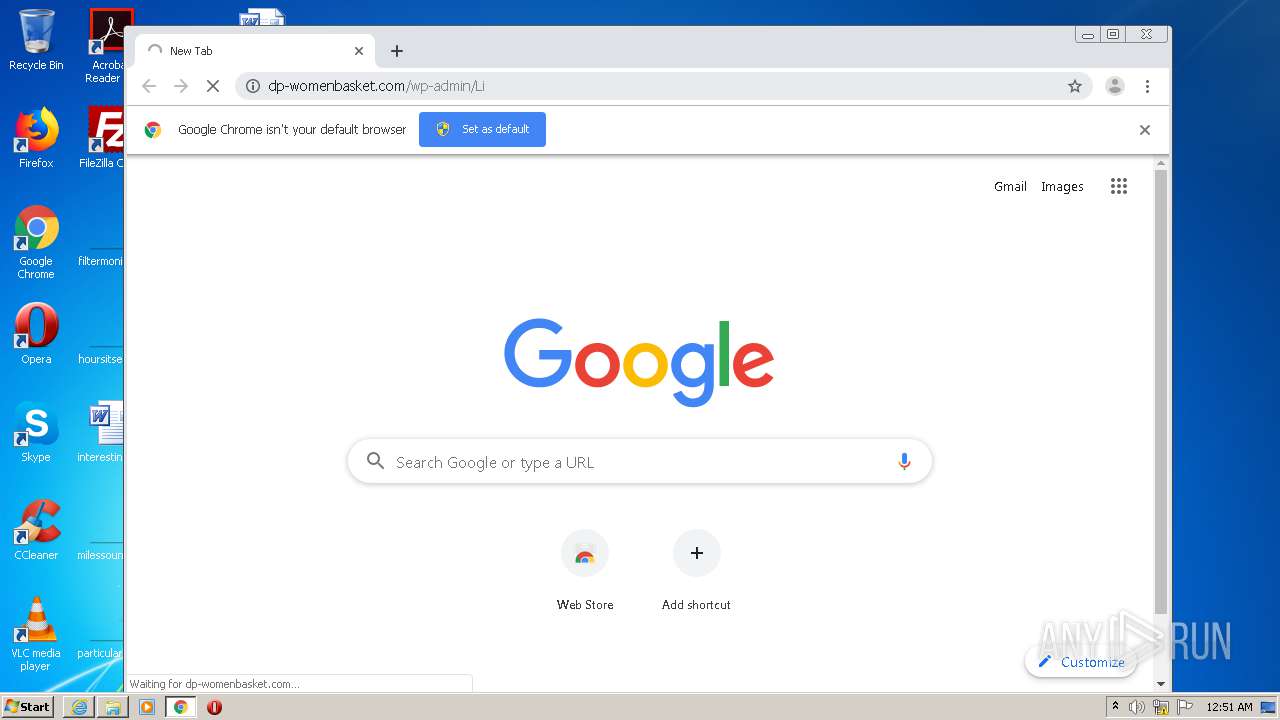
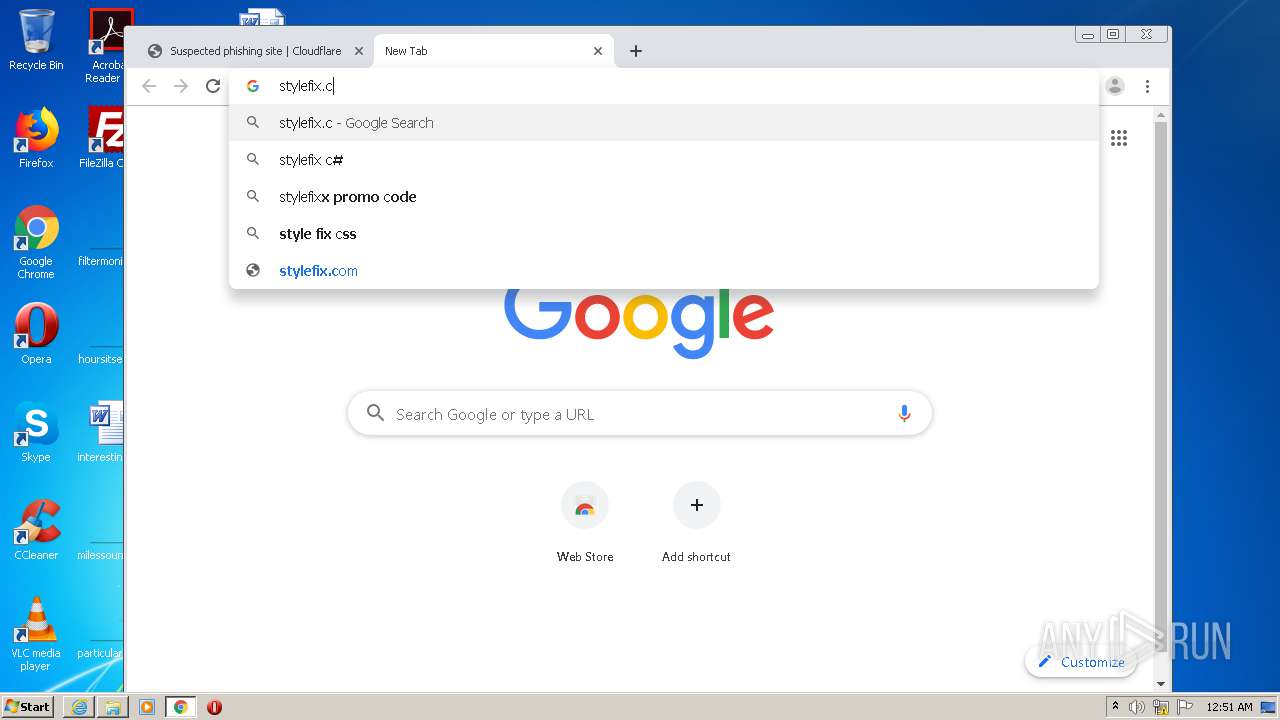
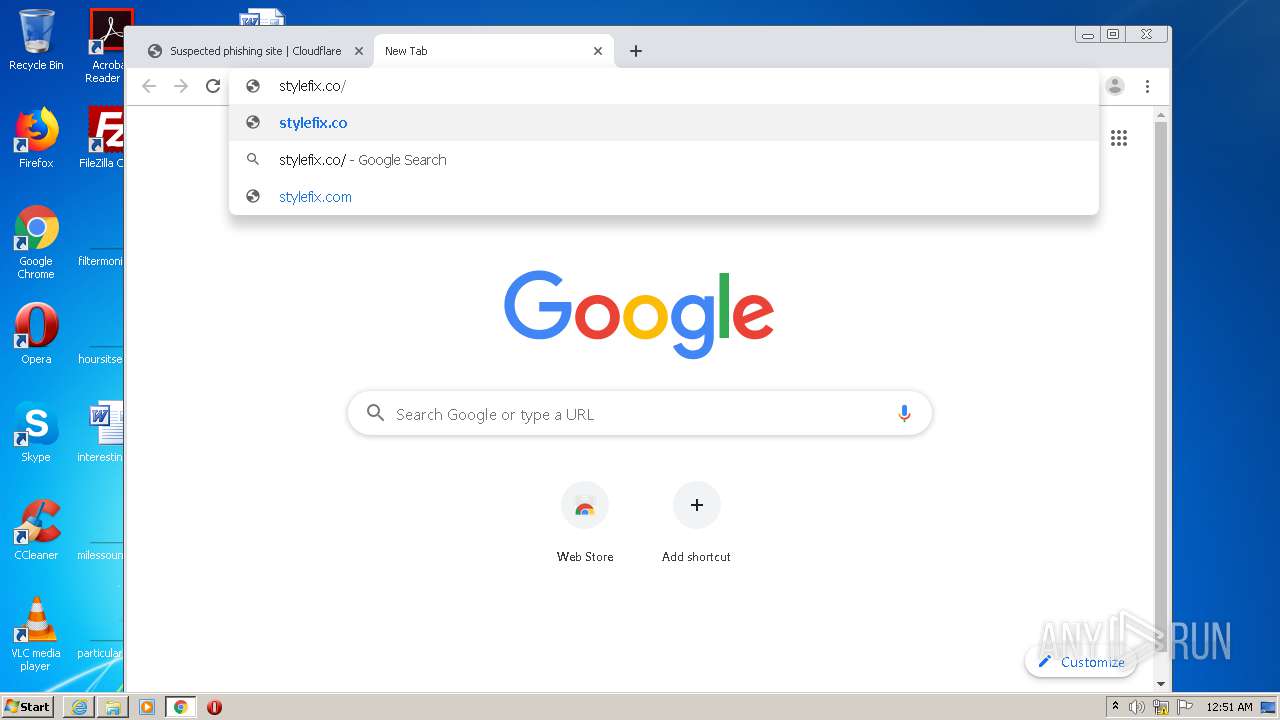
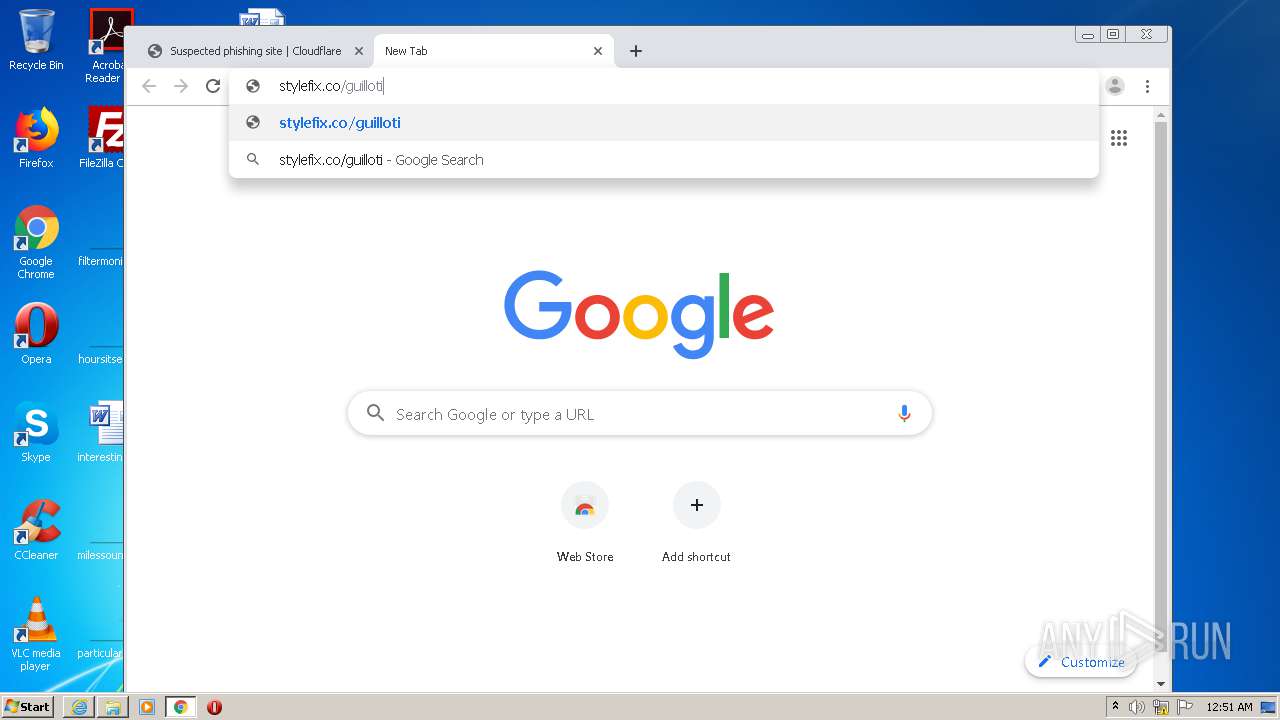
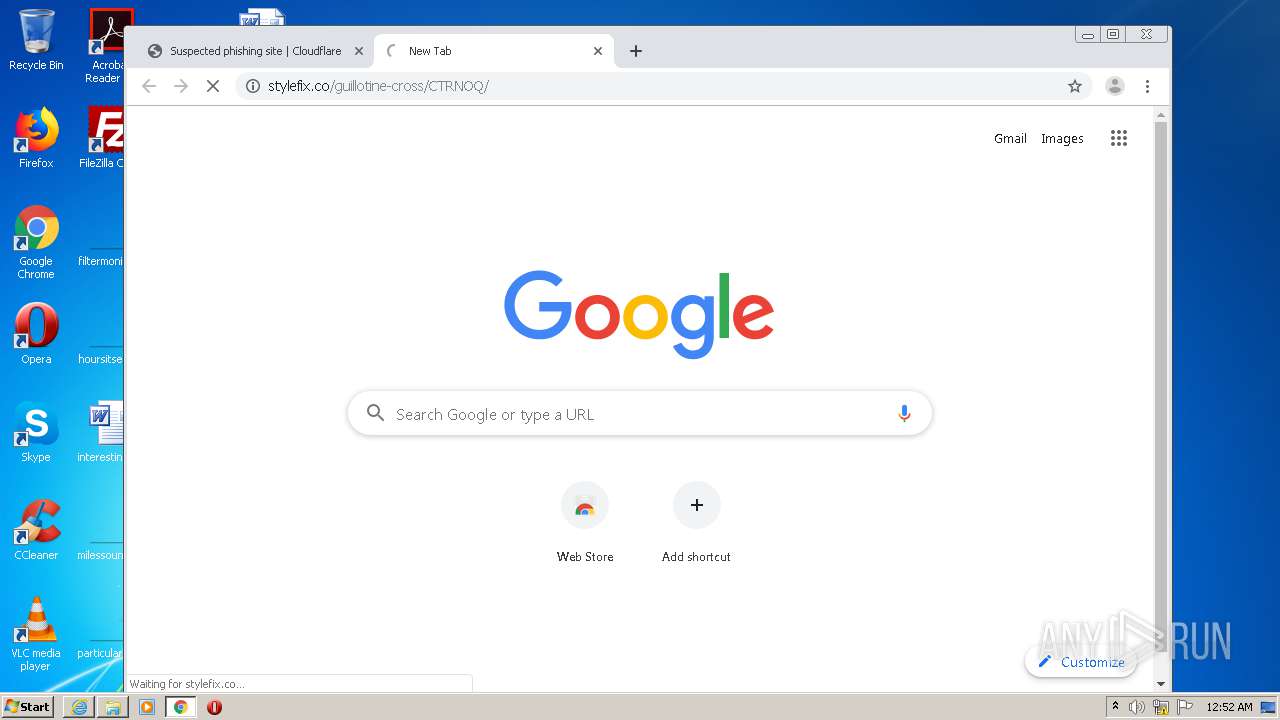
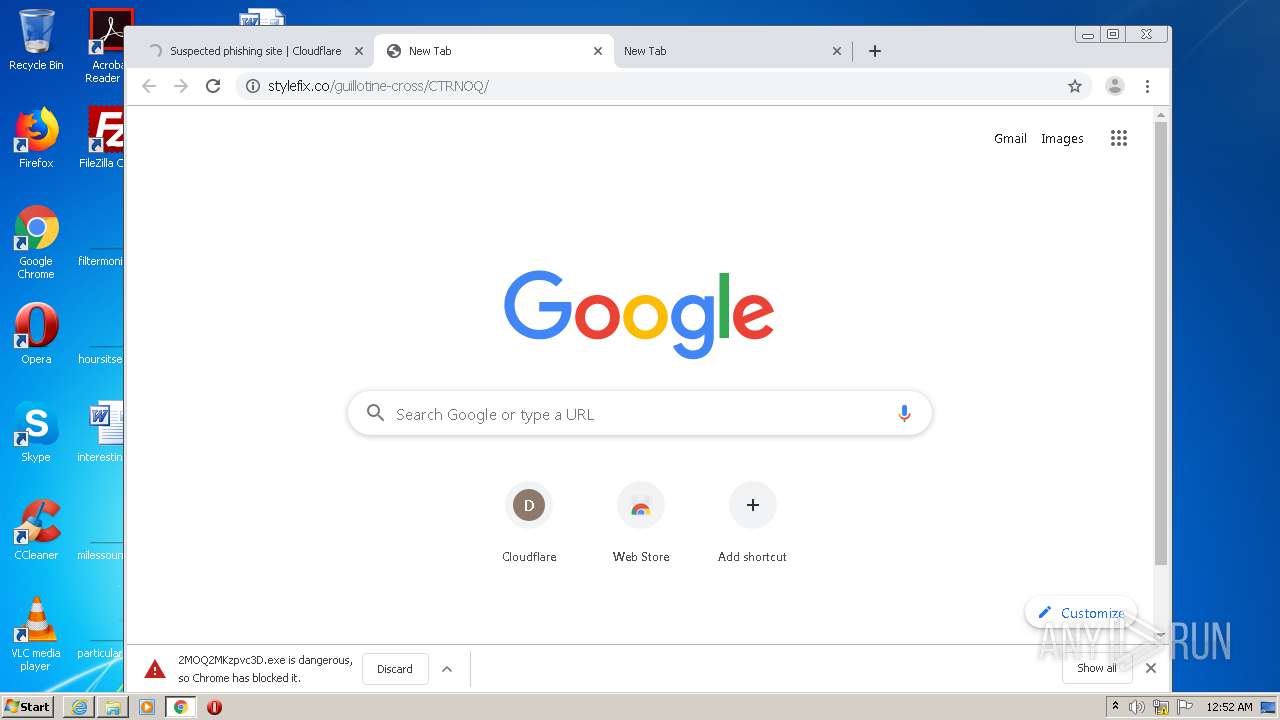
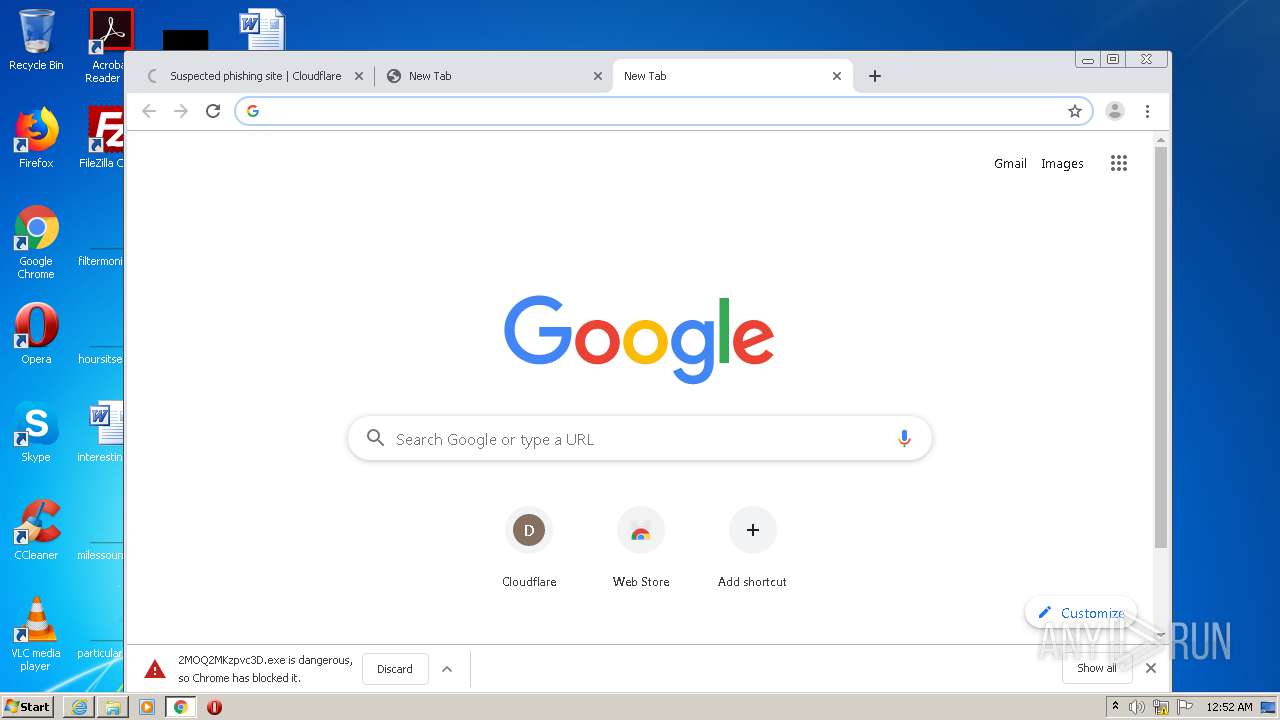
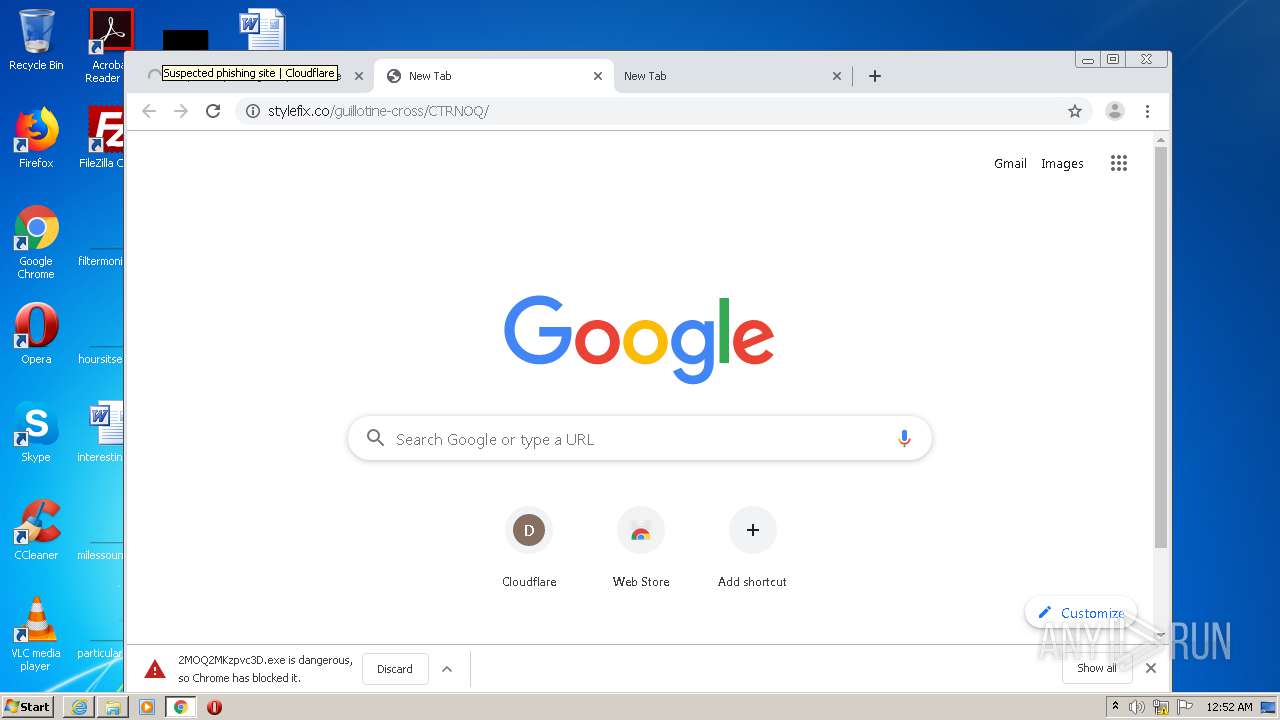
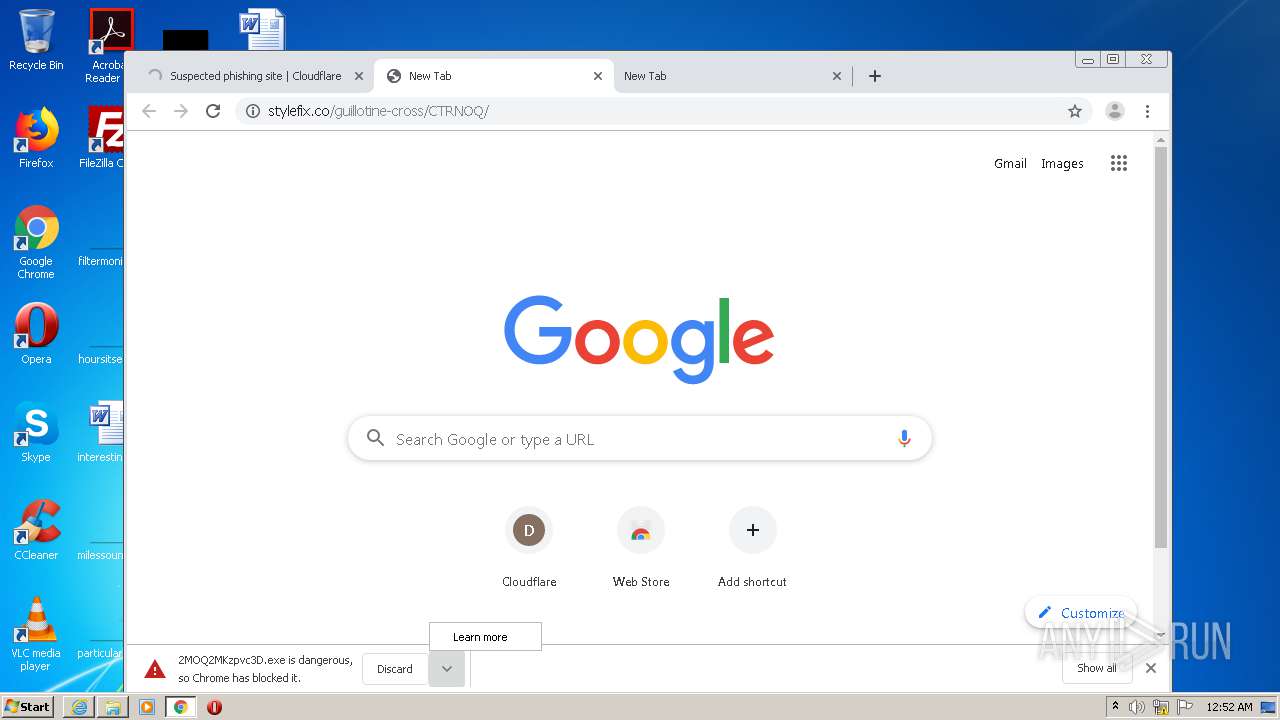
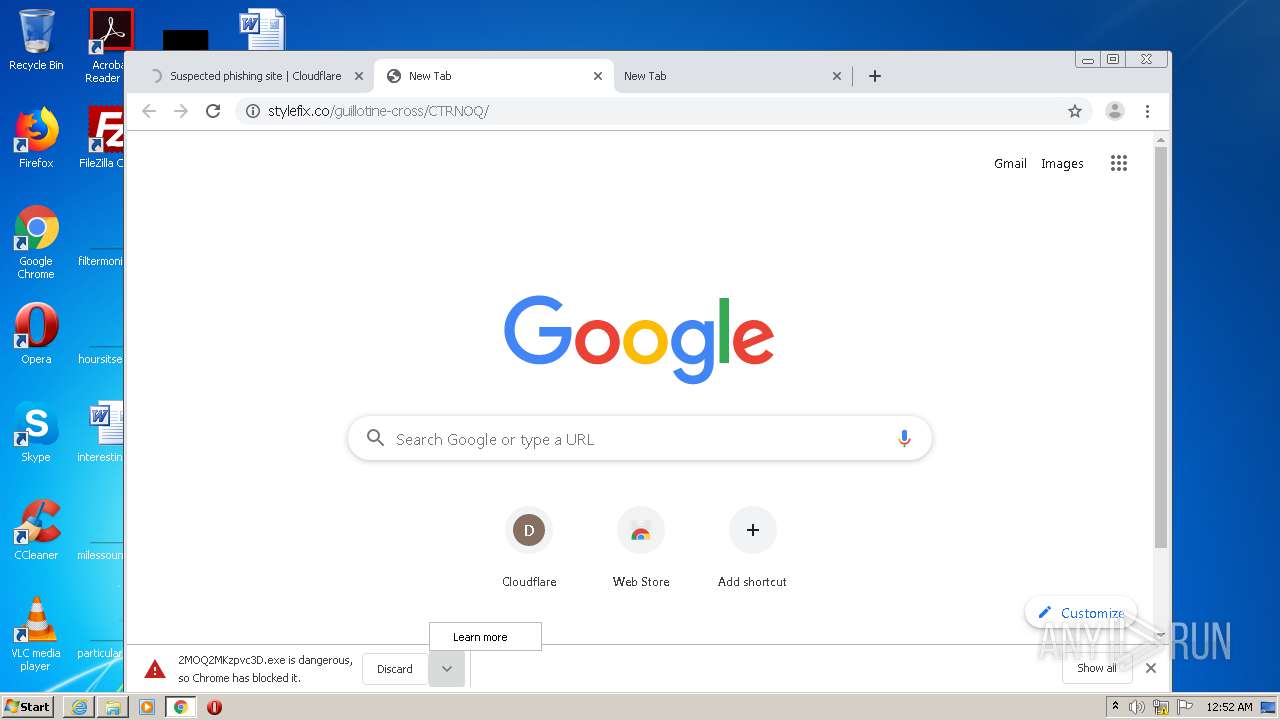
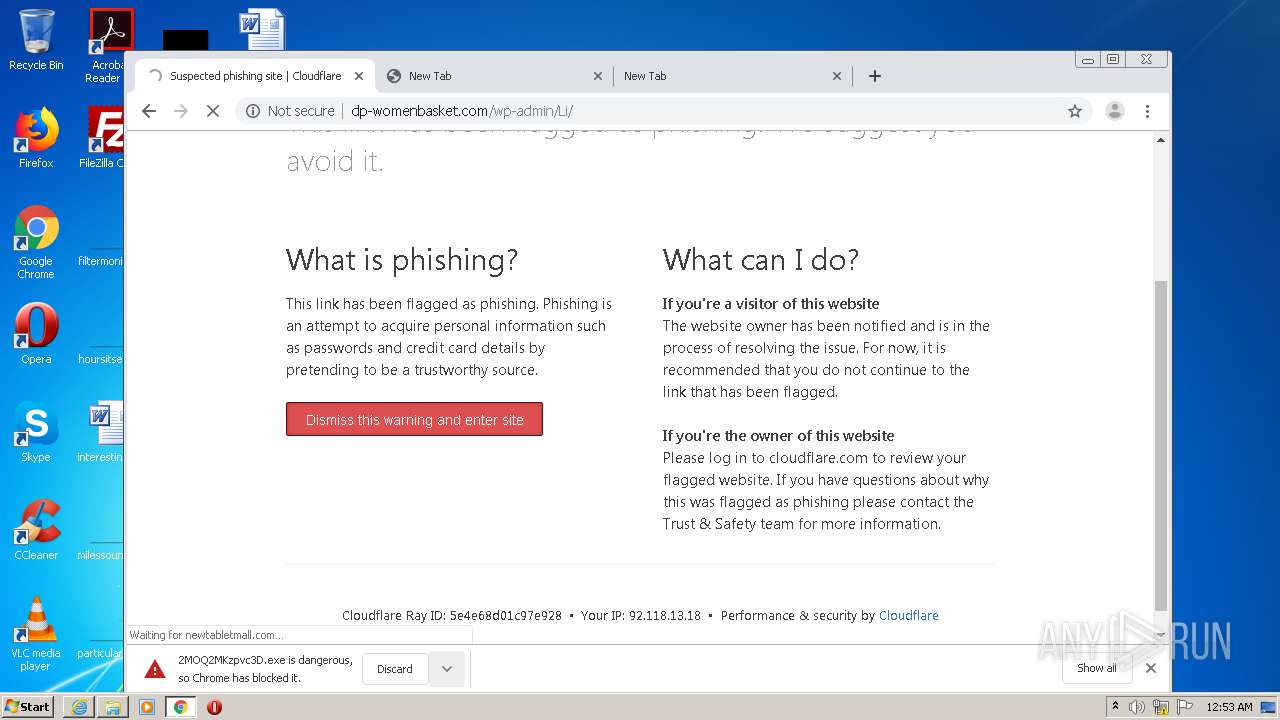
| URL: | http://stylefix.co/guillotine-cross/CTRNOQ/ |
| Full analysis: | https://app.any.run/tasks/55526c83-3b7c-47f3-af4f-08c3c311612f |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 19, 2020, 23:49:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 278D45969F3977EE8ABCCDE1DD75E29A |
| SHA1: | 6A9CCBB6C8824468309115EA6E40CBE101D4BA08 |
| SHA256: | B6267682185447125D614D2EC3347C5CADBB8654B30967DED48D8FD6AECCF4C1 |
| SSDEEP: | 3:N1KNR8GK2XN0x3LKn:Cz/axbK |
MALICIOUS
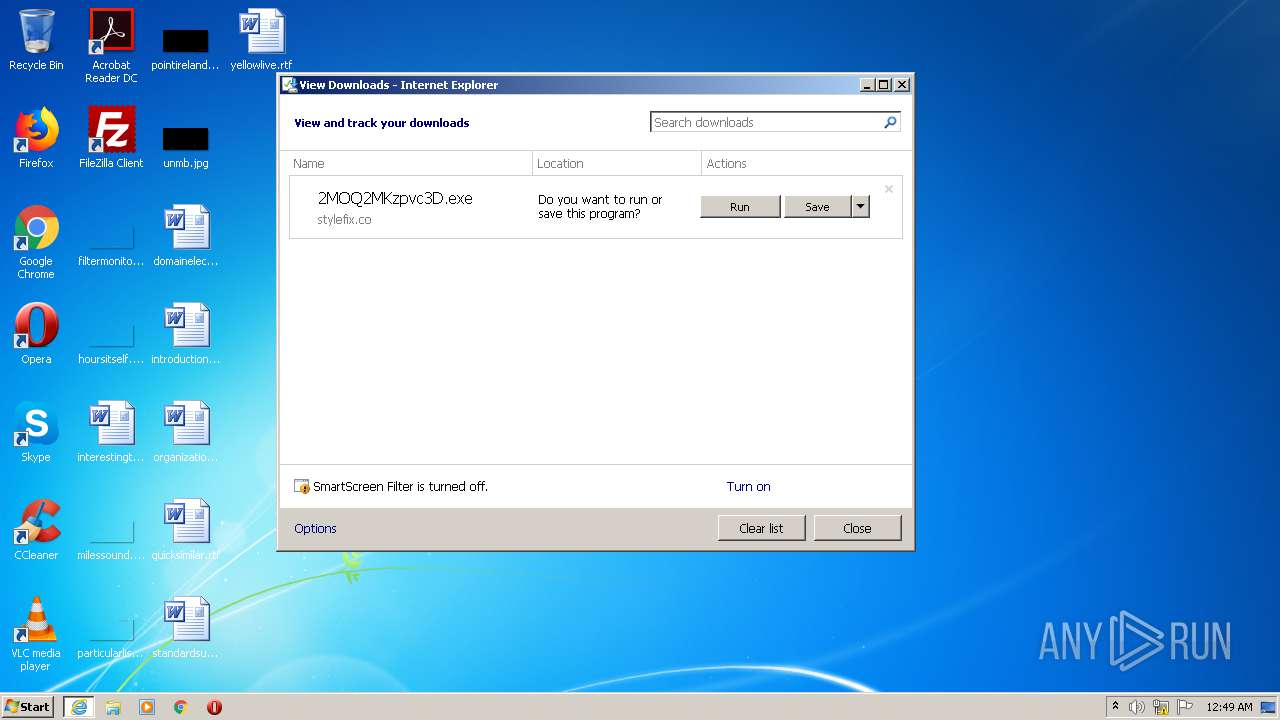
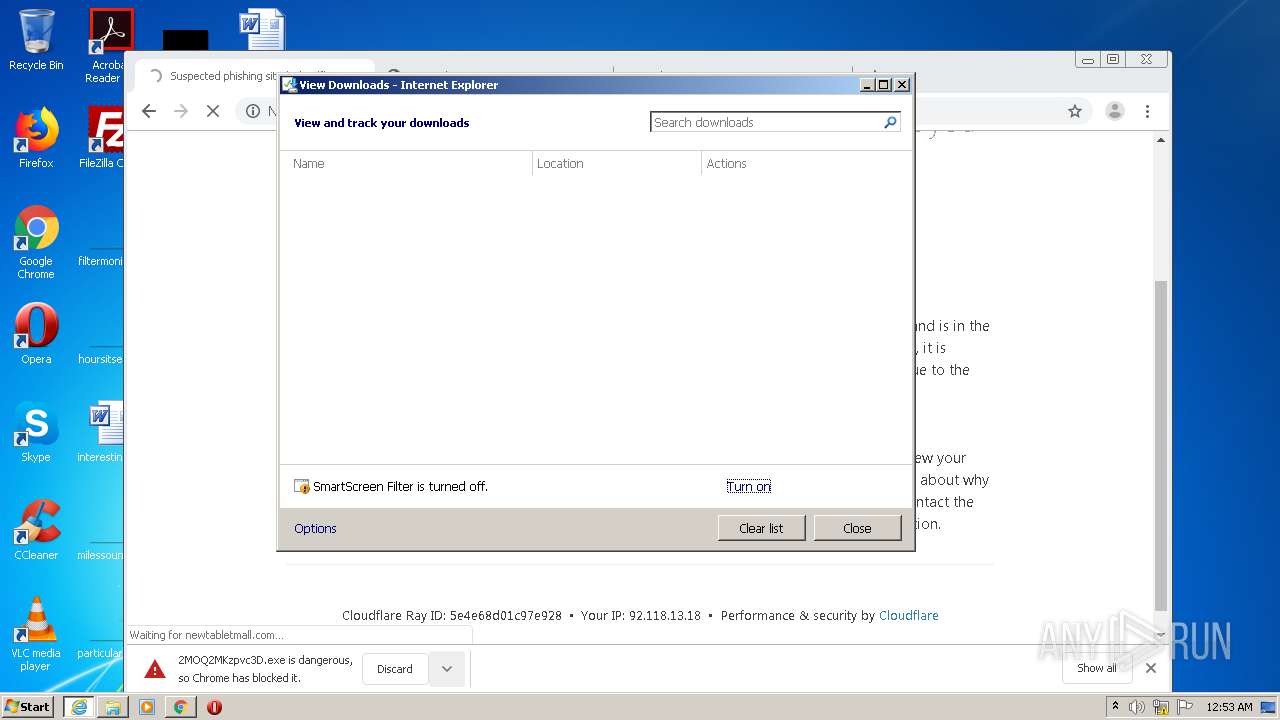
Downloads executable files from the Internet
- iexplore.exe (PID: 1956)
Application was dropped or rewritten from another process
- 2MOQ2MKzpvc3D.exe (PID: 1204)
- AzSqlExt.exe (PID: 1876)
Changes the autorun value in the registry
- AzSqlExt.exe (PID: 1876)
Connects to CnC server
- AzSqlExt.exe (PID: 1876)
EMOTET was detected
- AzSqlExt.exe (PID: 1876)
SUSPICIOUS
Executable content was dropped or overwritten
- iexplore.exe (PID: 1956)
- iexplore.exe (PID: 2080)
- 2MOQ2MKzpvc3D.exe (PID: 1204)
- chrome.exe (PID: 2536)
- chrome.exe (PID: 3320)
Cleans NTFS data-stream (Zone Identifier)
- 2MOQ2MKzpvc3D.exe (PID: 1204)
Reads Internet Cache Settings
- AzSqlExt.exe (PID: 1876)
Starts itself from another location
- 2MOQ2MKzpvc3D.exe (PID: 1204)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 2080)
- iexplore.exe (PID: 1956)
Changes internet zones settings
- iexplore.exe (PID: 2080)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2080)
Creates files in the user directory
- iexplore.exe (PID: 1956)
- iexplore.exe (PID: 2080)
Application launched itself
- iexplore.exe (PID: 2080)
- chrome.exe (PID: 2536)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2080)
Reads settings of System Certificates
- iexplore.exe (PID: 2080)
Changes settings of System certificates
- iexplore.exe (PID: 2080)
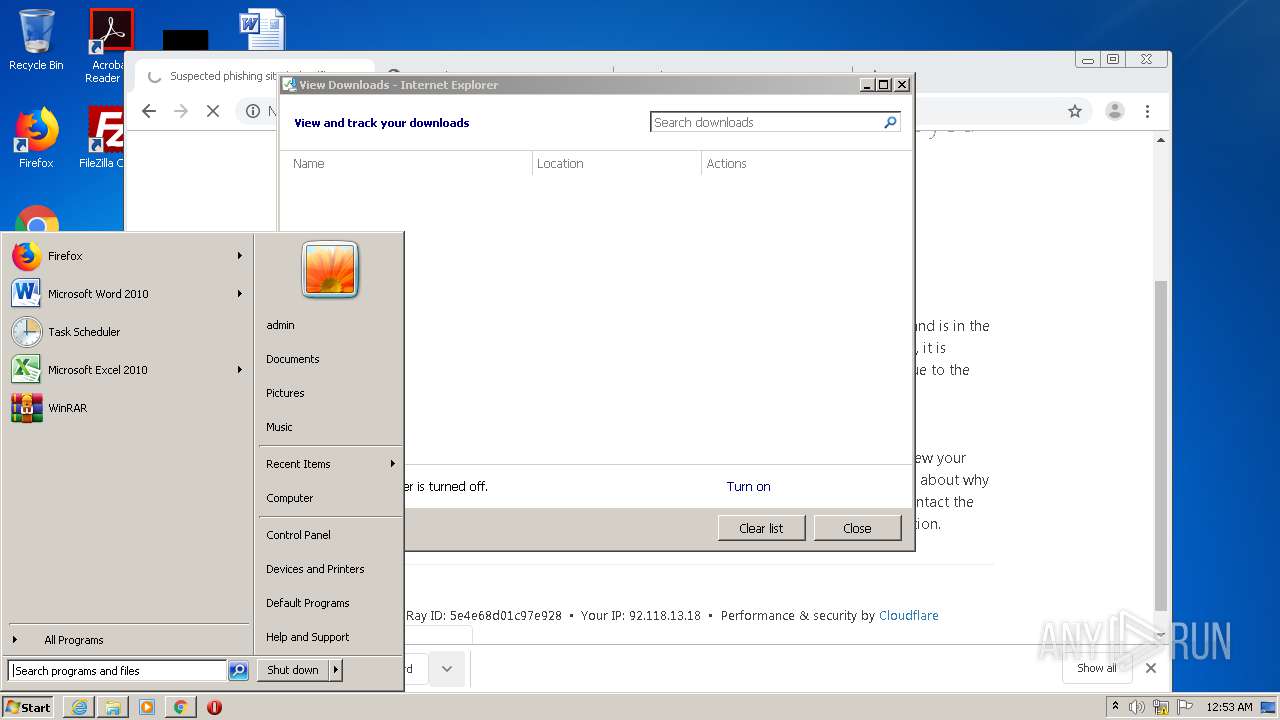
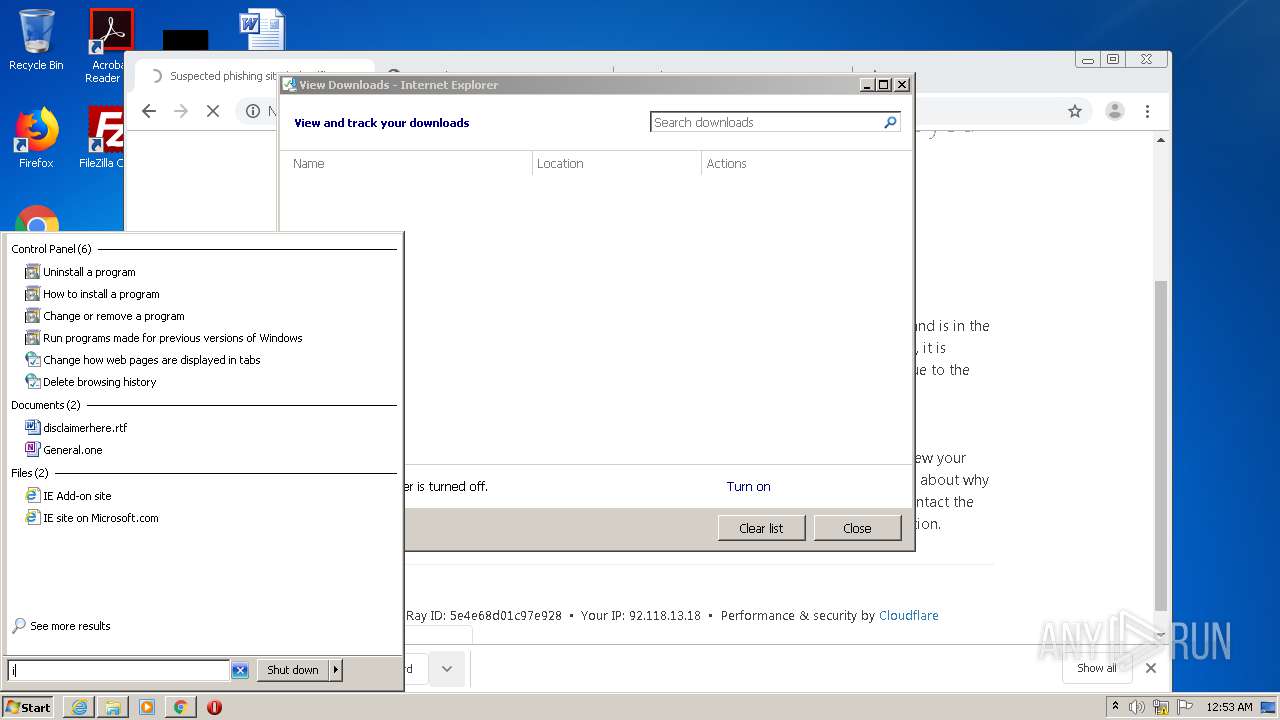
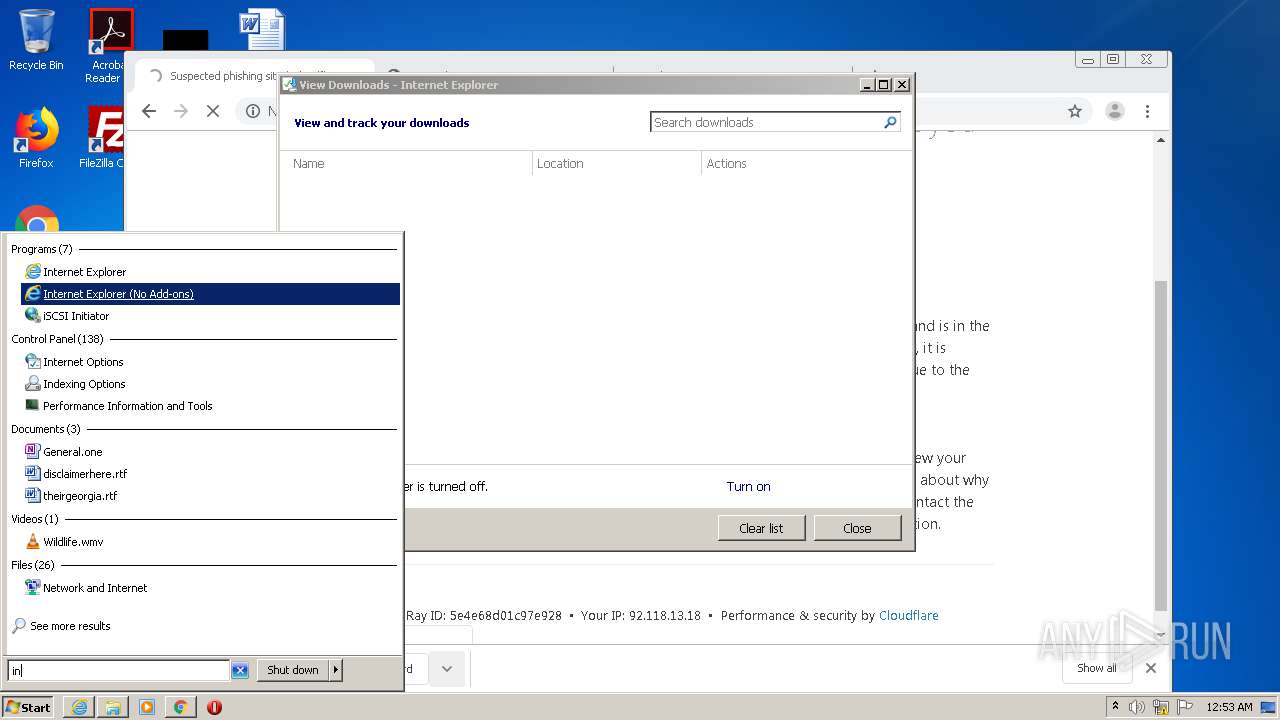
Manual execution by user
- chrome.exe (PID: 2536)
- explorer.exe (PID: 256)
Reads the hosts file
- chrome.exe (PID: 2536)
- chrome.exe (PID: 3320)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
71
Monitored processes
31
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 256 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1016,6160380183750622276,1394277728618949282,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=7197030722732749832 --mojo-platform-channel-handle=1012 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,6160380183750622276,1394277728618949282,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9733664759691775132 --mojo-platform-channel-handle=3024 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,6160380183750622276,1394277728618949282,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=215195328132851836 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2500 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2496 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1204 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\2MOQ2MKzpvc3D.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\2MOQ2MKzpvc3D.exe | iexplore.exe | ||||||||||||
User: admin Company: TODO: <Co Integrity Level: MEDIUM Description: TODO: <File descri Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 1352 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) | |||||||||||||||
| 1356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,6160380183750622276,1394277728618949282,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9545498050041058454 --mojo-platform-channel-handle=2056 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,6160380183750622276,1394277728618949282,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11306562494483308739 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3064 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,6160380183750622276,1394277728618949282,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18403249094754788103 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2260 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 164
Read events
2 005
Write events
153
Delete events
6
Modification events
| (PID) Process: | (2080) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2333865370 | |||
| (PID) Process: | (2080) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30844530 | |||
| (PID) Process: | (2080) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2080) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2080) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2080) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2080) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2080) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2080) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2080) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
7
Suspicious files
39
Text files
114
Unknown types
3
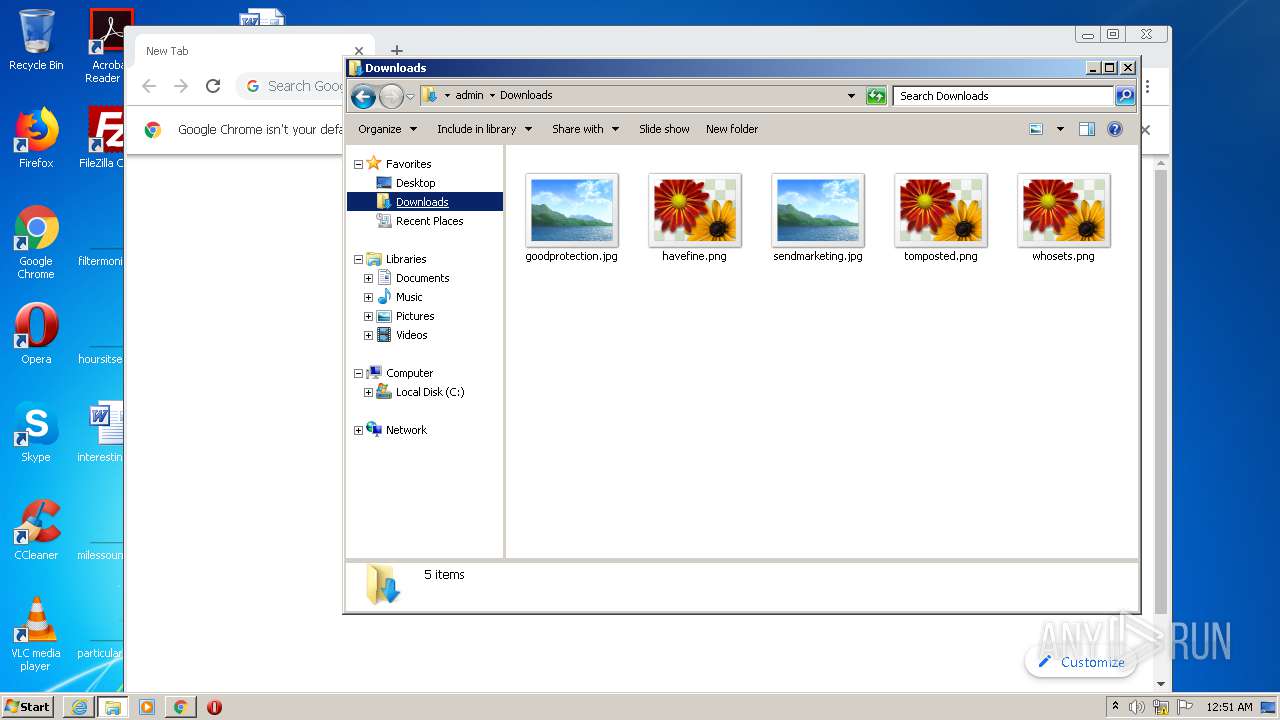
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1956 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\2MOQ2MKzpvc3D[1].exe | — | |
MD5:— | SHA256:— | |||
| 2080 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF4F44987333238363.TMP | — | |
MD5:— | SHA256:— | |||
| 2080 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\2MOQ2MKzpvc3D.exe.r73sbw3.partial:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 2080 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabBBD6.tmp | — | |
MD5:— | SHA256:— | |||
| 2080 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarBBD7.tmp | — | |
MD5:— | SHA256:— | |||
