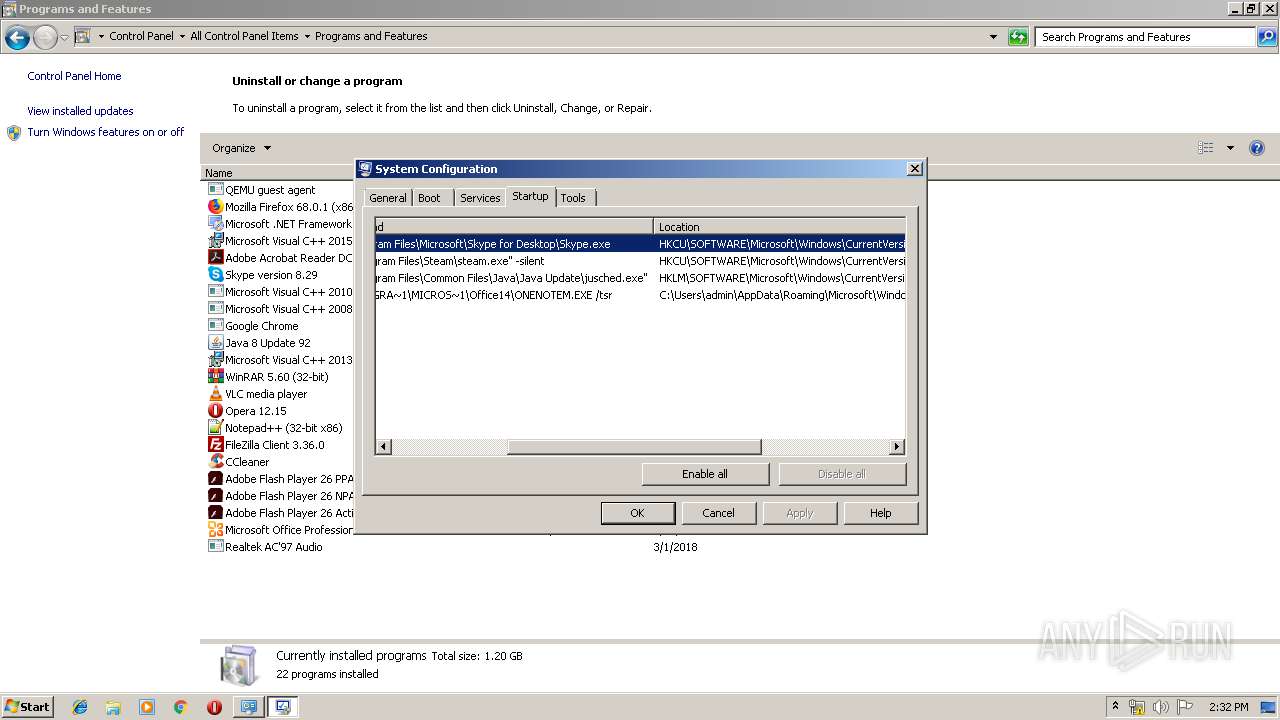
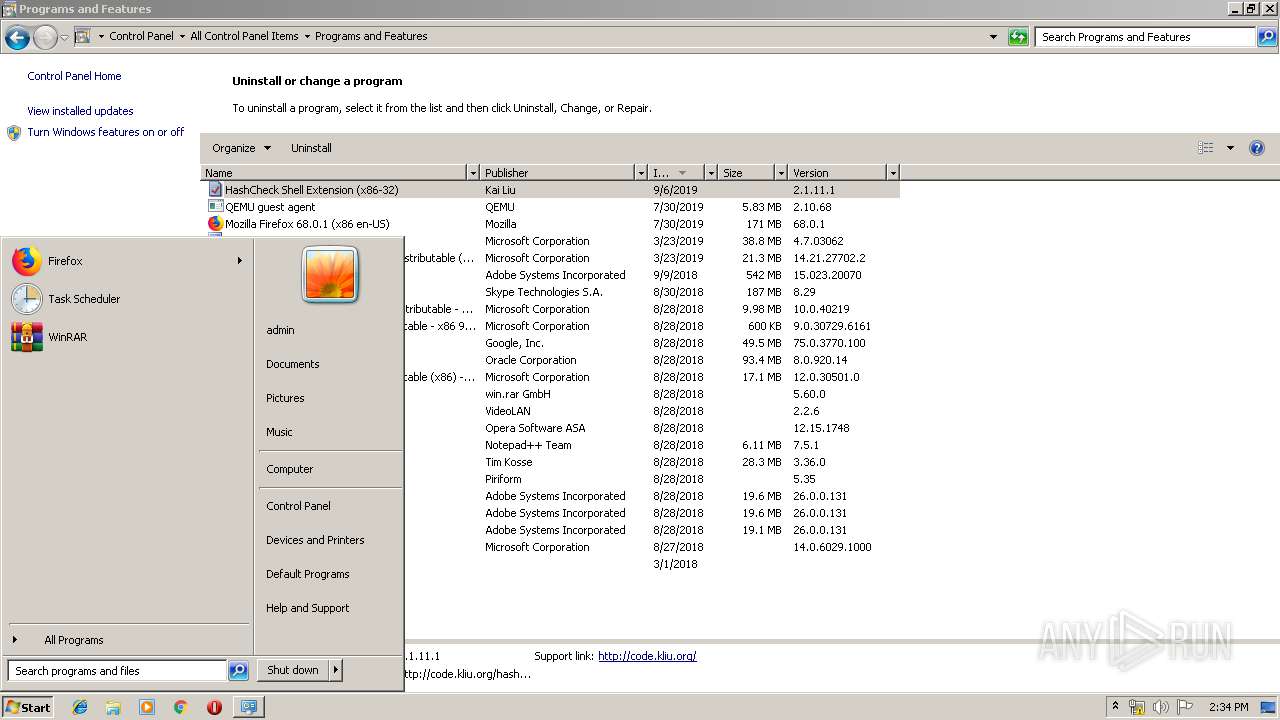
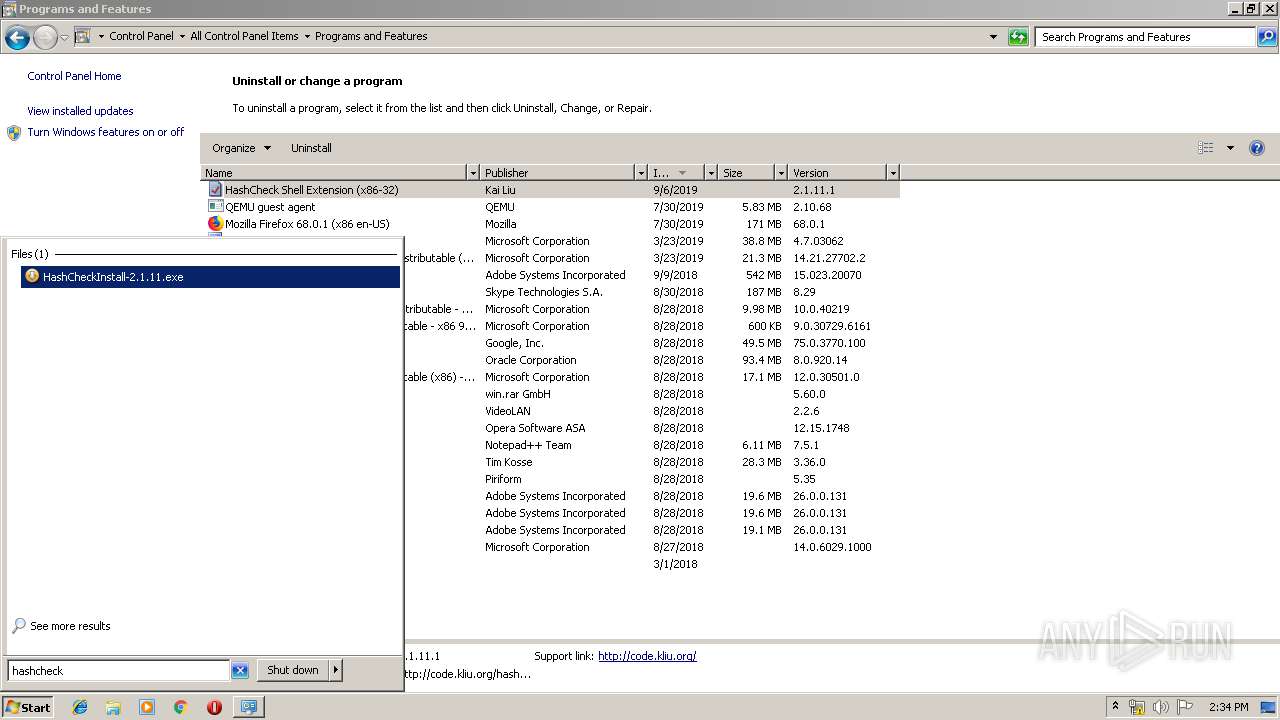
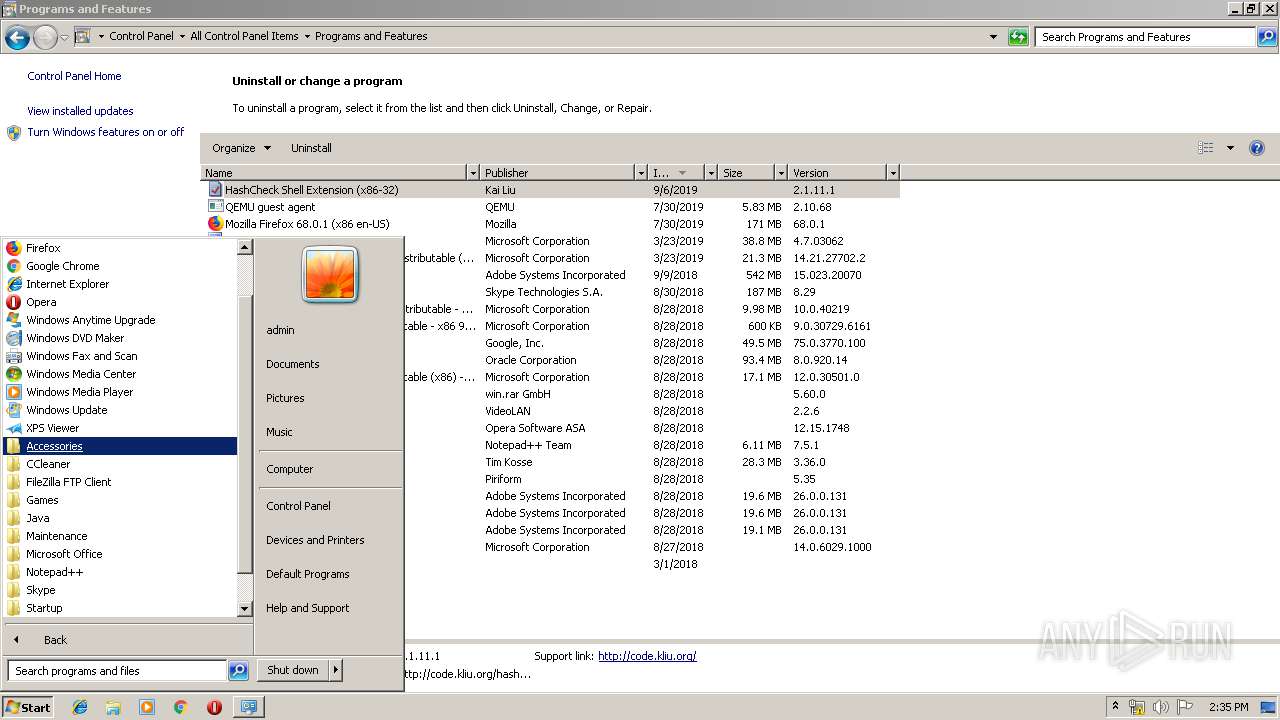
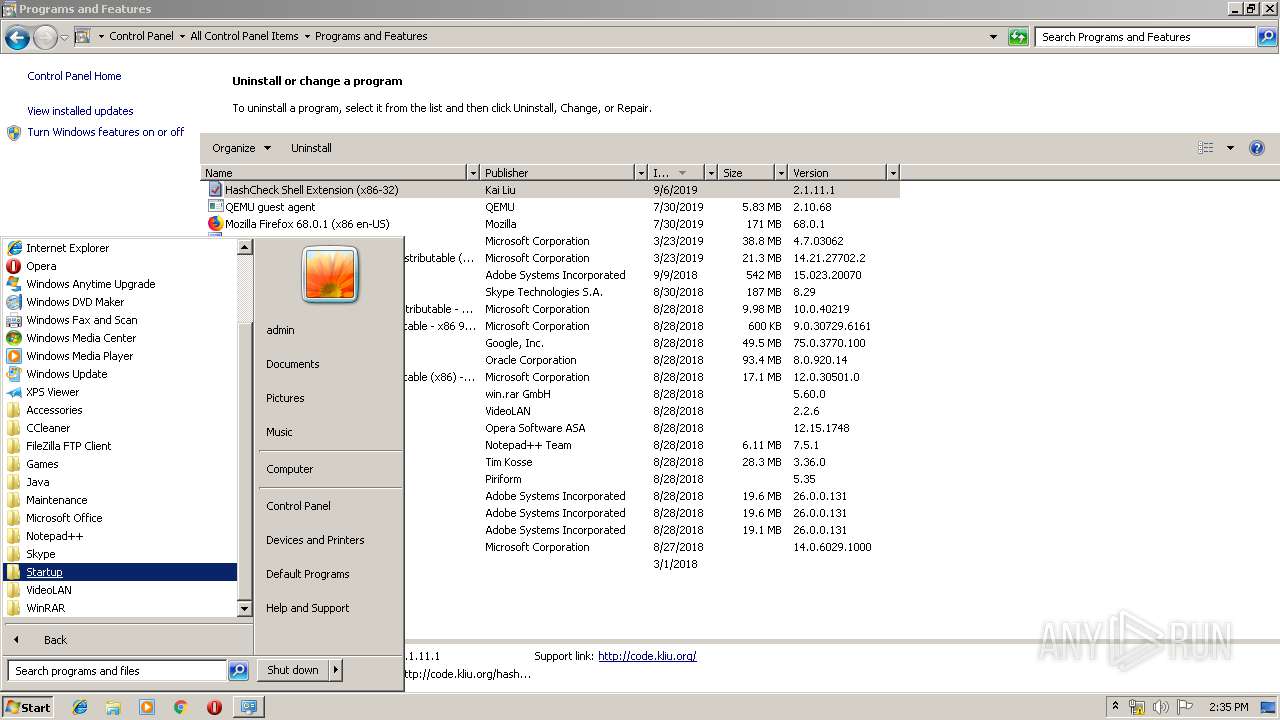
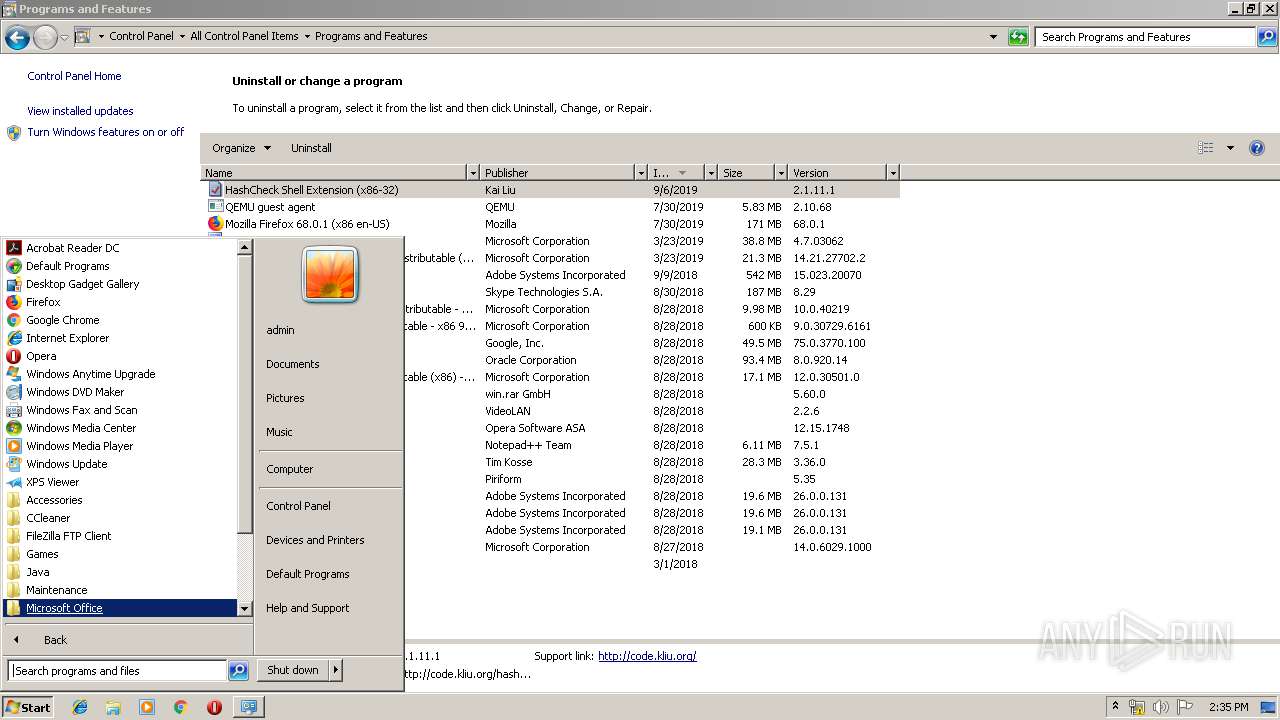
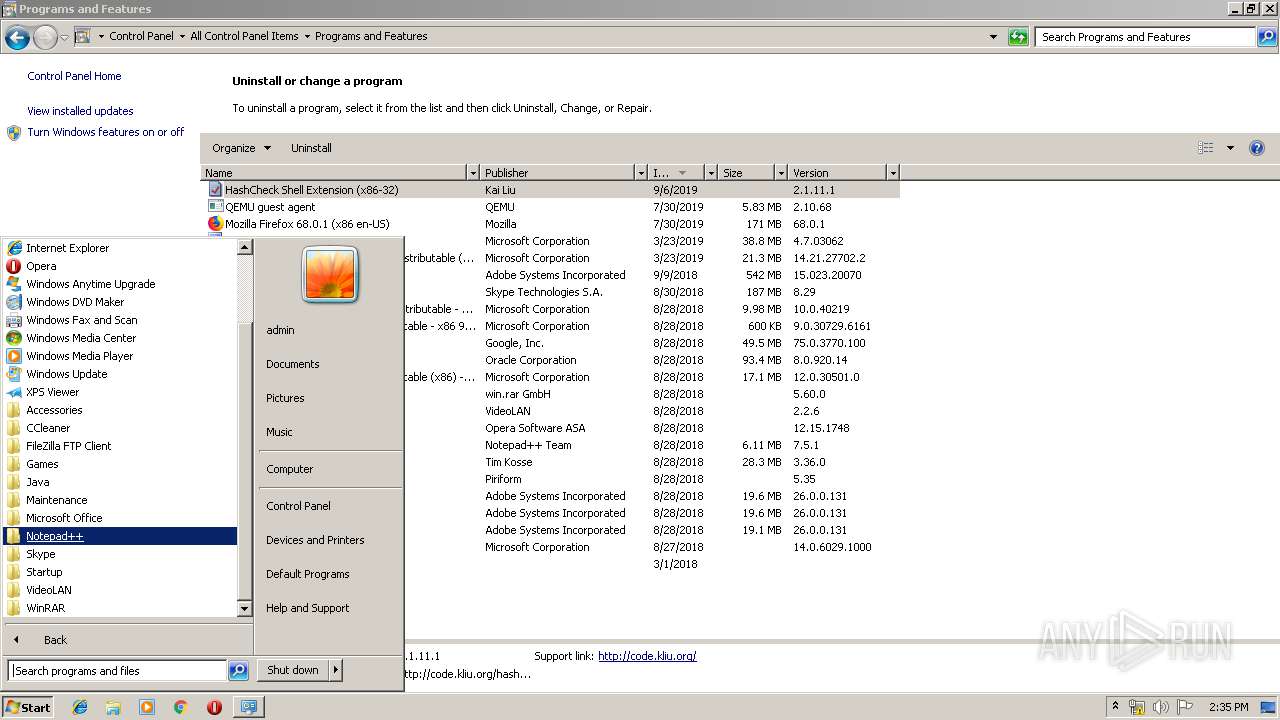
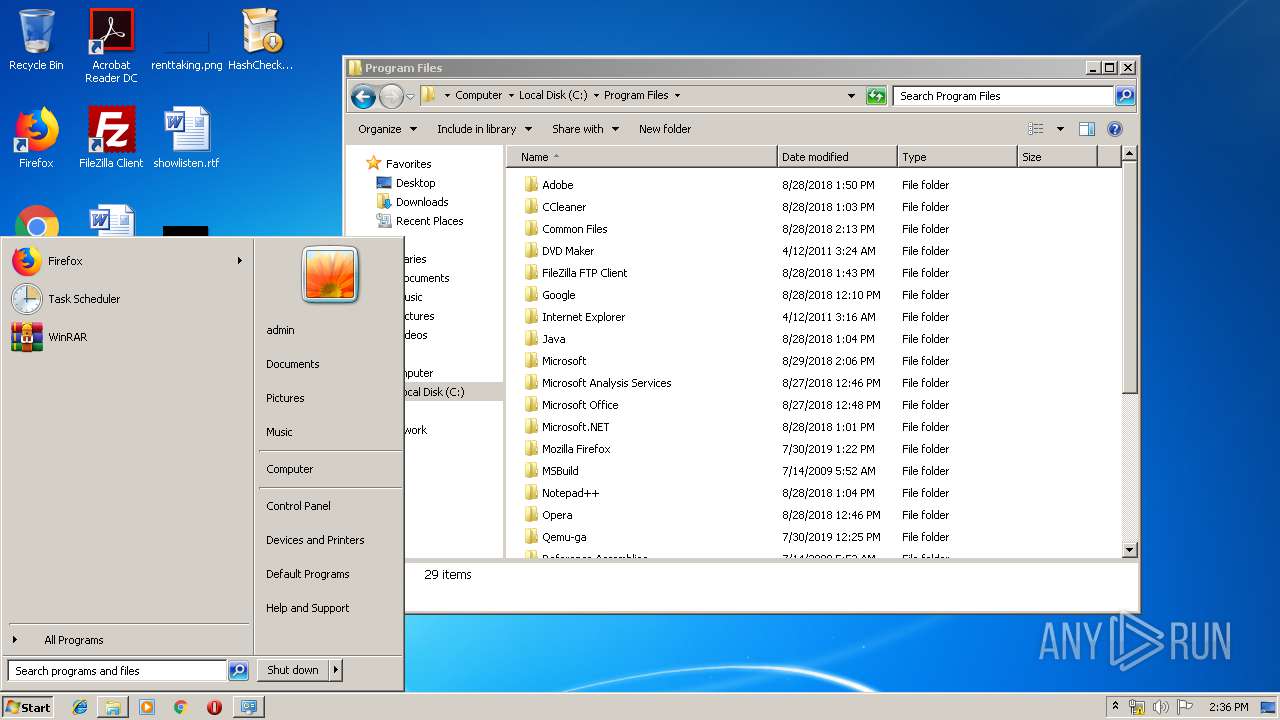
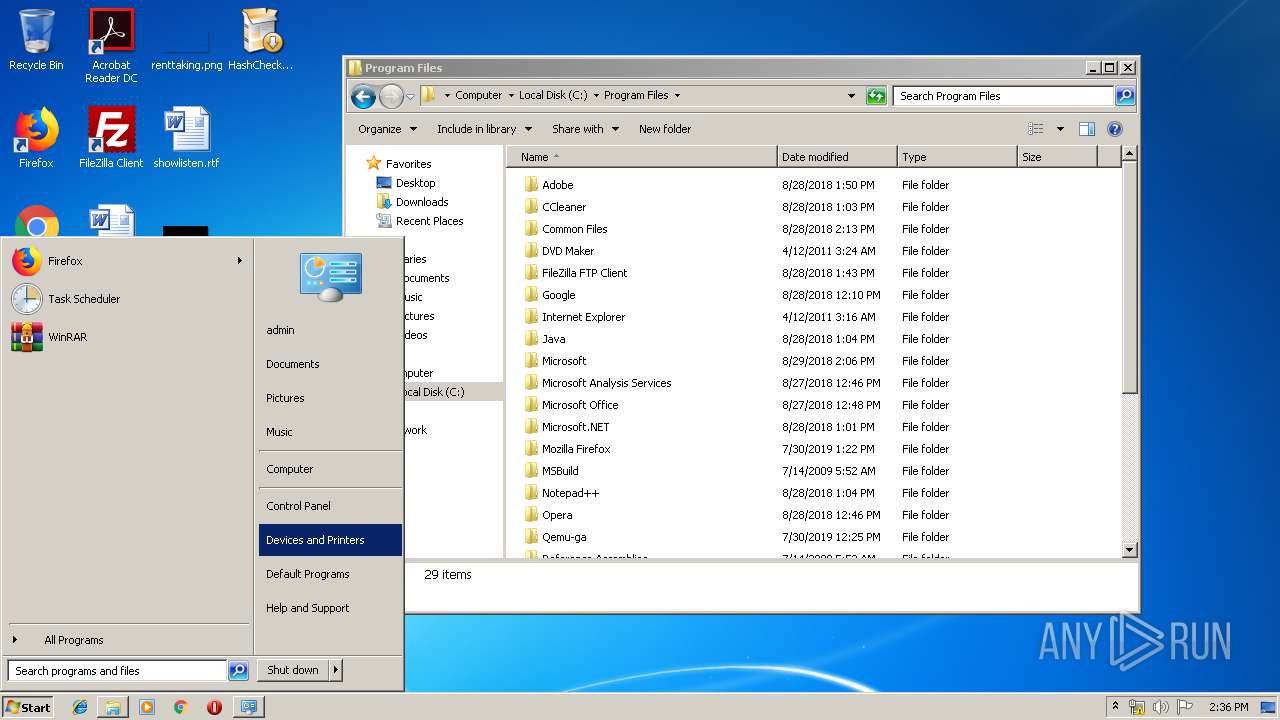
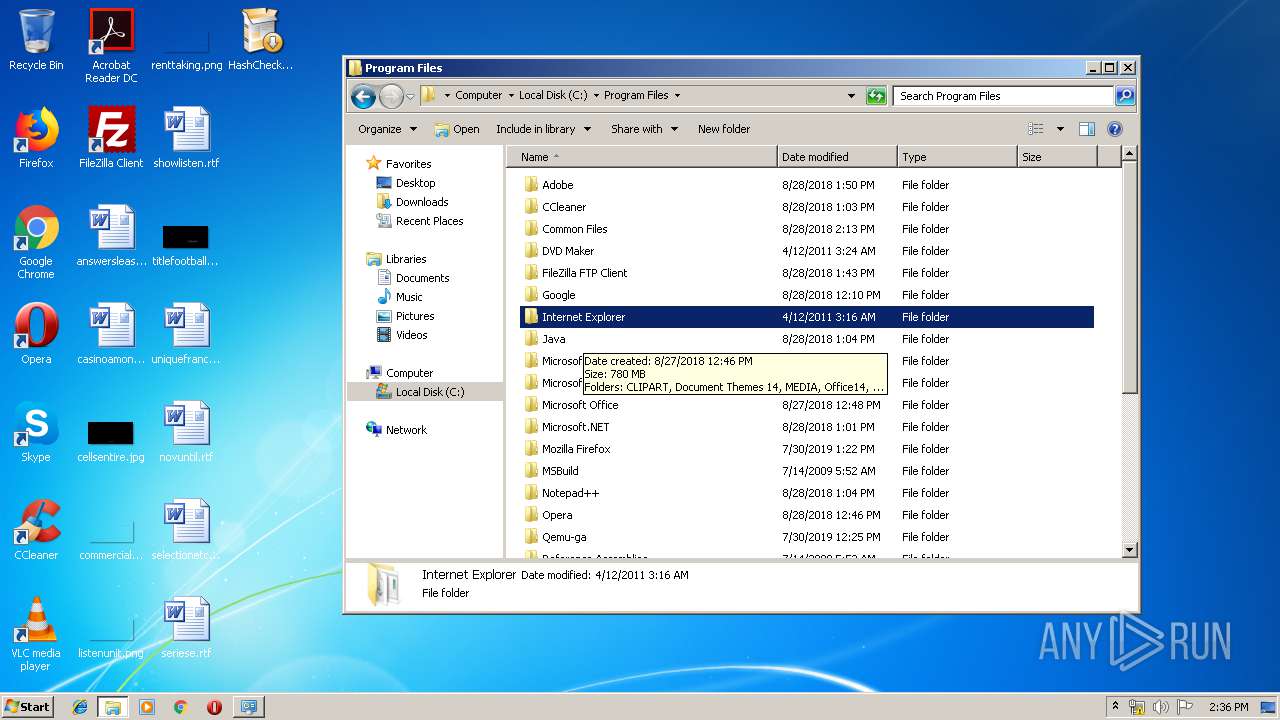
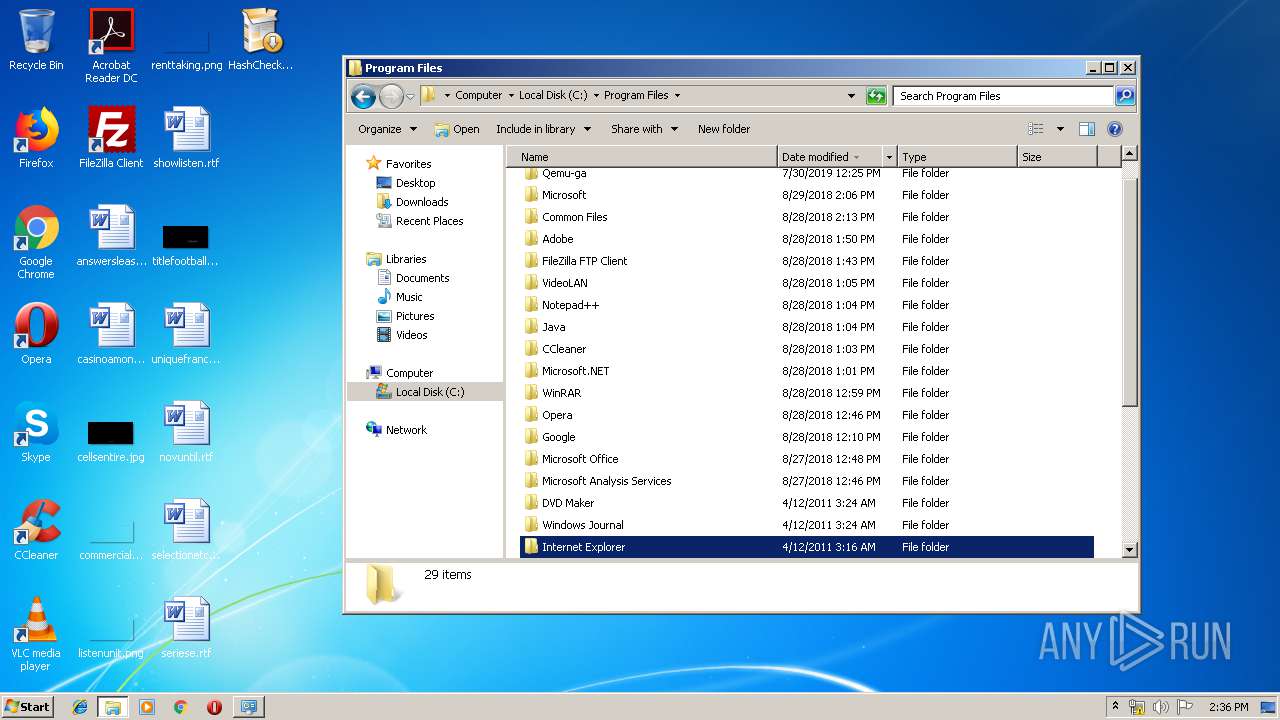
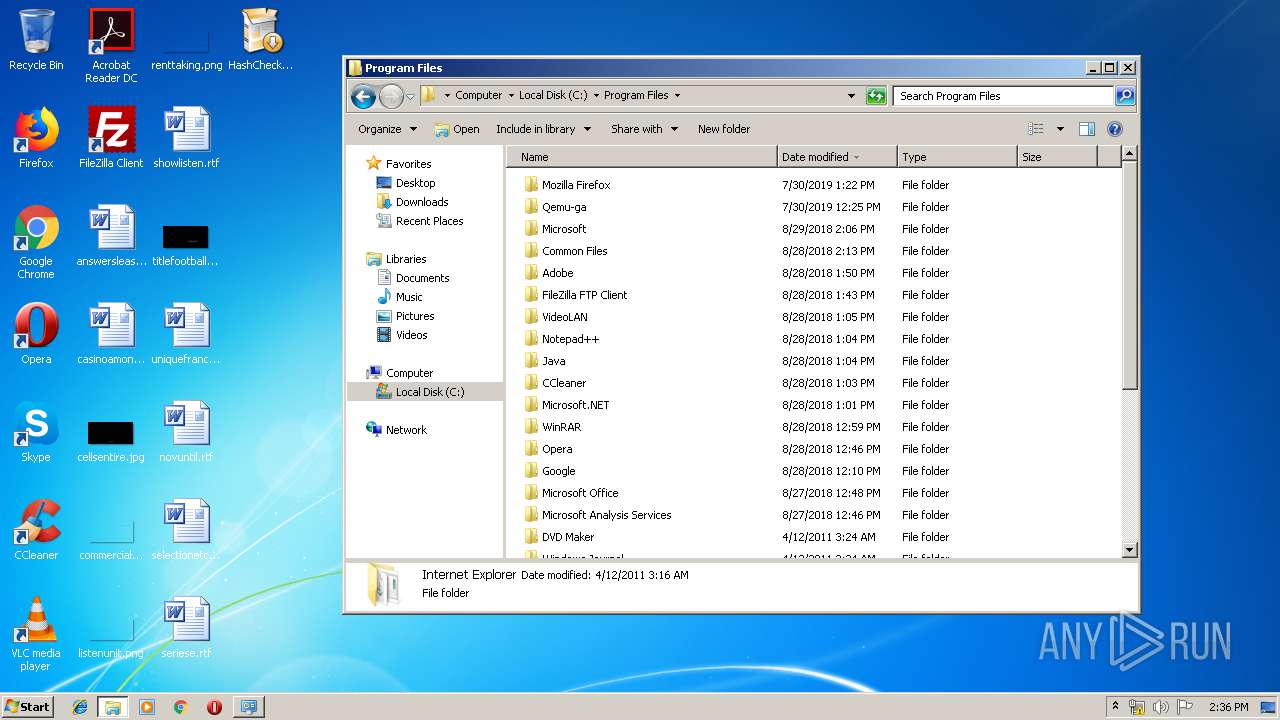
Searches for installed software
- explorer.exe (PID: 276)
INFO
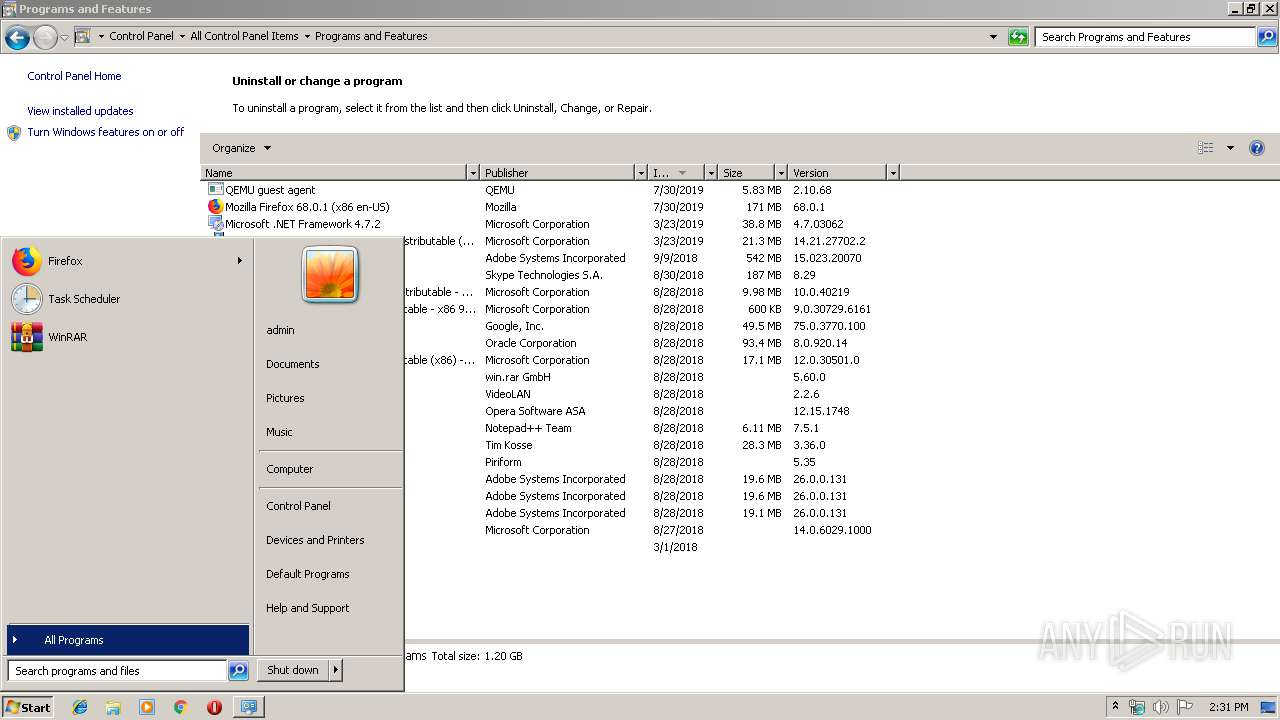
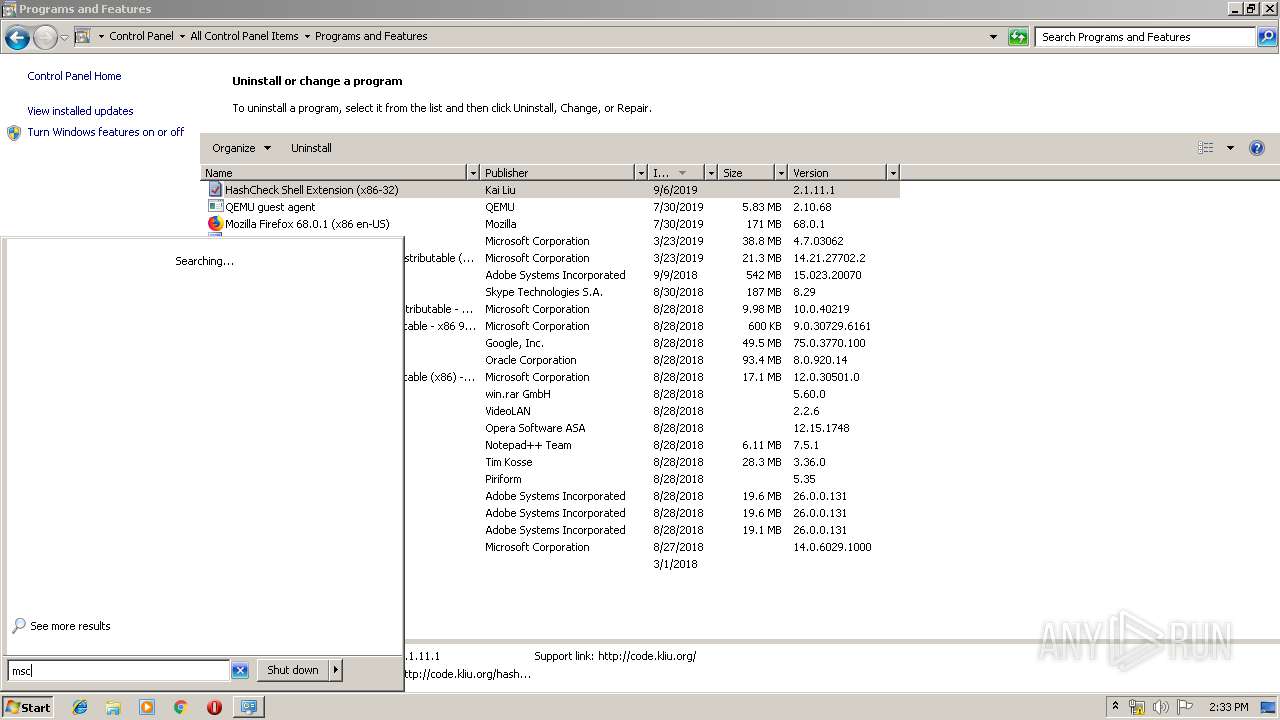
Manual execution by user
- msconfig.exe (PID: 1008)
- msconfig.exe (PID: 2872)
- HashCheckInstall-2.1.11.exe (PID: 2920)
Reads internet explorer settings
- iexplore.exe (PID: 1944)
Reads Internet Cache Settings
- iexplore.exe (PID: 1944)
Application launched itself
- iexplore.exe (PID: 3164)
Changes internet zones settings
- iexplore.exe (PID: 3164)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:07:09 08:13:25+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 4608 |
| InitializedDataSize: | 81408 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x146c |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.1.11.1 |
| ProductVersionNumber: | 2.1.11.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | code.kliu.org |
| FileDescription: | HashCheck Shell Extension Setup |
| FileVersion: | 2.1.11.1 |
| LegalCopyright: | Copyright © Kai Liu. All rights reserved. |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 09-Jul-2009 06:13:25 |
| Detected languages: |
|
| CompanyName: | code.kliu.org |
| FileDescription: | HashCheck Shell Extension Setup |
| FileVersion: | 2.1.11.1 |
| LegalCopyright: | Copyright © Kai Liu. All rights reserved. |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000098 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 2 |
| Time date stamp: | 09-Jul-2009 06:13:25 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000010A6 | 0x00001200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.51803 |
.rsrc | 0x00003000 | 0x00013C18 | 0x00013E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.47512 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.29975 | 887 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.74963 | 744 | UNKNOWN | English - United States | RT_ICON |
3 | 3.01957 | 296 | UNKNOWN | English - United States | RT_ICON |
4 | 4.84061 | 3752 | UNKNOWN | English - United States | RT_ICON |
5 | 6.16608 | 2216 | UNKNOWN | English - United States | RT_ICON |
6 | 5.42186 | 1384 | UNKNOWN | English - United States | RT_ICON |
7 | 5.39336 | 9640 | UNKNOWN | English - United States | RT_ICON |
8 | 5.62872 | 4264 | UNKNOWN | English - United States | RT_ICON |
9 | 5.59672 | 1128 | UNKNOWN | English - United States | RT_ICON |
100 | 2.89097 | 132 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
ADVPACK.dll |
COMCTL32.dll |
Cabinet.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
msvcrt.dll |
Total processes
55
Monitored processes
11
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 276 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1008 | "C:\Windows\system32\msconfig.exe" | C:\Windows\system32\msconfig.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: System Configuration Utility Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1264 | "C:\Windows\system32\msconfig.exe" | C:\Windows\system32\msconfig.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: System Configuration Utility Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1944 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3164 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2452 | "C:\Windows\system32\msconfig.exe" | C:\Windows\system32\msconfig.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: System Configuration Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2516 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2872 | "C:\Windows\system32\msconfig.exe" | C:\Windows\system32\msconfig.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: System Configuration Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2920 | "C:\Users\admin\Desktop\HashCheckInstall-2.1.11.exe" | C:\Users\admin\Desktop\HashCheckInstall-2.1.11.exe | — | explorer.exe | |||||||||||
User: admin Company: code.kliu.org Integrity Level: MEDIUM Description: HashCheck Shell Extension Setup Exit code: 0 Version: 2.1.11.1 Modules
| |||||||||||||||
| 3164 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3476 | "C:\Users\admin\Desktop\HashCheckInstall-2.1.11.exe" /uac | C:\Users\admin\Desktop\HashCheckInstall-2.1.11.exe | HashCheckInstall-2.1.11.exe | ||||||||||||
User: admin Company: code.kliu.org Integrity Level: HIGH Description: HashCheck Shell Extension Setup Exit code: 0 Version: 2.1.11.1 Modules
| |||||||||||||||
Total events
10 925
Read events
8 290
Write events
2 630
Delete events
5
Modification events
| (PID) Process: | (276) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | P:\Hfref\nqzva\Qrfxgbc\UnfuPurpxVafgnyy-2.1.11.rkr |
Value: 00000000000000000000000000000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (276) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000001C0000002500000093800C00090000000D000000CC19050033003000380030003400360042003000410046003400410033003900430042000000460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E006500780065000000740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C0049006E007400650072006E006500740020004500780070006C006F007200650072005C0051007500690063006B0020004C00610075006E00630068005C0055007300650072002000500069006E006E006500000000000034FF01F832FF01D4E3E1013DA94A7600000000FBFFFF7FF8E3E101987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000534275066D42750653427506000000000000000000000000080000002E006C00E72F0A77A48EF37600000000AC032E0000002E00E72F0A77B08EF37603005B019604010000002E005B148D23020000006CE4E101B07F0A7744E5E1010000000058005A0044E5E1010200000010E5E101F2700A7791830A771C8FF37611000000B8453100B045310078192F00F8FD580600E500008F148D23B0E4E10182914A7600E5E101B4E4E10127954A7600000000CC90FF01DCE4E101CD944A76CC90FF0188E5E101408CFF01E1944A7600000000408CFF0188E5E101E4E4E101090000000D000000CC19050033003000380030003400360042003000410046003400410033003900430042000000460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E006500780065000000740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C0049006E007400650072006E006500740020004500780070006C006F007200650072005C0051007500690063006B0020004C00610075006E00630068005C0055007300650072002000500069006E006E006500000000000034FF01F832FF01D4E3E1013DA94A7600000000FBFFFF7FF8E3E101987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000534275066D42750653427506000000000000000000000000080000002E006C00E72F0A77A48EF37600000000AC032E0000002E00E72F0A77B08EF37603005B019604010000002E005B148D23020000006CE4E101B07F0A7744E5E1010000000058005A0044E5E1010200000010E5E101F2700A7791830A771C8FF37611000000B8453100B045310078192F00F8FD580600E500008F148D23B0E4E10182914A7600E5E101B4E4E10127954A7600000000CC90FF01DCE4E101CD944A76CC90FF0188E5E101408CFF01E1944A7600000000408CFF0188E5E101E4E4E101090000000D000000CC19050033003000380030003400360042003000410046003400410033003900430042000000460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E006500780065000000740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C0049006E007400650072006E006500740020004500780070006C006F007200650072005C0051007500690063006B0020004C00610075006E00630068005C0055007300650072002000500069006E006E006500000000000034FF01F832FF01D4E3E1013DA94A7600000000FBFFFF7FF8E3E101987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000534275066D42750653427506000000000000000000000000080000002E006C00E72F0A77A48EF37600000000AC032E0000002E00E72F0A77B08EF37603005B019604010000002E005B148D23020000006CE4E101B07F0A7744E5E1010000000058005A0044E5E1010200000010E5E101F2700A7791830A771C8FF37611000000B8453100B045310078192F00F8FD580600E500008F148D23B0E4E10182914A7600E5E101B4E4E10127954A7600000000CC90FF01DCE4E101CD944A76CC90FF0188E5E101408CFF01E1944A7600000000408CFF0188E5E101E4E4E101 | |||
| (PID) Process: | (276) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (276) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ApplicationDestinations |
| Operation: | write | Name: | MaxEntries |
Value: 15 | |||
| (PID) Process: | (276) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (276) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0000000001000000070000000200000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (276) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\0 |
| Operation: | write | Name: | MRUListEx |
Value: 020000000300000004000000050000000100000000000000FFFFFFFF | |||
| (PID) Process: | (276) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Toolbar |
| Operation: | write | Name: | Locked |
Value: 1 | |||
| (PID) Process: | (276) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\Shell |
| Operation: | write | Name: | NavBar |
Value: 000000000000000000000000000000008B000000870000003153505305D5CDD59C2E1B10939708002B2CF9AE6B0000005A000000007B00360044003800420042003300440033002D0039004400380037002D0034004100390031002D0041004200350036002D003400460033003000430046004600450046004500390046007D005F0057006900640074006800000013000000F00000000000000000000000 | |||
| (PID) Process: | (276) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\RecentDocs\Folder |
| Operation: | delete value | Name: | 1 |
Value: 500072006F006700720061006D0073000000620032000000000000000000000050726F6772616D732E6C6E6B0000460008000400EFBE00000000000000002A00000000000000000000000000000000000000000000000000500072006F006700720061006D0073002E006C006E006B0000001C000000 | |||
Executable files
3
Suspicious files
0
Text files
6
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3164 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3164 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3164 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF53FAF968C69A0806.TMP | — | |
MD5:— | SHA256:— | |||
| 3164 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\RecoveryStore.{352E35A1-D0AB-11E9-B86F-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 3164 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFB1103E037F42DE4D.TMP | — | |
MD5:— | SHA256:— | |||
| 3164 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{28EC9EFD-D0AB-11E9-B86F-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 3164 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF5B64C5375F0EFB1E.TMP | — | |
MD5:— | SHA256:— | |||
| 3164 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{28EC9EFC-D0AB-11E9-B86F-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 276 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\7e4dca80246863e3.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
| 276 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\Programs.lnk | lnk | |
MD5:5E3C82FC1D3D767ED8270187949C3AC2 | SHA256:6E477D50D7D8228DB7F07C330DCB8B0F2D62896DEEF69EDBC9B03703F8BDDC24 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3164 | iexplore.exe | GET | 200 | 13.107.21.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3164 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |