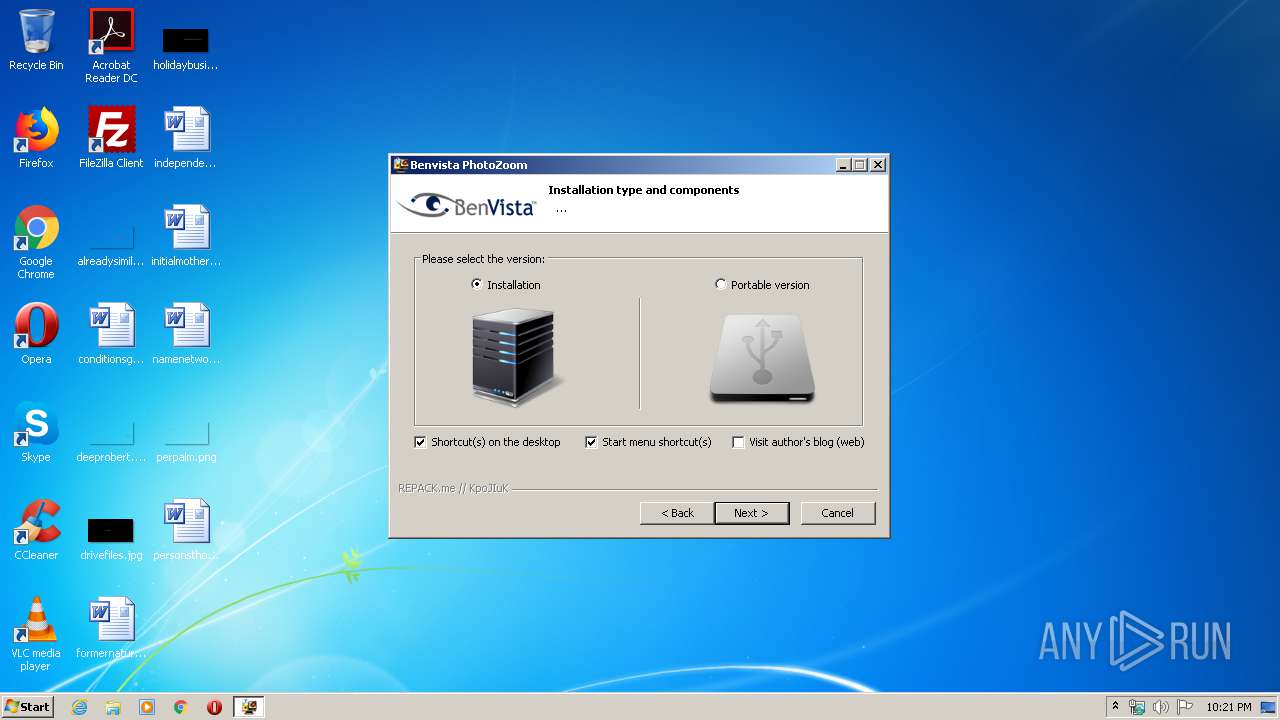
| File name: | Benvista.PhotoZoom.v8.0.6.exe |
| Full analysis: | https://app.any.run/tasks/84bdfc58-6c9a-470d-952a-a65204b549ba |
| Verdict: | Malicious activity |
| Analysis date: | March 30, 2020, 21:21:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 94B172559423763BFA6D8E566C68E0B6 |
| SHA1: | 28D2D27FD47BD1201622BF89F4C373218B8D5BEB |
| SHA256: | B689A13FD430C4C05C06E43FFAE5657D9839884BD3FAD2ACD9781E04379A8539 |
| SSDEEP: | 196608:8tAowAj68iNb8pV+7tn1LQTPz+5W7fi/SO+5Vp3ToqfY+/F:Y/jSeGZQTWWWuT3T3 |
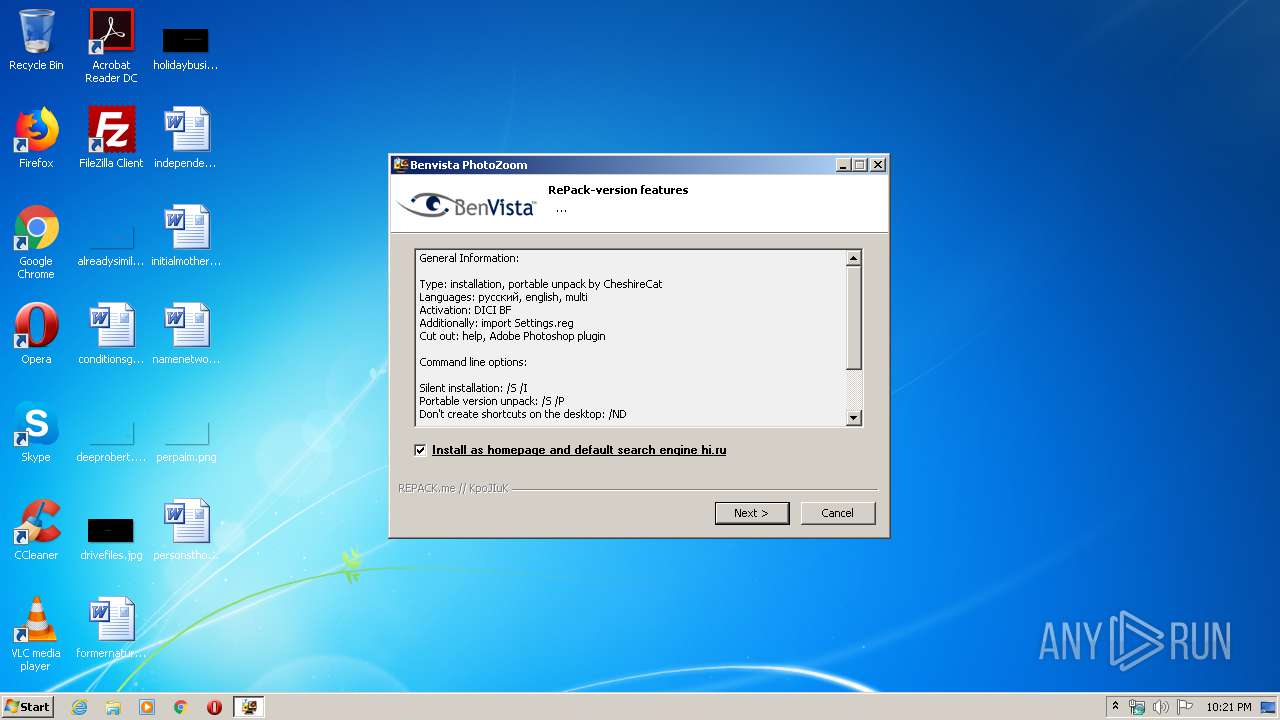
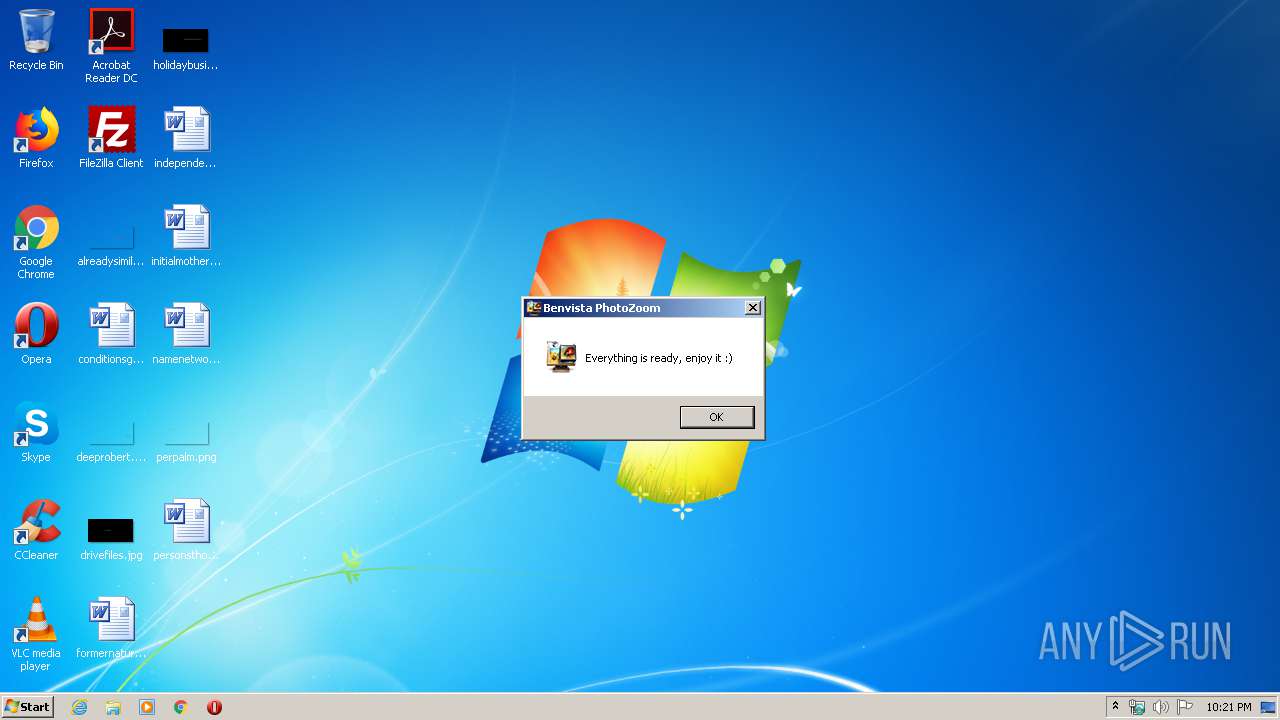
MALICIOUS
Application was dropped or rewritten from another process
- ns6E94.tmp (PID: 3472)
- ns704A.tmp (PID: 944)
Loads dropped or rewritten executable
- Benvista.PhotoZoom.v8.0.6.exe (PID: 1392)
SUSPICIOUS
Executable content was dropped or overwritten
- Benvista.PhotoZoom.v8.0.6.exe (PID: 1392)
Starts application with an unusual extension
- Benvista.PhotoZoom.v8.0.6.exe (PID: 1392)
Uses NETSH.EXE for network configuration
- ns6E94.tmp (PID: 3472)
INFO
Reads the hosts file
- Benvista.PhotoZoom.v8.0.6.exe (PID: 1392)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:02:24 20:19:59+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 28672 |
| InitializedDataSize: | 445952 |
| UninitializedDataSize: | 16896 |
| EntryPoint: | 0x39e3 |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 8.0.6.0 |
| ProductVersionNumber: | 8.0.6.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | BenVista Ltd. |
| FileDescription: | Benvista PhotoZoom v8.0.6 |
| FileVersion: | 8.0.6.0 |