| 2080 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\verBBF7.tmp | — | |
MD5:— | SHA256:— | |||
| 2536 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F8E2641-9E8.pma | — | |
MD5:— | SHA256:— | |||
| 1956 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\2MOQ2MKzpvc3D.exe.r73sbw3.partial | executable | |
MD5:— | SHA256:— | |||
| 2080 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{B6D62E01-1265-11EB-B41E-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 1956 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\BDPCH2I3.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
37
DNS requests
24
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3320 | chrome.exe | GET | — | 212.34.158.133:80 | http://newtabletmall.com/ | ES | — | — | malicious |
3320 | chrome.exe | GET | — | 212.34.158.133:80 | http://newtabletmall.com/ | ES | — | — | malicious |
1876 | AzSqlExt.exe | POST | 200 | 104.131.144.215:8080 | http://104.131.144.215:8080/QGl7e4MUqCe/LJWTt38FXUofEw8GpZ/ | US | binary | 132 b | malicious |
2080 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
1956 | iexplore.exe | GET | 200 | 35.189.10.17:80 | http://stylefix.co/guillotine-cross/CTRNOQ/ | US | executable | 505 Kb | malicious |
2080 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
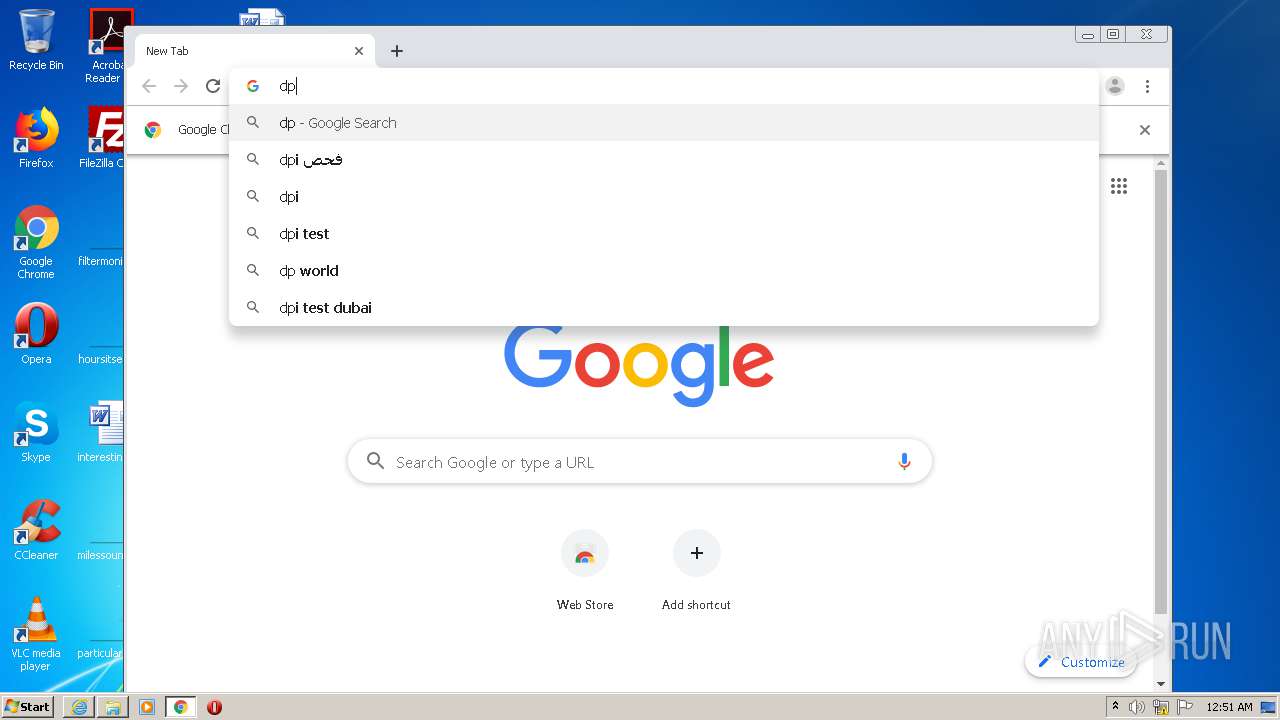
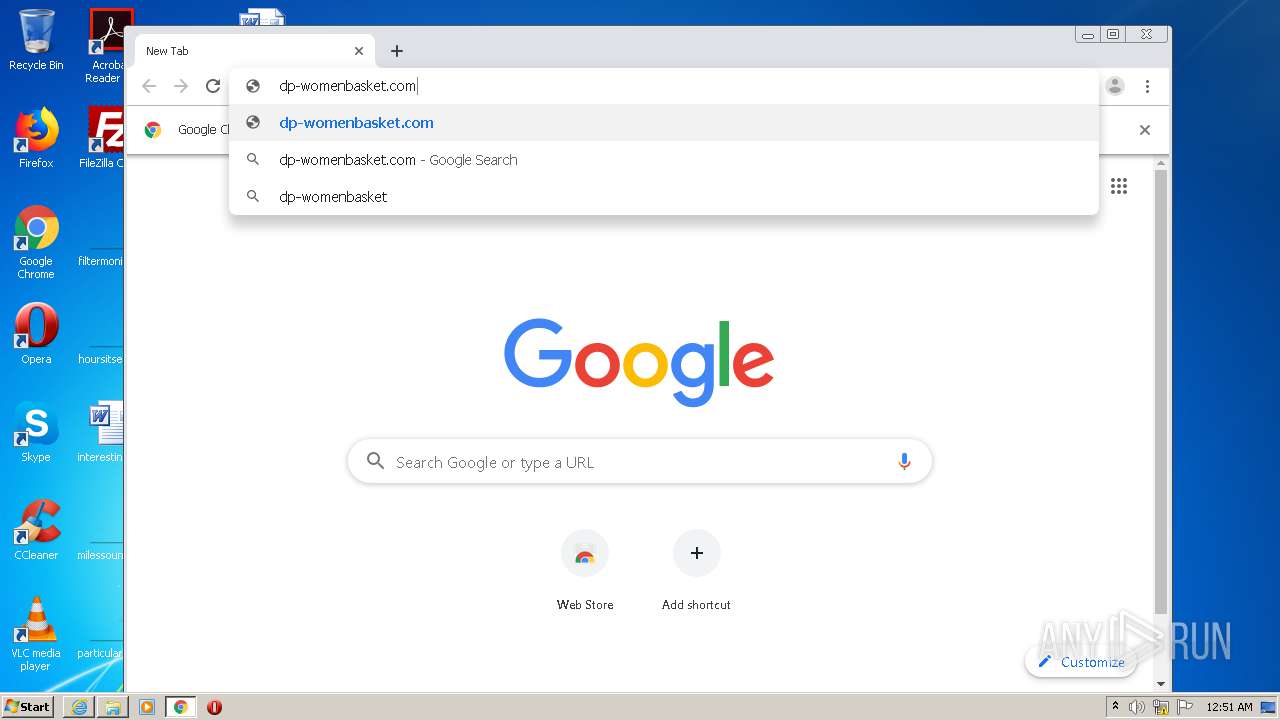
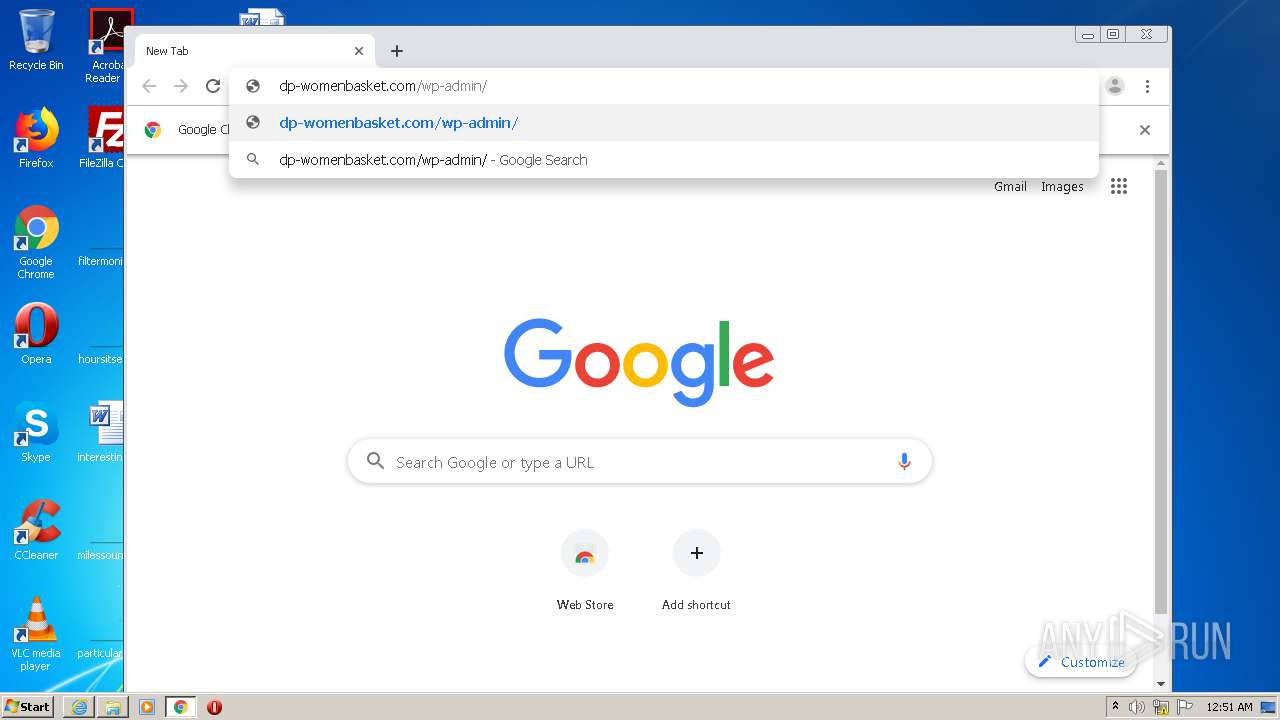
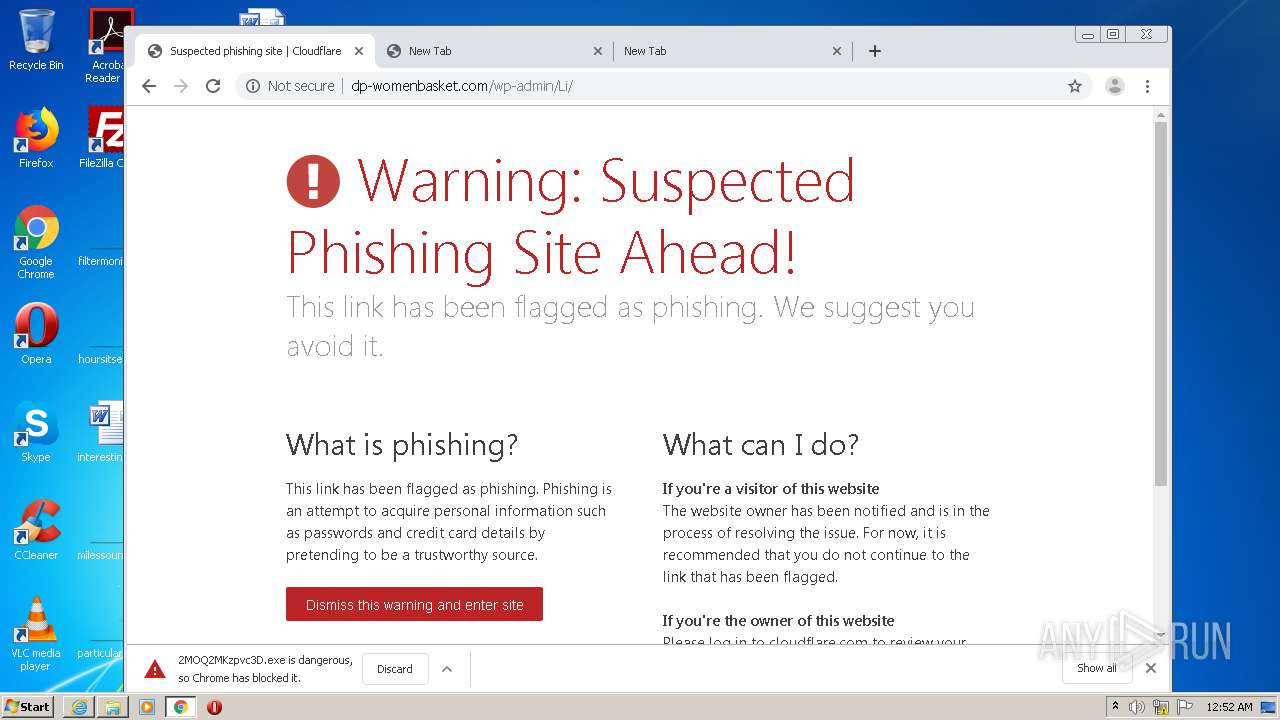
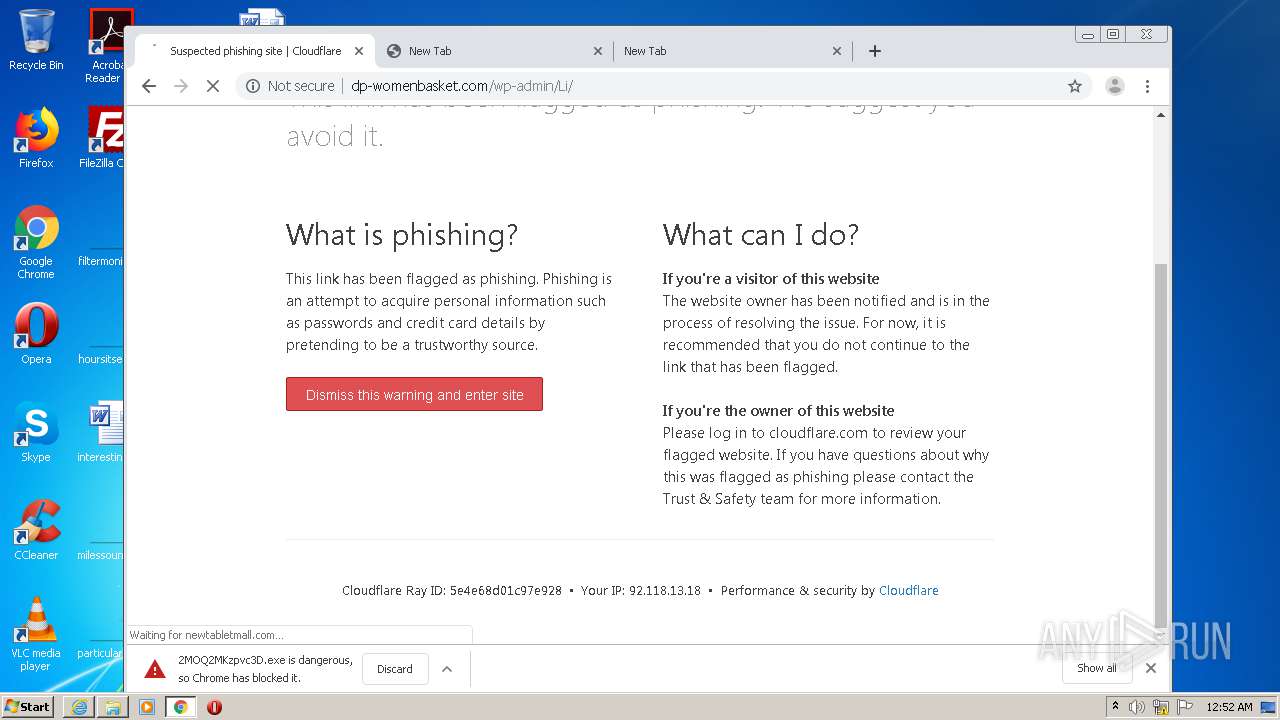
3320 | chrome.exe | GET | 200 | 104.28.13.193:80 | http://dp-womenbasket.com/wp-admin/Li/ | US | html | 1.68 Kb | suspicious |
3320 | chrome.exe | GET | 200 | 104.28.13.193:80 | http://dp-womenbasket.com/cdn-cgi/styles/cf.errors.css | US | text | 4.32 Kb | suspicious |
3320 | chrome.exe | GET | 200 | 35.189.10.17:80 | http://stylefix.co/guillotine-cross/CTRNOQ/ | US | executable | 505 Kb | malicious |
3320 | chrome.exe | GET | 301 | 104.28.13.193:80 | http://dp-womenbasket.com/wp-admin/Li | US | html | 1.23 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1956 | iexplore.exe | 35.189.10.17:80 | stylefix.co | Google Inc. | US | suspicious |
1876 | AzSqlExt.exe | 177.130.51.198:80 | — | Wsp Serviços de Telecomunicações Ltda | BR | malicious |
2080 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2080 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1876 | AzSqlExt.exe | 91.121.87.90:8080 | — | OVH SAS | FR | malicious |
1876 | AzSqlExt.exe | 104.131.144.215:8080 | — | Digital Ocean, Inc. | US | malicious |
3320 | chrome.exe | 172.217.18.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3320 | chrome.exe | 172.217.21.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
3320 | chrome.exe | 172.217.22.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3320 | chrome.exe | 172.217.18.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
stylefix.co |
| malicious |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1956 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1956 | iexplore.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
1876 | AzSqlExt.exe | A Network Trojan was detected | MALWARE [PTsecurity] Emotet |
1876 | AzSqlExt.exe | A Network Trojan was detected | MALWARE [PTsecurity] Emotet |
1876 | AzSqlExt.exe | A Network Trojan was detected | MALWARE [PTsecurity] Emotet |
3320 | chrome.exe | A Network Trojan was detected | AV POLICY CloudFlare Anti-Phishing Protection Warning in HTML Inbound |
3320 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3320 | chrome.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3 ETPRO signatures available at the full report