| File name: | AppSuite-PDF (1).msi |
| Full analysis: | https://app.any.run/tasks/d878414d-5c1a-4580-a329-ab7cade5dc83 |
| Verdict: | Malicious activity |
| Analysis date: | September 03, 2025, 17:44:36 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: PDF Editor, Author: user, Keywords: Installer, Comments: This installer database contains the logic and data required to install PDF Editor., Template: Intel;1033, Revision Number: {E5D0BE0F-D538-42F3-A1E6-D51C7BBCF7BE}, Create Time/Date: Thu May 29 01:26:22 2025, Last Saved Time/Date: Thu May 29 01:26:22 2025, Number of Pages: 200, Number of Words: 10, Name of Creating Application: WiX Toolset (5.0.2.0), Security: 2 |
| MD5: | 08E42764571804AA3E27530B03DD5D99 |
| SHA1: | 82CA6C9C8B0CF59F8DCE178352360ABCB99637AC |
| SHA256: | B66D89EE13A48E9C8D4A7AA2E3E1CB2B79F0B95E4F74F4184B85628656281588 |
| SSDEEP: | 98304:3a/8rG6Wj9FLEMN/2q/4pL51eLFfFQHZposE2kUanIu3L6vKM0a/8rGguJKeacPm:x |
MALICIOUS
GENERIC has been found (auto)
- msiexec.exe (PID: 2532)
SUSPICIOUS
Reads security settings of Internet Explorer
- msiexec.exe (PID: 3636)
INFO
Creates files or folders in the user directory
- msiexec.exe (PID: 2532)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 2532)
Checks proxy server information
- msiexec.exe (PID: 2532)
- msiexec.exe (PID: 3636)
Reads the software policy settings
- msiexec.exe (PID: 2532)
- msiexec.exe (PID: 3636)
Reads the computer name
- msiexec.exe (PID: 1864)
- msiexec.exe (PID: 3636)
Executable content was dropped or overwritten
- msiexec.exe (PID: 2532)
- msiexec.exe (PID: 3636)
Checks supported languages
- msiexec.exe (PID: 3636)
- msiexec.exe (PID: 1864)
Create files in a temporary directory
- msiexec.exe (PID: 2532)
- msiexec.exe (PID: 3636)
Reads the machine GUID from the registry
- msiexec.exe (PID: 3636)
Disables trace logs
- msiexec.exe (PID: 3636)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
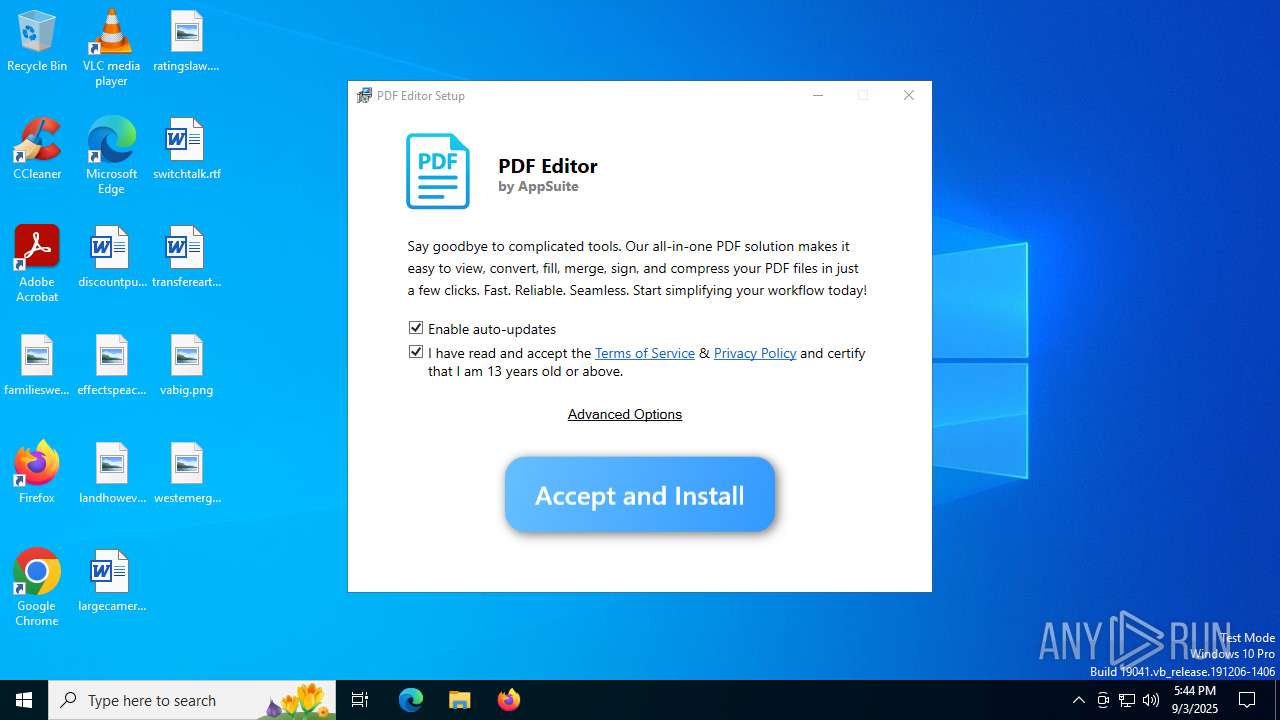
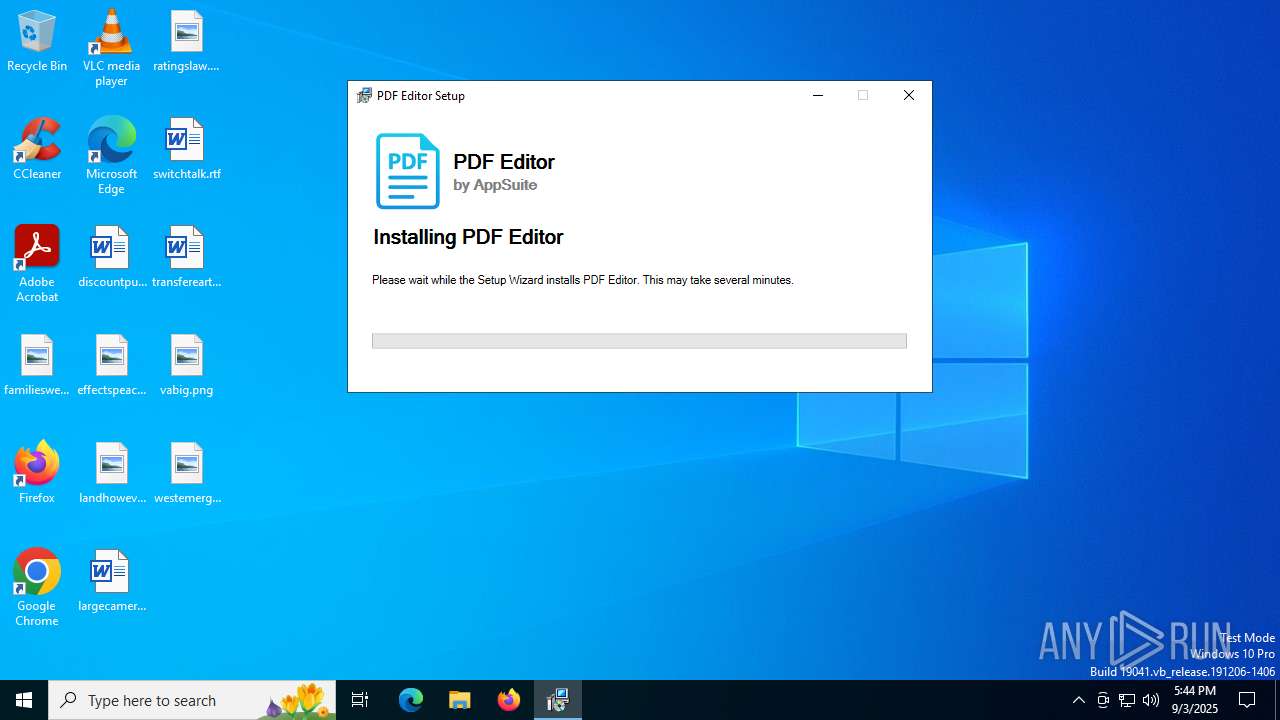
| Subject: | PDF Editor |
| Author: | user |
| Keywords: | Installer |
| Comments: | This installer database contains the logic and data required to install PDF Editor. |
| Template: | Intel;1033 |
| RevisionNumber: | {E5D0BE0F-D538-42F3-A1E6-D51C7BBCF7BE} |
| CreateDate: | 2025:05:29 01:26:22 |
| ModifyDate: | 2025:05:29 01:26:22 |
| Pages: | 200 |
| Words: | 10 |
| Software: | WiX Toolset (5.0.2.0) |
| Security: | Read-only recommended |
Total processes
139
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1864 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2200 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2532 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\AppSuite-PDF (1).msi" | C:\Windows\System32\msiexec.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3636 | C:\Windows\syswow64\MsiExec.exe -Embedding A9F22A75441CA2698FB69A1CFACD4A48 U | C:\Windows\SysWOW64\msiexec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6392 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
6 498
Read events
6 484
Write events
14
Delete events
0
Modification events
| (PID) Process: | (3636) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\MsiExec_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3636) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\MsiExec_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (3636) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\MsiExec_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3636) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\MsiExec_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (3636) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\MsiExec_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (3636) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\MsiExec_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3636) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\MsiExec_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3636) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\MsiExec_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3636) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\MsiExec_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (3636) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\MsiExec_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
7
Suspicious files
4
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2532 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\FE17BEC2A573BC9AE36869D0274FFA19_6DA81F04C5F9EAD2CD0268808FCE61E1 | binary | |
MD5:E33FE388A4A0B738E59AB3112C3EDB9E | SHA256:664C4F0C1BDFBBC83EDF304BEE37F36D32D8B73858BF78F7FE11BC33E4FA5292 | |||
| 3636 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI17207\EmbeddedUI.config | xml | |
MD5:C9C40AF1656F8531EAA647CACEB1E436 | SHA256:1A67F60962CA1CBF19873B62A8518EFE8C701A09CD609AF4C50ECC7F0B468BB8 | |||
| 3636 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI17207\WixSharp.dll | executable | |
MD5:CA64E60B4874854FF33BF6CE8619CEBB | SHA256:846A4B3FFBD090BBC659A183BE01D3A7F833D34E604DC64D607EF29577545BBF | |||
| 3636 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\tmpCE28.tmp | xml | |
MD5:06B11E5EEEB4239E332D0BB81598B9F3 | SHA256:E2B268346639C165AE970F4FB35B2C0DDDC1954AB862F31DE58D537CB3416CF1 | |||
| 3636 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI17207\WixToolset.Mba.Core.dll | executable | |
MD5:1E43E0952B5CC4C73245ACAD8114EE63 | SHA256:32C39201104A304E74244A7B8D6BEF7DC82C91324BC9B473EDA8163337291692 | |||
| 3636 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI17207\WixSharp.UI.dll | executable | |
MD5:19769632E246C6726BF03AB45027609D | SHA256:4856C78885D53CA633E36CC3A76BE435B2DF65B5EBED1510D1119CD1C241519B | |||
| 2532 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\248DDD9FCF61002E219645695E3FFC98_8CA320F42C1C527BA68EC7341846F93C | binary | |
MD5:C0D5EADAAC4667BD2B403BA24243CD21 | SHA256:AD2A0279B723FDE2B929281B4A8F133F64BB90280B4F3B4058FA9052CA0F106D | |||
| 2532 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\FE17BEC2A573BC9AE36869D0274FFA19_6DA81F04C5F9EAD2CD0268808FCE61E1 | binary | |
MD5:7E5E9912DE7A985FF6257B5E3005DE2C | SHA256:EC0BDEA0FCC54BE0A302CAC5A2513186CCD5A9E1BD9DE7C8DD81CE1773141571 | |||
| 2532 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\248DDD9FCF61002E219645695E3FFC98_8CA320F42C1C527BA68EC7341846F93C | binary | |
MD5:85B47DD0EA8E040DC7C8CD6A064F39FA | SHA256:AD3B20701097447472787FF268EDB88B81B3CD8AE0CA6EC0B66C85C1D068E72E | |||
| 2532 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI17207\WixSharp.UI.CA.dll | executable | |
MD5:D3CF446C9F3F258030FD984DD81D5826 | SHA256:B1302D4BFE97A7B1E791C880433148D7BAD4841DFAB54364081C0292336B32A7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
21
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2532 | msiexec.exe | GET | 200 | 18.173.205.57:80 | http://ocsps.ssl.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQg3SSkKA74hABkhmlBtJTz8w3hlAQU%2BWC71OPVNPa49QaAJadz20ZpqJ4CEEJLalPOx2YUHCpjsaUcQQQ%3D | unknown | — | — | whitelisted |
2532 | msiexec.exe | GET | 200 | 18.173.205.57:80 | http://ocsps.ssl.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSoEwb5tith0jIBy9frSyNGB1lsAAQUNr1J%2FzEs669qQP6ZwBbtuvxI3V8CED%2FrrkGJaIXpH9sg4JUMYFQ%3D | unknown | — | — | whitelisted |
72 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5980 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5980 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3876 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2532 | msiexec.exe | 18.173.205.57:80 | ocsps.ssl.com | — | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
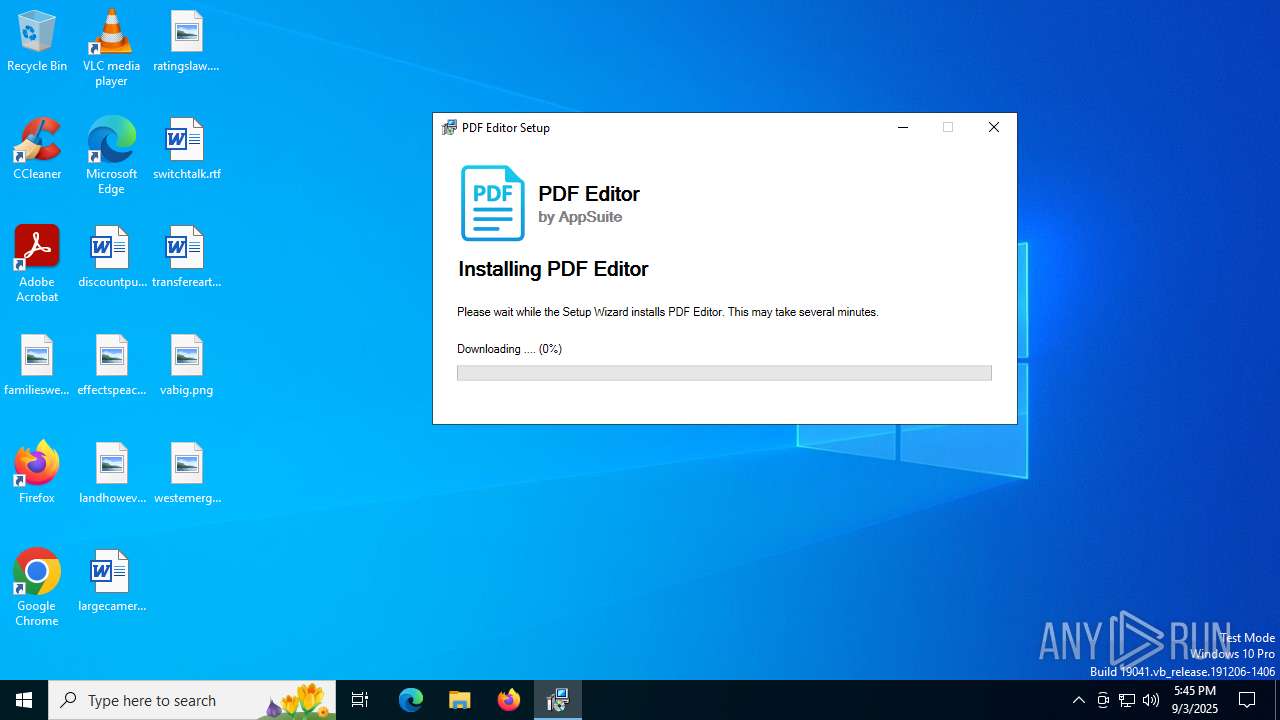
3636 | msiexec.exe | 3.160.150.107:443 | inst.productivity-tools.ai | — | US | malicious |
72 | svchost.exe | 40.126.32.72:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
72 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
ocsps.ssl.com |
| whitelisted |
inst.productivity-tools.ai |
| malicious |
vault.appsuites.ai |
| malicious |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |