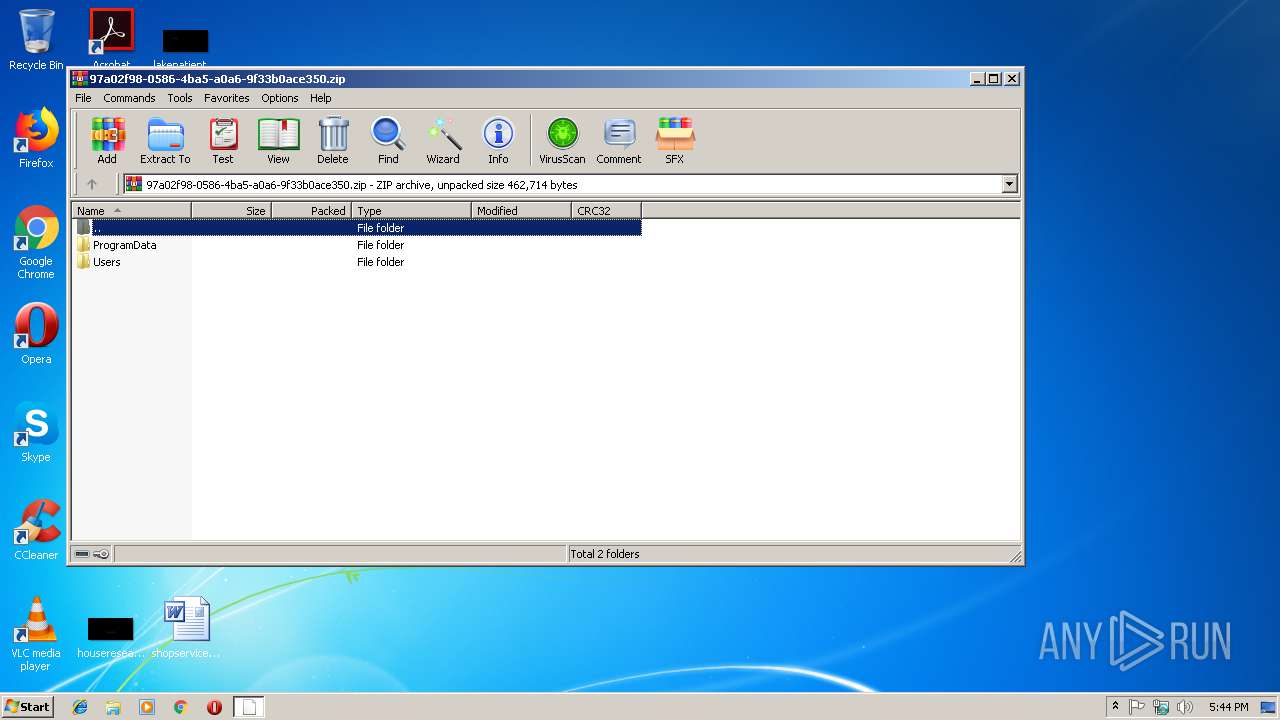
| File name: | 97a02f98-0586-4ba5-a0a6-9f33b0ace350.zip |
| Full analysis: | https://app.any.run/tasks/34d12ed8-525b-445d-87aa-b7069a252f57 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 15, 2018, 17:44:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 38264807B47B6B30513F64F8EA0C9B26 |
| SHA1: | 102FA7D7630F4040DC13A780BB3AA0084BED0049 |
| SHA256: | B690842DC11D8CF39E94A94C48CF16B9B8903D528559DE38AEE4C1F92B930247 |
| SSDEEP: | 3072:srzQaK5poTbP5qpQgndMDuQLE4XDVG3OCSKZA3tNZH:sr5OpoTlwndMDlFDVLTn3tNx |
MALICIOUS
Application was dropped or rewritten from another process
- Hdl.exe (PID: 3948)
- lpiograd.exe (PID: 3900)
- Hdl.exe (PID: 2484)
- lpiograd.exe (PID: 2644)
Emotet process was detected
- lpiograd.exe (PID: 3900)
Changes the autorun value in the registry
- lpiograd.exe (PID: 2644)
EMOTET was detected
- lpiograd.exe (PID: 2644)
Connects to CnC server
- lpiograd.exe (PID: 2644)
SUSPICIOUS
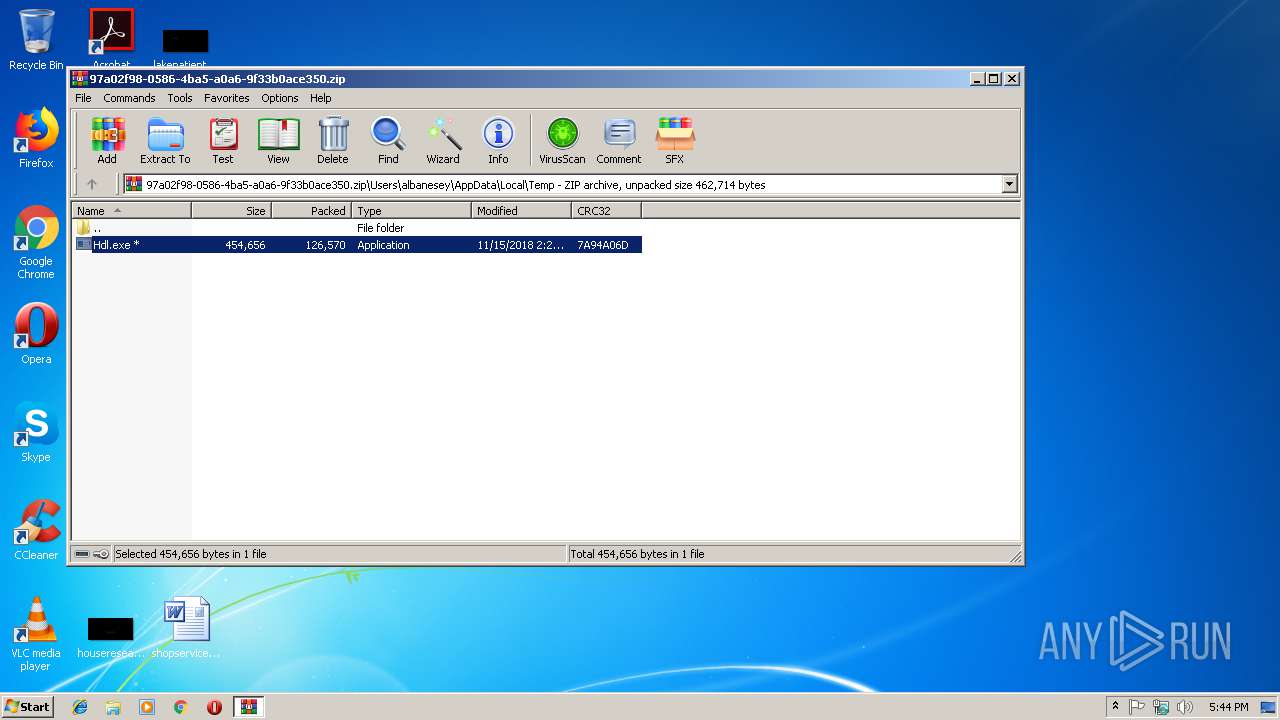
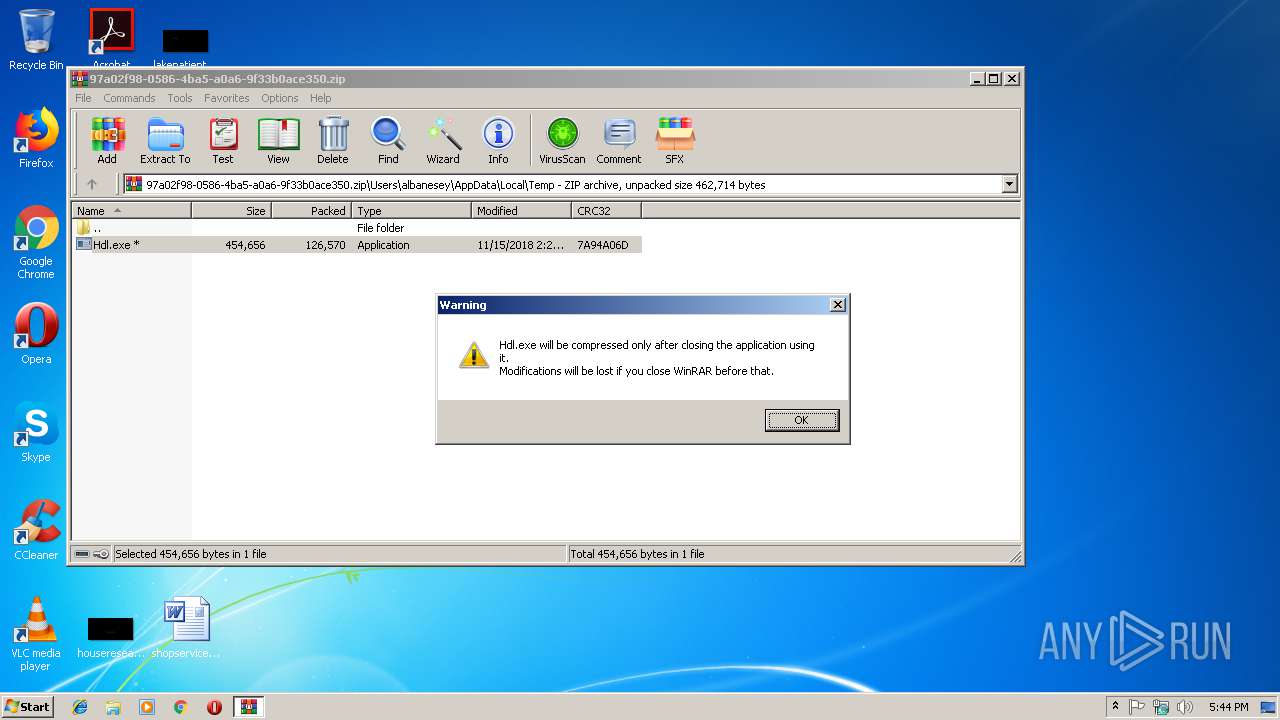
Creates files in the program directory
- WinRAR.exe (PID: 3044)
Executable content was dropped or overwritten
- Hdl.exe (PID: 2484)
- WinRAR.exe (PID: 3044)
Starts itself from another location
- Hdl.exe (PID: 2484)
Connects to unusual port
- lpiograd.exe (PID: 2644)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2018:11:15 14:25:14 |
| ZipCRC: | 0x7a94a06d |
| ZipCompressedSize: | 126570 |
| ZipUncompressedSize: | 454656 |
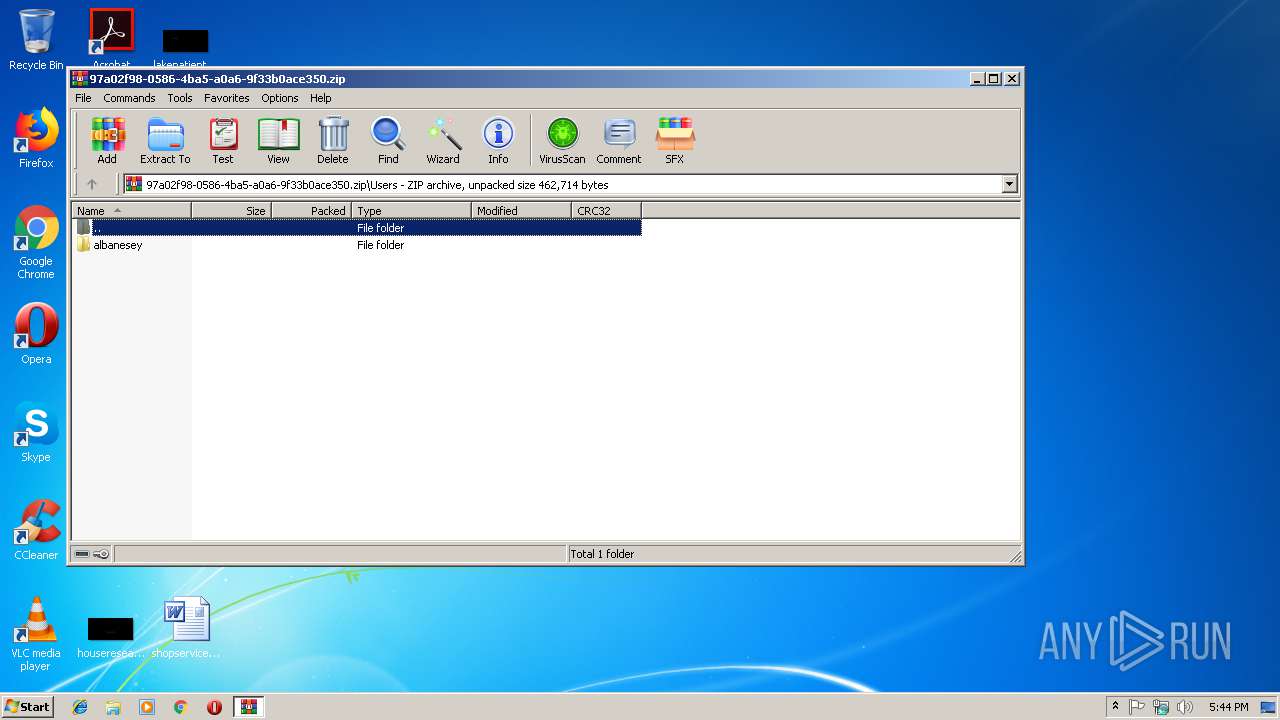
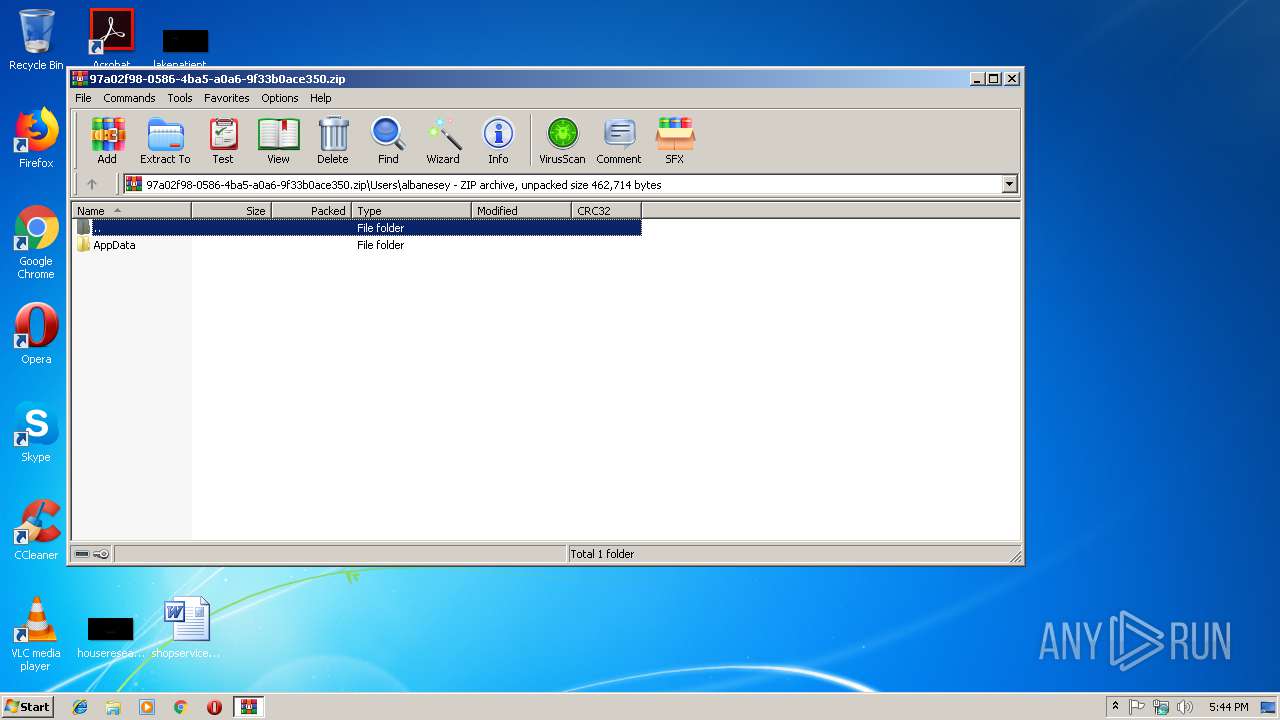
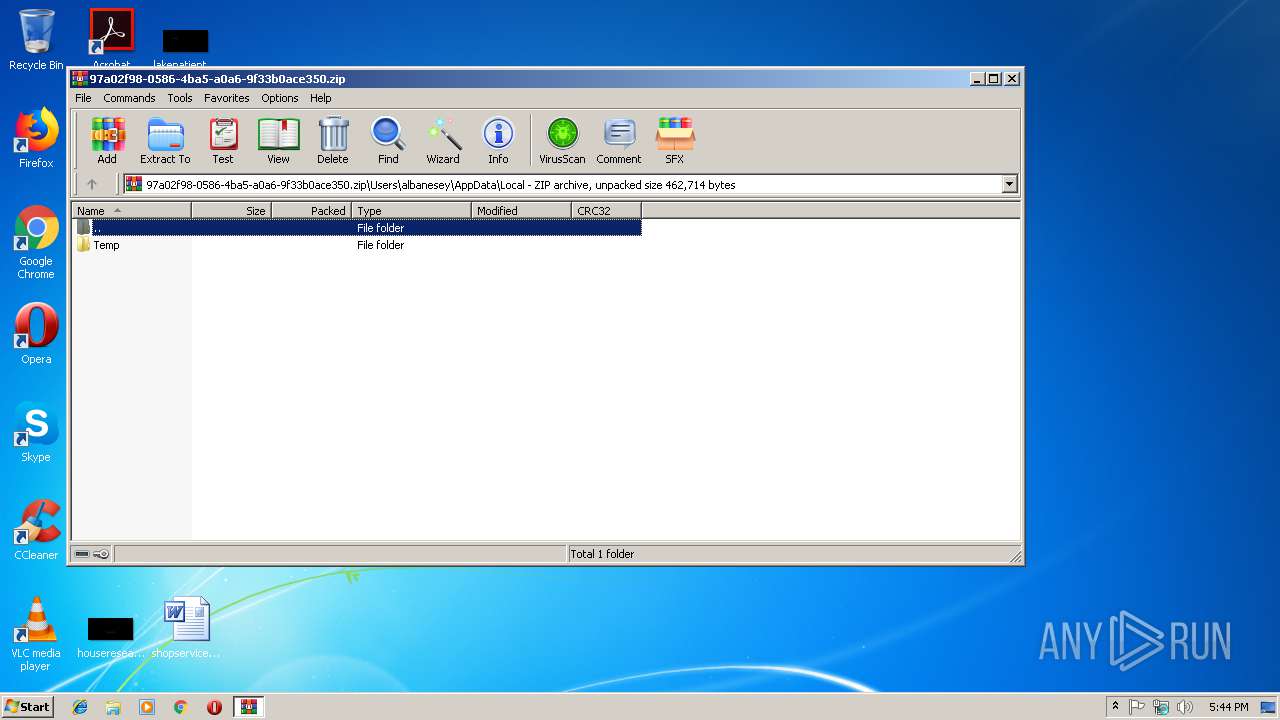
| ZipFileName: | Users/albanesey/AppData/Local/Temp/Hdl.exe |
Total processes
36
Monitored processes
5
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2484 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb3044.38141\Users\albanesey\AppData\Local\Temp\Hdl.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb3044.38141\Users\albanesey\AppData\Local\Temp\Hdl.exe | Hdl.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2644 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | lpiograd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
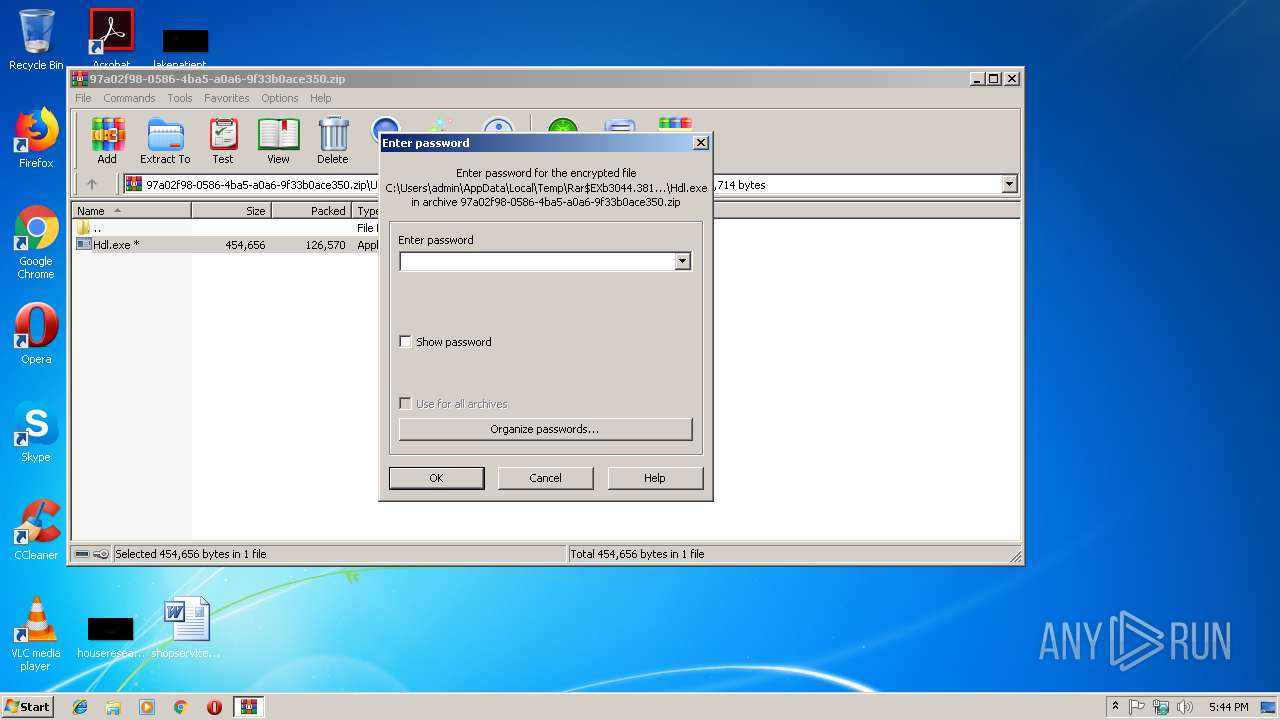
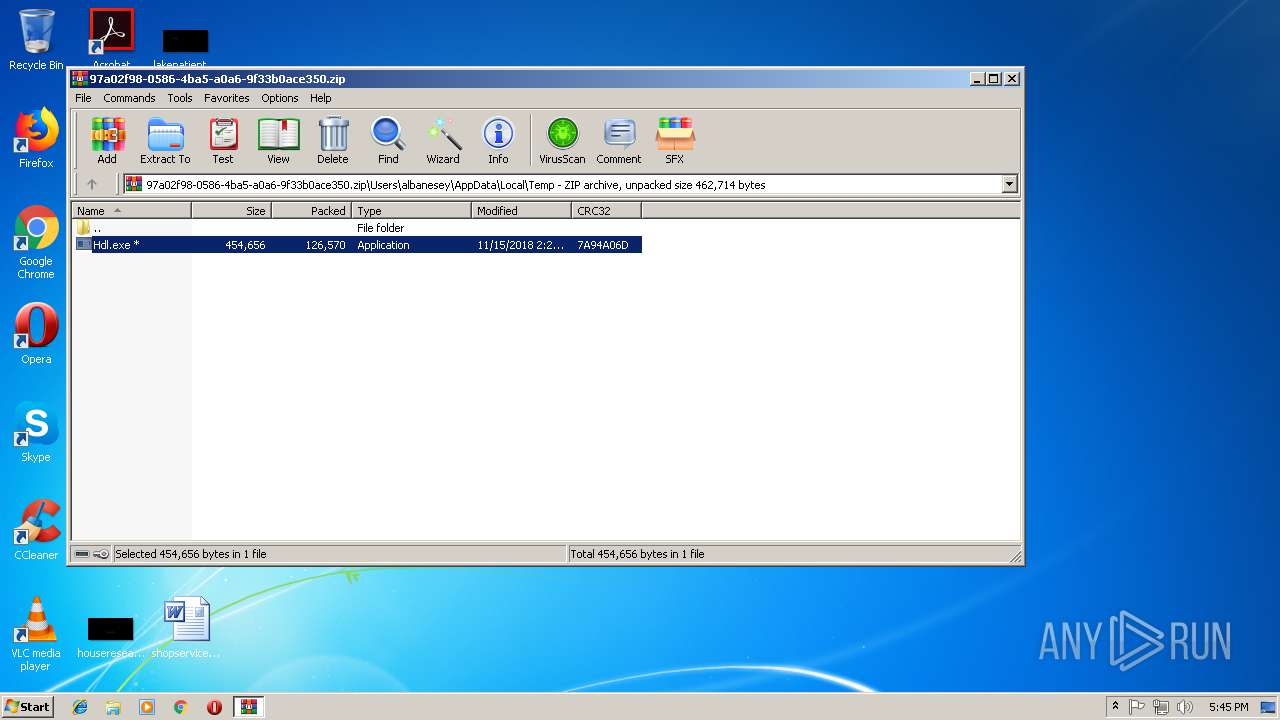
| 3044 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\97a02f98-0586-4ba5-a0a6-9f33b0ace350.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3900 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | Hdl.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3948 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb3044.38141\Users\albanesey\AppData\Local\Temp\Hdl.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb3044.38141\Users\albanesey\AppData\Local\Temp\Hdl.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
508
Read events
480
Write events
28
Delete events
0
Modification events
| (PID) Process: | (3044) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3044) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3044) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3044) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\97a02f98-0586-4ba5-a0a6-9f33b0ace350.zip | |||
| (PID) Process: | (3044) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3044) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3044) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3044) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3044) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3044) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3044 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb3044.38141\Users\albanesey\AppData\Local\Temp\Hdl.exe | executable | |
MD5:— | SHA256:— | |||
| 3044 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb3044.38141\ProgramData\McAfee\QuarMeta\97a02f98-0586-4ba5-a0a6-9f33b0ace350 | xml | |
MD5:— | SHA256:— | |||
| 2484 | Hdl.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
0
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2644 | lpiograd.exe | GET | 200 | 50.78.167.65:7080 | http://50.78.167.65:7080/ | US | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2644 | lpiograd.exe | 50.78.167.65:7080 | — | Comcast Cable Communications, LLC | US | malicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
2644 | lpiograd.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
1 ETPRO signatures available at the full report