| File name: | b66a60c1bad86476d28800fba424e63e6d1672e7fa6d68975a321ce456943de7 |
| Full analysis: | https://app.any.run/tasks/f2873630-bb0f-4fe9-b792-f84963c57247 |
| Verdict: | Malicious activity |
| Analysis date: | August 12, 2022, 18:35:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 3FF2243ED586414B2F9182F3AEC53FC9 |
| SHA1: | 722E23ACB38317AB79157017F0F905A52CBD0592 |
| SHA256: | B66A60C1BAD86476D28800FBA424E63E6D1672E7FA6D68975A321CE456943DE7 |
| SSDEEP: | 98304:2qzJy6+6efPk4OCgT/3sBvUGp819PY5ZWambTd:j/efPo65+1hY7Wtnd |
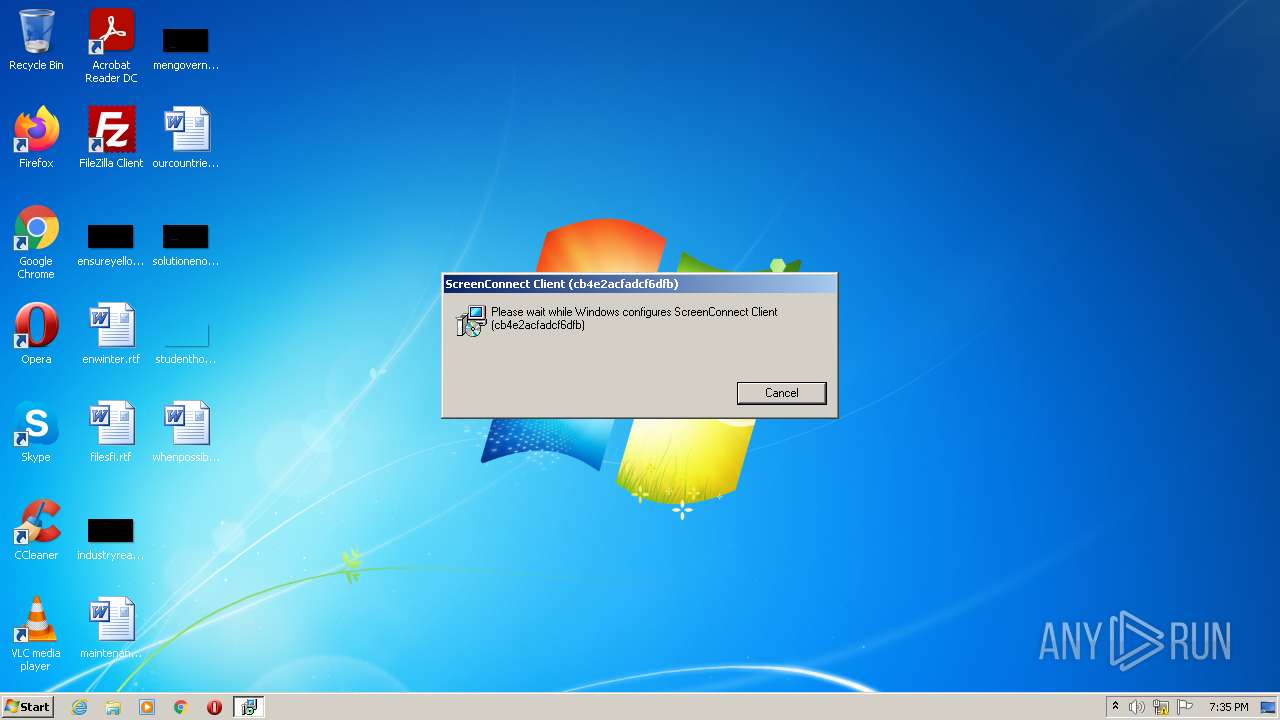
MALICIOUS
Drops executable file immediately after starts
- msiexec.exe (PID: 3792)
- rundll32.exe (PID: 4008)
- msiexec.exe (PID: 4084)
- ScreenConnect.ClientService.exe (PID: 3152)
- rundll32.exe (PID: 2532)
Loads dropped or rewritten executable
- ScreenConnect.WindowsClient.exe (PID: 3640)
- ScreenConnect.ClientService.exe (PID: 3152)
- rundll32.exe (PID: 4008)
- ScreenConnect.WindowsClient.exe (PID: 3304)
- rundll32.exe (PID: 2532)
- ScreenConnect.WindowsClient.exe (PID: 3816)
- ScreenConnect.ClientService.exe (PID: 2328)
- ScreenConnect.WindowsClient.exe (PID: 3204)
Application was dropped or rewritten from another process
- ScreenConnect.WindowsClient.exe (PID: 3640)
- ScreenConnect.ClientService.exe (PID: 3152)
- ScreenConnect.WindowsClient.exe (PID: 3304)
- ScreenConnect.ClientSetup.exe (PID: 2672)
- ScreenConnect.WindowsClient.exe (PID: 3204)
- ScreenConnect.WindowsClient.exe (PID: 3816)
- ScreenConnect.ClientService.exe (PID: 2328)
Deletes the SafeBoot registry key
- msiexec.exe (PID: 4084)
SUSPICIOUS
Executable content was dropped or overwritten
- b66a60c1bad86476d28800fba424e63e6d1672e7fa6d68975a321ce456943de7.exe (PID: 2176)
- msiexec.exe (PID: 3792)
- rundll32.exe (PID: 4008)
- msiexec.exe (PID: 4084)
- ScreenConnect.ClientService.exe (PID: 3152)
- ScreenConnect.ClientSetup.exe (PID: 2672)
- rundll32.exe (PID: 2532)
Checks supported languages
- b66a60c1bad86476d28800fba424e63e6d1672e7fa6d68975a321ce456943de7.exe (PID: 2176)
- MsiExec.exe (PID: 3400)
- msiexec.exe (PID: 4084)
- MsiExec.exe (PID: 1856)
- ScreenConnect.ClientService.exe (PID: 3152)
- ScreenConnect.WindowsClient.exe (PID: 3640)
- MsiExec.exe (PID: 1812)
- ScreenConnect.ClientSetup.exe (PID: 2672)
- ScreenConnect.WindowsClient.exe (PID: 3304)
- MsiExec.exe (PID: 3292)
- ScreenConnect.WindowsClient.exe (PID: 3204)
- ScreenConnect.ClientService.exe (PID: 2328)
- ScreenConnect.WindowsClient.exe (PID: 3816)
Reads the computer name
- b66a60c1bad86476d28800fba424e63e6d1672e7fa6d68975a321ce456943de7.exe (PID: 2176)
- msiexec.exe (PID: 4084)
- MsiExec.exe (PID: 3400)
- MsiExec.exe (PID: 1856)
- ScreenConnect.WindowsClient.exe (PID: 3640)
- MsiExec.exe (PID: 1812)
- ScreenConnect.ClientService.exe (PID: 3152)
- ScreenConnect.ClientSetup.exe (PID: 2672)
- ScreenConnect.WindowsClient.exe (PID: 3304)
- ScreenConnect.ClientService.exe (PID: 2328)
- ScreenConnect.WindowsClient.exe (PID: 3204)
- ScreenConnect.WindowsClient.exe (PID: 3816)
- MsiExec.exe (PID: 3292)
Drops a file with a compile date too recent
- msiexec.exe (PID: 3792)
- rundll32.exe (PID: 4008)
- msiexec.exe (PID: 4084)
- ScreenConnect.ClientService.exe (PID: 3152)
- rundll32.exe (PID: 2532)
Reads Windows owner or organization settings
- msiexec.exe (PID: 3792)
- msiexec.exe (PID: 4084)
Reads the Windows organization settings
- msiexec.exe (PID: 3792)
- msiexec.exe (PID: 4084)
Executed as Windows Service
- vssvc.exe (PID: 2984)
- ScreenConnect.ClientService.exe (PID: 3152)
- ScreenConnect.ClientService.exe (PID: 2328)
Reads Environment values
- vssvc.exe (PID: 2984)
Changes default file association
- msiexec.exe (PID: 4084)
Creates a directory in Program Files
- msiexec.exe (PID: 4084)
Creates files in the program directory
- ScreenConnect.ClientService.exe (PID: 3152)
- ScreenConnect.ClientService.exe (PID: 2328)
Reads CPU info
- ScreenConnect.WindowsClient.exe (PID: 3304)
- ScreenConnect.WindowsClient.exe (PID: 3816)
INFO
Checks supported languages
- msiexec.exe (PID: 3792)
- rundll32.exe (PID: 4008)
- vssvc.exe (PID: 2984)
- msiexec.exe (PID: 2472)
- rundll32.exe (PID: 2532)
Reads the computer name
- msiexec.exe (PID: 3792)
- rundll32.exe (PID: 4008)
- vssvc.exe (PID: 2984)
- msiexec.exe (PID: 2472)
- rundll32.exe (PID: 2532)
Application launched itself
- msiexec.exe (PID: 4084)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 3400)
- MsiExec.exe (PID: 1856)
- MsiExec.exe (PID: 1812)
- MsiExec.exe (PID: 3292)
- msiexec.exe (PID: 4084)
Creates files in the program directory
- msiexec.exe (PID: 4084)
Creates a software uninstall entry
- msiexec.exe (PID: 4084)
Searches for installed software
- msiexec.exe (PID: 4084)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 EXE PECompact compressed (generic) (53.4) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (35.5) |
| .exe | | | Win32 Executable (generic) (5.8) |
| .exe | | | Generic Win/DOS Executable (2.5) |
| .exe | | | DOS Executable Generic (2.5) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x1499 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 4781056 |
| CodeSize: | 48640 |
| LinkerVersion: | 14.16 |
| PEType: | PE32 |
| TimeStamp: | 2022:02:04 06:49:14+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 04-Feb-2022 05:49:14 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 04-Feb-2022 05:49:14 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000BCE6 | 0x0000BE00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.62079 |
.rdata | 0x0000D000 | 0x00005D68 | 0x00005E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.8737 |
.data | 0x00013000 | 0x000011E4 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.25909 |
.rsrc | 0x00015000 | 0x00487DEC | 0x00487E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.40702 |
.reloc | 0x0049D000 | 0x00000ECC | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.31471 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | Latin 1 / Western European | English - United States | RT_MANIFEST |
SCREENCONNECT.CORE, VERSION=22.6.8531.8234, CULTURE=NEUTRAL, PUBLICKEYTOKEN=4B14C015C87C1AD8 | 6.00122 | 457216 | Latin 1 / Western European | UNKNOWN | FILES |
SCREENCONNECT.WINDOWS, VERSION=22.6.8531.8234, CULTURE=NEUTRAL, PUBLICKEYTOKEN=4B14C015C87C1AD8 | 6.69357 | 1672192 | Latin 1 / Western European | UNKNOWN | FILES |
SCREENCONNECT.WINDOWSINSTALLER, VERSION=22.6.8531.8234, CULTURE=NEUTRAL, PUBLICKEYTOKEN=4B14C015C87C1AD8 | 5.76353 | 71168 | Latin 1 / Western European | UNKNOWN | FILES |
_ENTRYPOINT | 7.81492 | 2543240 | Latin 1 / Western European | UNKNOWN | FILES |
_RESOLVER | 3.8513 | 5632 | Latin 1 / Western European | UNKNOWN | FILES |
Imports
KERNEL32.dll |
OLEAUT32.dll |
mscoree.dll |
Total processes
54
Monitored processes
18
Malicious processes
11
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1812 | C:\Windows\system32\MsiExec.exe -Embedding 0EFE86D70BC08CCFC0B2D7E1D3C454C1 E Global\MSI0000 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1856 | C:\Windows\system32\MsiExec.exe -Embedding 81EEE927748E38565EF45134B1A08174 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2176 | "C:\Users\admin\AppData\Local\Temp\b66a60c1bad86476d28800fba424e63e6d1672e7fa6d68975a321ce456943de7.exe" | C:\Users\admin\AppData\Local\Temp\b66a60c1bad86476d28800fba424e63e6d1672e7fa6d68975a321ce456943de7.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2328 | "C:\Program Files\ScreenConnect Client (cb4e2acfadcf6dfb)\ScreenConnect.ClientService.exe" "?e=Access&y=Guest&h=instance-aab535-relay.screenconnect.com&p=443&s=9e3f469e-5762-4d1f-8f99-9cf9717f82aa&k=BgIAAACkAABSU0ExAAgAAAEAAQC5QfJPxEn43Gi67eGAyseFbyi8bDkKOFHFqab7QyWH3i%2fS1H3It0o4e%2b4S%2fmlx34%2bXzDFAUzWFN%2b0qqHVc%2fAOtAoABZ11qtn%2bPBGyyxOPPnutPeO%2fZRXsndWPdK3L4fn%2fWTfEhVV%2fLmMPZK5vNIk2k6%2fiB7E%2fTfvluQv0t%2fLLRKcPsSXdELEw5vAHhJenBj43bZ72ATwQakq5od%2bMGsQzZFWTjj6j70MZlBM8PD2Aylq7DCk1z919sEv1eUx3YfzEm85R2YJOLS%2fvy%2b668LN2bHlsyd%2foJB9b9I86LIiEZVtqvtDkxfLjtQrac02X9EDfq%2fytcu11ZpnLmTjTZfLyw&t=&c=CroixBleue&c=&c=&c=&c=&c=&c=&c=" | C:\Program Files\ScreenConnect Client (cb4e2acfadcf6dfb)\ScreenConnect.ClientService.exe | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Version: 22.6.8722.8249 Modules
| |||||||||||||||
| 2472 | "C:\Windows\System32\msiexec.exe" /i "C:\Windows\TEMP\setup.msi" | C:\Windows\System32\msiexec.exe | — | ScreenConnect.ClientSetup.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2532 | rundll32.exe "C:\Windows\Installer\MSIFDE1.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_916984 26 ScreenConnect.InstallerActions!ScreenConnect.ClientInstallerActions.FixupServiceArguments | C:\Windows\system32\rundll32.exe | MsiExec.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2672 | "C:\Windows\TEMP\ScreenConnect\22.6.8531.8234\ScreenConnect.ClientSetup.exe" | C:\Windows\TEMP\ScreenConnect\22.6.8531.8234\ScreenConnect.ClientSetup.exe | ScreenConnect.ClientService.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 2984 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3152 | "C:\Program Files\ScreenConnect Client (cb4e2acfadcf6dfb)\ScreenConnect.ClientService.exe" "?e=Access&y=Guest&h=instance-aab535-relay.screenconnect.com&p=443&s=9e3f469e-5762-4d1f-8f99-9cf9717f82aa&k=BgIAAACkAABSU0ExAAgAAAEAAQC5QfJPxEn43Gi67eGAyseFbyi8bDkKOFHFqab7QyWH3i%2fS1H3It0o4e%2b4S%2fmlx34%2bXzDFAUzWFN%2b0qqHVc%2fAOtAoABZ11qtn%2bPBGyyxOPPnutPeO%2fZRXsndWPdK3L4fn%2fWTfEhVV%2fLmMPZK5vNIk2k6%2fiB7E%2fTfvluQv0t%2fLLRKcPsSXdELEw5vAHhJenBj43bZ72ATwQakq5od%2bMGsQzZFWTjj6j70MZlBM8PD2Aylq7DCk1z919sEv1eUx3YfzEm85R2YJOLS%2fvy%2b668LN2bHlsyd%2foJB9b9I86LIiEZVtqvtDkxfLjtQrac02X9EDfq%2fytcu11ZpnLmTjTZfLyw&t=&c=CroixBleue&c=&c=&c=&c=&c=&c=&c=" | C:\Program Files\ScreenConnect Client (cb4e2acfadcf6dfb)\ScreenConnect.ClientService.exe | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Version: 22.6.8531.8234 Modules
| |||||||||||||||
| 3204 | "C:\Program Files\ScreenConnect Client (cb4e2acfadcf6dfb)\ScreenConnect.WindowsClient.exe" "RunRole" "f4b92ae2-b73e-4799-8bab-df64e8b7b5b3" "User" | C:\Program Files\ScreenConnect Client (cb4e2acfadcf6dfb)\ScreenConnect.WindowsClient.exe | — | ScreenConnect.ClientService.exe | |||||||||||
User: admin Company: ScreenConnect Software Integrity Level: MEDIUM Description: ScreenConnect Client Exit code: 0 Version: 22.6.8722.8249 Modules
| |||||||||||||||
Total events
8 378
Read events
7 862
Write events
390
Delete events
126
Modification events
| (PID) Process: | (2176) b66a60c1bad86476d28800fba424e63e6d1672e7fa6d68975a321ce456943de7.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2176) b66a60c1bad86476d28800fba424e63e6d1672e7fa6d68975a321ce456943de7.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2176) b66a60c1bad86476d28800fba424e63e6d1672e7fa6d68975a321ce456943de7.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2176) b66a60c1bad86476d28800fba424e63e6d1672e7fa6d68975a321ce456943de7.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (4084) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 400000000000000056D497447AAED801F40F00005C0B0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4084) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 400000000000000056D497447AAED801F40F00005C0B0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4084) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 69 | |||
| (PID) Process: | (4084) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 40000000000000002E96DA447AAED801F40F00005C0B0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4084) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000002E96DA447AAED801F40F0000C8010000E80300000100000000000000000000005BF6B0083F0B244AA58FE9682E4A0CDD0000000000000000 | |||
| (PID) Process: | (2984) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000E25ADF447AAED801A80B0000580C0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
49
Suspicious files
16
Text files
17
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4084 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 2176 | b66a60c1bad86476d28800fba424e63e6d1672e7fa6d68975a321ce456943de7.exe | C:\Users\admin\AppData\Local\Temp\setup.msi | executable | |
MD5:— | SHA256:— | |||
| 4084 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DFAF99D05AE6524AEC.TMP | gmc | |
MD5:— | SHA256:— | |||
| 4084 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:— | SHA256:— | |||
| 3792 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI87AF.tmp | executable | |
MD5:9205182C79B151346449CDB22EE42847 | SHA256:2827E52652A490E7F4AE6C62D97AC0543514D5D3D3A88CBE590897EFDBAB51A5 | |||
| 4008 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSI87AF.tmp-\Microsoft.Deployment.WindowsInstaller.dll | executable | |
MD5:5EF88919012E4A3D8A1E2955DC8C8D81 | SHA256:3E54286E348EBD3D70EAED8174CCA500455C3E098CDD1FCCB167BC43D93DB29D | |||
| 4084 | msiexec.exe | C:\Windows\Installer\d9be3.msi | executable | |
MD5:— | SHA256:— | |||
| 4084 | msiexec.exe | C:\Windows\Installer\MSI9F9C.tmp | binary | |
MD5:— | SHA256:— | |||
| 4084 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{08b0f65b-0b3f-4a24-a58f-e9682e4a0cdd}_OnDiskSnapshotProp | binary | |
MD5:— | SHA256:— | |||
| 4008 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSI87AF.tmp-\CustomAction.config | xml | |
MD5:EB99EE012EB63C162EEBC1DF3A15990B | SHA256:C5045C2D482F71215877EB668264EE47E1415792457F19A5A55651C3554CC7CD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
1
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3152 | ScreenConnect.ClientService.exe | 145.40.105.156:443 | instance-aab535-relay.screenconnect.com | — | NL | unknown |
2328 | ScreenConnect.ClientService.exe | 145.40.105.156:443 | instance-aab535-relay.screenconnect.com | — | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
instance-aab535-relay.screenconnect.com |
| unknown |
Threats
1 ETPRO signatures available at the full report