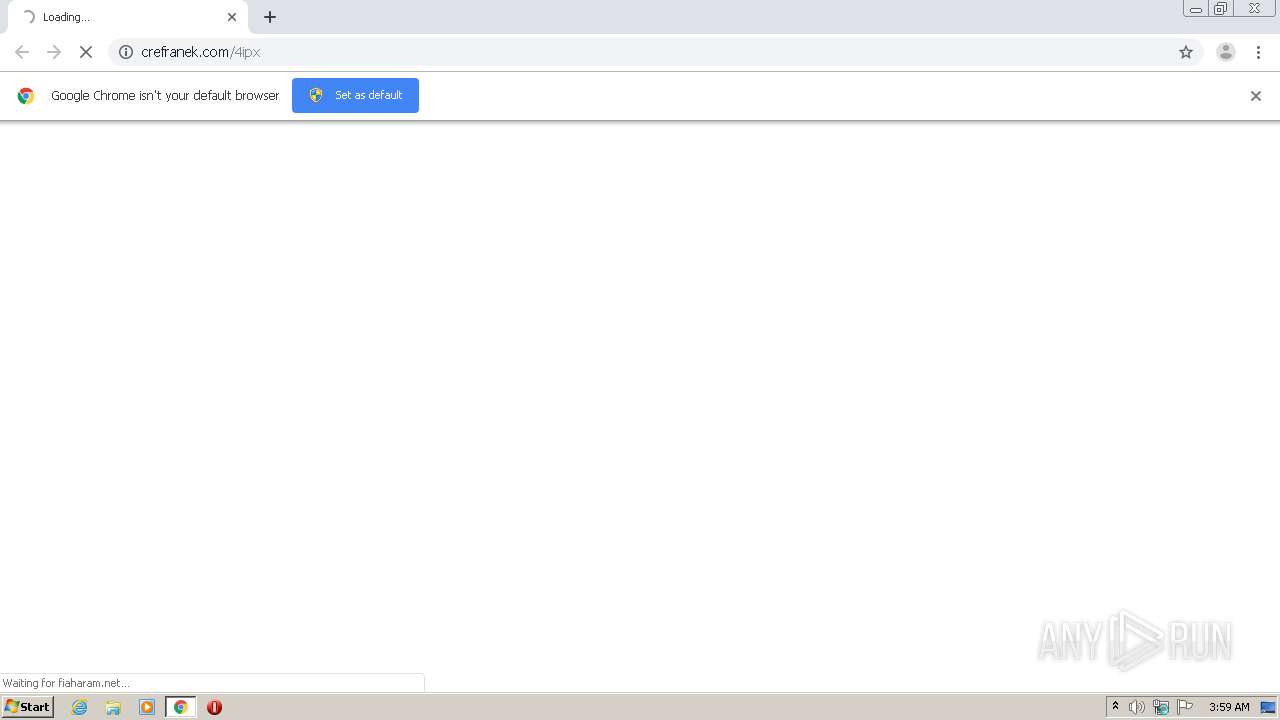
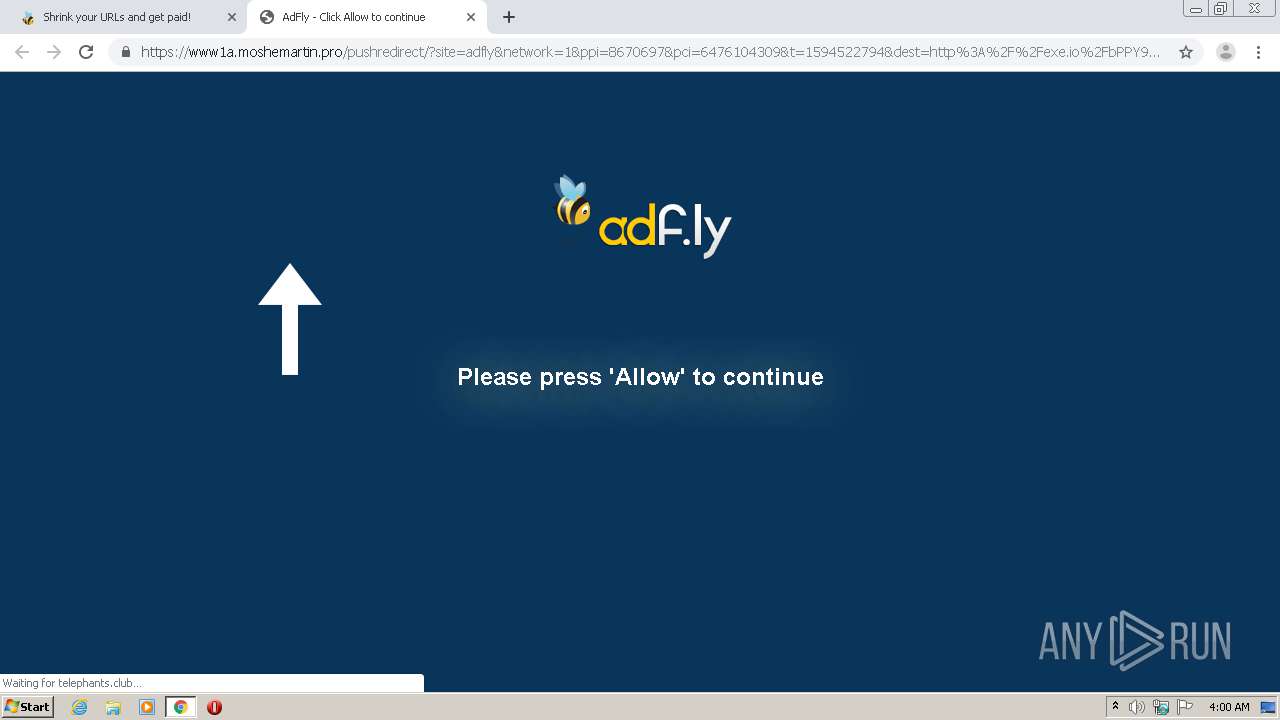
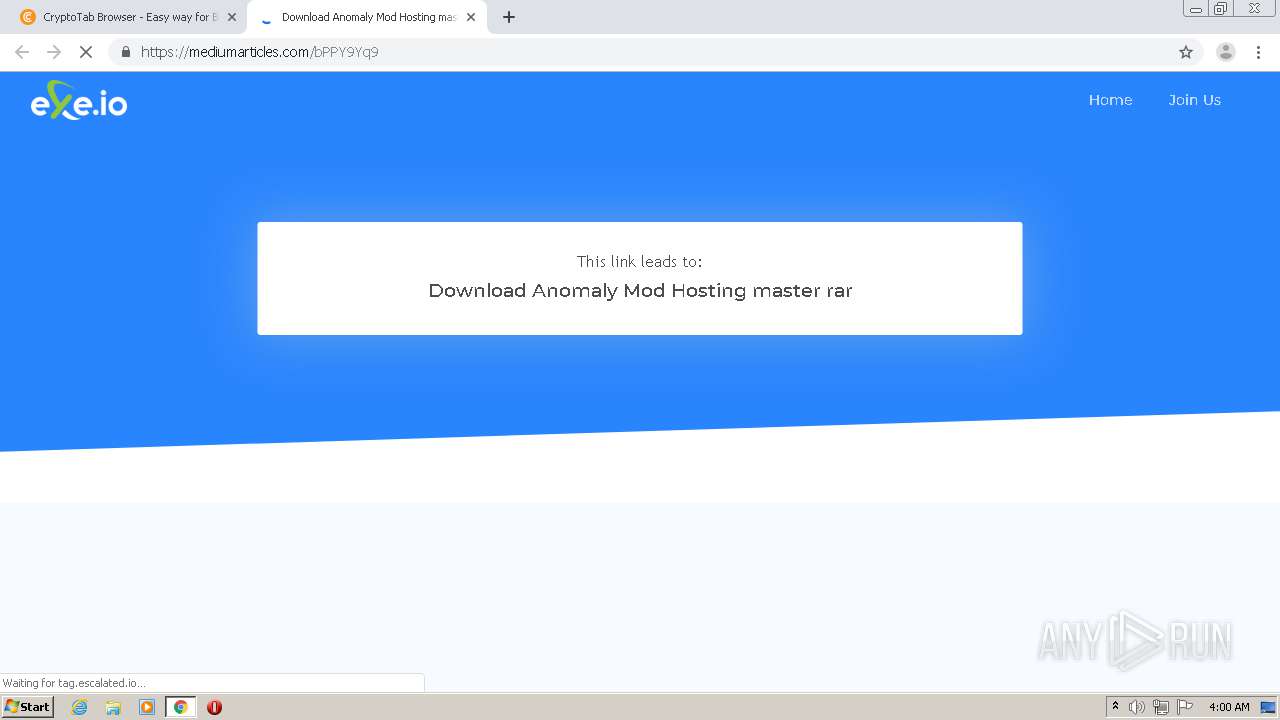
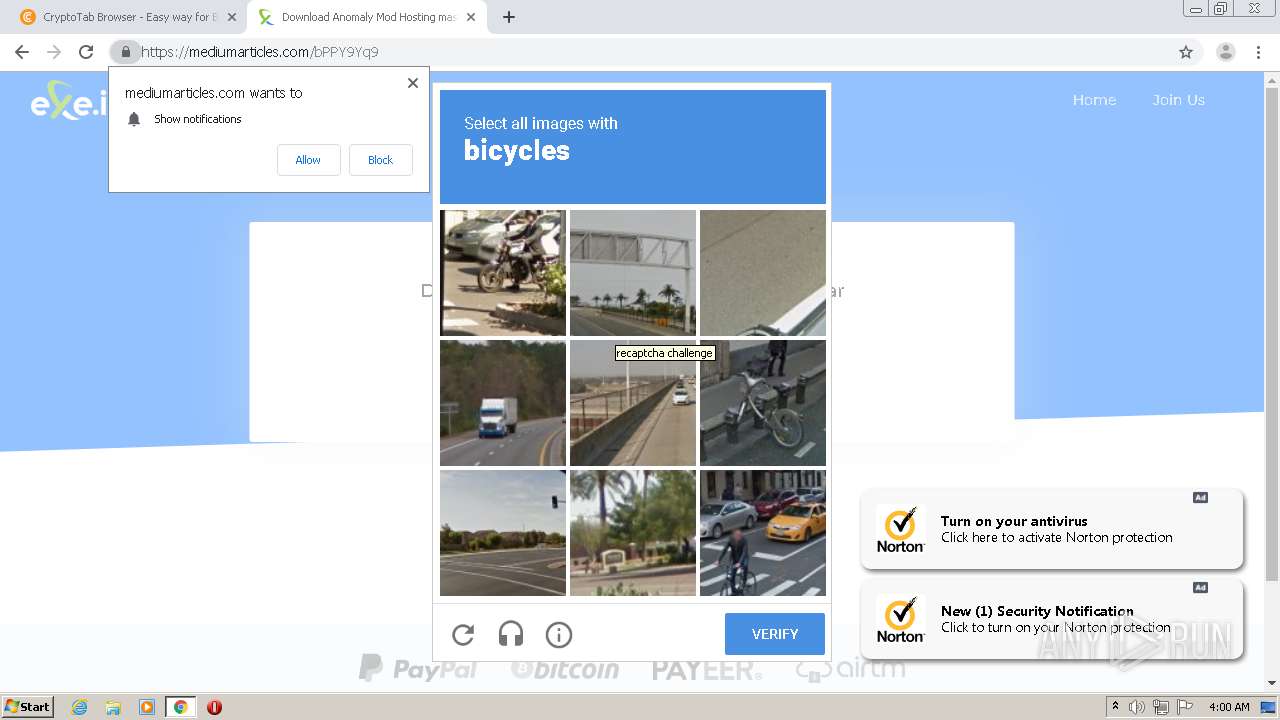
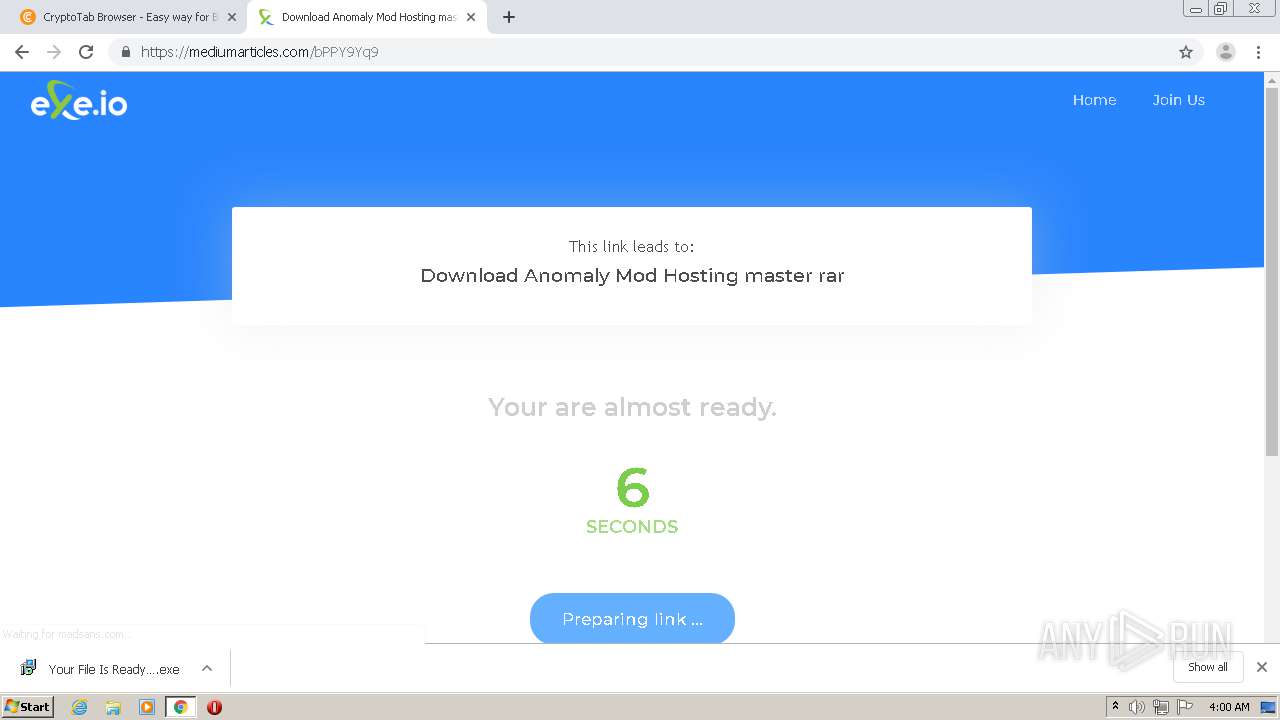
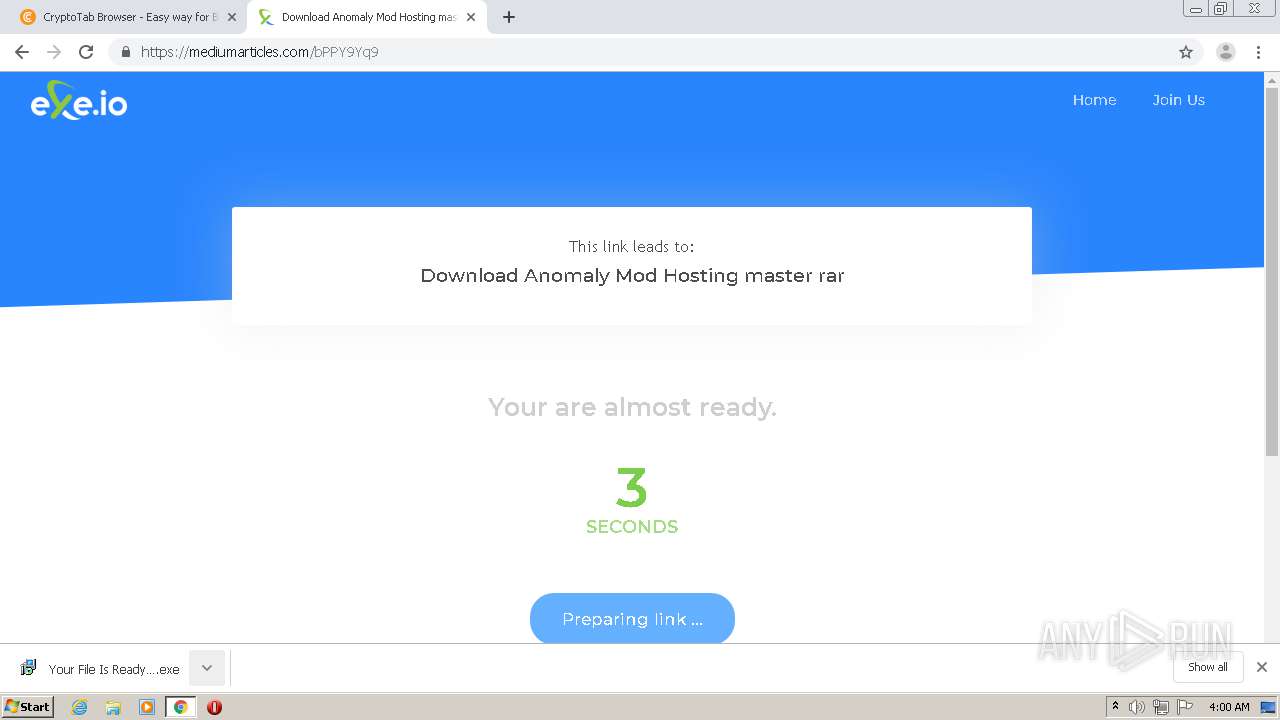
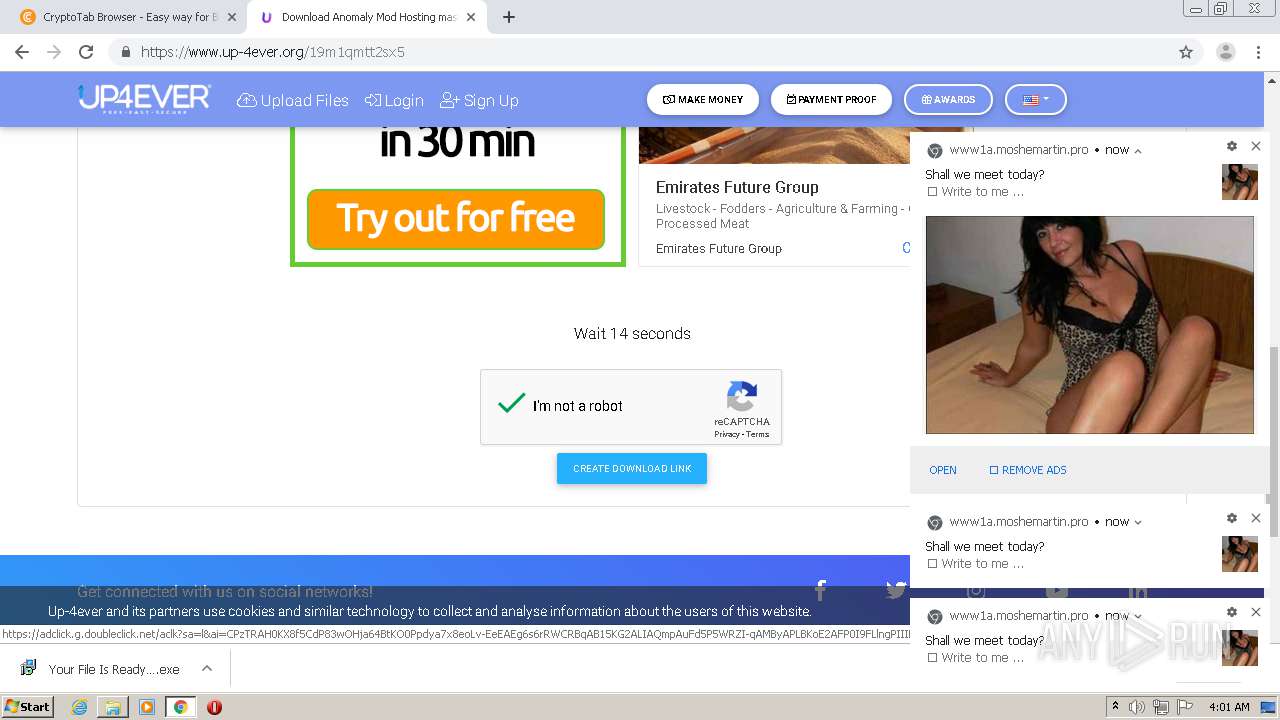
| URL: | http://crefranek.com/4ipx |
| Full analysis: | https://app.any.run/tasks/13f3e8f4-3567-4a26-86fe-cc046c606ee2 |
| Verdict: | Malicious activity |
| Analysis date: | July 12, 2020, 02:59:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | B993D97217E23E7075B5E4982085494C |
| SHA1: | 1B95CF3EFEB721F286102D662C21F34663B0C3AD |
| SHA256: | B5EB5FAA15AF3AA63C4BA5594122BBA8AEDABBBC057F0479F2C3BCF0E253DA72 |
| SSDEEP: | 3:N1KdXgicn:Caicn |
MALICIOUS
No malicious indicators.SUSPICIOUS
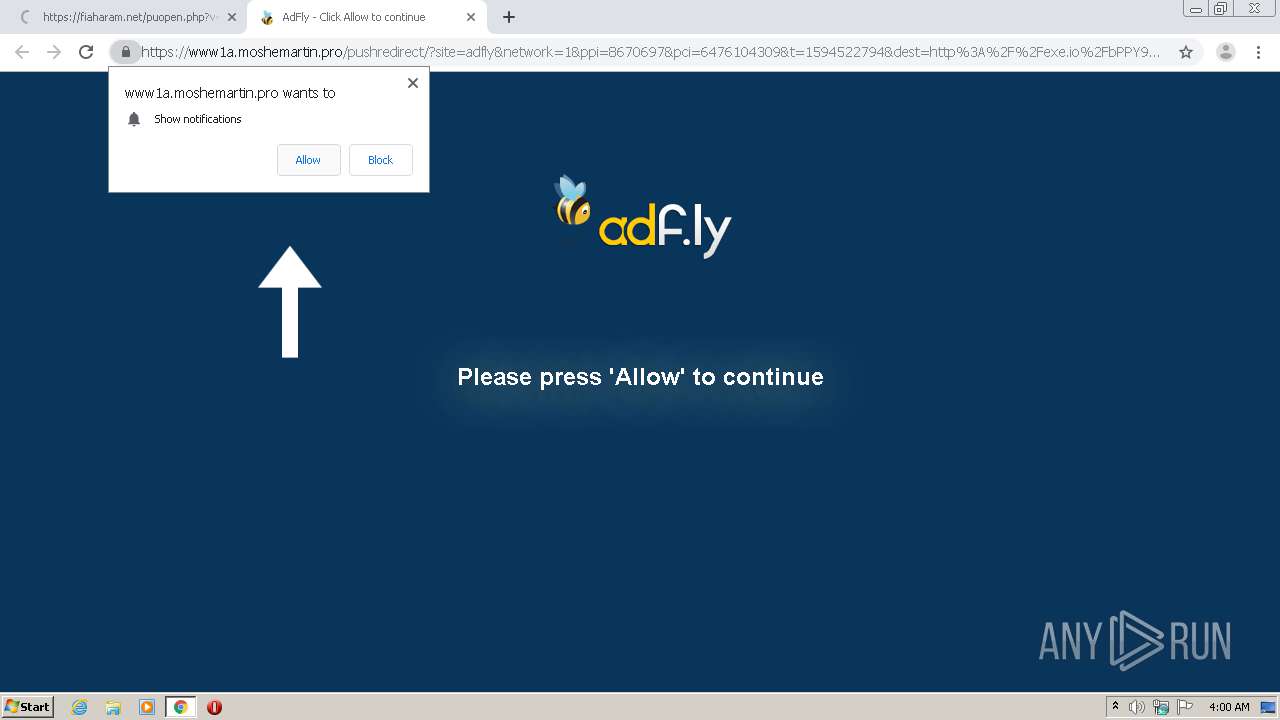
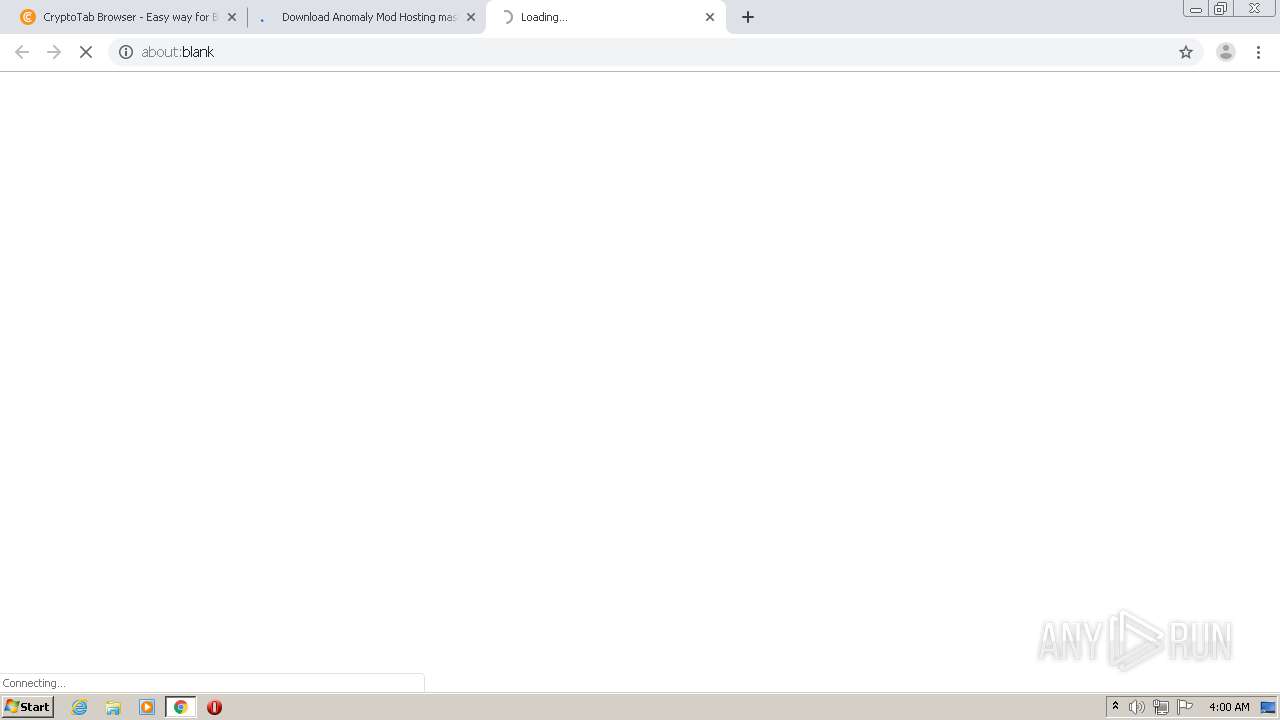
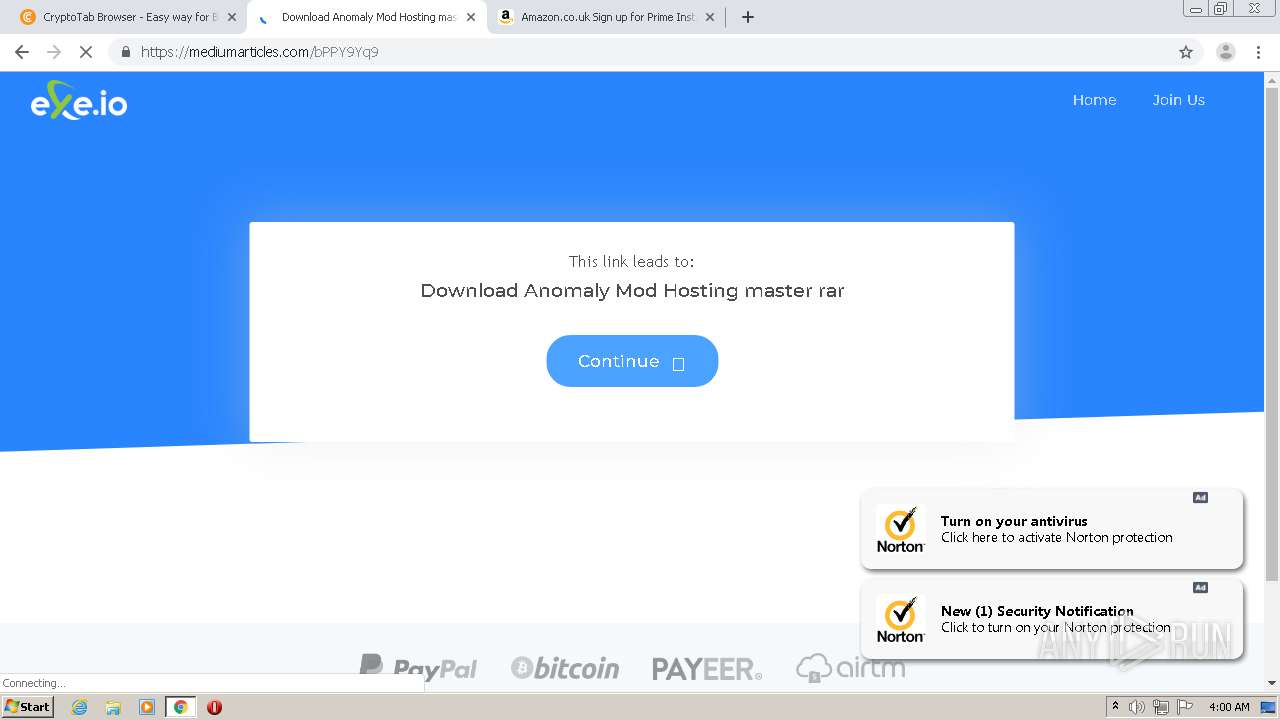
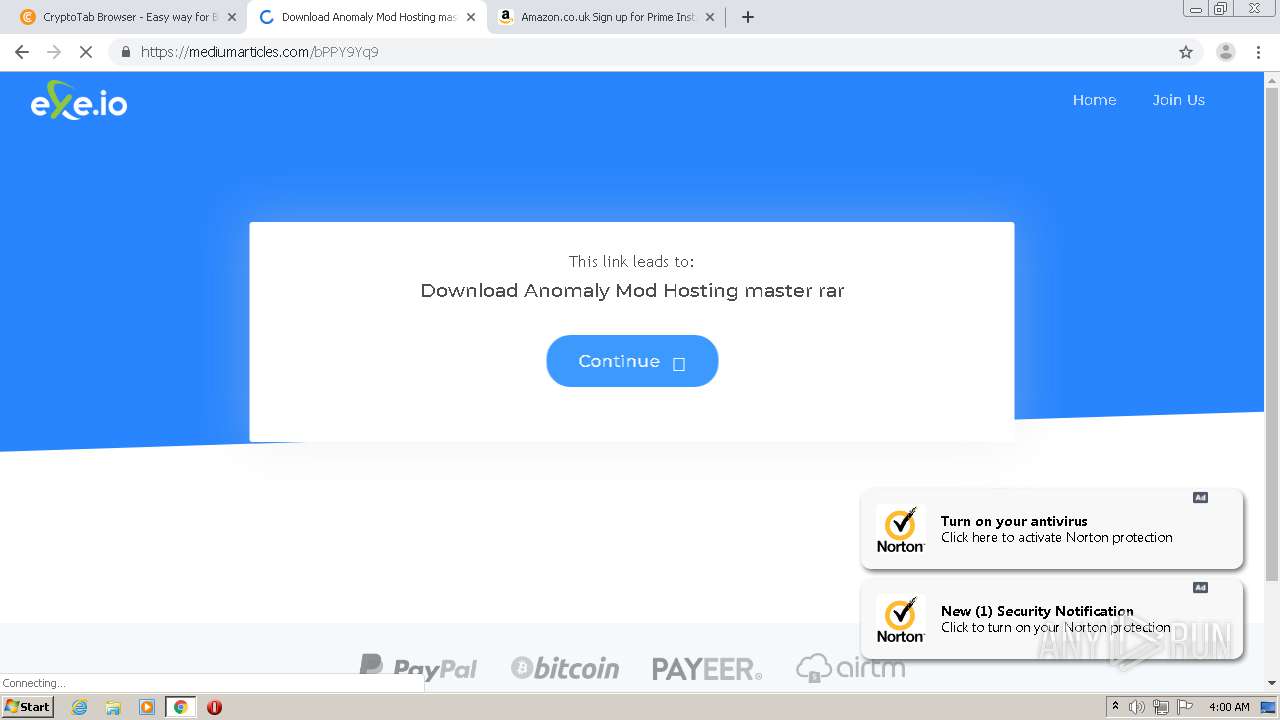
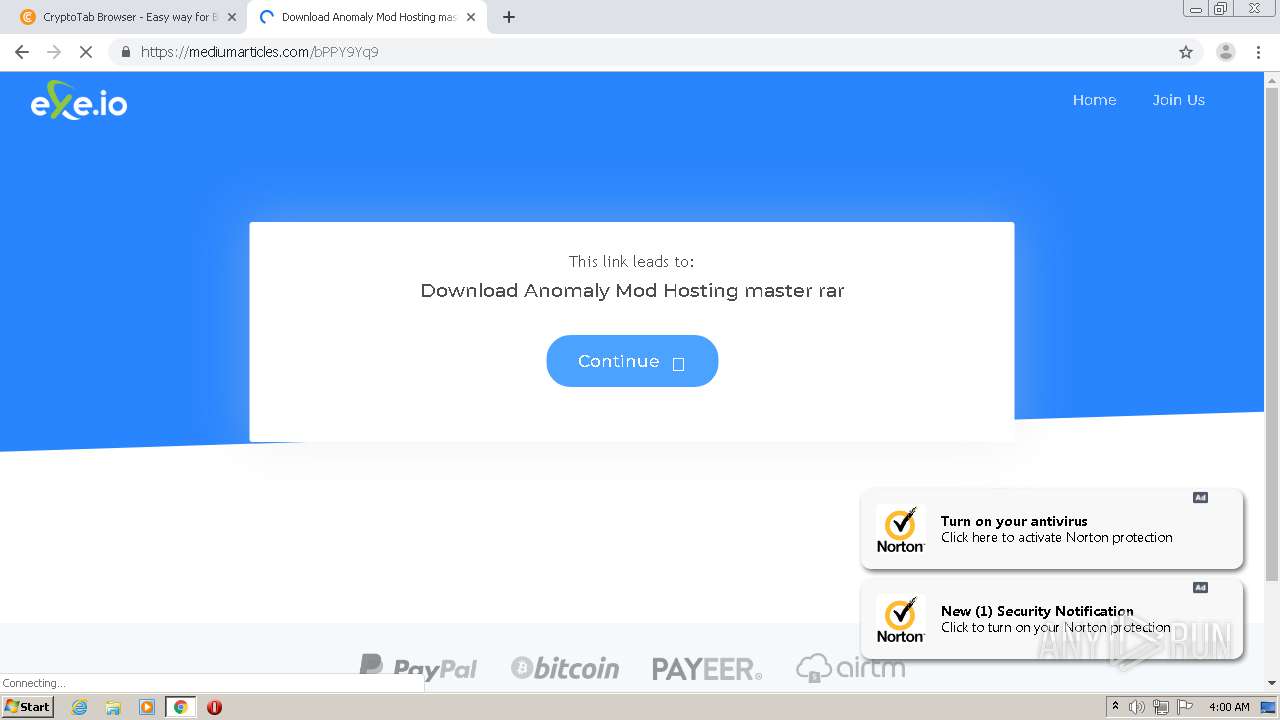
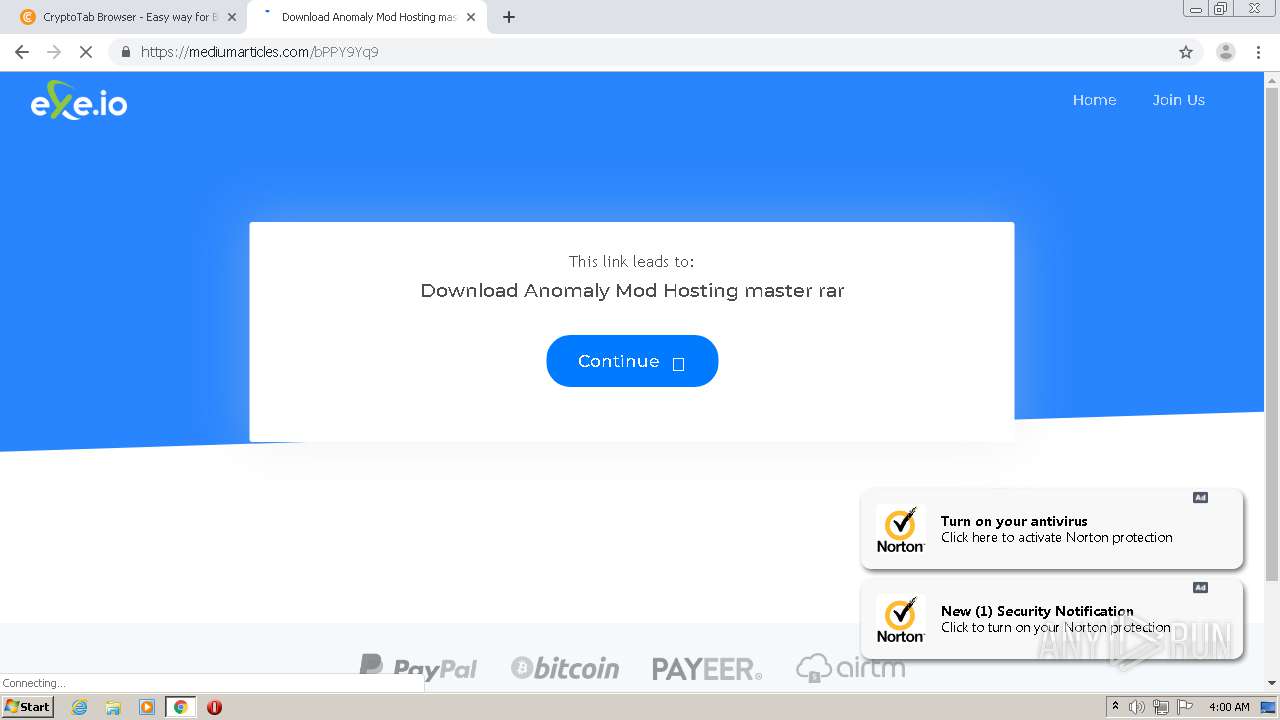
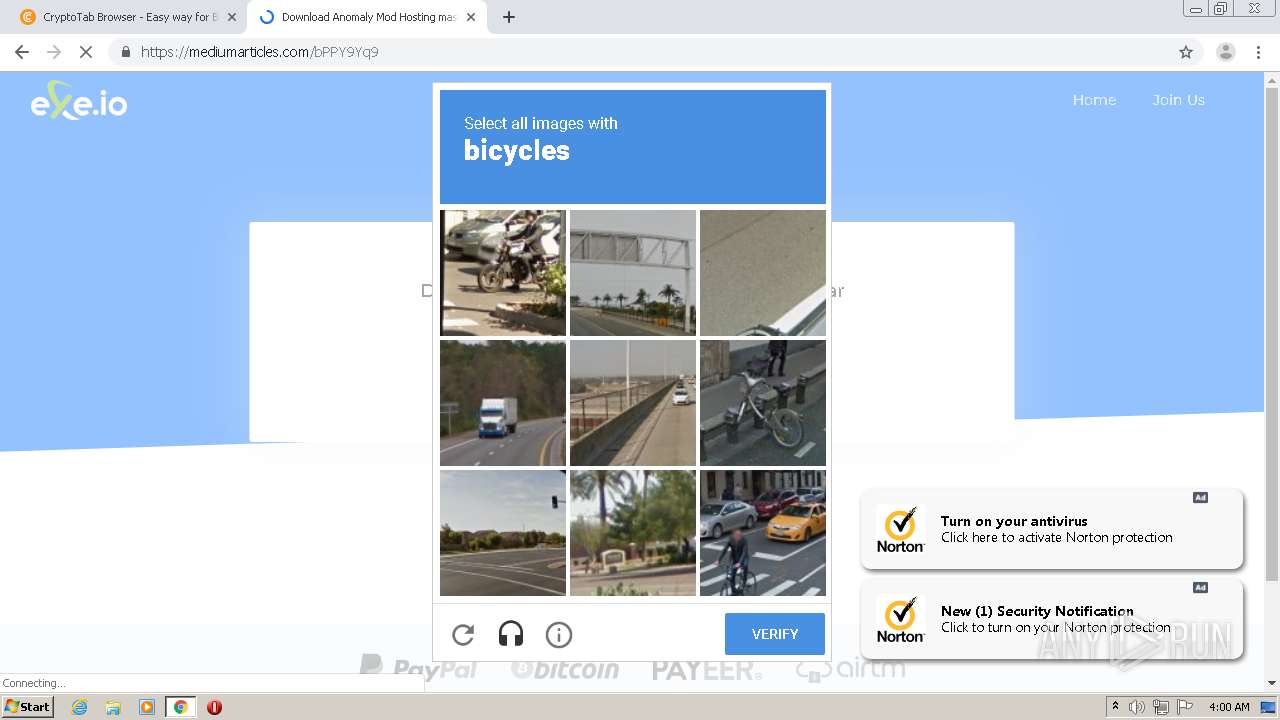
Modifies files in Chrome extension folder
- chrome.exe (PID: 1112)
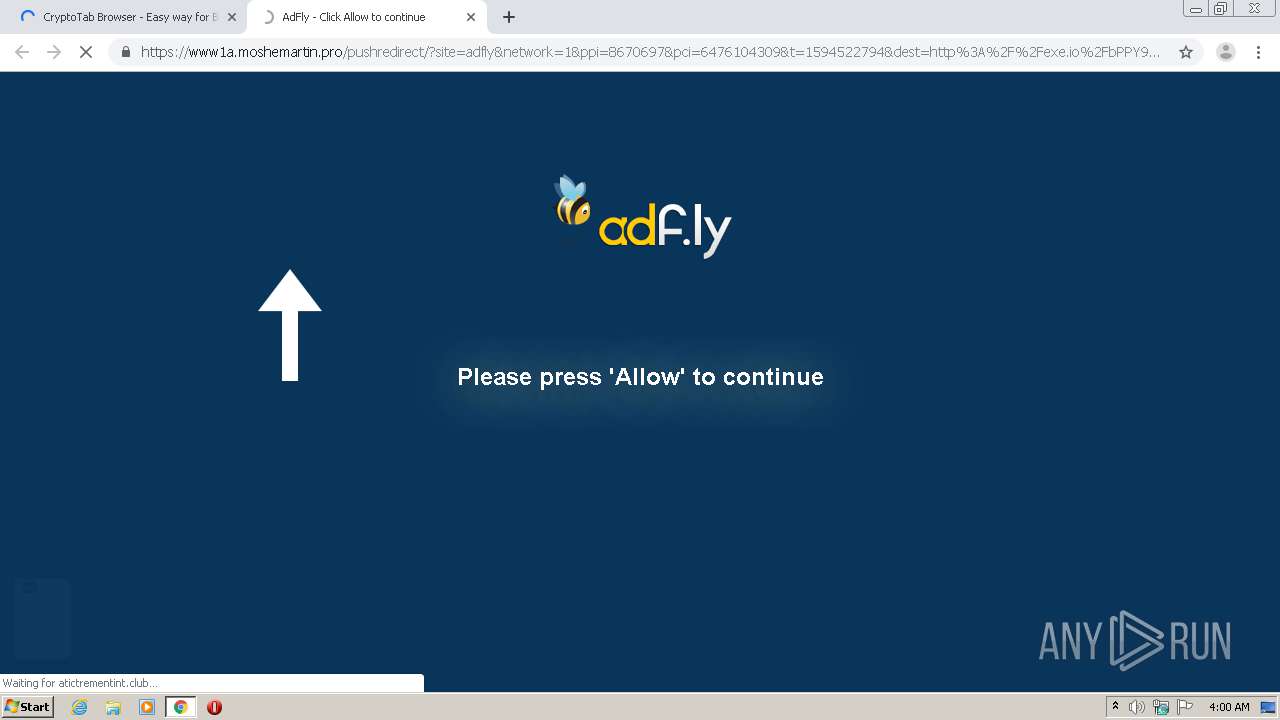
Executable content was dropped or overwritten
- chrome.exe (PID: 1112)
- chrome.exe (PID: 4072)
INFO
Reads the hosts file
- chrome.exe (PID: 1112)
- chrome.exe (PID: 4072)
Dropped object may contain TOR URL's
- chrome.exe (PID: 1112)
Reads settings of System Certificates
- chrome.exe (PID: 1112)
- chrome.exe (PID: 4072)
Reads Internet Cache Settings
- chrome.exe (PID: 1112)
Application launched itself
- chrome.exe (PID: 1112)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
88
Monitored processes
51
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,4650832698503505949,17881250459015128535,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12730877263530109931 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2904 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,4650832698503505949,17881250459015128535,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14242762174317209678 --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4788 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,4650832698503505949,17881250459015128535,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3499939839623687775 --renderer-client-id=36 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4376 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,4650832698503505949,17881250459015128535,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9157669174520871923 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3196 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6f41a9d0,0x6f41a9e0,0x6f41a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://crefranek.com/4ipx" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1196 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,4650832698503505949,17881250459015128535,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11351171786791960042 --mojo-platform-channel-handle=3136 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,4650832698503505949,17881250459015128535,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10746975900726639054 --renderer-client-id=35 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4428 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,4650832698503505949,17881250459015128535,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10346095735217373846 --renderer-client-id=41 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3504 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,4650832698503505949,17881250459015128535,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12991832547883459314 --mojo-platform-channel-handle=5184 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 034
Read events
907
Write events
122
Delete events
5
Modification events
| (PID) Process: | (1112) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1112) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1112) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1112) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1112) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1112-13238996391696250 |
Value: 259 | |||
| (PID) Process: | (1112) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1112) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1112) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (1112) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1112-13238996391696250 |
Value: 259 | |||
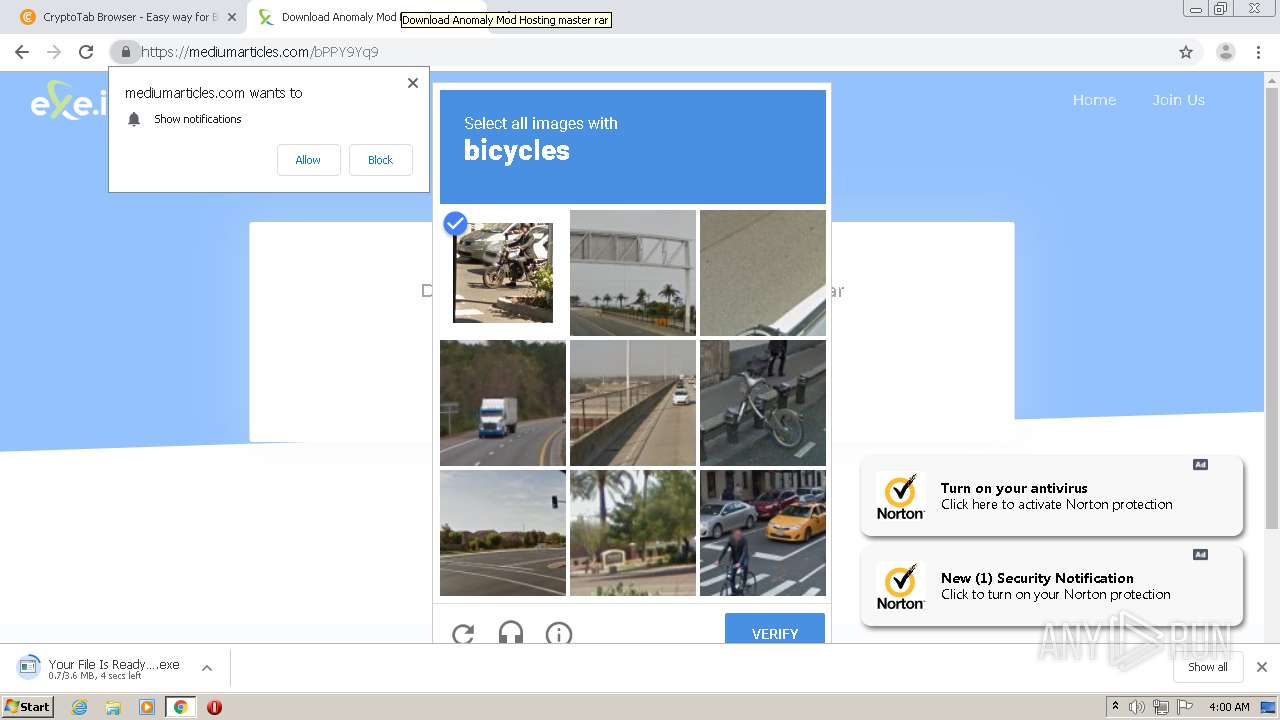
Executable files
4
Suspicious files
231
Text files
376
Unknown types
23
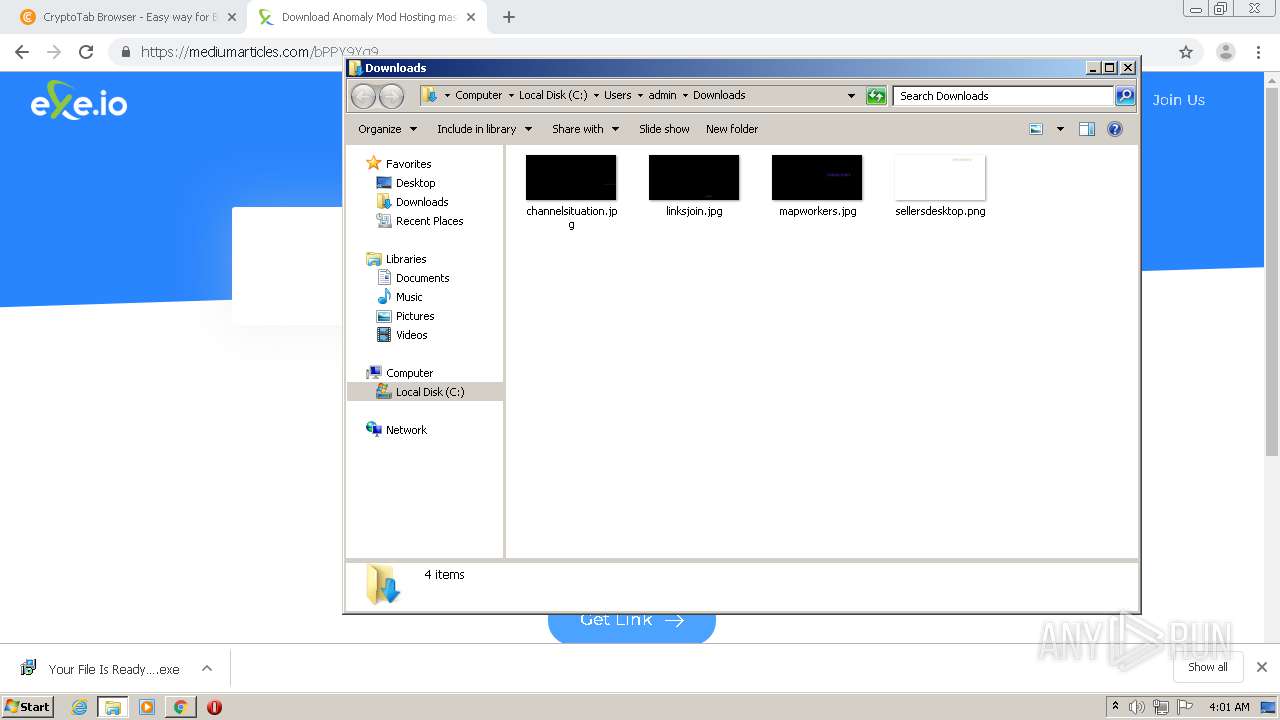
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1112 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F0A7CA8-458.pma | — | |
MD5:— | SHA256:— | |||
| 1112 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\7a0b1ae8-05eb-4a9c-a493-c77c98f9c4fc.tmp | — | |
MD5:— | SHA256:— | |||
| 1112 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1112 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF109e16.TMP | text | |
MD5:— | SHA256:— | |||
| 1112 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1112 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1112 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF109e84.TMP | text | |
MD5:— | SHA256:— | |||
| 1112 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1112 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1112 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF109fdc.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
39
TCP/UDP connections
216
DNS requests
119
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
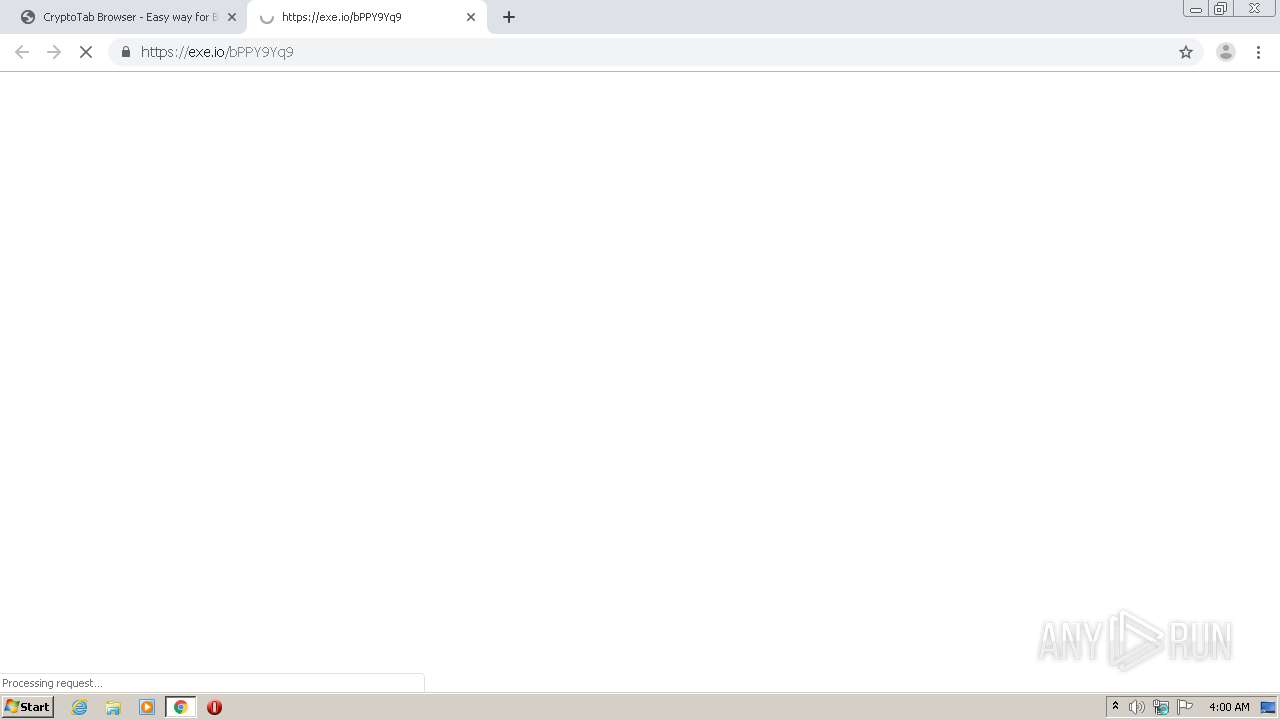
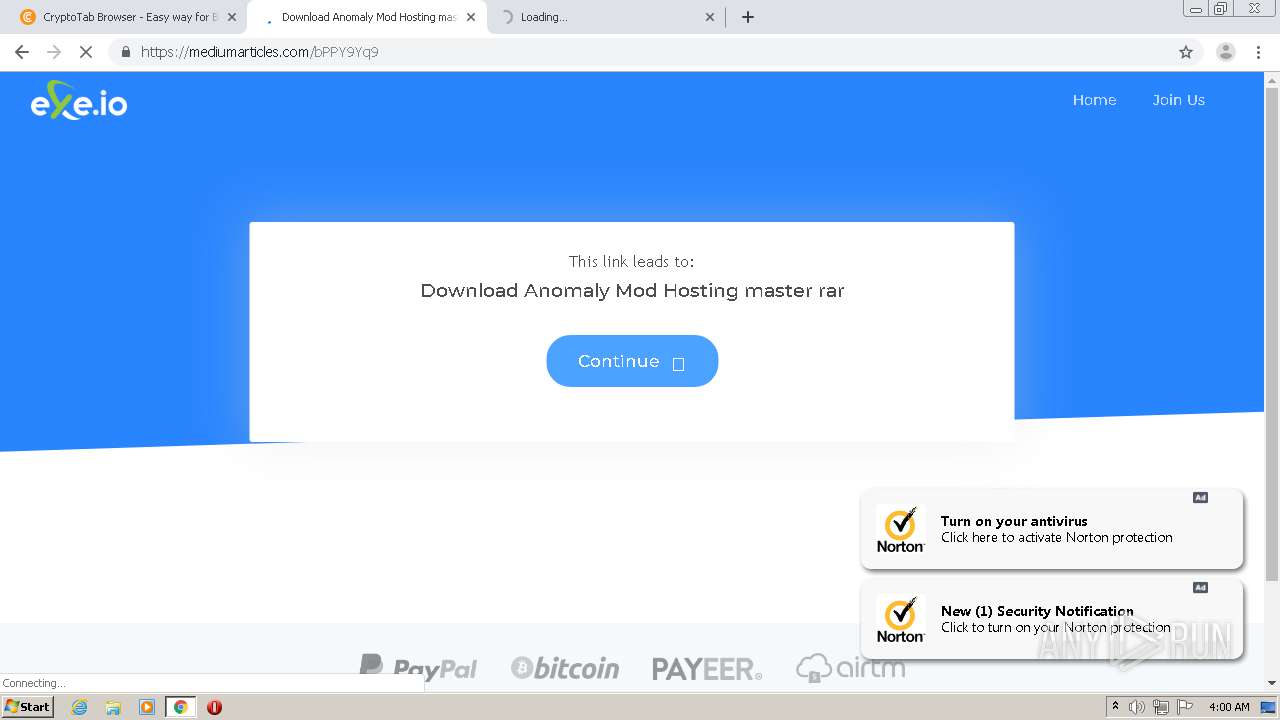
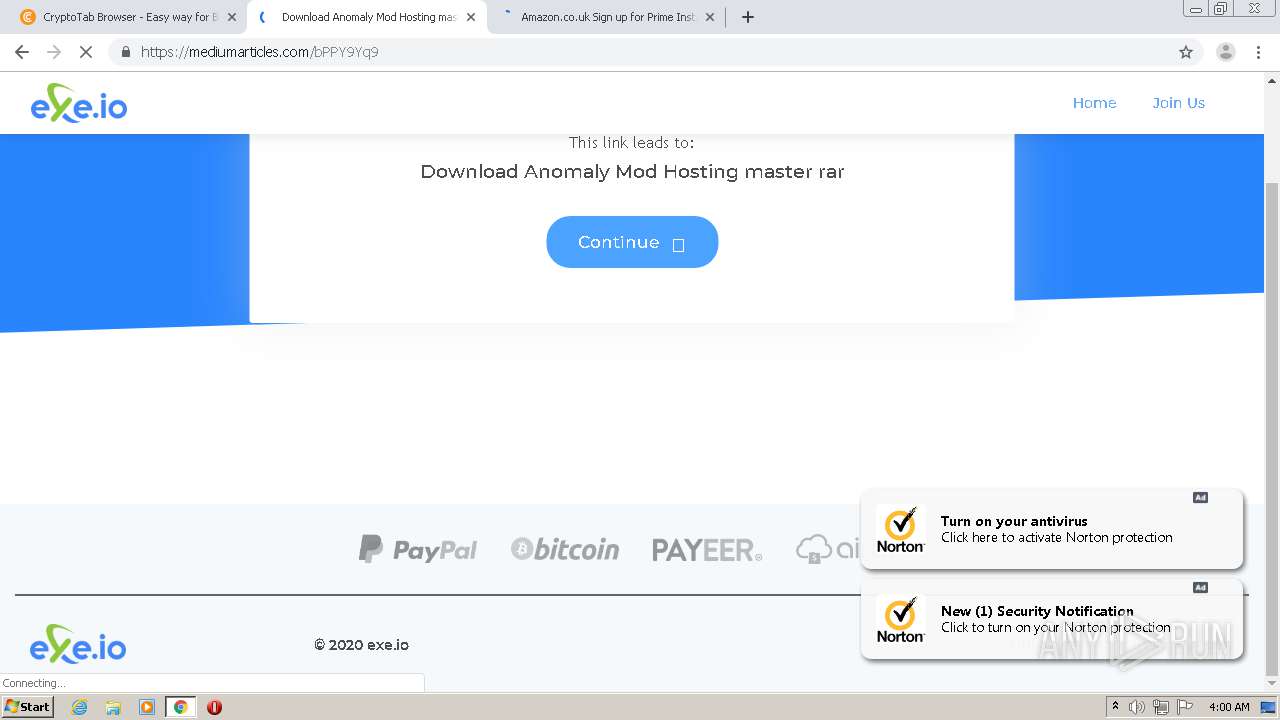
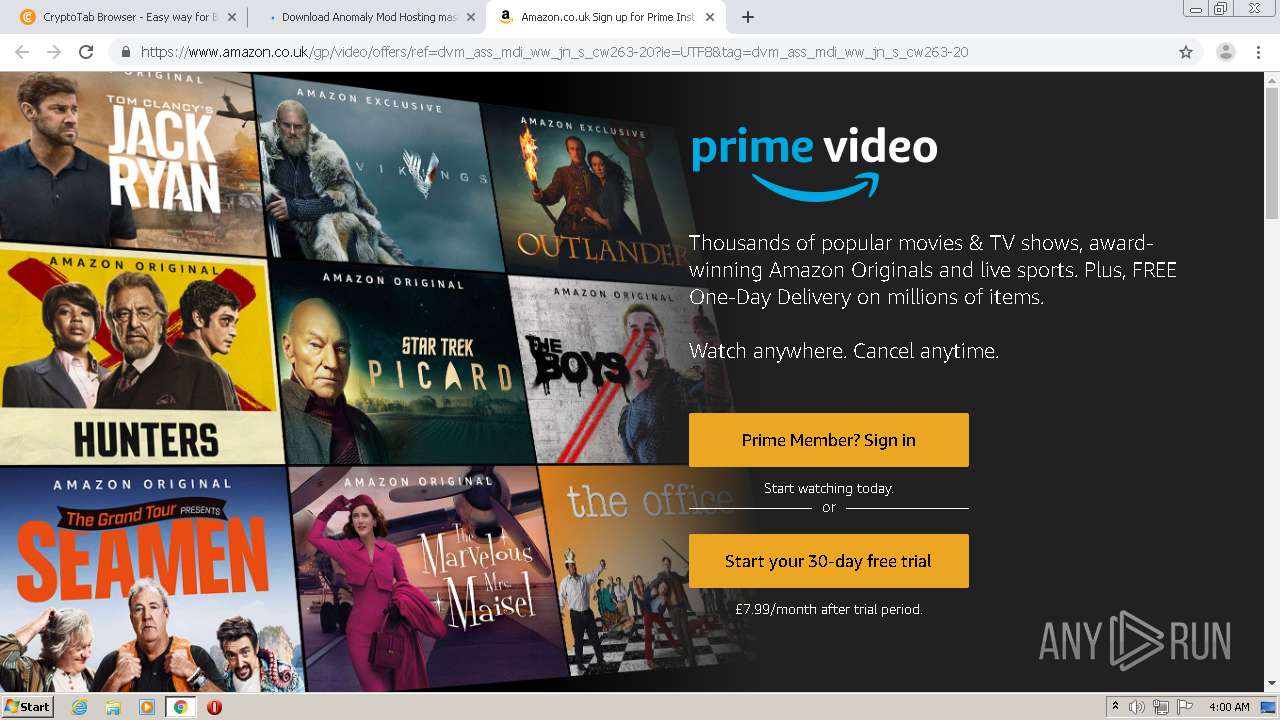
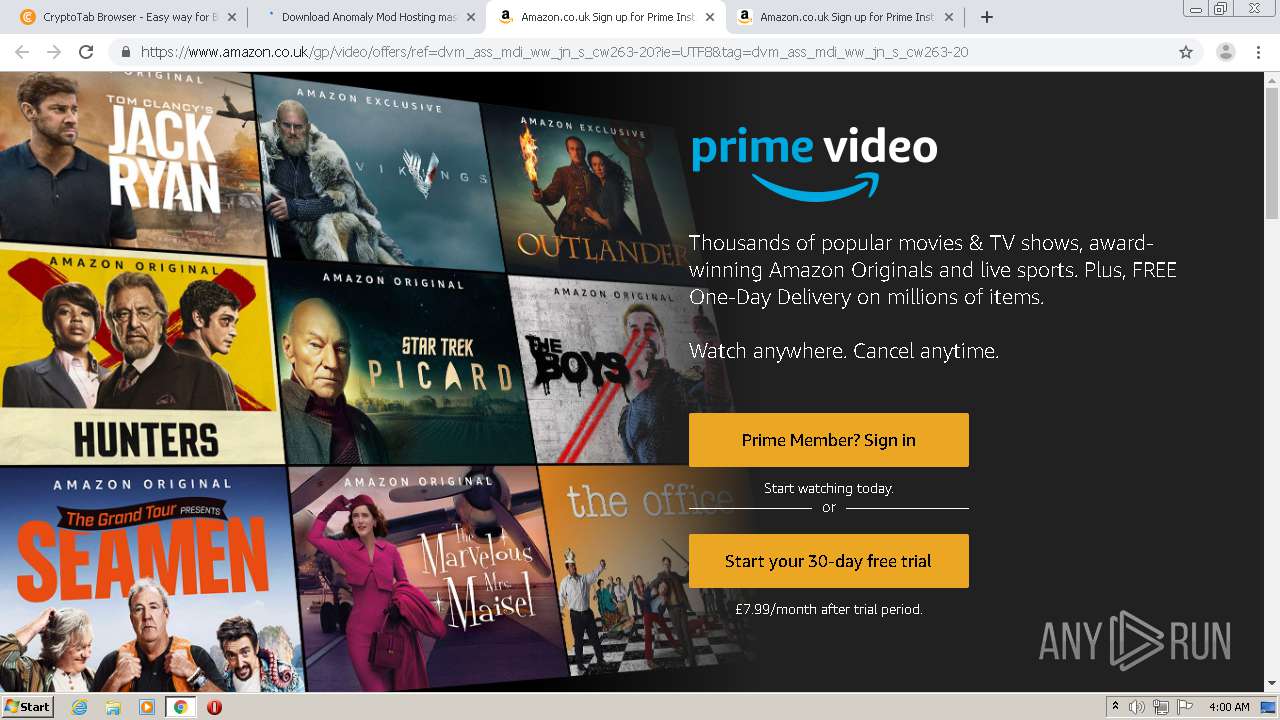
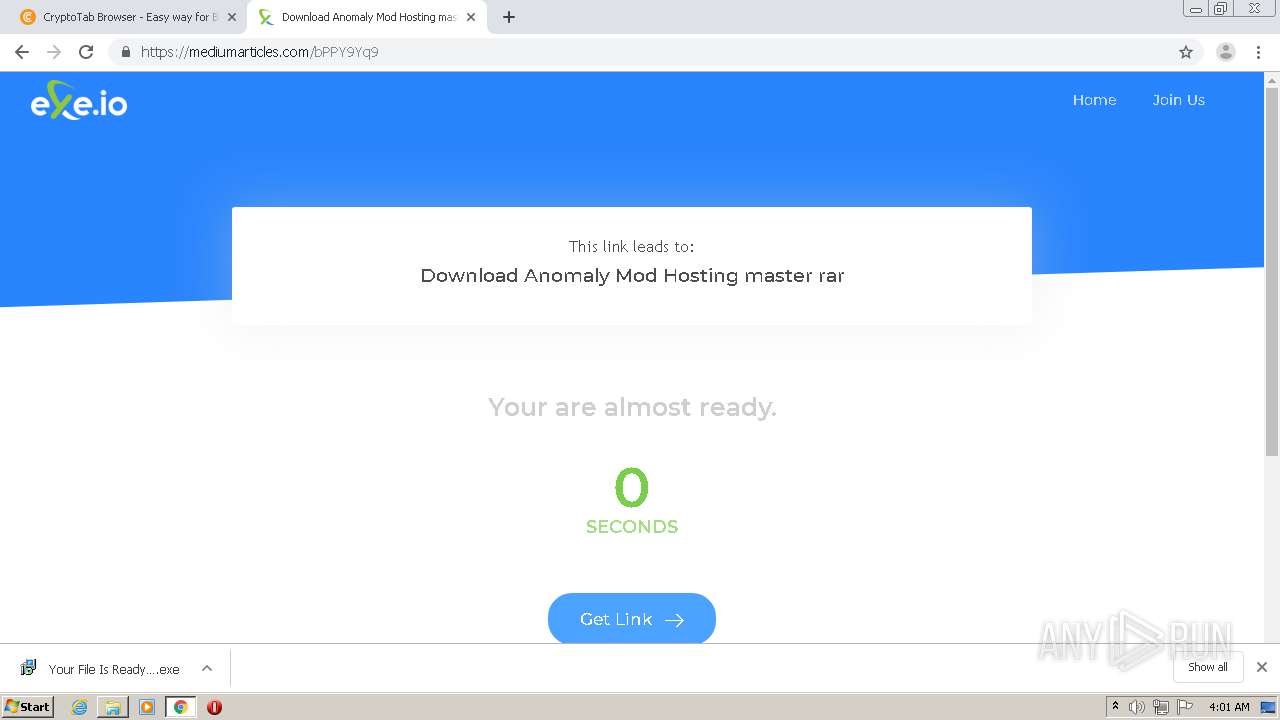
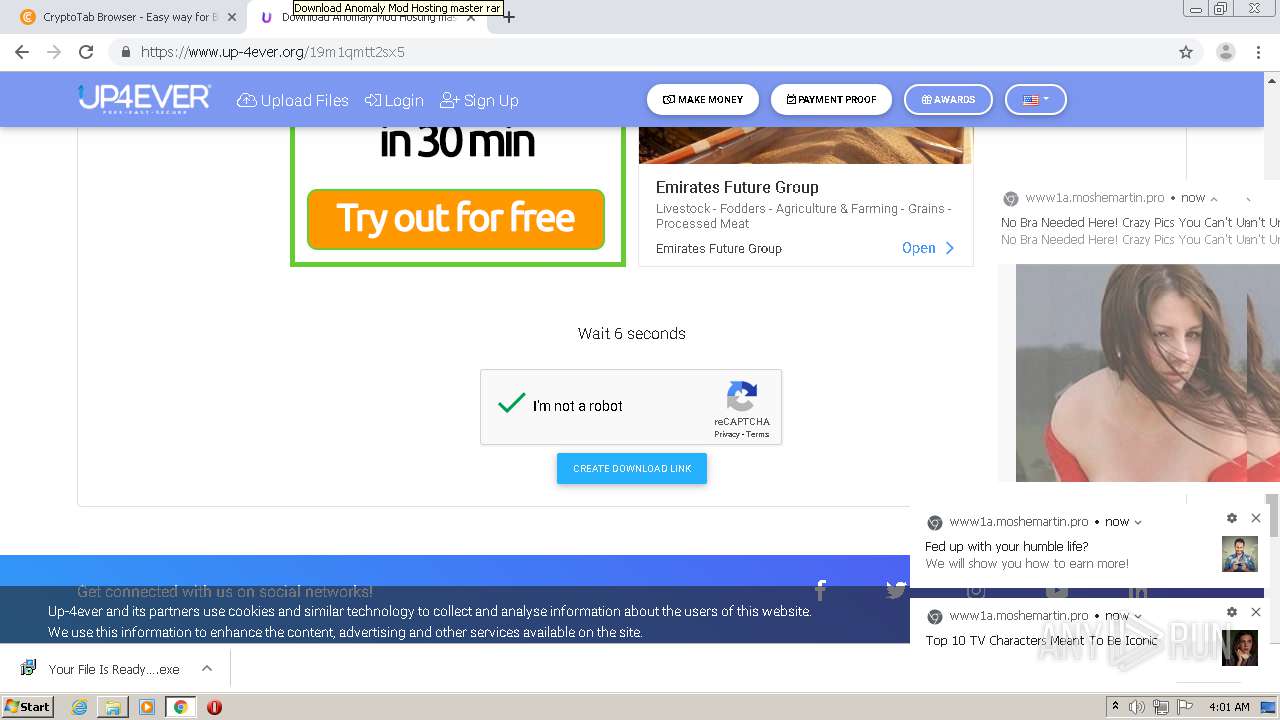
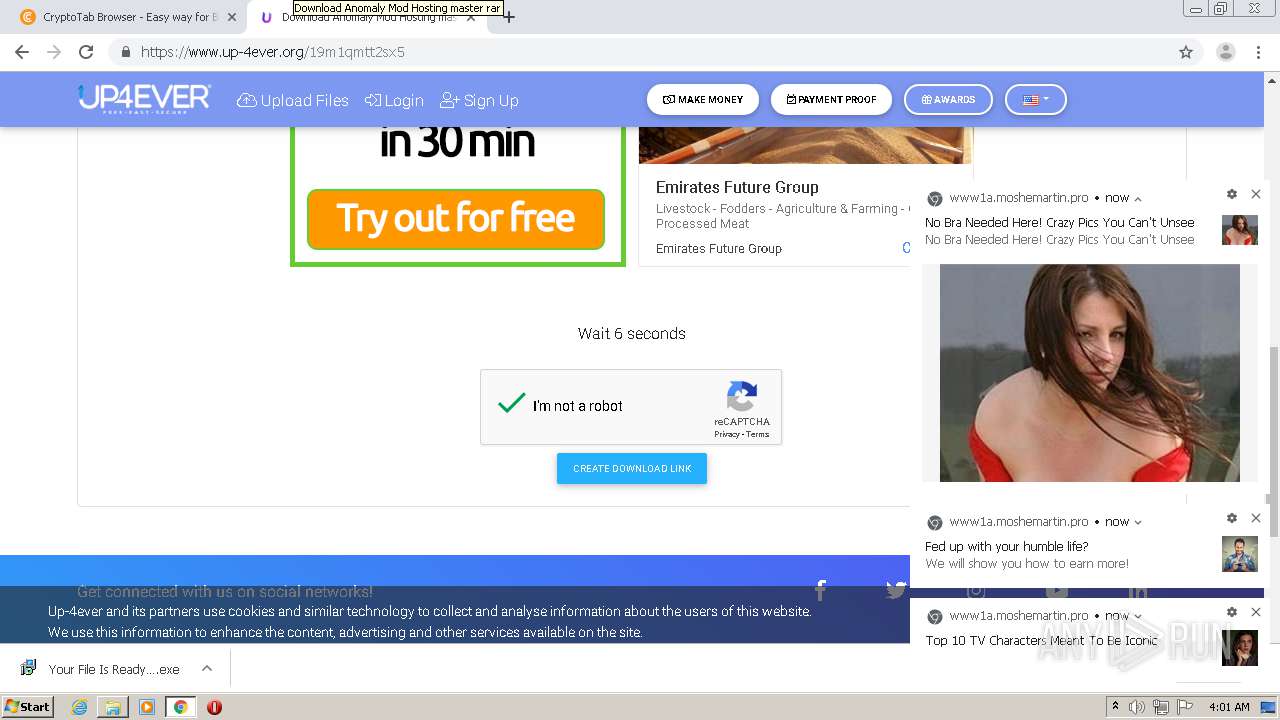
4072 | chrome.exe | GET | 301 | 104.31.82.15:80 | http://crefranek.com/4ipx | US | — | — | malicious |
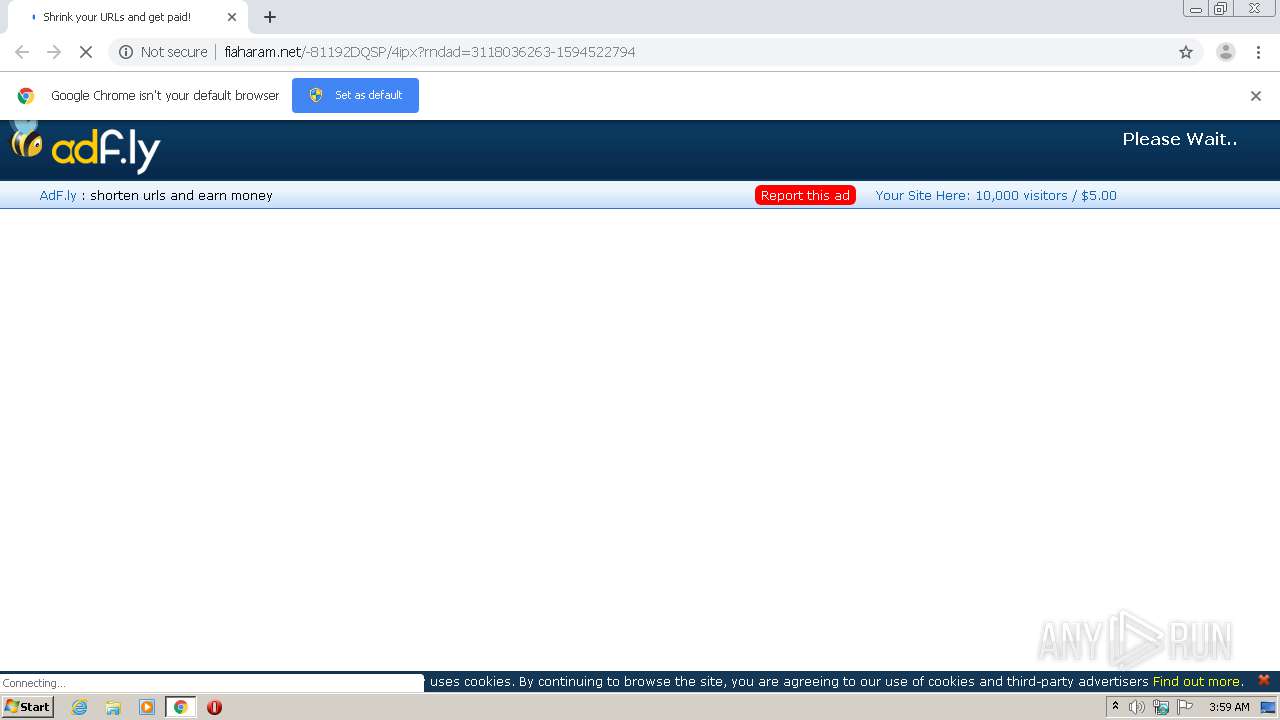
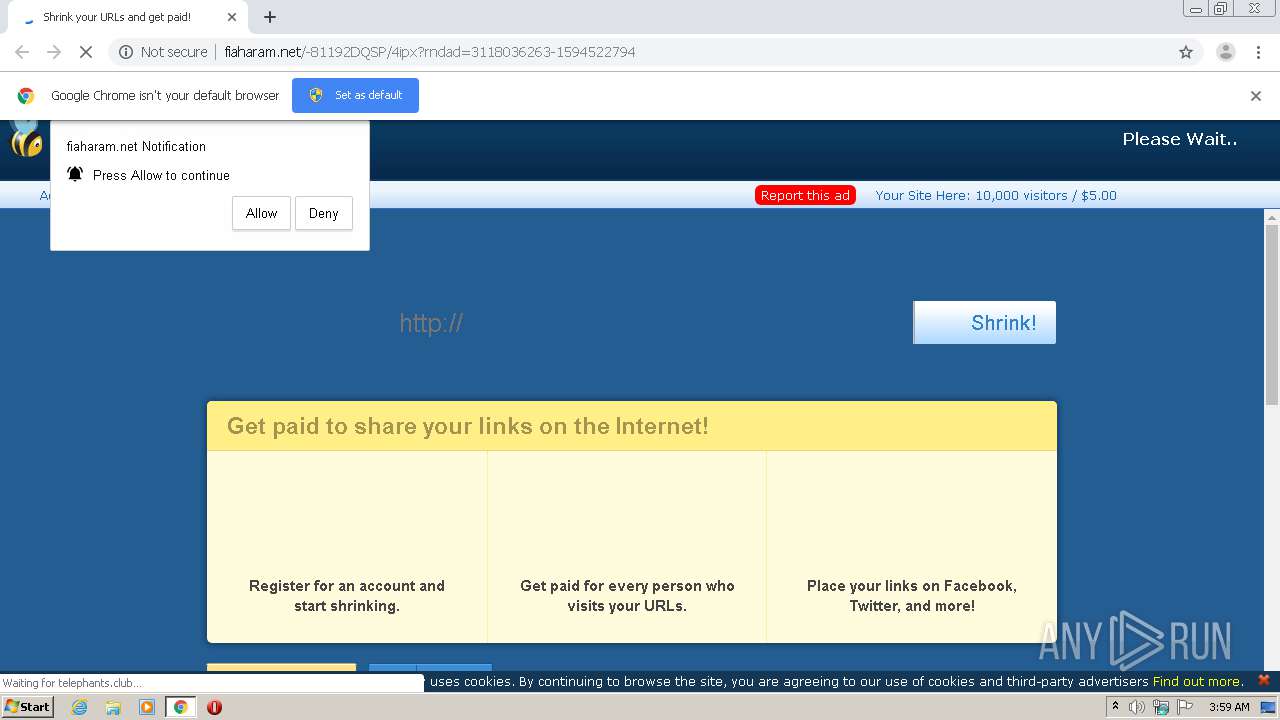
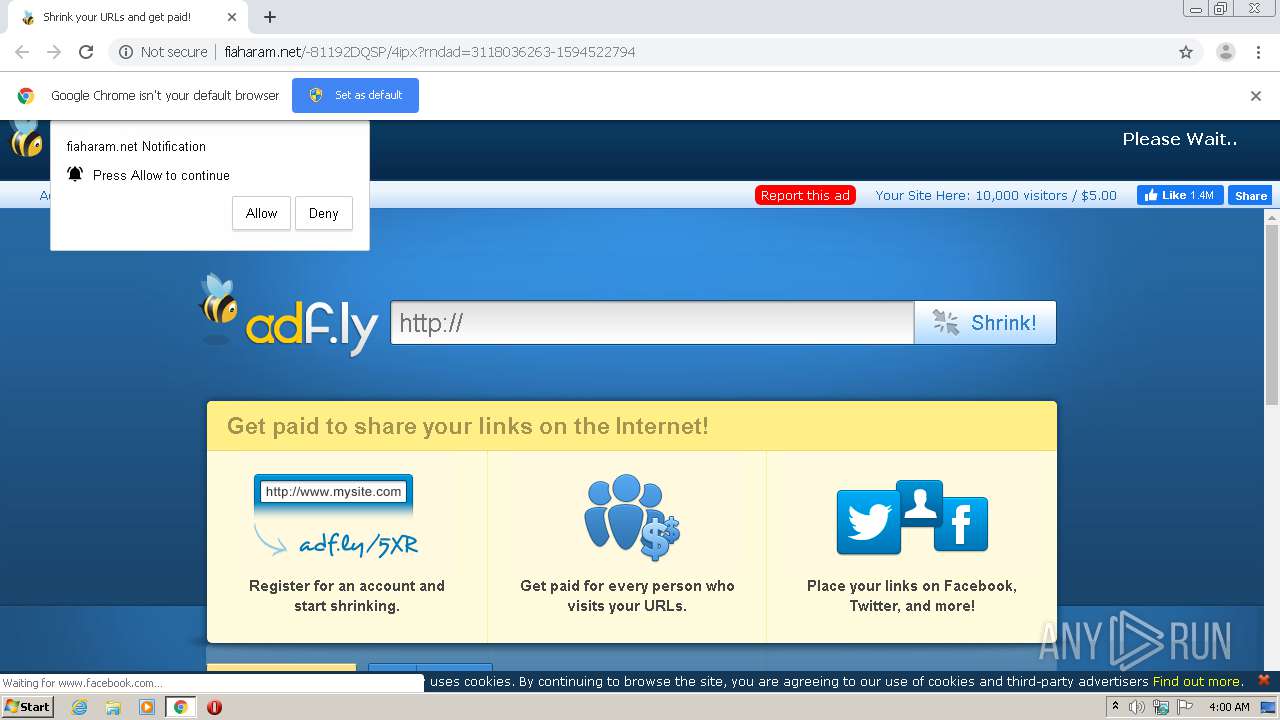
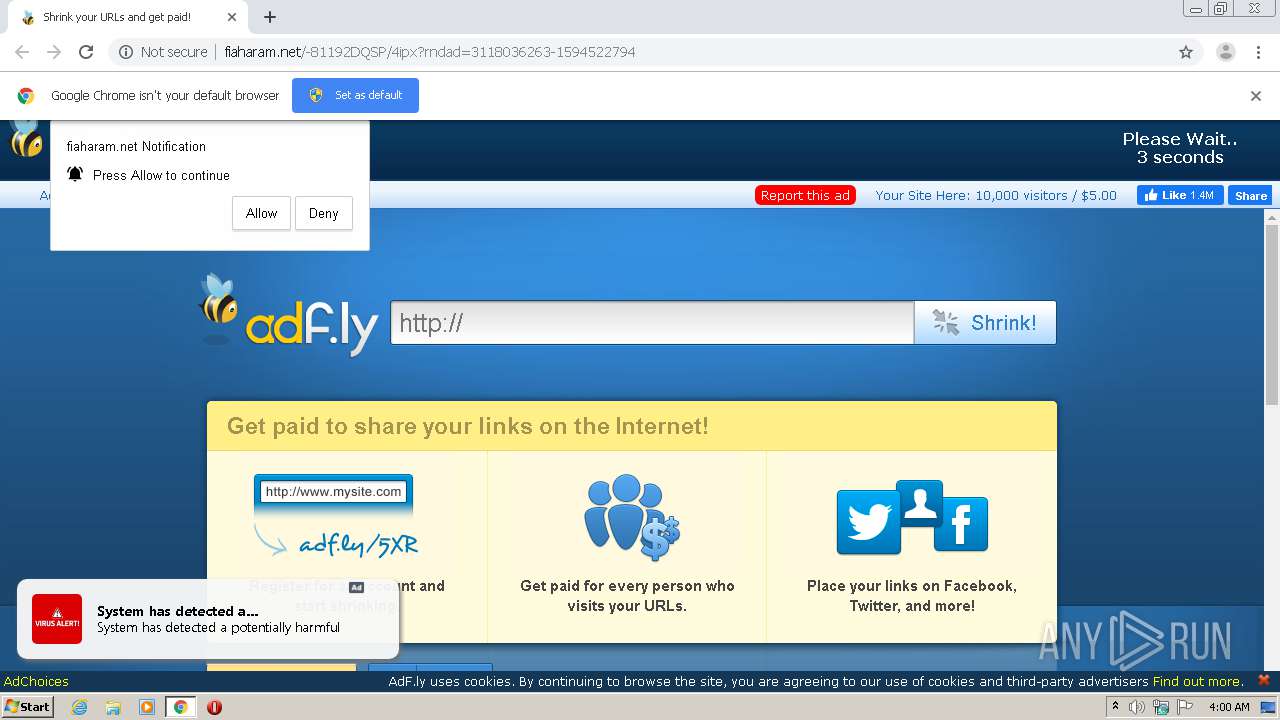
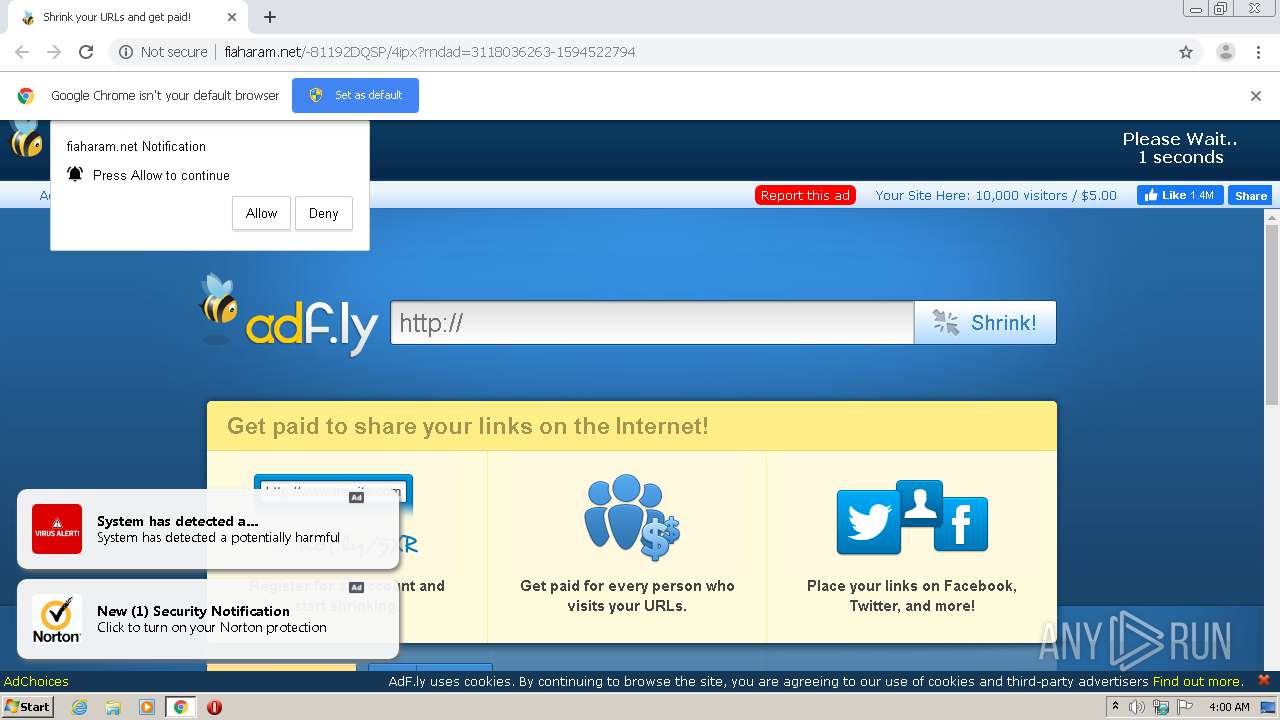
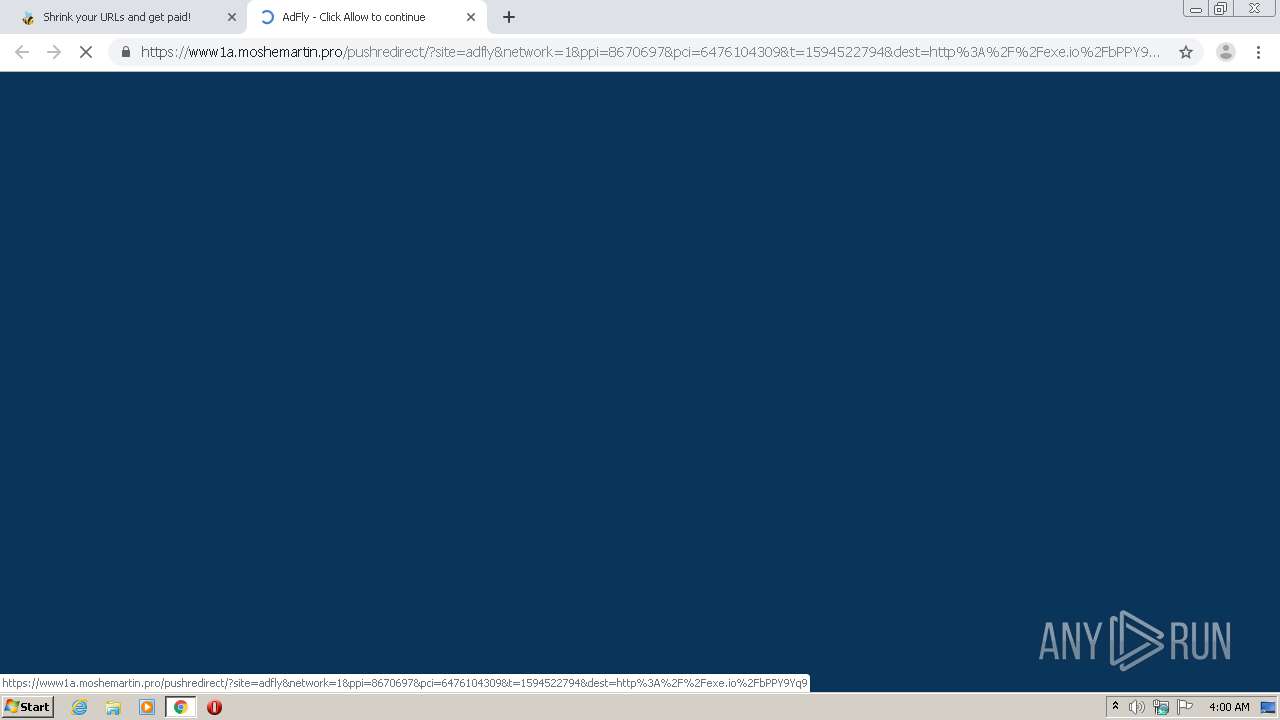
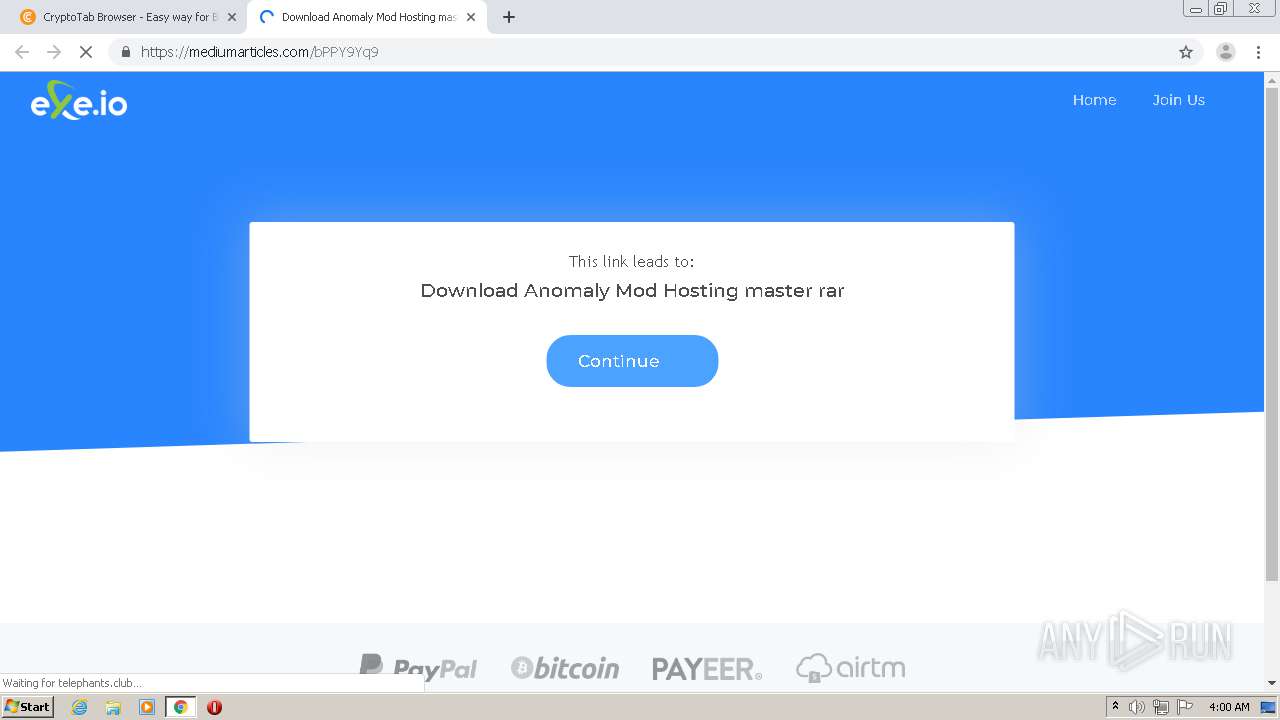
4072 | chrome.exe | GET | 200 | 172.64.131.35:80 | http://fiaharam.net/-81192DQSP/4ipx?rndad=3118036263-1594522794 | US | html | 5.61 Kb | whitelisted |
4072 | chrome.exe | GET | 200 | 172.64.130.35:80 | http://cdn.fiaharam.net/static/js/view111.js | US | text | 28.1 Kb | whitelisted |
4072 | chrome.exe | GET | 200 | 172.64.130.35:80 | http://cdn.fiaharam.net/static/js/main.js | US | text | 667 b | whitelisted |
4072 | chrome.exe | GET | 200 | 52.222.167.144:80 | http://d1nmxiiewlx627.cloudfront.net/?ixmnd=709056 | US | compressed | 34.9 Kb | whitelisted |
4072 | chrome.exe | GET | 200 | 172.64.130.35:80 | http://cdn.fiaharam.net/static/js/b64.js | US | text | 1.07 Kb | whitelisted |
4072 | chrome.exe | GET | 200 | 172.64.131.35:80 | http://fiaharam.net/js/display.js | US | text | 13.1 Kb | whitelisted |
4072 | chrome.exe | GET | 200 | 172.64.131.35:80 | http://fiaharam.net/fp.rev11.php?ver=8670697&nocache=977 | US | text | 12.8 Kb | whitelisted |
4072 | chrome.exe | GET | 200 | 172.64.130.35:80 | http://cdn.fiaharam.net/static/css/adfly_7.css | US | text | 869 b | whitelisted |
4072 | chrome.exe | GET | 200 | 172.64.130.35:80 | http://cdn.fiaharam.net/static/js/amvn.js | US | text | 124 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4072 | chrome.exe | 172.217.22.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
4072 | chrome.exe | 104.31.82.15:80 | crefranek.com | Cloudflare Inc | US | shared |
4072 | chrome.exe | 216.58.207.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
