| File name: | inst_mawebdrm.exe |
| Full analysis: | https://app.any.run/tasks/f68d0e33-0d74-4c27-a63f-f387f9ba1c73 |
| Verdict: | Malicious activity |
| Analysis date: | April 16, 2020, 19:38:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | CC63829D8892CCF42072405B36A3CBB6 |
| SHA1: | B1D21A6423452CC39C06A9540693BD51CE8DD178 |
| SHA256: | B6862ABBEF37673B77B8351ED66212753D93DF4DA190049E97DD41B51A784E09 |
| SSDEEP: | 98304:6V8vsHQswrD9Y0NVoWMPhH9d5S72je65QLdBfIcpJYtFR/P+AOA1gdgmsQcEr/13:6Cvsk9WWU59d47FeQQcpCPjOGgdJsQ/x |
MALICIOUS
Loads dropped or rewritten executable
- inst_mawebdrm.exe (PID: 3148)
- markany_ImageSafer_v5.18.0416.exe (PID: 660)
- install.exe (PID: 4000)
- IMGSF50Start_x86.exe (PID: 2852)
- conhost.exe (PID: 1456)
- certutil.exe (PID: 1844)
- conhost.exe (PID: 3556)
- conhost.exe (PID: 2760)
- explorer.exe (PID: 372)
- MaWebDRMAgent.exe (PID: 2056)
Application was dropped or rewritten from another process
- MaRPackCheck.exe (PID: 3736)
- markany_ImageSafer_v5.18.0416.exe (PID: 660)
- install.exe (PID: 4000)
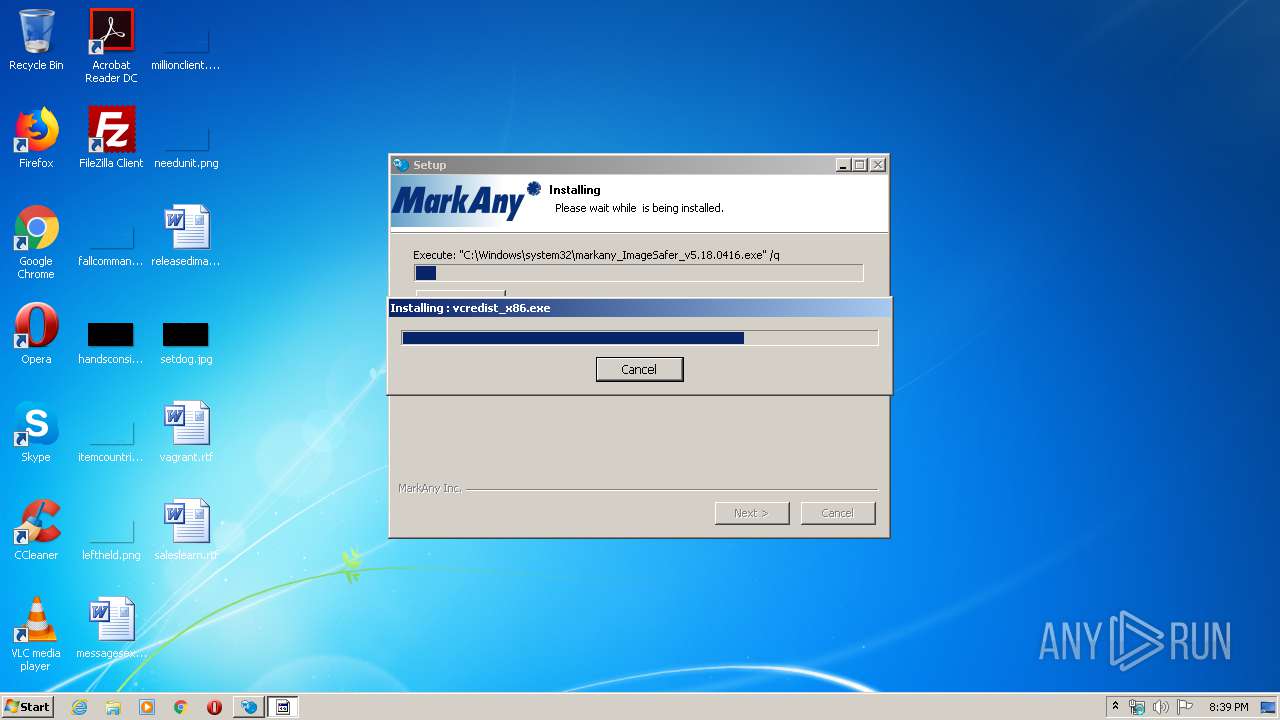
- vcredist_x86.exe (PID: 3036)
- IMGSF50Svc.exe (PID: 1688)
- IMGSF50Start_x86.exe (PID: 2852)
- certutil.exe (PID: 1844)
- IMGSF50Svc.exe (PID: 3492)
- IMGSF50Svc.exe (PID: 2120)
- MaWebDRMSVC.exe (PID: 3440)
- MaWebDRMAgent.exe (PID: 2056)
- MaWebDRMSVC.exe (PID: 1228)
- CRIMgr.exe (PID: 3212)
- MaWebDRMSVC.exe (PID: 2496)
Changes settings of System certificates
- regedit.exe (PID: 4068)
- msiexec.exe (PID: 3488)
Actions looks like stealing of personal data
- certutil.exe (PID: 1844)
- CRIMgr.exe (PID: 3212)
Changes internet zones settings
- CRIMgr.exe (PID: 3212)
SUSPICIOUS
Executable content was dropped or overwritten
- inst_mawebdrm.exe (PID: 3148)
- MaRPackCheck.exe (PID: 3736)
- markany_ImageSafer_v5.18.0416.exe (PID: 660)
- msiexec.exe (PID: 3488)
- vcredist_x86.exe (PID: 3036)
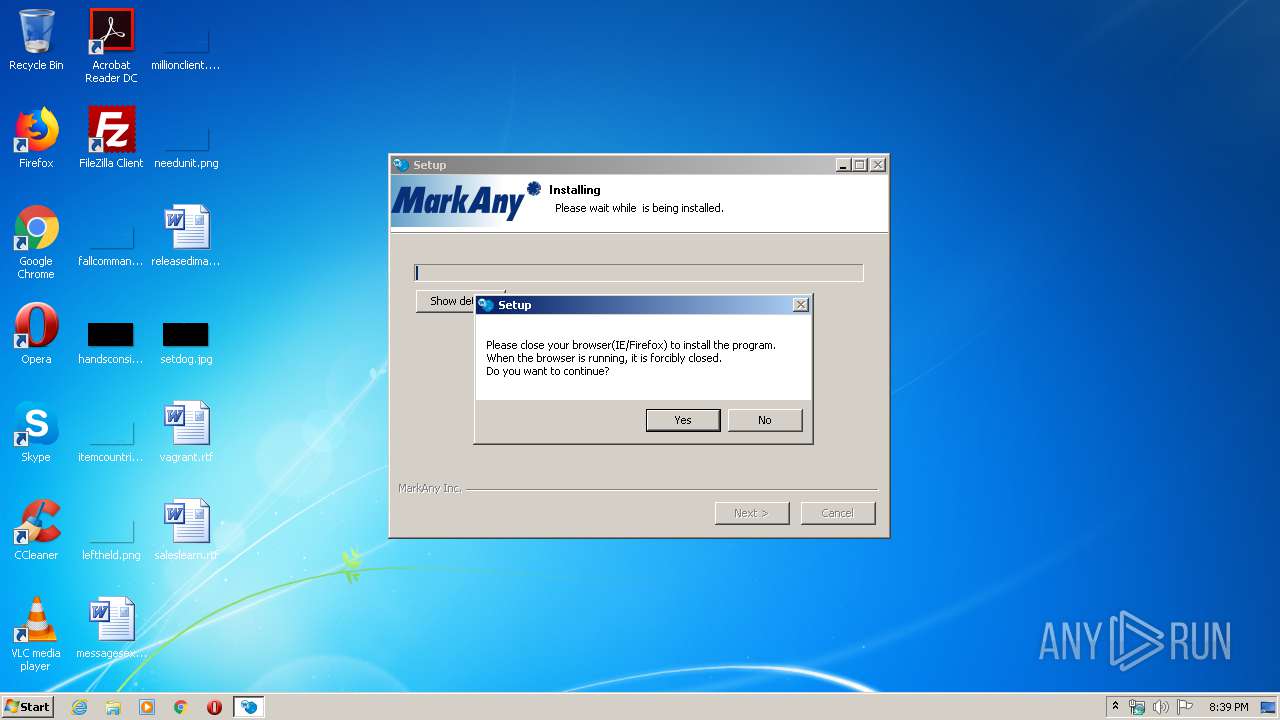
Uses TASKKILL.EXE to kill Browsers
- inst_mawebdrm.exe (PID: 3148)
Reads Internet Cache Settings
- MaRPackCheck.exe (PID: 3736)
Uses TASKKILL.EXE to kill process
- inst_mawebdrm.exe (PID: 3148)
Creates files in the Windows directory
- inst_mawebdrm.exe (PID: 3148)
- markany_ImageSafer_v5.18.0416.exe (PID: 660)
- msiexec.exe (PID: 3488)
Executed as Windows Service
- IMGSF50Svc.exe (PID: 2120)
- MaWebDRMSVC.exe (PID: 2496)
Removes files from Windows directory
- markany_ImageSafer_v5.18.0416.exe (PID: 660)
- inst_mawebdrm.exe (PID: 3148)
- msiexec.exe (PID: 3488)
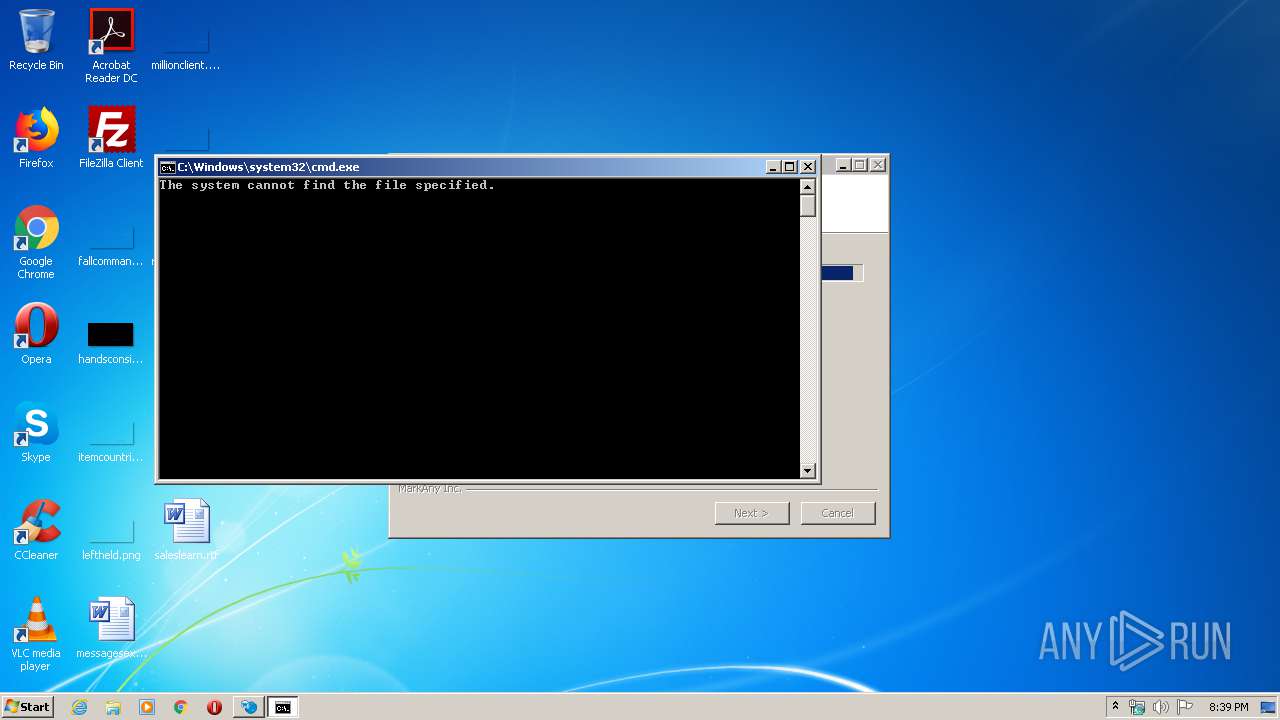
Starts CMD.EXE for commands execution
- inst_mawebdrm.exe (PID: 3148)
Creates files in the program directory
- inst_mawebdrm.exe (PID: 3148)
Creates files in the user directory
- certutil.exe (PID: 1844)
- CRIMgr.exe (PID: 3212)
Creates a software uninstall entry
- inst_mawebdrm.exe (PID: 3148)
Modifies the open verb of a shell class
- CRIMgr.exe (PID: 3212)
Adds / modifies Windows certificates
- msiexec.exe (PID: 3488)
INFO
Reads settings of System Certificates
- msiexec.exe (PID: 3488)
- MaWebDRMAgent.exe (PID: 2056)
Creates a software uninstall entry
- msiexec.exe (PID: 3488)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:08:01 02:34:02+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25600 |
| InitializedDataSize: | 162816 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x31f1 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.5.1.43 |
| ProductVersionNumber: | 2.5.1.43 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Unknown (0483) |
| CharacterSet: | Windows, Latin1 |
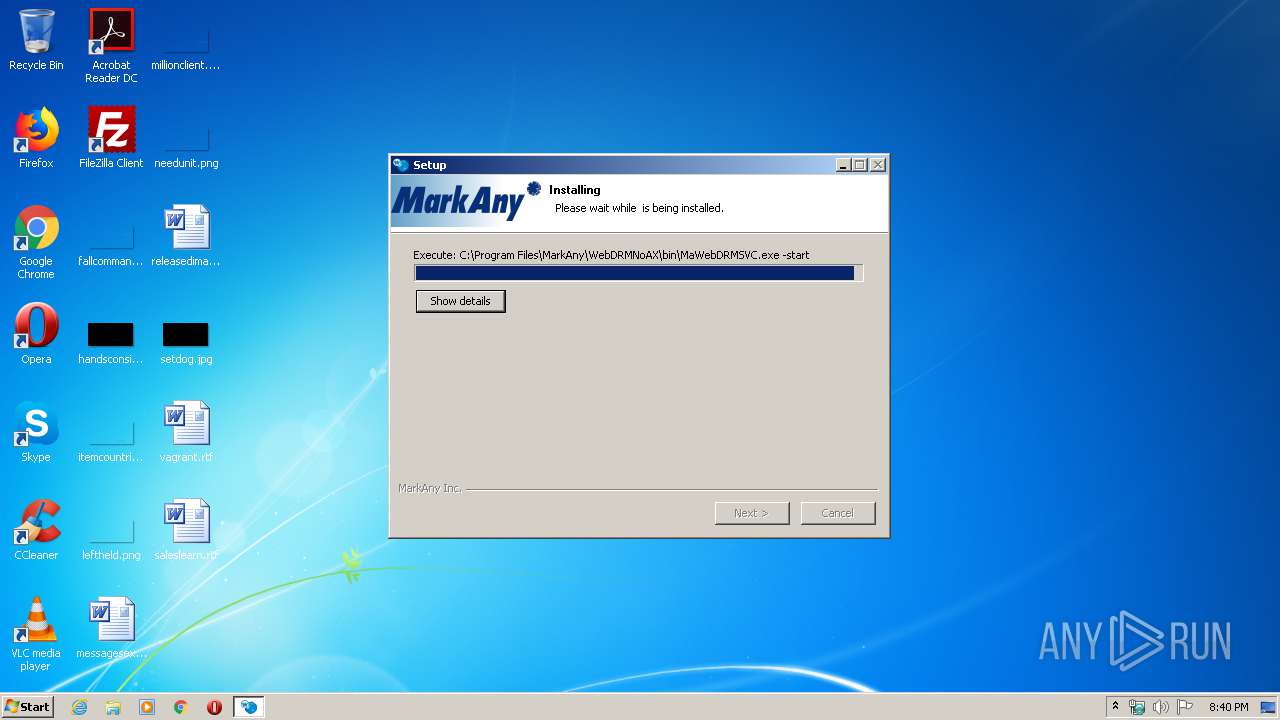
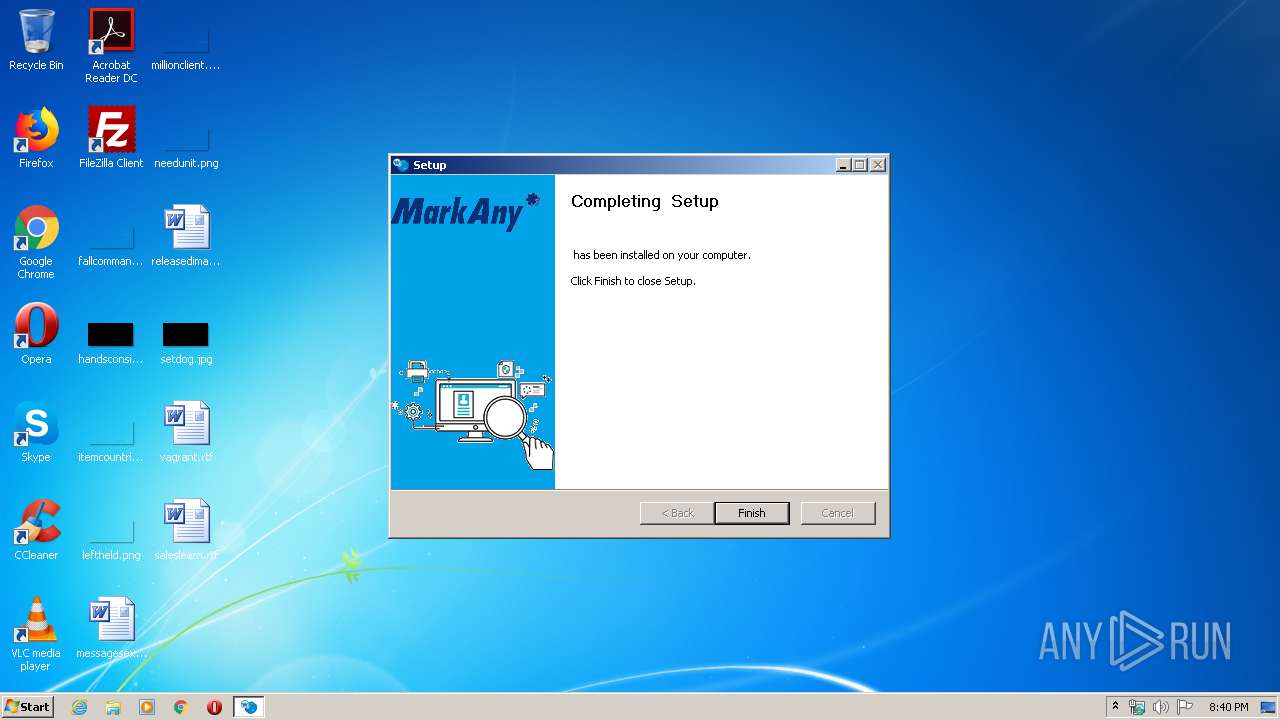
| Comments: | MarkAny WebDRMNoAX |
| CompanyName: | MarkAny Inc. |
| FileDescription: | MarkAny WebDRMNoAX |
| FileVersion: | 2.5.1.43 |
| LegalCopyright: | MarkAny Inc. |
| ProductName: | MarkAny WebDRMNoAX |
| ProductVersion: | 2.5.1.43 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Aug-2017 00:34:02 |
| Detected languages: |
|
| Comments: | MarkAny WebDRMNoAX |
| CompanyName: | MarkAny Inc. |
| FileDescription: | MarkAny WebDRMNoAX |
| FileVersion: | 2.5.1.43 |
| LegalCopyright: | MarkAny Inc. |
| ProductName: | MarkAny WebDRMNoAX |
| ProductVersion: | 2.5.1.43 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 01-Aug-2017 00:34:02 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006254 | 0x00006400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.43386 |
.rdata | 0x00008000 | 0x00001354 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.23627 |
.data | 0x0000A000 | 0x00025518 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.04463 |
.ndata | 0x00030000 | 0x00010000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00040000 | 0x00006708 | 0x00006800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.16029 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.2901 | 1072 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 2.06599 | 3752 | UNKNOWN | English - United States | RT_ICON |
3 | 0 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 0 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 0 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 0 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 0 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 4.62 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.67385 | 512 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
74
Monitored processes
28
Malicious processes
9
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
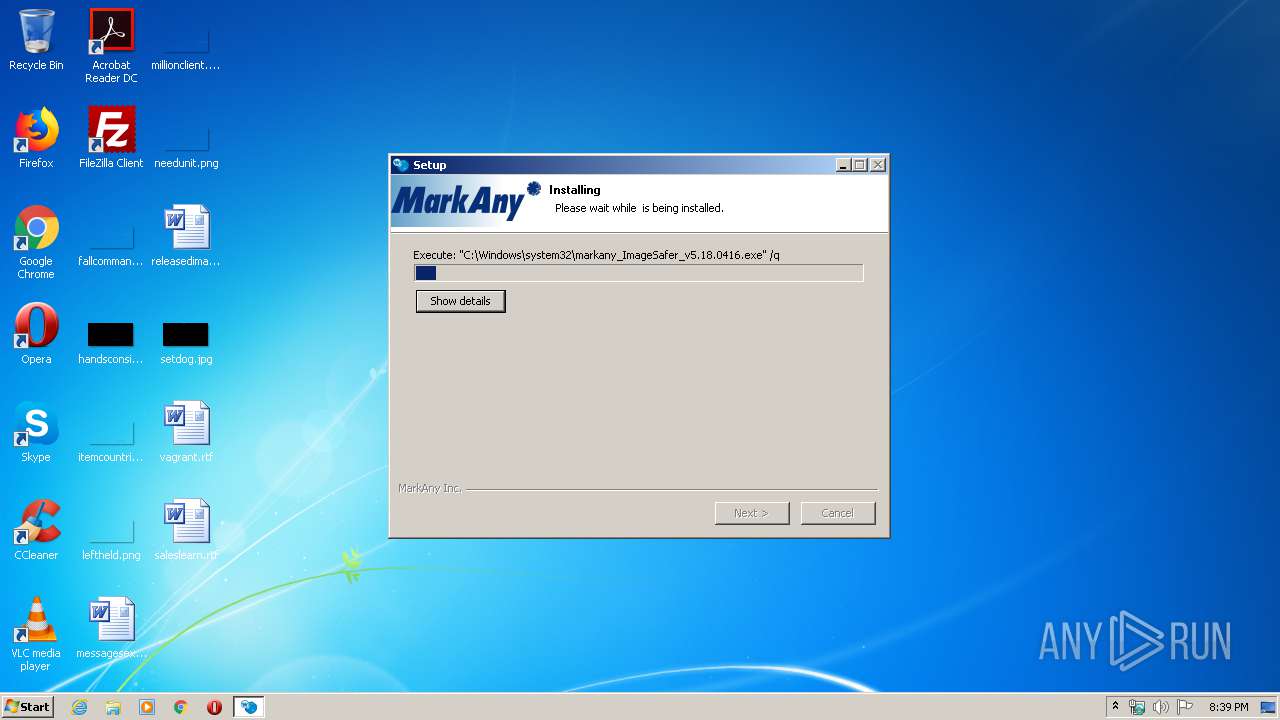
| 660 | "C:\Windows\system32\markany_ImageSafer_v5.18.0416.exe" /q | C:\Windows\system32\markany_ImageSafer_v5.18.0416.exe | inst_mawebdrm.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
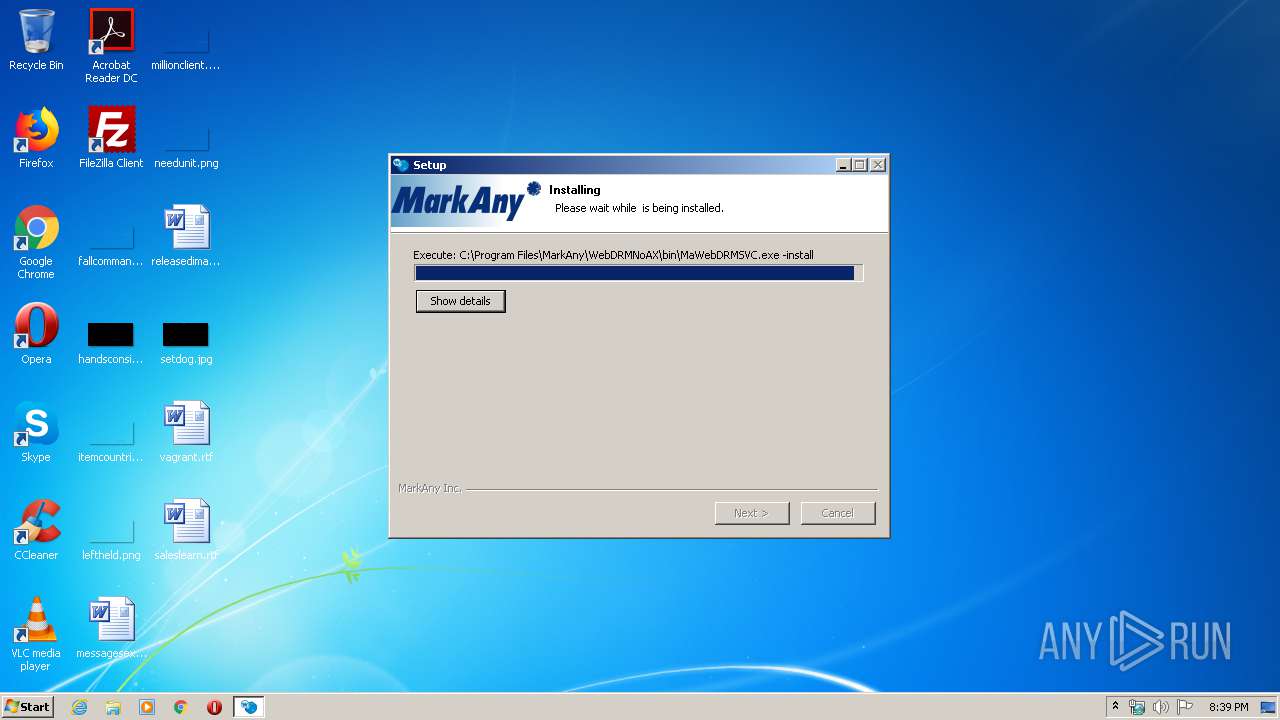
| 1228 | "C:\Program Files\MarkAny\WebDRMNoAX\bin\MaWebDRMSVC.exe" -install | C:\Program Files\MarkAny\WebDRMNoAX\bin\MaWebDRMSVC.exe | — | inst_mawebdrm.exe | |||||||||||
User: admin Company: MarkAny Inc. Integrity Level: HIGH Description: MaWebDRMSVC.exe Exit code: 0 Version: 2, 5, 1, 42 Modules
| |||||||||||||||
| 1456 | \??\C:\Windows\system32\conhost.exe "-383789891-12687131331663351448-927350101-382787285-1332914432-1985088747216615748" | C:\Windows\system32\conhost.exe | — | csrss.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1468 | TaskKill /F /IM iexplore.exe | C:\Windows\system32\TaskKill.exe | — | inst_mawebdrm.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1536 | "C:\Users\admin\AppData\Local\Temp\inst_mawebdrm.exe" | C:\Users\admin\AppData\Local\Temp\inst_mawebdrm.exe | — | explorer.exe | |||||||||||
User: admin Company: MarkAny Inc. Integrity Level: MEDIUM Description: MarkAny WebDRMNoAX Exit code: 3221226540 Version: 2.5.1.43 Modules
| |||||||||||||||
| 1688 | C:\Windows\IMGSF50Svc.exe -start | C:\Windows\IMGSF50Svc.exe | — | markany_ImageSafer_v5.18.0416.exe | |||||||||||
User: admin Company: MarkAny Integrity Level: HIGH Description: Image SAFER 5.0 Session Managing Service for x86 Exit code: 0 Version: 5, 0, 18, 416 Modules
| |||||||||||||||
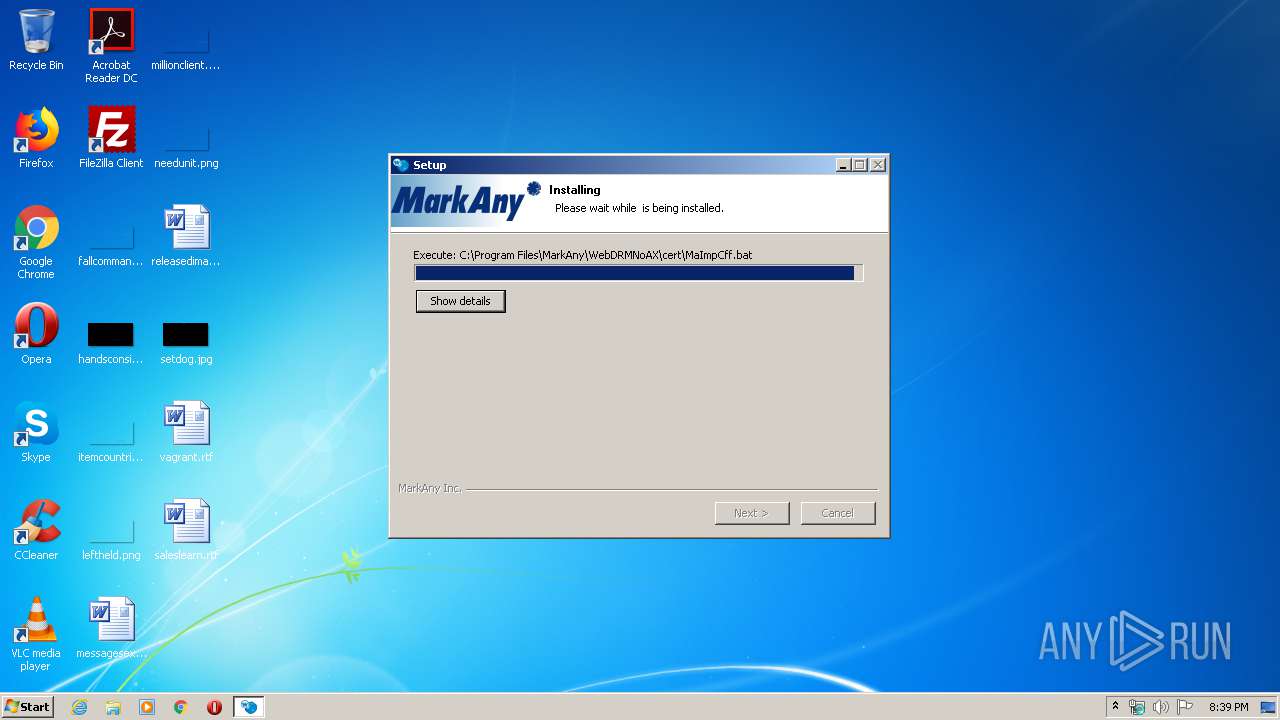
| 1844 | "C:\Program Files\MarkAny\WebDRMNoAX\cert\certutil.exe" -A -n "C:\Program Files\MarkAny\WebDRMNoAX\cert\maca.crt" -i "C:\Program Files\MarkAny\WebDRMNoAX\cert\maca.crt" -t "TCu,TCu,TCu" -d . | C:\Program Files\MarkAny\WebDRMNoAX\cert\certutil.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2056 | "C:\Program Files\MarkAny\WebDRMNoAX\bin\MaWebDRMAgent.exe" | C:\Program Files\MarkAny\WebDRMNoAX\bin\MaWebDRMAgent.exe | MaWebDRMSVC.exe | ||||||||||||
User: admin Company: MarkAny Inc. Integrity Level: HIGH Description: MaWebDRMAgent For NoAX Exit code: 0 Version: 2, 5, 1, 43 Modules
| |||||||||||||||
| 2120 | C:\Windows\IMGSF50Svc.exe | C:\Windows\IMGSF50Svc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: MarkAny Integrity Level: SYSTEM Description: Image SAFER 5.0 Session Managing Service for x86 Exit code: 0 Version: 5, 0, 18, 416 Modules
| |||||||||||||||
Total events
2 492
Read events
802
Write events
1 666
Delete events
24
Modification events
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | P:\Hfref\nqzva\NccQngn\Ybpny\Grzc\vafg_znjroqez.rkr |
Value: 00000000000000000000000000000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 0000000040000000500000008BC825000A00000018000000868F0F007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000005CE9ED0100000000000000000000000000000000480B20020000000005000000D80B200200000000340C200270E9ED01C0E9ED010000000000000000C0DB2002050000002000000000000000000000000100000064666C7464666C7400000000400000000459A377AD0501A70000000000000000010000000000000000000000B02D0C08A82C0C08A4E9ED013DA9D27600000000FBFFFF7FC8E9ED01987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000371054065310540637105406000000000000000000000000080000002E006C006E006B0000006E006400200011000000483D3200403D32002E006C006E006B0000002F0080EA0000C85704AB34EAED018291D27680EAED01EC430000E45704AB48EAED01B69CD276F04311024C06000060EAED01603F11026CEAED0111000000483D3200403D320060EAED01803F1102D0EA0000BC5704AB80EAED018291D276D0EAED0184EAED012795D27600000000EC431102ACEAED01CD94D276EC43110258EBED01603F1102E194D27600000000603F110258EBED01B4EAED010A00000018000000868F0F007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000005CE9ED0100000000000000000000000000000000480B20020000000005000000D80B200200000000340C200270E9ED01C0E9ED010000000000000000C0DB2002050000002000000000000000000000000100000064666C7464666C7400000000400000000459A377AD0501A70000000000000000010000000000000000000000B02D0C08A82C0C08A4E9ED013DA9D27600000000FBFFFF7FC8E9ED01987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000371054065310540637105406000000000000000000000000080000002E006C006E006B0000006E006400200011000000483D3200403D32002E006C006E006B0000002F0080EA0000C85704AB34EAED018291D27680EAED01EC430000E45704AB48EAED01B69CD276F04311024C06000060EAED01603F11026CEAED0111000000483D3200403D320060EAED01803F1102D0EA0000BC5704AB80EAED018291D276D0EAED0184EAED012795D27600000000EC431102ACEAED01CD94D276EC43110258EBED01603F1102E194D27600000000603F110258EBED01B4EAED010A00000018000000868F0F007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000005CE9ED0100000000000000000000000000000000480B20020000000005000000D80B200200000000340C200270E9ED01C0E9ED010000000000000000C0DB2002050000002000000000000000000000000100000064666C7464666C7400000000400000000459A377AD0501A70000000000000000010000000000000000000000B02D0C08A82C0C08A4E9ED013DA9D27600000000FBFFFF7FC8E9ED01987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000371054065310540637105406000000000000000000000000080000002E006C006E006B0000006E006400200011000000483D3200403D32002E006C006E006B0000002F0080EA0000C85704AB34EAED018291D27680EAED01EC430000E45704AB48EAED01B69CD276F04311024C06000060EAED01603F11026CEAED0111000000483D3200403D320060EAED01803F1102D0EA0000BC5704AB80EAED018291D276D0EAED0184EAED012795D27600000000EC431102ACEAED01CD94D276EC43110258EBED01603F1102E194D27600000000603F110258EBED01B4EAED01 | |||
| (PID) Process: | (3736) MaRPackCheck.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3736) MaRPackCheck.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3736) MaRPackCheck.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3736) MaRPackCheck.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3736) MaRPackCheck.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3736) MaRPackCheck.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3736) MaRPackCheck.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
66
Suspicious files
9
Text files
33
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3148 | inst_mawebdrm.exe | C:\Windows\system32\markany_ImageSafer_v5.18.0416.exe | executable | |
MD5:— | SHA256:— | |||
| 3148 | inst_mawebdrm.exe | C:\Users\admin\AppData\Local\Temp\nseEBA1.tmp\modern-wizard.bmp | image | |
MD5:— | SHA256:— | |||
| 3736 | MaRPackCheck.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\vcredist_x86[1].exe | executable | |
MD5:FD30ACC7A696C32F661B33668E73BF7B | SHA256:97C260D35BCFE18E046A1C413B9FC5A2754B8F790F7ACE669A3BE2500C0DF229 | |||
| 3148 | inst_mawebdrm.exe | C:\Users\admin\AppData\Local\Temp\nseEBA1.tmp\System.dll | executable | |
MD5:55A26D7800446F1373056064C64C3CE8 | SHA256:904FD5481D72F4E03B01A455F848DEDD095D0FB17E33608E0D849F5196FB6FF8 | |||
| 660 | markany_ImageSafer_v5.18.0416.exe | C:\Windows\system32\MaRPackCheck.exe | executable | |
MD5:C0C550881FC0D4DAAEE3819CD8FCF89F | SHA256:6A0D1132E0E5AB7E0B71779F16DBFDC1F37B29F8937C9259D68D7D5C9AA3F23B | |||
| 3148 | inst_mawebdrm.exe | C:\Users\admin\AppData\Local\Temp\nseEBA1.tmp\MaPlugins.dll | executable | |
MD5:5450157DED399912B02D03AAF03053C2 | SHA256:45D24CA2FD9A0F6603365001E770A5E1D0103CAA32D9667DEC55D26F3598D110 | |||
| 660 | markany_ImageSafer_v5.18.0416.exe | C:\Users\admin\AppData\Local\Temp\nsk3889.tmp\nsProcess.dll | executable | |
MD5:05450FACE243B3A7472407B999B03A72 | SHA256:95FE9D92512FF2318CC2520311EF9145B2CEE01209AB0E1B6E45C7CE1D4D0E89 | |||
| 3036 | vcredist_x86.exe | C:\fa220b4387bbecf6a1ffb2\vc_red.msi | executable | |
MD5:E493A21C57D160F4FA023C63145FE580 | SHA256:2CC196BED01619B5498A974C19CFCBA6A04B7746E84808F06D9E4DE3129AB4DB | |||
| 3036 | vcredist_x86.exe | C:\fa220b4387bbecf6a1ffb2\install.res.1040.dll | executable | |
MD5:E154E908FEA2658DD8E68B85F1D12C9E | SHA256:D2323AD38DC863226C4FC4B0AD49A621100E96265BA17C361603A613F9A8FAA1 | |||
| 3036 | vcredist_x86.exe | C:\fa220b4387bbecf6a1ffb2\install.res.1049.dll | executable | |
MD5:BB8CC77EED188B459AD376A2FE755ACD | SHA256:AA4B5C8C52DF5482C9C9C51EA95FD0408DA5856DFA0DA24363C03D07DFAB72EE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
2
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3736 | MaRPackCheck.exe | 23.213.14.160:80 | download.microsoft.com | Time Warner Cable Internet LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3736 | MaRPackCheck.exe | A Network Trojan was detected | ET MALWARE User-Agent (HTTP) |
3736 | MaRPackCheck.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
Process | Message |
|---|---|
MaWebDRMAgent.exe | C:\Users\admin\AppData\LocalLow\MarkAny |