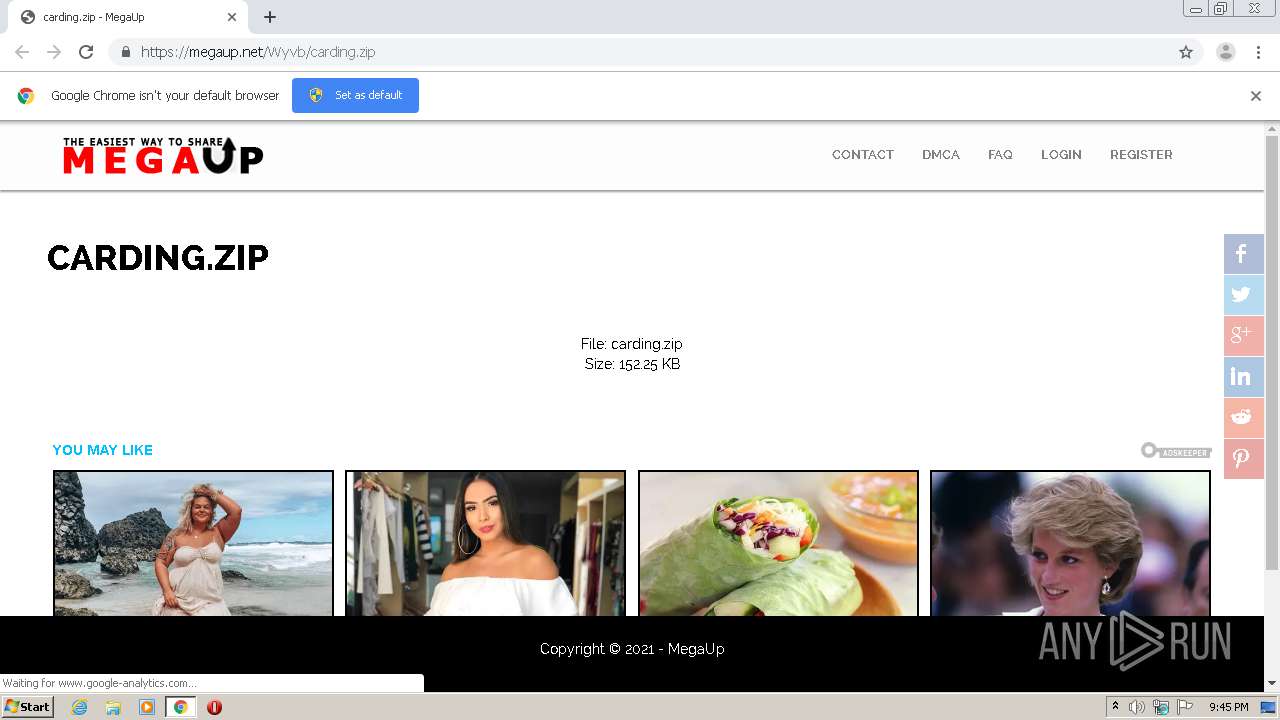
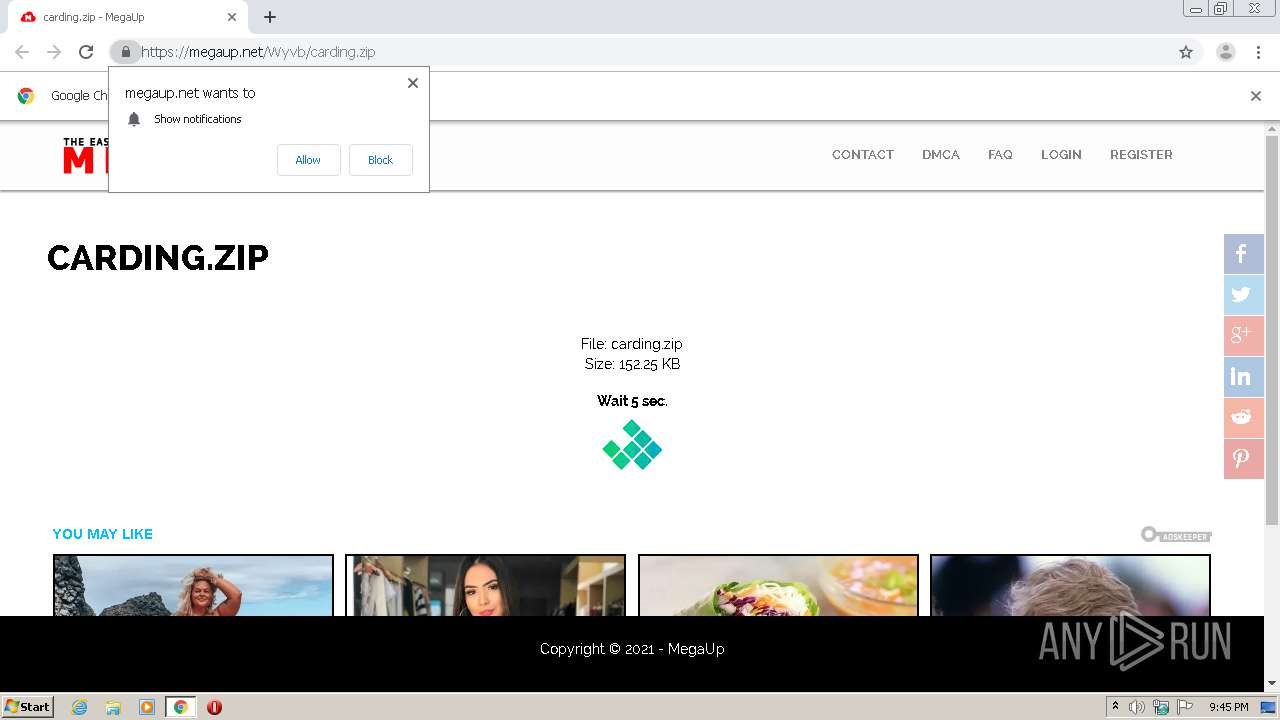
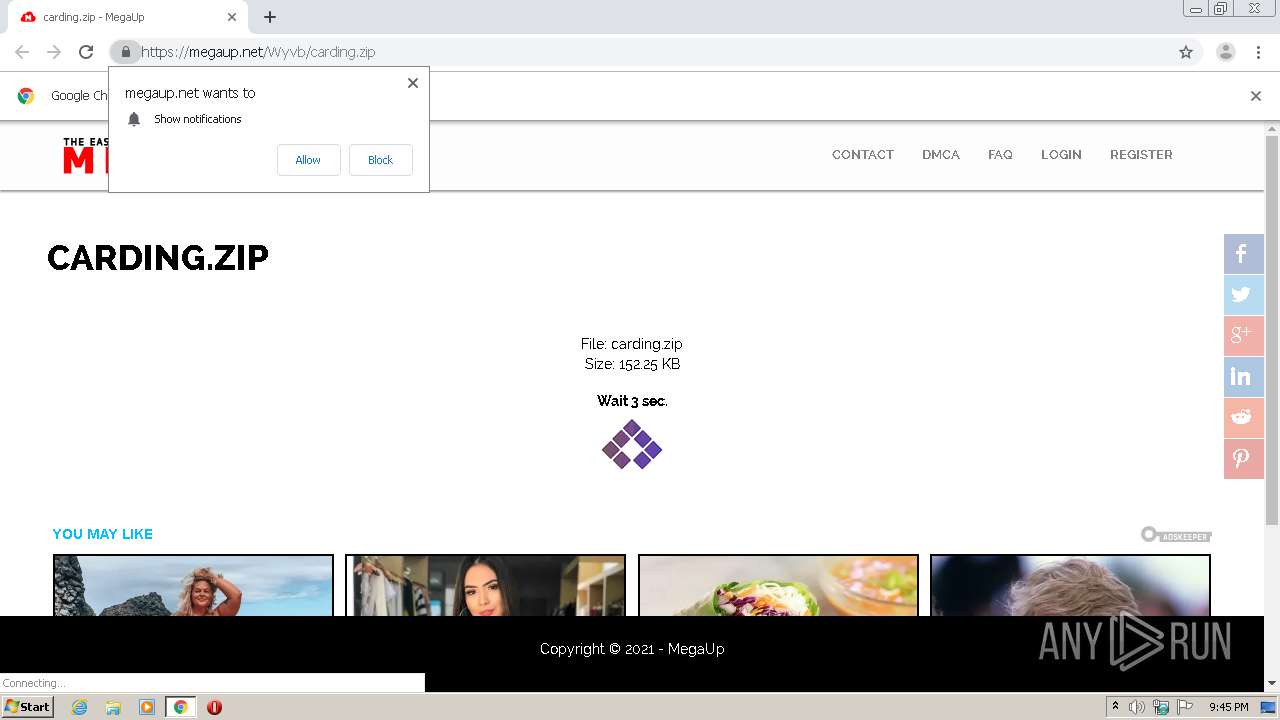
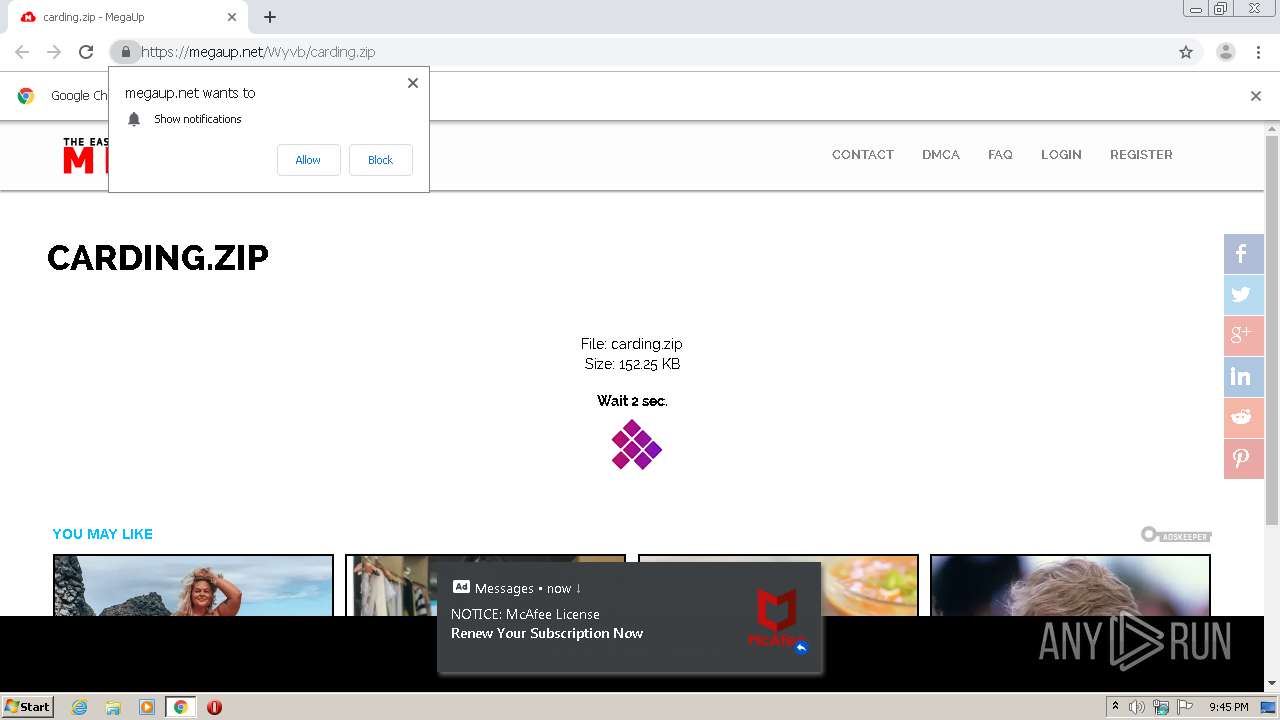
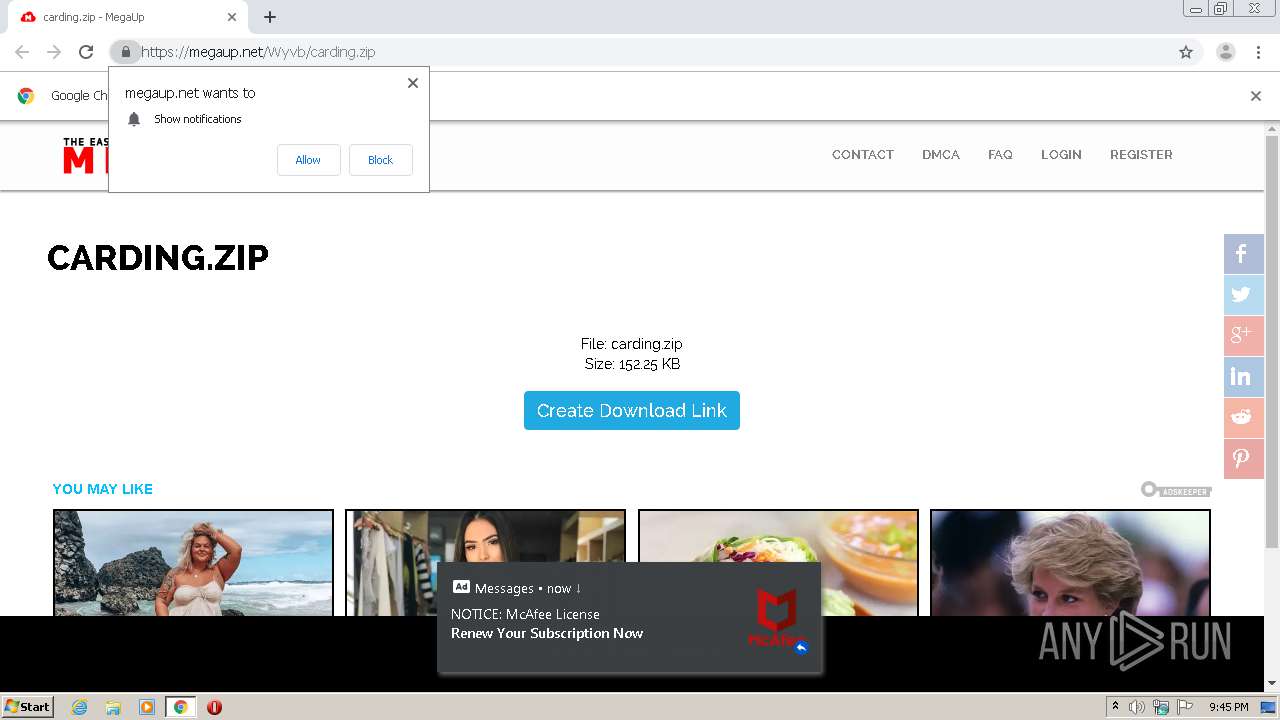
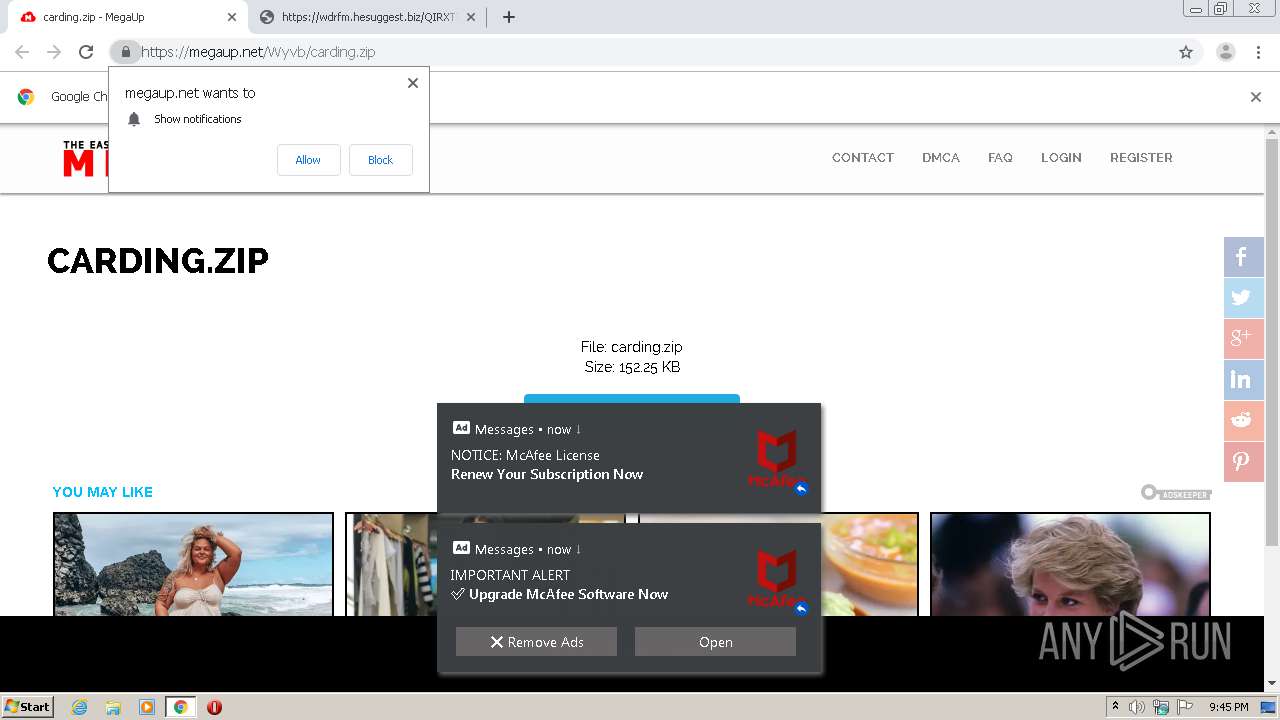
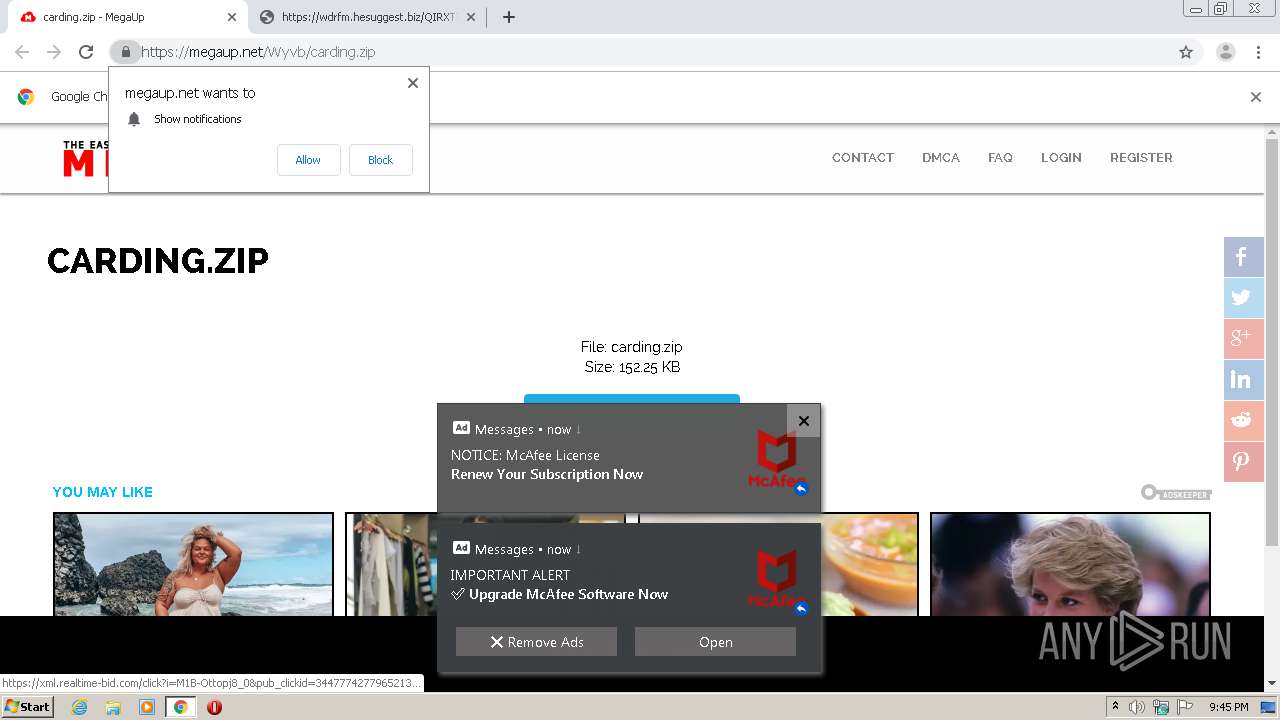
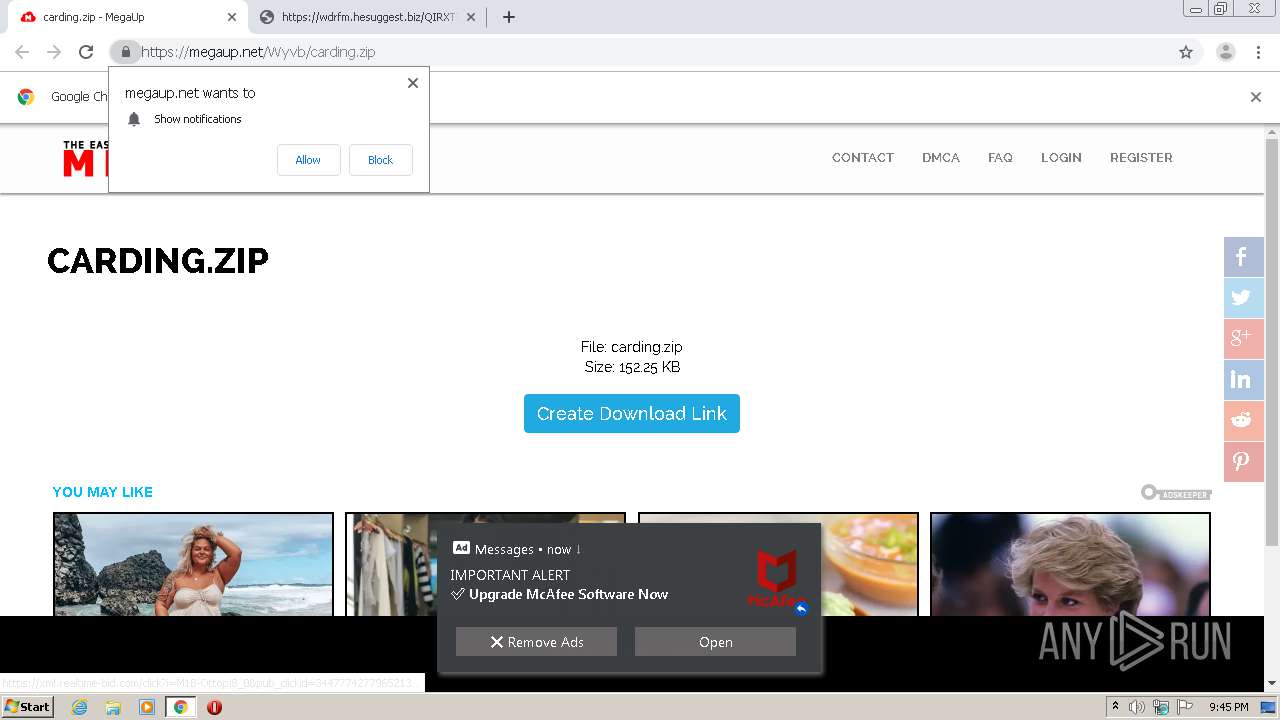
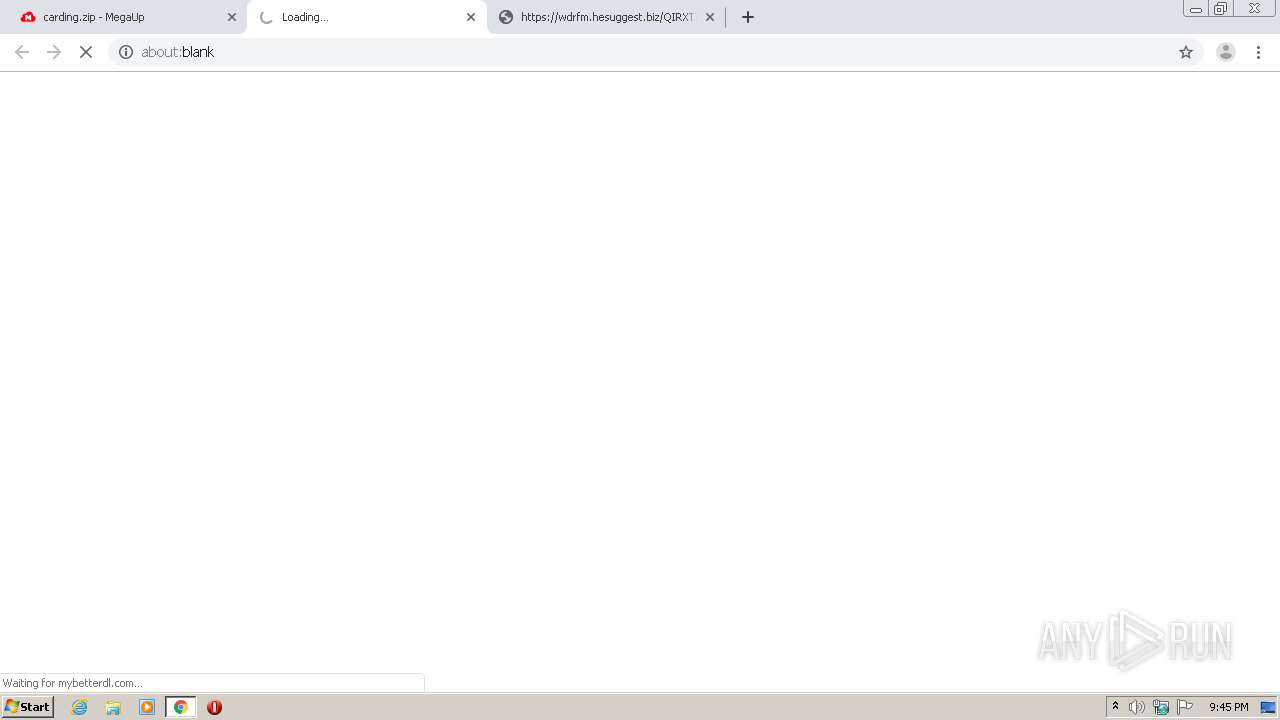
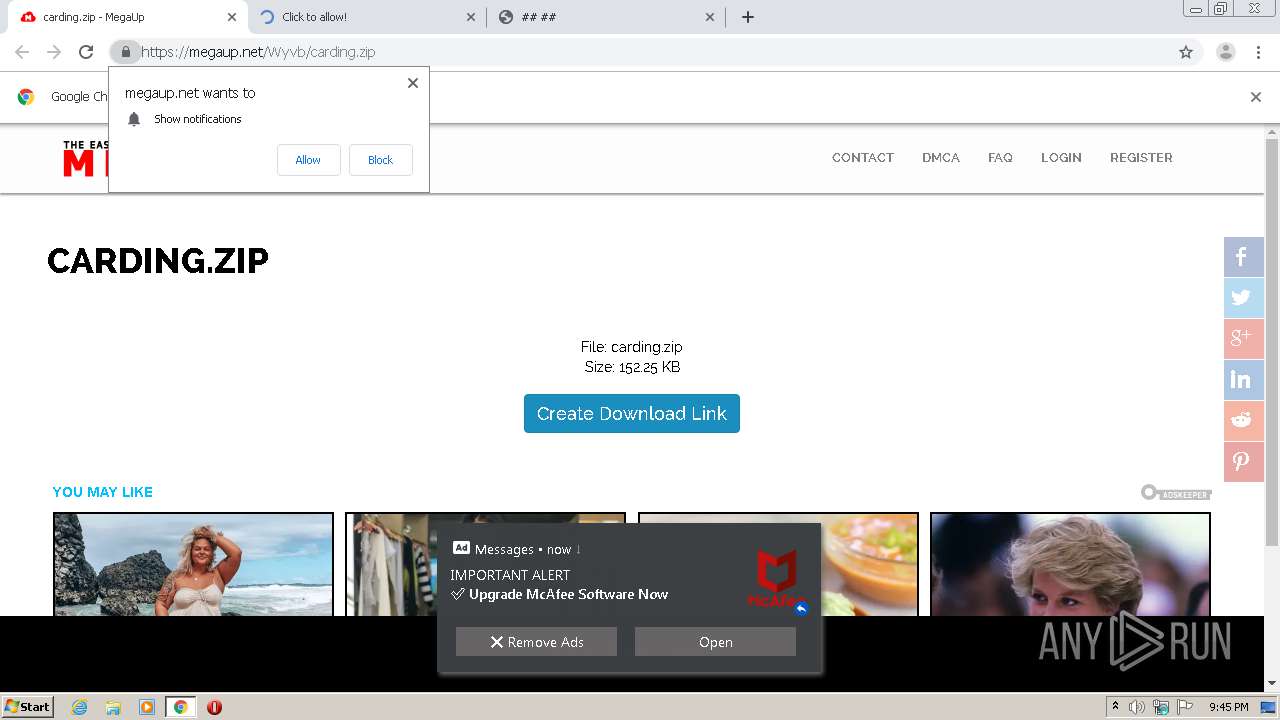
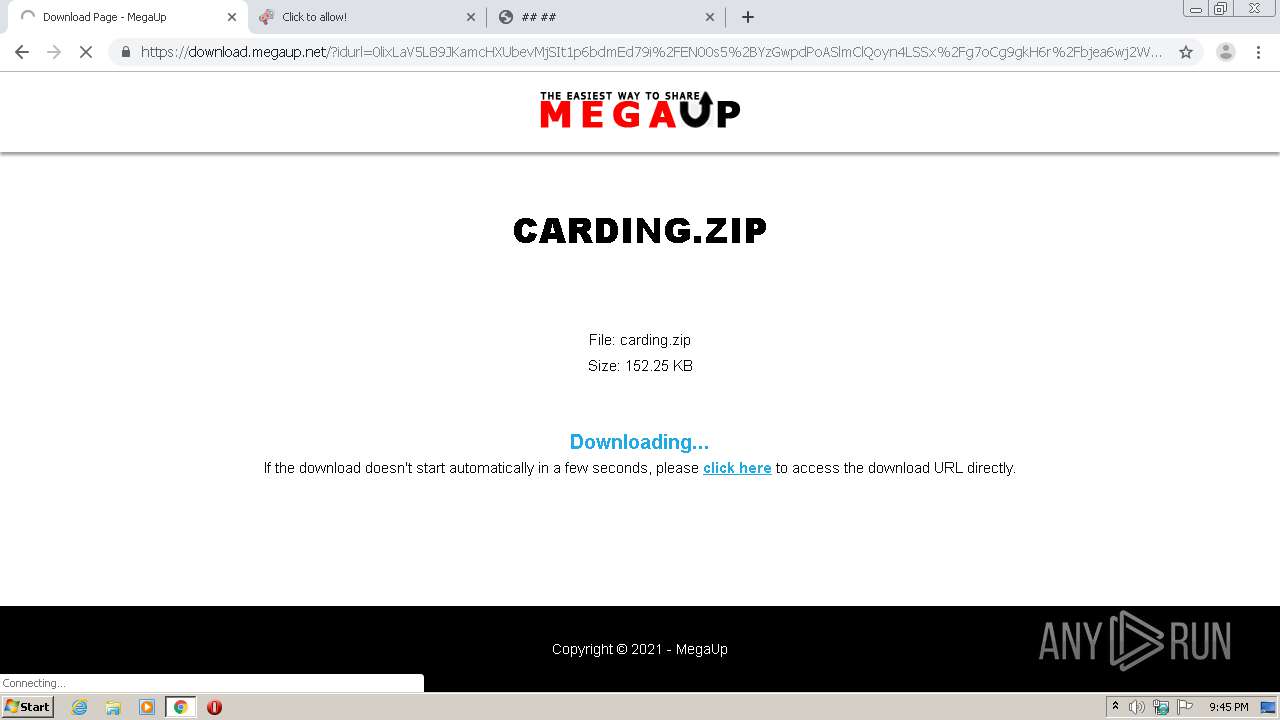
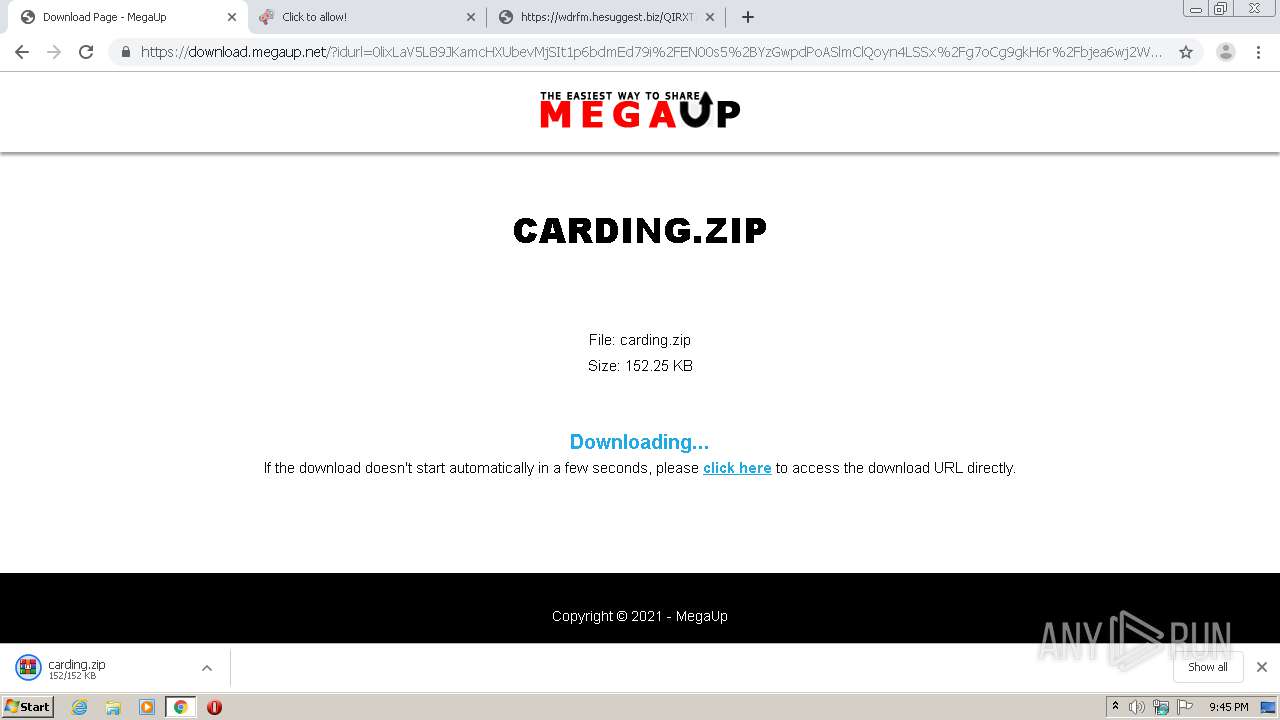
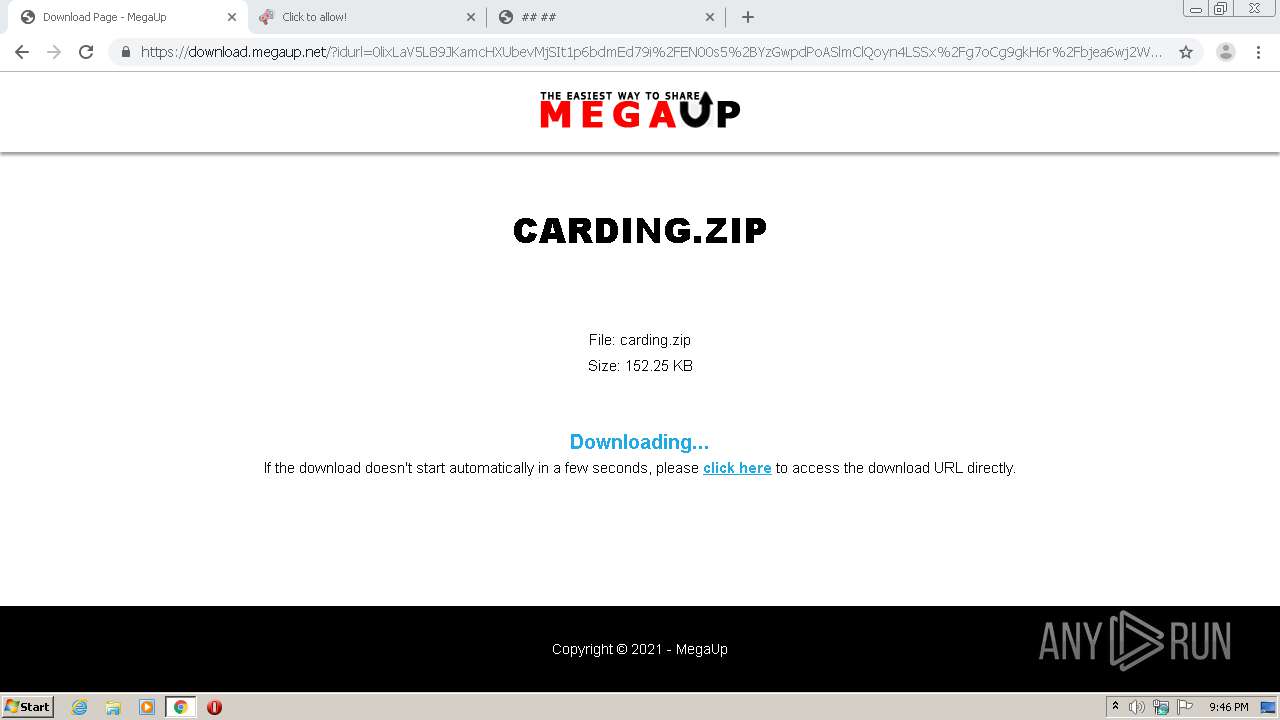
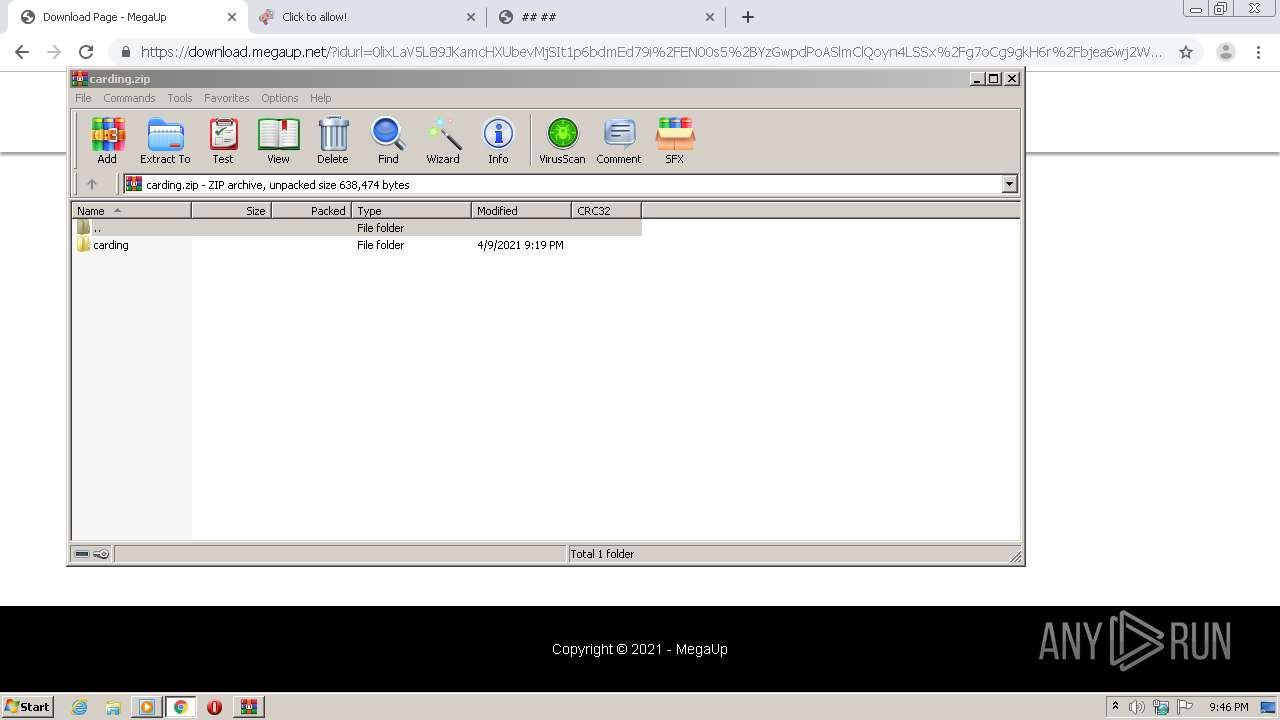
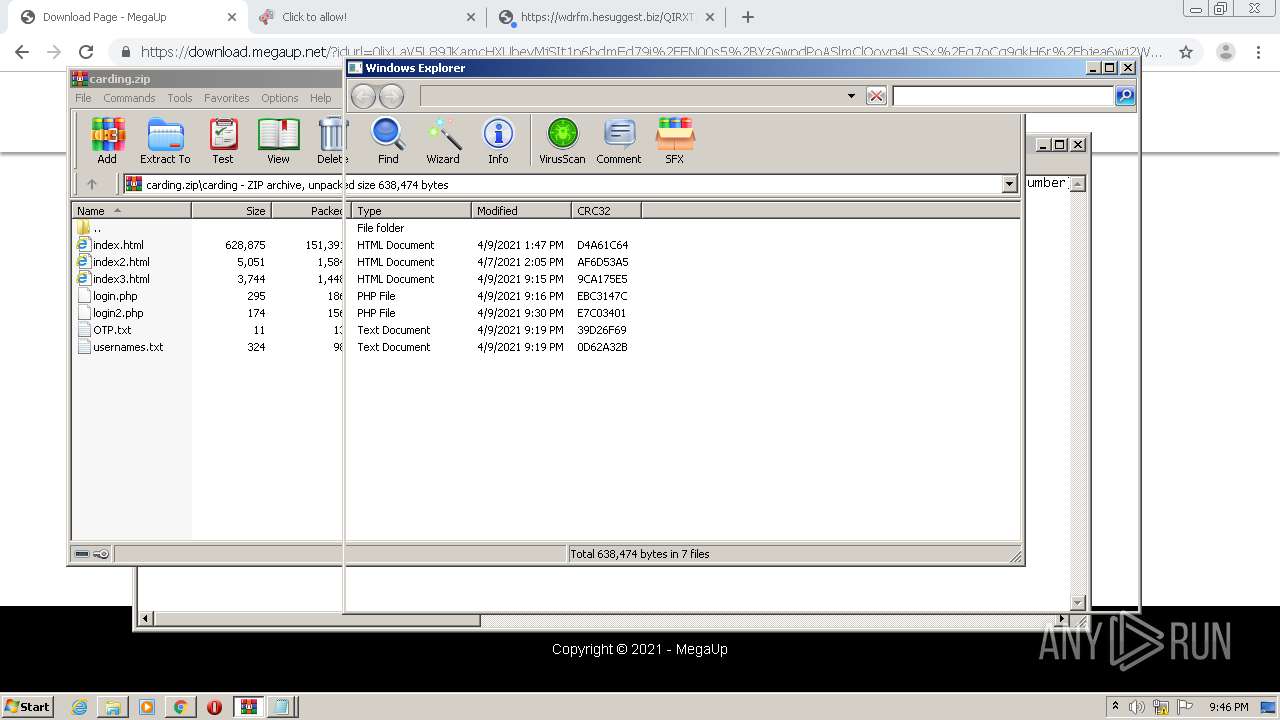
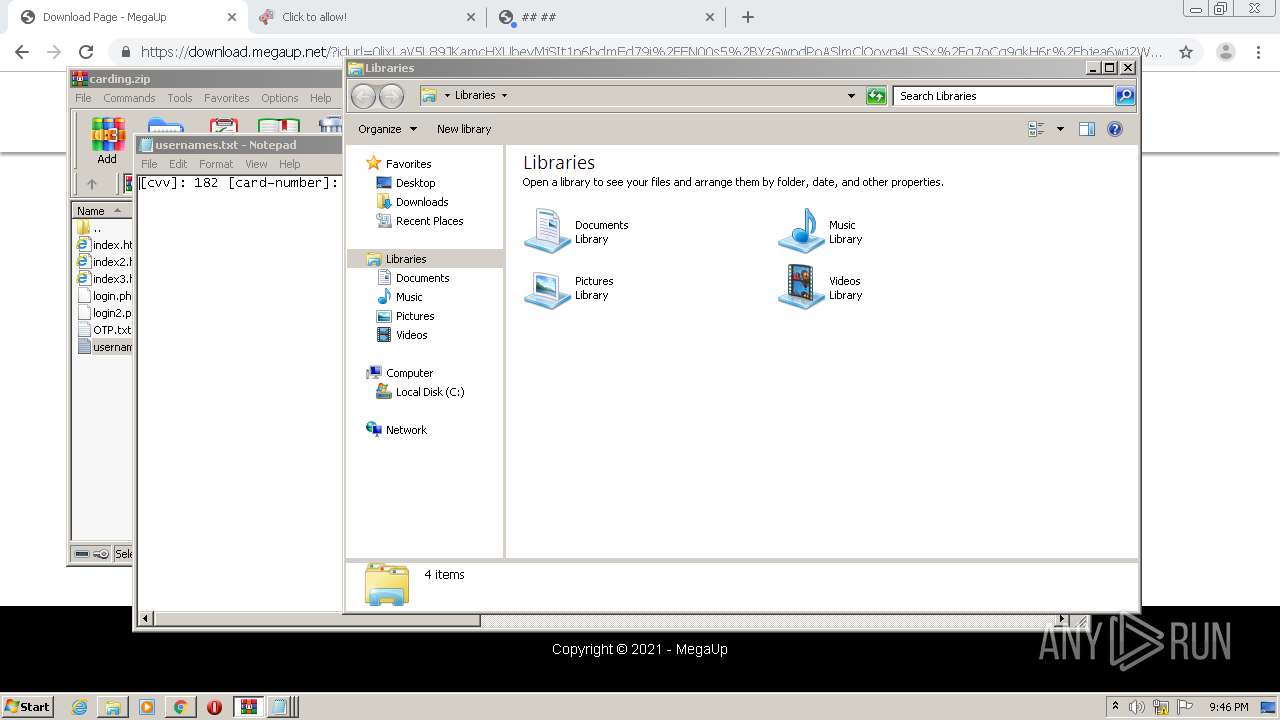
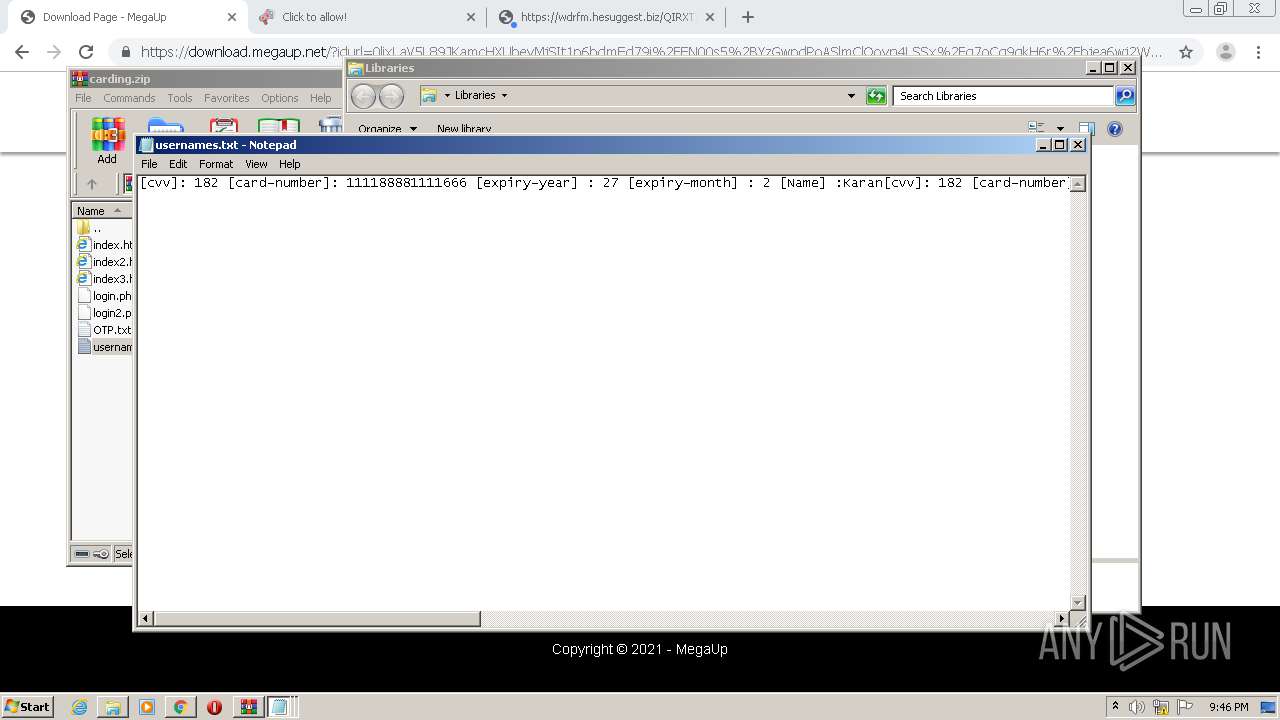
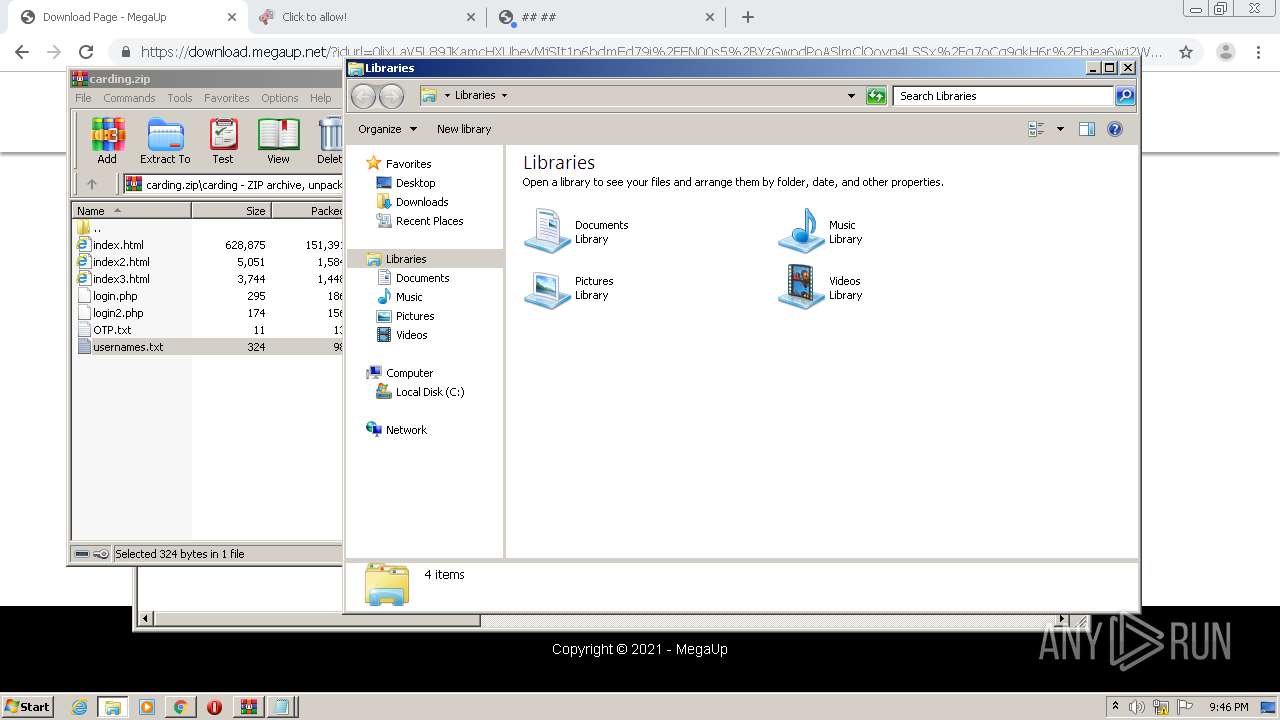
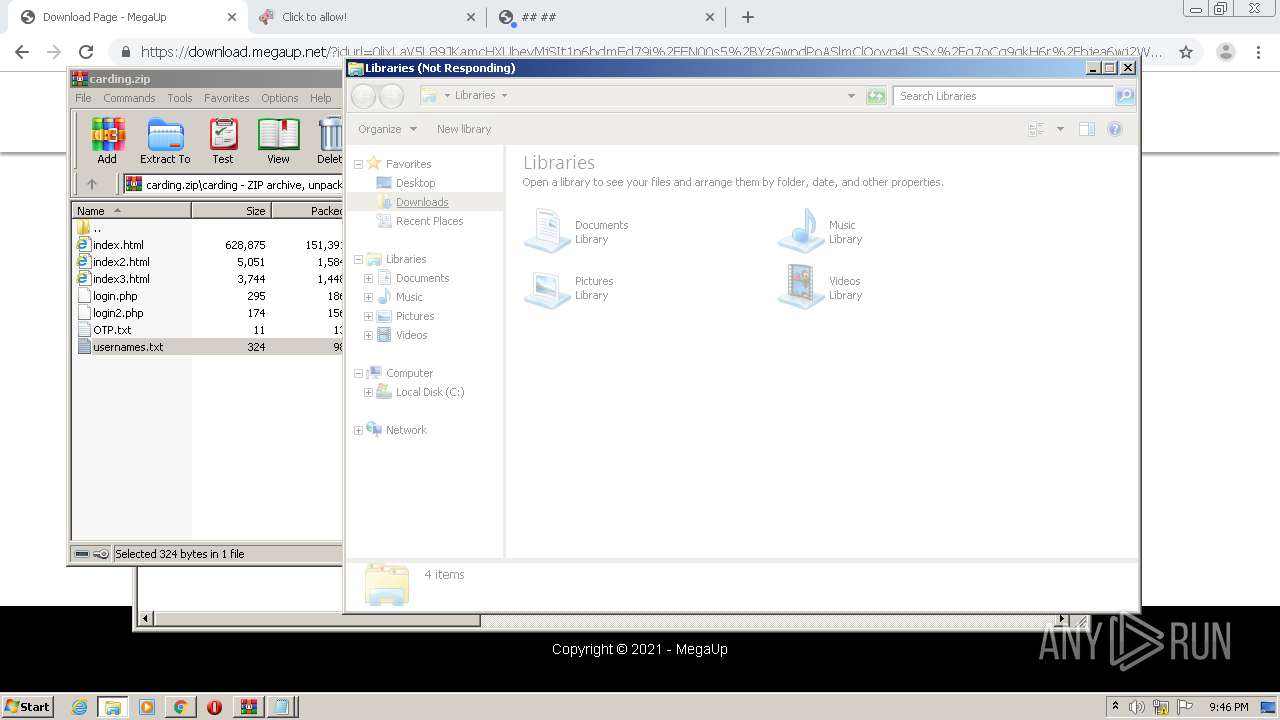
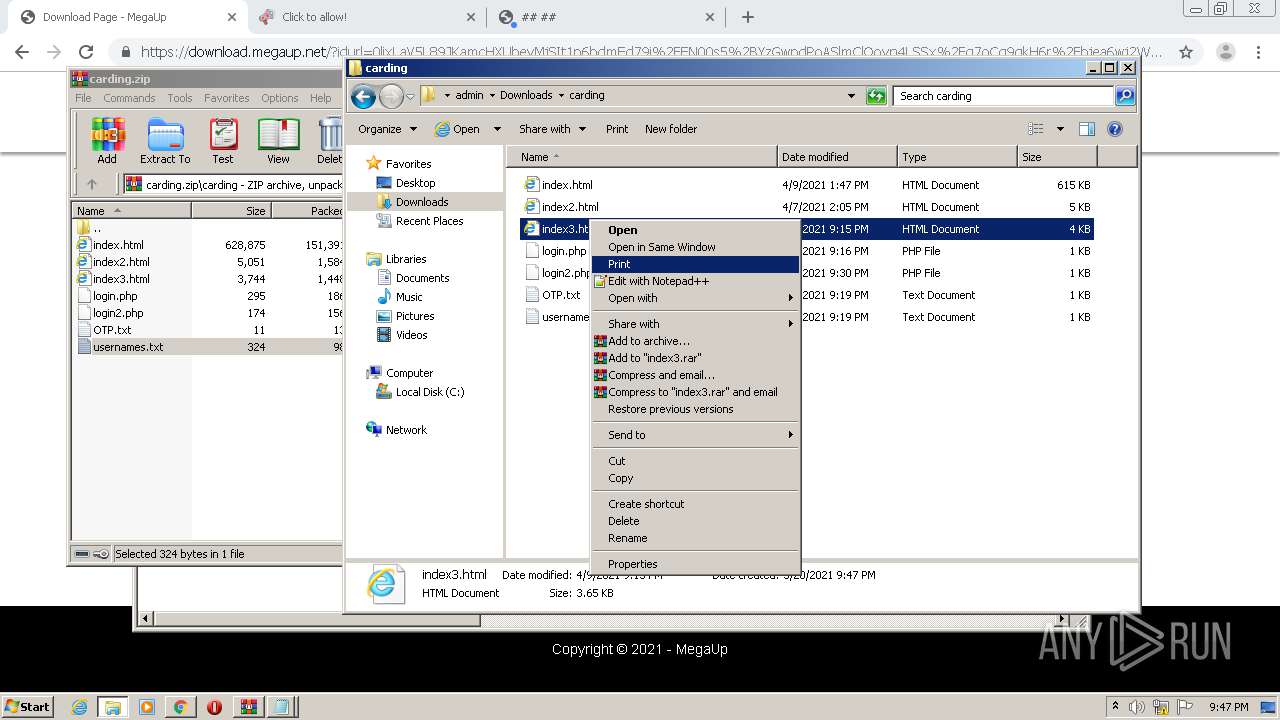
| URL: | https://megaup.net/Wyvb/carding.zip |
| Full analysis: | https://app.any.run/tasks/da16954e-737a-43eb-8aea-2baaf655a24b |
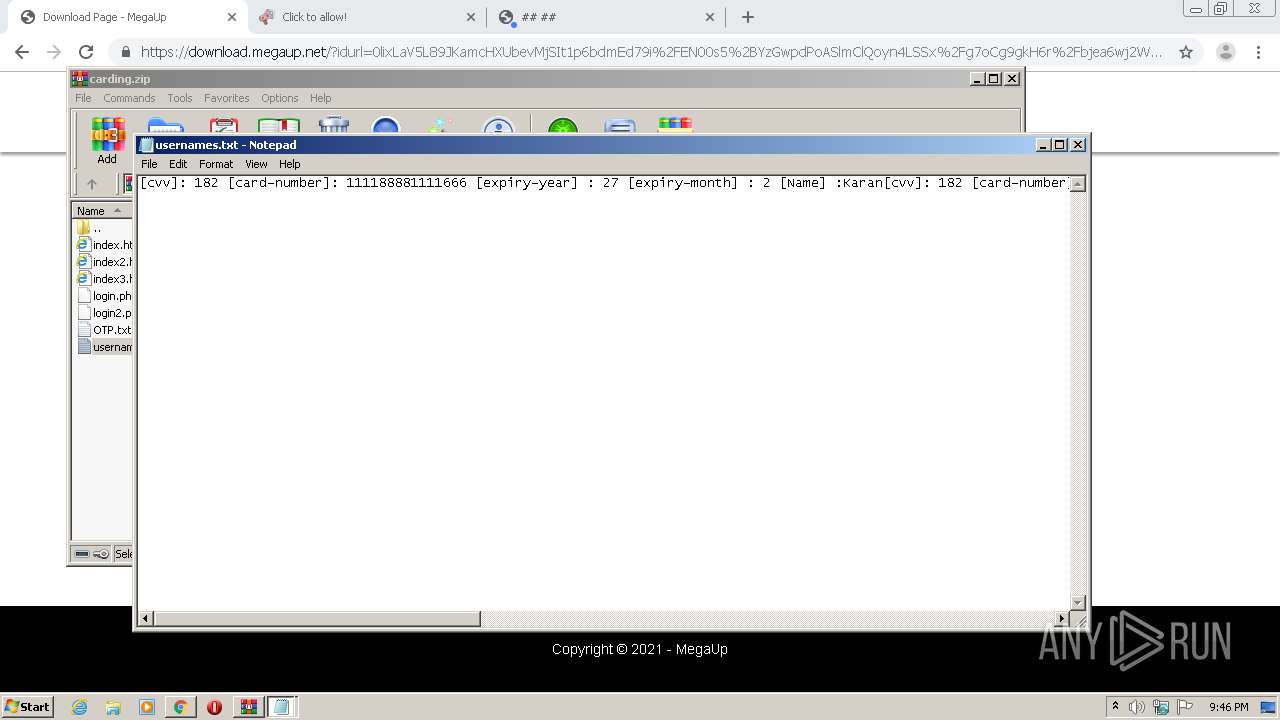
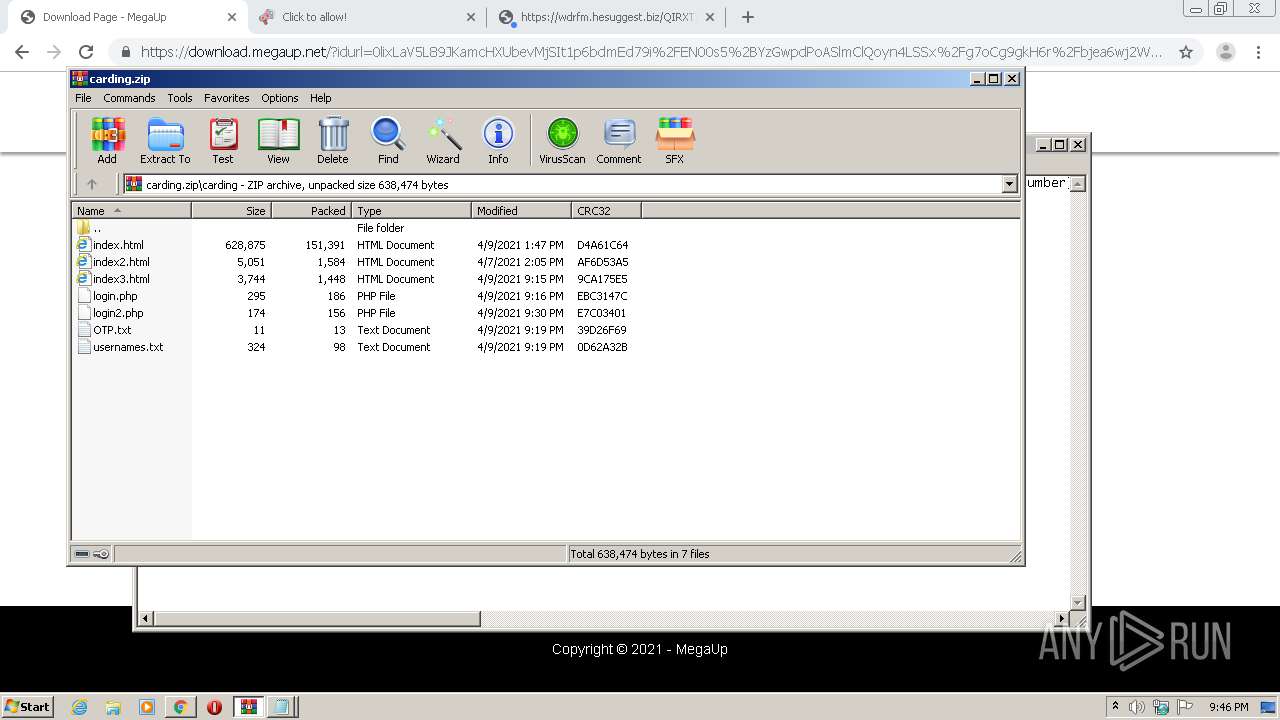
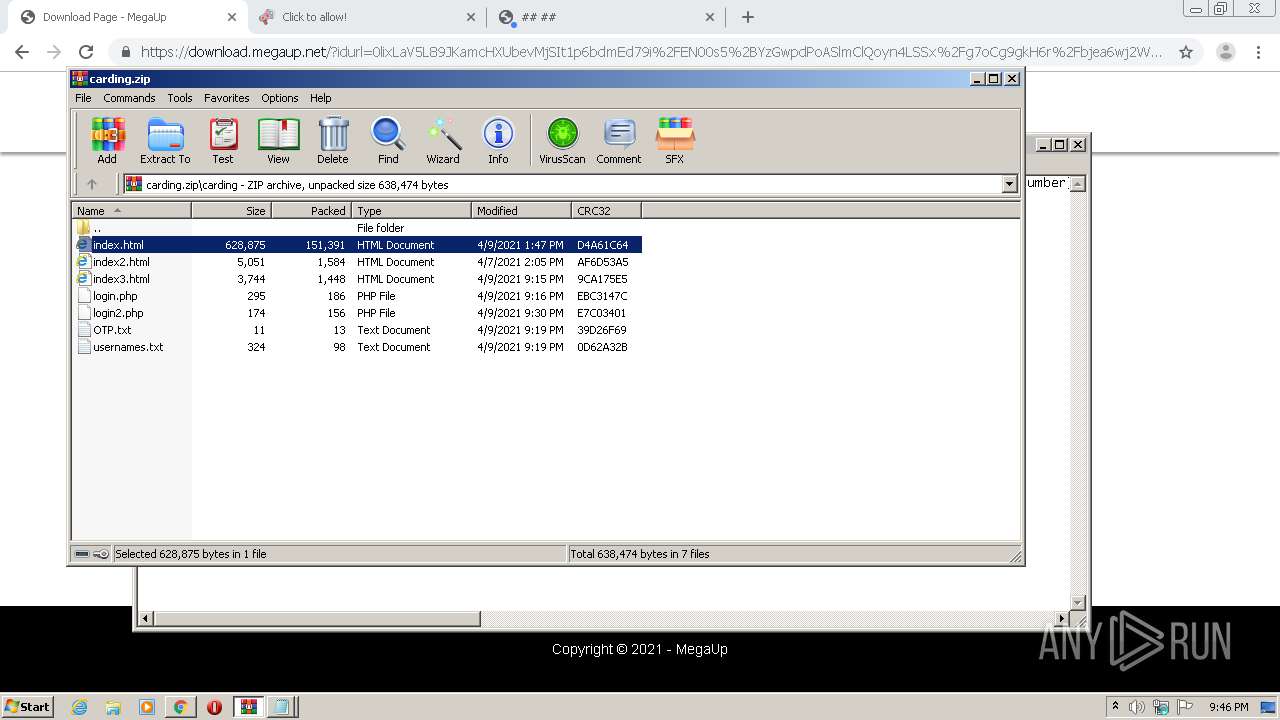
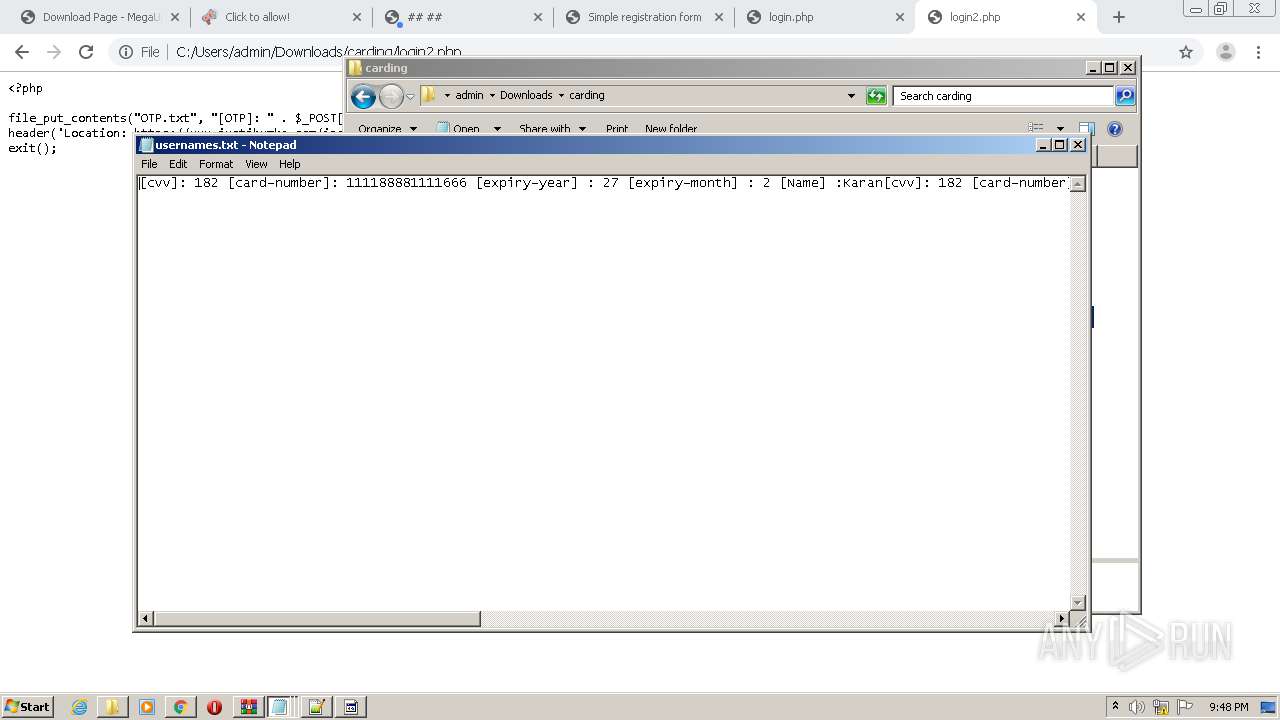
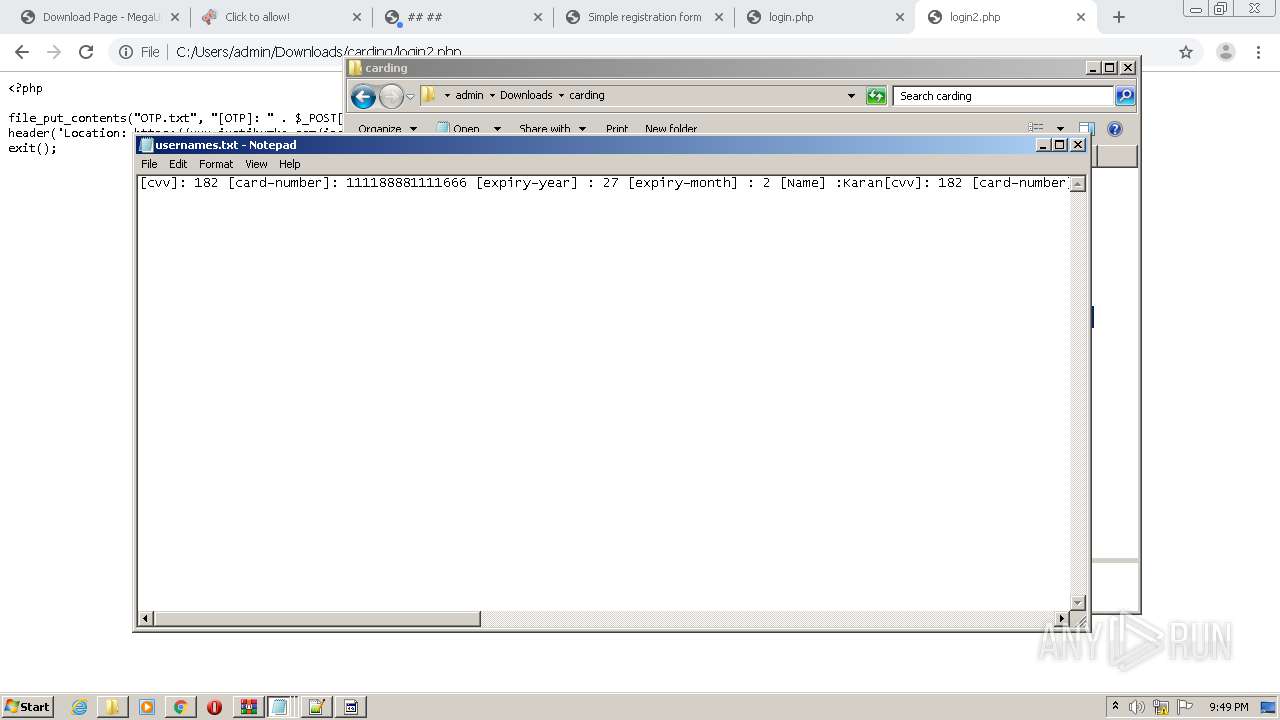
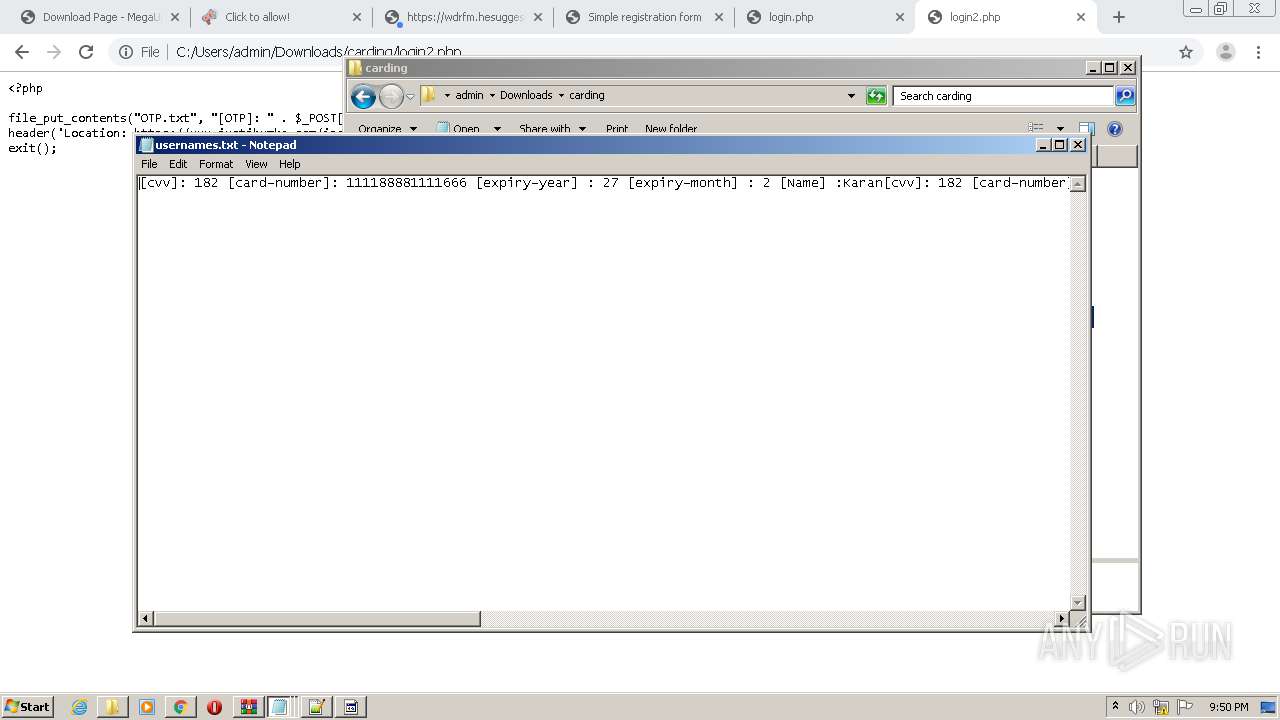
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2021, 20:45:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 9281EB80AC081B83669031064B6D333C |
| SHA1: | FED084408DE1FC6BD0EDD137CCF5A684D53A2794 |
| SHA256: | B6665145D783F74D7AE45EB1E41C0262E154E4655D23D4539585B6A5CEFBE83B |
| SSDEEP: | 3:N8XCrEKvV:2yrEmV |
MALICIOUS
No malicious indicators.SUSPICIOUS
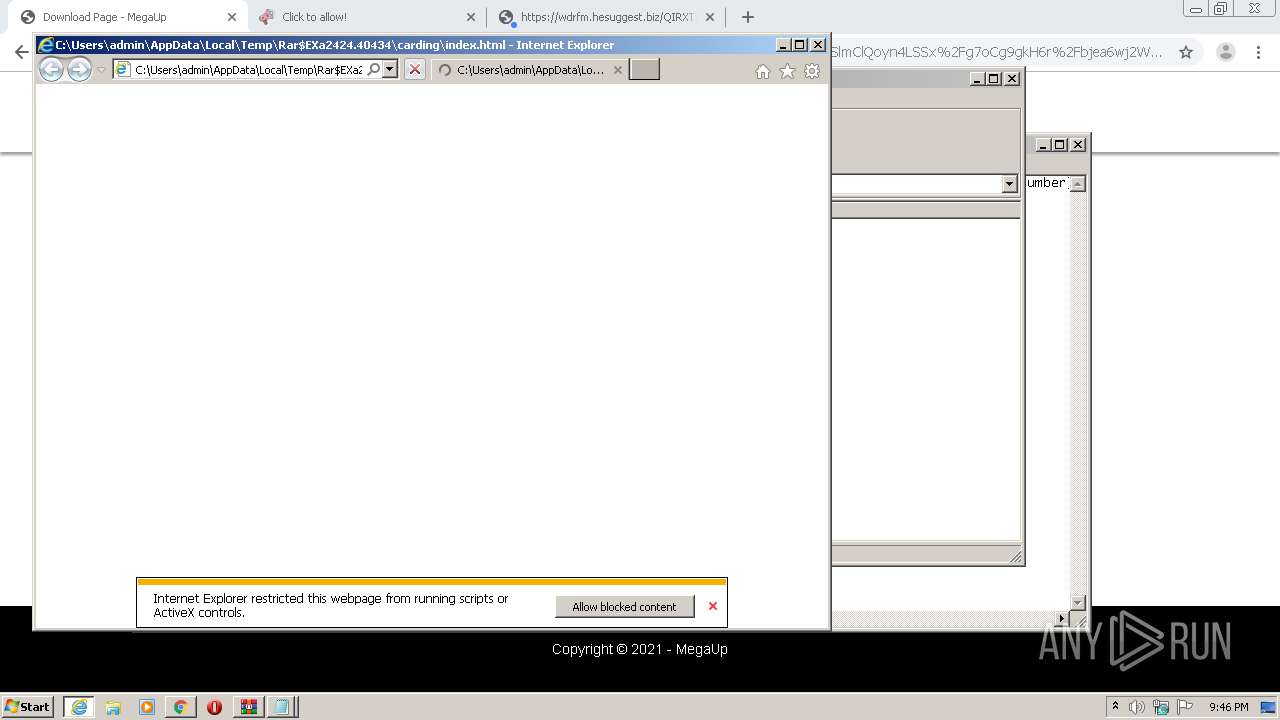
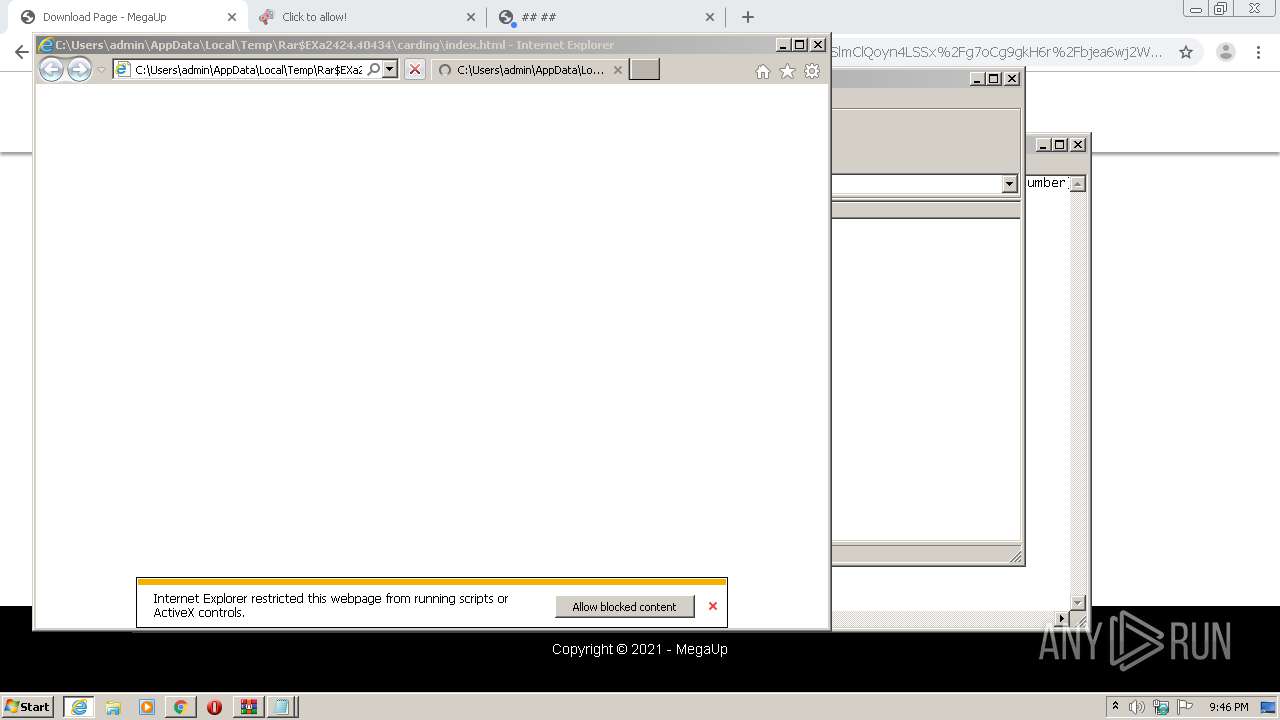
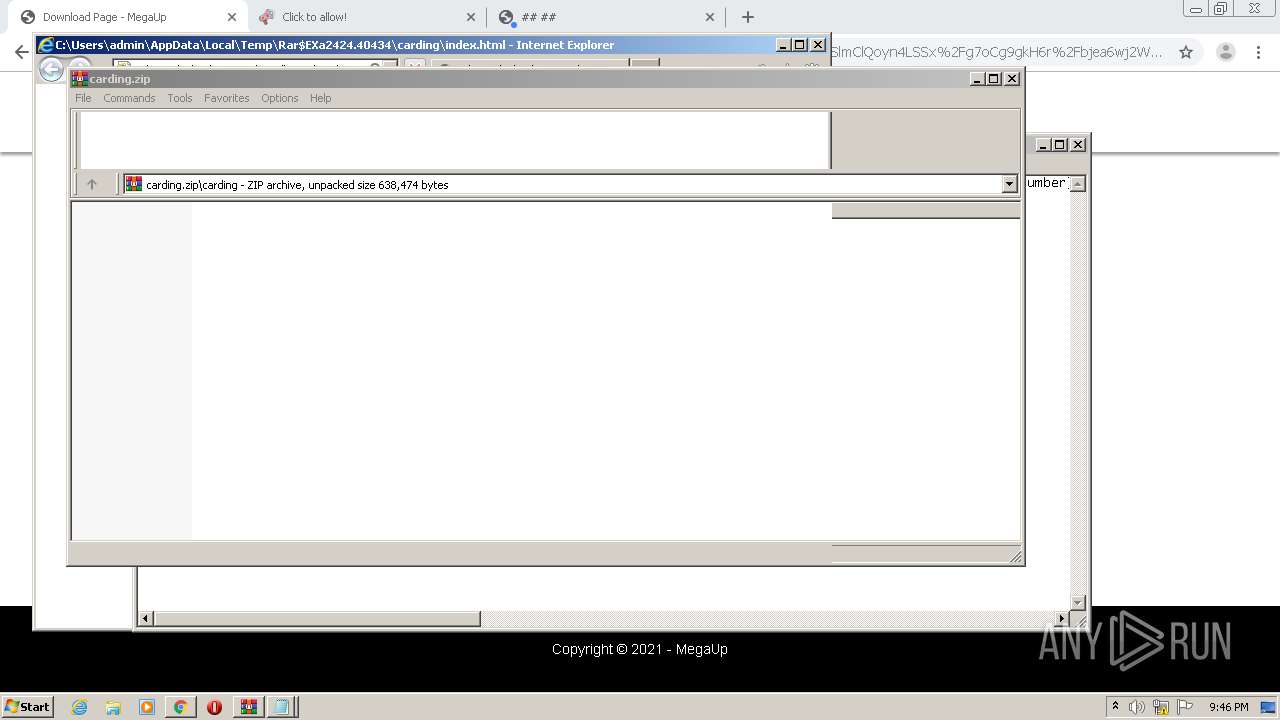
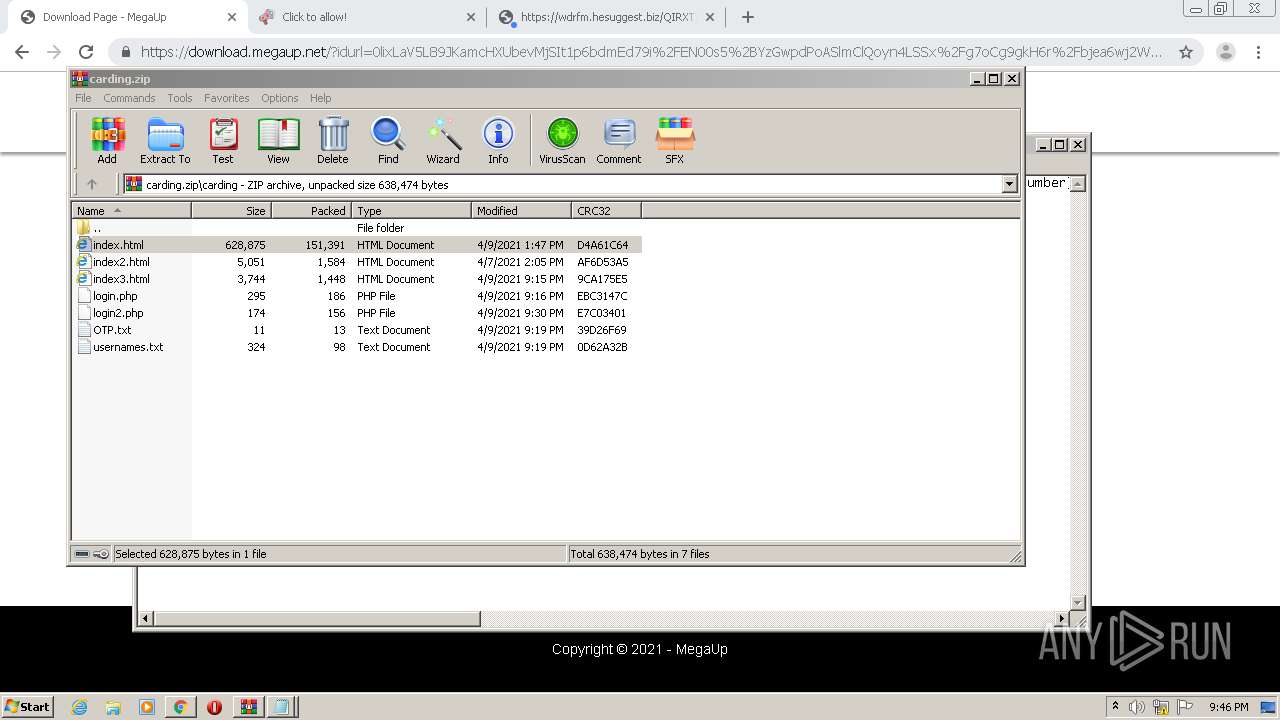
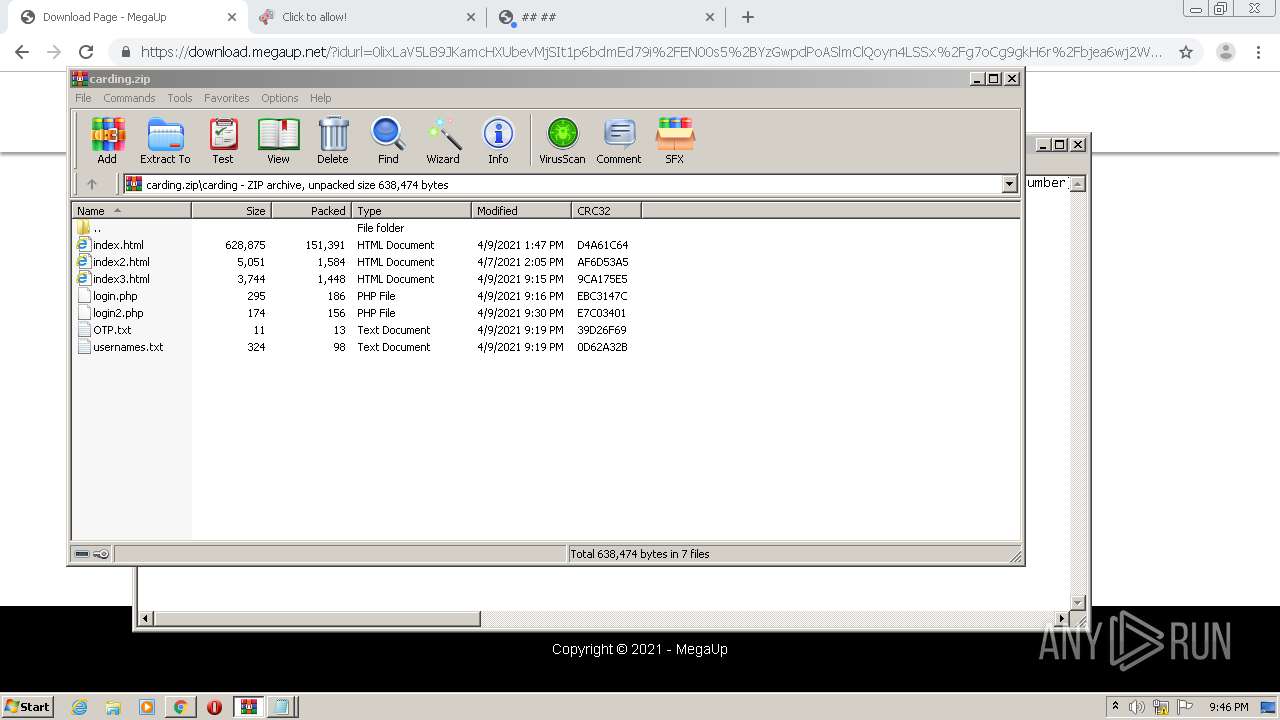
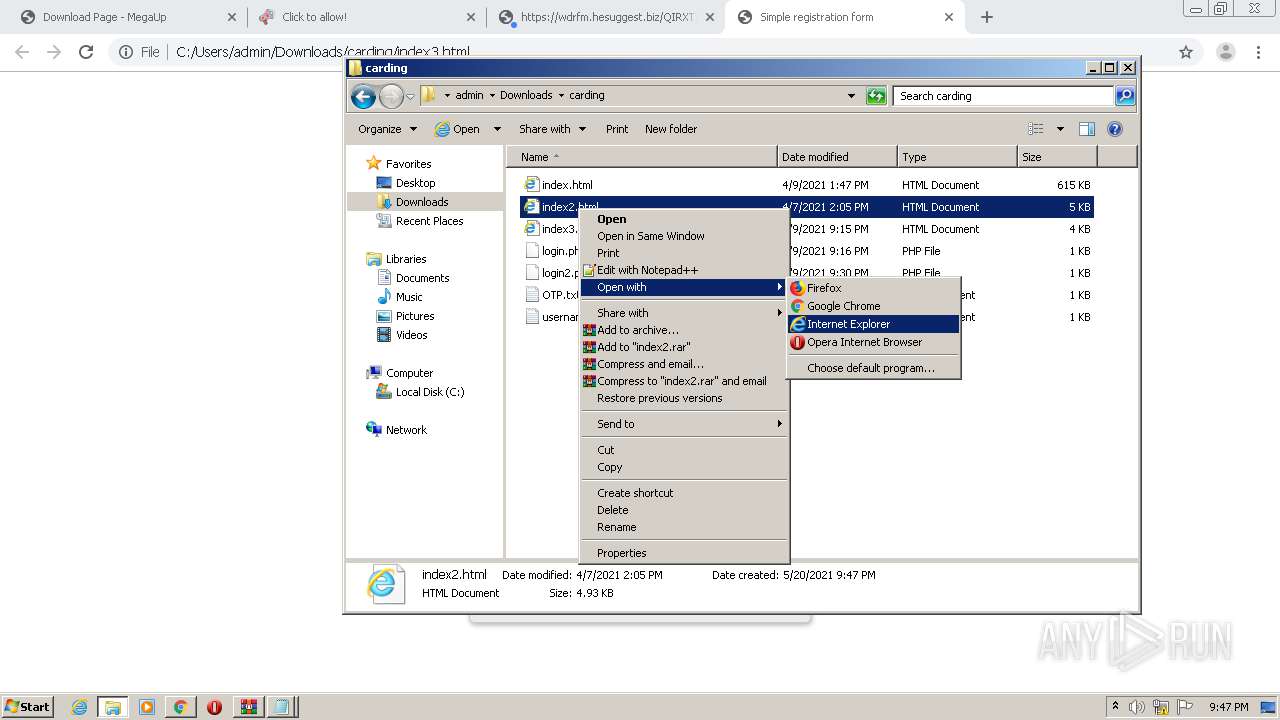
Starts Internet Explorer
- WinRAR.exe (PID: 2424)
INFO
Reads the hosts file
- chrome.exe (PID: 576)
- chrome.exe (PID: 3956)
Application launched itself
- chrome.exe (PID: 576)
- iexplore.exe (PID: 3492)
- chrome.exe (PID: 4040)
- chrome.exe (PID: 956)
- chrome.exe (PID: 2620)
Changes settings of System certificates
- iexplore.exe (PID: 812)
Reads settings of System Certificates
- iexplore.exe (PID: 812)
- chrome.exe (PID: 3956)
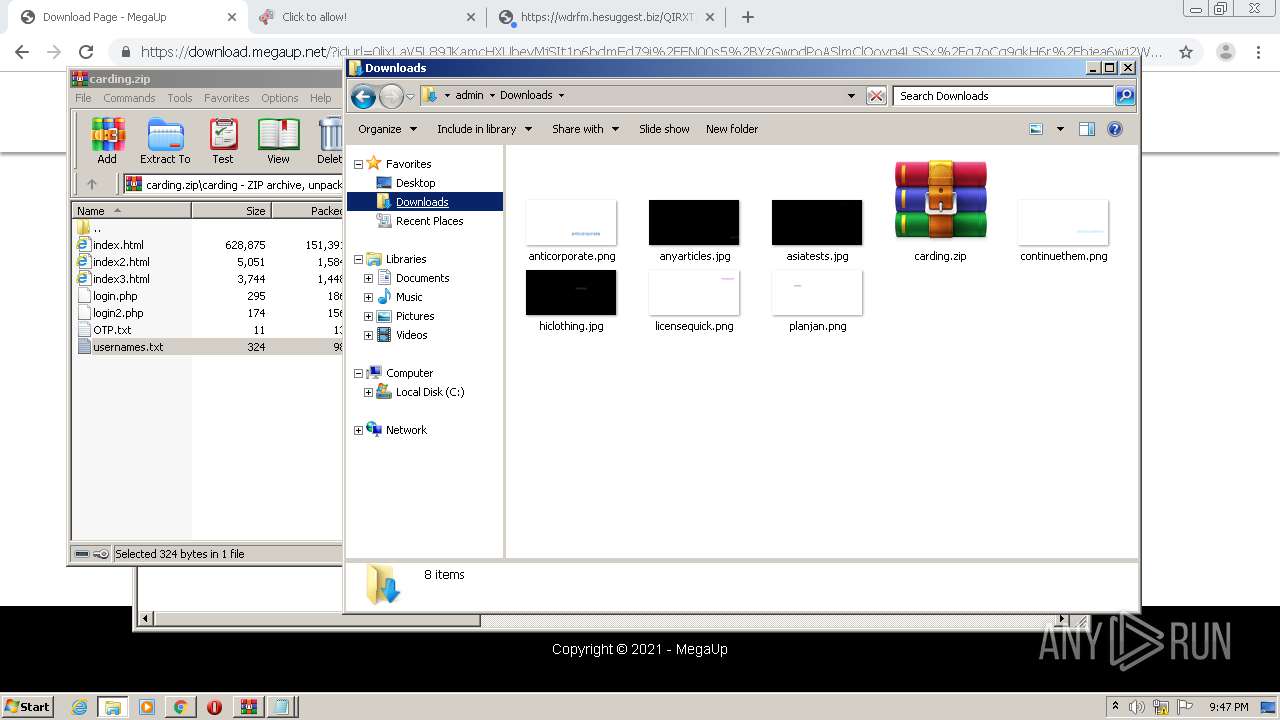
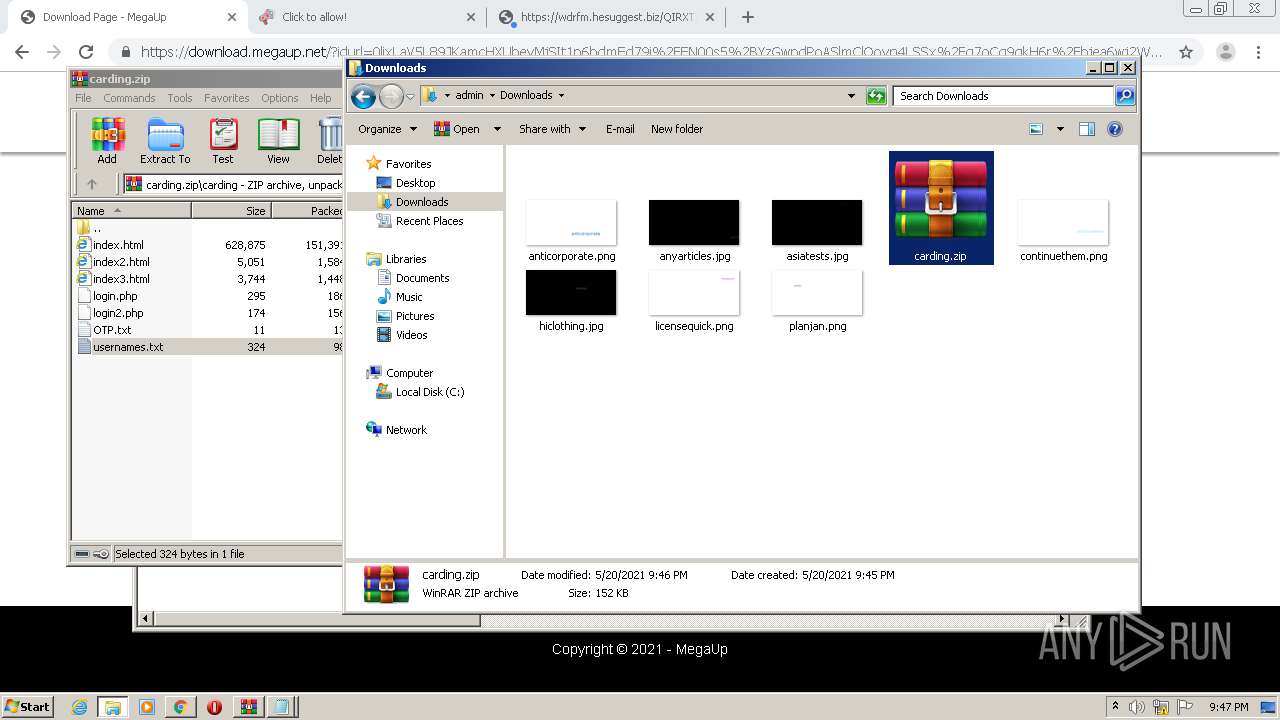
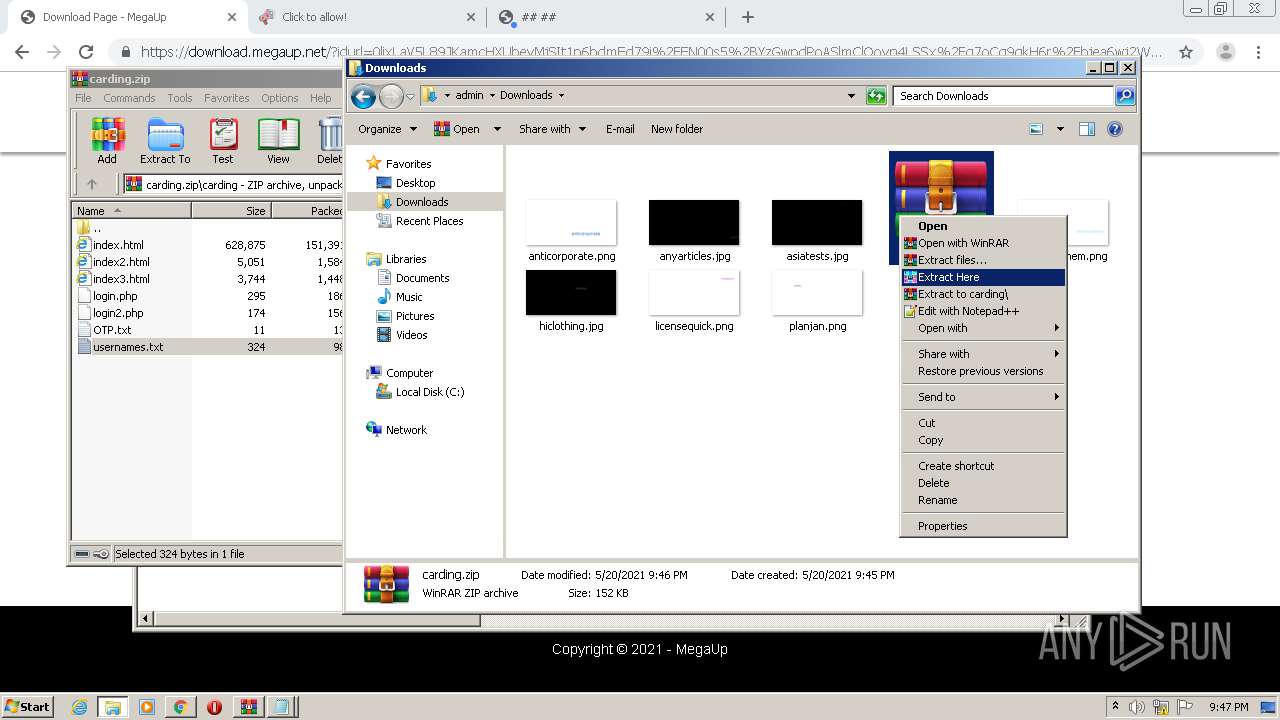
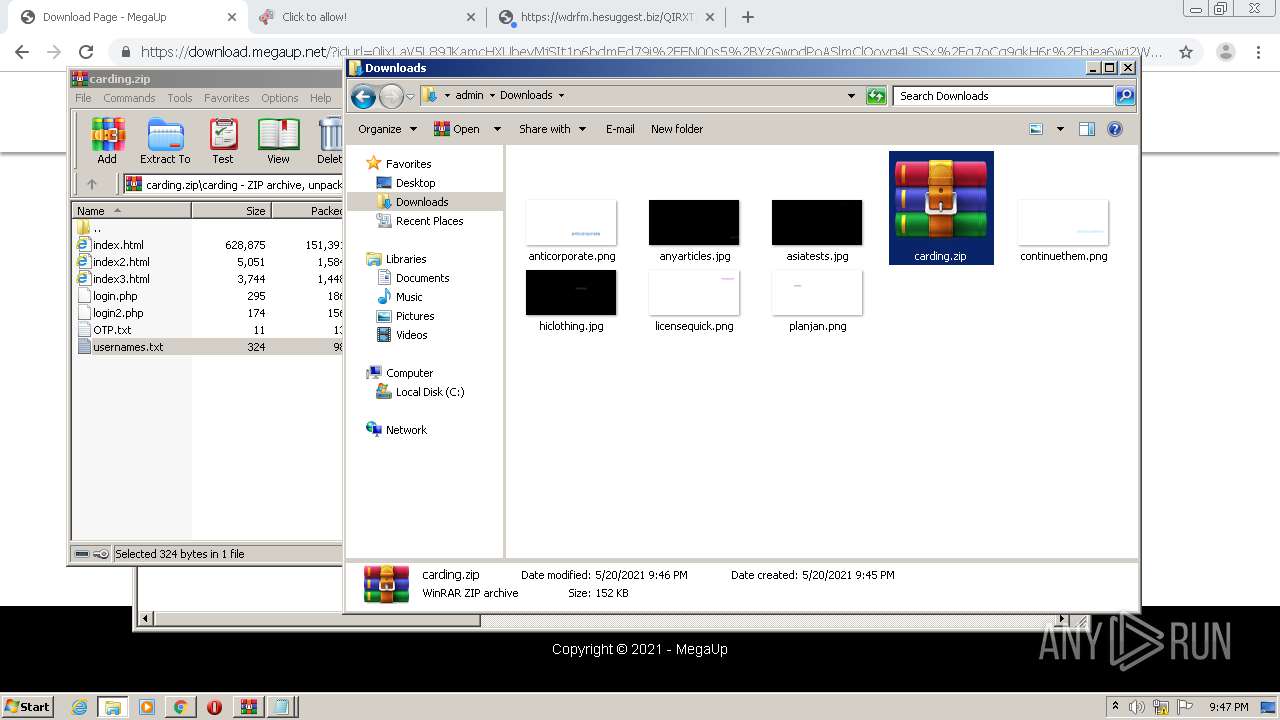
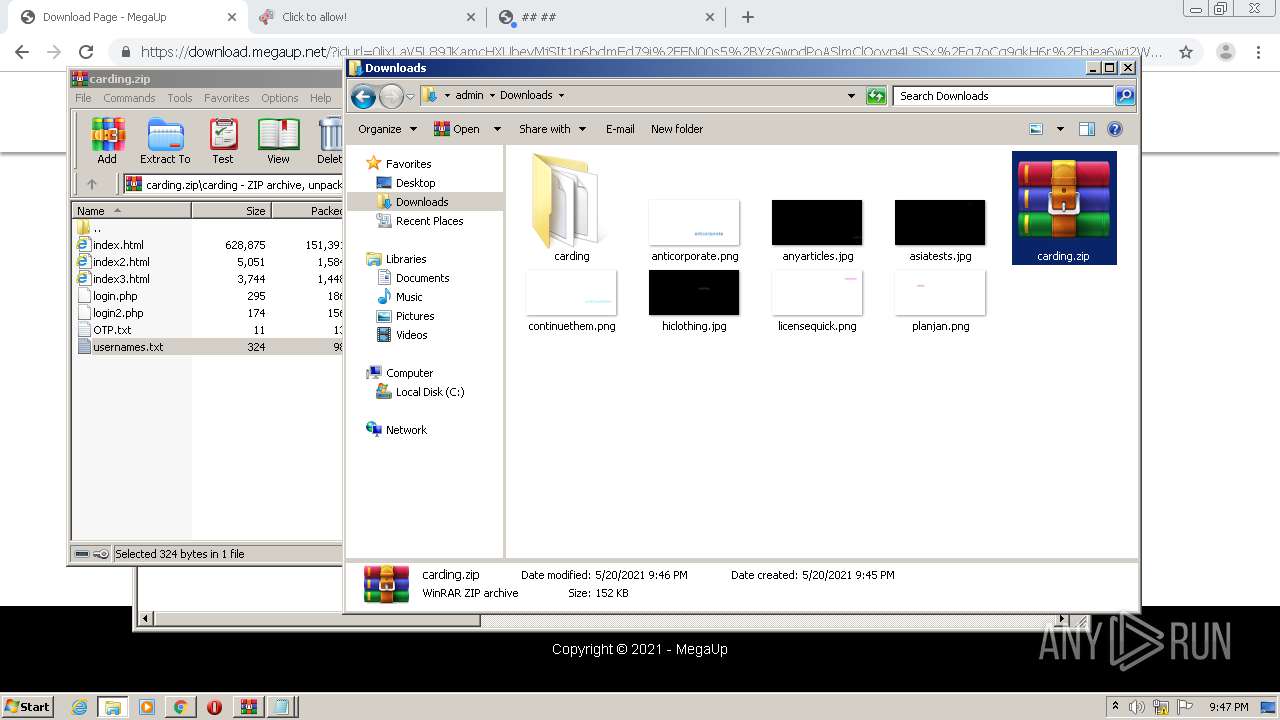
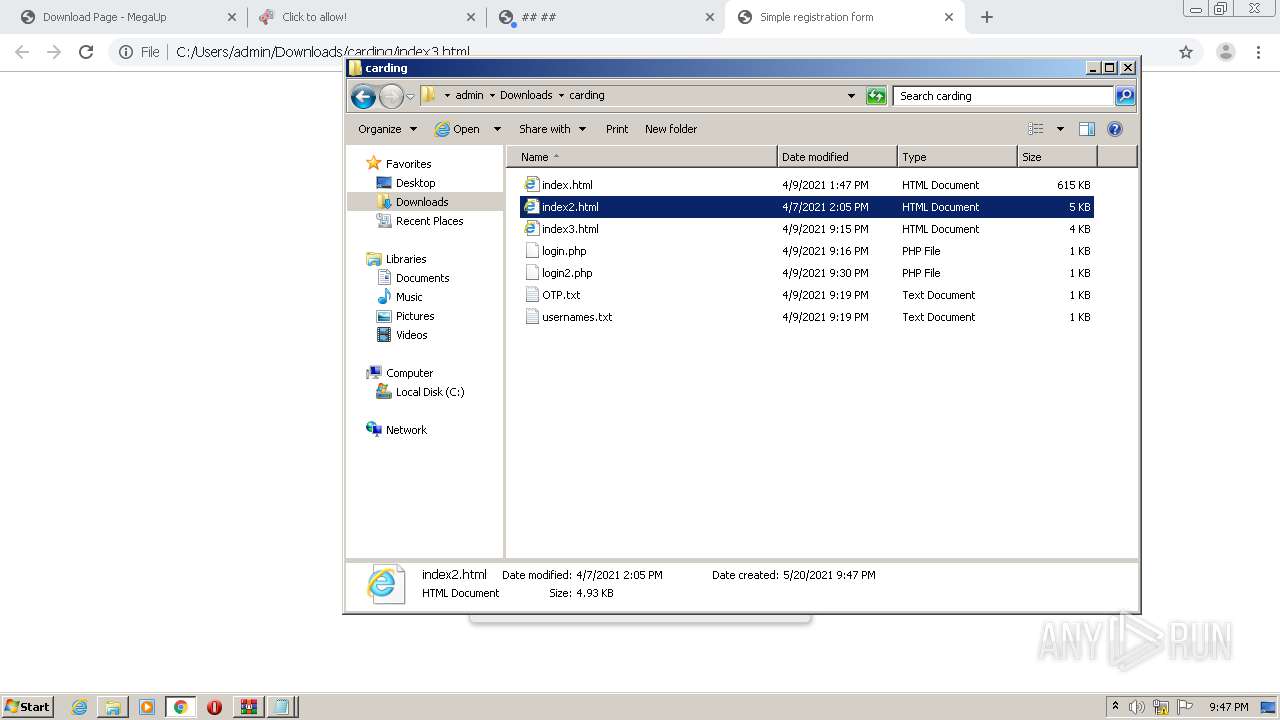
Manual execution by user
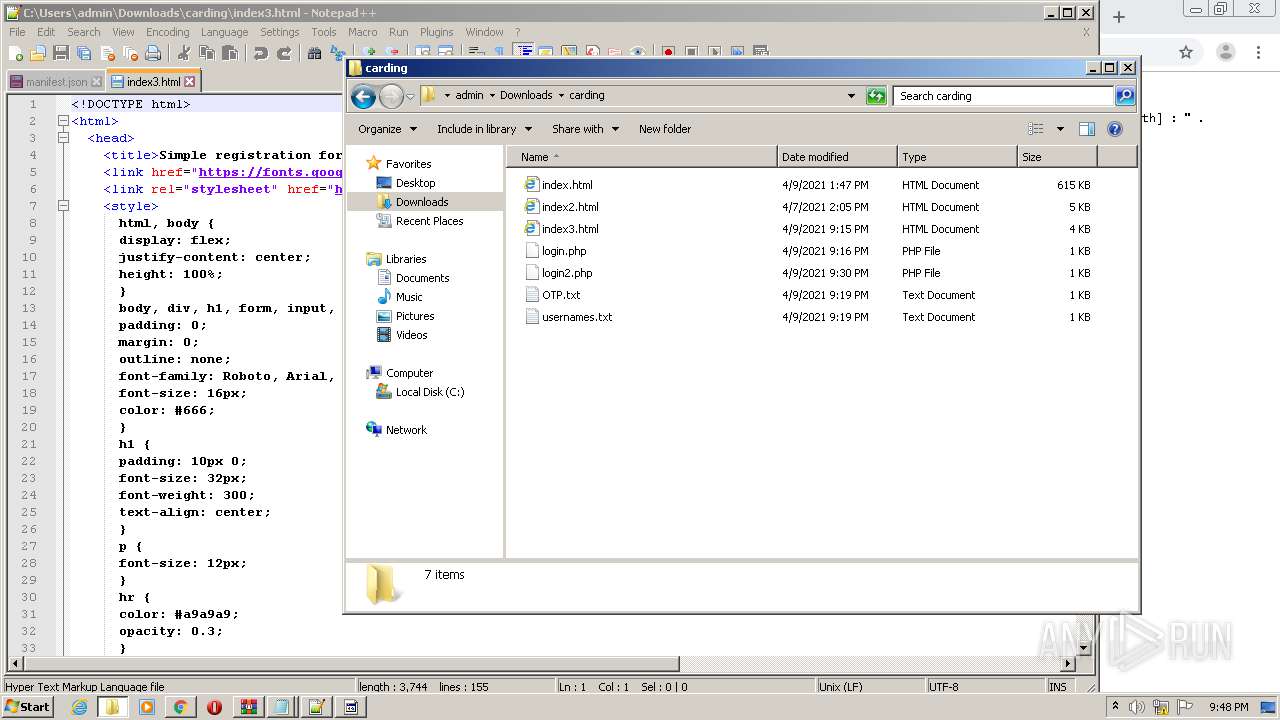
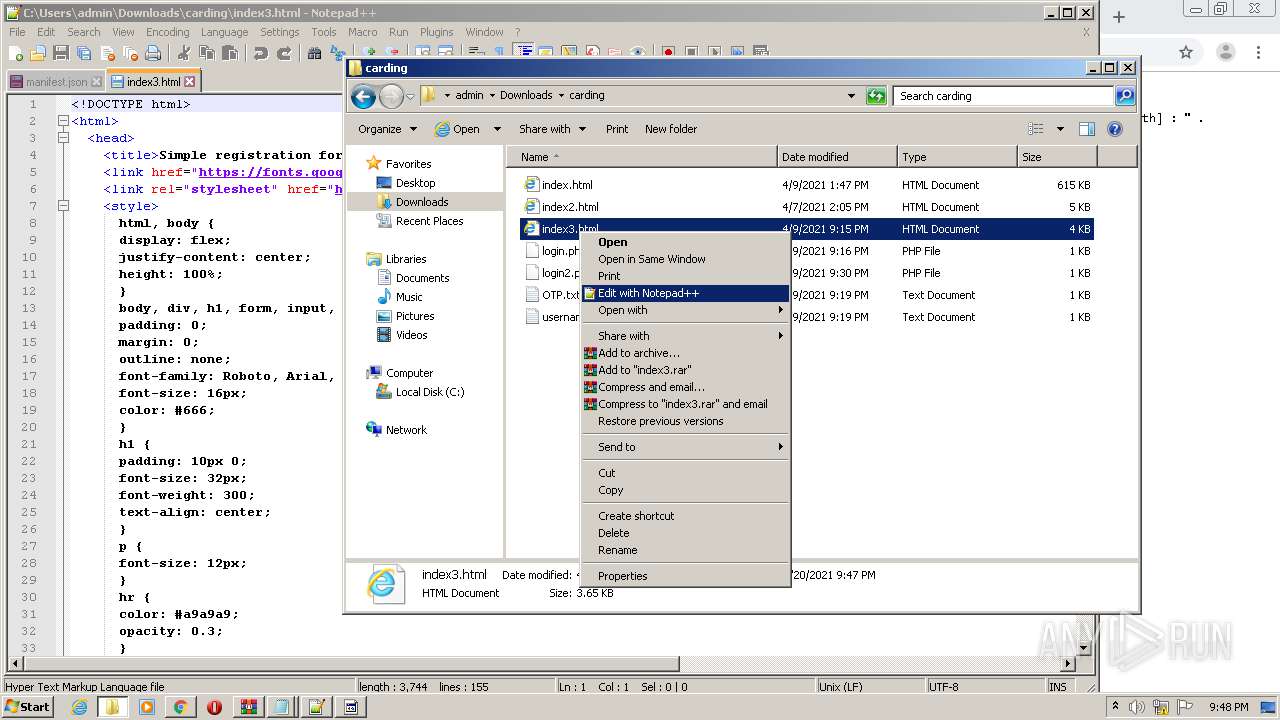
- explorer.exe (PID: 2072)
- WinRAR.exe (PID: 3380)
- chrome.exe (PID: 956)
- chrome.exe (PID: 2620)
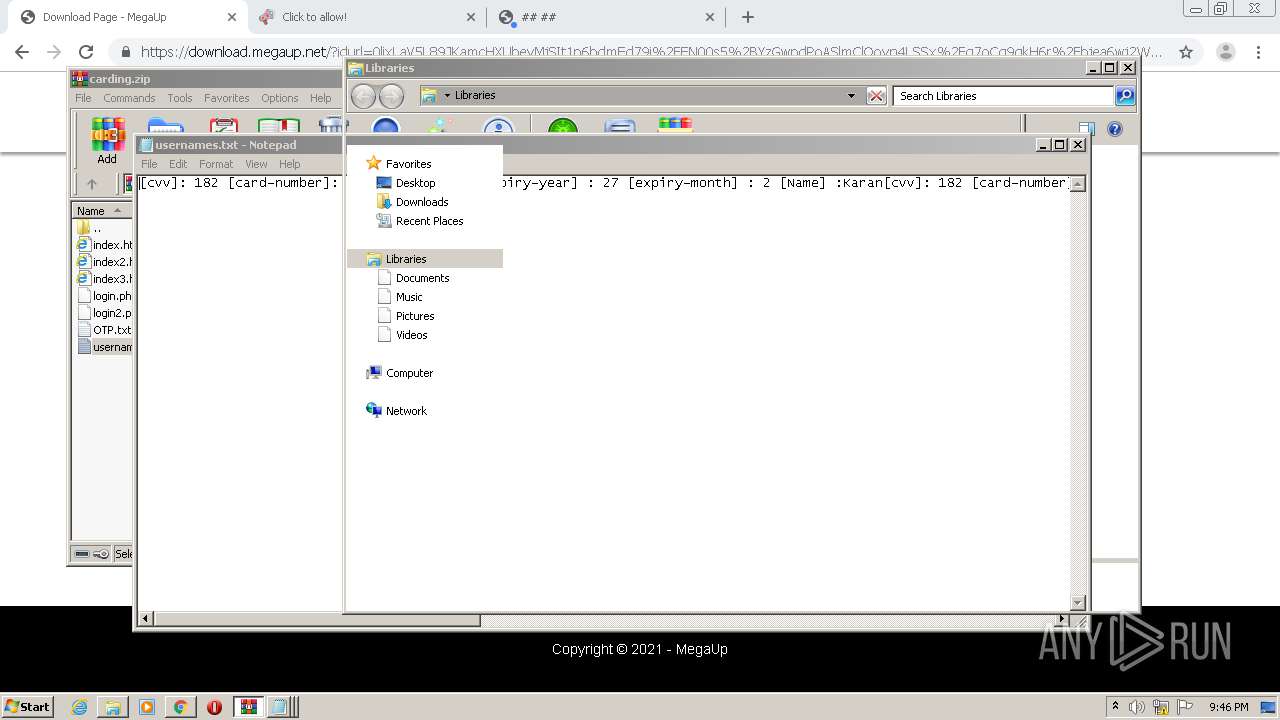
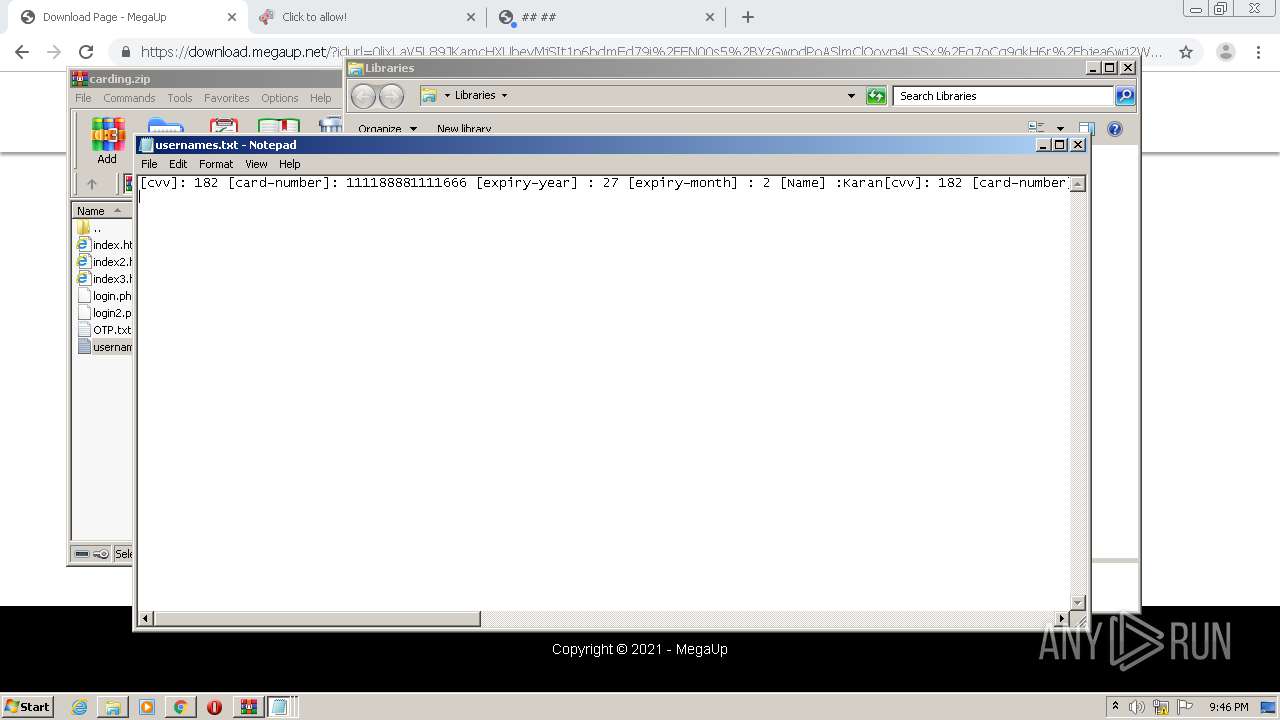
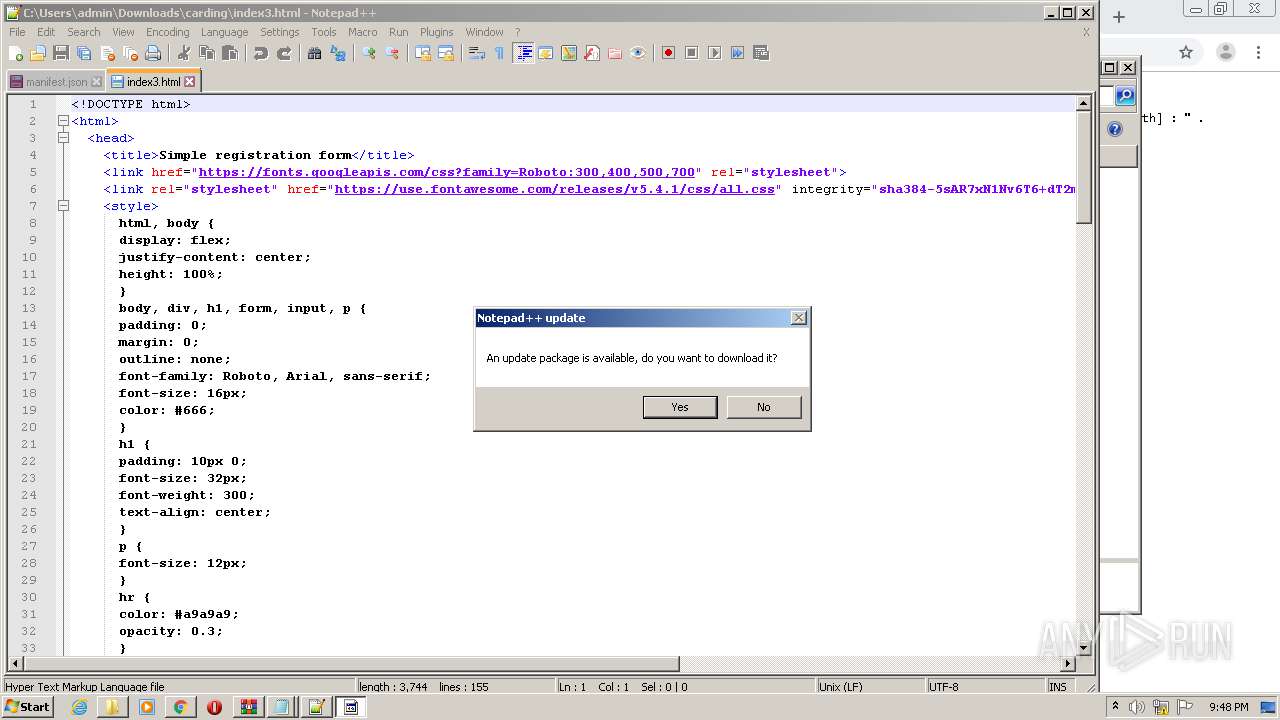
- notepad++.exe (PID: 1656)
- chrome.exe (PID: 4040)
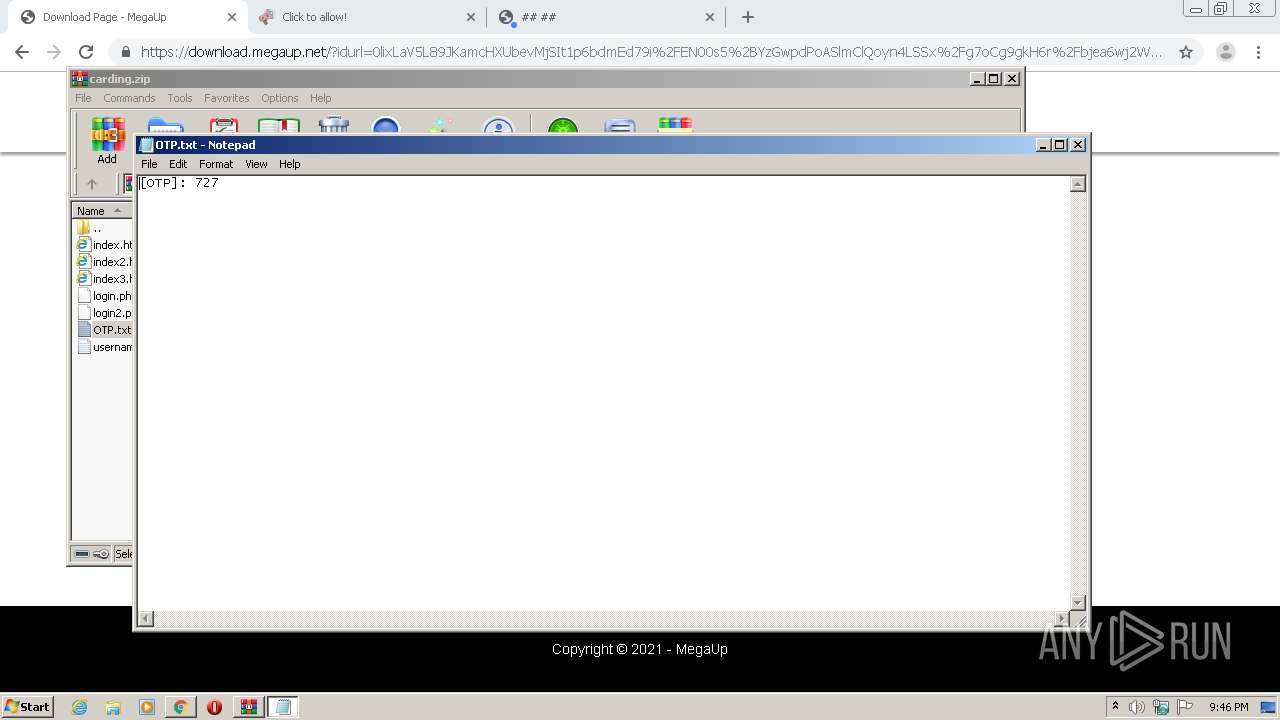
- NOTEPAD.EXE (PID: 2352)
- NOTEPAD.EXE (PID: 3468)
Adds / modifies Windows certificates
- iexplore.exe (PID: 812)
Changes internet zones settings
- iexplore.exe (PID: 3492)
Reads internet explorer settings
- iexplore.exe (PID: 812)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
80
Monitored processes
36
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://megaup.net/Wyvb/carding.zip" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 812 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3492 CREDAT:144385 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
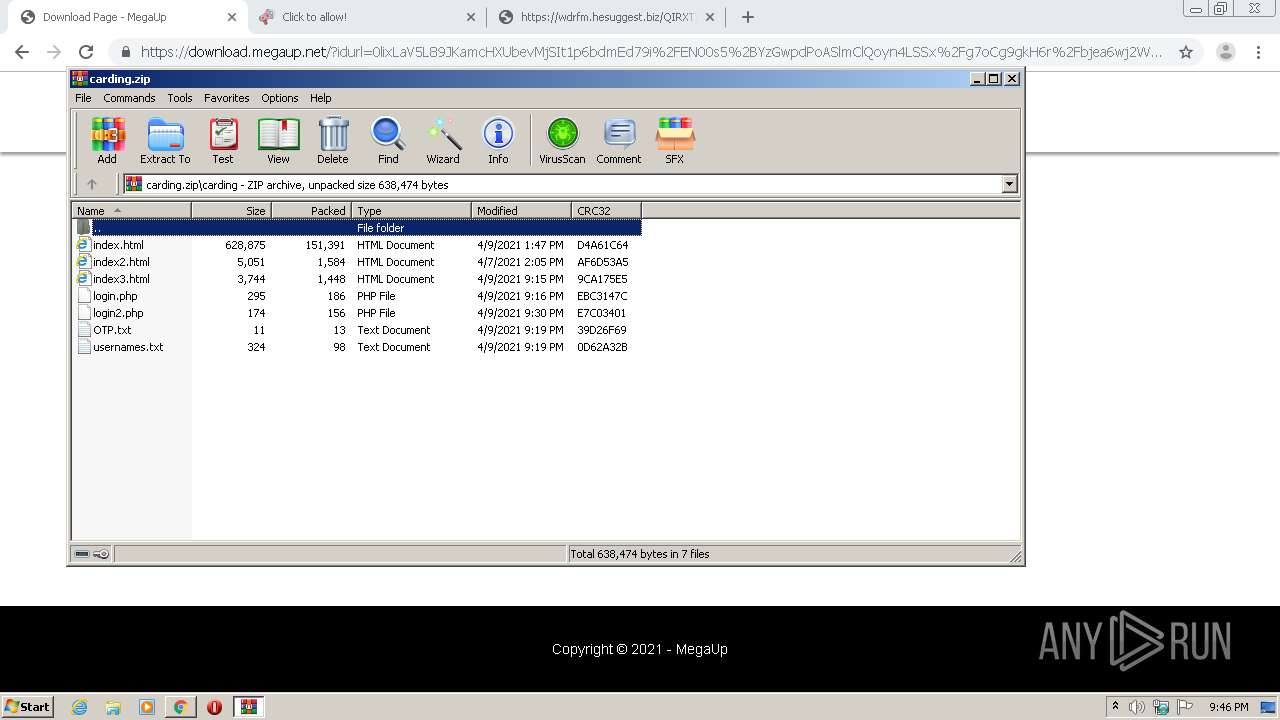
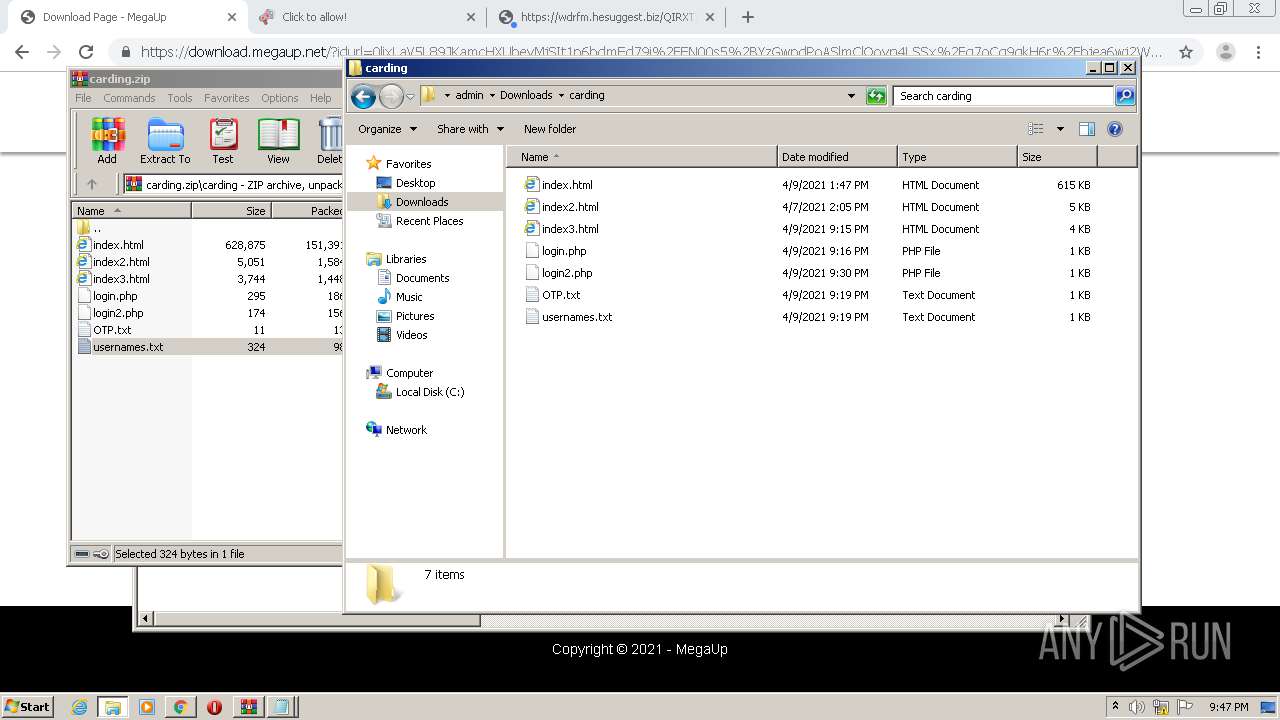
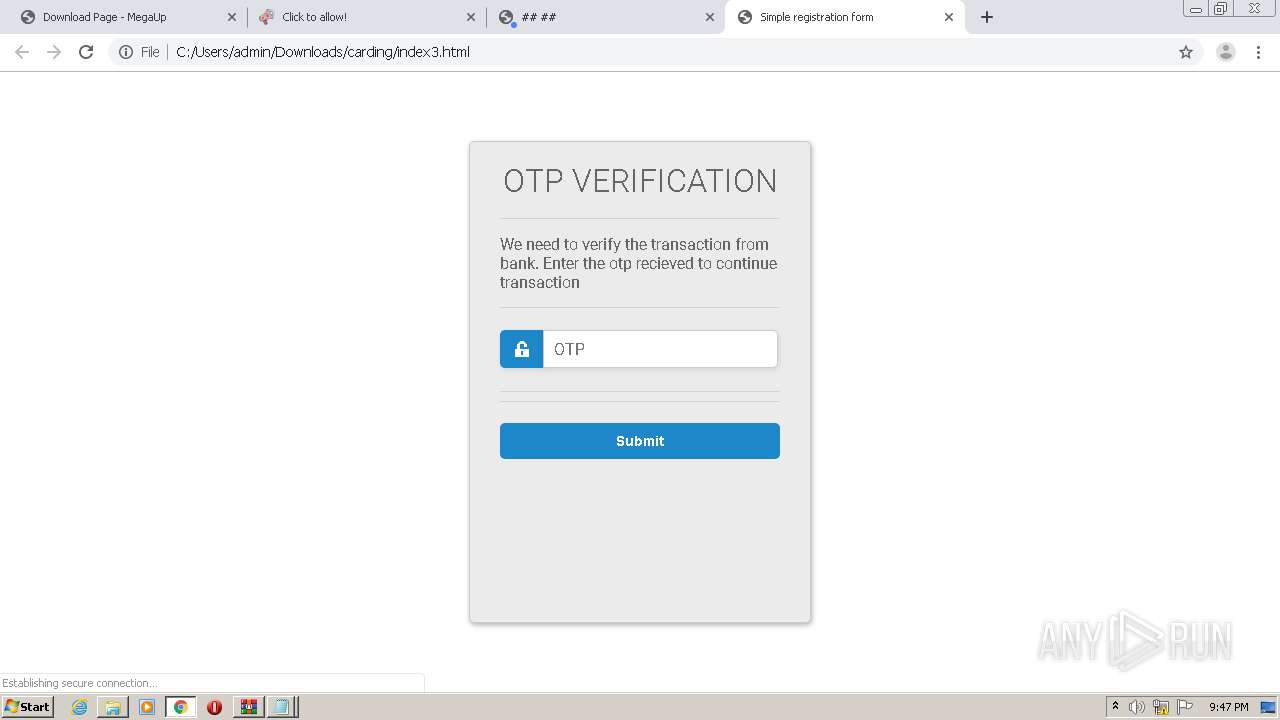
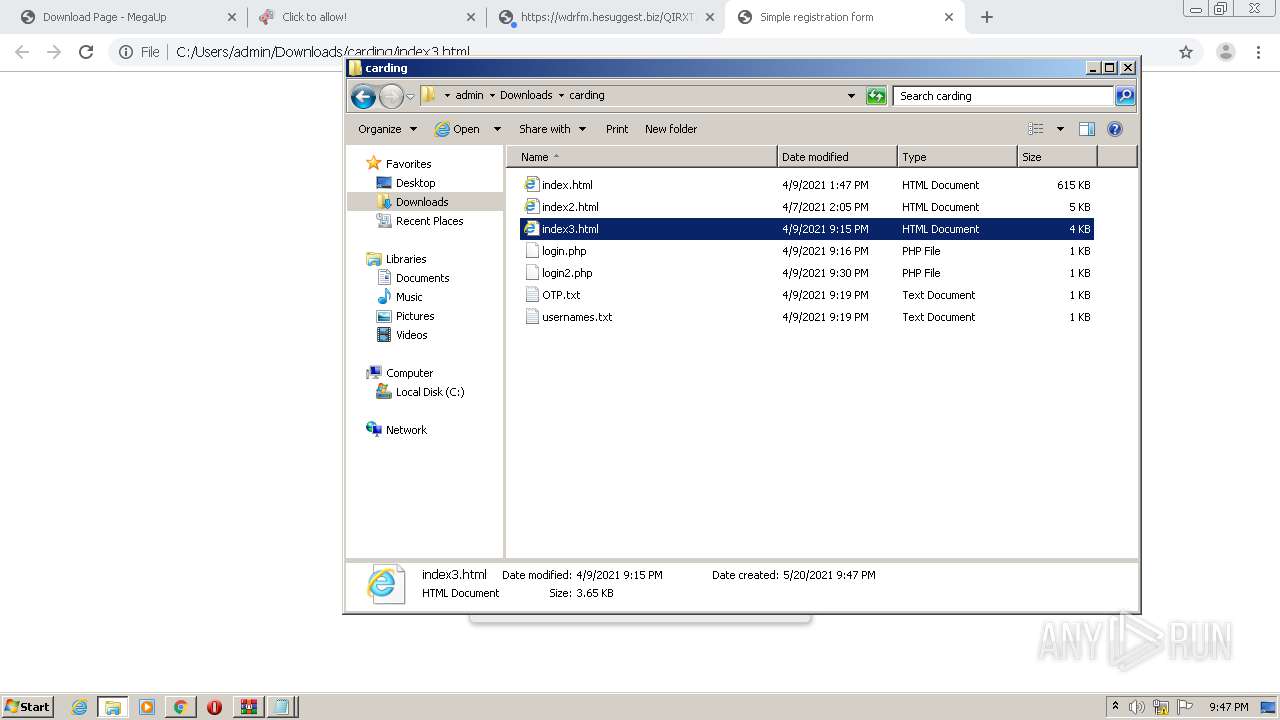
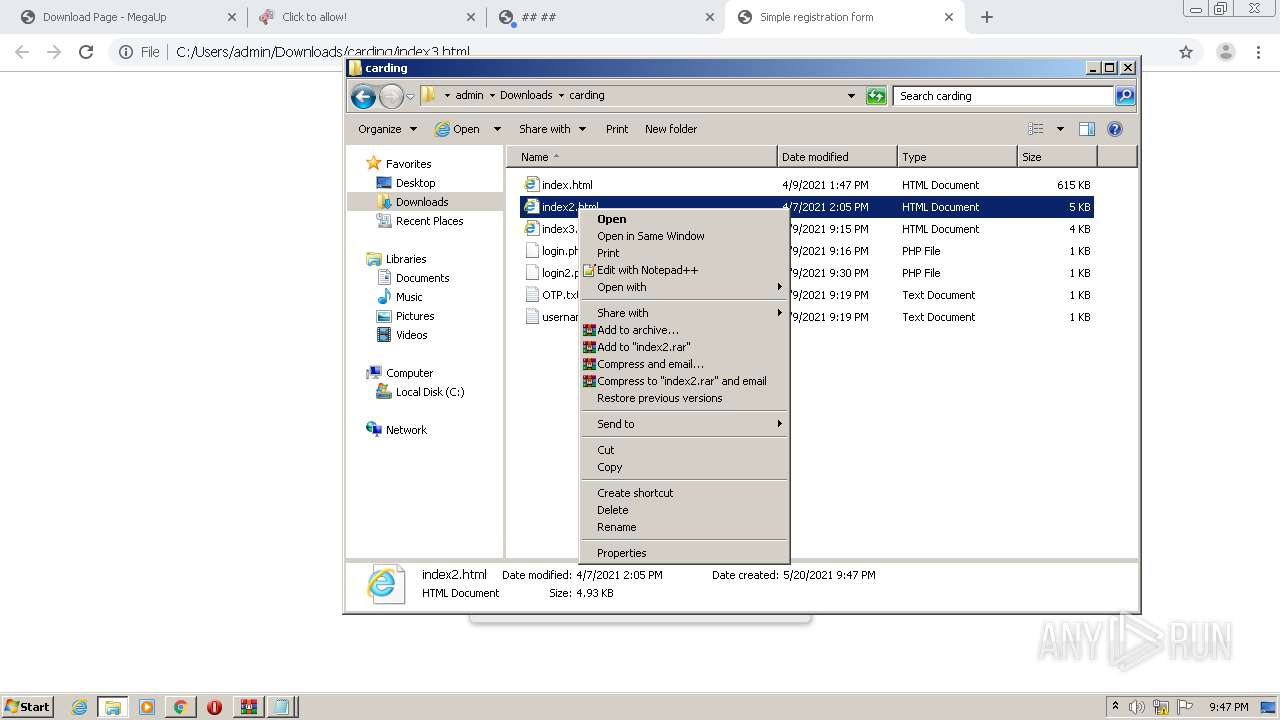
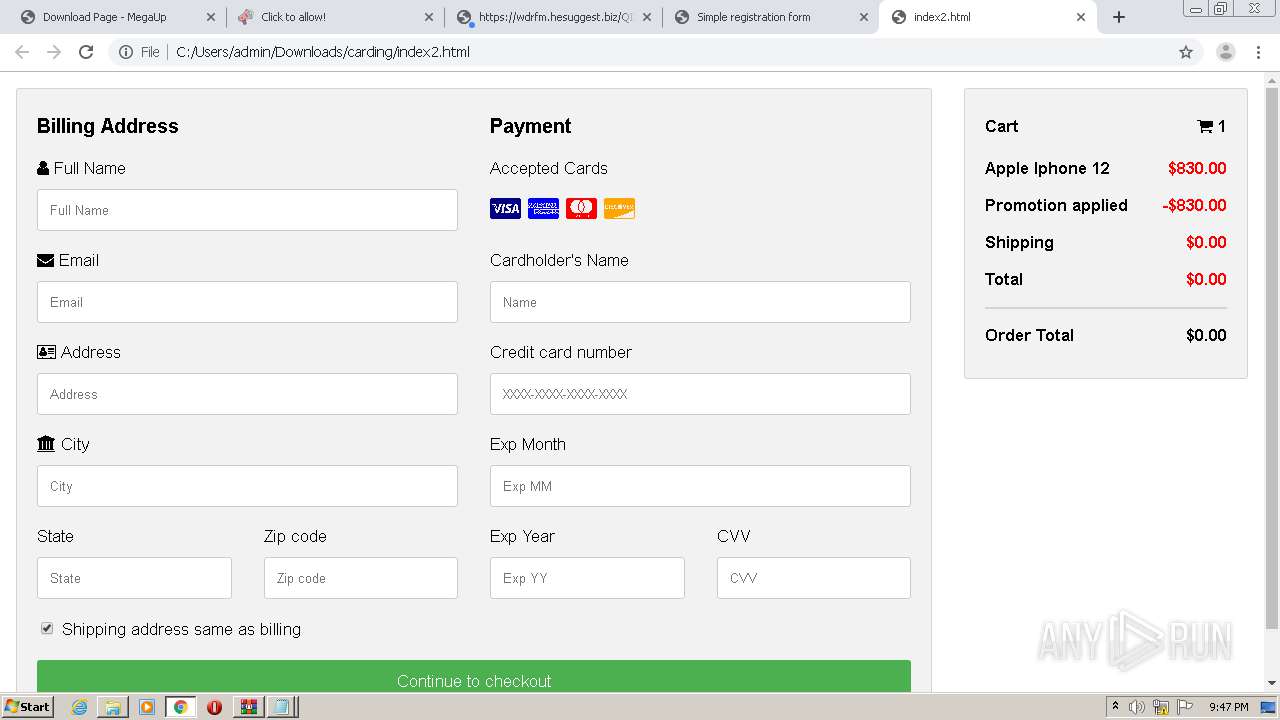
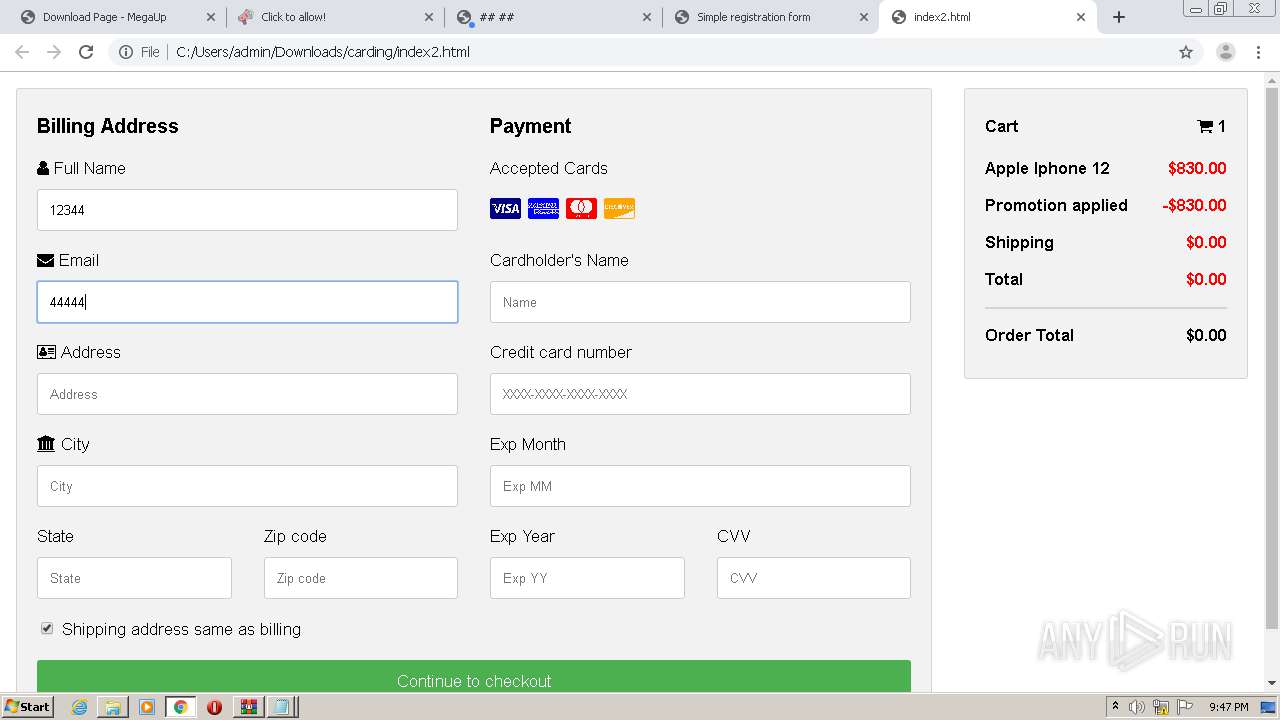
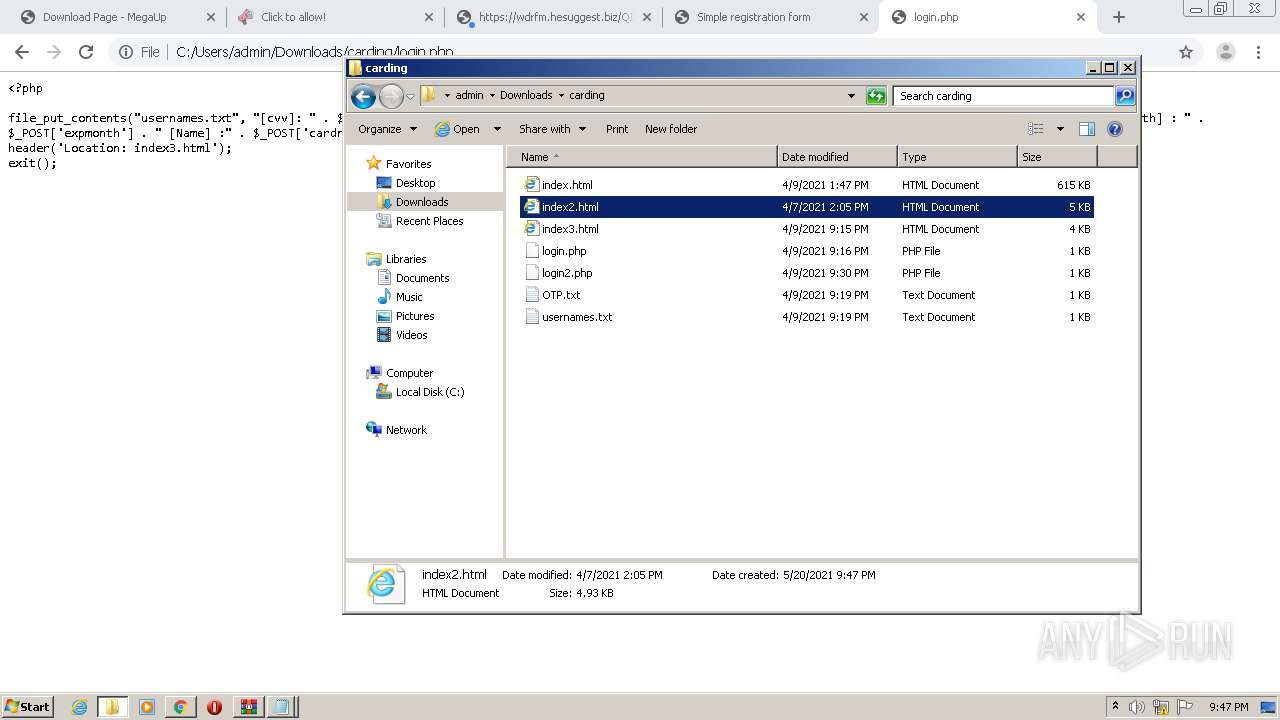
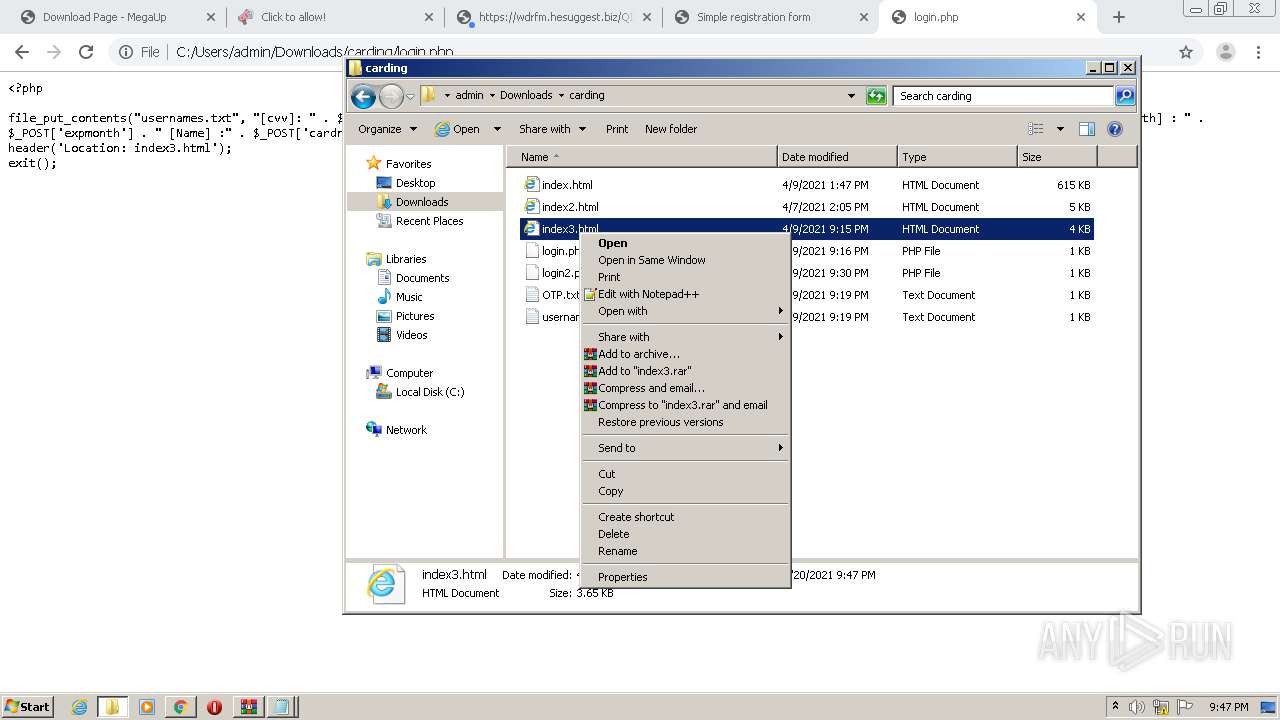
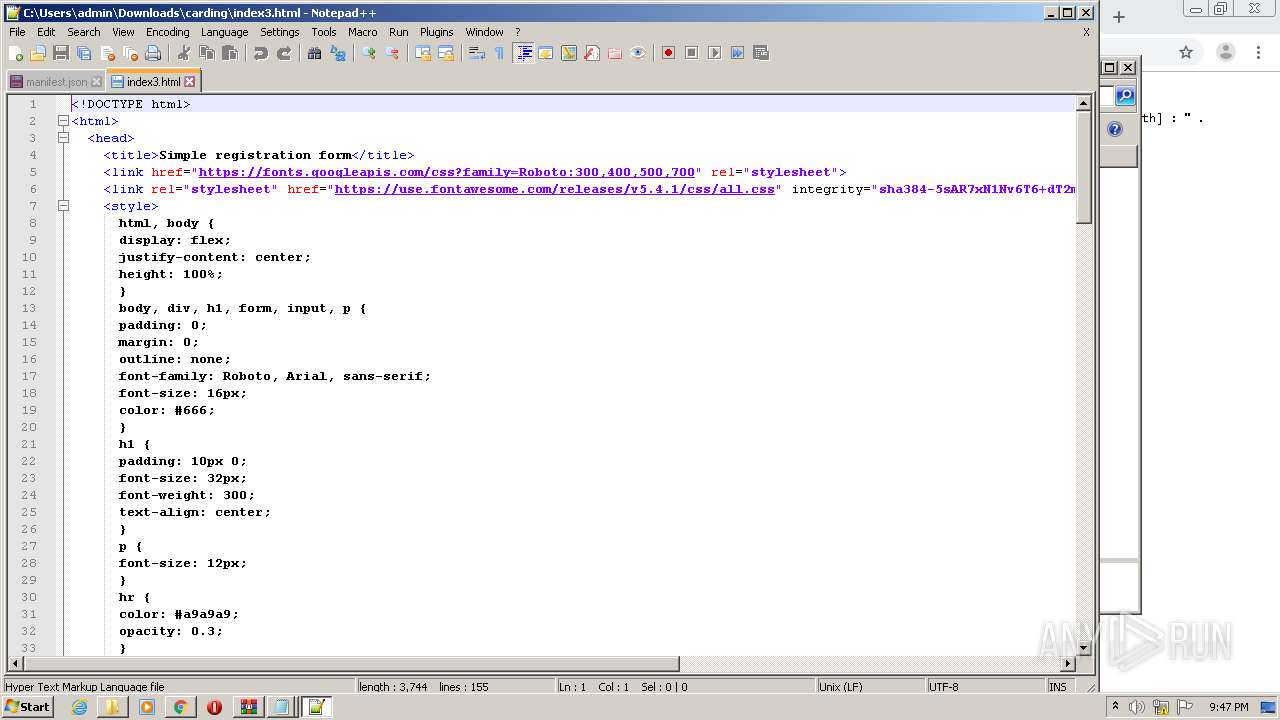
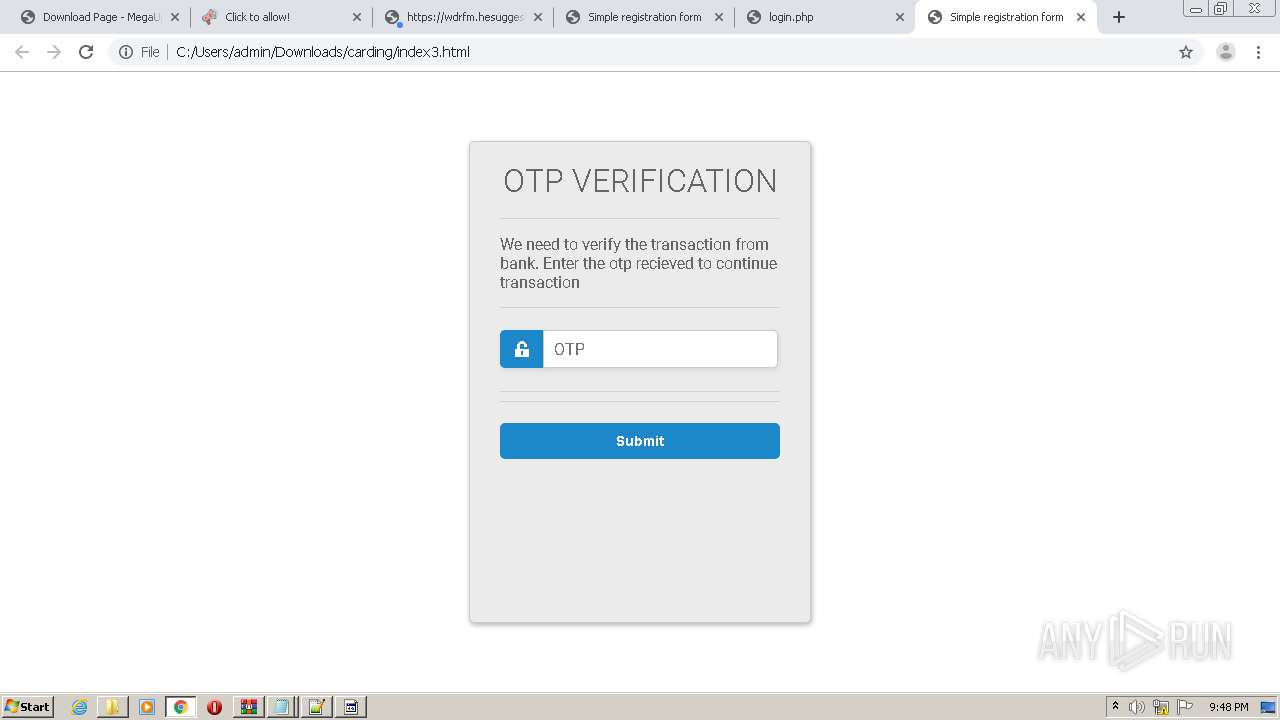
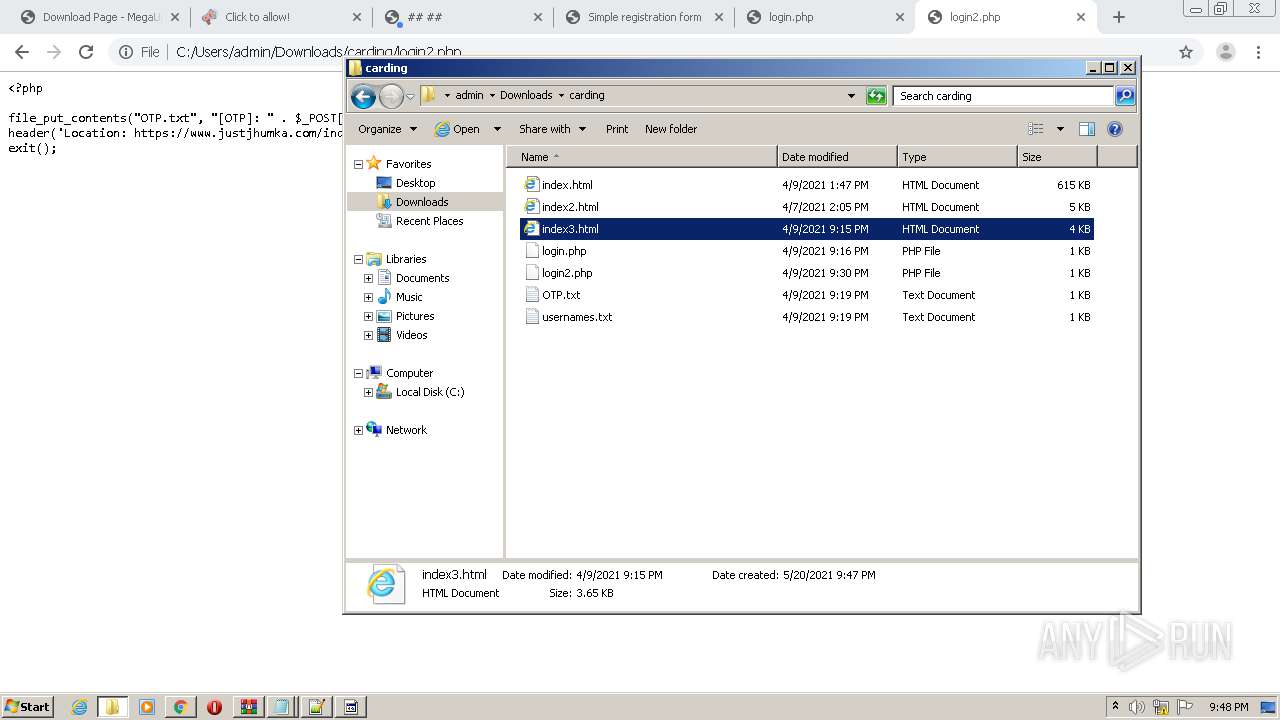
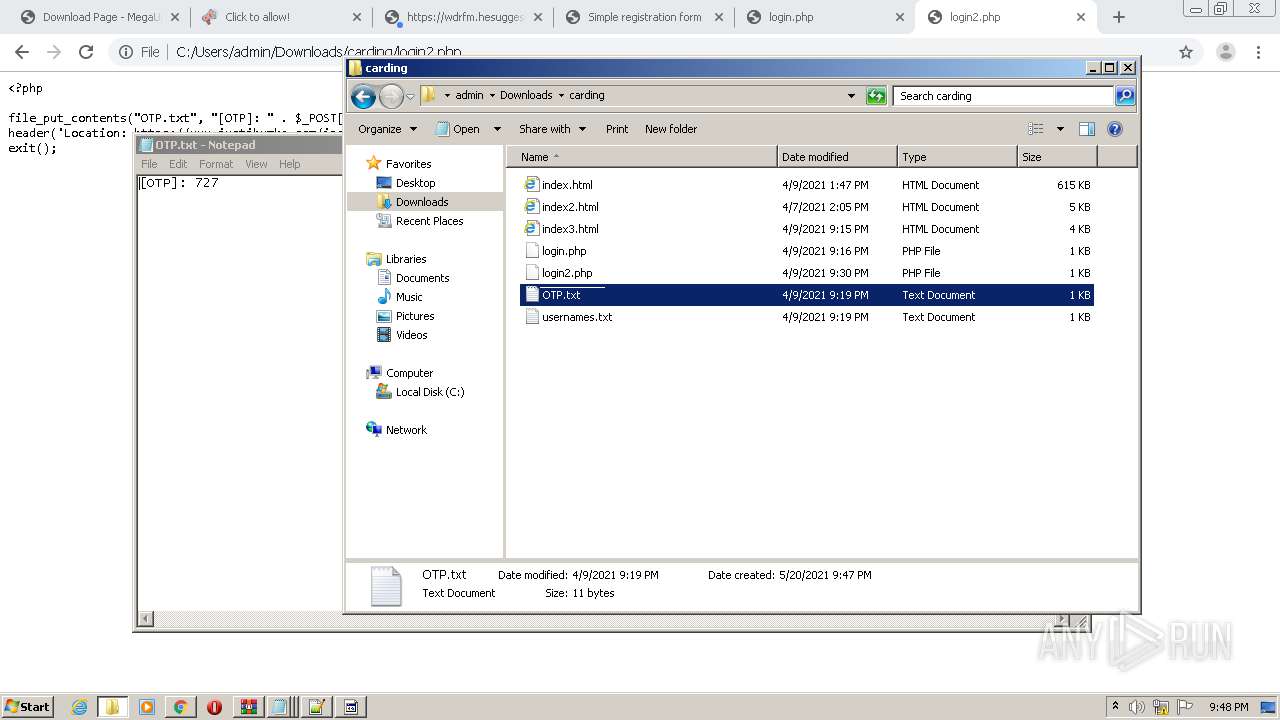
| 956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" -- "C:\Users\admin\Downloads\carding\index3.html" | C:\Program Files\Google\Chrome\Application\chrome.exe | — | explorer.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,8520630034932452218,9658611888261515032,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5808511231888892592 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2184 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1988 --on-initialized-event-handle=316 --parent-handle=320 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1384 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,8520630034932452218,9658611888261515032,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15902832028239837047 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2792 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,8520630034932452218,9658611888261515032,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9955420454403738406 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2360 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1624 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6bf0a9d0,0x6bf0a9e0,0x6bf0a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1656 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Downloads\carding\index3.html" | C:\Program Files\Notepad++\notepad++.exe | — | explorer.exe | |||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.51 Modules
| |||||||||||||||
| 1832 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,8520630034932452218,9658611888261515032,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7924992740685463909 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3600 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
12 193
Read events
11 992
Write events
194
Delete events
7
Modification events
| (PID) Process: | (576) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (576) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (576) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (576) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (576) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1184) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 576-13266017137516625 |
Value: 259 | |||
| (PID) Process: | (576) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (576) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (576) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (576) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
117
Text files
131
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-60A6CA72-240.pma | — | |
MD5:— | SHA256:— | |||
| 576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\9e73708e-3985-46f1-a4d3-50c2af5a2d39.tmp | — | |
MD5:— | SHA256:— | |||
| 576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFf05b4.TMP | text | |
MD5:— | SHA256:— | |||
| 576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RFf0611.TMP | text | |
MD5:— | SHA256:— | |||
| 576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFf07d6.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
41
TCP/UDP connections
119
DNS requests
63
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3956 | chrome.exe | GET | 302 | 173.192.101.24:80 | http://p203248.mybetterdl.com/adServe/adClick?ai=aMZ3O5C3_XuOOOAK9gPWUp-QRg5faAcC9DA5z6WpIa1PDtaXfxldUU9xO0kmet_HlyUsbmo7MNZeImf_cJChhlilzreV8_GPnF2ENxXJkWhqgEE0f5Fjh8XnLiFpVgC8Bvf4RIcbQkeDZG8TCuTZ6pDoEwlyap2kGfOJDaetLPU7Nqb57KegJApS280DUX4uMVooT7XZXmbz2v3qS6KuQKwWcH55acyZA6kszsKrsACqe2y5QePb60iNZi4bObC81QlvVKC08ytv0-cfxRgHaSCijZY_SNQadM5ECUeELJfkQmjZE96sjp8DPbGbSNtJN0JJKTQdChujiGYQ-VGfM1BKQ8__OyXIgafZ9sDvHt0Fy9LbfW_6duFoOnPfBtp4nikxEDznWgUW0YeVoTdAMXo_8JgIlG3qFgRrt2Me9tiD9H7QO_kArl5uhZt-QnVQY1pRSQ8gFb5lkkLEB146pQ&ui=N0ohnK6XOmcH2x8FQqAWwgcsWc8-Vo_0IaIc3yOo5HJlUEpXMvk0BV56A2kKRg1gEqG3jGFVeGdqu5qkuQOAxJBdcE_XSlqi_pJymkeCvfB8XW5UpuGsiw&si=1&oref=1ba79dd970b9a0c073e9df641a7ee943&optunit=sNOoY4uUFdgO3saqVkE20Q&rb=Y7rCTiHgJuA&rr=0&isco=t&abtg=0 | US | — | — | suspicious |
3956 | chrome.exe | GET | 302 | 173.192.101.24:80 | http://mybetterdl.com/aS/feedclick?s=N0ohnK6XOmcH2x8FQqAWwvRohOIAQNxpk1tebTgoDTt6b6d4apTbbLUC6hWIeTga6IkCbg7sKEuYDMm3vSUGcDcdXBK6ua5HOB2e7s6wLdtSKyBRczvj6sZTps4EeX4dsOyE_yhG9DLGVWViaJip_rcJ2ubPMYW2f1-_Vn8uwdc1Yfmvyh62NXe50VyfA5IFpvjfm5yPcSqJKKBKyHrvpkl1UXQ6558iJOlLfK4fNl9LJZhOolNafBjWjGPG_SWSYUZQkWSuAyvBON-B_EYntlc8u5zsipgJyD_rwpcIZQK8t8dhlsFLTmm780GQ81AmgPixy1Px7aeUl9o-xDkTKykI5envOLf41YQWgG4Rdnv4erNIOuO3tj4vYNzFECESTT6vMzMSs4xU5qjp7dLJ5VufklTVvU4Qv736hQykl0HaVsnpF26cAdfqgFZN0DGgnPy_KWp60_jutQ5Krdu8xBr43MkSCh3xvk0Wbrth_xo-ebbsA-GILdcibKjoh3amWtSUVesa_wXWplXpfRIr5Xi3w6KK6coFN-wIKG6XTySB3_pEhVCdOp_eyaRC6IUiKRDLAQ_F3x3fi0DAJIJYMa2hVweOW-Q2xdM9P3GwyKn8cf4-8E5tE7-X4fvdqopAzMBxJNf0xDunTE3oZ4NcgKfxaUl8cmtZTxAMZBiWsCk_1bzWt1N49gwl_w8Y2W_iDeuslyM8qYi-MhHHSpeSliMQP1LutzMJxwHhz_8ss4UqJNZ2gUkk1iJDcGGXJkxTgUG6_lkpn_UkOAaZARvAF-nH1O-TB25_qdNN0_Hiw_G0nGA3rPGIy0oauXHoWT4nGQJlr_Gu928L0CgmAWnYUteTxqsJ0jetMQYPw77TaCj6Id4RkvjWV2fblvcVN9yt9NZIUYNt7SCacyncrmZMKTRHxEvUKzLwzJsajy9_T7RX1EnojRwa8vpNs769ub8kJA-1dwlN5xD1m_shszUmxgW8rS4VEK1V6VEqlbyUo9pCu43q8rwTrgbqjLGgXLS9jDK34kTa-WG5-xlGe0EOpU80L84loquu401UL1S-EnCJFjao_sy4tafGVHR6c0eYcOYCkv8TSN9Oz7KUuHHuSEbPer4OrbqzsXngl4p5u5rKWmpwAowHldcIkSucK5ukEaniU6UPjfGC_CWRXp1kiFVcKnJdReypQ_kHyAjmZhkydZtmbf1h5w29jZySgQugC7Z5TUhZrstr5m79qHyfiX0TFX0lZ8JGQWuAvdblqVt0pTEhBeym1bDixCwEi0T2iY-C3aJegNBcfx0th3Q4kX5XNGcGrSMJezX5AHmIAixG5d8NeutwDXIOGrMJhF3pZZSIozchMvjABcuF-dFI8f1-u829ws8dcHIX1IdBO5DwQysScRYEKwA4plQHA5K8iCqxQydHdO2S5m9l-W3BaD69w8zPi-QLzK7xSCmorLnGIxV2e1cjGw | US | — | — | whitelisted |
812 | iexplore.exe | GET | 200 | 23.51.123.27:80 | http://s.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCEGMYDTj7gJd4qdA1oxYY%2BEA%3D | NL | der | 1.52 Kb | shared |
812 | iexplore.exe | GET | 200 | 23.51.123.27:80 | http://s.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCEGMYDTj7gJd4qdA1oxYY%2BEA%3D | NL | der | 1.52 Kb | shared |
812 | iexplore.exe | GET | 200 | 23.51.123.27:80 | http://s.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCEGMYDTj7gJd4qdA1oxYY%2BEA%3D | NL | der | 1.52 Kb | shared |
812 | iexplore.exe | GET | 200 | 23.51.123.27:80 | http://s.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCEGMYDTj7gJd4qdA1oxYY%2BEA%3D | NL | der | 1.52 Kb | shared |
812 | iexplore.exe | GET | 200 | 23.51.123.27:80 | http://s.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCEGMYDTj7gJd4qdA1oxYY%2BEA%3D | NL | der | 1.52 Kb | shared |
812 | iexplore.exe | GET | 200 | 23.51.123.27:80 | http://s.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCEGMYDTj7gJd4qdA1oxYY%2BEA%3D | NL | der | 1.52 Kb | shared |
812 | iexplore.exe | GET | 200 | 23.51.123.27:80 | http://s.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCEGMYDTj7gJd4qdA1oxYY%2BEA%3D | NL | der | 1.52 Kb | shared |
812 | iexplore.exe | GET | 200 | 23.51.123.27:80 | http://s.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCEGMYDTj7gJd4qdA1oxYY%2BEA%3D | NL | der | 1.52 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3956 | chrome.exe | 143.204.101.97:443 | dmmzkfd82wayn.cloudfront.net | — | US | unknown |
3956 | chrome.exe | 91.212.150.173:443 | megaup.net | NForce Entertainment B.V. | RU | unknown |
3956 | chrome.exe | 142.91.159.115:443 | keydawnawe.com | — | NL | unknown |
3956 | chrome.exe | 104.19.134.80:443 | jsc.adskeeper.co.uk | Cloudflare Inc | US | unknown |
3956 | chrome.exe | 142.250.185.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
3956 | chrome.exe | 142.250.184.200:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
3956 | chrome.exe | 13.225.74.39:443 | apsstoure.biz | — | US | unknown |
3956 | chrome.exe | 23.109.82.74:443 | altowriestwispy.com | — | NL | unknown |
3956 | chrome.exe | 143.204.98.52:443 | rdifferenco.club | — | US | suspicious |
3956 | chrome.exe | 104.21.63.78:443 | freychang.fun | Cloudflare Inc | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
megaup.net |
| whitelisted |
accounts.google.com |
| shared |
dmmzkfd82wayn.cloudfront.net |
| whitelisted |
altowriestwispy.com |
| suspicious |
keydawnawe.com |
| suspicious |
jsc.adskeeper.co.uk |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
apsstoure.biz |
| shared |
amorphysp.fun |
| malicious |
rdifferenco.club |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1040 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1040 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1040 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |