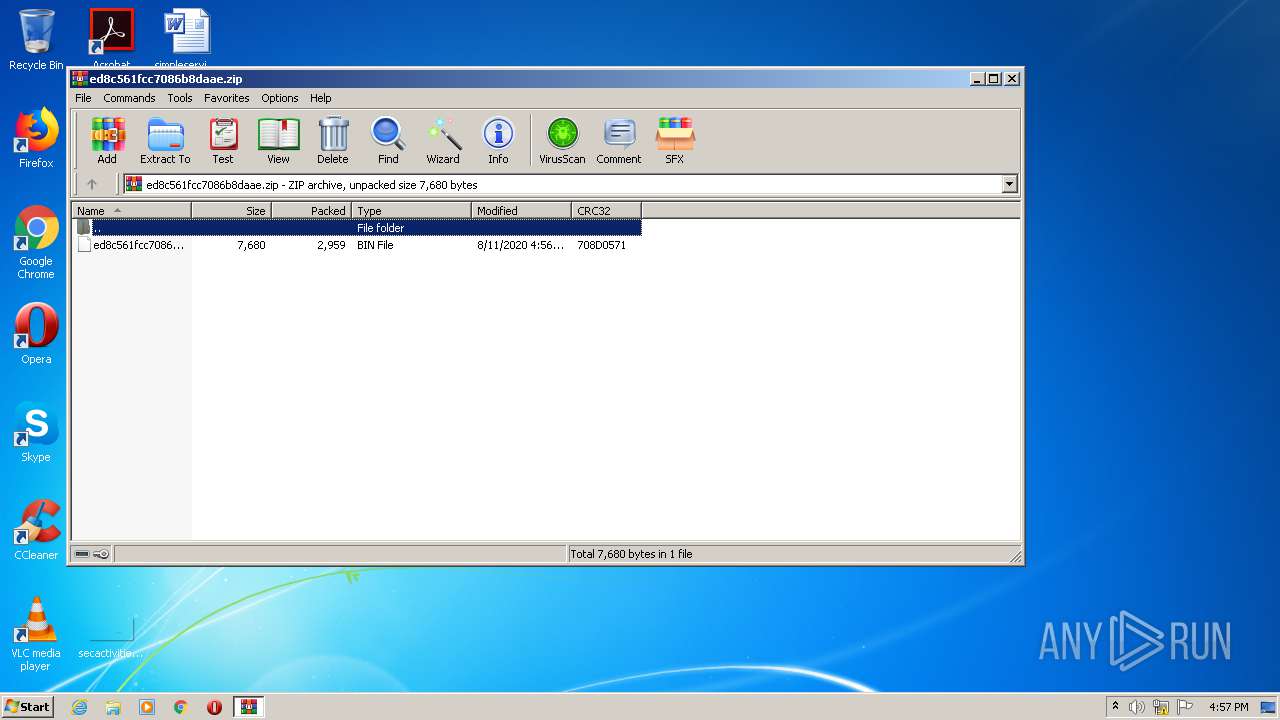
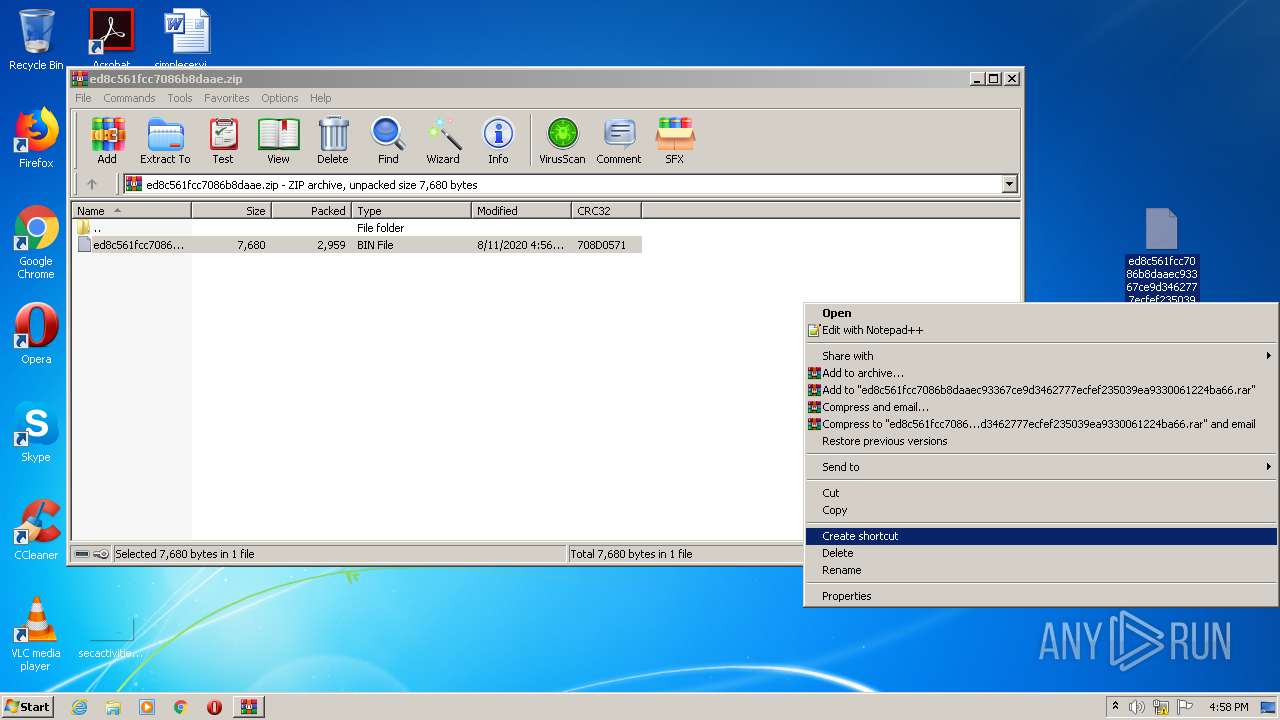
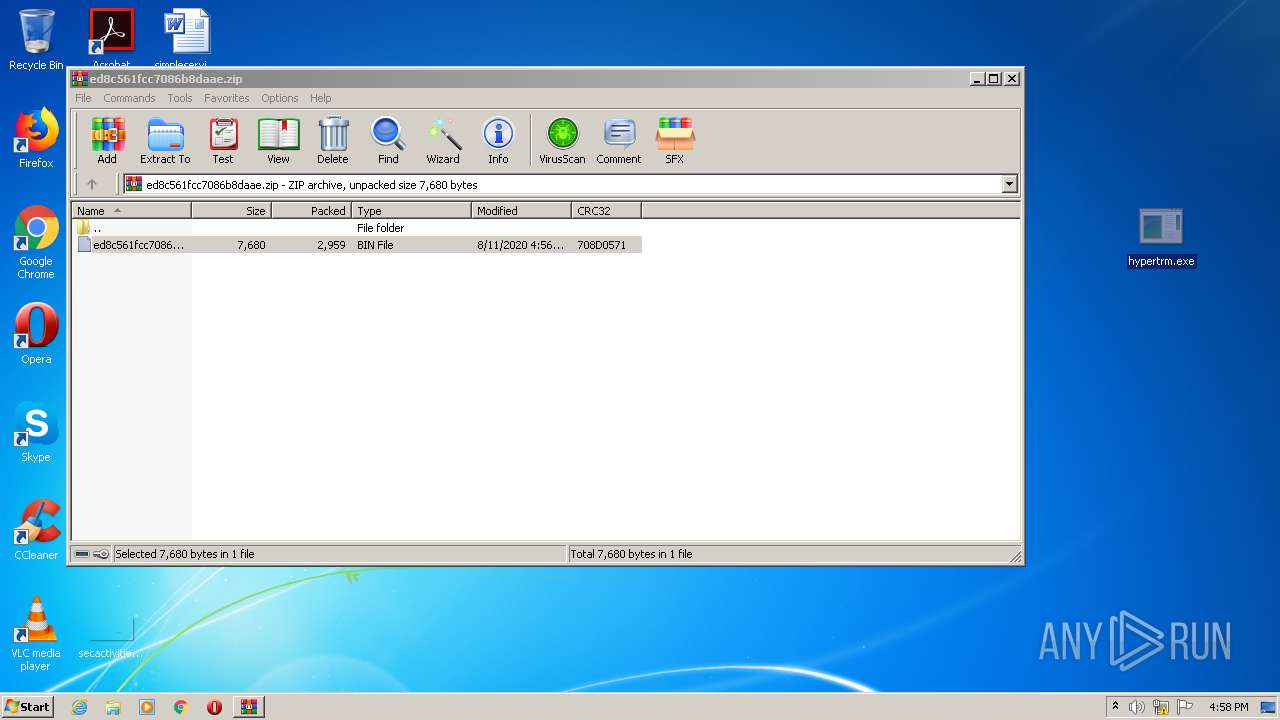
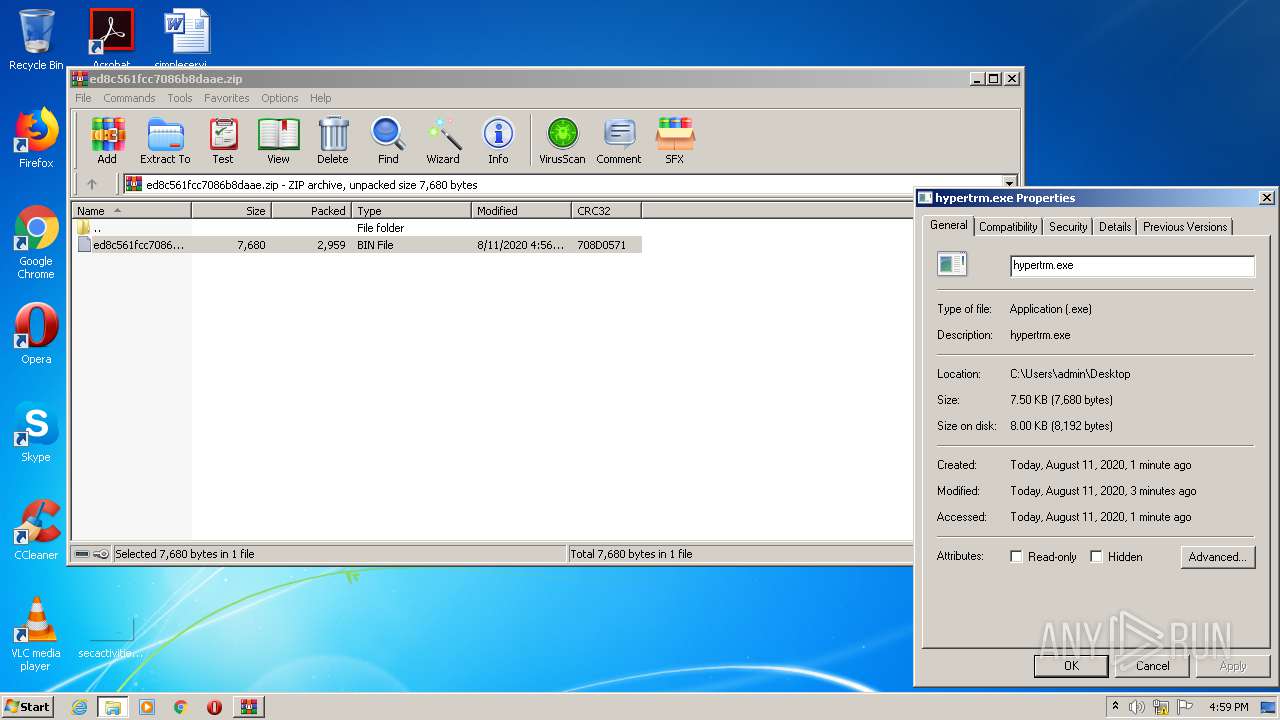
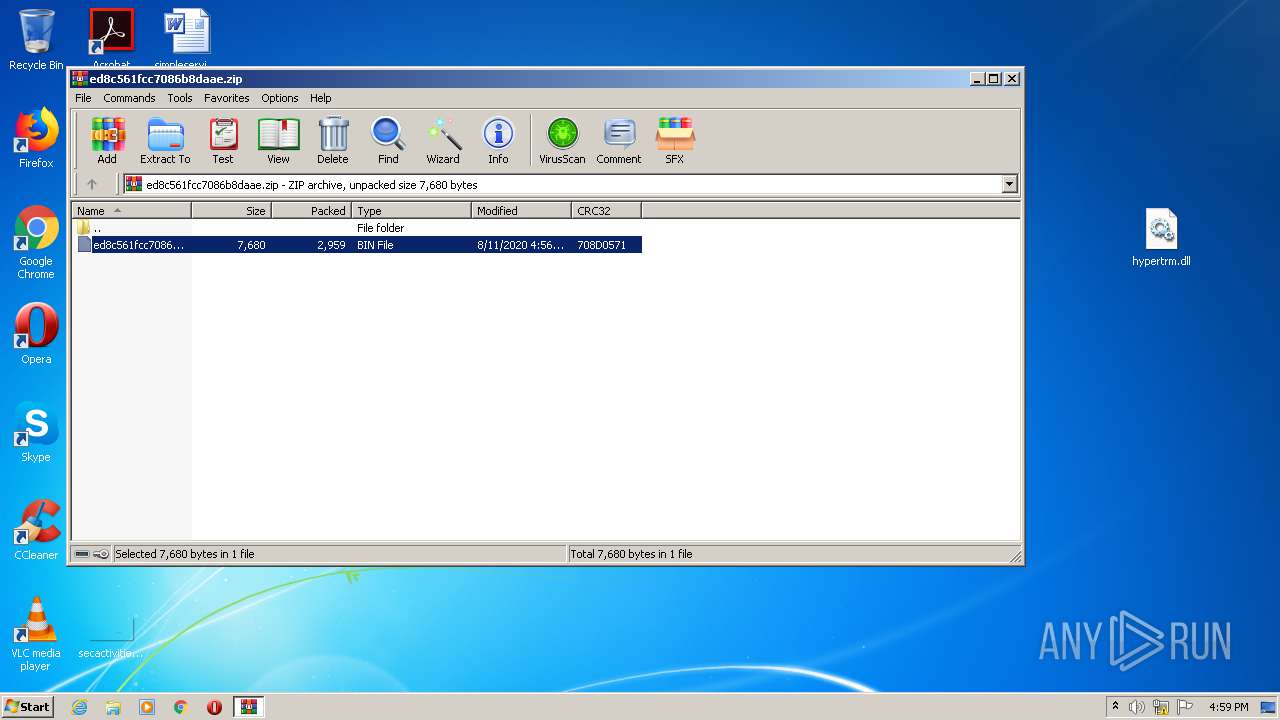
| File name: | ed8c561fcc7086b8daae.zip |
| Full analysis: | https://app.any.run/tasks/aa500103-ee4b-439c-bafe-a244e52e9320 |
| Verdict: | Malicious activity |
| Analysis date: | August 11, 2020, 15:57:30 |
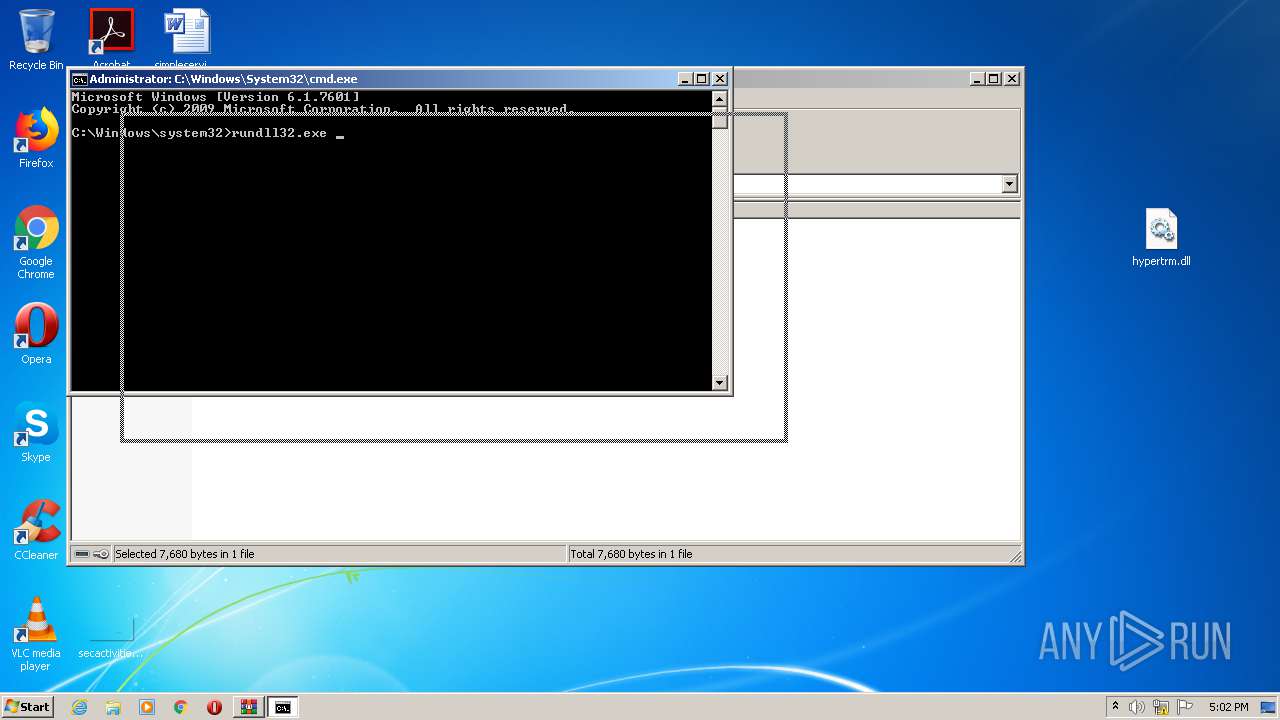
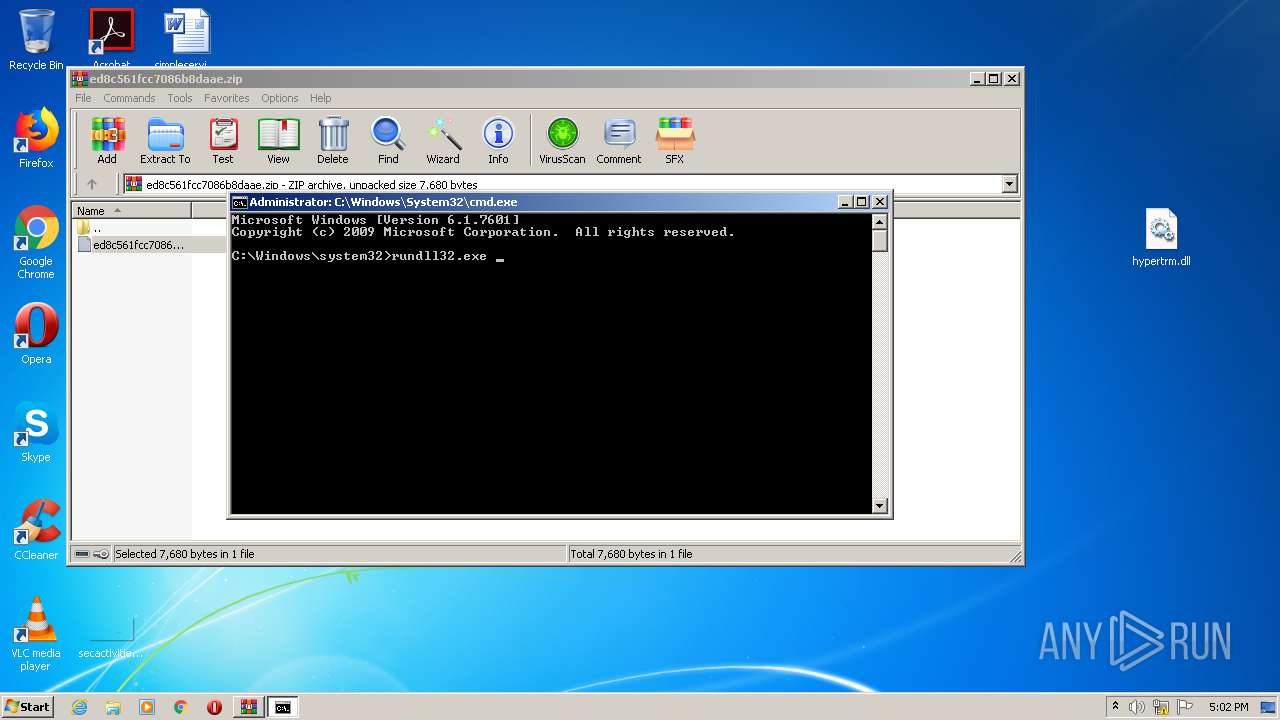
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 8B66040A237D1A157FFD6FDFD3FF99B2 |
| SHA1: | 45C7D87923010809CFBA8F61BBE9470DFFF760A0 |
| SHA256: | B65BD74E867A1EB68A890CA2806745EDA29A1782AFCD1D190FB9B0A6C4B133D2 |
| SSDEEP: | 96:IE69d0Z24h9/EnSASC1CubeMkbjycgkgQNgyfwgdsn:IE69d0Z2m9snRR4RMkhVN9fwisn |
MALICIOUS
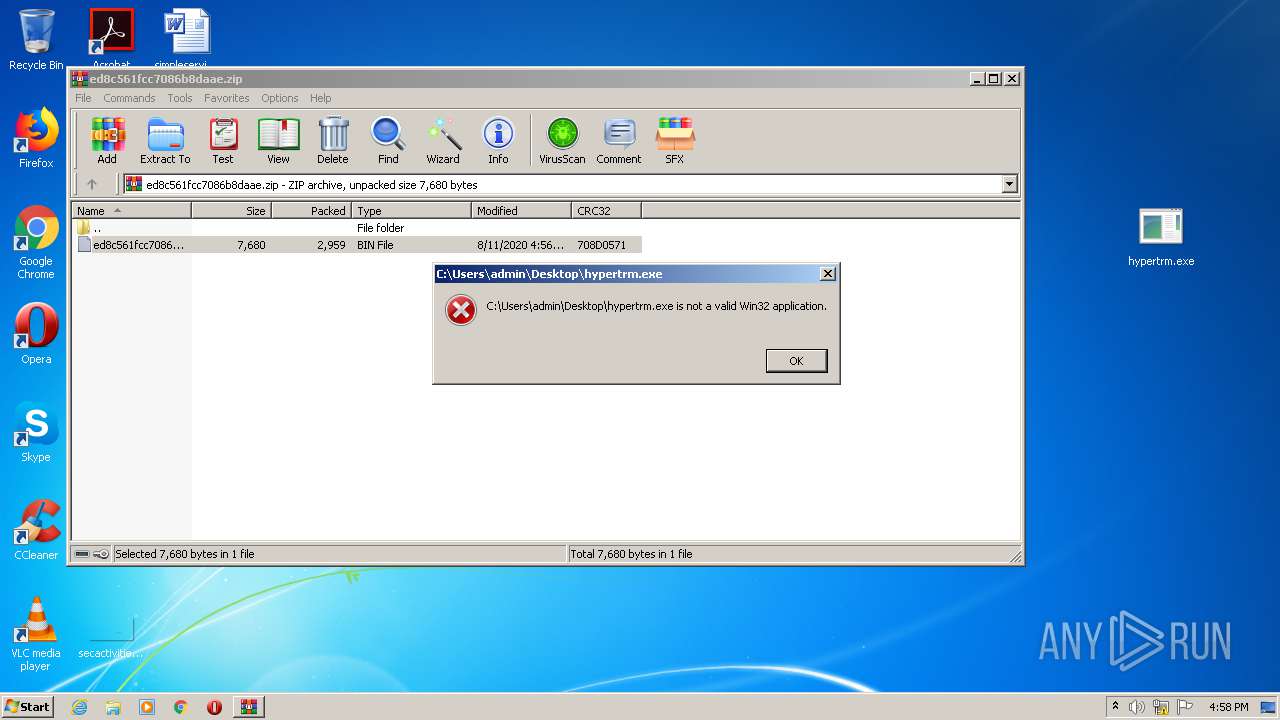
Loads dropped or rewritten executable
- svchost.exe (PID: 860)
- explorer.exe (PID: 356)
- SearchProtocolHost.exe (PID: 2568)
- consent.exe (PID: 3924)
- SearchProtocolHost.exe (PID: 284)
Runs app for hidden code execution
- explorer.exe (PID: 356)
SUSPICIOUS
Creates or modifies windows services
- svchost.exe (PID: 860)
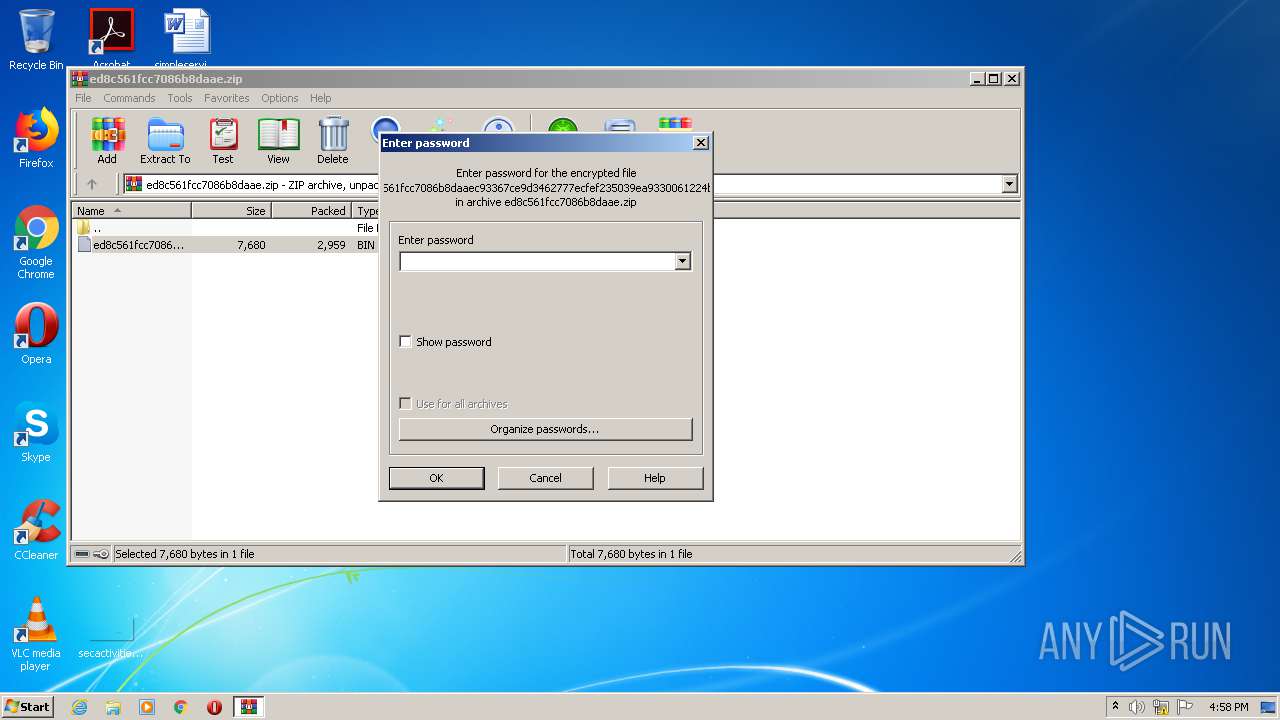
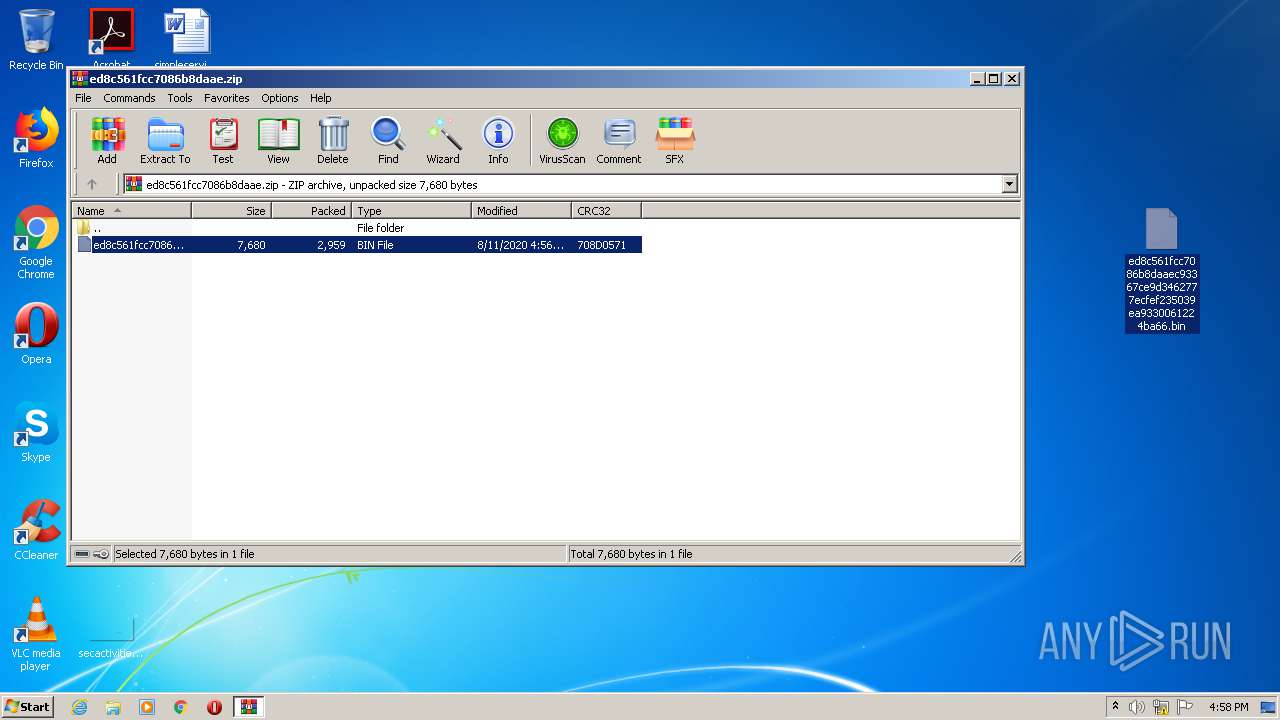
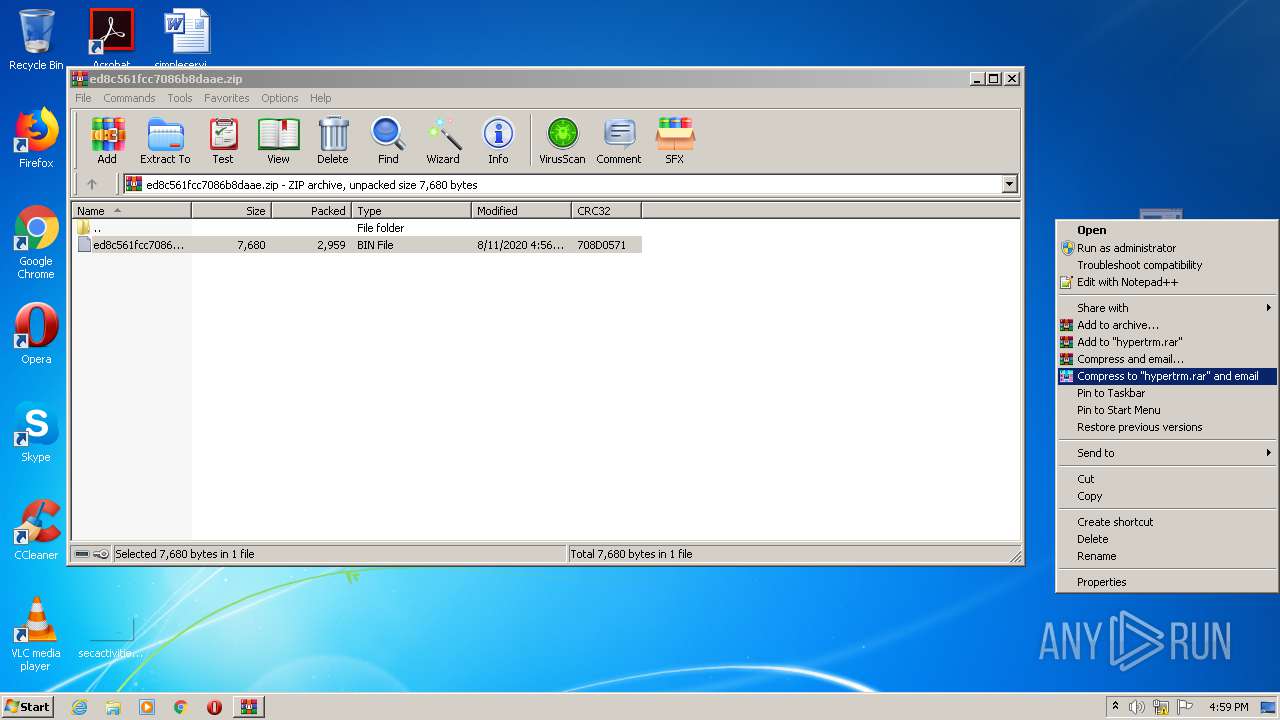
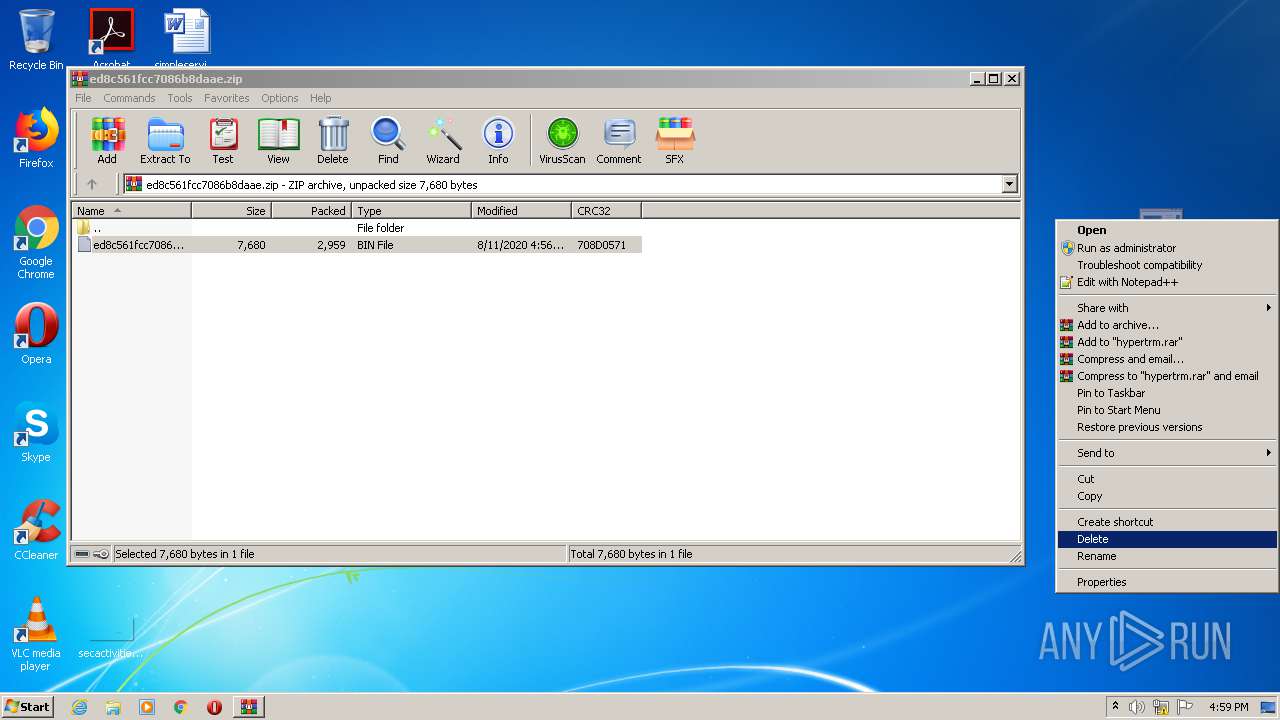
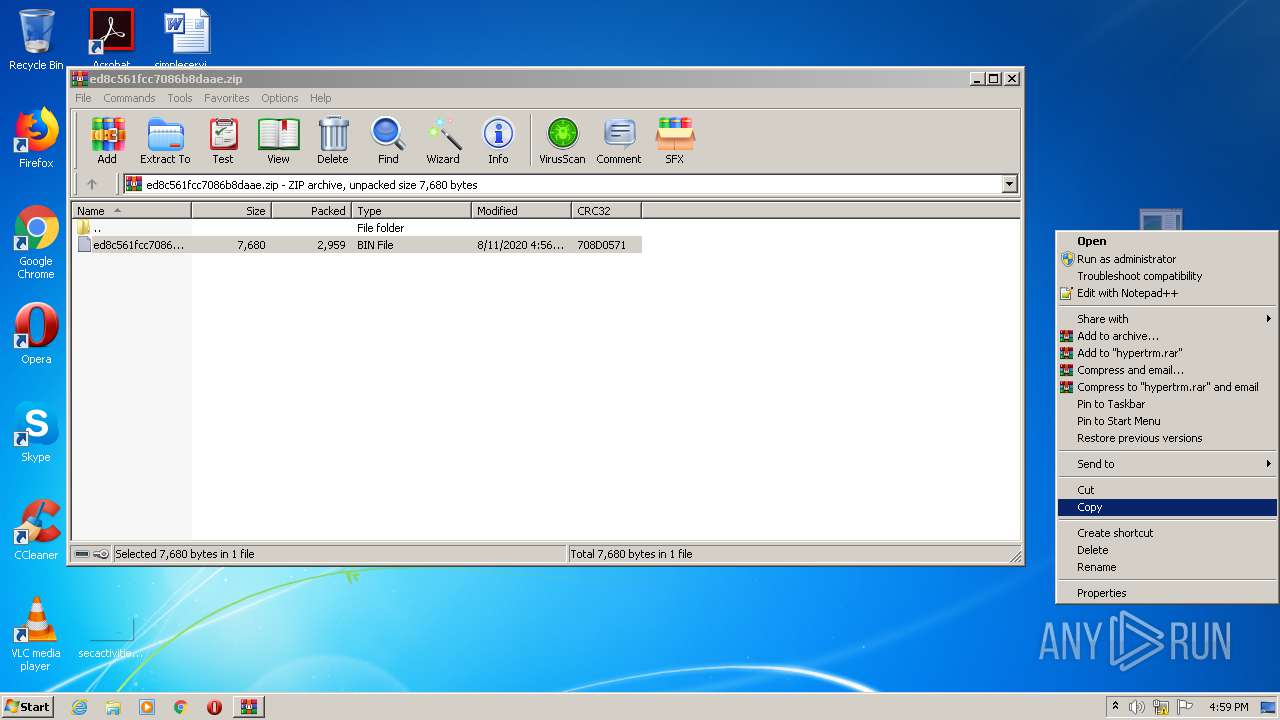
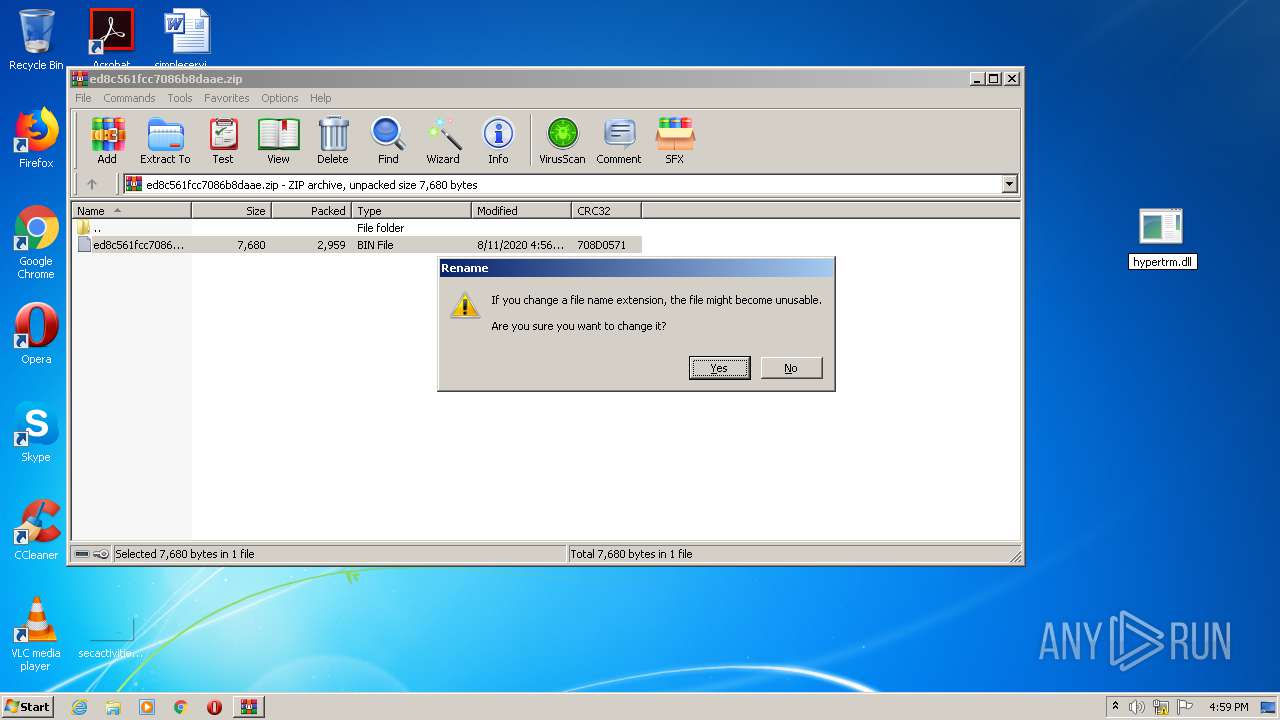
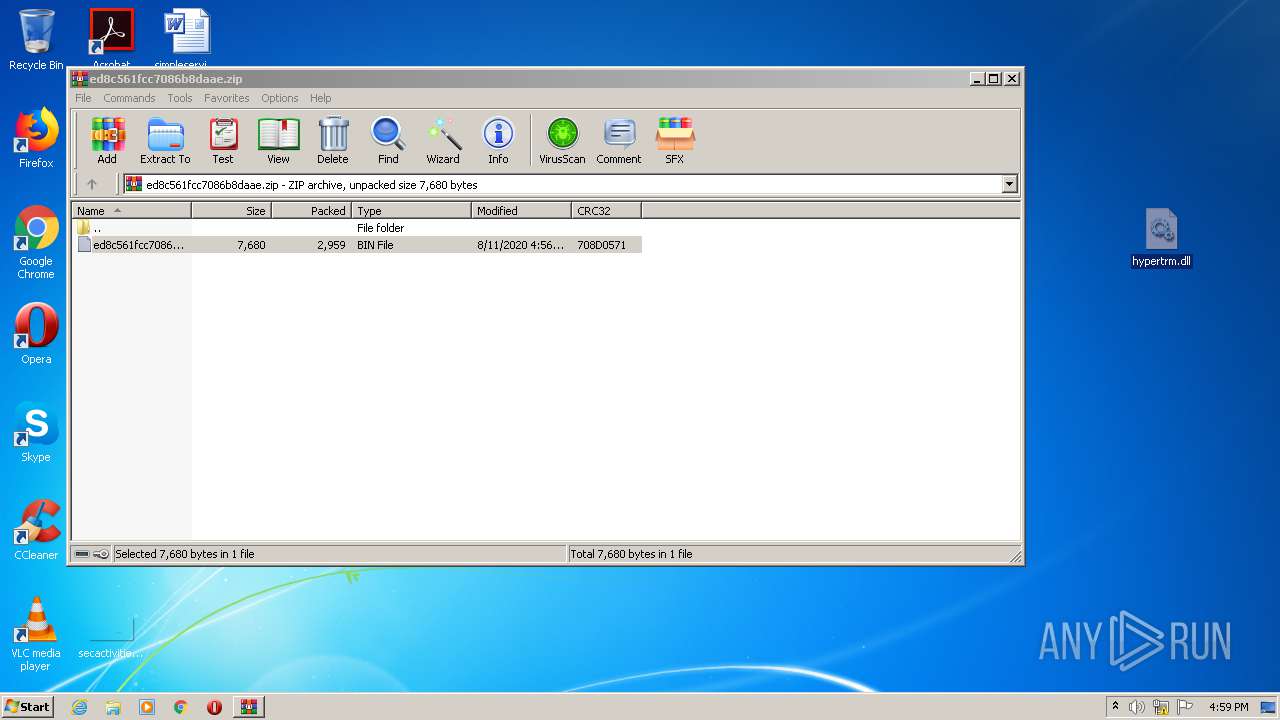
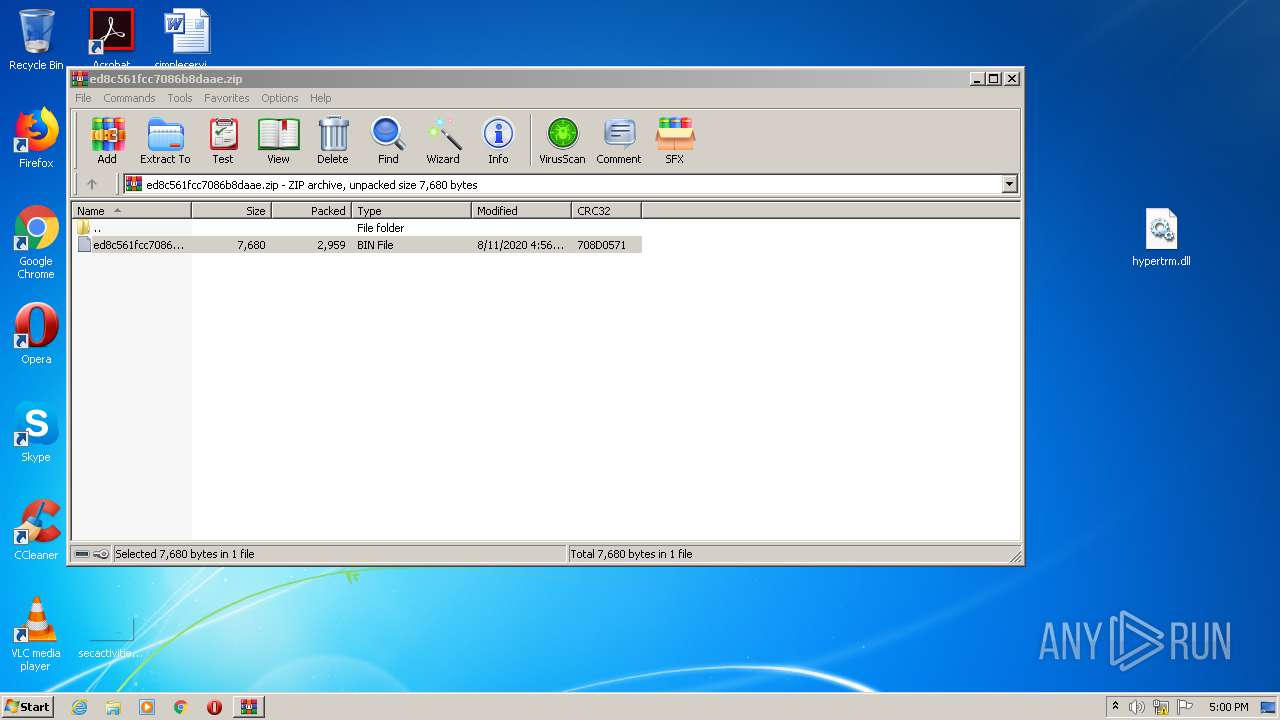
Executable content was dropped or overwritten
- WinRAR.exe (PID: 604)
- explorer.exe (PID: 356)
Creates files in the Windows directory
- WMIADAP.EXE (PID: 2128)
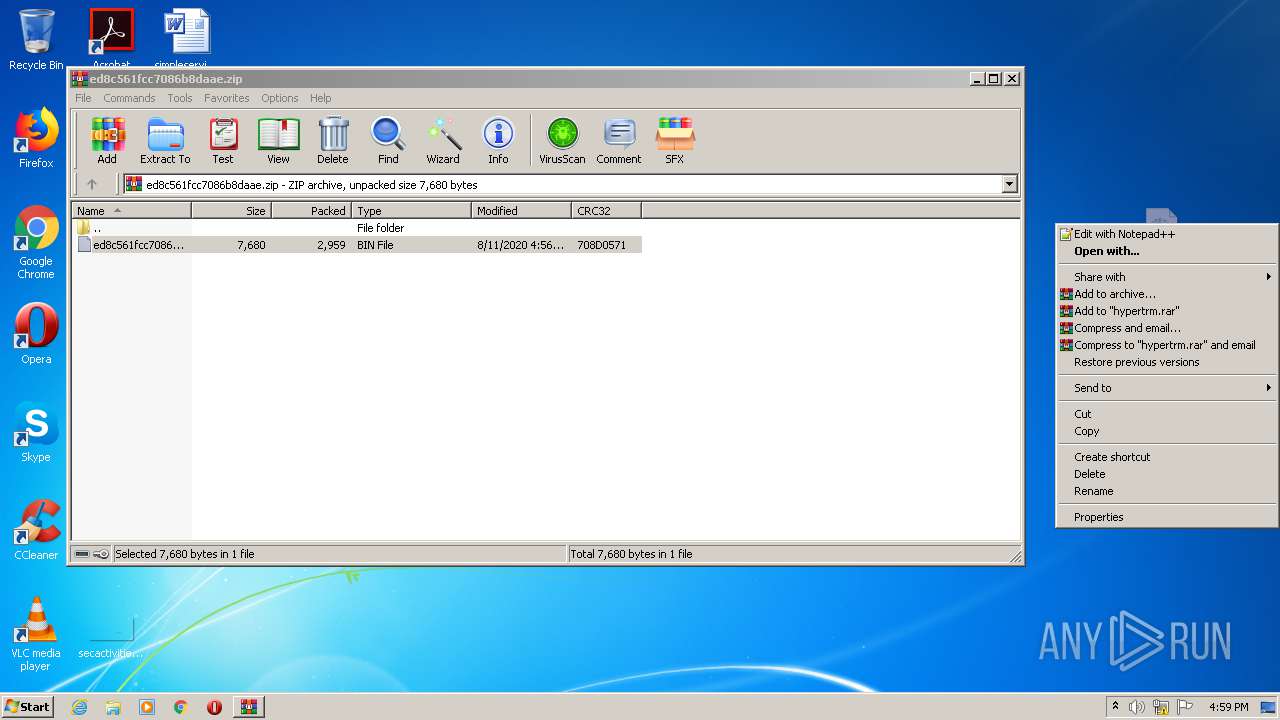
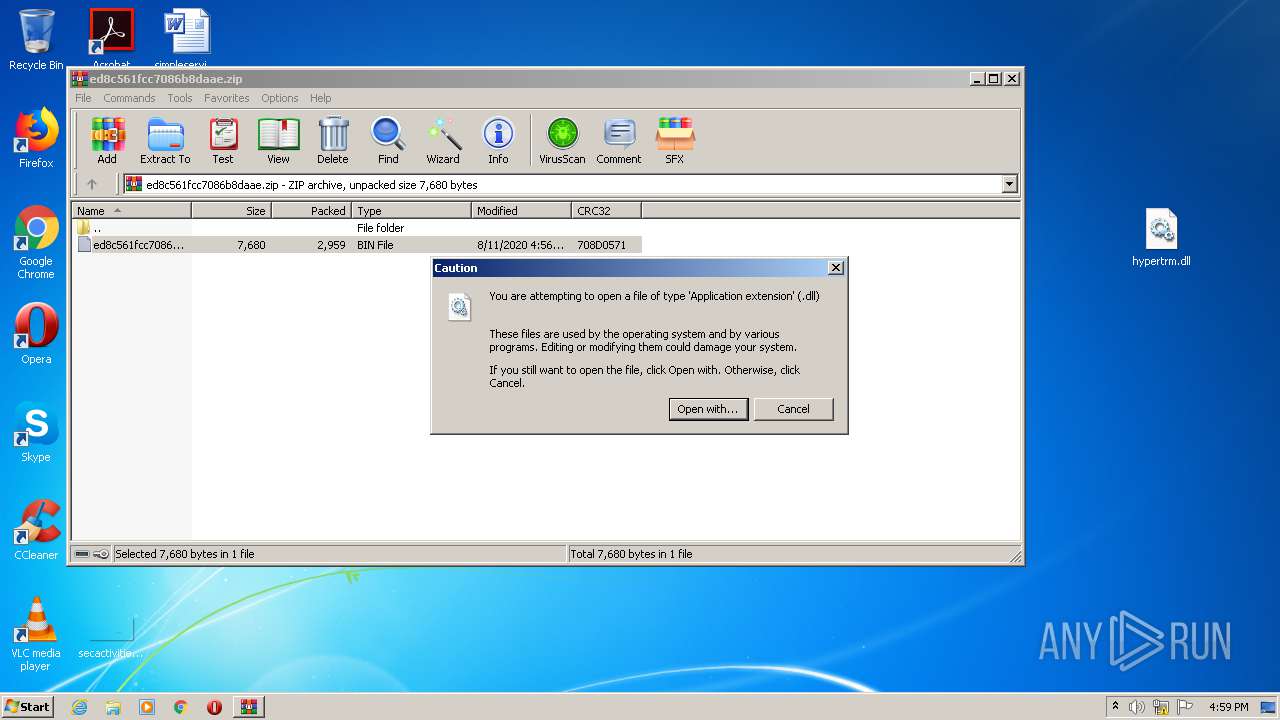
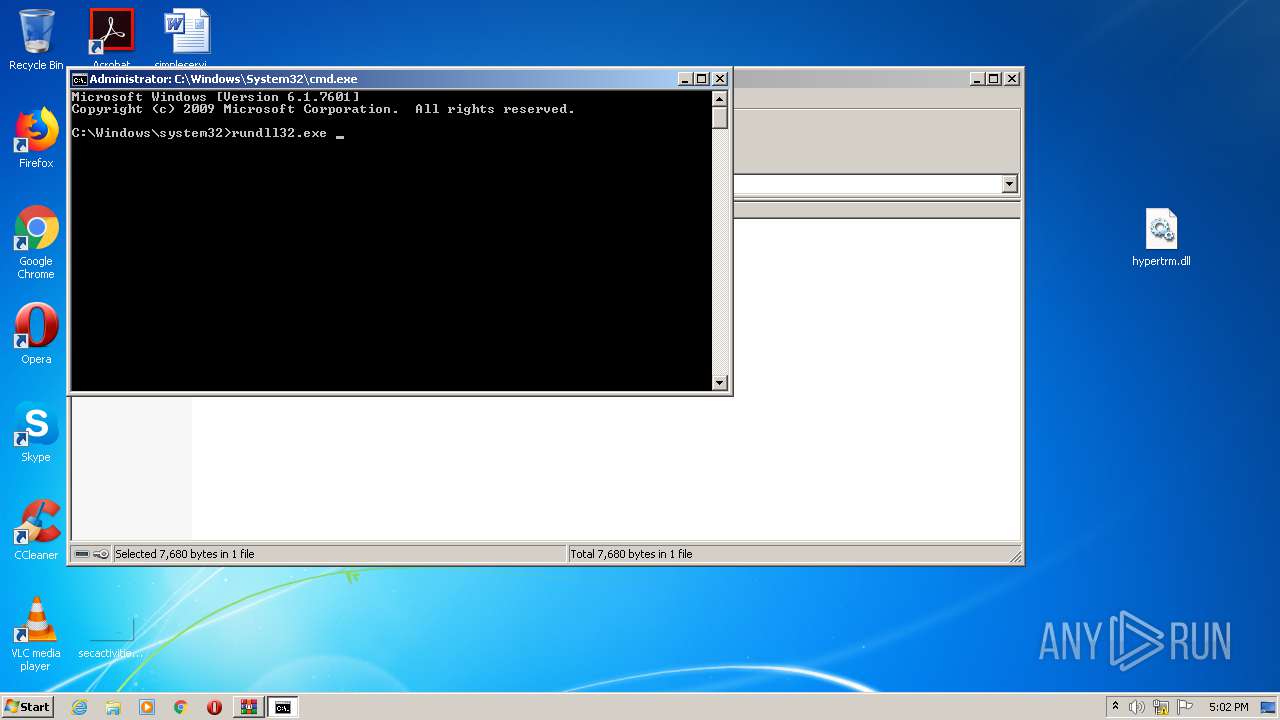
Uses RUNDLL32.EXE to load library
- explorer.exe (PID: 356)
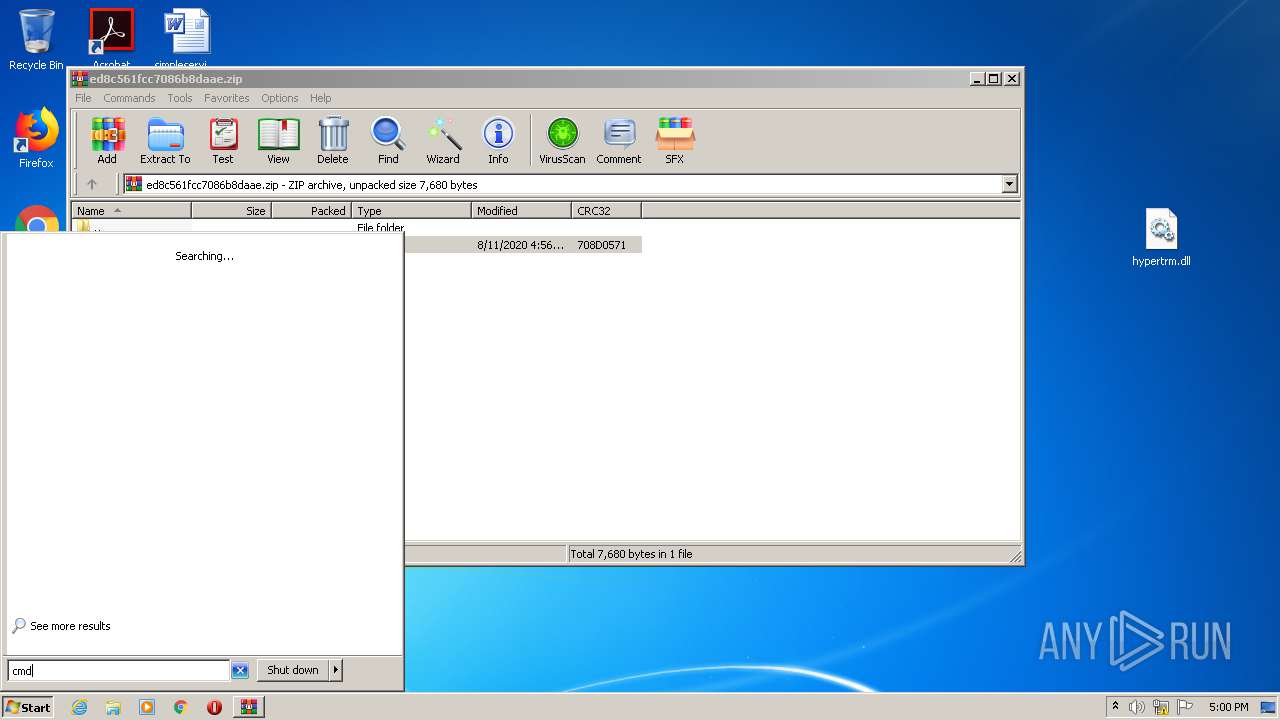
Starts CMD.EXE for commands execution
- explorer.exe (PID: 356)
Removes files from Windows directory
- WMIADAP.EXE (PID: 2128)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
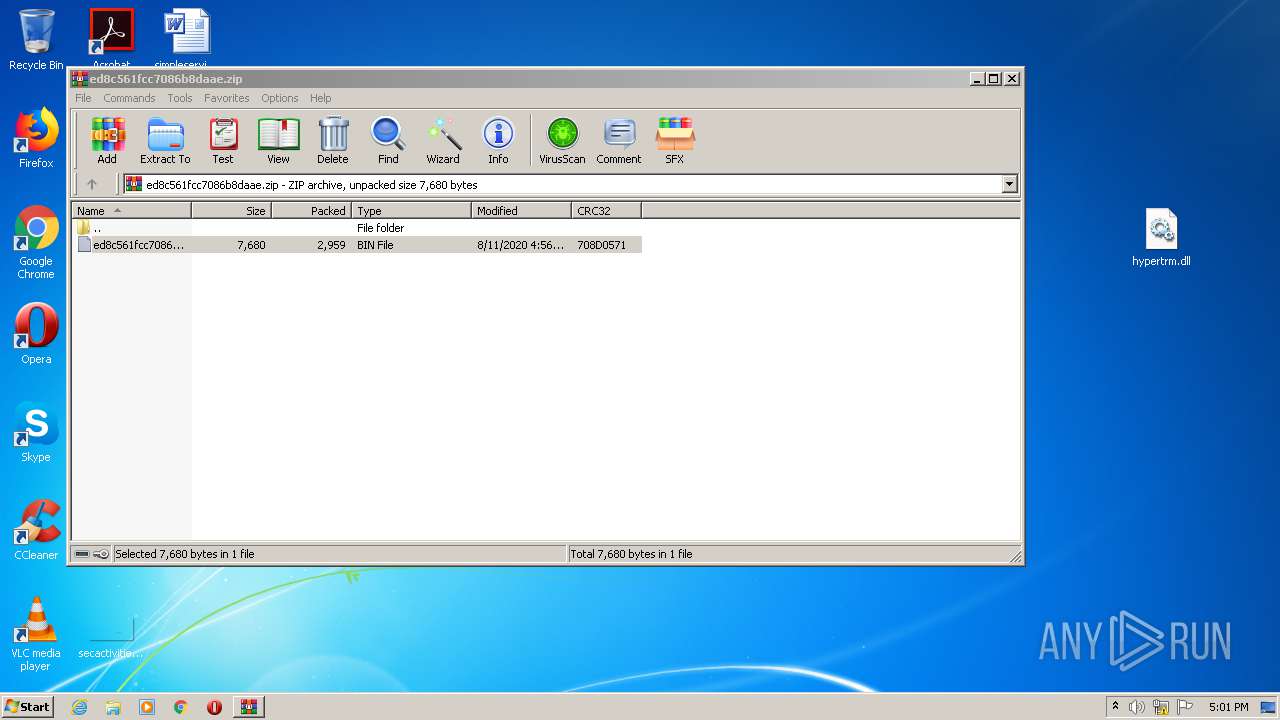
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:08:11 15:56:29 |
| ZipCRC: | 0x708d0571 |
| ZipCompressedSize: | 2959 |
| ZipUncompressedSize: | 7680 |
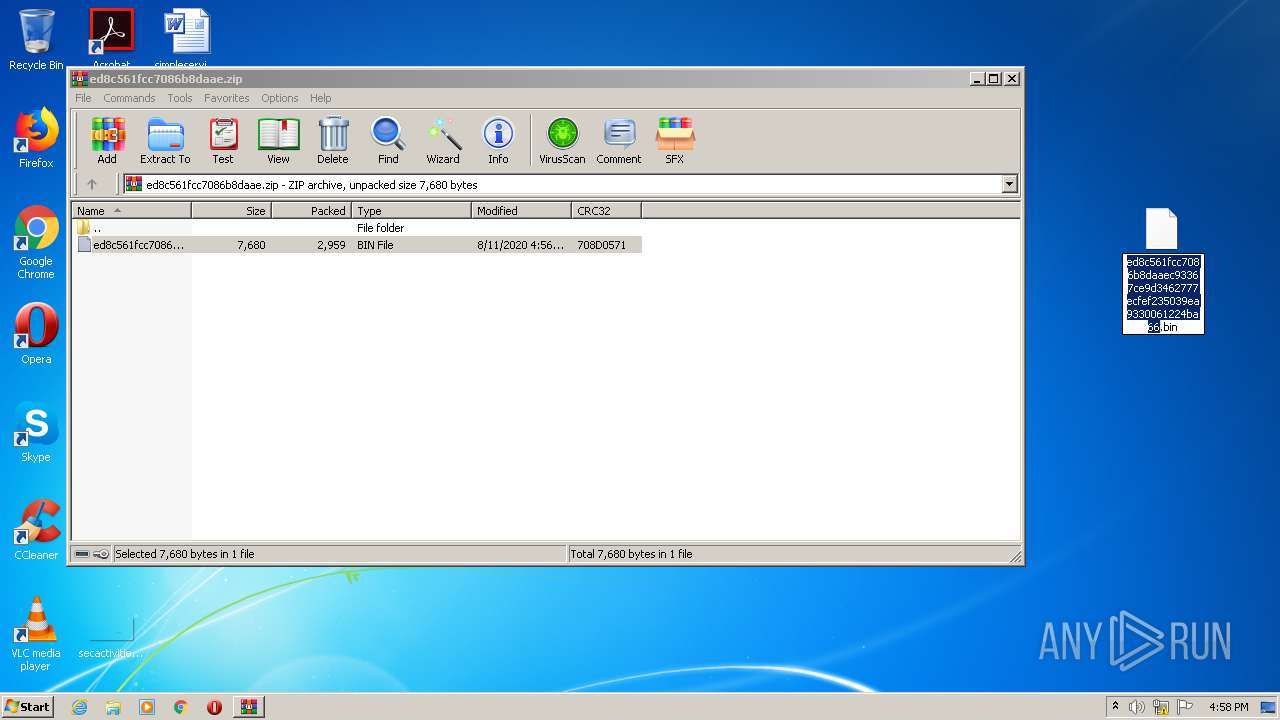
| ZipFileName: | ed8c561fcc7086b8daaec93367ce9d3462777ecfef235039ea9330061224ba66.bin |
Total processes
57
Monitored processes
11
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe4_ Global\UsGthrCtrlFltPipeMssGthrPipe4 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
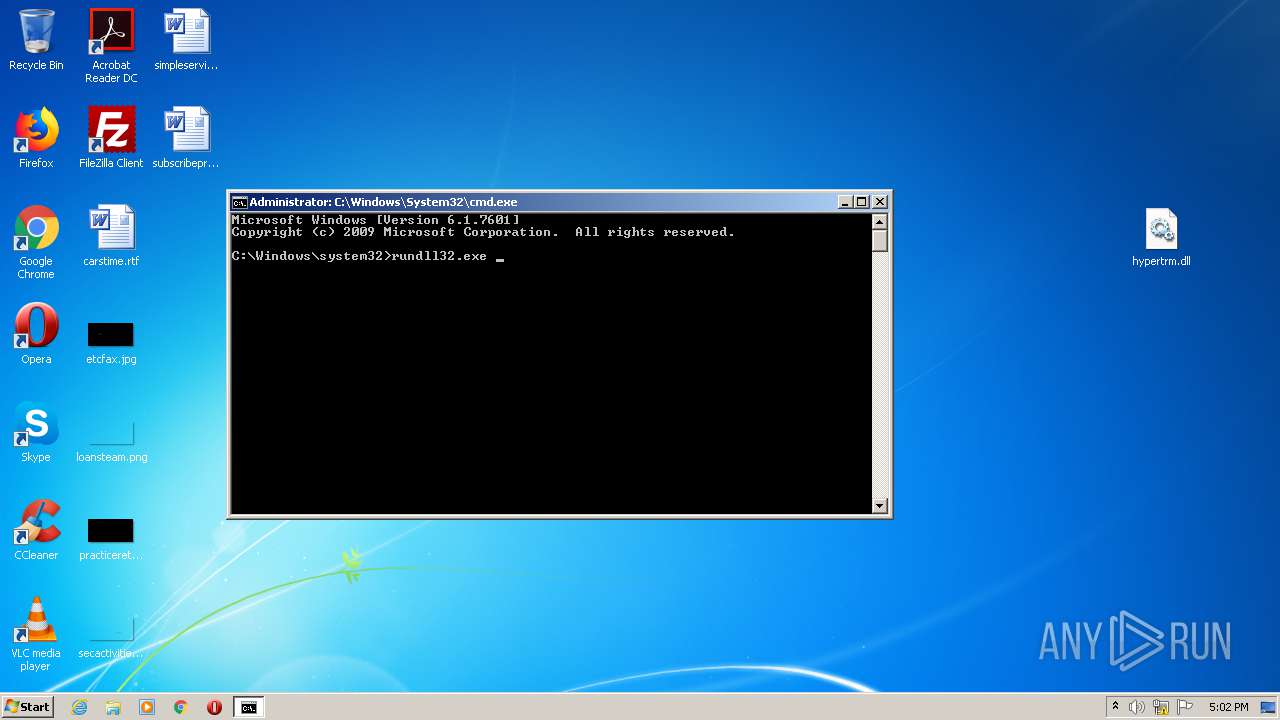
| 356 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
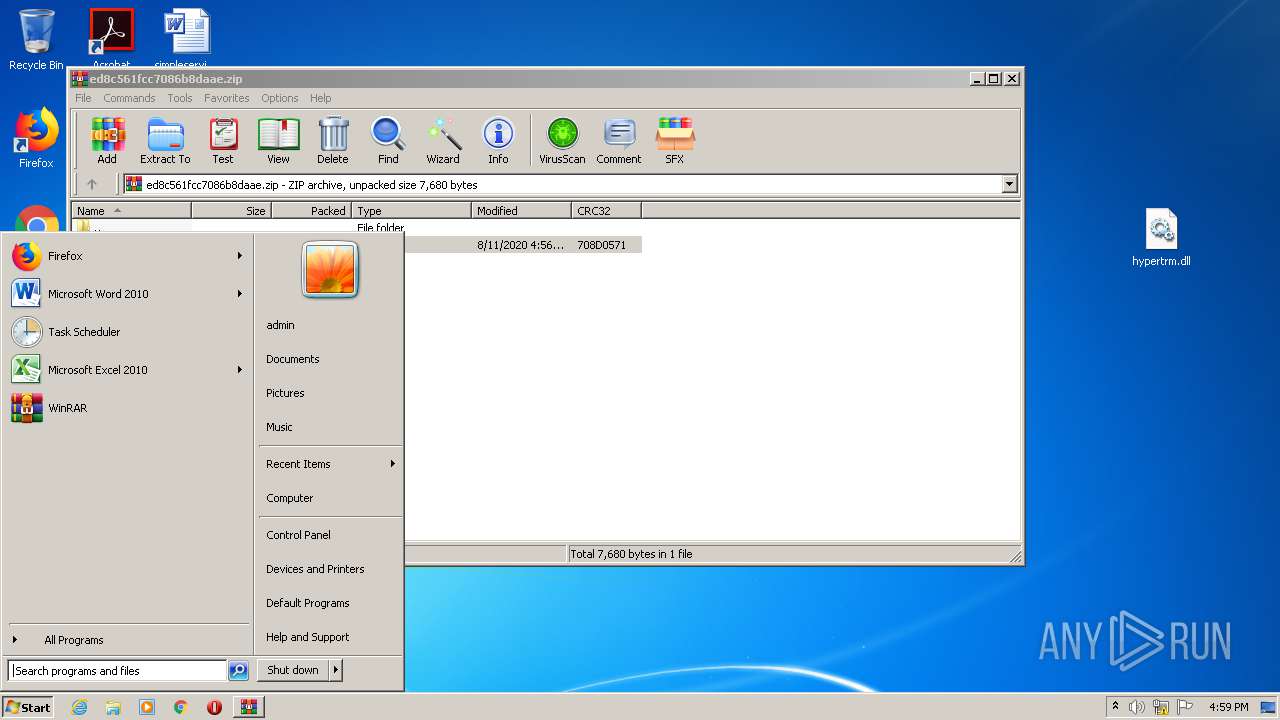
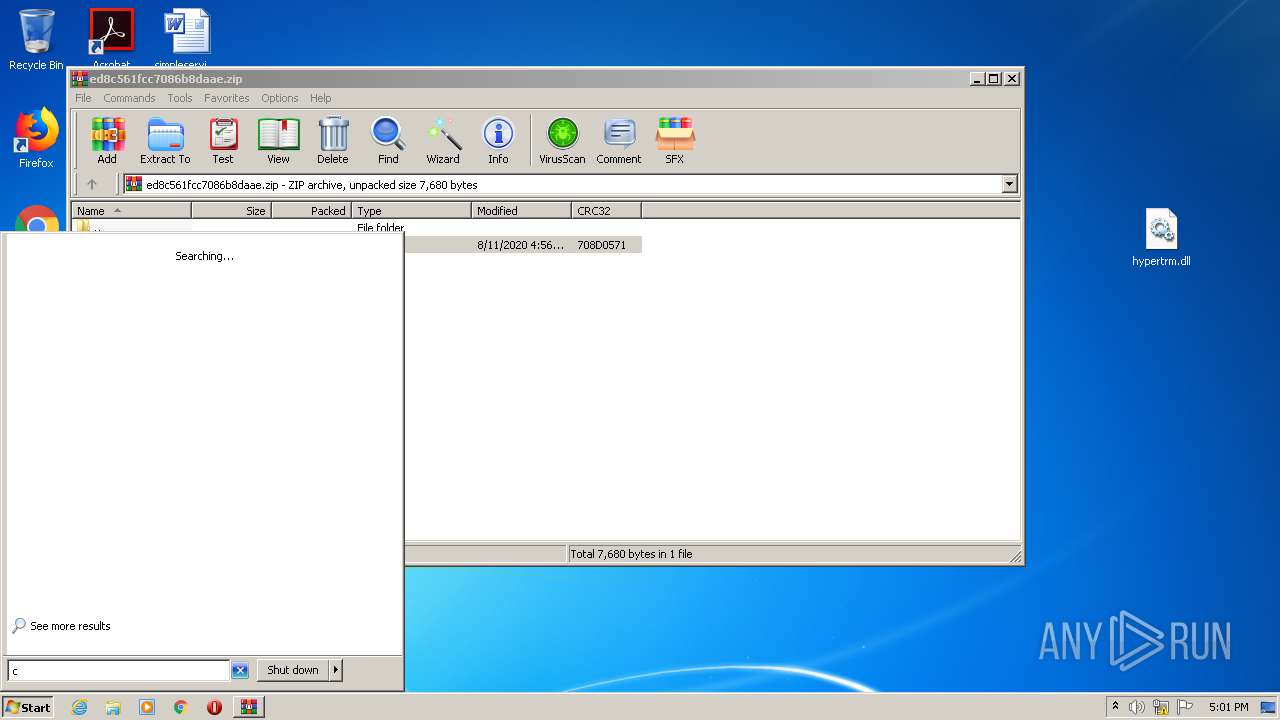
| 604 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\ed8c561fcc7086b8daae.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 860 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
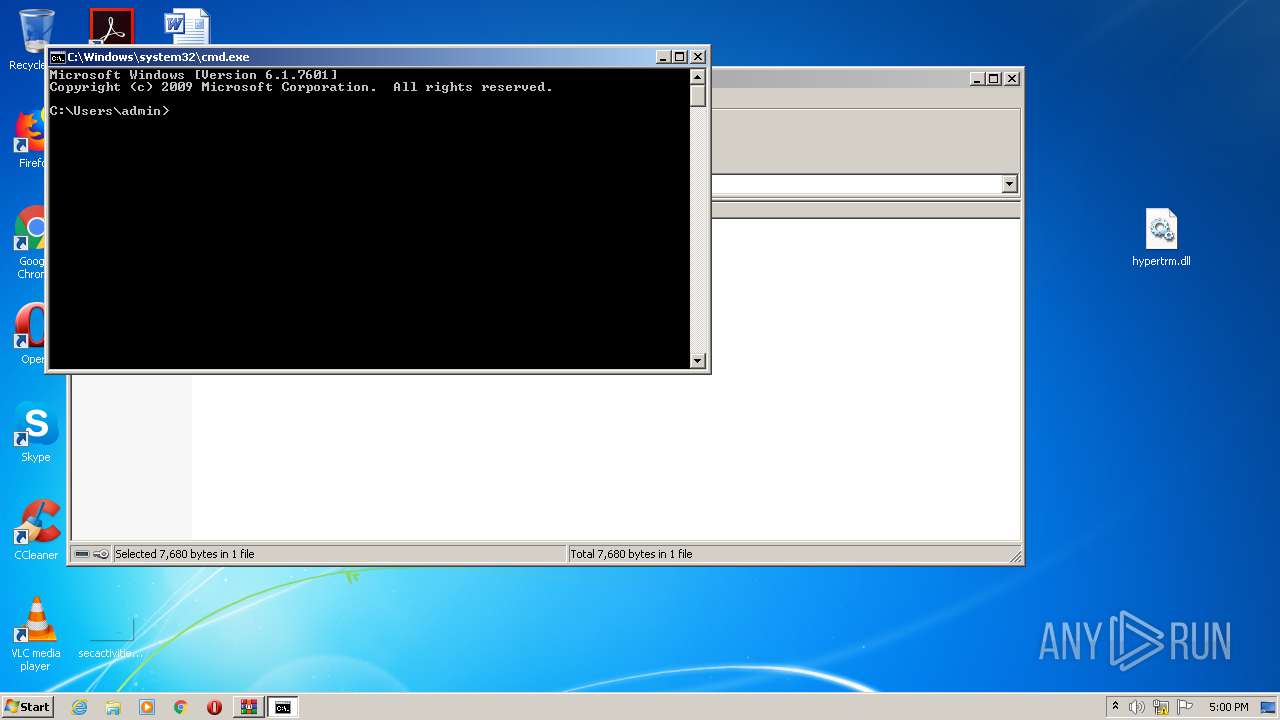
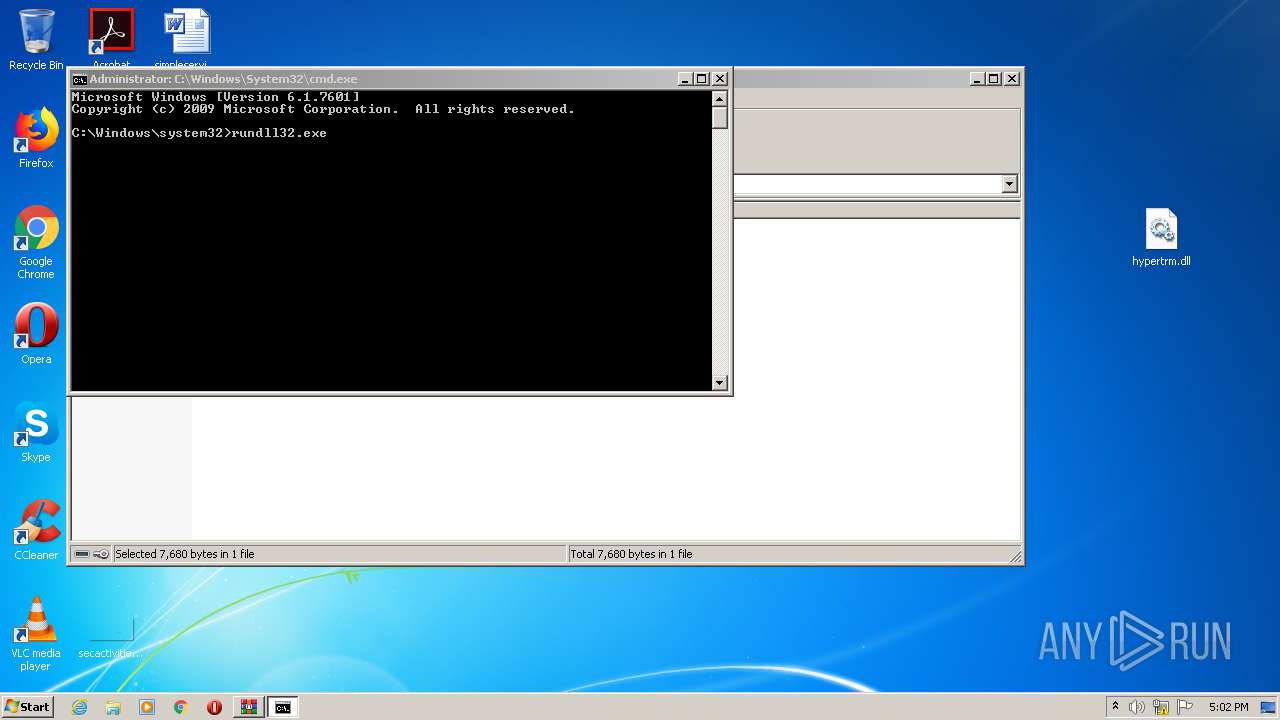
| 1528 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2128 | wmiadap.exe /F /T /R | C:\Windows\system32\wbem\WMIADAP.EXE | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Reverse Performance Adapter Maintenance Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2456 | consent.exe 860 240 00128968 | C:\Windows\system32\consent.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Consent UI for administrative applications Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2568 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe3_ Global\UsGthrCtrlFltPipeMssGthrPipe3 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
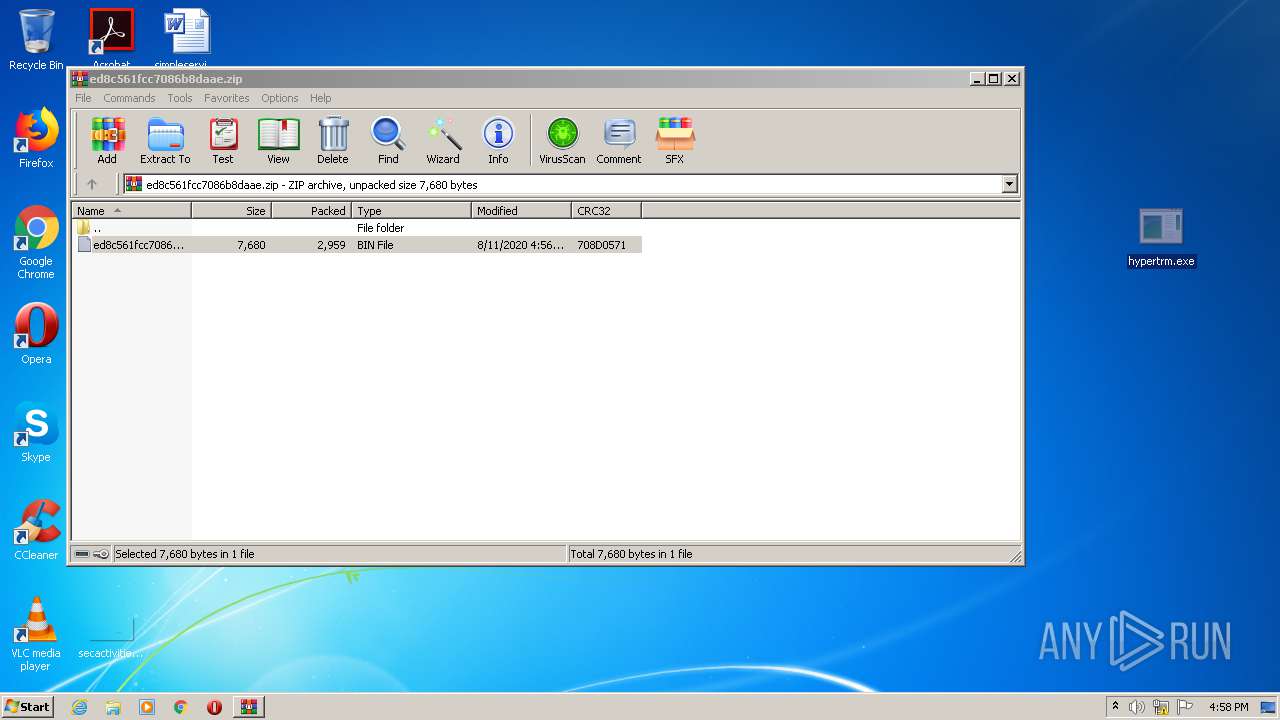
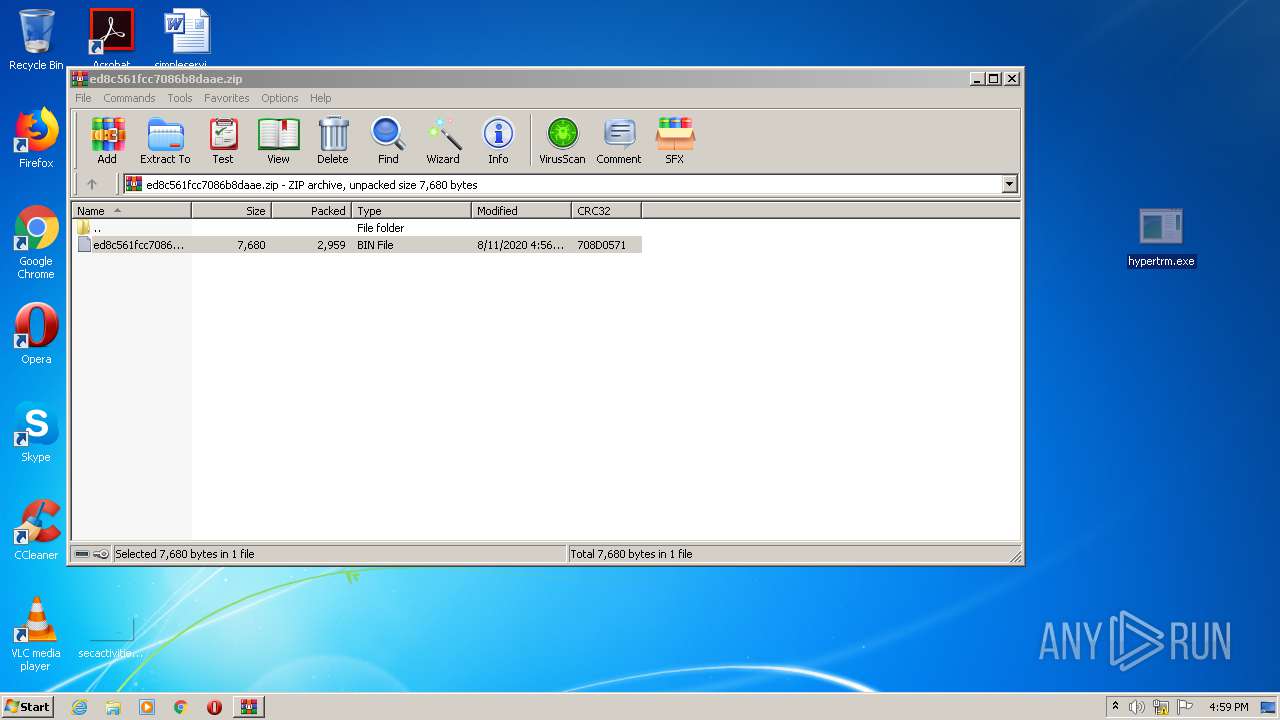
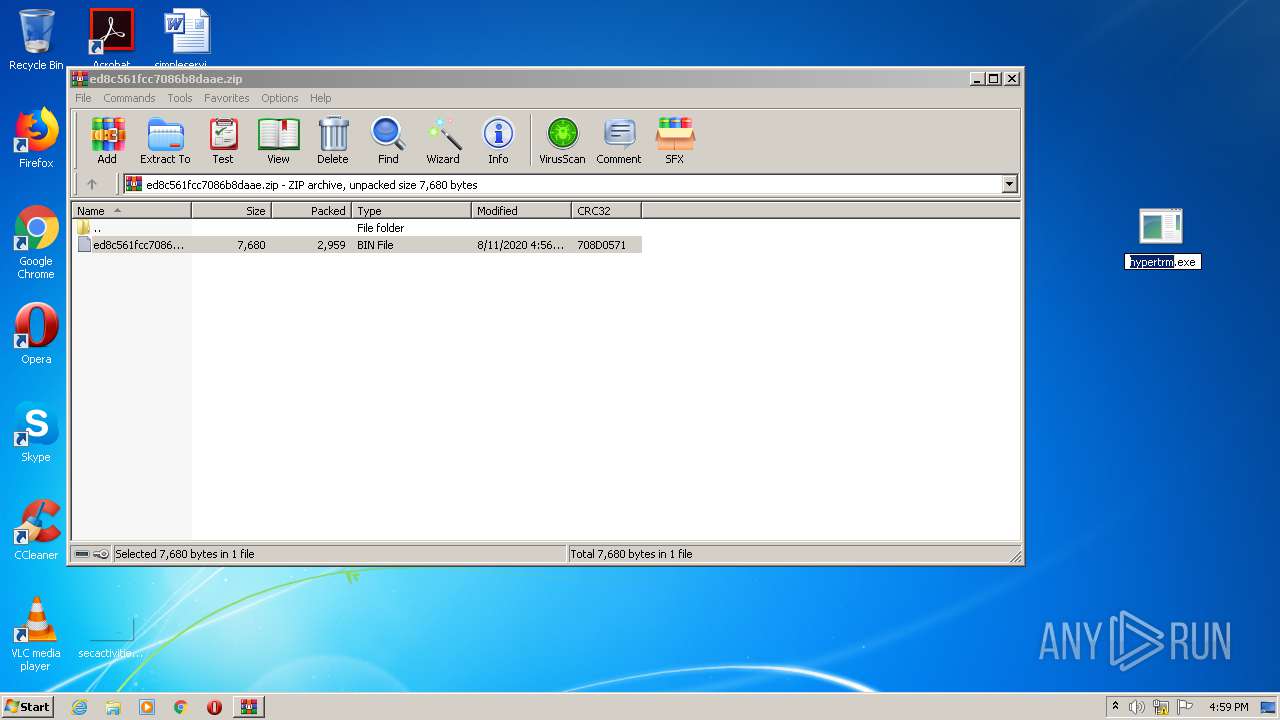
| 2788 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\hypertrm.dll | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
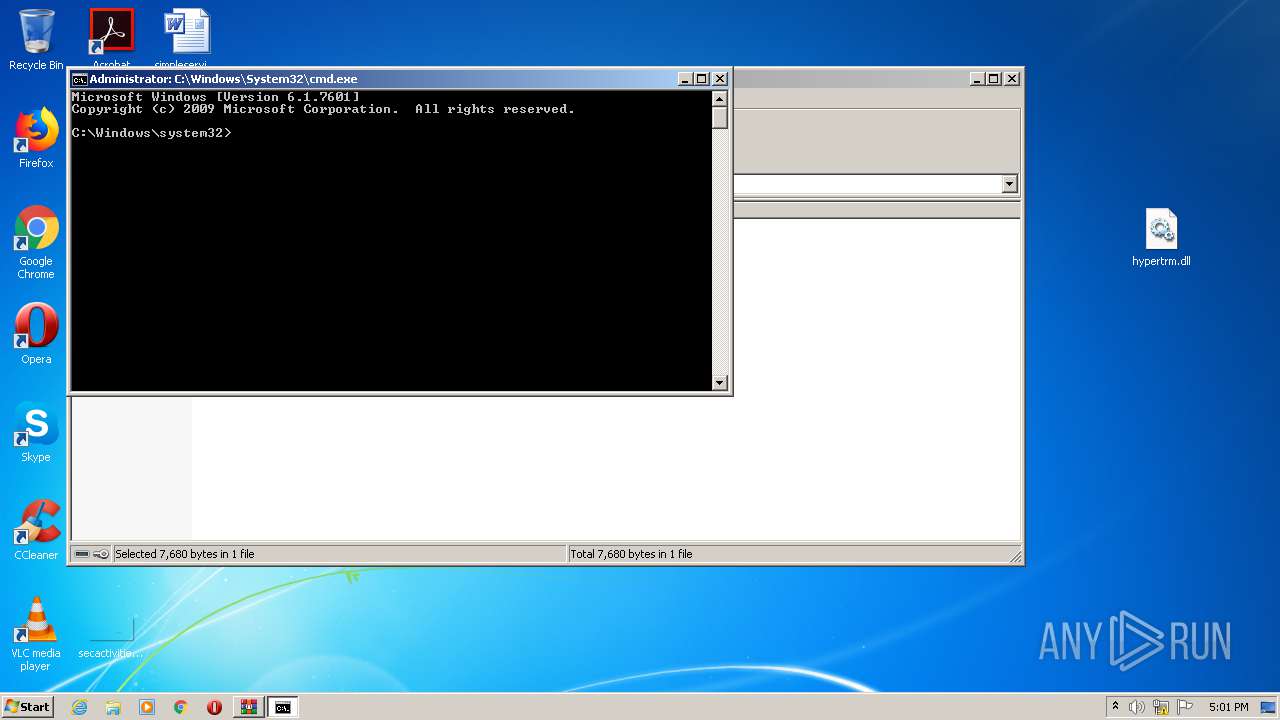
| 2944 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
17 856
Read events
17 119
Write events
729
Delete events
8
Modification events
| (PID) Process: | (860) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\IKEEXT |
| Operation: | write | Name: | CurrentLru |
Value: F803000000000000 | |||
| (PID) Process: | (604) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (604) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (604) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\137\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (604) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\137\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (604) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\ed8c561fcc7086b8daae.zip | |||
| (PID) Process: | (604) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (604) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (604) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (604) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
4
Suspicious files
9
Text files
4
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2128 | WMIADAP.EXE | C:\Windows\System32\wbem\Performance\WmiApRpl_new.h | — | |
MD5:— | SHA256:— | |||
| 2128 | WMIADAP.EXE | C:\Windows\System32\wbem\Performance\WmiApRpl_new.ini | — | |
MD5:— | SHA256:— | |||
| 2128 | WMIADAP.EXE | C:\Windows\system32\PerfStringBackup.TMP | — | |
MD5:— | SHA256:— | |||
| 860 | svchost.exe | C:\Windows\SoftwareDistribution\DataStore\DataStore.edb | — | |
MD5:— | SHA256:— | |||
| 860 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
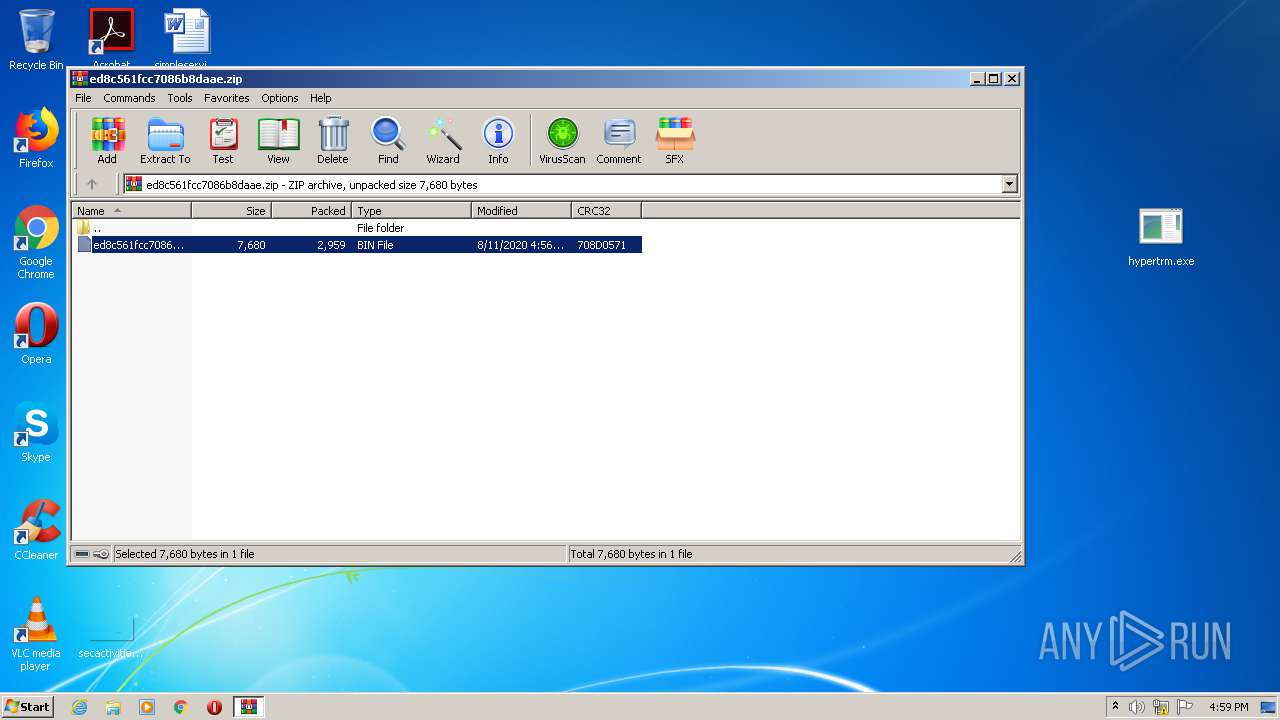
| 356 | explorer.exe | C:\Users\admin\Desktop\hypertrm.exe | executable | |
MD5:— | SHA256:— | |||
| 604 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb604.30895\ed8c561fcc7086b8daaec93367ce9d3462777ecfef235039ea9330061224ba66.bin | executable | |
MD5:— | SHA256:— | |||
| 356 | explorer.exe | C:\Users\admin\Desktop\hypertrm.dll | executable | |
MD5:— | SHA256:— | |||
| 2128 | WMIADAP.EXE | C:\Windows\system32\PerfStringBackup.INI | binary | |
MD5:— | SHA256:— | |||
| 2128 | WMIADAP.EXE | C:\Windows\system32\perfc009.dat | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report