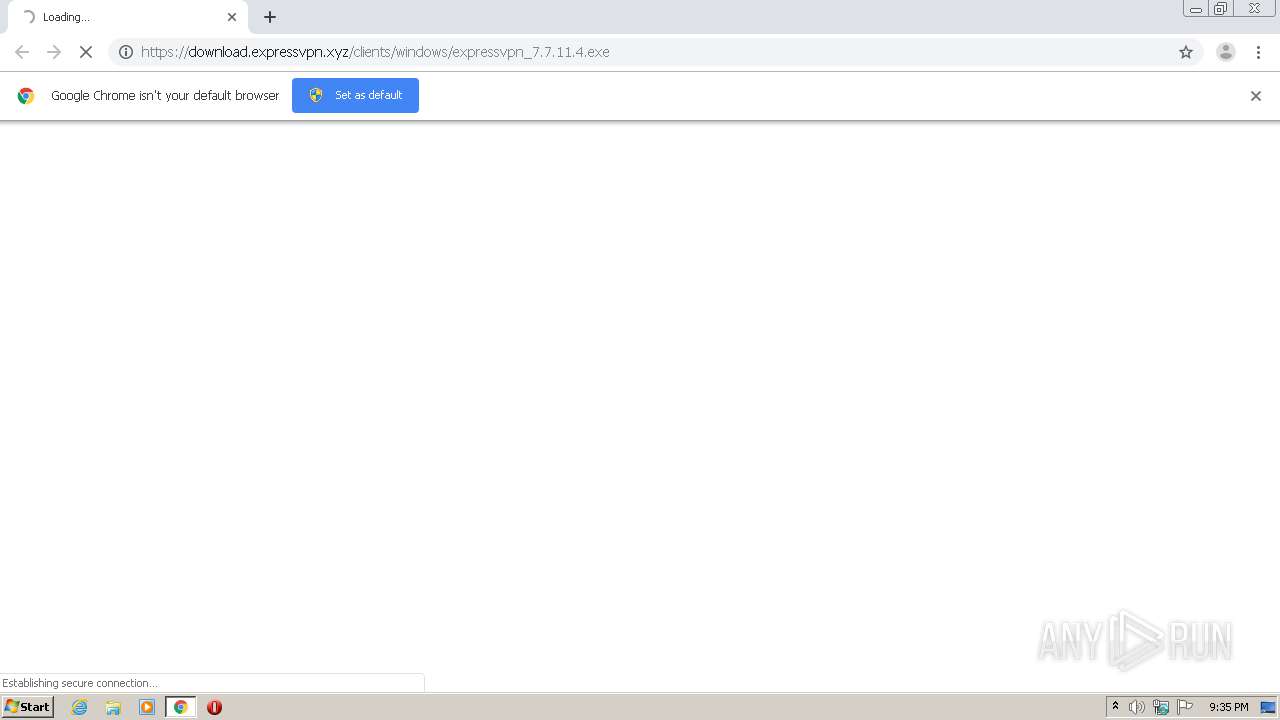
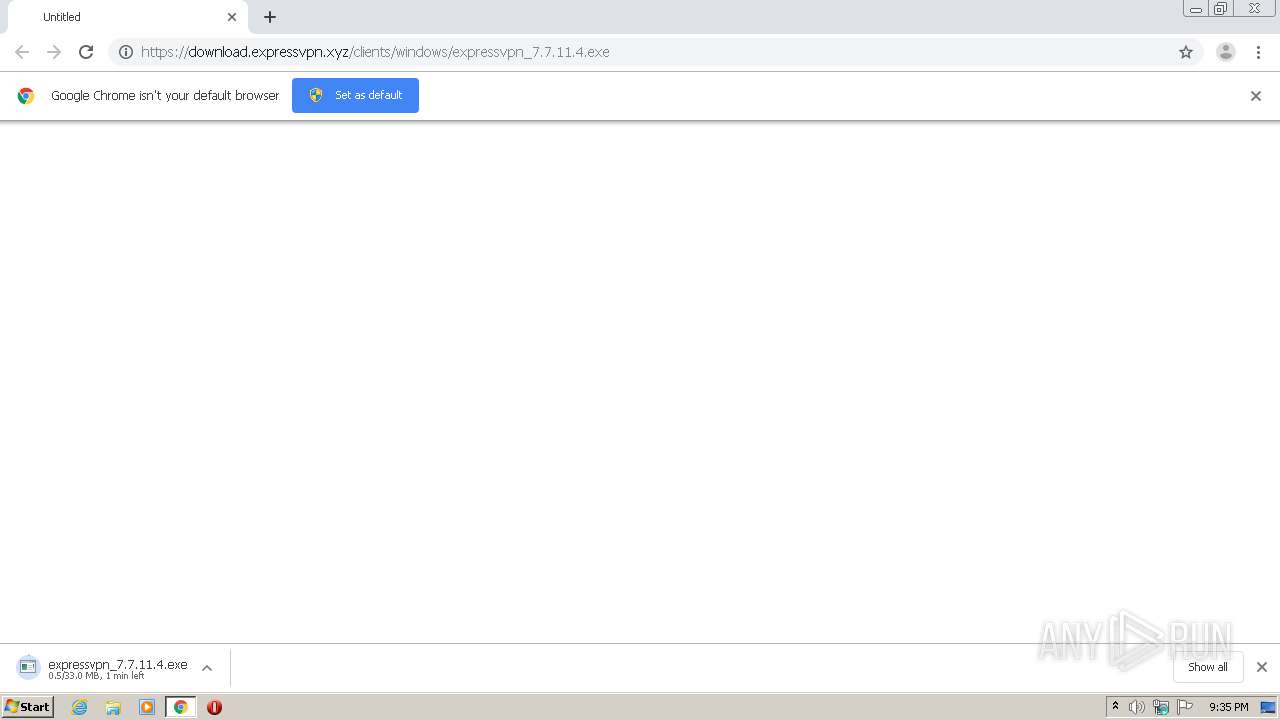
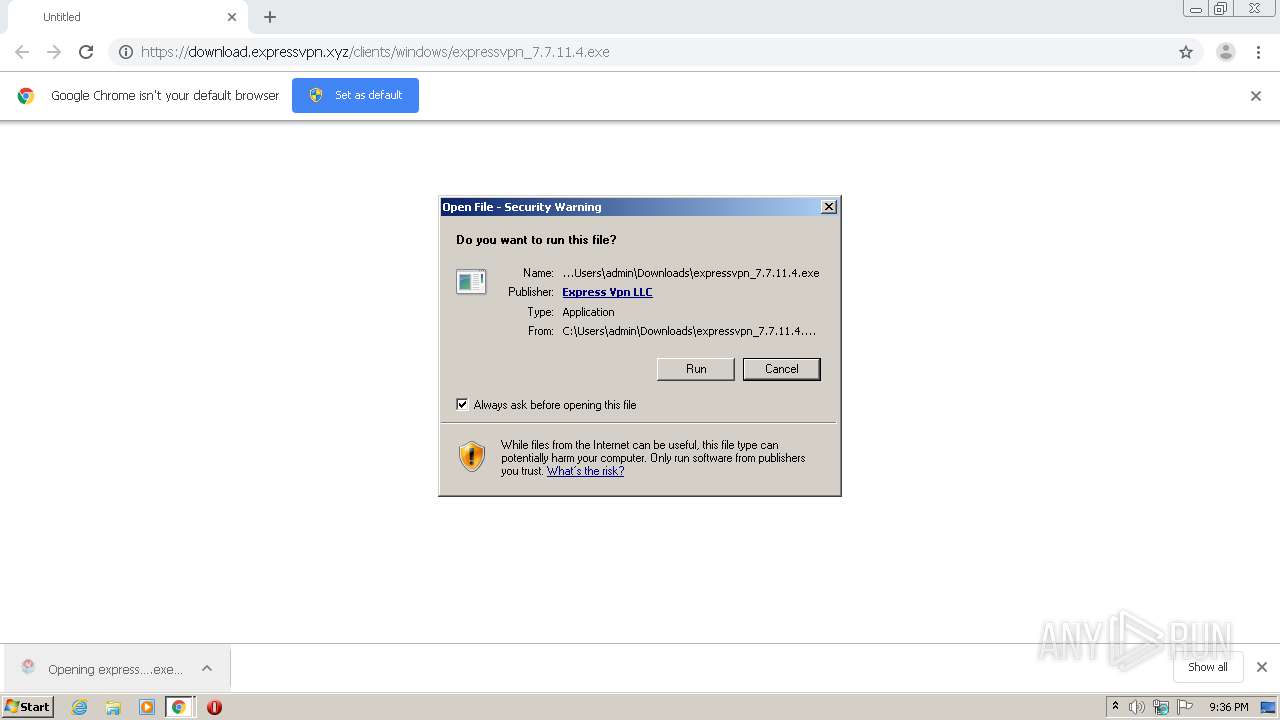
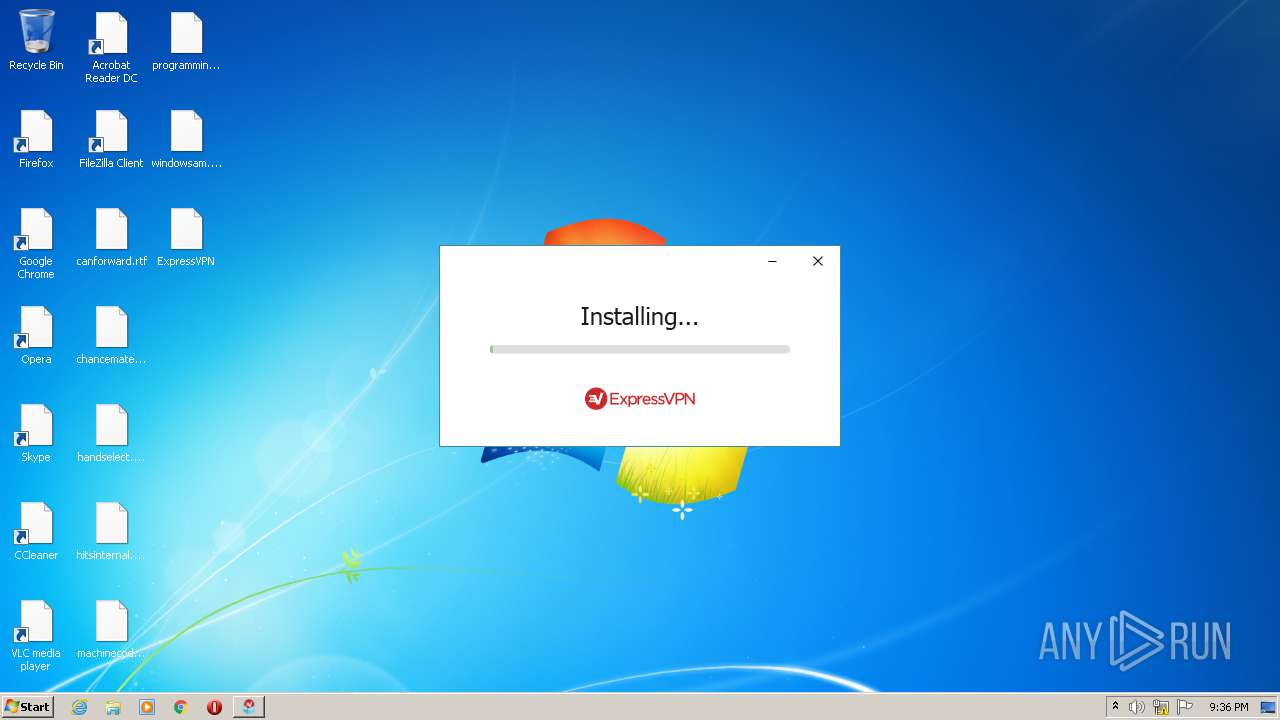
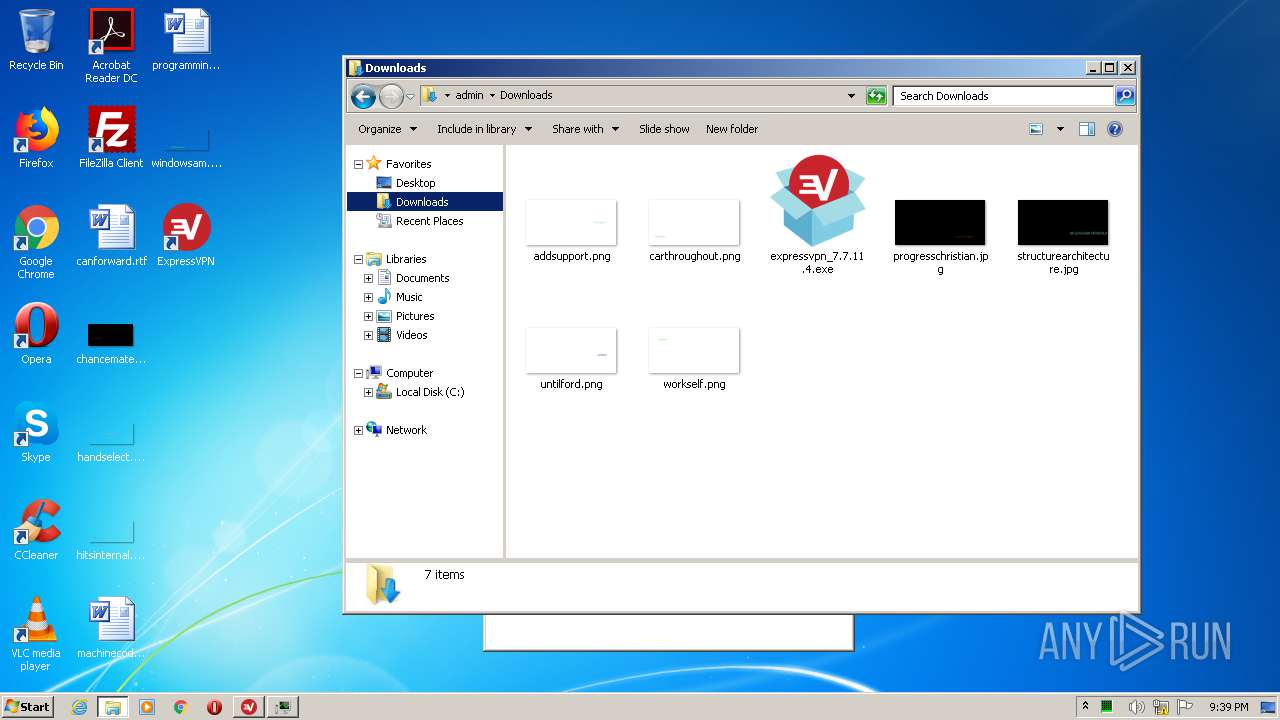
| URL: | https://download.expressvpn.xyz/clients/windows/expressvpn_7.7.11.4.exe |
| Full analysis: | https://app.any.run/tasks/fca14caa-2612-466a-9d0d-16b28874db34 |
| Verdict: | Malicious activity |
| Analysis date: | July 04, 2020, 20:35:21 |
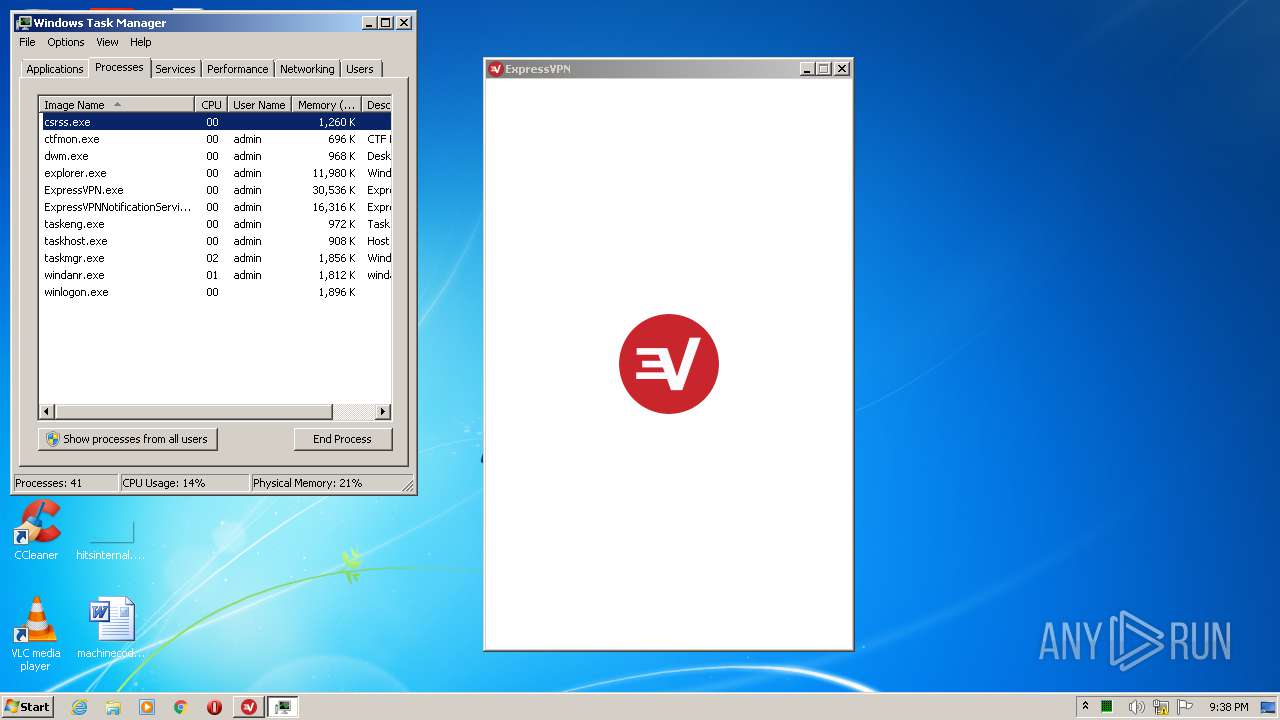
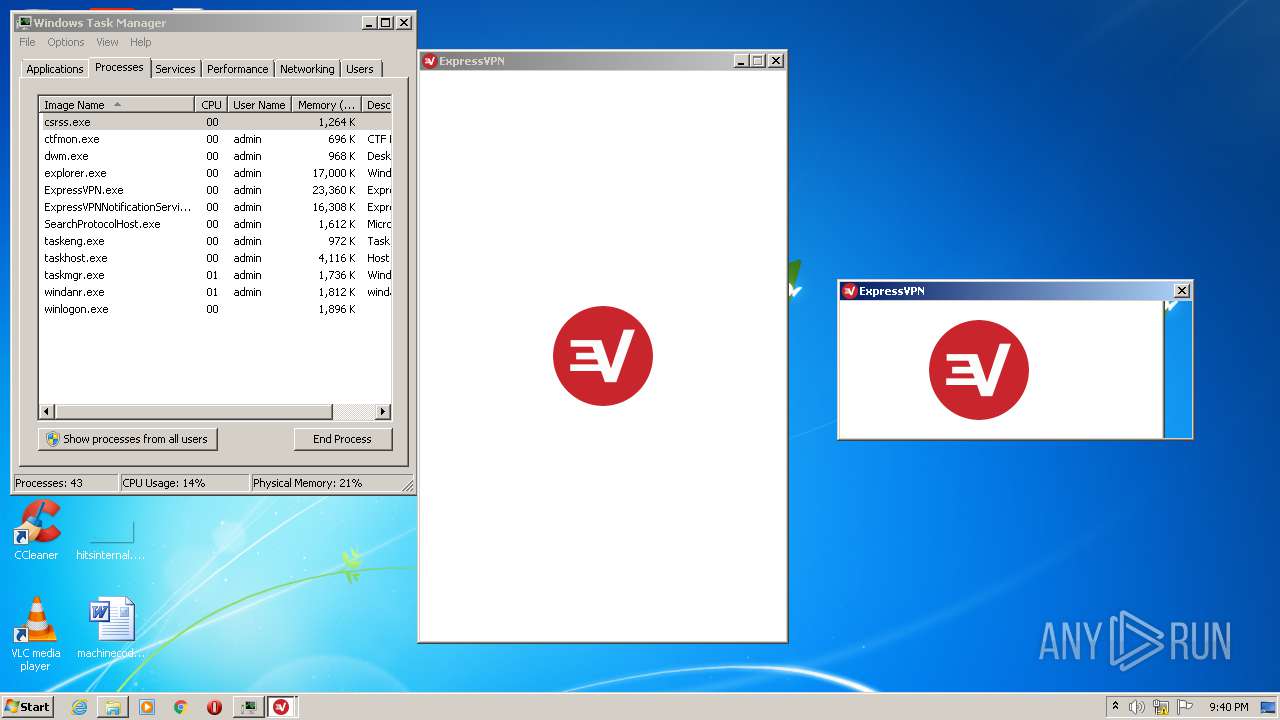
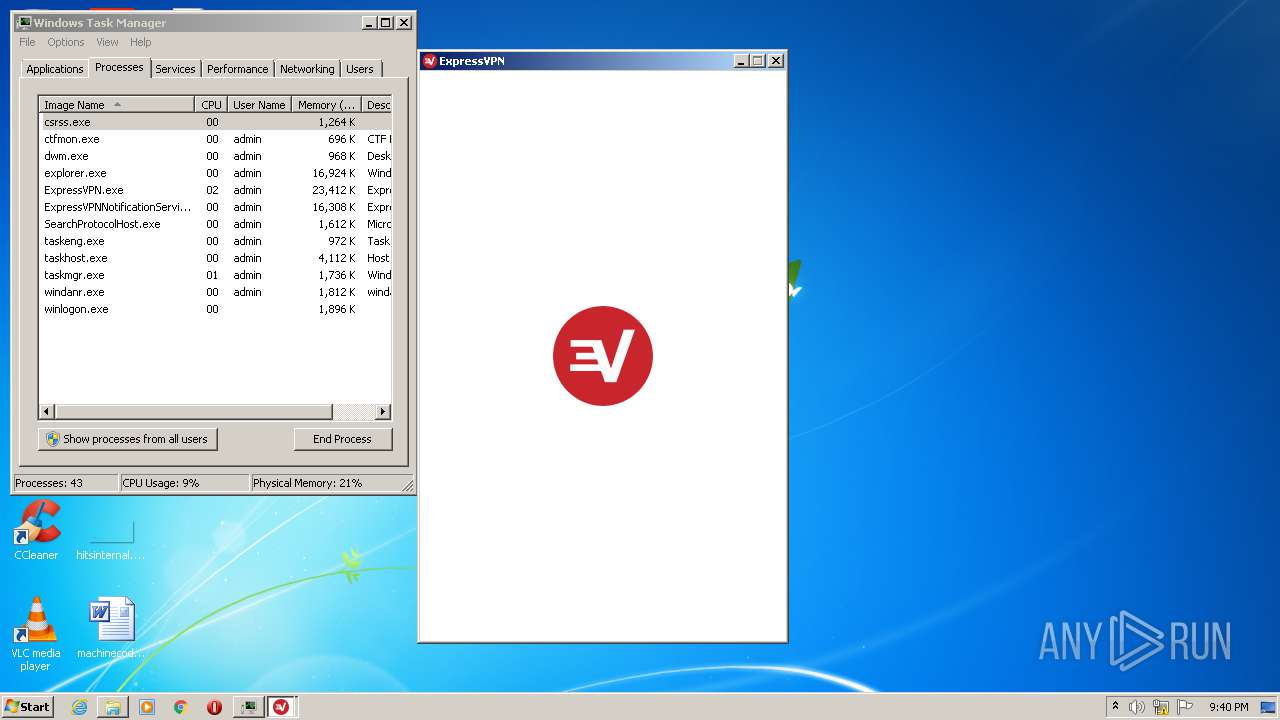
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 95ECADC67C3F1E78B04F9119A095D9DC |
| SHA1: | D1BA49B2651B642B072EB5D54F1F80526AB921D7 |
| SHA256: | B6A41226A29C42C6AAB8CE3155621F54A21F1057E6053E472CF79E56BDE4374C |
| SSDEEP: | 3:N8SElYXzMmDL/AVgfOfgUmC:2SKYXzMmDL/AV4g |
MALICIOUS
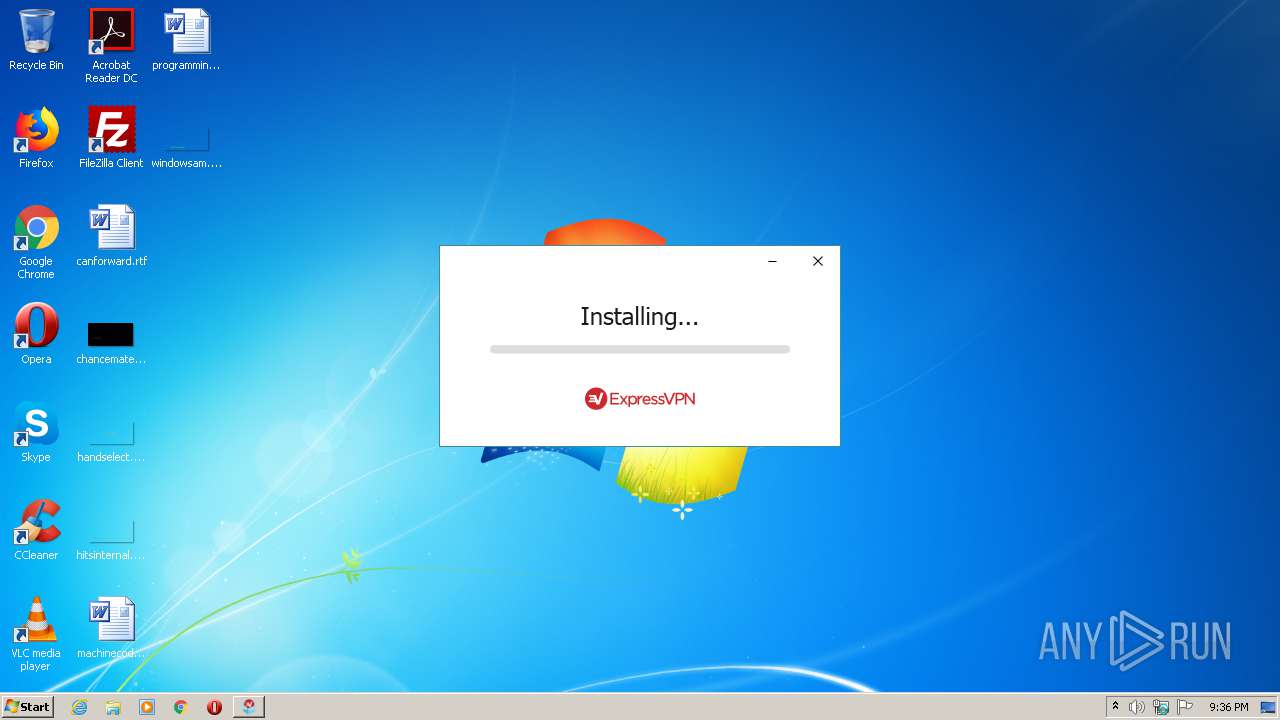
Application was dropped or rewritten from another process
- expressvpn_7.7.11.4.exe (PID: 3052)
- expressvpn_7.7.11.4.exe (PID: 980)
- ExpressVPN_7.7.11.4.exe (PID: 1952)
- ExpressVPNNotificationService.exe (PID: 2604)
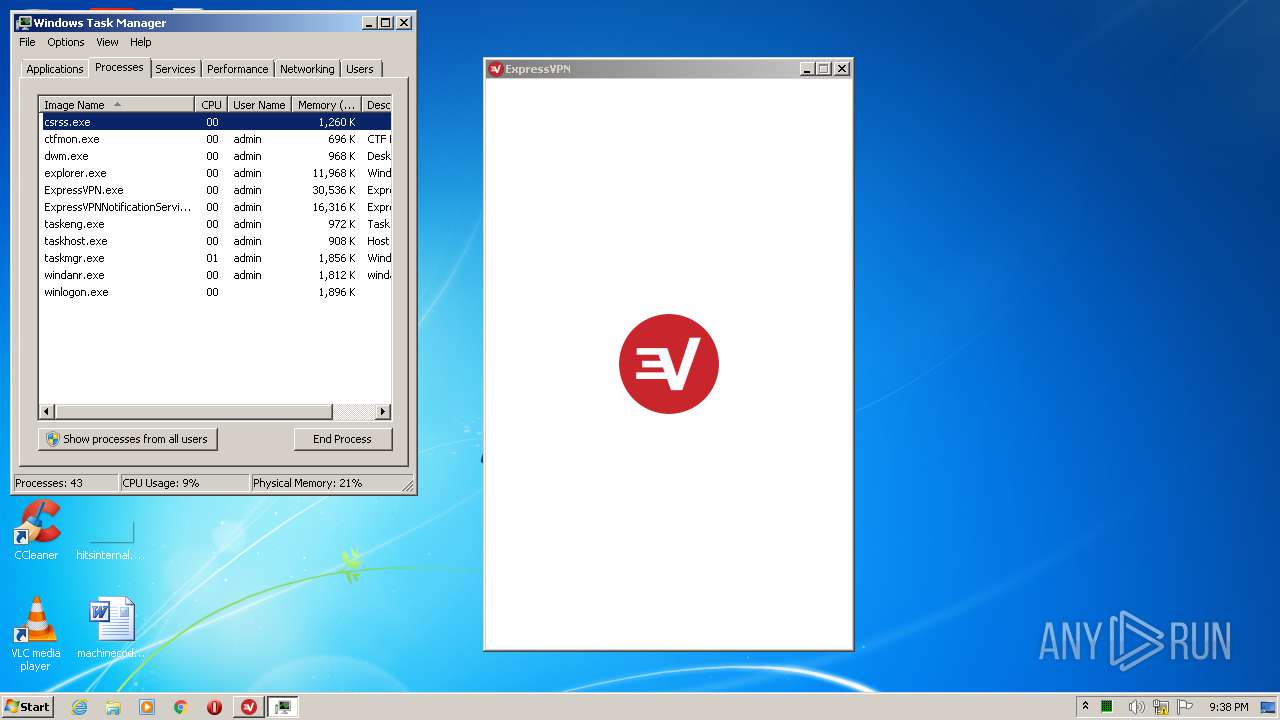
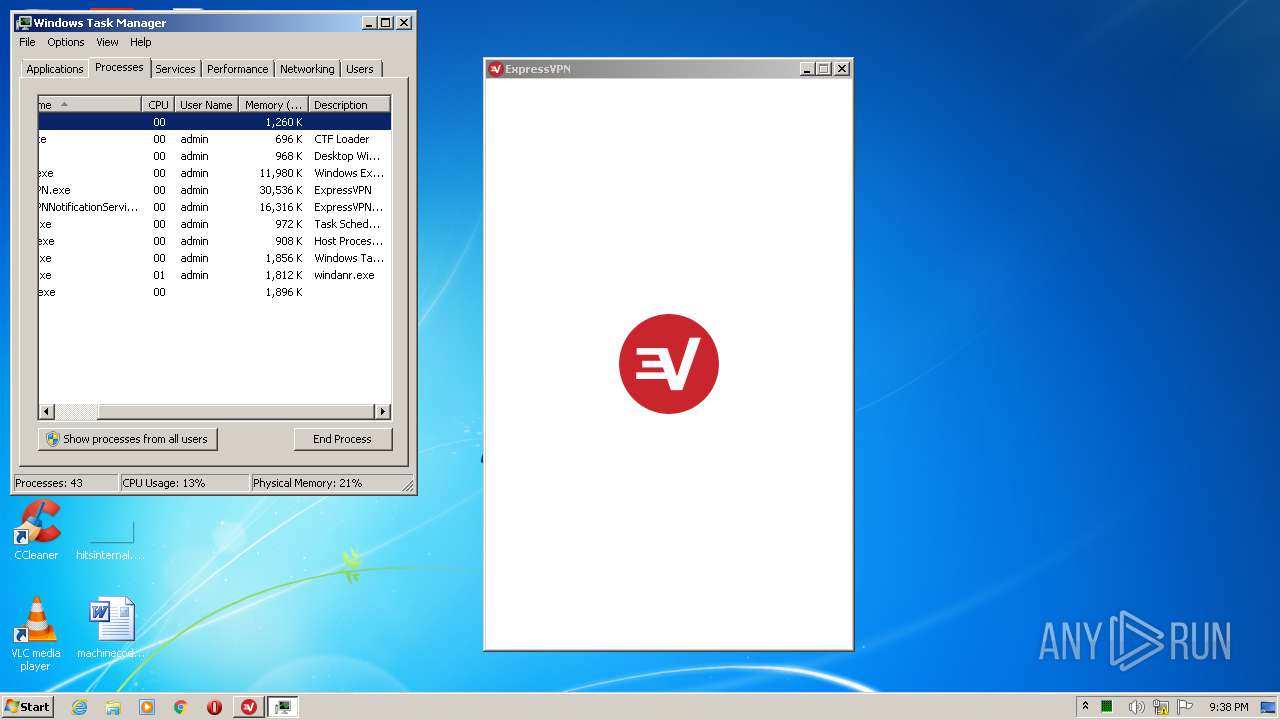
- ExpressVPN.exe (PID: 3568)
- XvUtil.exe (PID: 3396)
- ExpressVPN-Installer.exe (PID: 3304)
- tapinstall.exe (PID: 3288)
- nssm.exe (PID: 2416)
- nssm.exe (PID: 1652)
- nssm.exe (PID: 1780)
- nssm.exe (PID: 3812)
- nssm.exe (PID: 2836)
- XvUtil.exe (PID: 2588)
- nssm.exe (PID: 3196)
- expressvpnd.exe (PID: 1456)
- XvUtil.exe (PID: 3604)
- ExpressVPN.exe (PID: 668)
Loads dropped or rewritten executable
- expressvpn_7.7.11.4.exe (PID: 980)
- rundll32.exe (PID: 532)
- rundll32.exe (PID: 2856)
- rundll32.exe (PID: 2780)
- rundll32.exe (PID: 1020)
- ExpressVPNNotificationService.exe (PID: 2604)
- rundll32.exe (PID: 1576)
- rundll32.exe (PID: 2476)
- ExpressVPN.exe (PID: 3568)
- XvUtil.exe (PID: 3396)
- ExpressVPN-Installer.exe (PID: 3304)
- expressvpnd.exe (PID: 1456)
- XvUtil.exe (PID: 2588)
- XvUtil.exe (PID: 3604)
- ExpressVPN.exe (PID: 668)
Changes the autorun value in the registry
- ExpressVPN_7.7.11.4.exe (PID: 1952)
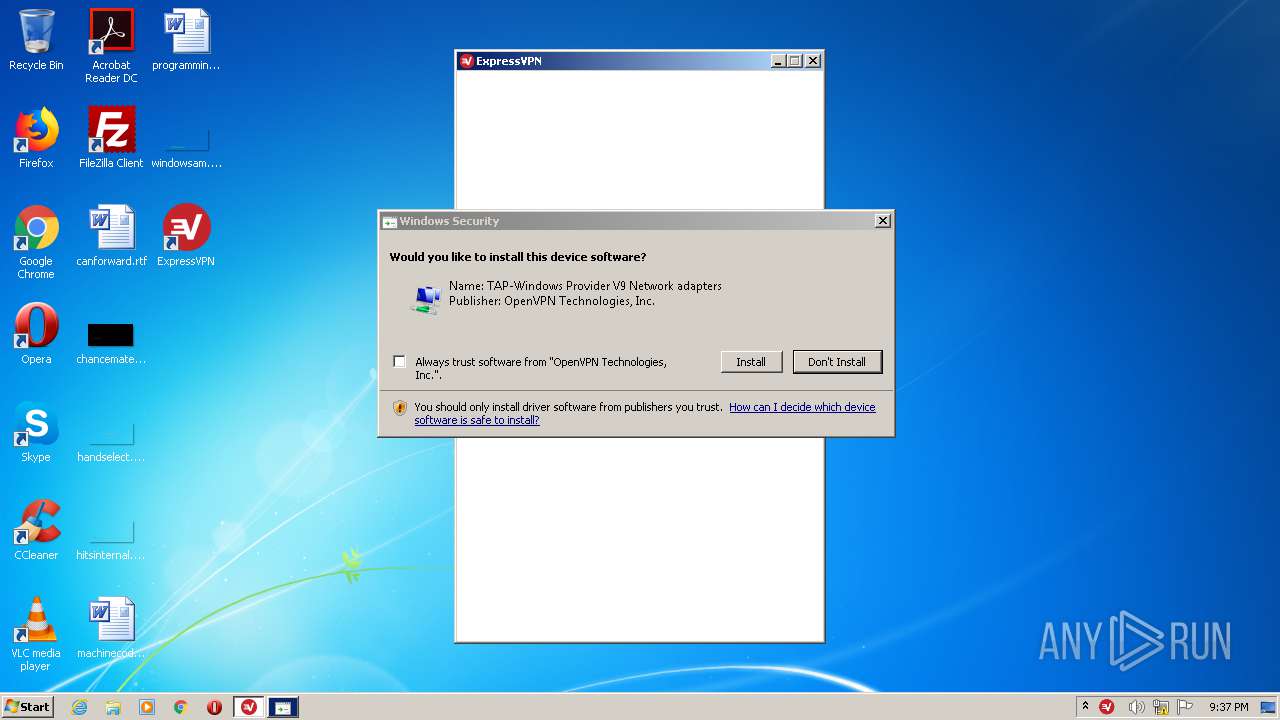
Changes settings of System certificates
- tapinstall.exe (PID: 3288)
- msiexec.exe (PID: 3608)
Starts NET.EXE for service management
- ExpressVPN-Installer.exe (PID: 3304)
- expressvpnd.exe (PID: 1456)
SUSPICIOUS
Creates a software uninstall entry
- ExpressVPN_7.7.11.4.exe (PID: 1952)
Executable content was dropped or overwritten
- chrome.exe (PID: 184)
- expressvpn_7.7.11.4.exe (PID: 3052)
- expressvpn_7.7.11.4.exe (PID: 980)
- msiexec.exe (PID: 3608)
- ExpressVPN_7.7.11.4.exe (PID: 1952)
- rundll32.exe (PID: 1576)
- rundll32.exe (PID: 2476)
- tapinstall.exe (PID: 3288)
- DrvInst.exe (PID: 2312)
- DrvInst.exe (PID: 2352)
Starts itself from another location
- expressvpn_7.7.11.4.exe (PID: 980)
Executed as Windows Service
- vssvc.exe (PID: 3960)
- nssm.exe (PID: 1652)
Uses RUNDLL32.EXE to load library
- MsiExec.exe (PID: 1008)
- MsiExec.exe (PID: 2204)
- DrvInst.exe (PID: 2312)
Searches for installed software
- ExpressVPN_7.7.11.4.exe (PID: 1952)
Creates files in the program directory
- ExpressVPN_7.7.11.4.exe (PID: 1952)
- rundll32.exe (PID: 2780)
- expressvpnd.exe (PID: 1456)
Reads Environment values
- ExpressVPNNotificationService.exe (PID: 2604)
- ExpressVPN.exe (PID: 3568)
- ExpressVPN.exe (PID: 668)
Changes the autorun value in the registry
- msiexec.exe (PID: 3608)
Modifies the open verb of a shell class
- msiexec.exe (PID: 3608)
Creates files in the user directory
- ExpressVPN.exe (PID: 3568)
- ExpressVPN.exe (PID: 668)
Reads Internet Cache Settings
- ExpressVPN.exe (PID: 3568)
Adds / modifies Windows certificates
- tapinstall.exe (PID: 3288)
- msiexec.exe (PID: 3608)
Creates files in the driver directory
- DrvInst.exe (PID: 2312)
- DrvInst.exe (PID: 2352)
Removes files from Windows directory
- DrvInst.exe (PID: 2312)
- DrvInst.exe (PID: 2352)
Executed via COM
- DrvInst.exe (PID: 2352)
- DrvInst.exe (PID: 2312)
Creates files in the Windows directory
- DrvInst.exe (PID: 2312)
- DrvInst.exe (PID: 2352)
Starts SC.EXE for service management
- expressvpnd.exe (PID: 1456)
Uses NETSH.EXE for network configuration
- XvUtil.exe (PID: 2588)
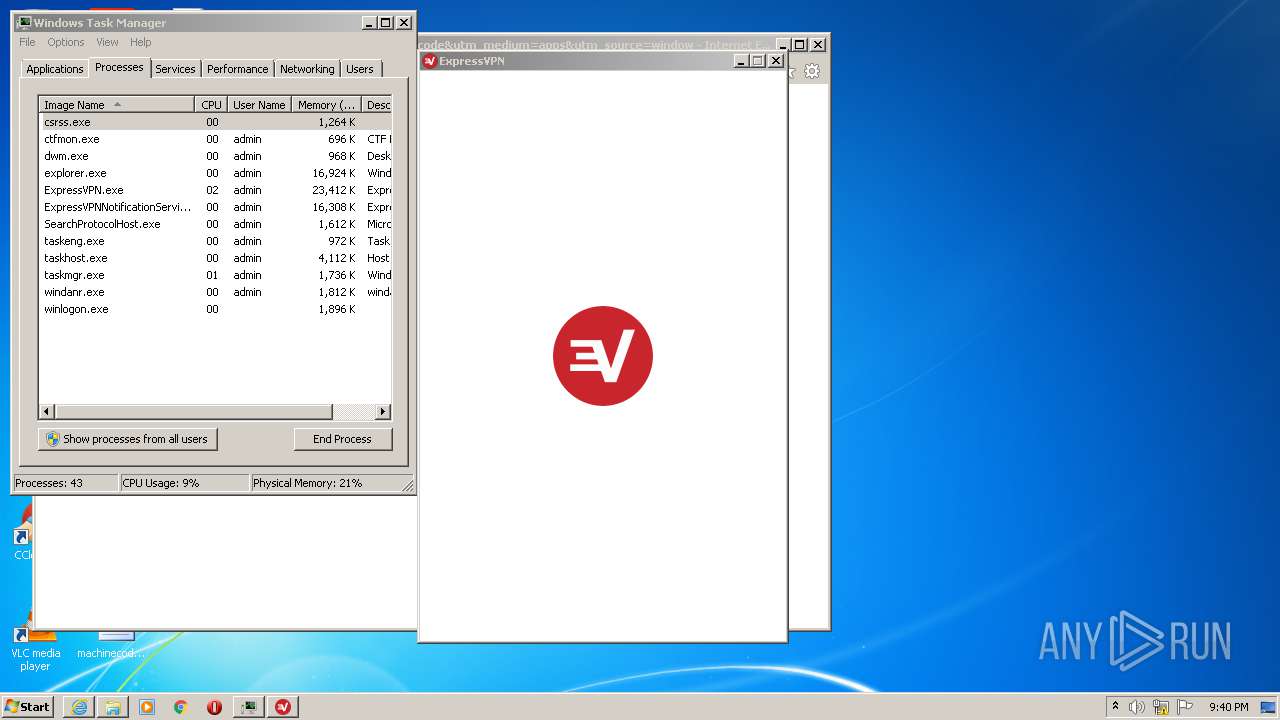
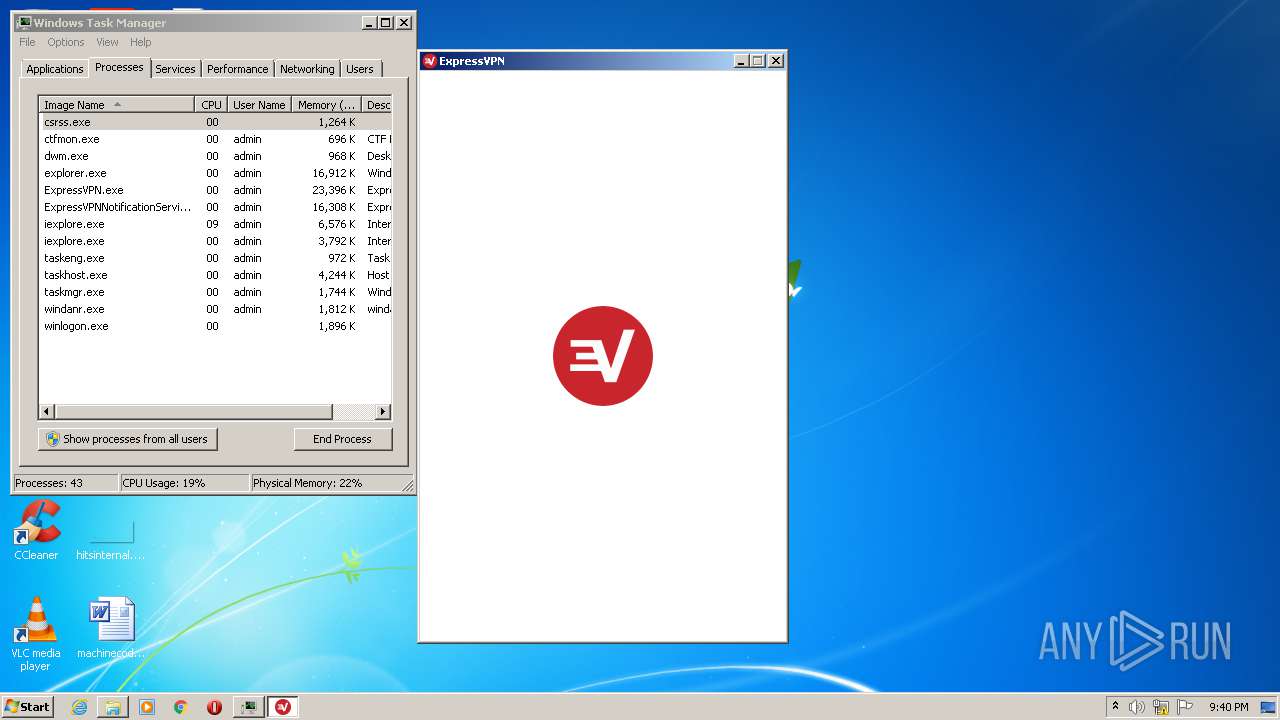
Starts Internet Explorer
- ExpressVPN.exe (PID: 3568)
- ExpressVPN.exe (PID: 668)
INFO
Reads the hosts file
- chrome.exe (PID: 3876)
- chrome.exe (PID: 184)
Reads Internet Cache Settings
- chrome.exe (PID: 184)
- iexplore.exe (PID: 1856)
- iexplore.exe (PID: 2072)
- iexplore.exe (PID: 3072)
- iexplore.exe (PID: 1872)
Application launched itself
- chrome.exe (PID: 184)
- msiexec.exe (PID: 3608)
- iexplore.exe (PID: 1856)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 1008)
- MsiExec.exe (PID: 2204)
Reads settings of System Certificates
- chrome.exe (PID: 3876)
- msiexec.exe (PID: 3608)
- ExpressVPNNotificationService.exe (PID: 2604)
- iexplore.exe (PID: 2072)
- iexplore.exe (PID: 1856)
- iexplore.exe (PID: 1872)
Creates files in the program directory
- msiexec.exe (PID: 3608)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3960)
Creates a software uninstall entry
- msiexec.exe (PID: 3608)
Searches for installed software
- DrvInst.exe (PID: 2312)
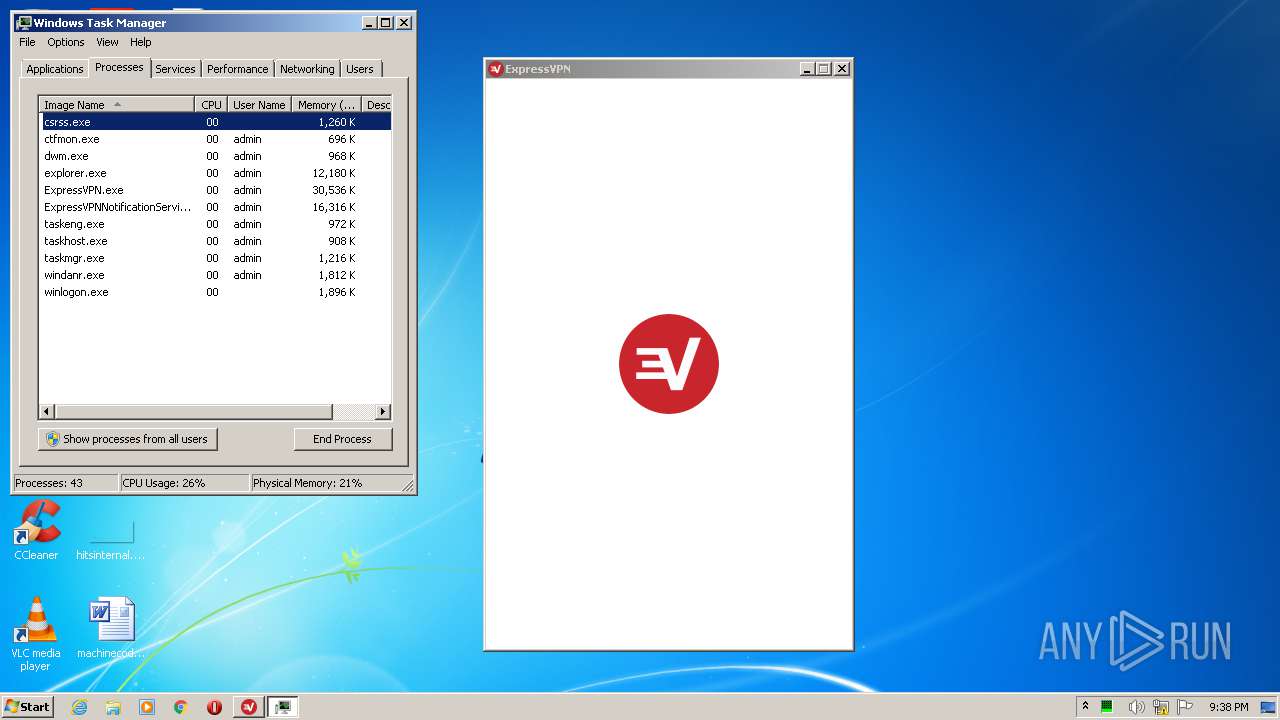
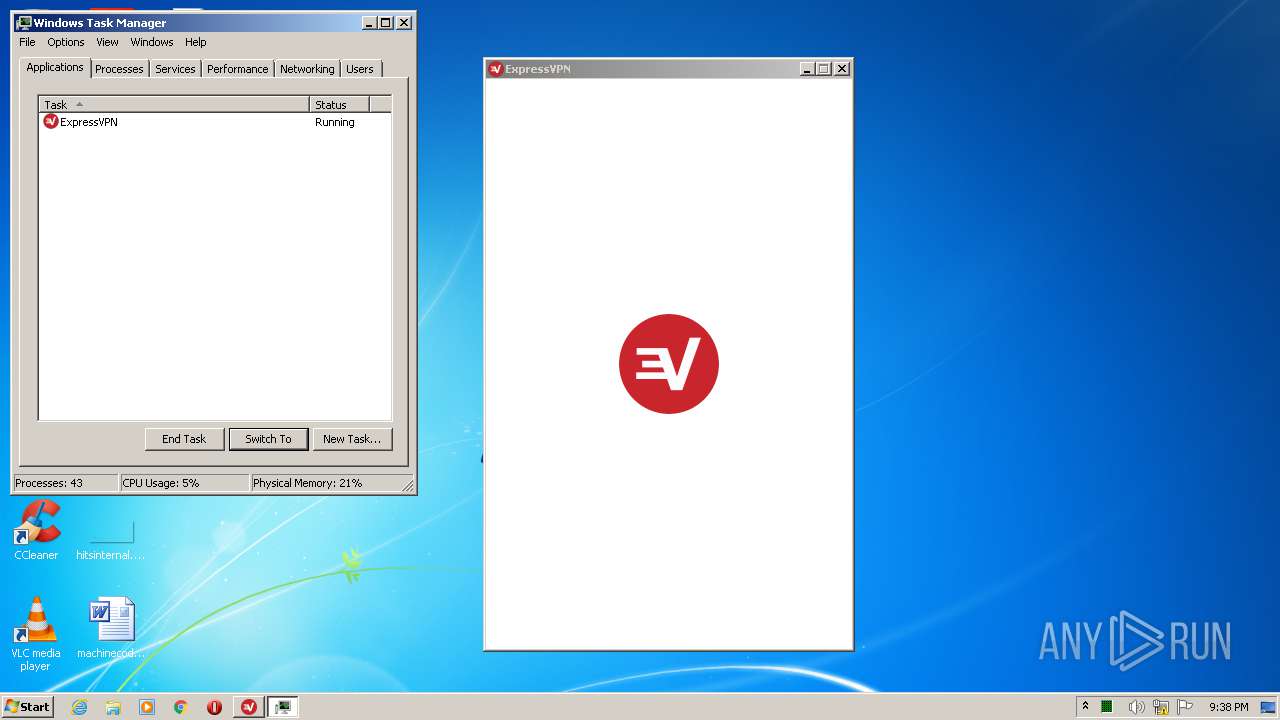
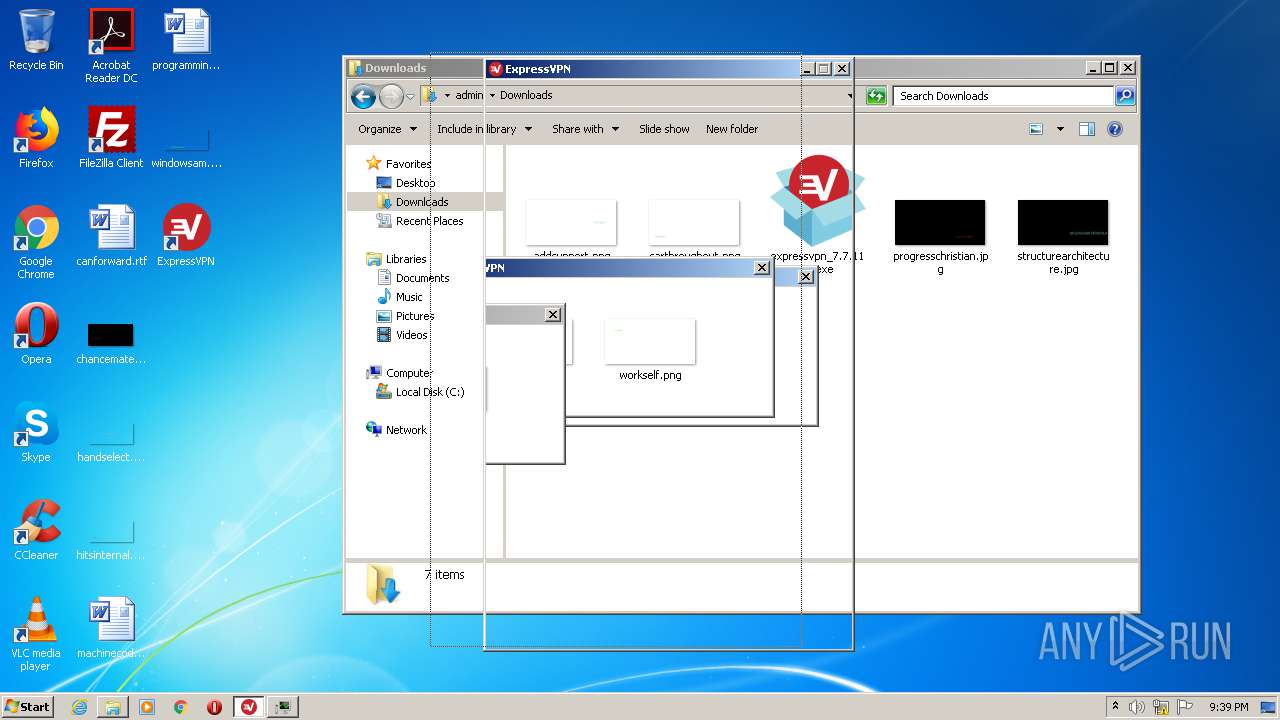
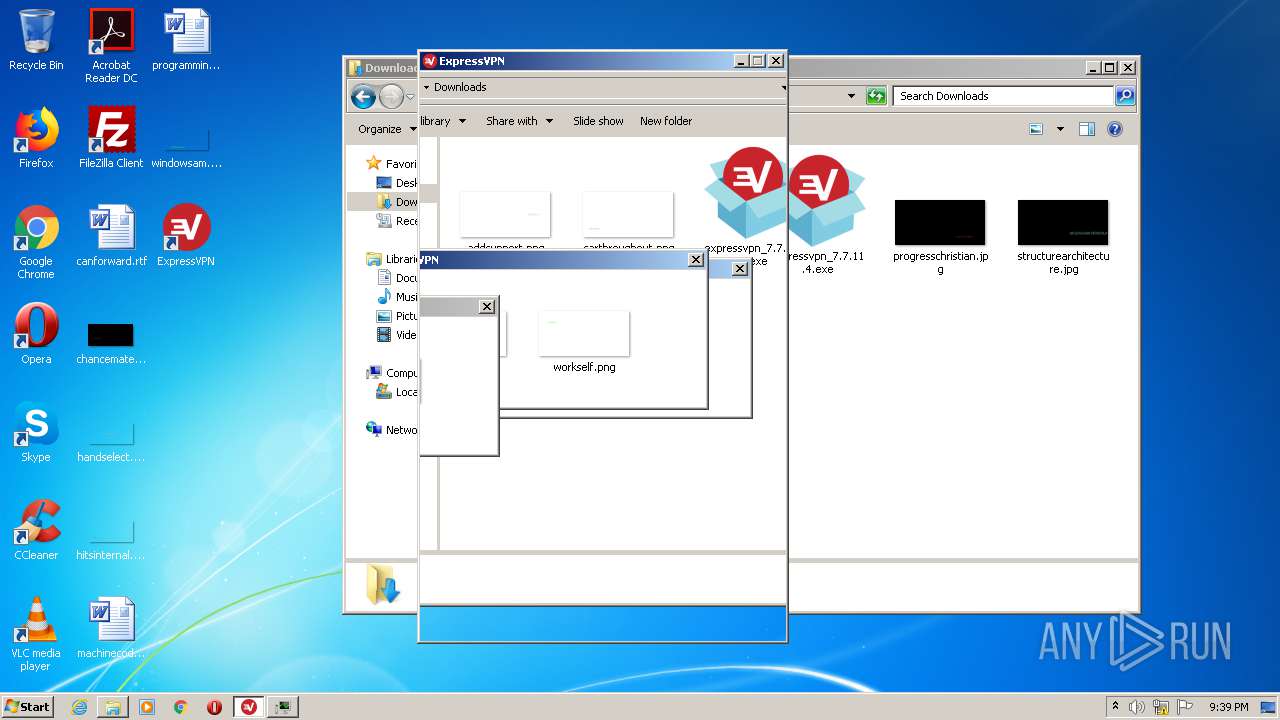
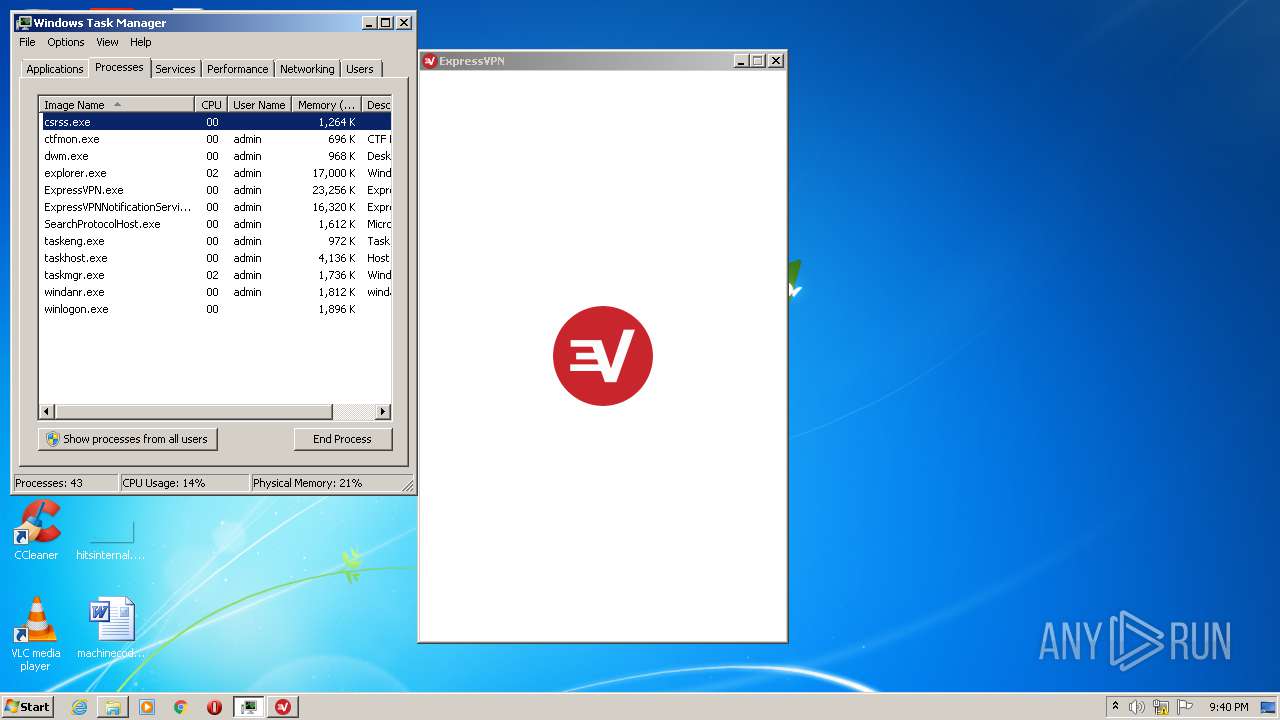
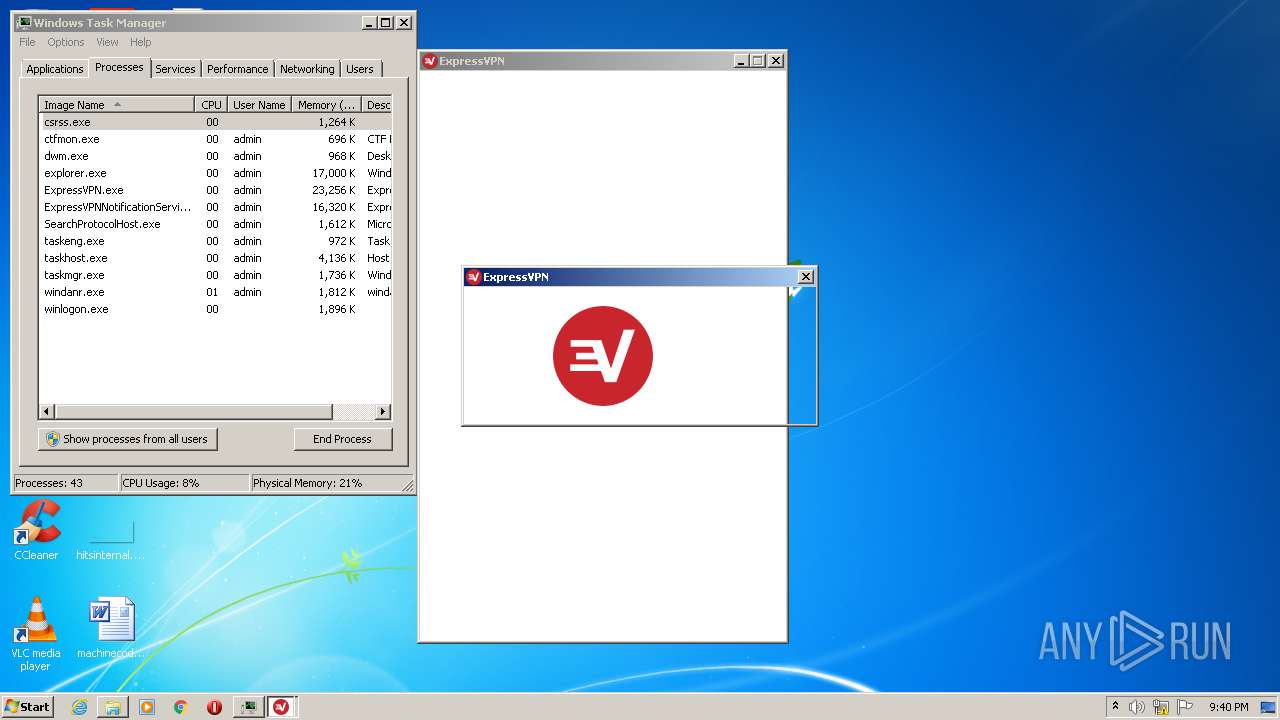
Manual execution by user
- explorer.exe (PID: 836)
- taskmgr.exe (PID: 4064)
- ExpressVPN.exe (PID: 668)
Changes internet zones settings
- iexplore.exe (PID: 1856)
- iexplore.exe (PID: 3072)
Creates files in the user directory
- iexplore.exe (PID: 2072)
- iexplore.exe (PID: 1872)
Changes settings of System certificates
- iexplore.exe (PID: 1856)
Reads internet explorer settings
- iexplore.exe (PID: 2072)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1856)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
112
Monitored processes
54
Malicious processes
24
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://download.expressvpn.xyz/clients/windows/expressvpn_7.7.11.4.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 532 | rundll32.exe "C:\Windows\Installer\MSI3E6D.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1130265 1 WixSharp Setup!ExpressVpn.Client.Setup.CustomActions.SetKb3033929 | C:\Windows\system32\rundll32.exe | — | MsiExec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 668 | "C:\Program Files\ExpressVPN\expressvpn-ui\ExpressVPN.exe" | C:\Program Files\ExpressVPN\expressvpn-ui\ExpressVPN.exe | explorer.exe | ||||||||||||
User: admin Company: ExpressVPN Integrity Level: MEDIUM Description: ExpressVPN Exit code: 0 Version: 7.7.11.4 Modules
| |||||||||||||||
| 680 | C:\Windows\system32\net1 stop expressvpnsplittunnel | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,3111810866834796717,13162155344746360254,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17727695367452481365 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2464 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 836 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,3111810866834796717,13162155344746360254,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6781300833177266636 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2280 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 980 | "C:\Users\admin\AppData\Local\Temp\{ADAA93F4-F715-4586-9C6B-74AF614B0C59}\.cr\expressvpn_7.7.11.4.exe" -burn.clean.room="C:\Users\admin\Downloads\expressvpn_7.7.11.4.exe" -burn.filehandle.attached=148 -burn.filehandle.self=156 | C:\Users\admin\AppData\Local\Temp\{ADAA93F4-F715-4586-9C6B-74AF614B0C59}\.cr\expressvpn_7.7.11.4.exe | expressvpn_7.7.11.4.exe | ||||||||||||
User: admin Company: ExpressVPN Integrity Level: MEDIUM Description: ExpressVPN Exit code: 0 Version: 7.7.11.4 Modules
| |||||||||||||||
| 1008 | C:\Windows\system32\MsiExec.exe -Embedding 00F8DF495485A07C8E8903CE9132203C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1020 | rundll32.exe "C:\Windows\Installer\MSI4005.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1130515 5 WixSharp Setup!ExpressVpn.Client.Setup.CustomActions.SetWin10 | C:\Windows\system32\rundll32.exe | — | MsiExec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
6 876
Read events
3 843
Write events
2 957
Delete events
76
Modification events
| (PID) Process: | (1912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 184-13238368535074625 |
Value: 259 | |||
| (PID) Process: | (184) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (184) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (184) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (184) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (184) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (184) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (184) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (184) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (184) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
130
Suspicious files
145
Text files
388
Unknown types
76
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 184 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F00E817-B8.pma | — | |
MD5:— | SHA256:— | |||
| 184 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\160be63e-4bc0-409c-ba88-eb8d92f664eb.tmp | — | |
MD5:— | SHA256:— | |||
| 184 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 184 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 184 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF1073ab.TMP | text | |
MD5:— | SHA256:— | |||
| 184 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 184 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 184 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
| 184 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 184 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF107580.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
44
TCP/UDP connections
73
DNS requests
41
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2072 | iexplore.exe | GET | 200 | 52.222.167.237:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
2072 | iexplore.exe | GET | 200 | 52.222.167.182:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
2072 | iexplore.exe | GET | 200 | 52.222.167.52:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
2072 | iexplore.exe | GET | 200 | 104.18.21.226:80 | http://ocsp.globalsign.com/rootr1/ME8wTTBLMEkwRzAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCDkbwjNvPLFRm7zMB3V80 | US | der | 1.49 Kb | whitelisted |
2072 | iexplore.exe | GET | 200 | 52.222.167.182:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
2072 | iexplore.exe | GET | 200 | 52.222.167.237:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
2072 | iexplore.exe | GET | 200 | 52.222.167.152:80 | http://ocsp.sca1b.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQz9arGHWbnBV0DFzpNHz4YcTiFDQQUWaRmBlKge5WSPKOUByeWdFv5PdACEApWG7%2BOHNwAE%2B8fzO%2FQGf4%3D | US | der | 471 b | whitelisted |
2072 | iexplore.exe | GET | 200 | 104.18.21.226:80 | http://ocsp.globalsign.com/rootr1/ME8wTTBLMEkwRzAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCDkbwjNvPLFRm7zMB3V80 | US | der | 1.49 Kb | whitelisted |
2072 | iexplore.exe | GET | 200 | 104.18.21.226:80 | http://ocsp.globalsign.com/rootr1/ME8wTTBLMEkwRzAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCDkbwjNvPLFRm7zMB3V80 | US | der | 1.49 Kb | whitelisted |
2072 | iexplore.exe | GET | 200 | 52.222.167.71:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3876 | chrome.exe | 172.217.22.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3876 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
3876 | chrome.exe | 52.222.174.100:443 | download.expressvpn.xyz | Amazon.com, Inc. | US | unknown |
3876 | chrome.exe | 172.217.18.100:443 | www.google.com | Google Inc. | US | whitelisted |
3876 | chrome.exe | 172.217.16.174:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
3876 | chrome.exe | 216.58.212.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2072 | iexplore.exe | 52.222.174.115:443 | www.ujsrxts.com | Amazon.com, Inc. | US | suspicious |
2072 | iexplore.exe | 52.222.167.237:80 | o.ss2.us | Amazon.com, Inc. | US | whitelisted |
2072 | iexplore.exe | 52.222.167.182:80 | ocsp.rootg2.amazontrust.com | Amazon.com, Inc. | US | whitelisted |
2072 | iexplore.exe | 52.222.167.52:80 | ocsp.rootg2.amazontrust.com | Amazon.com, Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.expressvpn.xyz |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
www.ujsrxts.com |
| malicious |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| shared |