| URL: | http://ads.ad-center.com/b?ad_domain=hlok.qertewrt.com&ad_path=%2Foffer&prod=141&ref=5086402&sf=&utm_source=www.readebooks.me&utm_medium=referral&placement=http%3A%2F%2Fwww.readebooks.me%2Fdownload%2F42363379%2F%3Fformat%3Dpdf&adserver=1.4.1&m=books&lp=472&lid=30d26201-c9f6-4def-8740-df563ba2cb0a&lid_hash=44d728bac228fb5672d950de91189b37&bounce=http%3A%2F%2Fwww.urbookdownload.com%2Fsignup%3Fb%3D1 |
| Full analysis: | https://app.any.run/tasks/178da960-2347-4b53-9e81-cf73f0613107 |
| Verdict: | Malicious activity |
| Analysis date: | December 22, 2019, 08:10:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 10B3BC14B52DCC6B1B6D6177B3B6F86D |
| SHA1: | EB6780E4F11B8E4A7B2549E2B1BCF19D2831B110 |
| SHA256: | B62A973ED0FF74A83EC627D2D9D11E2A8BE72CFEC6FC97B77C2BA80F4D4A82C4 |
| SSDEEP: | 12:W+uw6sSX9DZssP6fKh1wK4SFuWhTBo1csvGKcC:qskDadv6uWzQbB |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2148)
INFO
Reads the hosts file
- chrome.exe (PID: 2180)
- chrome.exe (PID: 2148)
Application launched itself
- chrome.exe (PID: 2148)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
66
Monitored processes
31
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,18368019146270478229,2049338201933400176,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17411000719318302454 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2416 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 716 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,18368019146270478229,2049338201933400176,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5975902405317163023 --mojo-platform-channel-handle=4004 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,18368019146270478229,2049338201933400176,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17010336791854575080 --mojo-platform-channel-handle=3456 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,18368019146270478229,2049338201933400176,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8718882941772433876 --mojo-platform-channel-handle=3468 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,18368019146270478229,2049338201933400176,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12983503522124295404 --mojo-platform-channel-handle=4468 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,18368019146270478229,2049338201933400176,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7948997343822440285 --mojo-platform-channel-handle=4188 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,18368019146270478229,2049338201933400176,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11081667306697194719 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2780 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,18368019146270478229,2049338201933400176,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11972927237780524197 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2192 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,18368019146270478229,2049338201933400176,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13024566352682494861 --mojo-platform-channel-handle=3776 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,18368019146270478229,2049338201933400176,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3394186206466267079 --renderer-client-id=28 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3876 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
643
Read events
544
Write events
94
Delete events
5
Modification events
| (PID) Process: | (2148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2148-13221475870207500 |
Value: 259 | |||
| (PID) Process: | (2148) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
52
Text files
232
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\d4dc9c98-8167-48c4-9a07-1017e7951aa2.tmp | — | |
MD5:— | SHA256:— | |||
| 2148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF39a89e.TMP | text | |
MD5:— | SHA256:— | |||
| 2148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF39a8be.TMP | text | |
MD5:— | SHA256:— | |||
| 2148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
37
TCP/UDP connections
63
DNS requests
38
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2180 | chrome.exe | GET | 200 | 172.217.23.174:80 | http://www.google-analytics.com/ga_exp.js?utmxkey=&utmx=&utmxx=&utmxtime=1577002272751 | US | — | — | whitelisted |
2180 | chrome.exe | GET | 200 | 3.83.180.6:80 | http://www.urbookdownload.com/images/signup/books/k/book-content.jpg | US | image | 22.3 Kb | unknown |
2180 | chrome.exe | GET | 200 | 3.83.180.6:80 | http://www.urbookdownload.com/css/signup/books/k/main.php?cache_control=1 | US | text | 15.1 Kb | unknown |
2180 | chrome.exe | GET | 200 | 3.83.180.6:80 | http://www.urbookdownload.com/images/signup/books/k/video-throbber.gif | US | image | 10.3 Kb | unknown |
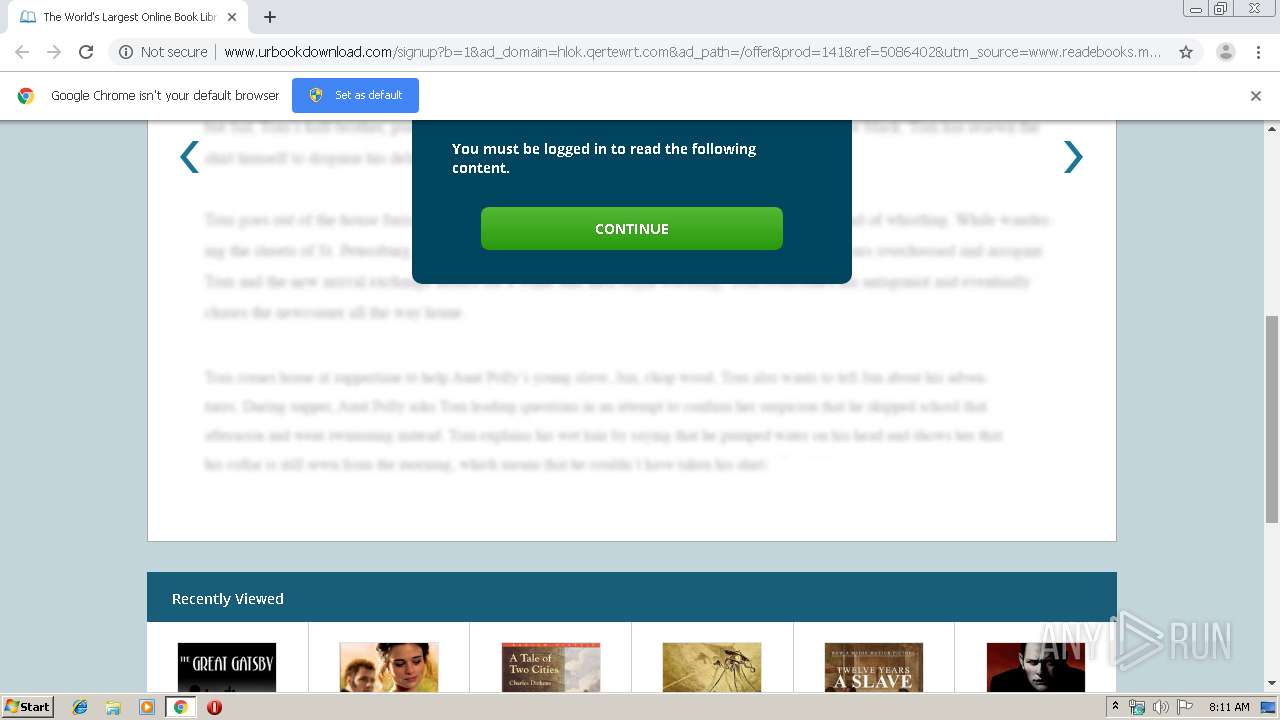
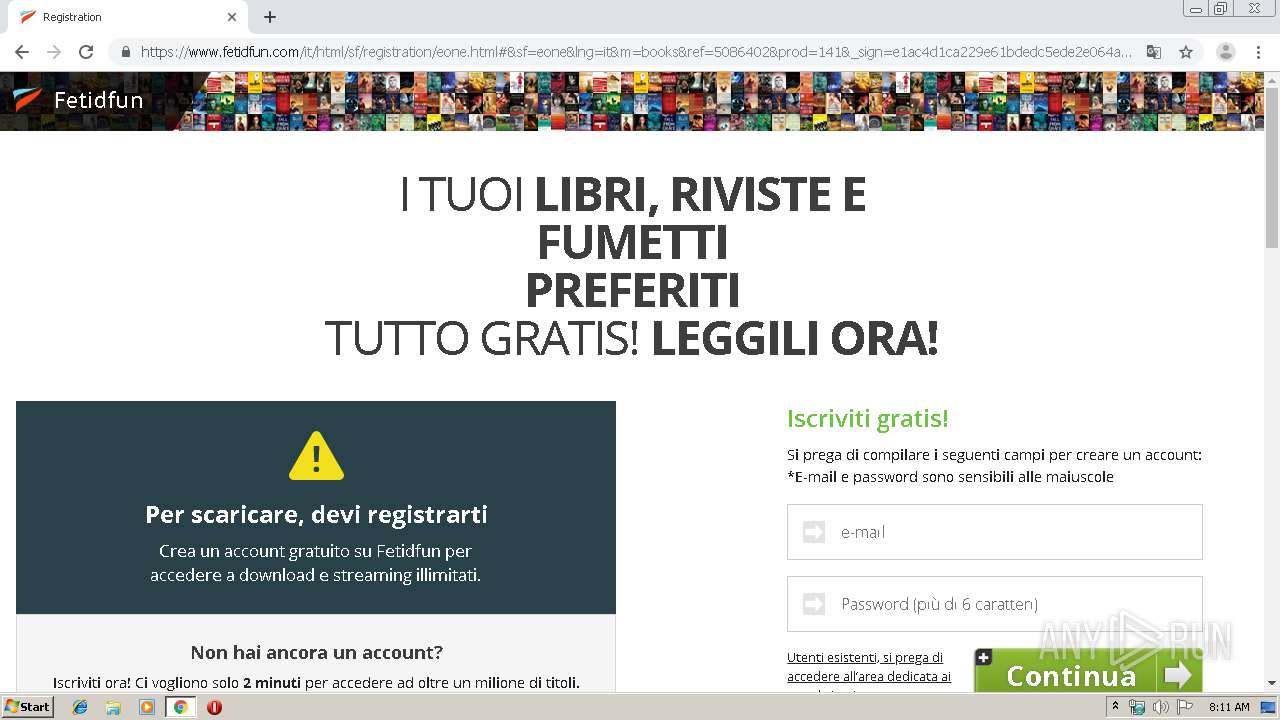
2180 | chrome.exe | GET | 200 | 3.83.180.6:80 | http://www.urbookdownload.com/signup?b=1&ad_domain=hlok.qertewrt.com&ad_path=/offer&prod=141&ref=5086402&utm_source=www.readebooks.me&utm_medium=referral&placement=http://www.readebooks.me/download/42363379/?format=pdf&adserver=1.4.1&m=books&lp=472&lid=30d26201-c9f6-4def-8740-df563ba2cb0a&lid_hash=44d728bac228fb5672d950de91189b37&bounce=http://www.urbookdownload.com/signup?b=1&sid=737&bt=1577002272241&bh=2776639233 | US | html | 3.50 Kb | unknown |
2180 | chrome.exe | GET | 200 | 3.83.180.6:80 | http://www.urbookdownload.com/images/signup/books/k/menu-icon.png | US | image | 1.16 Kb | unknown |
2180 | chrome.exe | GET | 200 | 3.83.180.6:80 | http://www.urbookdownload.com/images/signup/books/k/4-star.png | US | image | 1.75 Kb | unknown |
2180 | chrome.exe | GET | 200 | 3.83.180.6:80 | http://www.urbookdownload.com/images/signup/books/k/popup-logo.png | US | image | 4.75 Kb | unknown |
2180 | chrome.exe | GET | 200 | 3.83.180.6:80 | http://www.urbookdownload.com/images/signup/books/k/book6.jpg | US | image | 16.3 Kb | unknown |
2180 | chrome.exe | GET | 200 | 3.83.180.6:80 | http://www.urbookdownload.com/images/signup/books/k/book1.jpg | US | image | 10.1 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
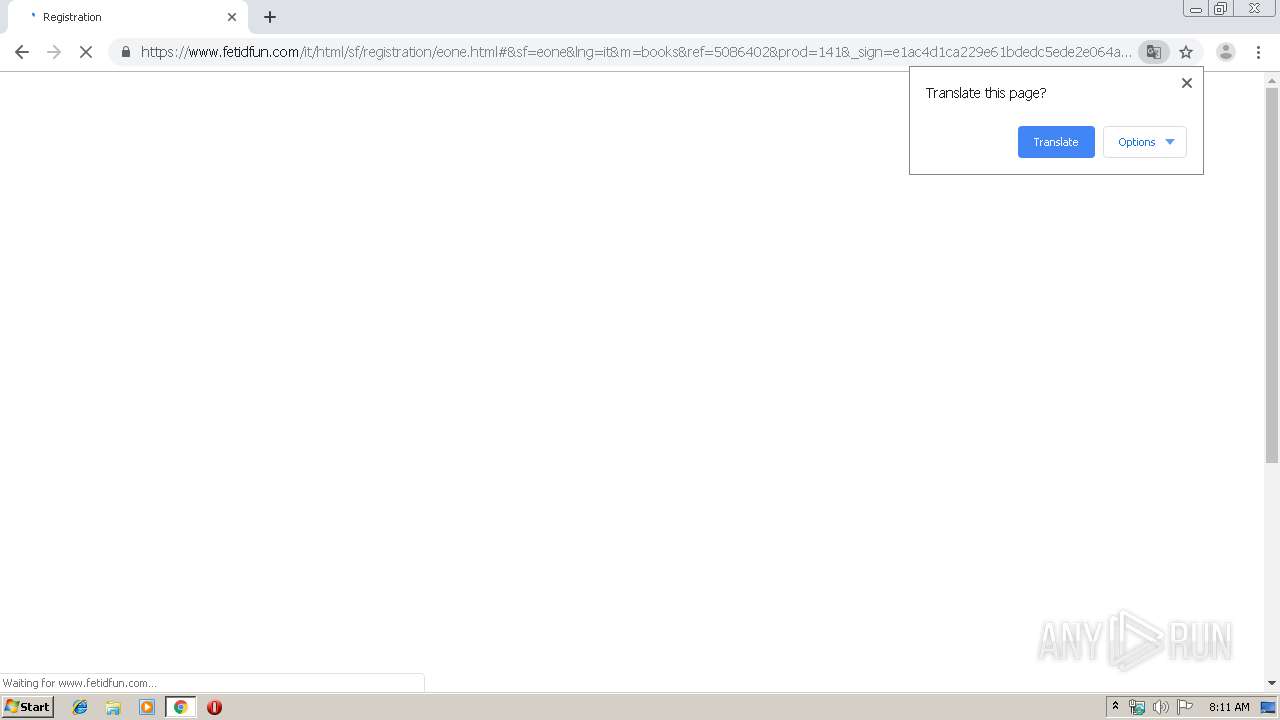
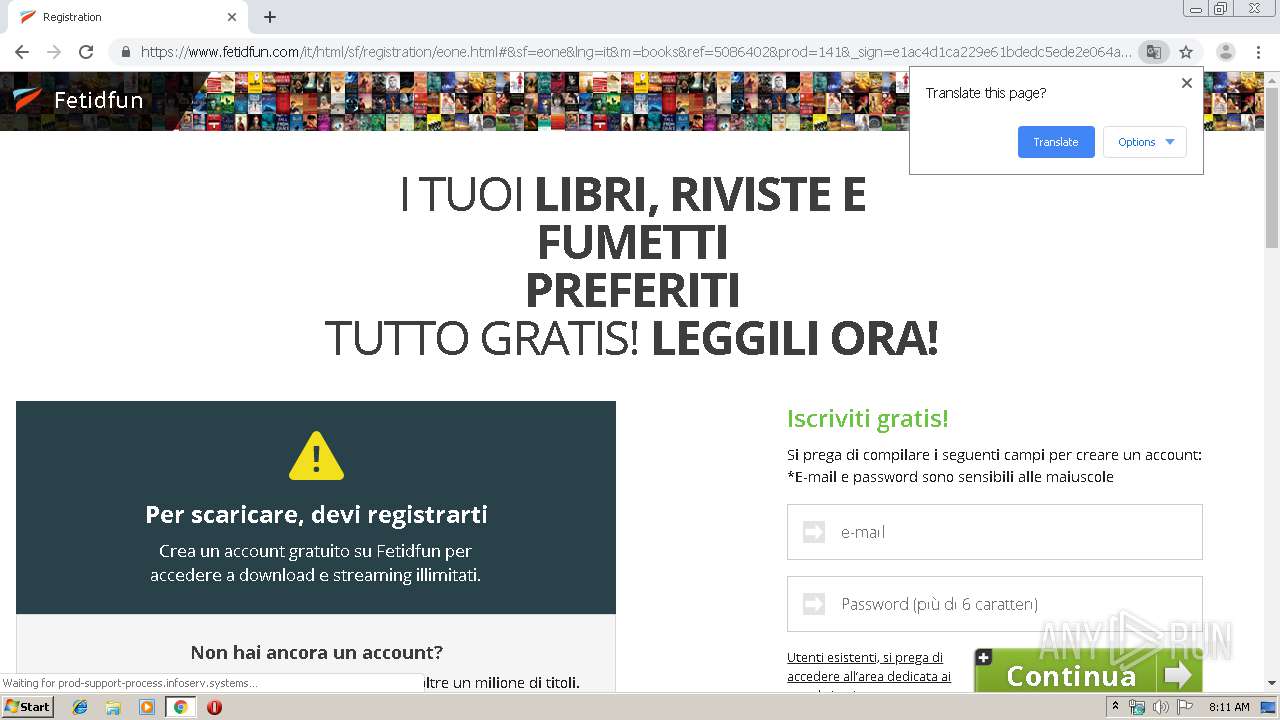
— | — | 54.228.242.20:80 | ads.ad-center.com | Amazon.com, Inc. | IE | unknown |
2180 | chrome.exe | 216.58.208.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2180 | chrome.exe | 54.228.242.20:80 | ads.ad-center.com | Amazon.com, Inc. | IE | unknown |
2180 | chrome.exe | 172.217.18.109:443 | accounts.google.com | Google Inc. | US | suspicious |
2180 | chrome.exe | 172.217.23.174:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
2180 | chrome.exe | 172.217.22.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2180 | chrome.exe | 64.233.184.155:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
2180 | chrome.exe | 172.217.23.104:80 | www.googletagmanager.com | Google Inc. | US | suspicious |
2180 | chrome.exe | 172.217.16.202:80 | ajax.googleapis.com | Google Inc. | US | whitelisted |
2180 | chrome.exe | 52.216.185.13:443 | s3.amazonaws.com | Amazon.com, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
ads.ad-center.com |
| suspicious |
accounts.google.com |
| shared |
www.urbookdownload.com |
| unknown |
fonts.googleapis.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
downloadplayerz.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2180 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2180 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |