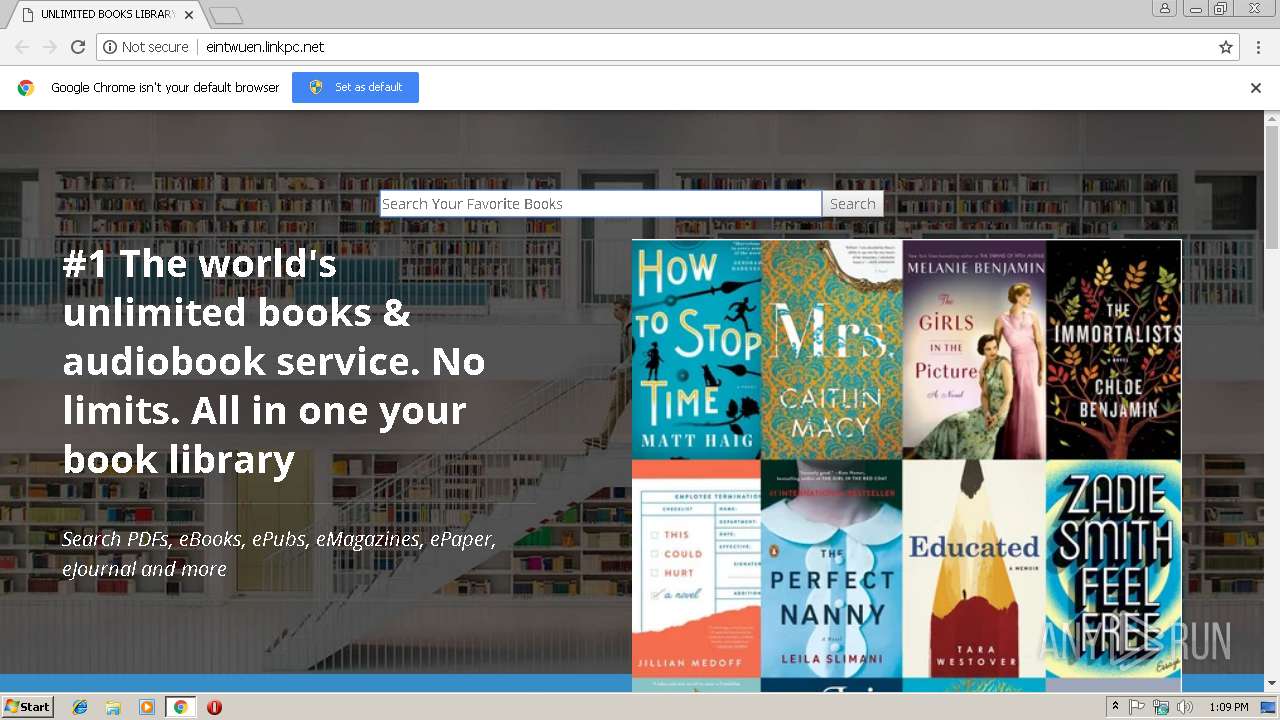
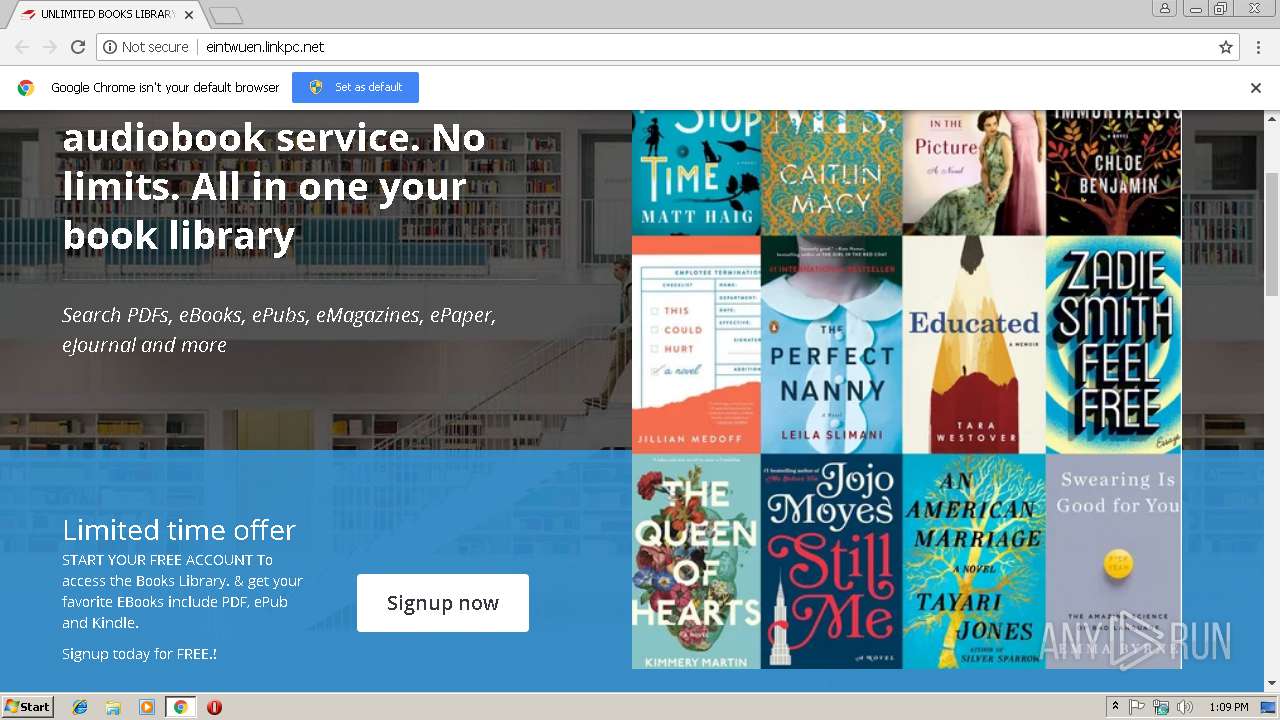
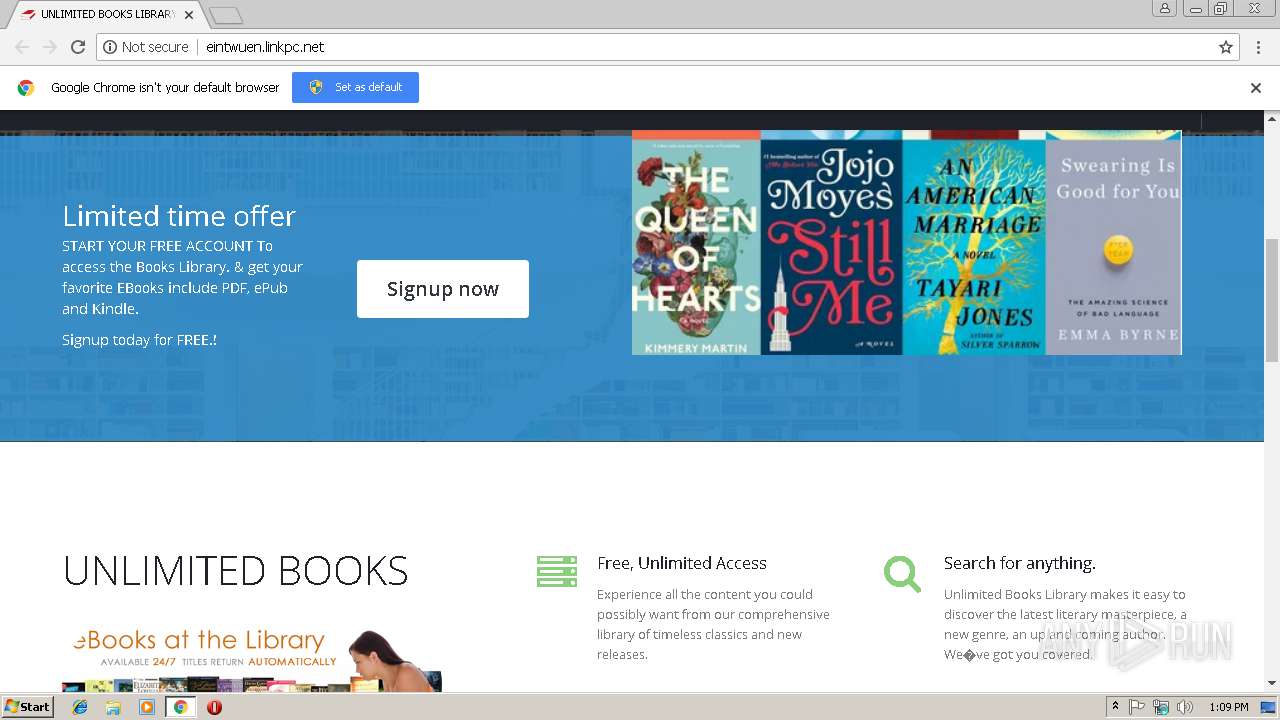
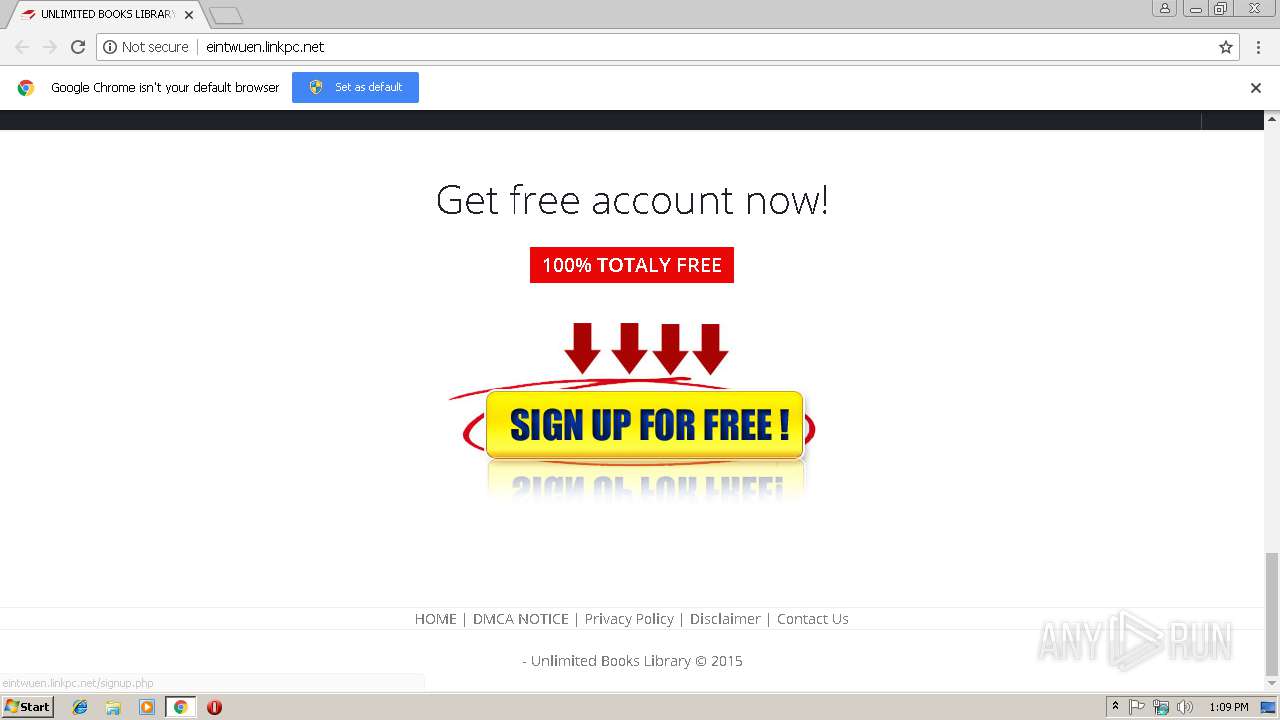
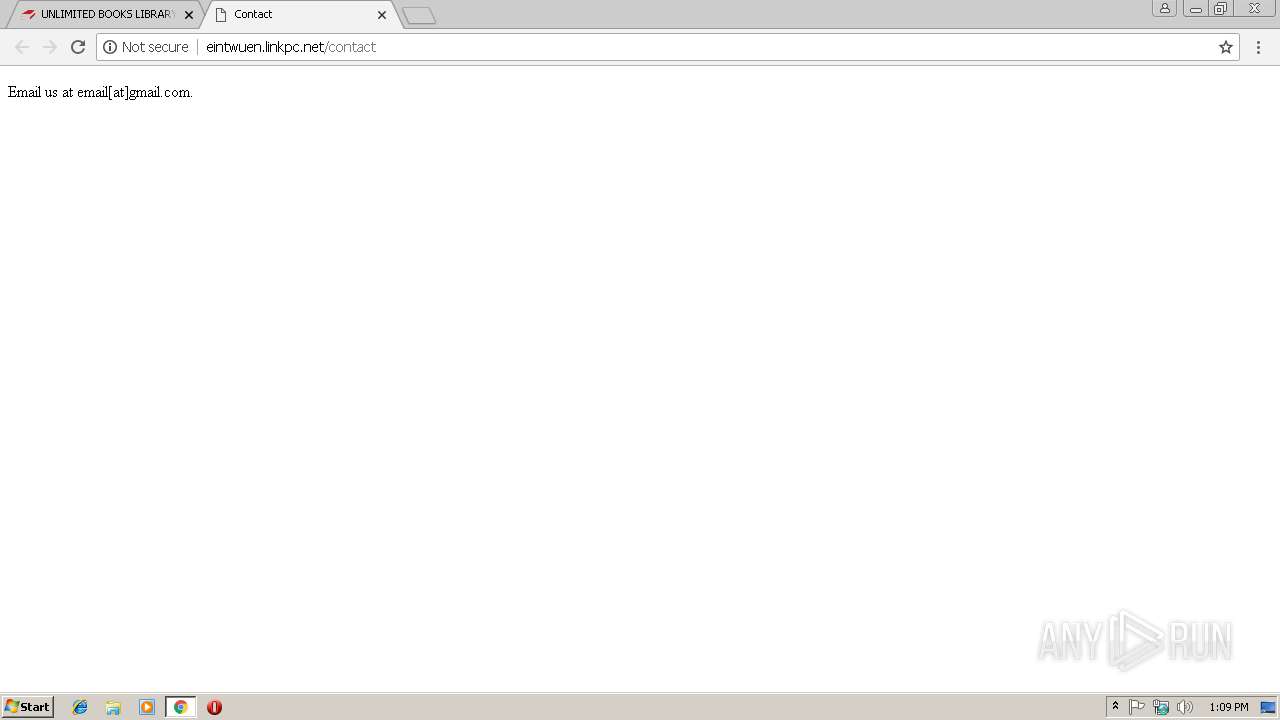
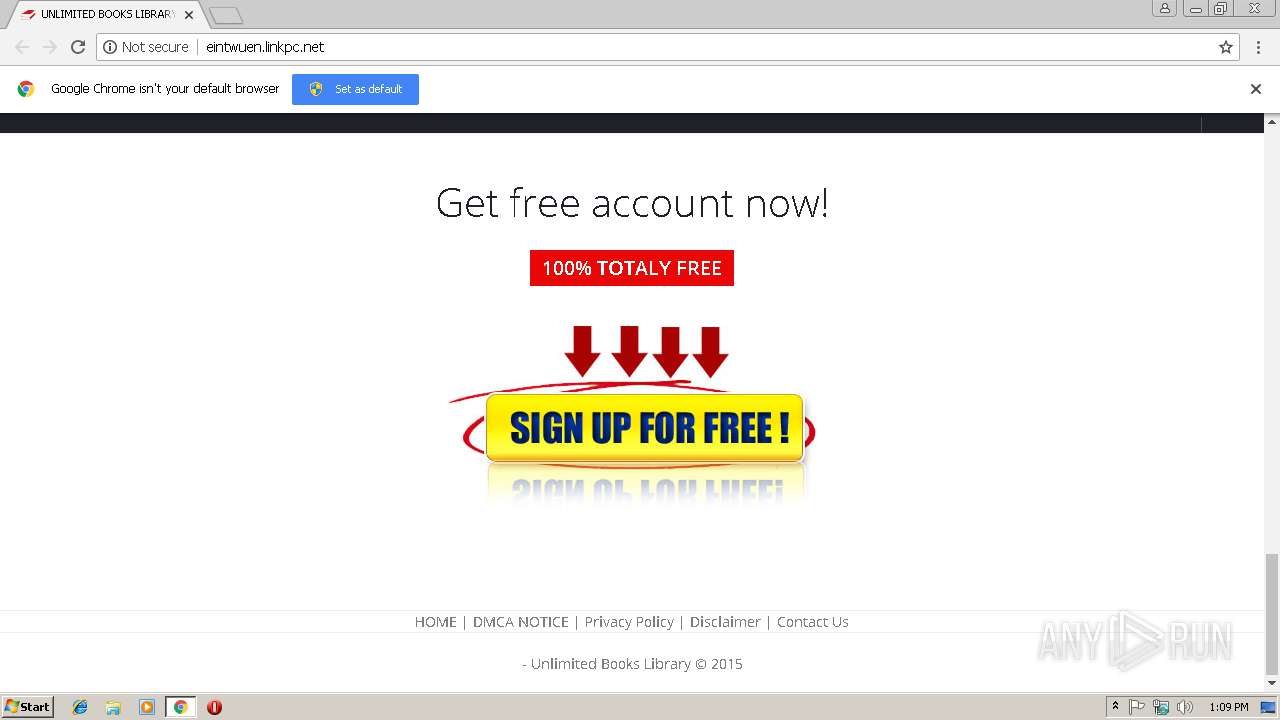
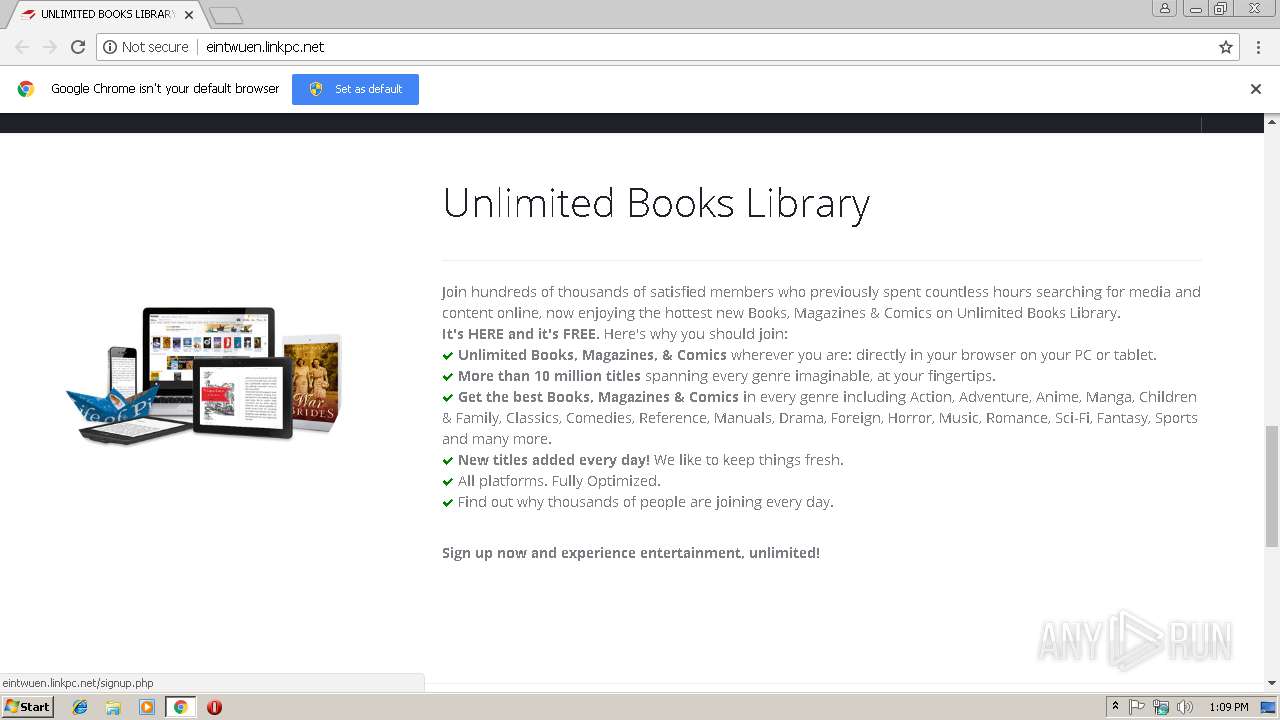
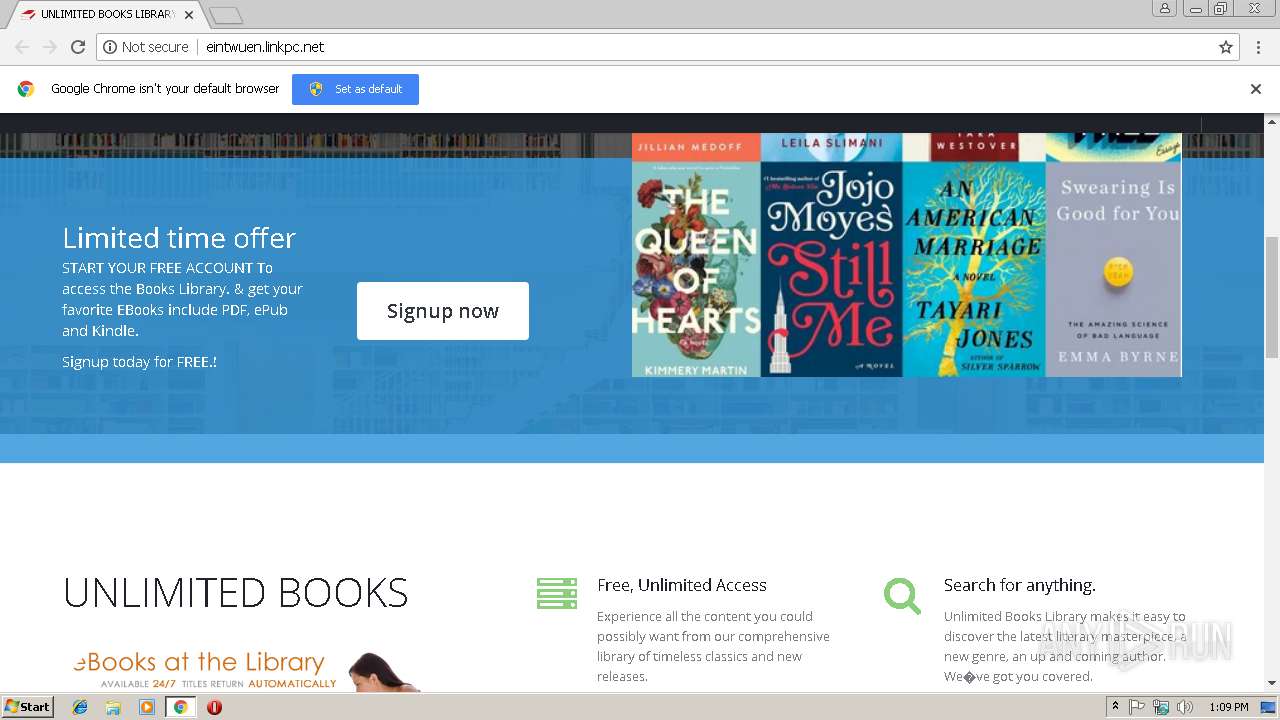
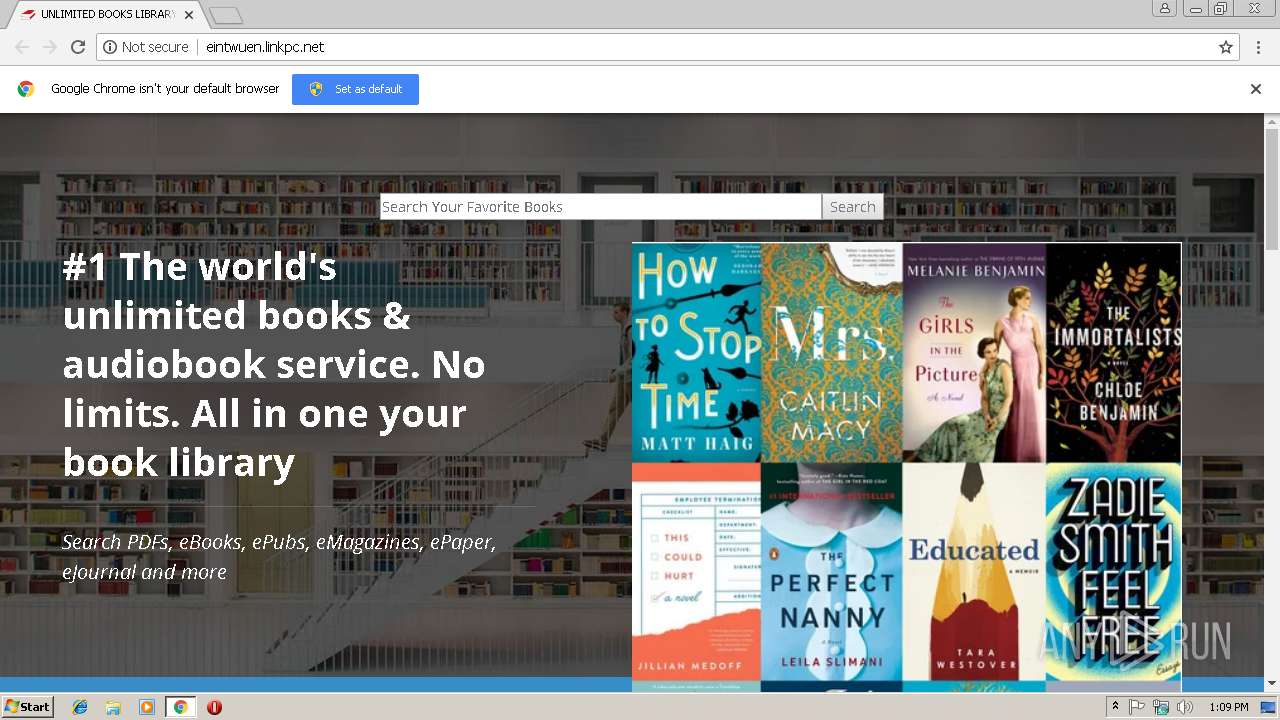
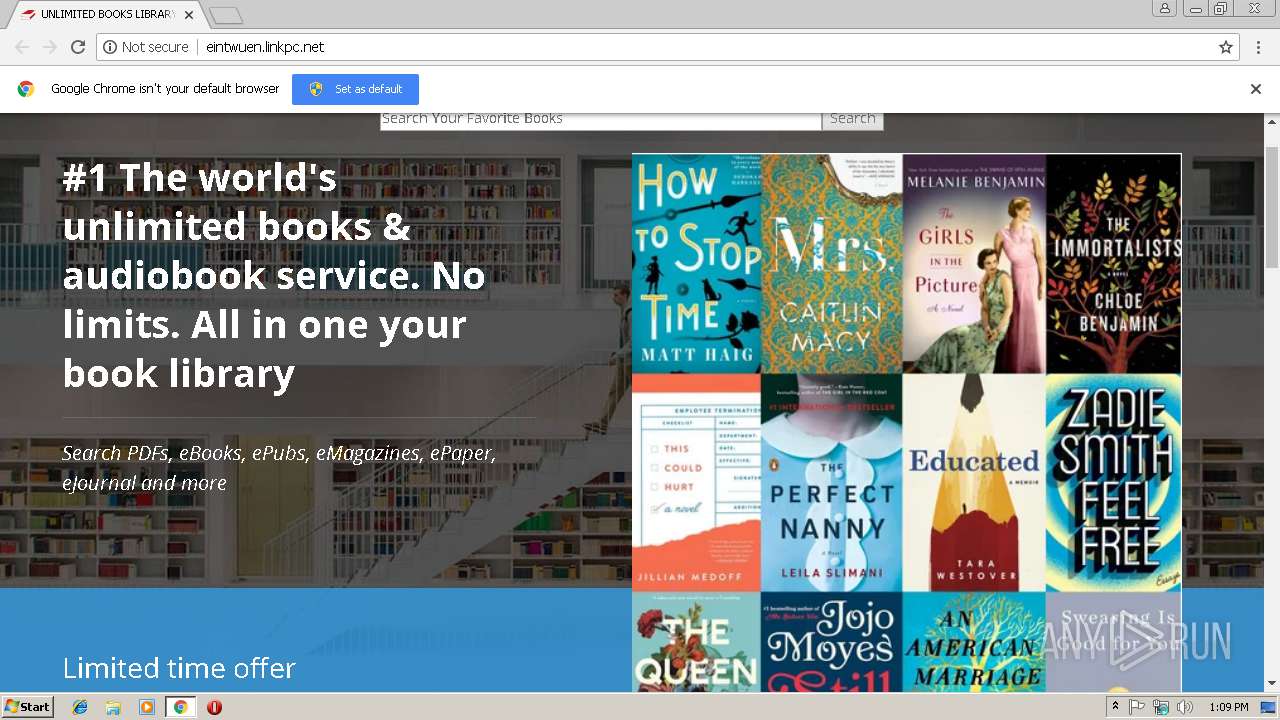
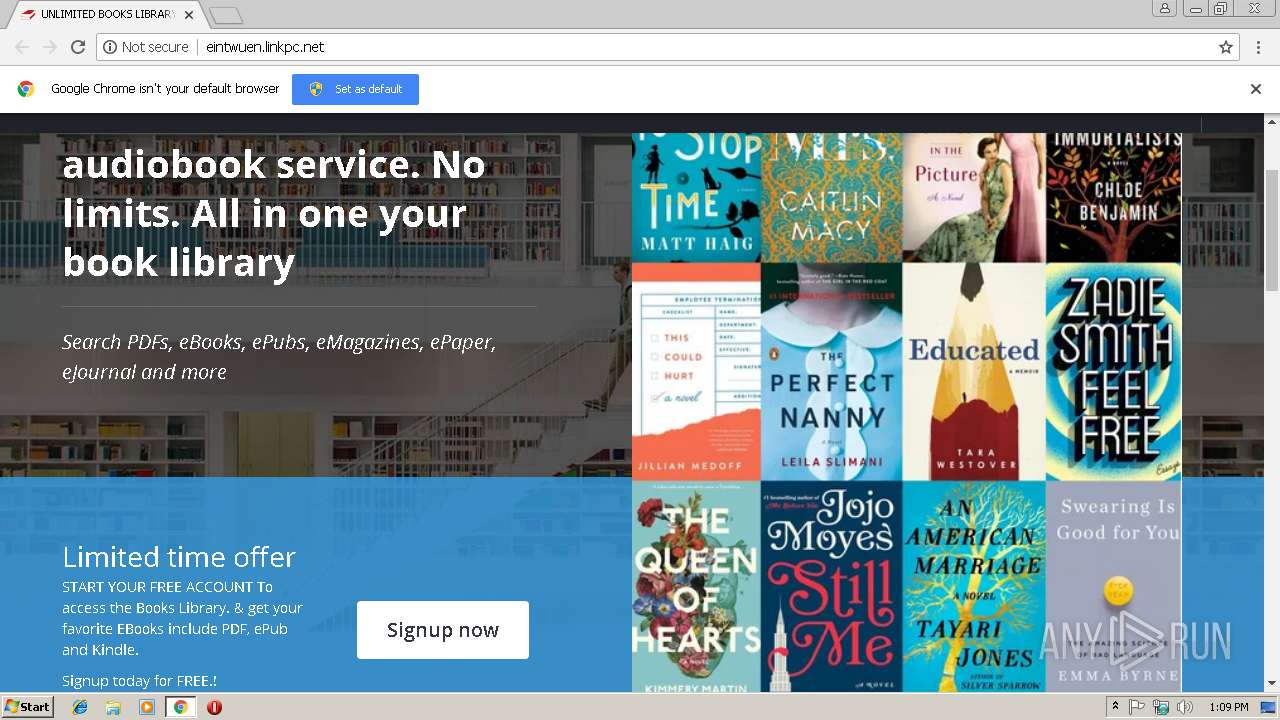
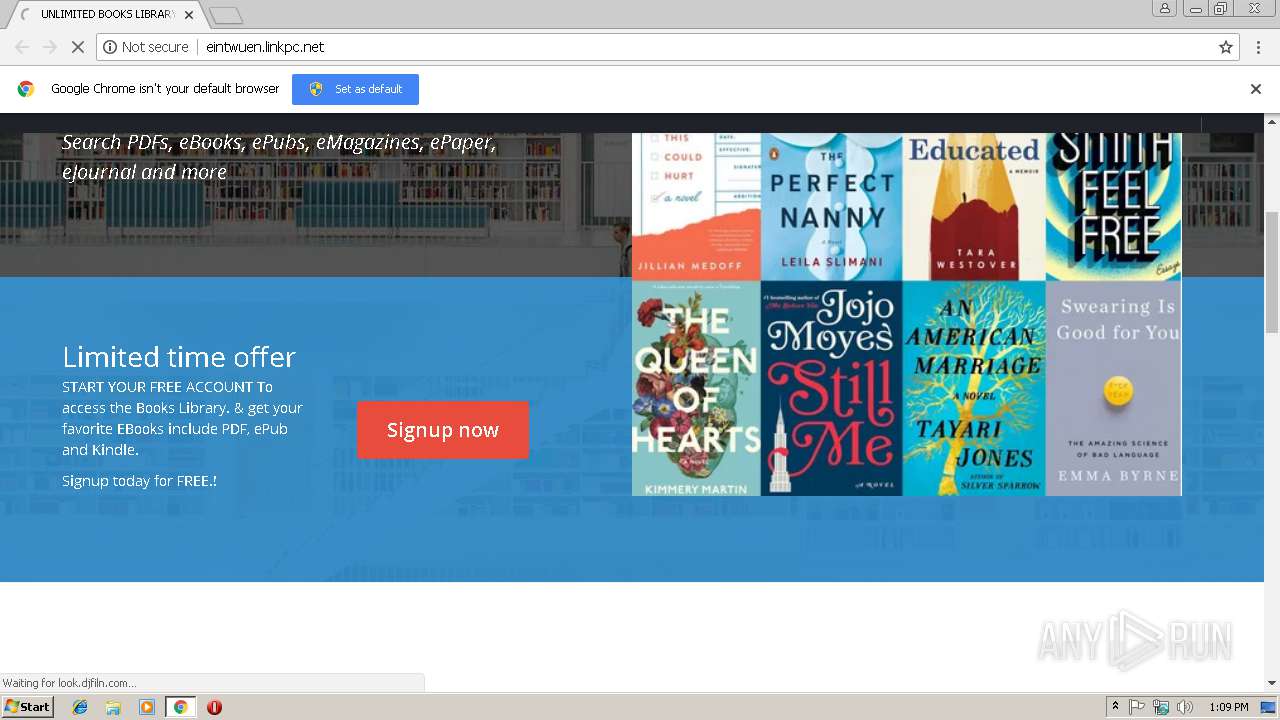
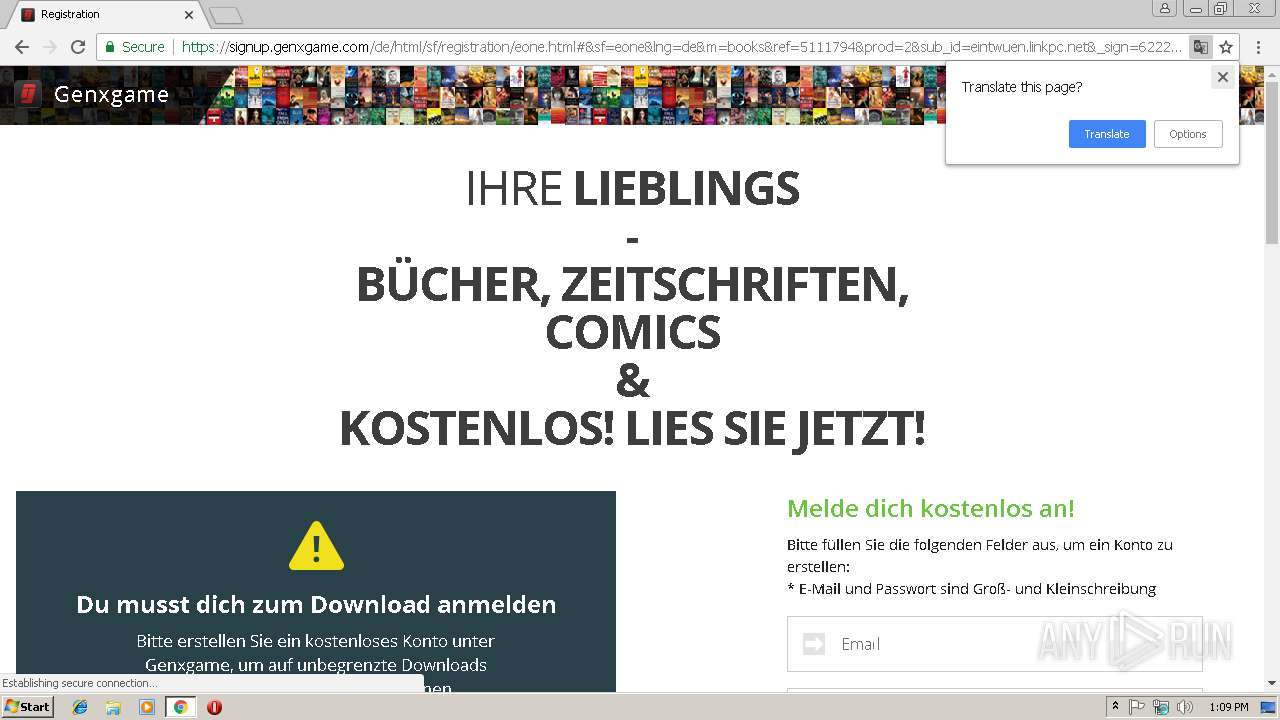
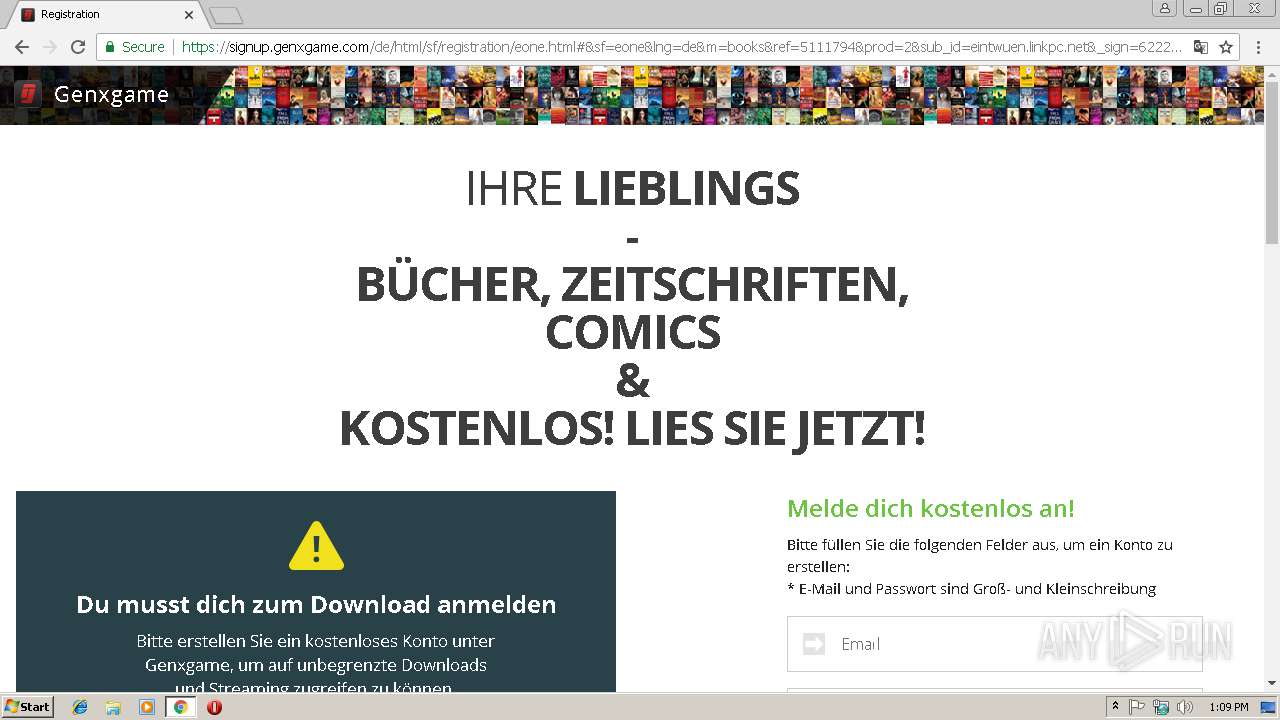
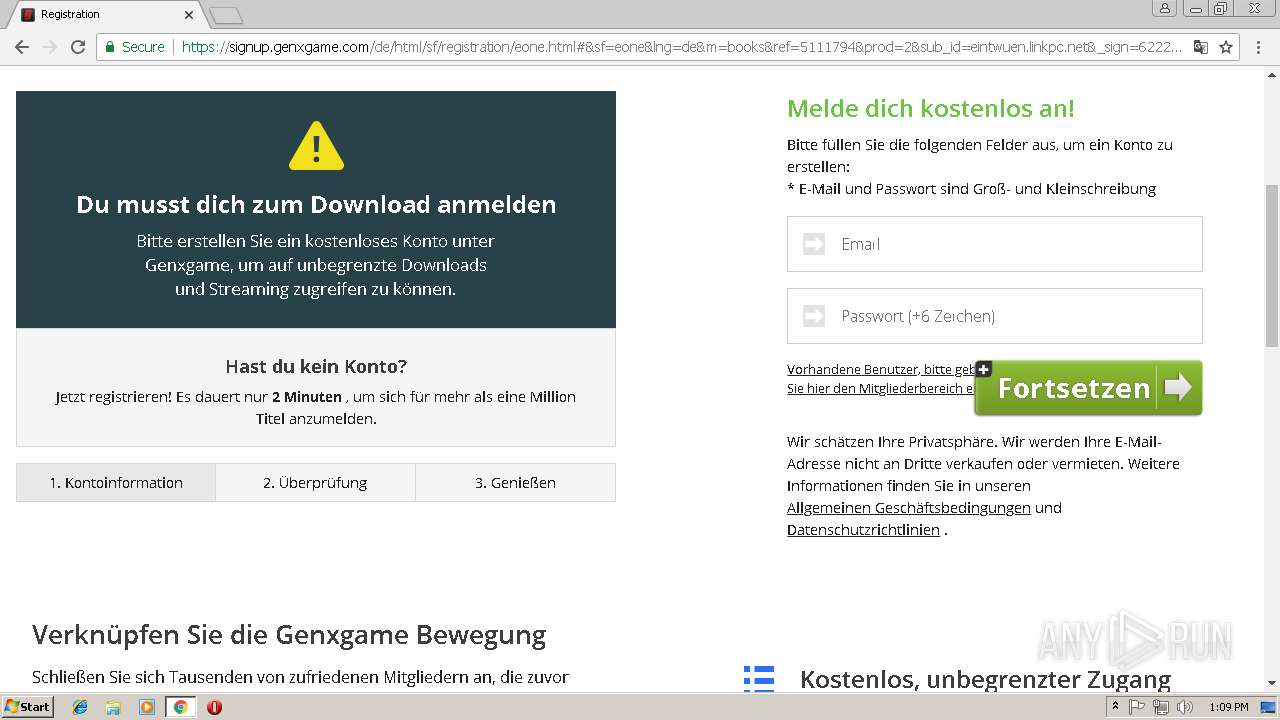
| URL: | http://eintwuen.linkpc.net |
| Full analysis: | https://app.any.run/tasks/05fa3f3d-faba-43ba-82d4-d5ccc55c90cf |
| Verdict: | Malicious activity |
| Analysis date: | January 22, 2019, 13:08:47 |
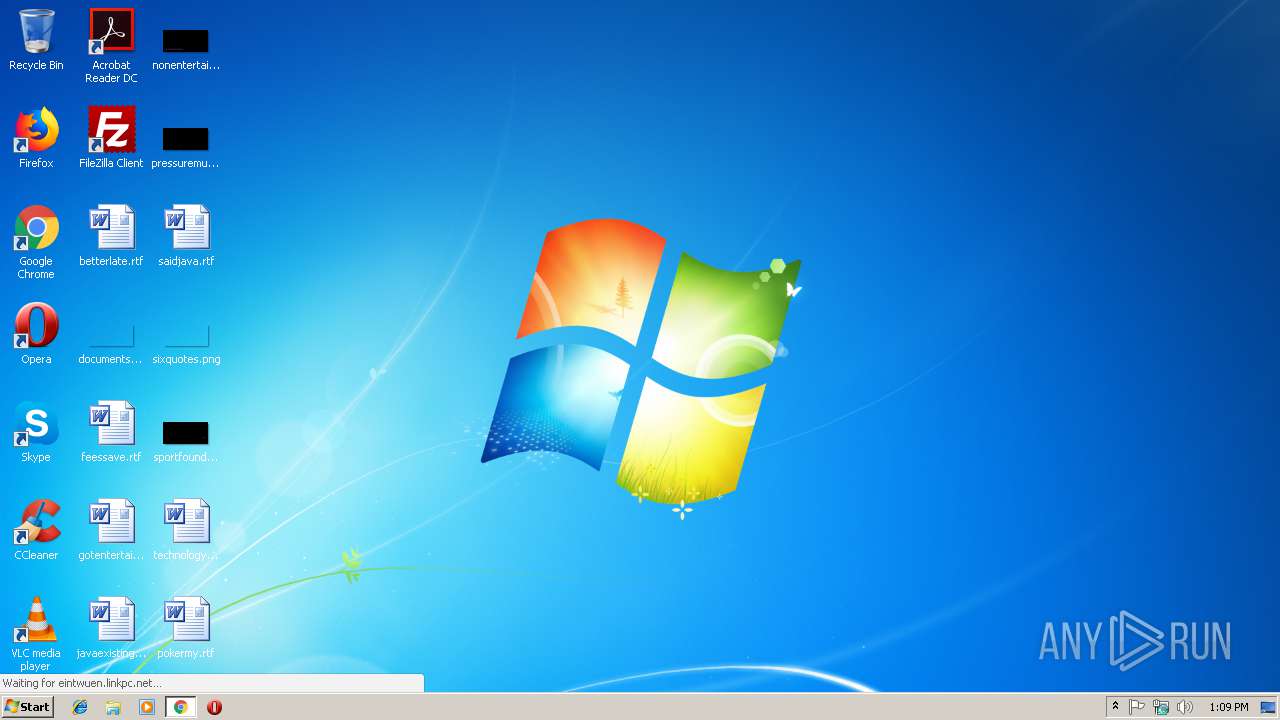
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | DB38017AF8FB290E635EF6F771C81931 |
| SHA1: | 506746FC56A6FB7D64CE6F31829F9D4F35563493 |
| SHA256: | B635985E2BE7BA9414C018505136B74724CA5EAE19460B045799CED5E34C9B01 |
| SSDEEP: | 3:N1KbKSVUAR:CVVZR |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 3004)
Connects to unusual port
- chrome.exe (PID: 3004)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
38
Monitored processes
9
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2200 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=884,6782429653125926169,8958812780097232084,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=B51D1A0AC804F08F04A7E6C3B2ADA01A --mojo-platform-channel-handle=860 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=884,6782429653125926169,8958812780097232084,131072 --enable-features=PasswordImport --service-pipe-token=EDEA617641312201EF0F4322488F25AD --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=EDEA617641312201EF0F4322488F25AD --renderer-client-id=4 --mojo-platform-channel-handle=1900 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2724 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=884,6782429653125926169,8958812780097232084,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=EB8C010442CE2A5719B854D15234638B --mojo-platform-channel-handle=3584 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2920 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=884,6782429653125926169,8958812780097232084,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4C340D6575D7133E88B7FA1C3F79FFDA --mojo-platform-channel-handle=516 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3008 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3004 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://eintwuen.linkpc.net | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=884,6782429653125926169,8958812780097232084,131072 --enable-features=PasswordImport --service-pipe-token=D334FF1F5863B9F93A75015075729B00 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=D334FF1F5863B9F93A75015075729B00 --renderer-client-id=3 --mojo-platform-channel-handle=2144 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3728 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6f3b00b0,0x6f3b00c0,0x6f3b00cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3888 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=884,6782429653125926169,8958812780097232084,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=ED773286B1869F76042EACEFEA1AEA9D --mojo-platform-channel-handle=3096 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
507
Read events
459
Write events
45
Delete events
3
Modification events
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3004-13192636143124625 |
Value: 259 | |||
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
0
Suspicious files
23
Text files
77
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\3010bb6a-552f-4793-9238-4f91f49e1711.tmp | — | |
MD5:— | SHA256:— | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\0759d357-4348-4837-b8a5-71bb930bbd89.tmp | — | |
MD5:— | SHA256:— | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF246ce3.TMP | text | |
MD5:— | SHA256:— | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF246ce3.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
56
DNS requests
27
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
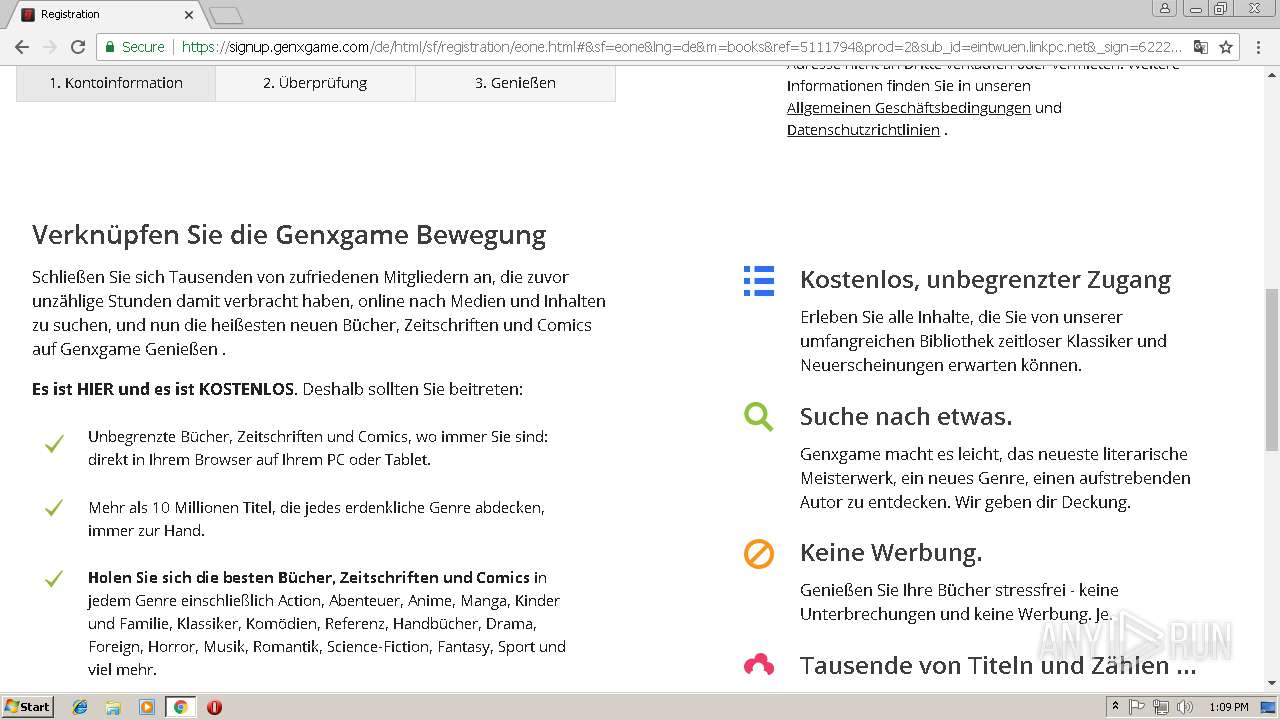
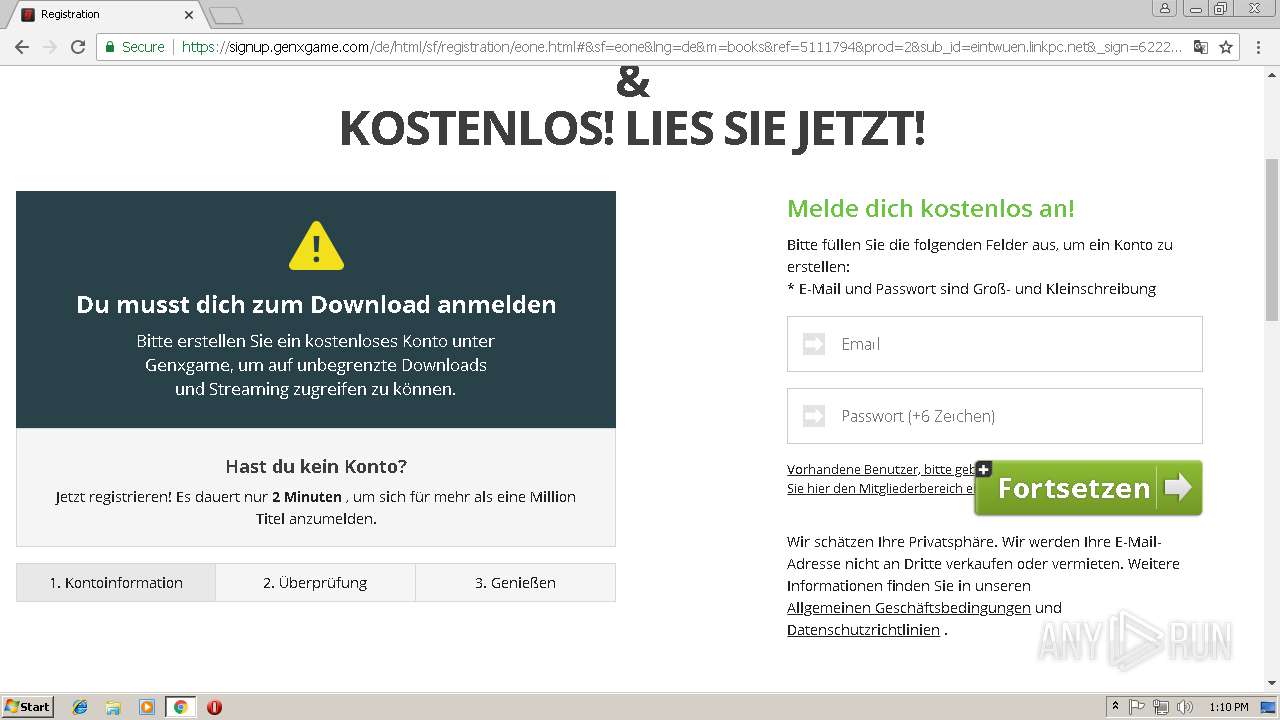
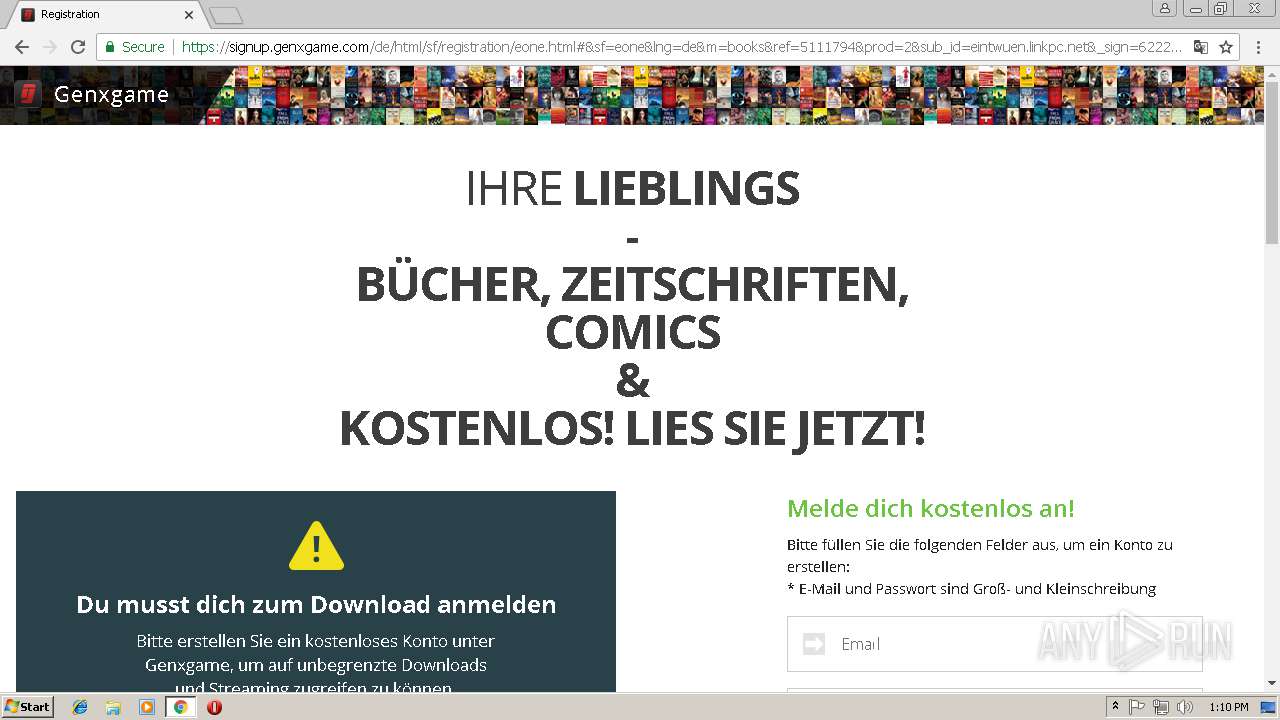
3004 | chrome.exe | GET | 200 | 104.248.60.92:80 | http://eintwuen.linkpc.net/ | US | html | 3.95 Kb | malicious |
3004 | chrome.exe | GET | 404 | 104.248.60.92:80 | http://eintwuen.linkpc.net/lib/font-awesome/fonts/fontawesome-webfont.woff2?v=4.6.3 | US | html | 1.33 Kb | malicious |
3004 | chrome.exe | GET | 200 | 104.248.60.92:80 | http://eintwuen.linkpc.net/index/free-sign-up.jpg | US | image | 20.1 Kb | malicious |
3004 | chrome.exe | GET | 200 | 104.248.60.92:80 | http://eintwuen.linkpc.net/index/device.gif | US | image | 42.2 Kb | malicious |
3004 | chrome.exe | GET | 200 | 104.248.60.92:80 | http://eintwuen.linkpc.net/index/genesis.js | US | text | 12.5 Kb | malicious |
3004 | chrome.exe | GET | 404 | 104.248.60.92:80 | http://eintwuen.linkpc.net/lib/font-awesome/fonts/fontawesome-webfont.woff?v=4.6.3 | US | html | 1.33 Kb | malicious |
3004 | chrome.exe | GET | 200 | 172.217.21.195:80 | http://fonts.gstatic.com/s/opensans/v15/mem5YaGs126MiZpBA-UN_r8OUuhp.woff2 | US | woff2 | 14.2 Kb | whitelisted |
3004 | chrome.exe | GET | 200 | 104.248.60.92:80 | http://eintwuen.linkpc.net/index/icon.ico | US | image | 14.7 Kb | malicious |
3004 | chrome.exe | GET | 200 | 172.217.21.195:80 | http://fonts.gstatic.com/s/opensans/v15/mem8YaGs126MiZpBA-UFVZ0b.woff2 | US | woff2 | 13.7 Kb | whitelisted |
3004 | chrome.exe | GET | 200 | 104.248.60.92:80 | http://eintwuen.linkpc.net/index/min.css | US | text | 87.1 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3004 | chrome.exe | 172.217.18.174:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3004 | chrome.exe | 216.58.208.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3004 | chrome.exe | 104.248.60.92:80 | eintwuen.linkpc.net | — | US | malicious |
3004 | chrome.exe | 172.217.21.202:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3004 | chrome.exe | 172.217.22.1:443 | 1.bp.blogspot.com | Google Inc. | US | whitelisted |
3004 | chrome.exe | 216.58.206.14:443 | clients1.google.com | Google Inc. | US | whitelisted |
3004 | chrome.exe | 216.58.206.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3004 | chrome.exe | 176.34.187.161:80 | look.djfiln.com | Amazon.com, Inc. | IE | unknown |
3004 | chrome.exe | 18.185.163.80:80 | titan.infra.systems | — | US | unknown |
3004 | chrome.exe | 34.233.63.79:80 | studcat.infra.systems | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
eintwuen.linkpc.net |
| malicious |
www.gstatic.com |
| whitelisted |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
1.bp.blogspot.com |
| whitelisted |
3.bp.blogspot.com |
| whitelisted |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3004 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3004 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
1 ETPRO signatures available at the full report