4072 | chrome.exe | 172.64.130.35:80 | fiaharam.net | Cloudflare Inc | US | suspicious |
4072 | chrome.exe | 172.217.21.234:80 | ajax.googleapis.com | Google Inc. | US | whitelisted |
4072 | chrome.exe | 172.64.131.35:80 | fiaharam.net | Cloudflare Inc | US | malicious |
— | — | 52.222.166.159:80 | questaurah.club | Amazon.com, Inc. | US | suspicious |
4072 | chrome.exe | 52.222.166.32:80 | providentsopport.site | Amazon.com, Inc. | US | unknown |
4072 | chrome.exe | 157.240.195.35:80 | www.facebook.com | — | US | suspicious |
4072 | chrome.exe | 216.58.212.174:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crefranek.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
fiaharam.net |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
cdn.fiaharam.net |
| whitelisted |
d1nmxiiewlx627.cloudfront.net |
| whitelisted |
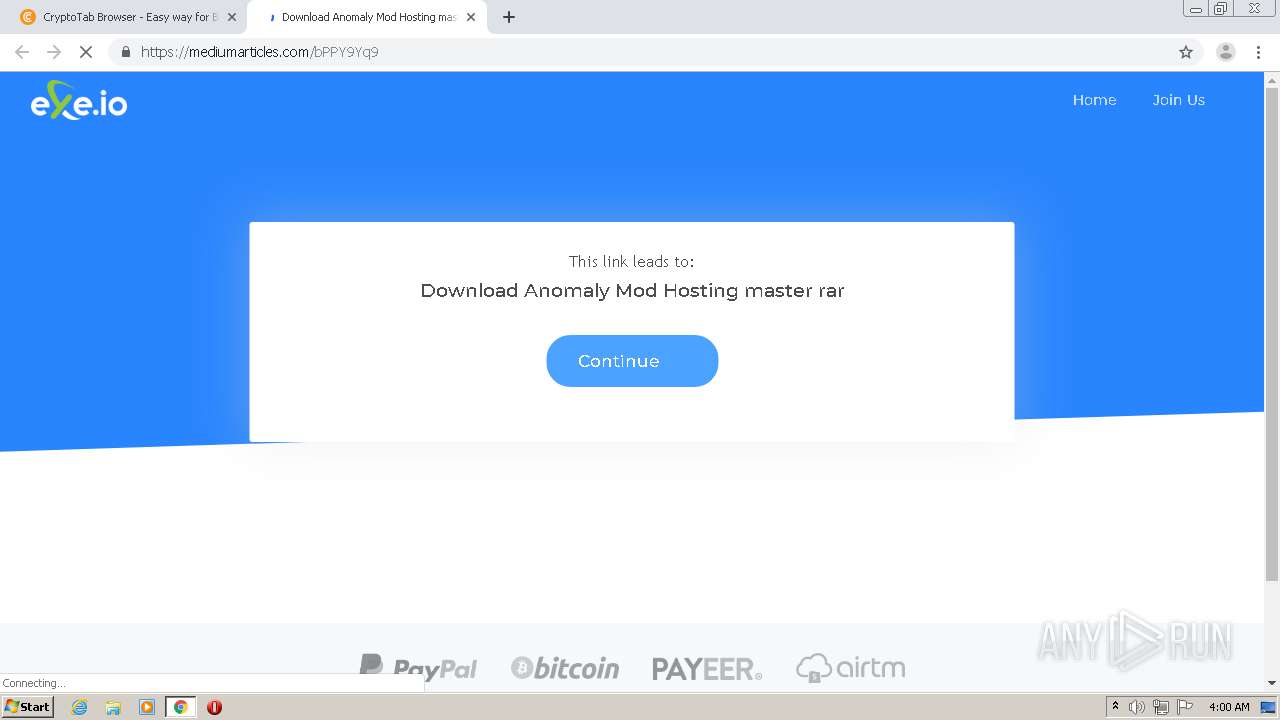
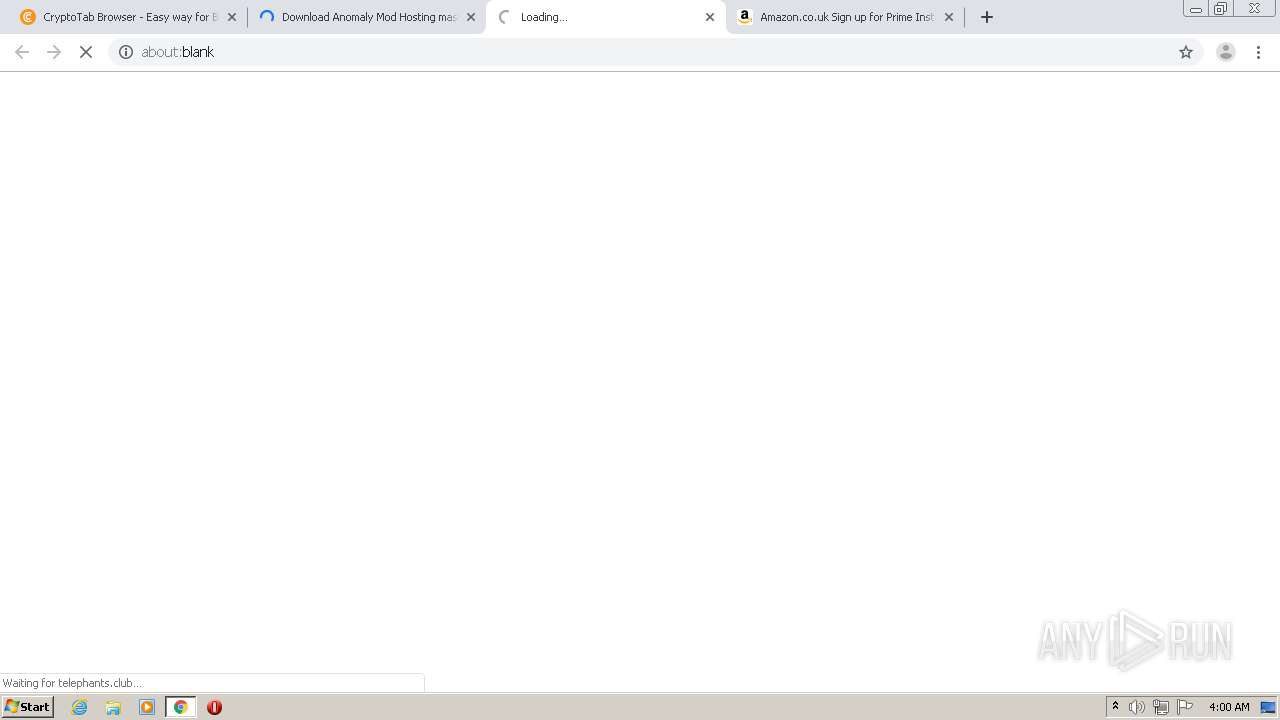
telephants.club |
| malicious |
questaurah.club |
| suspicious |
providentsopport.site |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4072 | chrome.exe | Attempted User Privilege Gain | AV POLICY Observed Suspicious JScript serving Adware Inbound |