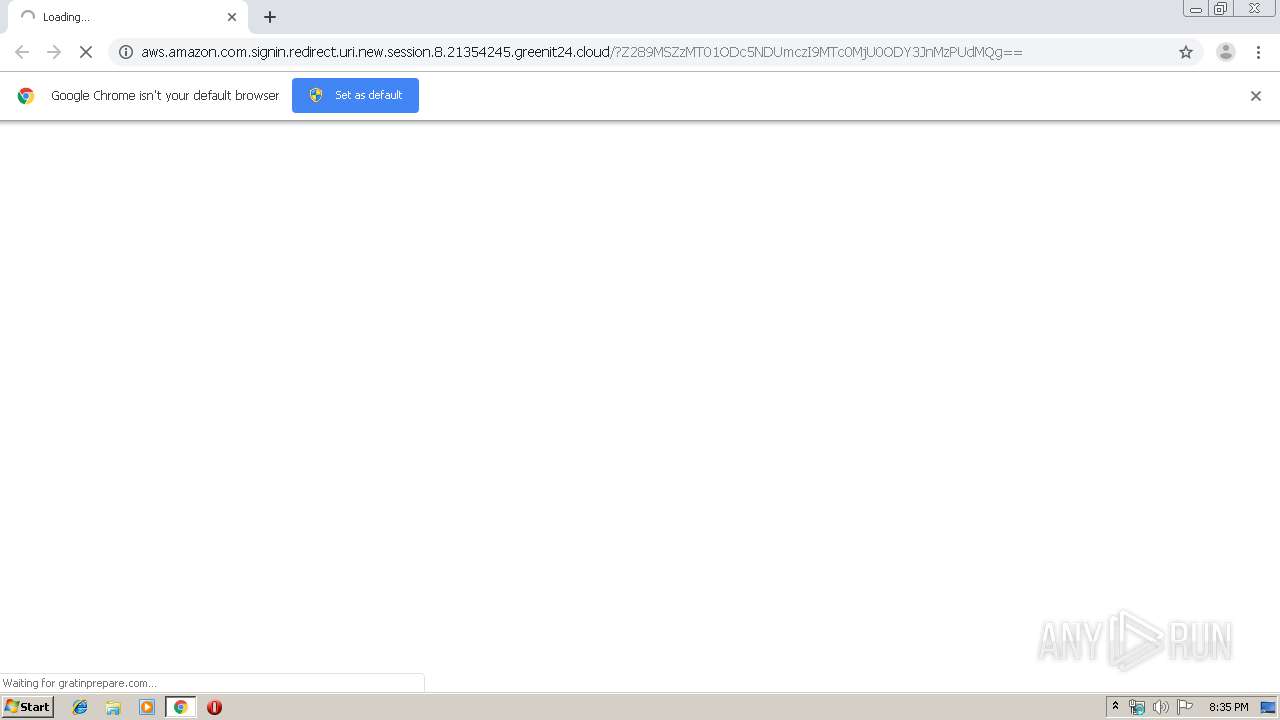
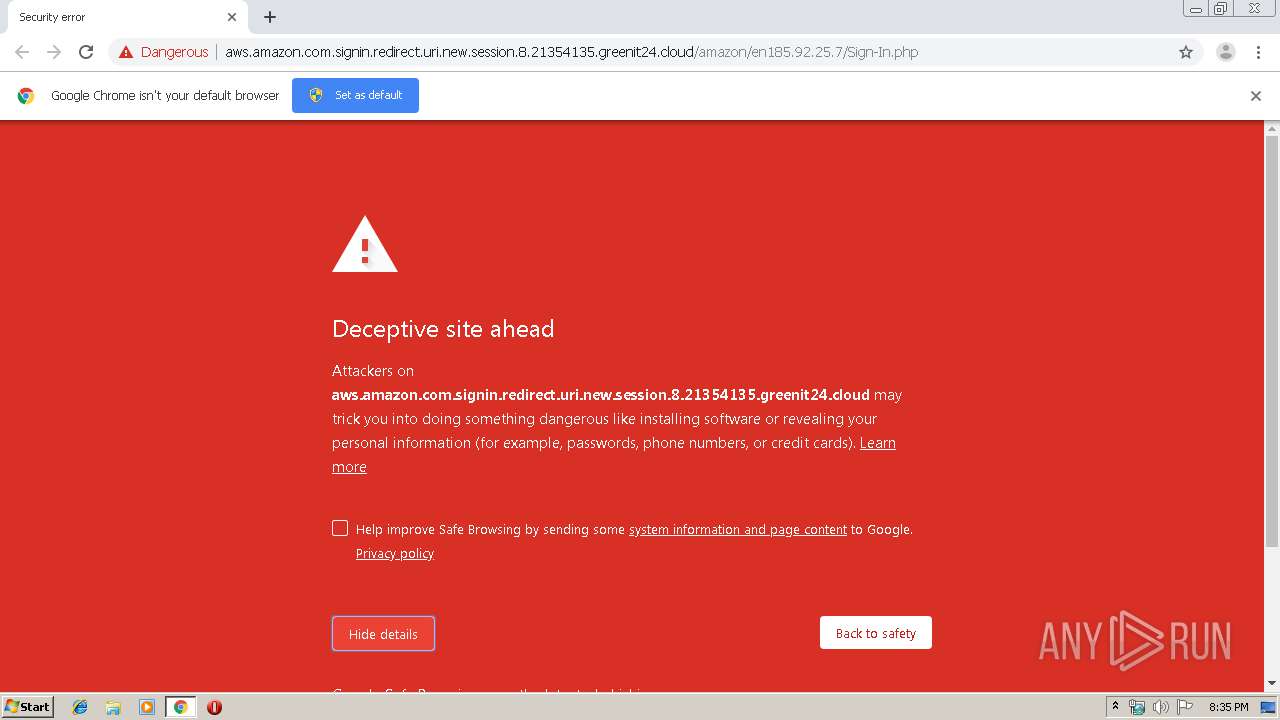
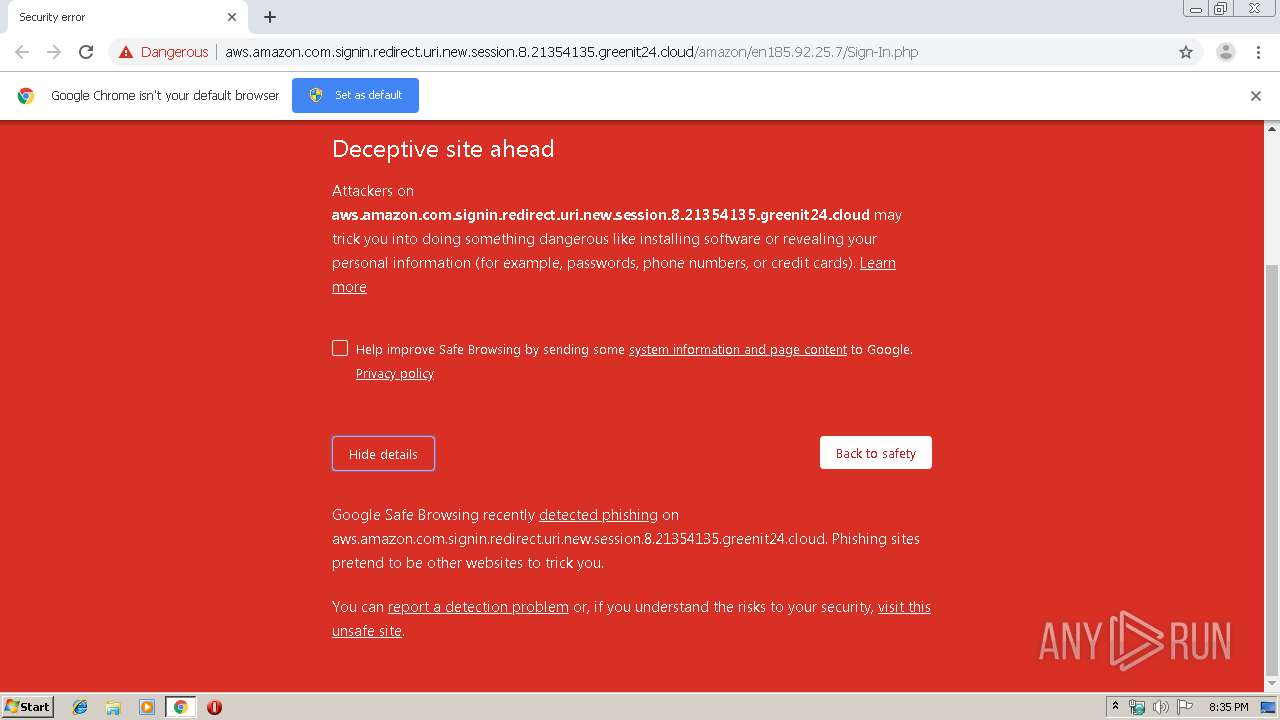
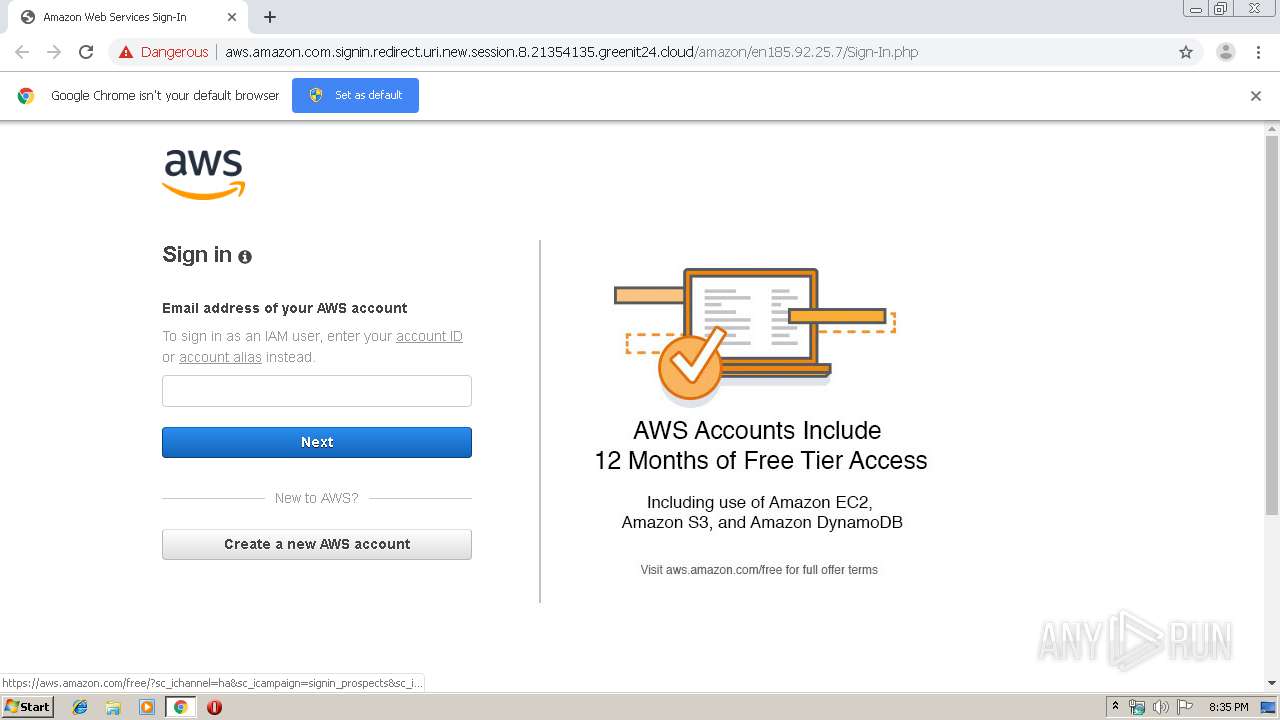
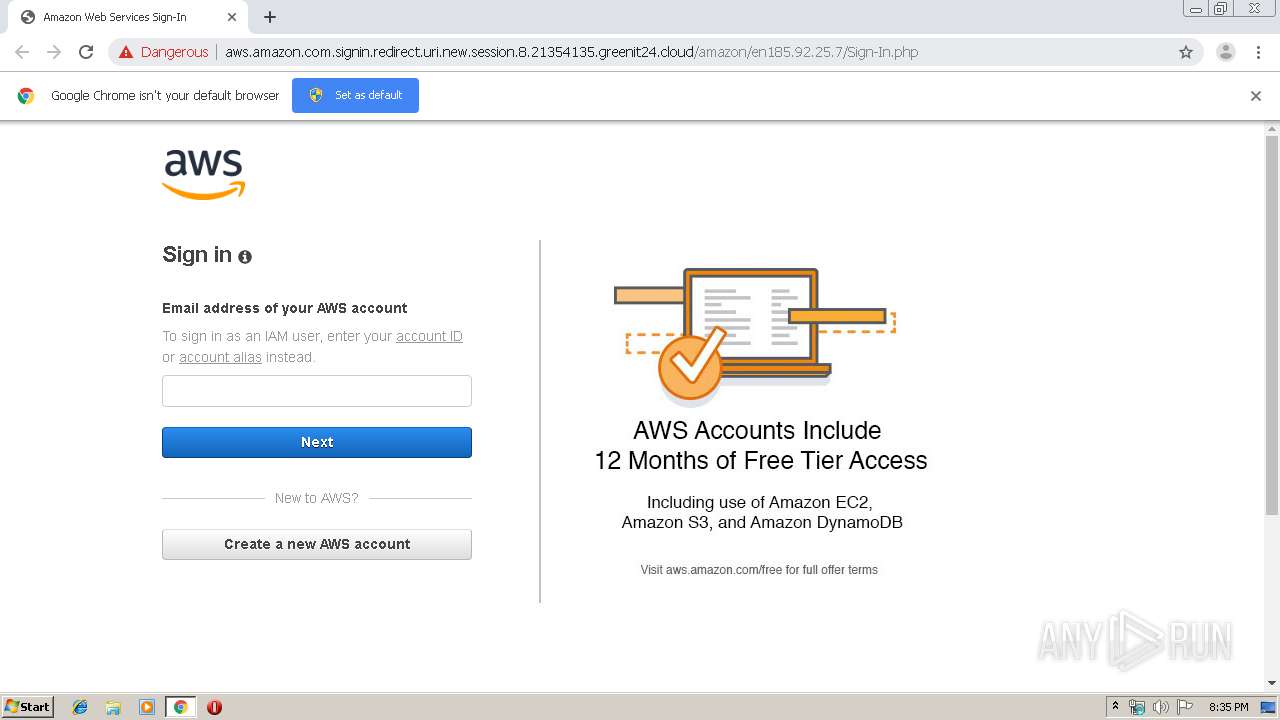
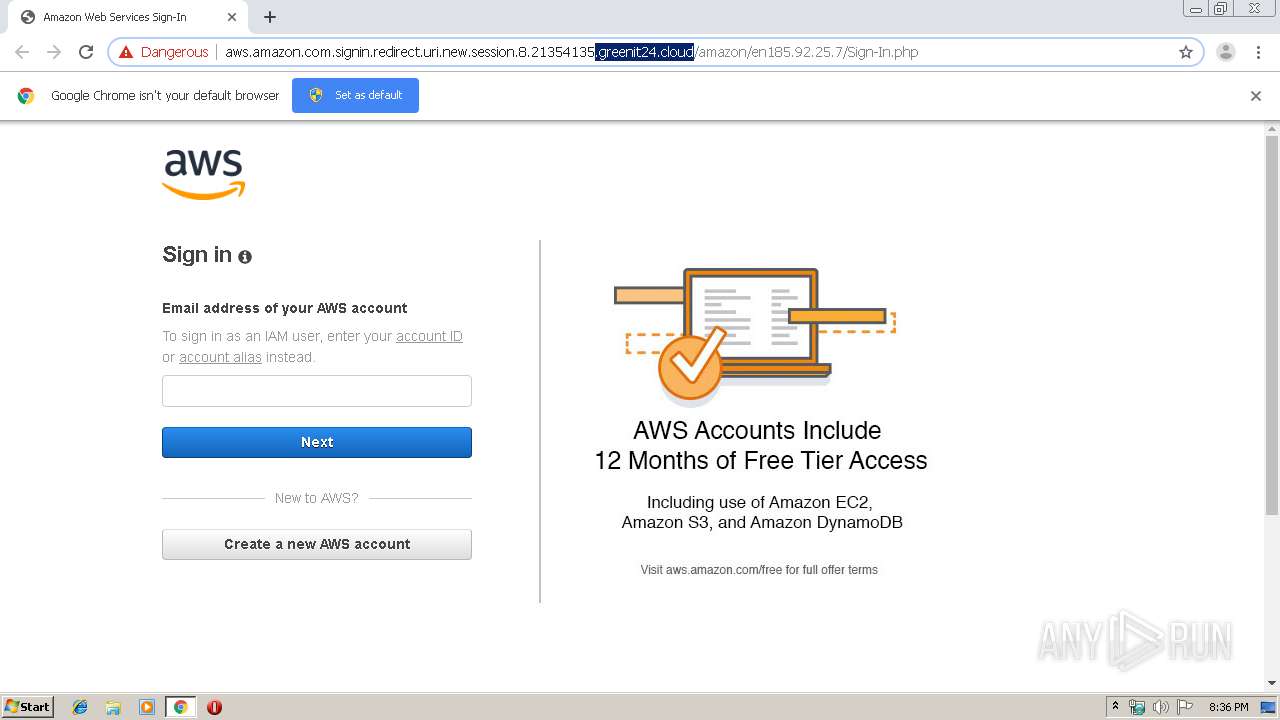
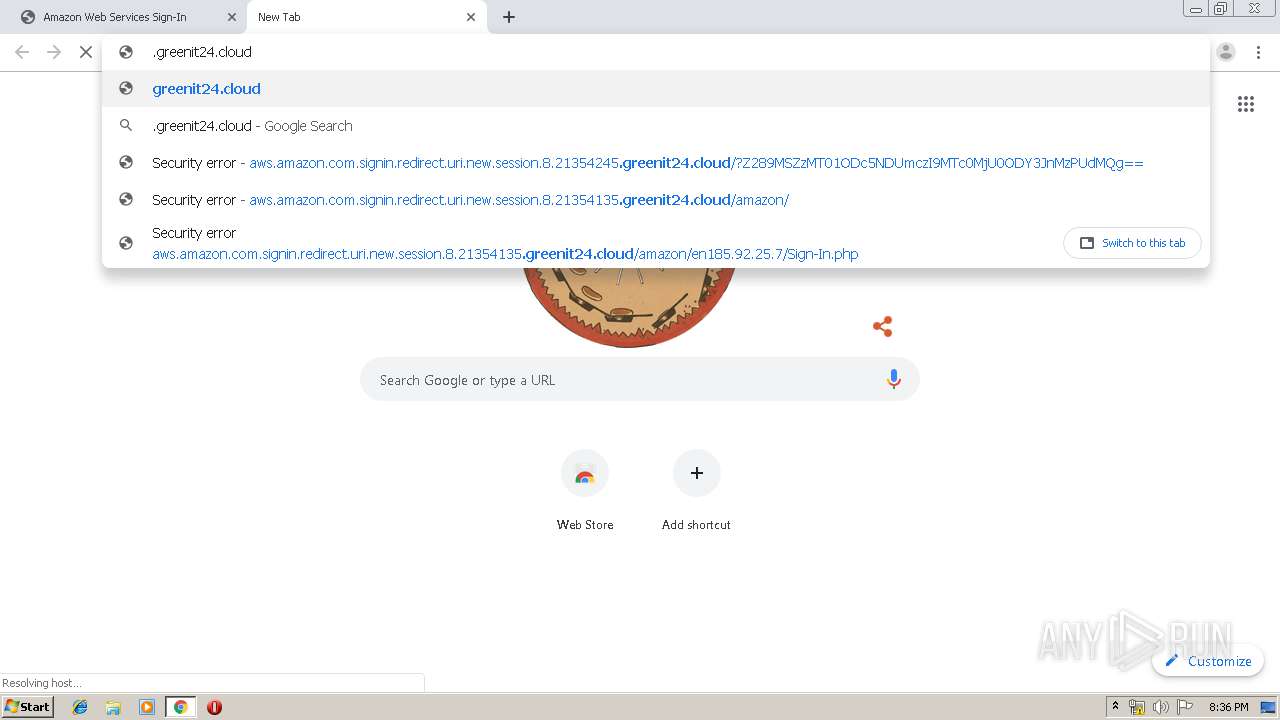
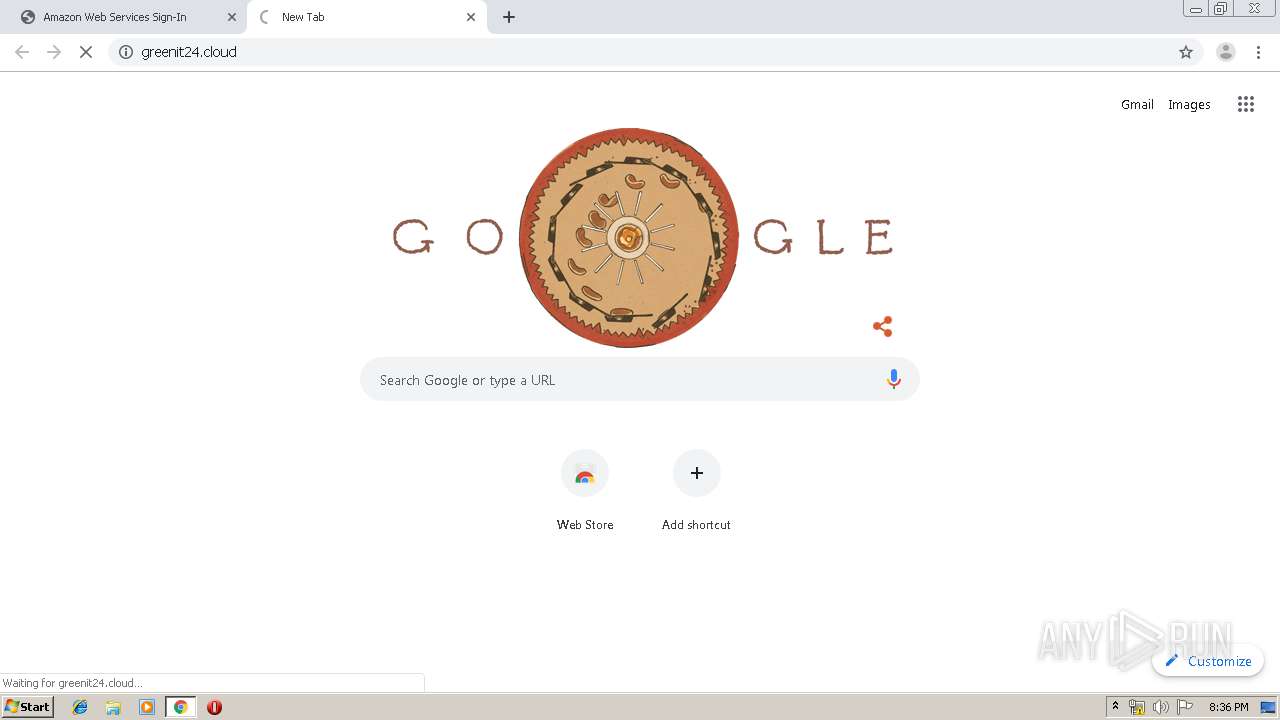
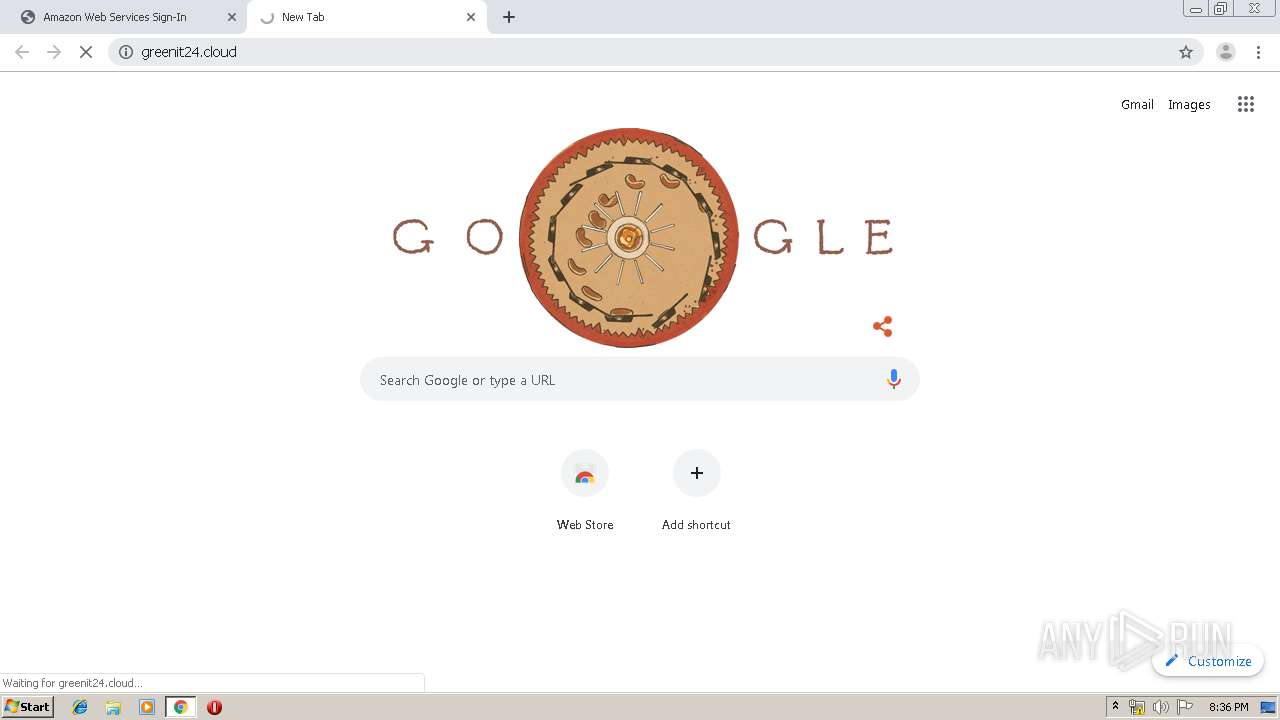
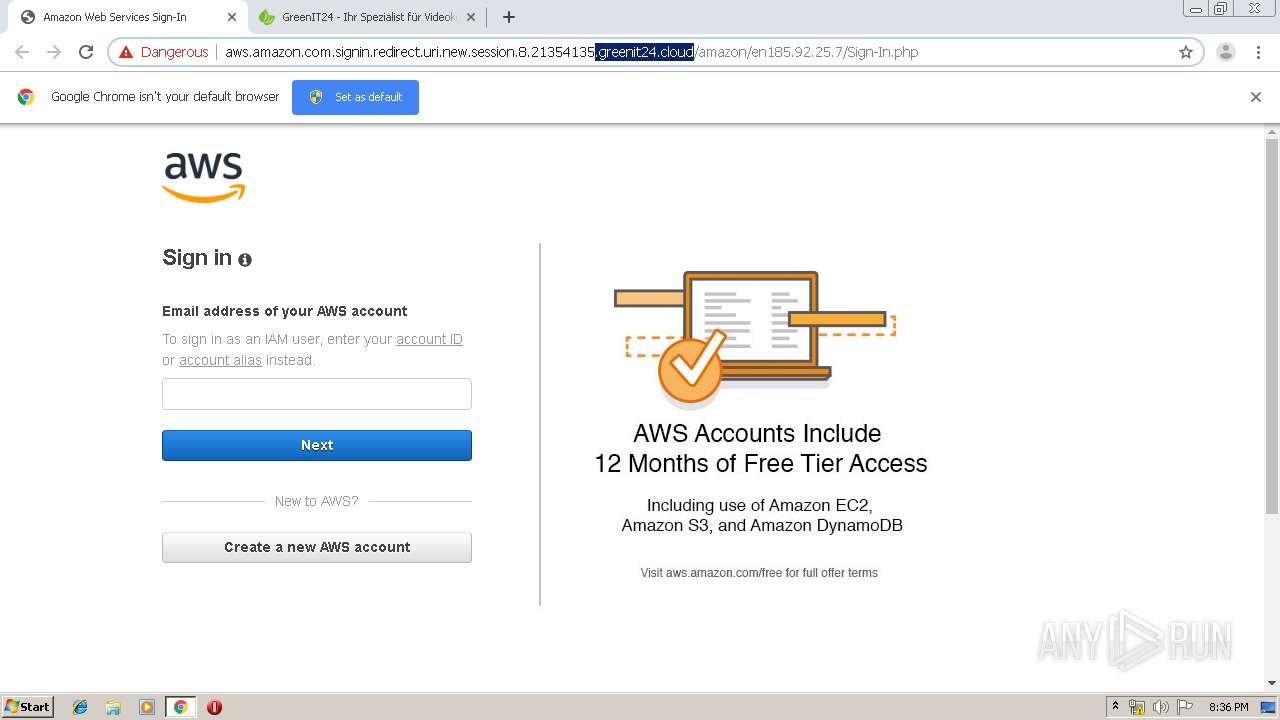
| URL: | http://aws.amazon.com.signin.redirect.uri.new.session.8.21354245.greenit24.cloud/?Z289MSZzMT01ODc5NDUmczI9MTc0MjU0ODY3JnMzPUdMQg== |
| Full analysis: | https://app.any.run/tasks/c7782dd2-82e4-46ac-a77e-df55f97b78e2 |
| Verdict: | Malicious activity |
| Analysis date: | October 14, 2019, 19:34:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 0D7B638378E20A396E375416AAECC961 |
| SHA1: | DF3BB4C8CDCB37FA42878ECBF54DBD1BCAD93E80 |
| SHA256: | B618CAEEE3200E5B219F23B7C33803FA13D229D50B22E4DF7C98B14B1EEE490F |
| SSDEEP: | 3:N1KfiIEoLGKIa3BMeXMLLzRL1fLCQAL9/uXoTNH2TaPL2x1:Cq5oLGTa369mQu9/qoTJOaP6H |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1404)
INFO
Reads the hosts file
- chrome.exe (PID: 4092)
- chrome.exe (PID: 1404)
Application launched itself
- chrome.exe (PID: 1404)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
69
Monitored processes
34
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15424139841796353461 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2004 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3479794751398846865 --mojo-platform-channel-handle=4324 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1912 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=223366190871954886 --mojo-platform-channel-handle=4064 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17526709799811257652 --mojo-platform-channel-handle=2928 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1216 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1184132672236339649 --renderer-client-id=26 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2784 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://aws.amazon.com.signin.redirect.uri.new.session.8.21354245.greenit24.cloud/?Z289MSZzMT01ODc5NDUmczI9MTc0MjU0ODY3JnMzPUdMQg==" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3667807439682248142 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2956 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1596 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1972058238518039847 --mojo-platform-channel-handle=4448 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6368772488140183356 --mojo-platform-channel-handle=484 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
627
Read events
524
Write events
98
Delete events
5
Modification events
| (PID) Process: | (1404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (592) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1404-13215555312096375 |
Value: 259 | |||
| (PID) Process: | (1404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (1404) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
80
Text files
286
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\71cd244d-baf1-4763-aadb-1eb8fd205ce5.tmp | — | |
MD5:— | SHA256:— | |||
| 1404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RF39a95a.TMP | text | |
MD5:— | SHA256:— | |||
| 1404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
53
DNS requests
32
Threats
16
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4092 | chrome.exe | GET | 302 | 111.90.158.141:80 | http://gratinprepare.com/public/?:nav=click::tracker&deploy=587945&user=toms%40datacom.co.nz&email_id=174254867&url=aHR0cDovL2F3cy5hbWF6b24uY29tLnNpZ25pbi5yZWRpcmVjdC51cmkubmV3LnNlc3Npb24uOC4yMTM1NDEzNS5ncmVlbml0MjQuY2xvdWQvYW1hem9uLw== | MY | — | — | suspicious |
4092 | chrome.exe | GET | 302 | 111.90.158.141:80 | http://gratinprepare.com/public/?:nav=default::index&go=1&s1=587945&s2=174254867 | MY | — | — | suspicious |
4092 | chrome.exe | GET | 302 | 111.90.158.141:80 | http://aws.amazon.com.signin.redirect.uri.new.session.8.21354245.greenit24.cloud/?Z289MSZzMT01ODc5NDUmczI9MTc0MjU0ODY3JnMzPUdMQg== | MY | — | — | suspicious |
4092 | chrome.exe | GET | 302 | 111.90.158.141:80 | http://gratinprepare.com/?var=Om5hdj1jbGljazo6dHJhY2tlciZkZXBsb3k9NTg3OTQ1JnVzZXI9dG9tcyU0MGRhdGFjb20uY28ubnomZW1haWxfaWQ9MTc0MjU0ODY3JnVybD1hSFIwY0RvdkwyRjNjeTVoYldGNmIyNHVZMjl0TG5OcFoyNXBiaTV5WldScGNtVmpkQzUxY21rdWJtVjNMbk5sYzNOcGIyNHVPQzR5TVRNMU5ERXpOUzVuY21WbGJtbDBNalF1WTJ4dmRXUXZZVzFoZW05dUx3PT0= | MY | — | — | suspicious |
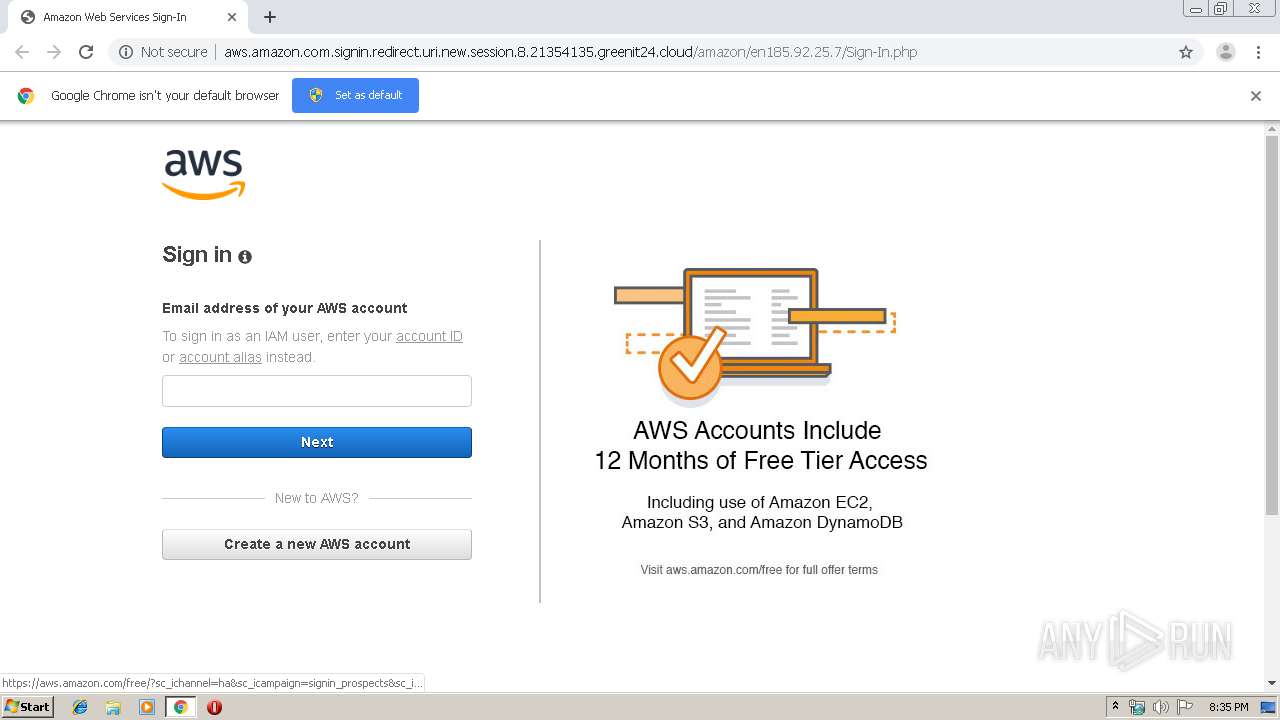
4092 | chrome.exe | GET | 200 | 111.90.158.141:80 | http://aws.amazon.com.signin.redirect.uri.new.session.8.21354135.greenit24.cloud/amazon/en185.92.25.7/Amazon%20Web%20Services%20Sign-In_files/fwcim.js | MY | text | 380 Kb | suspicious |
4092 | chrome.exe | GET | 200 | 111.90.158.141:80 | http://aws.amazon.com.signin.redirect.uri.new.session.8.21354135.greenit24.cloud/amazon/en185.92.25.7/Amazon%20Web%20Services%20Sign-In_files/Prospect_image.jpg | MY | image | 33.7 Kb | suspicious |
4092 | chrome.exe | POST | 404 | 111.90.158.141:80 | http://aws.amazon.com.signin.redirect.uri.new.session.8.21354135.greenit24.cloud/metrics/pageload | MY | html | 214 b | suspicious |
4092 | chrome.exe | GET | 302 | 172.217.18.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 512 b | whitelisted |
4092 | chrome.exe | GET | 302 | 172.217.18.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 507 b | whitelisted |
4092 | chrome.exe | GET | 200 | 173.194.183.168:80 | http://r3---sn-aigl6ney.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=185.92.25.7&mm=28&mn=sn-aigl6ney&ms=nvh&mt=1571081659&mv=m&mvi=2&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4092 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
4092 | chrome.exe | 111.90.158.141:80 | aws.amazon.com.signin.redirect.uri.new.session.8.21354245.greenit24.cloud | Shinjiru Technology Sdn Bhd | MY | suspicious |
4092 | chrome.exe | 172.217.18.164:443 | www.google.com | Google Inc. | US | whitelisted |
4092 | chrome.exe | 172.217.16.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
4092 | chrome.exe | 172.217.22.78:443 | clients1.google.com | Google Inc. | US | whitelisted |
4092 | chrome.exe | 172.217.18.174:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
4092 | chrome.exe | 173.194.183.168:80 | r3---sn-aigl6ney.gvt1.com | Google Inc. | US | whitelisted |
4092 | chrome.exe | 216.58.208.33:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
4092 | chrome.exe | 216.58.207.67:443 | www.google.co.uk | Google Inc. | US | whitelisted |
4092 | chrome.exe | 173.194.5.203:80 | r5---sn-aigl6n76.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
aws.amazon.com.signin.redirect.uri.new.session.8.21354245.greenit24.cloud |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
gratinprepare.com |
| suspicious |
aws.amazon.com.signin.redirect.uri.new.session.8.21354135.greenit24.cloud |
| suspicious |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
console.aws.amazon.com |
| suspicious |
aws.amazon.com |
| shared |
signin.aws.amazon.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
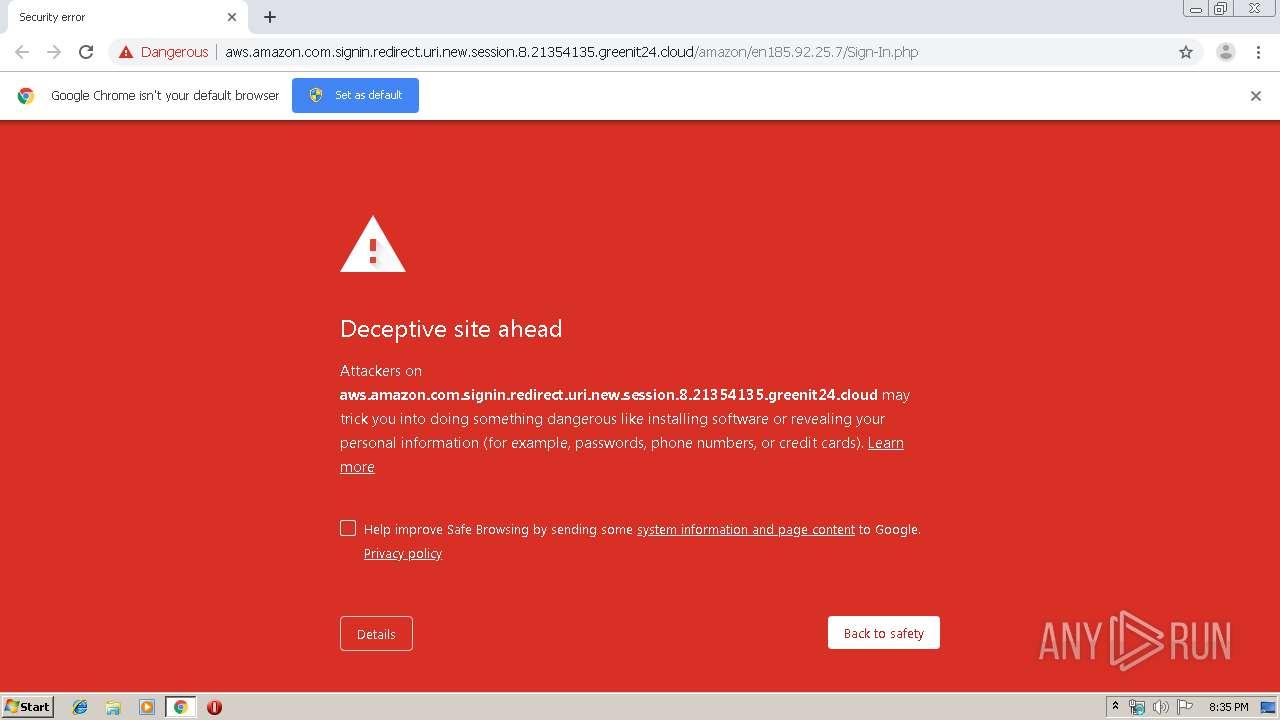
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
4092 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.cloud Domain |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
4092 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.cloud Domain |
4092 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.cloud Domain |
4092 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.cloud Domain |
4092 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.cloud Domain |
4092 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.cloud Domain |
4092 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.cloud Domain |
4092 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.cloud Domain |
2 ETPRO signatures available at the full report