| LegalCopyright: | © BenVista Ltd. |
| ProductName: | Benvista PhotoZoom v8.0.6 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Feb-2012 19:19:59 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | BenVista Ltd. |
| FileDescription: | Benvista PhotoZoom v8.0.6 |
| FileVersion: | 8.0.6.0 |
| LegalCopyright: | © BenVista Ltd. |
| ProductName: | Benvista PhotoZoom v8.0.6 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 24-Feb-2012 19:19:59 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006F10 | 0x00007000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.49816 |
.rdata | 0x00008000 | 0x00002A92 | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.39389 |
.data | 0x0000B000 | 0x00067EBC | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.47278 |
.ndata | 0x00073000 | 0x000F1000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00164000 | 0x00020B18 | 0x00020C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.74808 |
.reloc | 0x00185000 | 0x00000F8A | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 7.91786 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.22222 | 968 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 6.95177 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 6.94022 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 6.2725 | 3752 | UNKNOWN | English - United States | RT_ICON |
5 | 6.47817 | 2216 | UNKNOWN | English - United States | RT_ICON |
6 | 6.22027 | 1384 | UNKNOWN | English - United States | RT_ICON |
7 | 6.84381 | 1128 | UNKNOWN | English - United States | RT_ICON |
8 | 0 | 744 | UNKNOWN | English - United States | RT_ICON |
9 | 0 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 2.9807 | 132 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
44
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 944 | "C:\Users\admin\AppData\Local\Temp\nsj6B95.tmp\ns704A.tmp" route.exe delete 95.141.193.133 | C:\Users\admin\AppData\Local\Temp\nsj6B95.tmp\ns704A.tmp | — | Benvista.PhotoZoom.v8.0.6.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
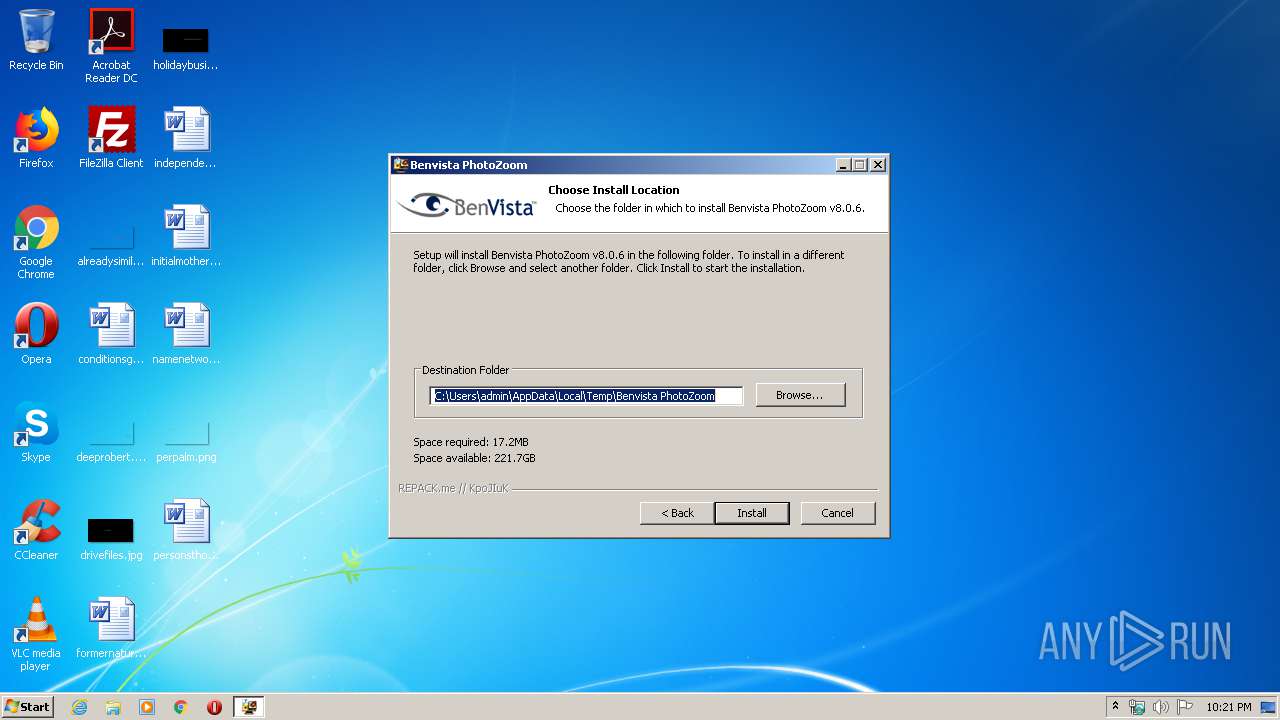
| 1392 | "C:\Users\admin\AppData\Local\Temp\Benvista.PhotoZoom.v8.0.6.exe" | C:\Users\admin\AppData\Local\Temp\Benvista.PhotoZoom.v8.0.6.exe | explorer.exe | ||||||||||||
User: admin Company: BenVista Ltd. Integrity Level: HIGH Description: Benvista PhotoZoom v8.0.6 Exit code: 0 Version: 8.0.6.0 Modules
| |||||||||||||||
| 2632 | netsh.exe advfirewall firewall delete rule name="all" remoteip=95.141.193.133 | C:\Windows\system32\netsh.exe | — | ns6E94.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3472 | "C:\Users\admin\AppData\Local\Temp\nsj6B95.tmp\ns6E94.tmp" netsh.exe advfirewall firewall delete rule name="all" remoteip=95.141.193.133 | C:\Users\admin\AppData\Local\Temp\nsj6B95.tmp\ns6E94.tmp | — | Benvista.PhotoZoom.v8.0.6.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 3632 | route.exe delete 95.141.193.133 | C:\Windows\system32\route.exe | — | ns704A.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Route Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4052 | "C:\Users\admin\AppData\Local\Temp\Benvista.PhotoZoom.v8.0.6.exe" | C:\Users\admin\AppData\Local\Temp\Benvista.PhotoZoom.v8.0.6.exe | — | explorer.exe | |||||||||||
User: admin Company: BenVista Ltd. Integrity Level: MEDIUM Description: Benvista PhotoZoom v8.0.6 Exit code: 3221226540 Version: 8.0.6.0 | |||||||||||||||
Total events
400
Read events
338
Write events
62
Delete events
0
Modification events
| (PID) Process: | (2632) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2632) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-100 |
Value: DHCP Quarantine Enforcement Client | |||
| (PID) Process: | (2632) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-101 |
Value: Provides DHCP based enforcement for NAP | |||
| (PID) Process: | (2632) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-103 |
Value: 1.0 | |||
| (PID) Process: | (2632) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-102 |
Value: Microsoft Corporation | |||
| (PID) Process: | (2632) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-1 |
Value: IPsec Relying Party | |||
| (PID) Process: | (2632) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-2 |
Value: Provides IPsec based enforcement for Network Access Protection | |||
| (PID) Process: | (2632) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-4 |
Value: 1.0 | |||
| (PID) Process: | (2632) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-3 |
Value: Microsoft Corporation | |||
| (PID) Process: | (2632) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\tsgqec.dll,-100 |
Value: RD Gateway Quarantine Enforcement Client | |||
Executable files
10
Suspicious files
0
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1392 | Benvista.PhotoZoom.v8.0.6.exe | C:\Users\admin\AppData\Local\Temp\nsj6B95.tmp\ns704A.tmp | — | |
MD5:— | SHA256:— | |||
| 1392 | Benvista.PhotoZoom.v8.0.6.exe | C:\Users\admin\AppData\Local\Temp\nsj6B94.tmp | — | |
MD5:— | SHA256:— | |||
| 1392 | Benvista.PhotoZoom.v8.0.6.exe | C:\Users\admin\AppData\Local\Temp\~DF6783B5C422BF0DAF.TMP | — | |
MD5:— | SHA256:— | |||
| 1392 | Benvista.PhotoZoom.v8.0.6.exe | C:\Users\admin\AppData\Local\Temp\nsj6B95.tmp\ns6E94.tmp | executable | |
MD5:— | SHA256:— | |||
| 1392 | Benvista.PhotoZoom.v8.0.6.exe | C:\Users\admin\AppData\Local\Temp\nsj6B95.tmp\modern-header.bmp | image | |
MD5:— | SHA256:— | |||
| 1392 | Benvista.PhotoZoom.v8.0.6.exe | C:\Users\admin\AppData\Local\Temp\nsj6B95.tmp\repackme.gif | image | |
MD5:23D3840ADB8F4F1EFC083A1F7E640191 | SHA256:82A1454402156D74F4F23C992D5D772B665546208EFF44790871B8DCB36D2304 | |||
| 1392 | Benvista.PhotoZoom.v8.0.6.exe | C:\Users\admin\AppData\Local\Temp\Benvista PhotoZoom\App\PhotoZoomPro\PhotoZoomPro.exe | executable | |
MD5:— | SHA256:— | |||
| 1392 | Benvista.PhotoZoom.v8.0.6.exe | C:\Users\admin\AppData\Local\Temp\nsj6B95.tmp\newadvsplash.dll | executable | |
MD5:55A723E125AFBC9B3A41D46F41749068 | SHA256:0A70CC4B93D87ECD93E538CFBED7C9A4B8B5C6F1042C6069757BDA0D1279ED06 | |||
| 1392 | Benvista.PhotoZoom.v8.0.6.exe | C:\Users\admin\AppData\Local\Temp\nsj6B95.tmp\Aero.dll | executable | |
MD5:869C5949A10B32D3A31966CC5291301B | SHA256:B19961DE6CA07E08704D6372718542F70DBBB203E59BF9BBE3A58F6E069A625C | |||
| 1392 | Benvista.PhotoZoom.v8.0.6.exe | C:\Users\admin\AppData\Local\Temp\Benvista PhotoZoom\PhotoZoomPro_Portable.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report