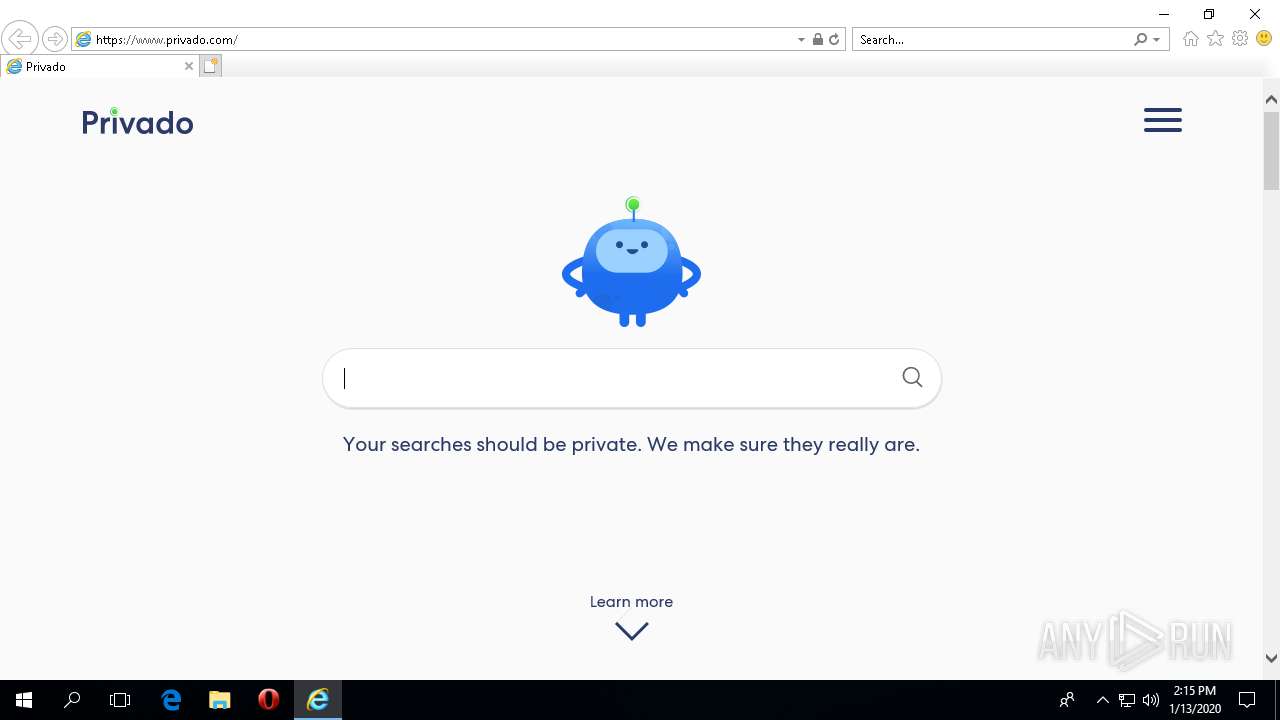
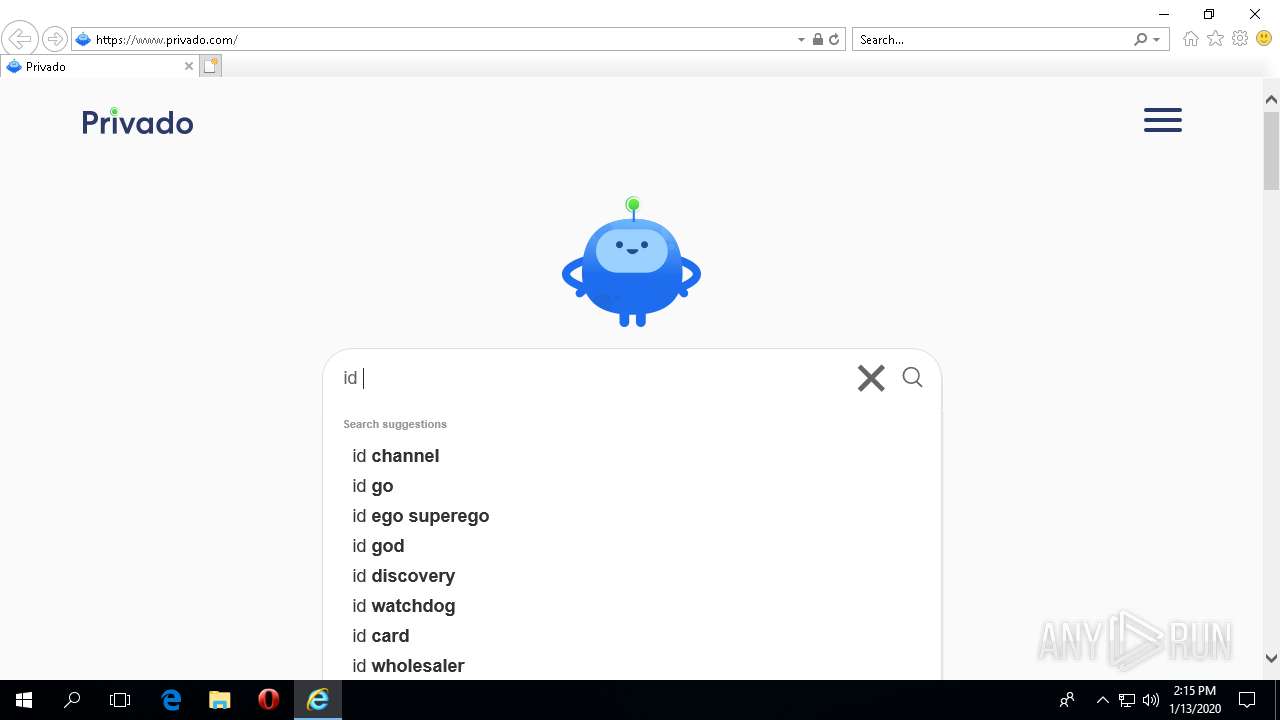
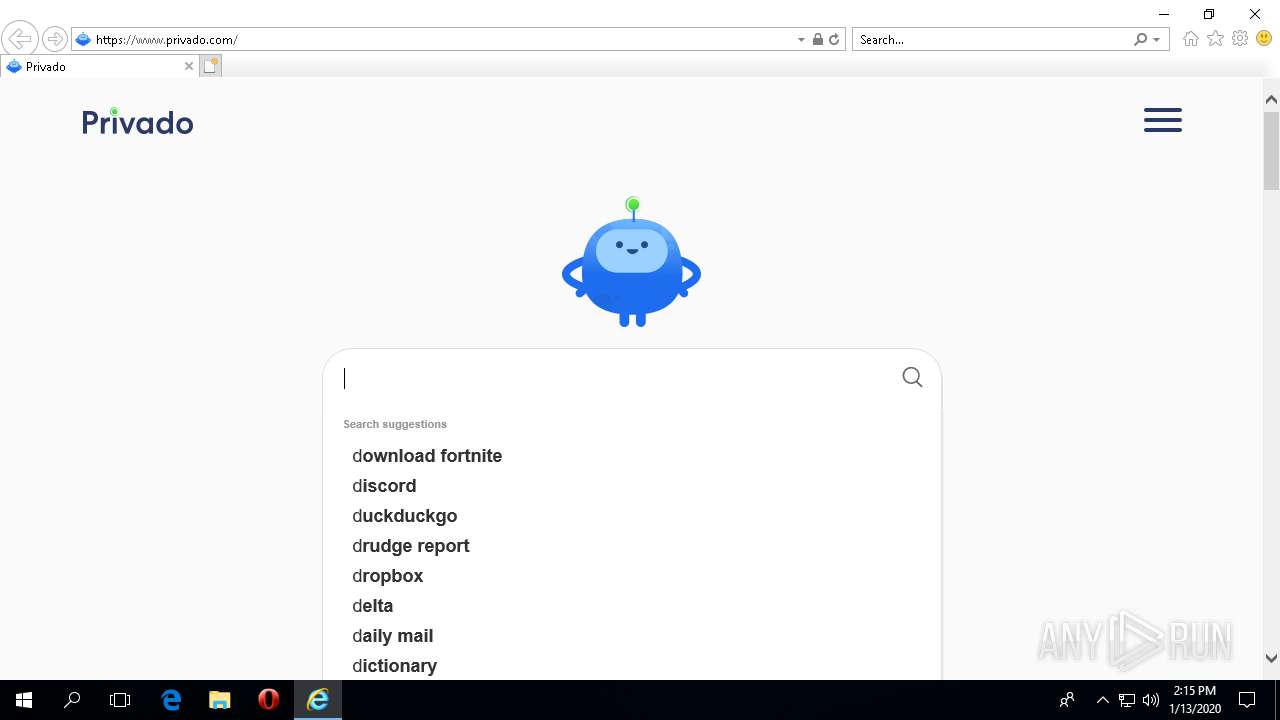
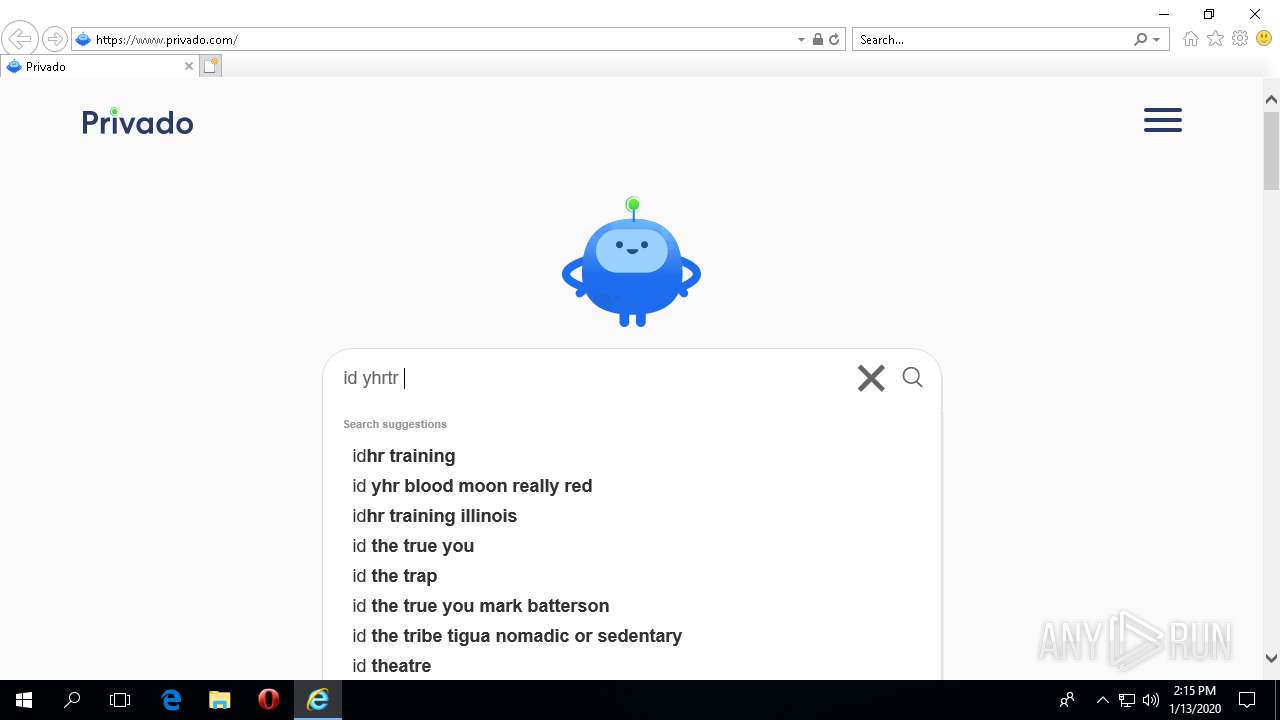
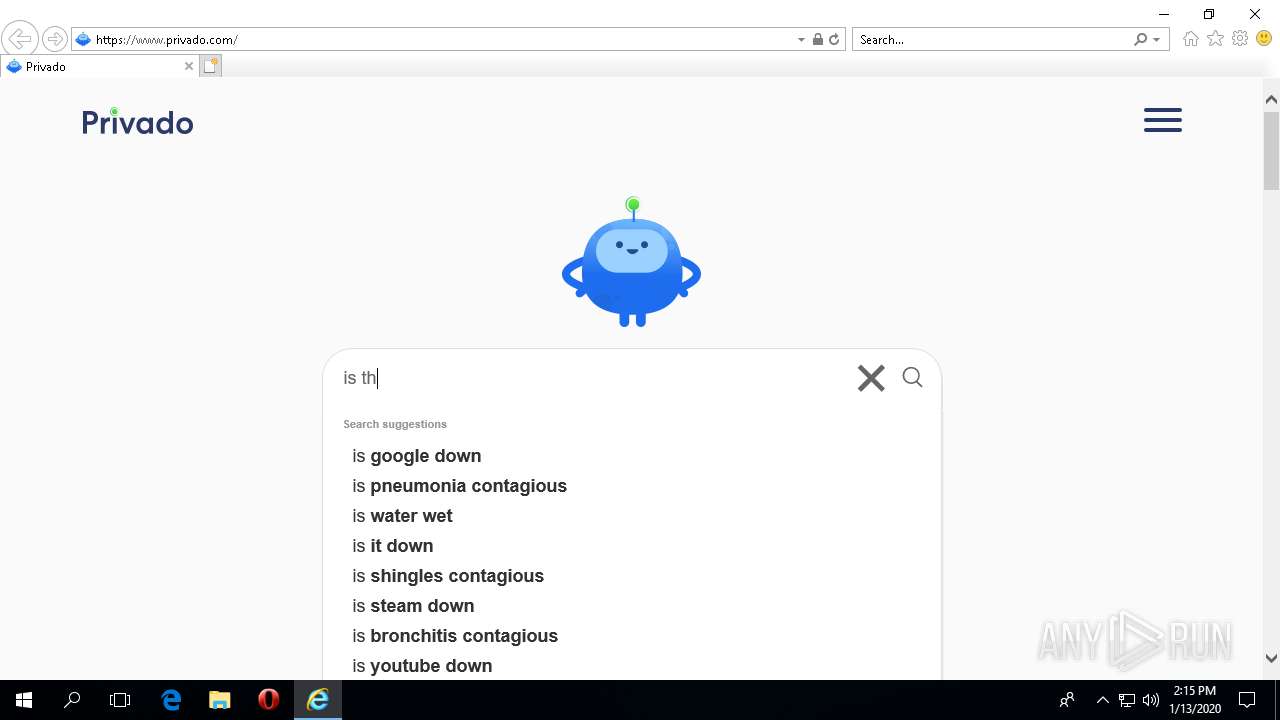
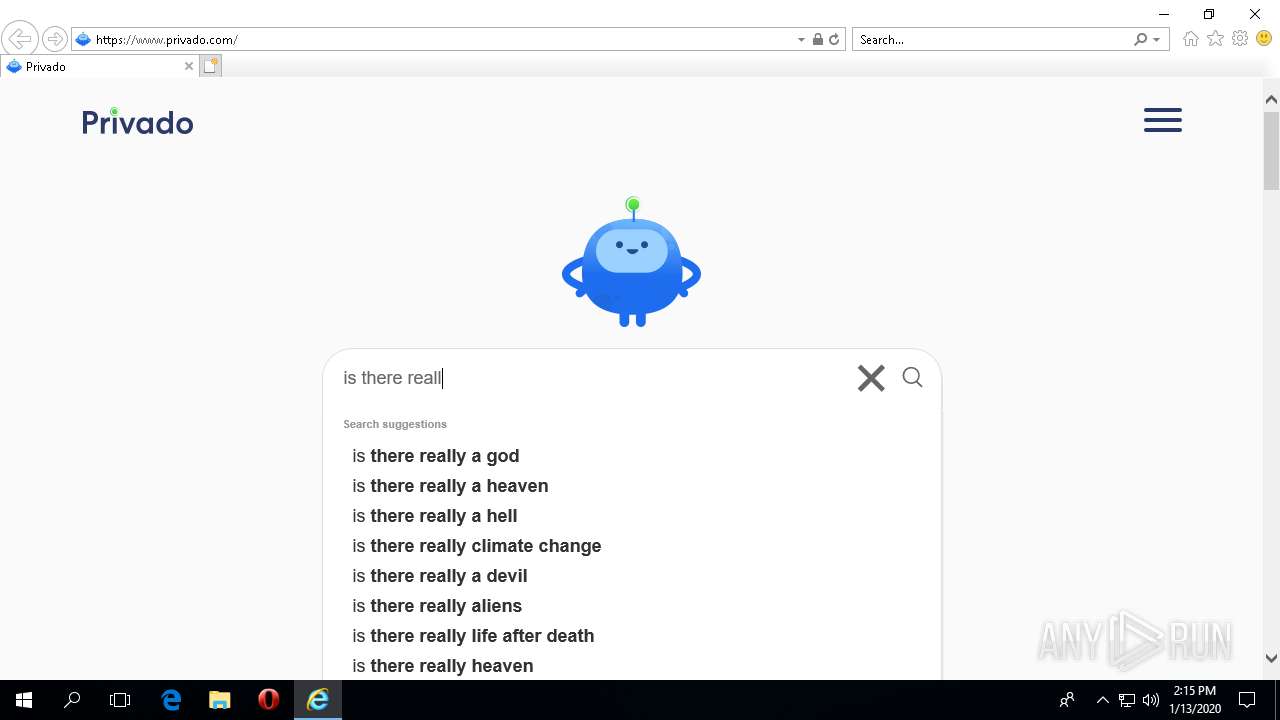
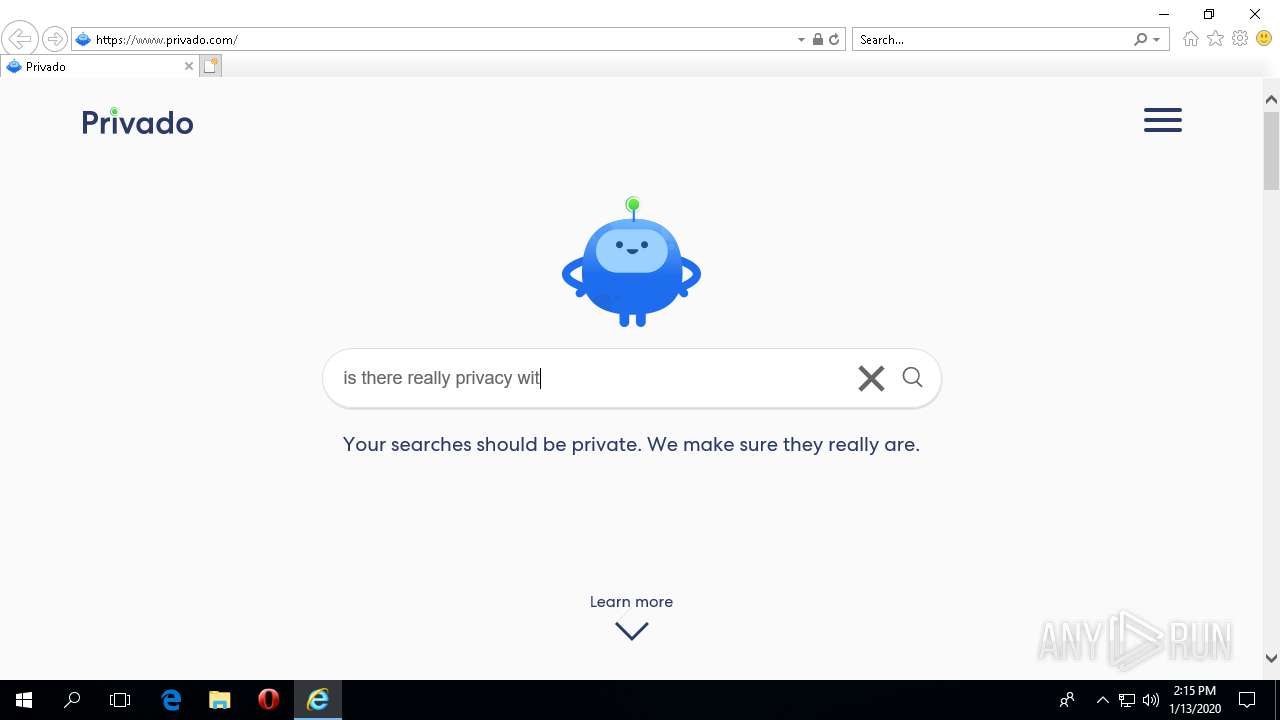
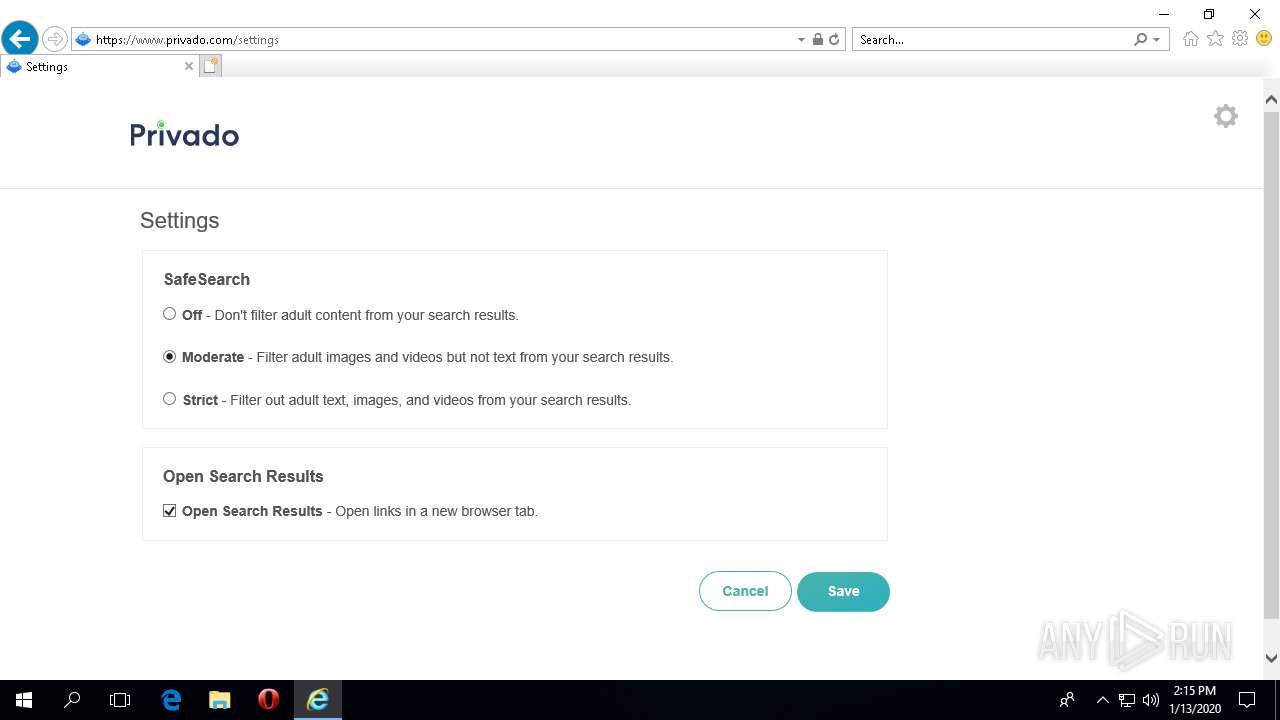
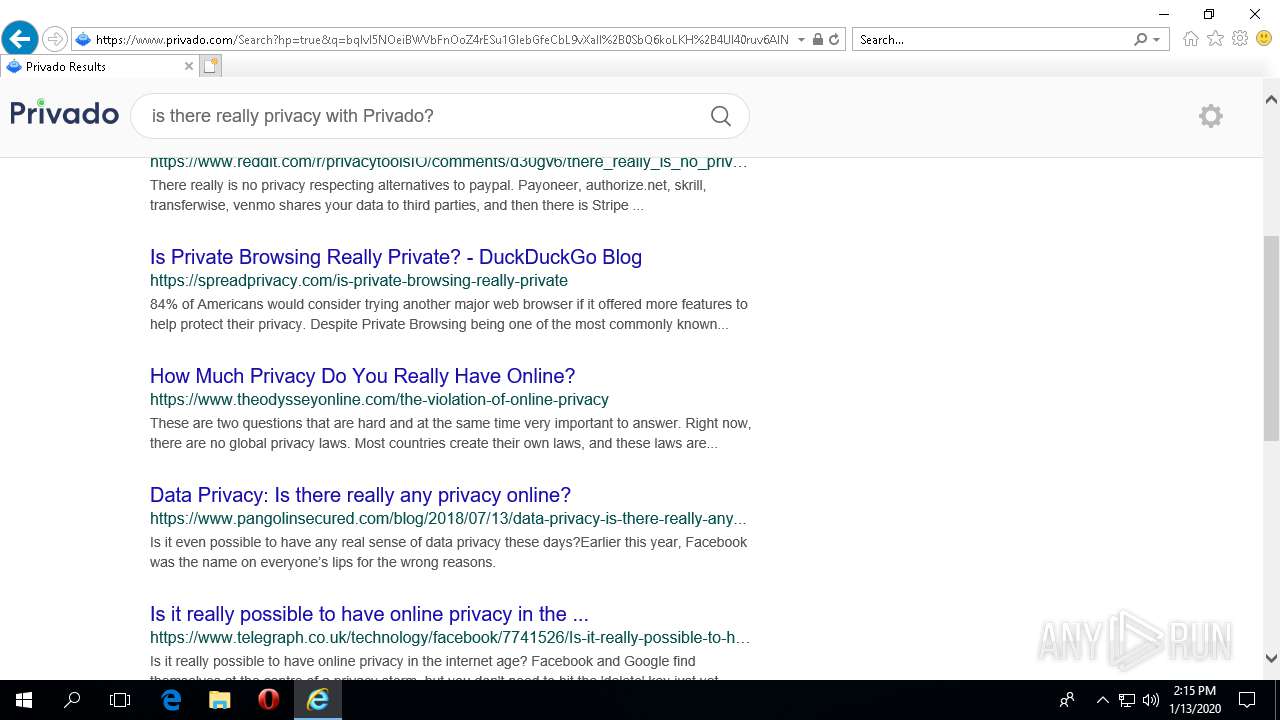
| URL: | https://www.privado.com/ |
| Full analysis: | https://app.any.run/tasks/995671c9-5289-419a-ba75-92b7a06a696e |
| Verdict: | No threats detected |
| Analysis date: | January 13, 2020, 14:14:45 |
| OS: | Windows 10 Professional (build: 16299, 64 bit) |
| Indicators: | |
| MD5: | 2884D297D40D7959CD02530C459B76FA |
| SHA1: | 4E50A95C99D91289288EF0A24203CD62C101D402 |
| SHA256: | B6689C9CE3A5B14868231F290727D8E1EB0DB115D1AF0E0D5B0BDBCD361C5467 |
| SSDEEP: | 3:N8DSLu8KyK3:2OL+yG |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Changes internet zones settings
- iexplore.exe (PID: 2652)
Reads internet explorer settings
- IEXPLORE.EXE (PID: 3224)
Reads the machine GUID from the registry
- IEXPLORE.EXE (PID: 3224)
- iexplore.exe (PID: 2652)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
96
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2652 | "C:\Program Files\internet explorer\iexplore.exe" "https://www.privado.com/" | C:\Program Files\internet explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3224 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:2652 CREDAT:9474 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 330
Read events
1 200
Write events
130
Delete events
0
Modification events
| (PID) Process: | (2652) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkLowPart |
Value: 0 | |||
| (PID) Process: | (2652) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkHighPart |
Value: 0 | |||
| (PID) Process: | (2652) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 0 | |||
| (PID) Process: | (2652) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 0 | |||
| (PID) Process: | (2652) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3873734289 | |||
| (PID) Process: | (2652) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30788123 | |||
| (PID) Process: | (2652) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2652) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2652) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2652) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
Executable files
0
Suspicious files
3
Text files
55
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3224 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\IE\LD57I5PR\privado_icon[1].png | image | |
MD5:— | SHA256:— | |||
| 3224 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\IE\FZ4P8RAN\style[1].css | text | |
MD5:— | SHA256:— | |||
| 2652 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\UrlBlock\URL716C.tmp | — | |
MD5:— | SHA256:— | |||
| 3224 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\IE\2I6MPL32\cookie[1].png | image | |
MD5:— | SHA256:— | |||
| 3224 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\IE\2I6MPL32\magnify[1].png | image | |
MD5:— | SHA256:— | |||
| 3224 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\IE\2I6MPL32\paparazzi[1].gif | image | |
MD5:— | SHA256:— | |||
| 3224 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\IE\LD57I5PR\11T9GOGN.htm | html | |
MD5:— | SHA256:— | |||
| 3224 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\IE\FZ4P8RAN\css[1].css | text | |
MD5:— | SHA256:— | |||
| 3224 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\IE\5UIG5DSE\close[1].png | image | |
MD5:— | SHA256:— | |||
| 3224 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\IE\LD57I5PR\Bottom_ellipse[1].svg | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
26
DNS requests
16
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3224 | IEXPLORE.EXE | 18.196.217.191:443 | feed.cf-se.com | Amazon.com, Inc. | DE | unknown |
3224 | IEXPLORE.EXE | 13.35.253.42:443 | www.privado.com | — | US | malicious |
3224 | IEXPLORE.EXE | 216.58.206.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3224 | IEXPLORE.EXE | 143.204.214.92:443 | app.privado.com | — | US | unknown |
3224 | IEXPLORE.EXE | 23.102.47.40:443 | urs.microsoft.com | Microsoft Corporation | IE | unknown |
3224 | IEXPLORE.EXE | 52.3.46.30:443 | content-publisher-events.streamesh.net | Amazon.com, Inc. | US | unknown |
3224 | IEXPLORE.EXE | 18.214.211.38:443 | suggest.privado.com | — | US | unknown |
2652 | iexplore.exe | 143.204.214.92:443 | app.privado.com | — | US | unknown |
2652 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2652 | iexplore.exe | 137.117.228.253:443 | c.urs.microsoft.com | Microsoft Corporation | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.privado.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
app.privado.com |
| malicious |
urs.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
suggest.privado.com |
| suspicious |
iecvlist.microsoft.com |
| whitelisted |
c.urs.microsoft.com |
| whitelisted |
feed.cf-se.com |
| shared |
content-publisher-events.streamesh.net |
| unknown |