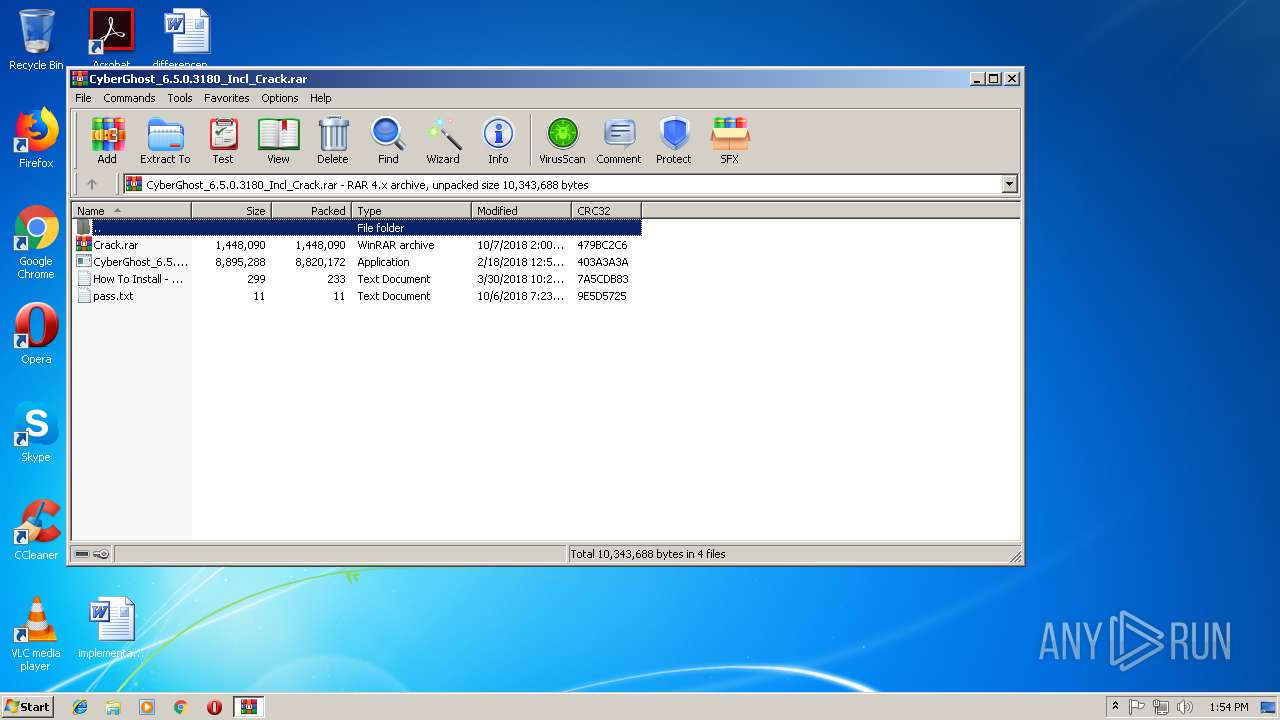
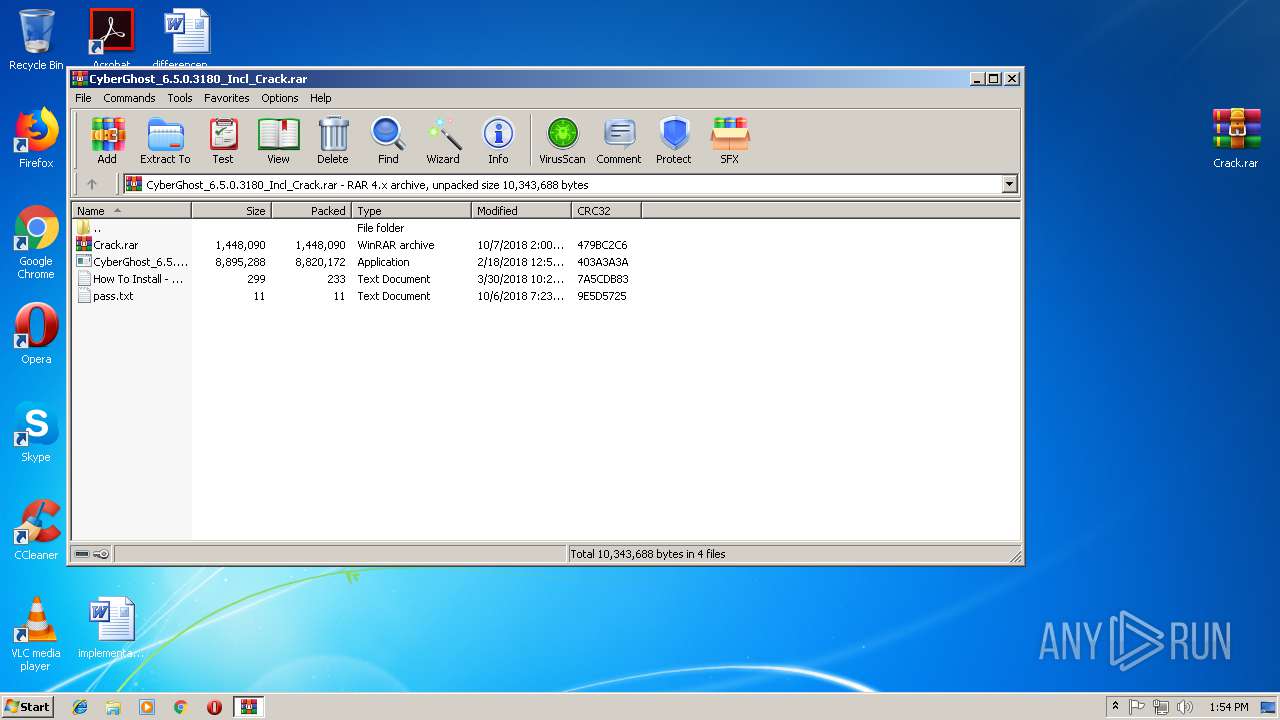
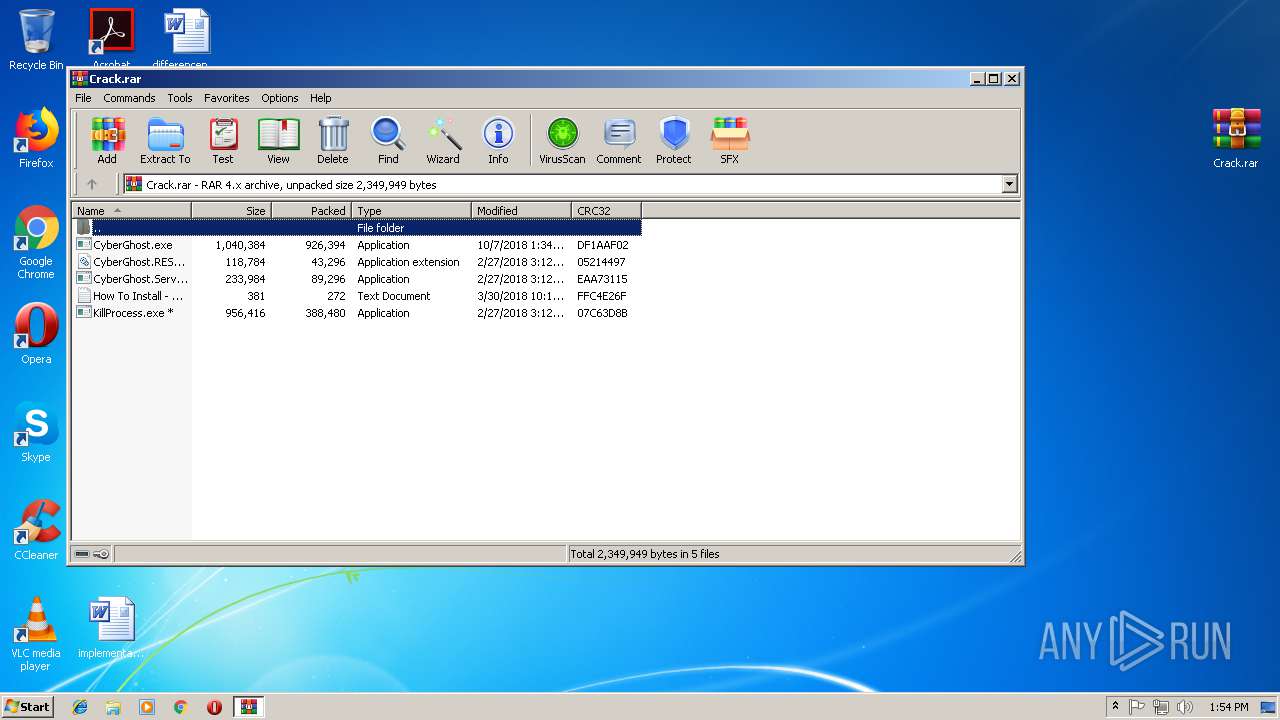
| File name: | CyberGhost_6.5.0.3180_Incl_Crack.rar |
| Full analysis: | https://app.any.run/tasks/483e76ba-28fa-4ab3-9d3f-0a106b7e1f33 |
| Verdict: | Malicious activity |
| Analysis date: | November 04, 2018, 13:53:40 |
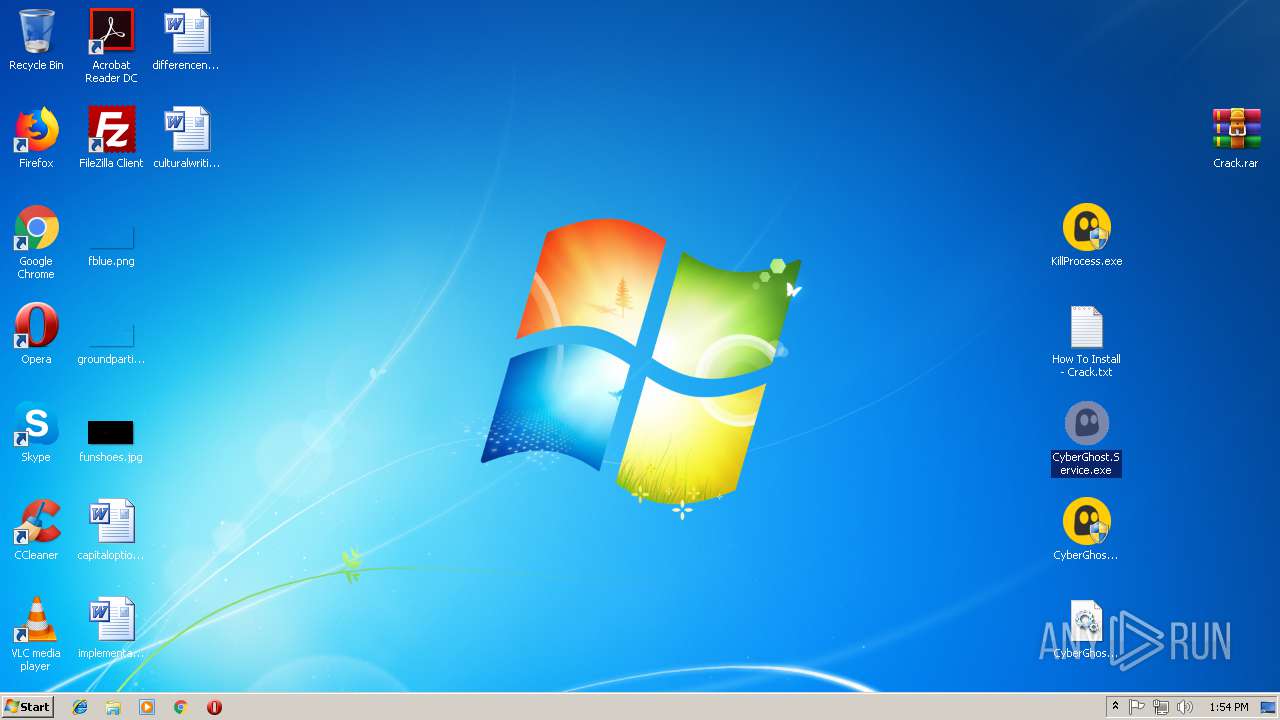
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | FB56A34435C8A80CCDB0B343F74BAEFE |
| SHA1: | 6E0FE4B7AF796DE05A6E797ED32FDAA315C1FDAA |
| SHA256: | B67DE258F0DC4FCF742DEAB8358A6162E1A49F6CDE98C5B7378BD572193B455E |
| SSDEEP: | 196608:4sJBxZ8eXhGmfKacvV85GCWd04JVxfafOyZ7yBPcr9si3hpHv/CdPl:lJBxZ8MGmCX2wCWdJaxS0rqi3rS3 |
MALICIOUS
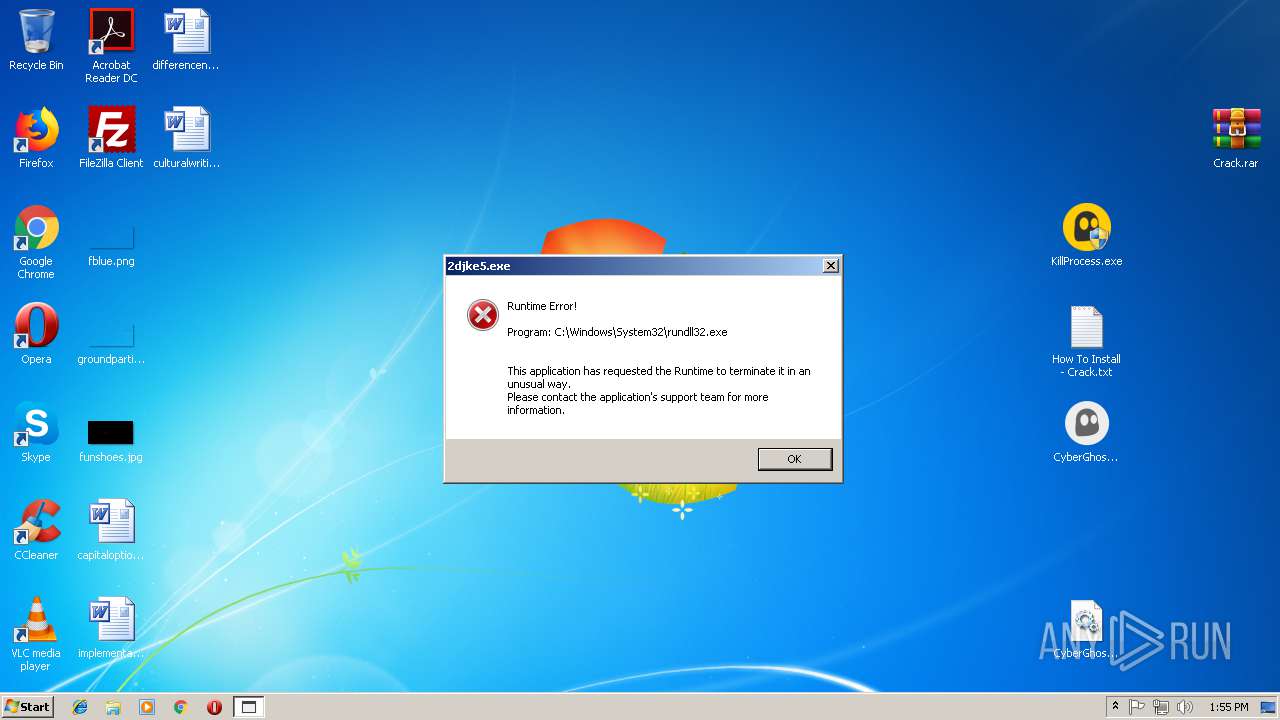
Application was dropped or rewritten from another process
- KillProcess.exe (PID: 2648)
- CyberGhost.exe (PID: 776)
- cyberghostclient.exe (PID: 3556)
- CyberGhost.exe (PID: 3480)
- KillProcess.exe (PID: 2912)
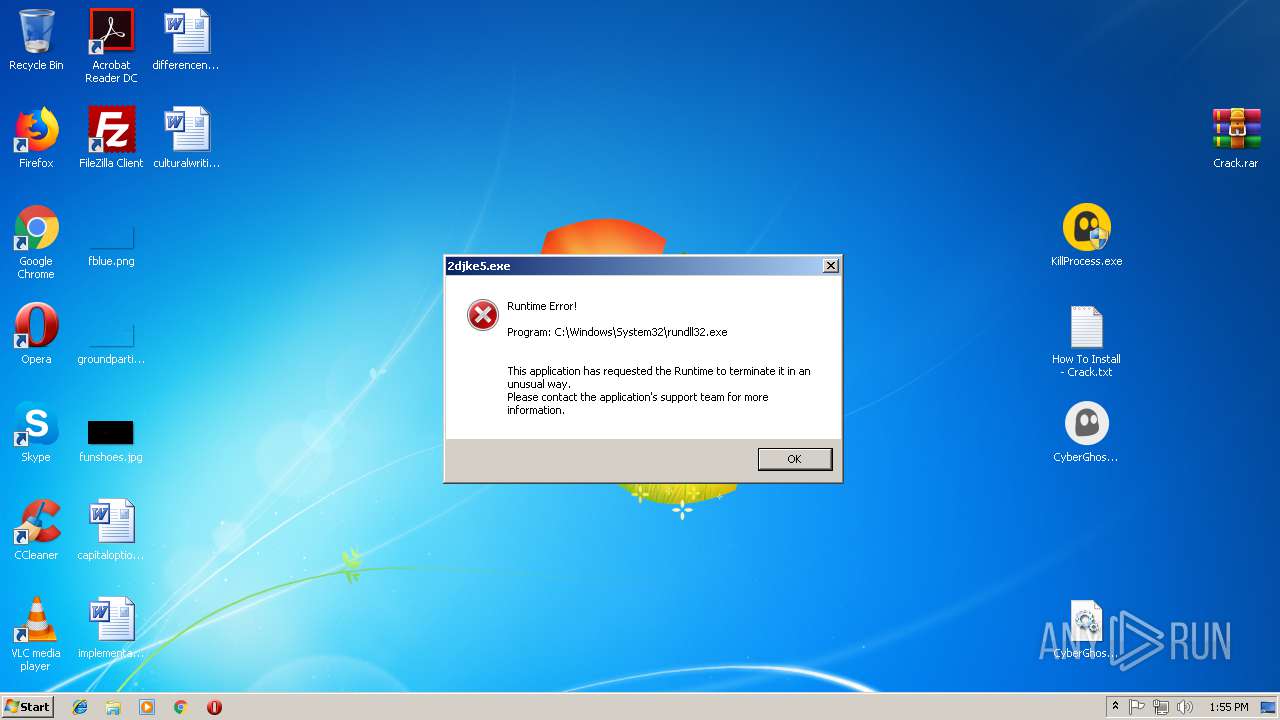
- 2djke5.exe (PID: 3648)
- csrss.exe (PID: 456)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 716)
Changes the autorun value in the registry
- cyberghostclient.exe (PID: 3556)
- csrss.exe (PID: 456)
Changes settings of System certificates
- CyberGhost.exe (PID: 3480)
SUSPICIOUS
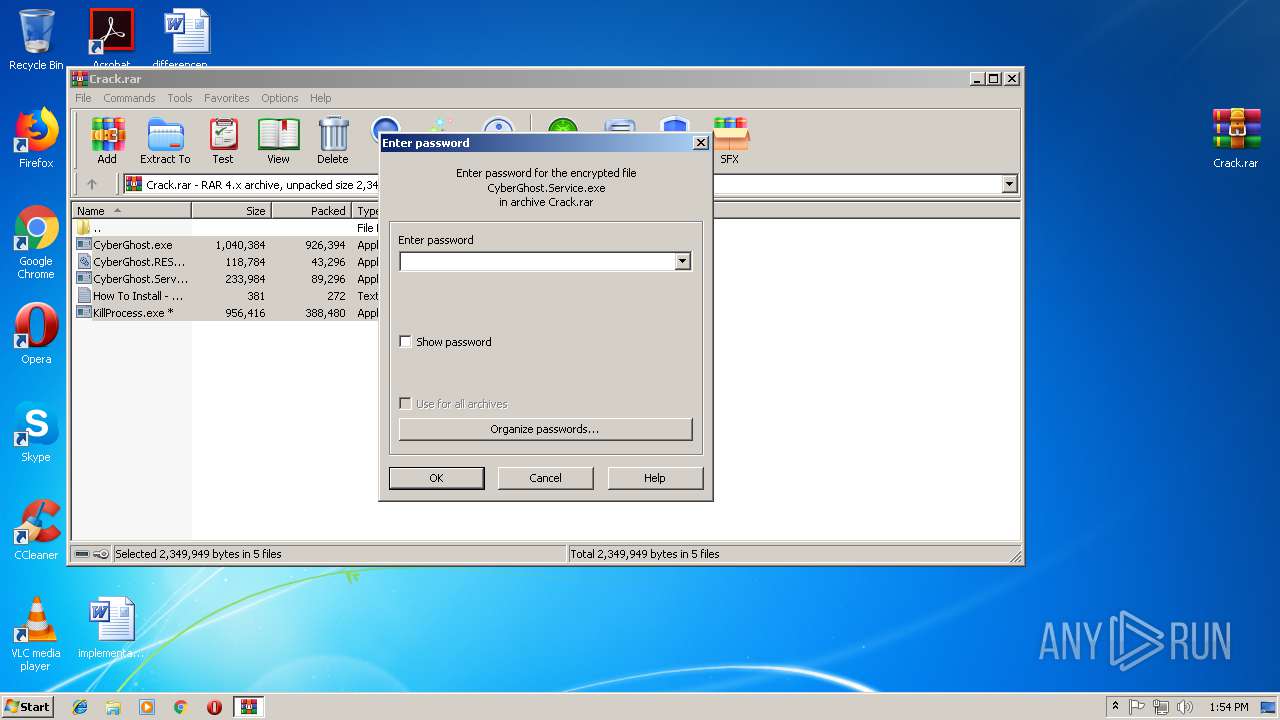
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3368)
- CyberGhost.exe (PID: 3480)
- cyberghostclient.exe (PID: 3556)
Creates files in the user directory
- CyberGhost.exe (PID: 3480)
- cyberghostclient.exe (PID: 3556)
Adds / modifies Windows certificates
- CyberGhost.exe (PID: 3480)
Starts itself from another location
- CyberGhost.exe (PID: 3480)
- cyberghostclient.exe (PID: 3556)
Creates files in the program directory
- dw20.exe (PID: 3484)
INFO
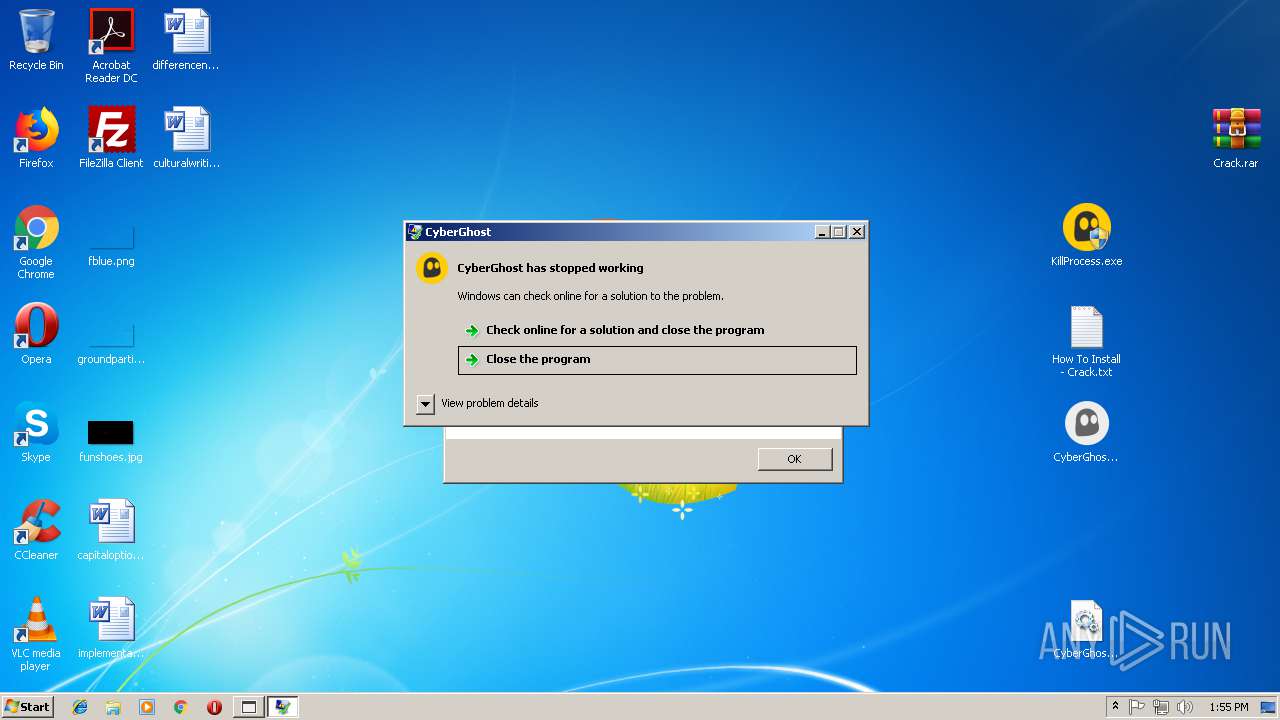
Application was crashed
- cyberghostclient.exe (PID: 3556)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
| CompressedSize: | 285 |
|---|---|
| UncompressedSize: | 299 |
| OperatingSystem: | Win32 |
| ModifyDate: | 2018:03:30 10:20:26 |
| PackingMethod: | Normal |
| ArchivedFileName: | How To Install - Crack.txt |
Total processes
48
Monitored processes
12
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | "C:\Users\admin\AppData\Roaming\csrss.exe" -reg "explorer.exe, C:\Program Files\cyberghostclient.exe" -proc 3556 C:\Program Files\cyberghostclient.exe | C:\Users\admin\AppData\Roaming\csrss.exe | cyberghostclient.exe | ||||||||||||
User: admin Company: CyberGhost S.A. Integrity Level: HIGH Description: CyberGhost Exit code: 0 Version: 6.5.0.3180 Modules
| |||||||||||||||
| 700 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\CyberGhost_6.5.0.3180_Incl_Crack.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 716 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe14_ Global\UsGthrCtrlFltPipeMssGthrPipe14 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
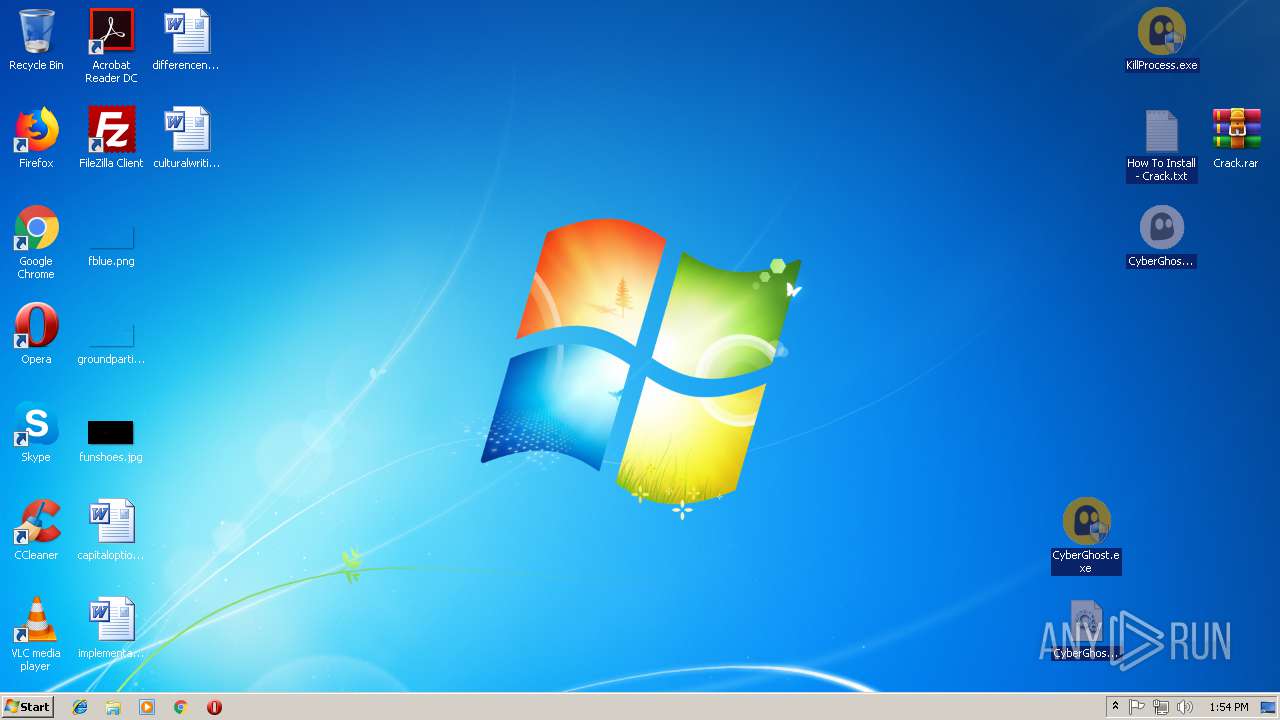
| 776 | "C:\Users\admin\Desktop\CyberGhost.exe" | C:\Users\admin\Desktop\CyberGhost.exe | — | explorer.exe | |||||||||||
User: admin Company: CyberGhost S.A. Integrity Level: MEDIUM Description: CyberGhost Exit code: 3221226540 Version: 6.5.0.3180 Modules
| |||||||||||||||
| 2648 | "C:\Users\admin\Desktop\KillProcess.exe" | C:\Users\admin\Desktop\KillProcess.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2912 | "C:\Users\admin\Desktop\KillProcess.exe" | C:\Users\admin\Desktop\KillProcess.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
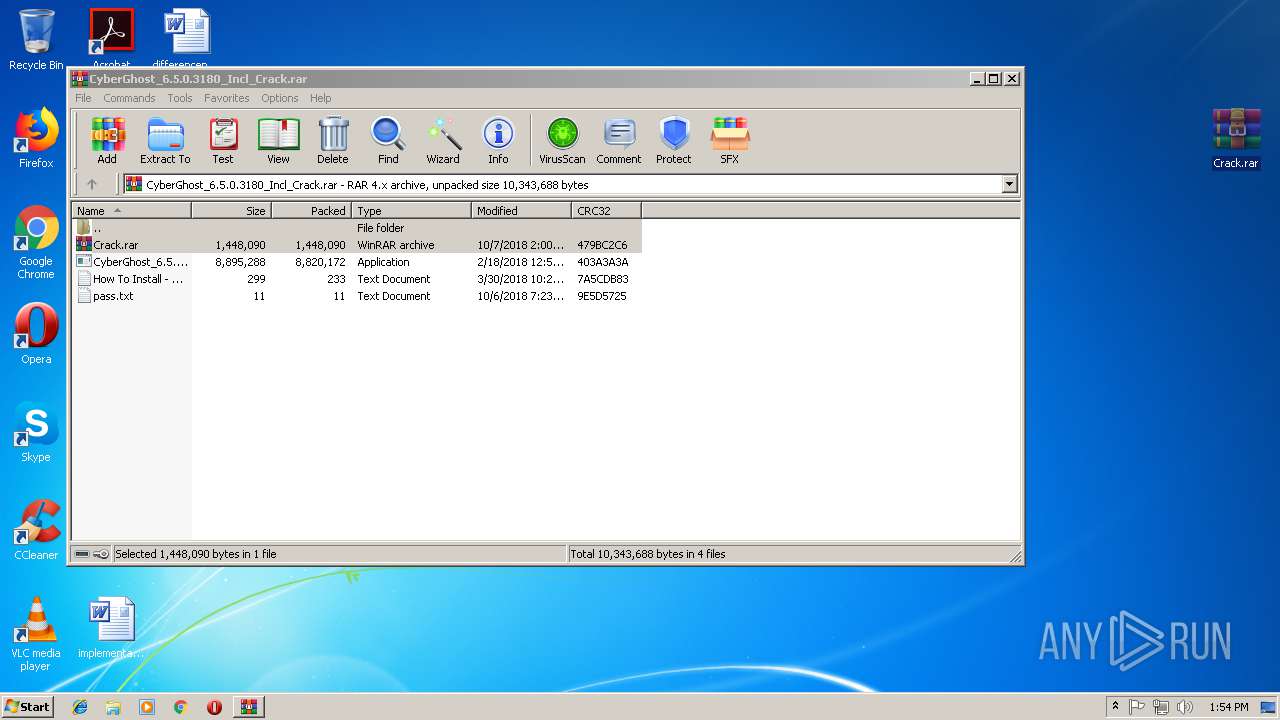
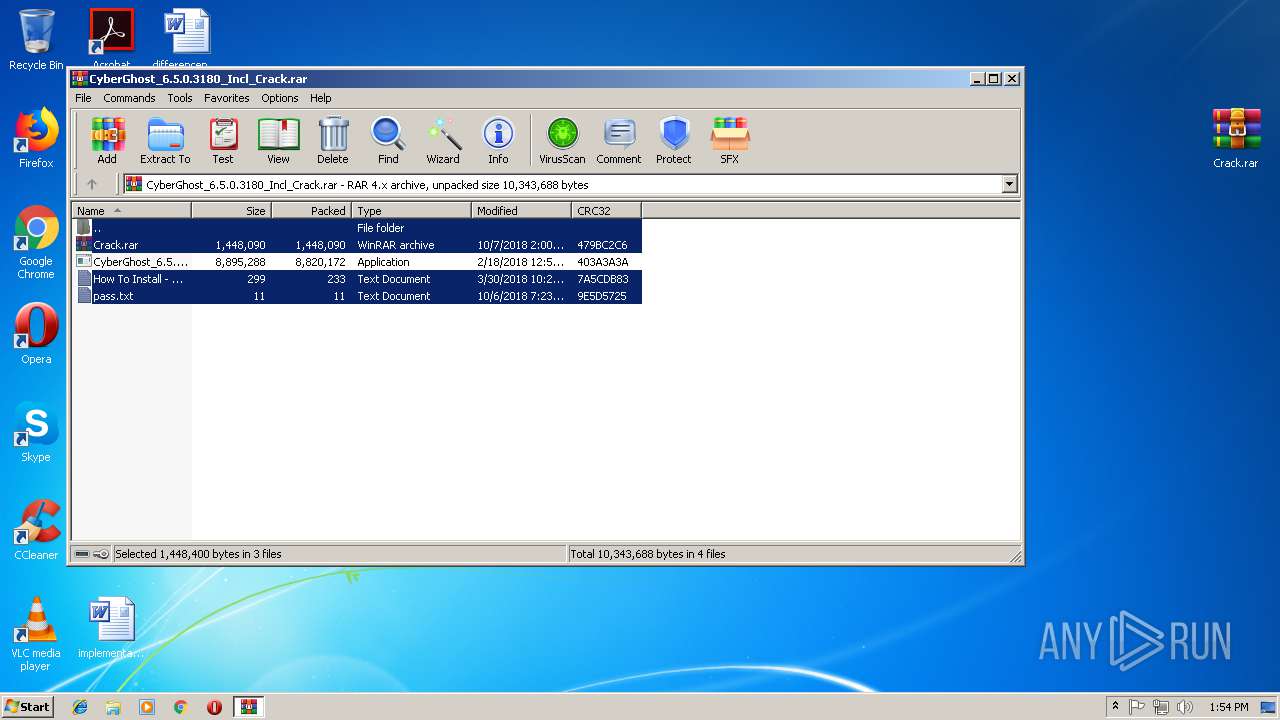
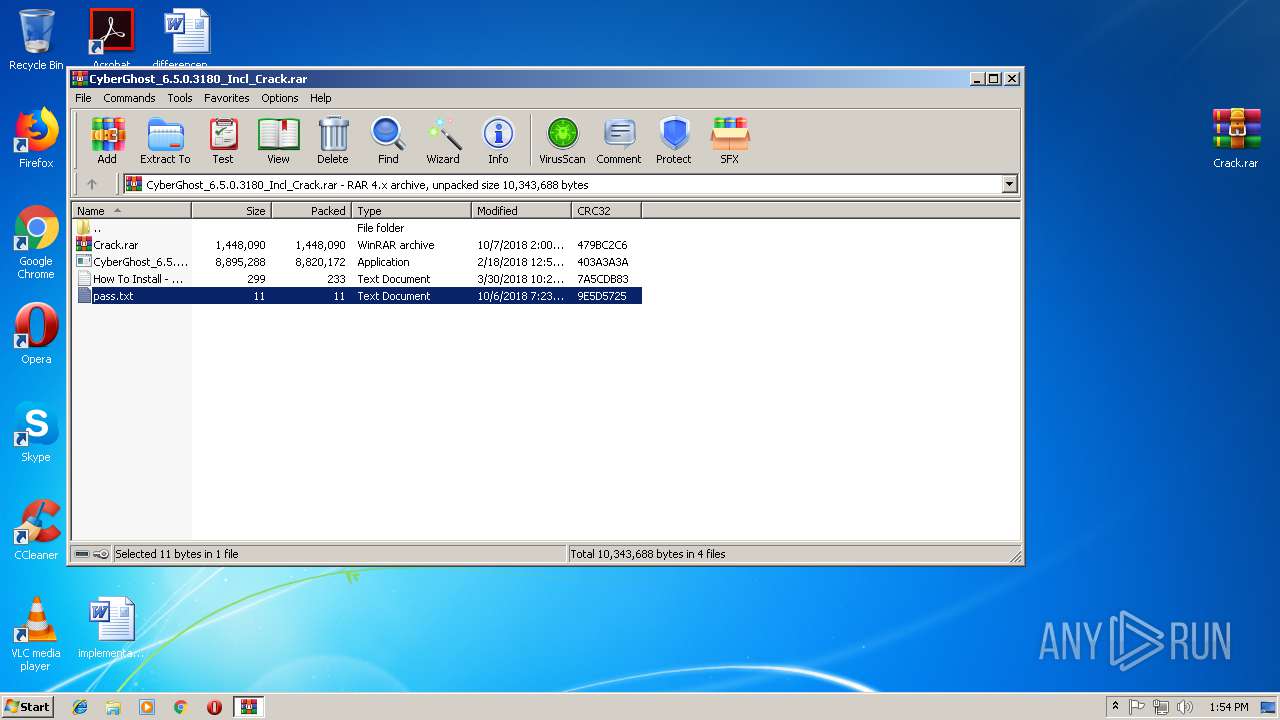
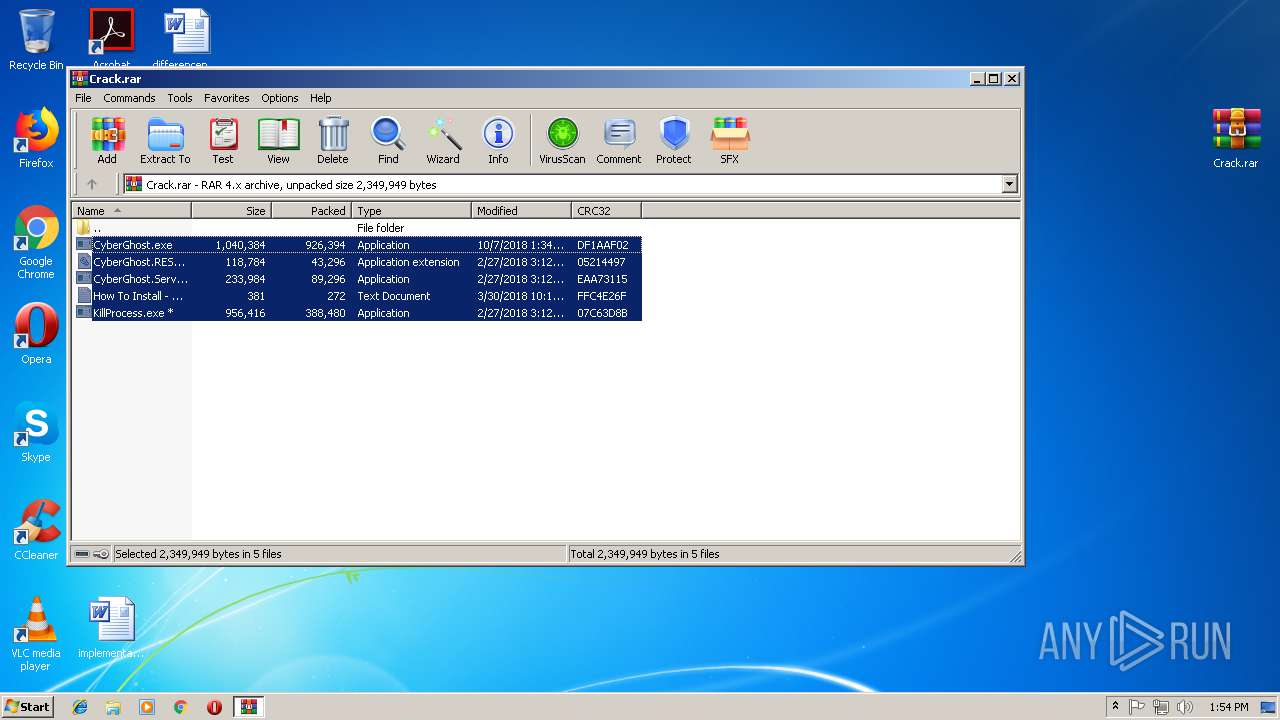
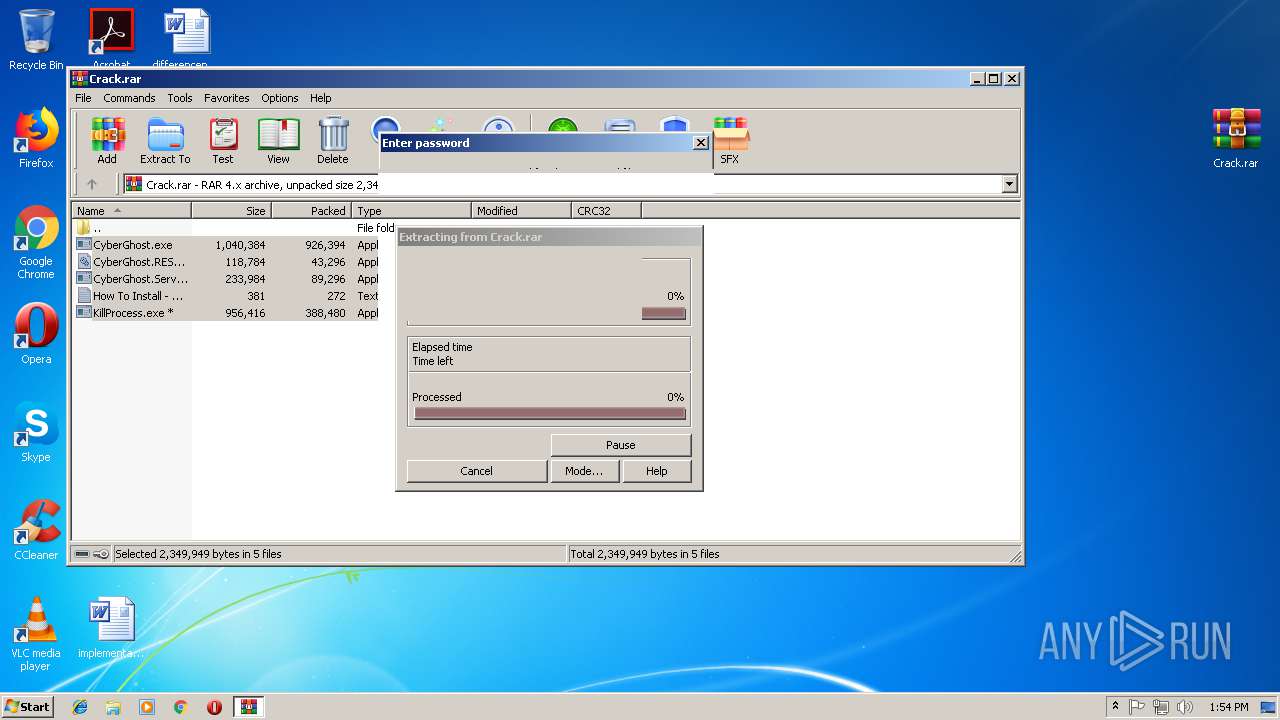
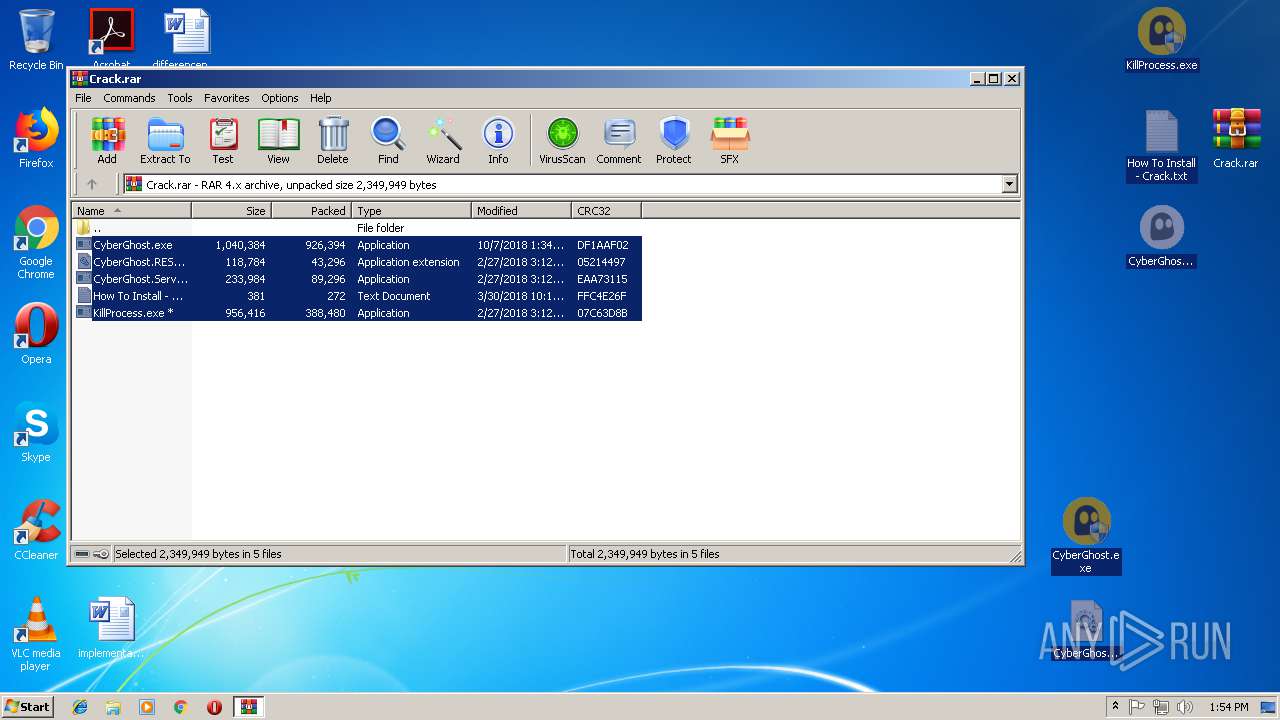
| 3368 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Crack.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
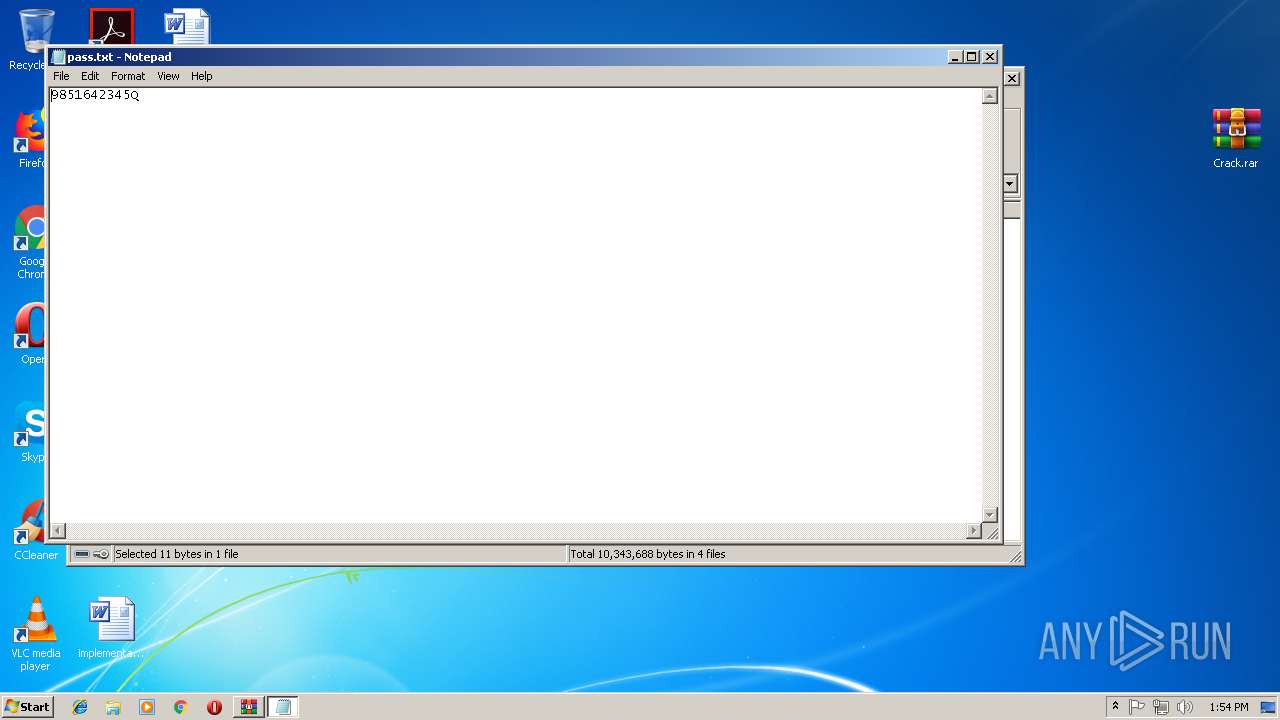
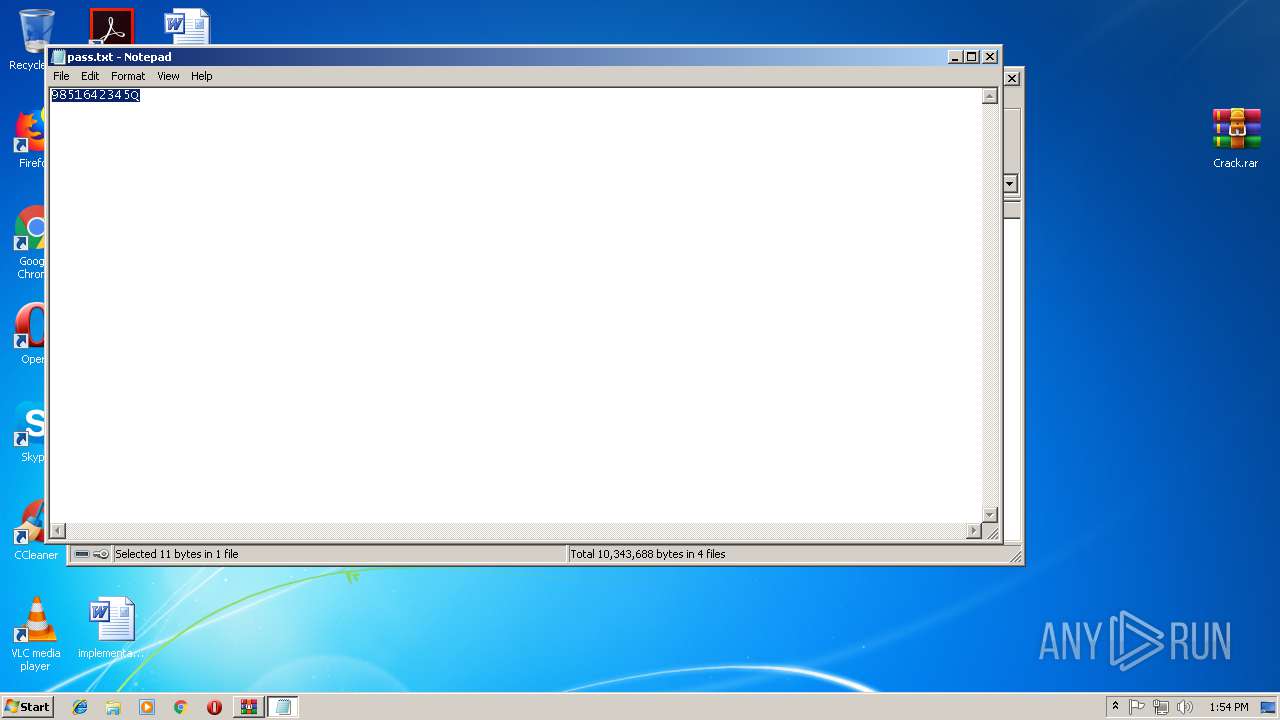
| 3372 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\Rar$DIa700.17060\pass.txt | C:\Windows\system32\NOTEPAD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3480 | "C:\Users\admin\Desktop\CyberGhost.exe" | C:\Users\admin\Desktop\CyberGhost.exe | explorer.exe | ||||||||||||
User: admin Company: CyberGhost S.A. Integrity Level: HIGH Description: CyberGhost Exit code: 0 Version: 6.5.0.3180 Modules
| |||||||||||||||
| 3484 | dw20.exe -x -s 744 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\dw20.exe | — | cyberghostclient.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Error Reporting Shim Exit code: 0 Version: 2.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
Total events
1 815
Read events
1 500
Write events
315
Delete events
0
Modification events
| (PID) Process: | (700) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (700) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (700) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (700) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\CyberGhost_6.5.0.3180_Incl_Crack.rar | |||
| (PID) Process: | (700) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (700) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (700) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (700) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3372) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosX |
Value: 44 | |||
| (PID) Process: | (3372) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosY |
Value: 44 | |||
Executable files
6
Suspicious files
3
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3368 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3368.18568\CyberGhost.exe | — | |
MD5:— | SHA256:— | |||
| 700 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa700.16255\Crack.rar | compressed | |
MD5:25B59F6AE8AC623722E220C45D3C6E4E | SHA256:F7927528B4ED9CE3CA74977CA5955533B221A1CCE8F3B72AC999AE805310CB63 | |||
| 3368 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3368.18568\CyberGhost.Service.exe | executable | |
MD5:B280BDEE5E98567E1296701F5CD34252 | SHA256:7ED107C69B944561BCC65BC19DB998129FABC5419A0D4FA2DC7674883C55A6A3 | |||
| 3368 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3368.18568\CyberGhost.RESTCommunicator.dll | executable | |
MD5:6AB3A38215FC8F0C30AF51360F192808 | SHA256:33CE014CAB9242EF7C775A9E8CA2AADD58555B68122BC9E6899362D615264C92 | |||
| 3368 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3368.18568\How To Install - Crack.txt | text | |
MD5:3D1C63F9F4A684541537F245218FEB98 | SHA256:FE4D2D7F045CE1CF86EE374AC8CA061D56A69C05E00A4A714DCF156F2F0281AC | |||
| 3480 | CyberGhost.exe | C:\Users\admin\AppData\Roaming\Microsoft\SystemCertificates\My\Certificates\E02357FC7708441D4B0BE5F371F4B28961870F70 | binary | |
MD5:DA6C793FB0533AF0139A6D76C9956547 | SHA256:BCEC4BFFD8EE03E0FDF1C1577EF4635AC08DB1F94CF07B0C406A6B3A171E9E1D | |||
| 3480 | CyberGhost.exe | C:\Program Files\cyberghostclient.exe | executable | |
MD5:B9B40E71F0D869BF70CD29578D38E008 | SHA256:96432D869C8870913AC10952907D1C9F135368A4B3CF0037EF90E8E98CDAA42A | |||
| 3480 | CyberGhost.exe | C:\Users\admin\AppData\Roaming\2djke5.exe | executable | |
MD5:80A0A3DA2F9717C0532CC760B1E7F746 | SHA256:58C69A35991347E174F2DDCB5C25D74C288DBD98212478C4983C0DBC1CCE0F52 | |||
| 3556 | cyberghostclient.exe | C:\Users\admin\AppData\Roaming\csrss.exe | executable | |
MD5:B9B40E71F0D869BF70CD29578D38E008 | SHA256:96432D869C8870913AC10952907D1C9F135368A4B3CF0037EF90E8E98CDAA42A | |||
| 3484 | dw20.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_cyberghostclient_eedd376d37f1e914459798683895e2514bf75640_0dc2e248\Report.wer | binary | |
MD5:CBA92E1CD585F17E5B7CA02B24A65CBD | SHA256:F0CD1958809FAF53827A4D464D48498D49CB6AB3C5D21CEE55A84CA8194F40F9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
2
Threats
3
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3480 | CyberGhost.exe | 88.99.66.31:443 | 2no.co | Hetzner Online GmbH | DE | malicious |
3480 | CyberGhost.exe | 159.65.182.87:443 | idontknow.moe | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
2no.co |
| whitelisted |
idontknow.moe |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | svchost.exe | Potentially Bad Traffic | SUSPICIOUS [PTsecurity] DNS bad file hosting service idontknow.moe |
2 ETPRO signatures available at the full report