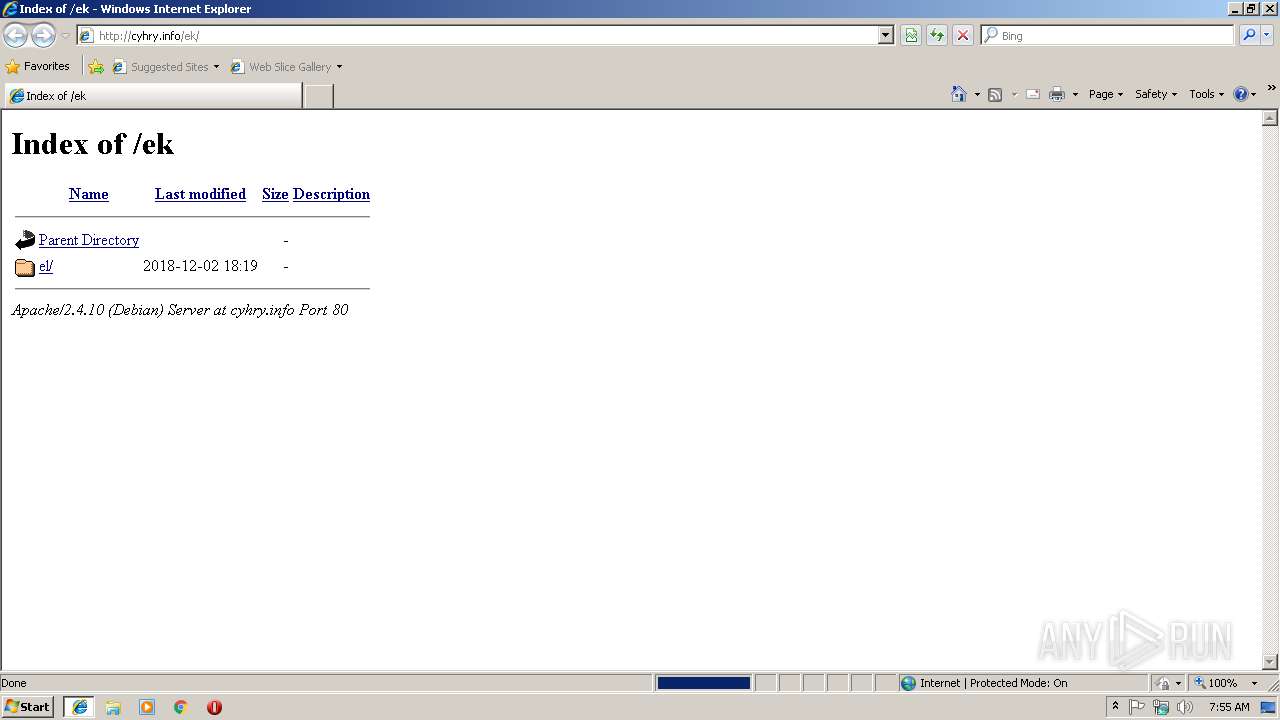
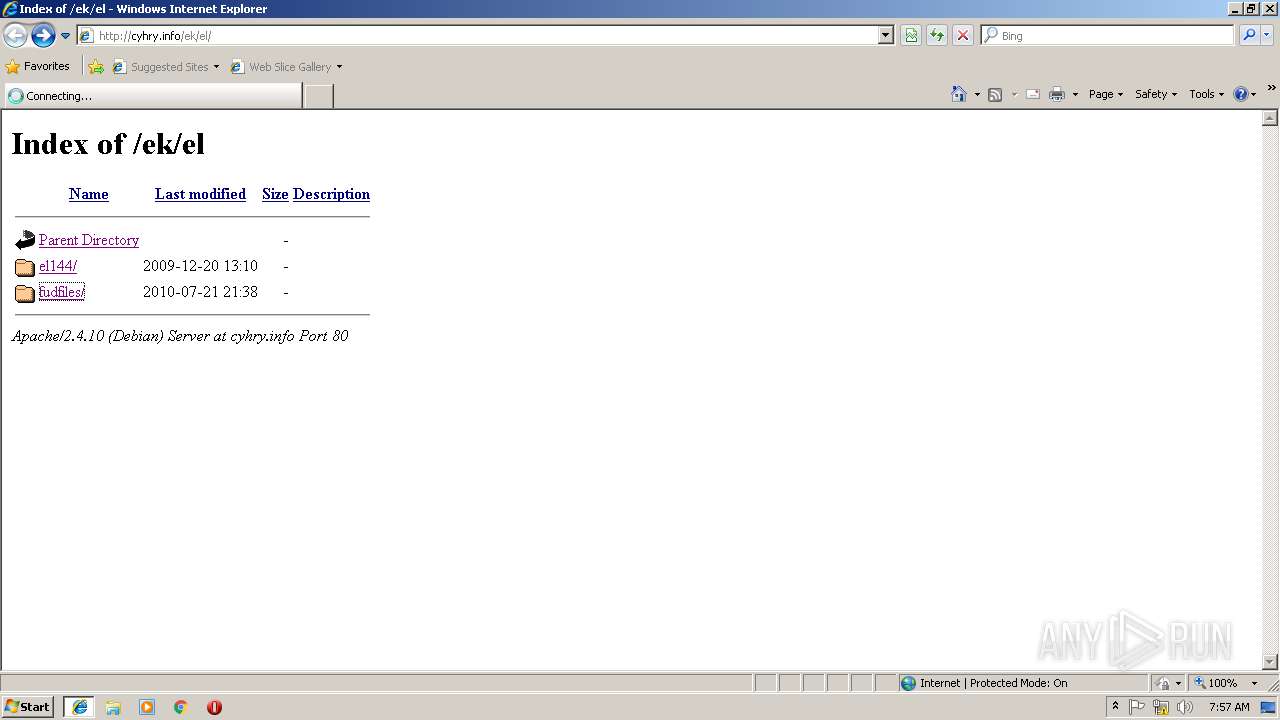
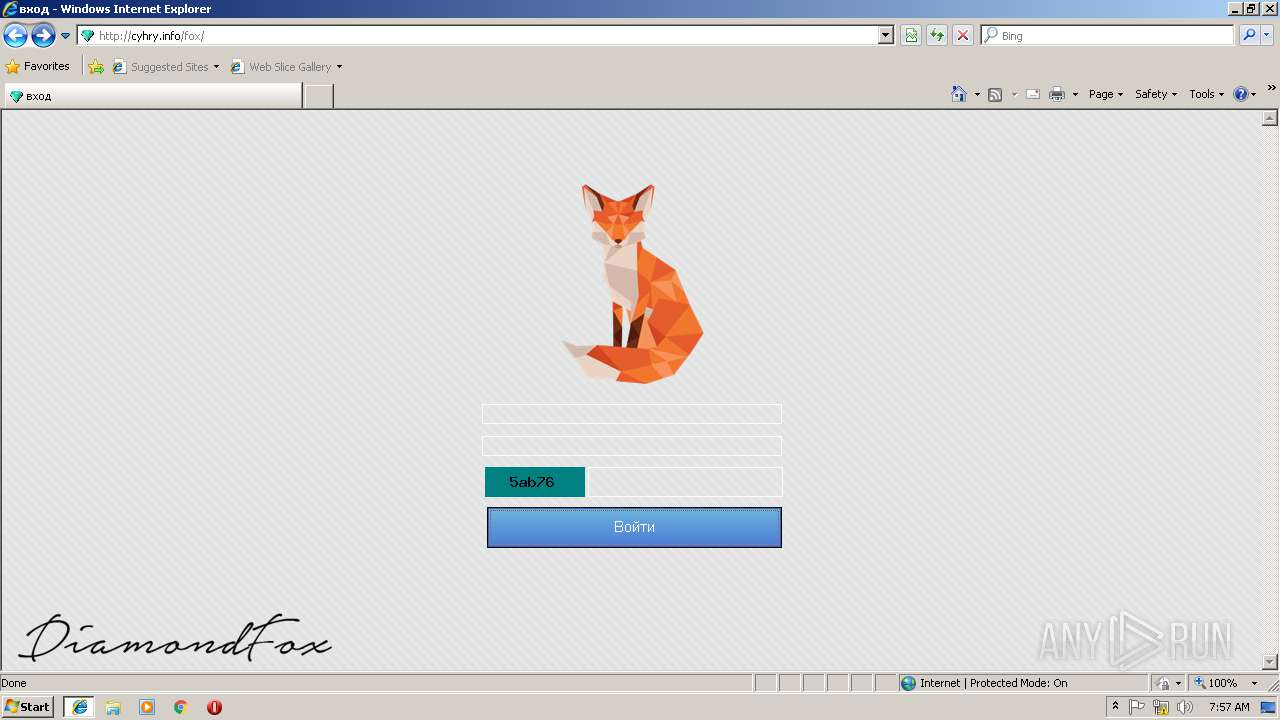
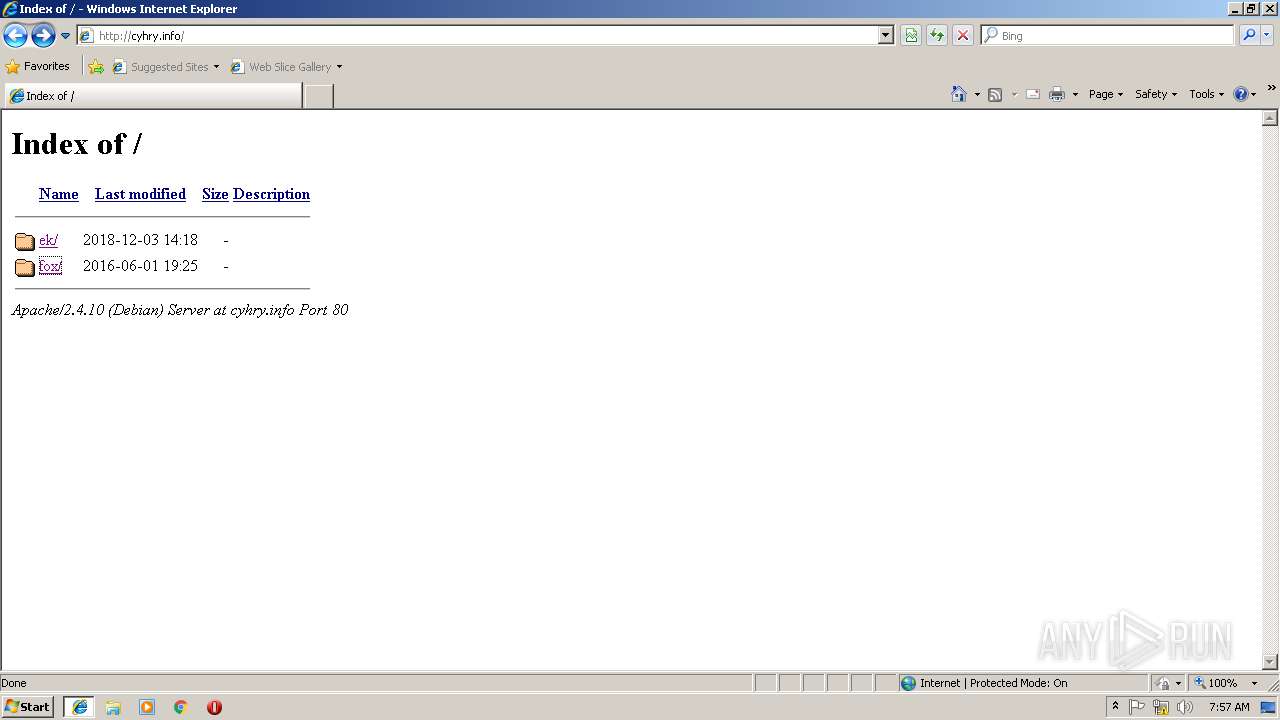
| URL: | http://cyhry.info/ek |
| Full analysis: | https://app.any.run/tasks/8994d51c-b432-4496-b988-163596fc66db |
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2018, 07:55:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E62D105ADC9A431406B8898508412BE4 |
| SHA1: | D342B0DB1AEB9C83391D08376D21AED24E5E025C |
| SHA256: | B5D9B4379B339267A40AE9F6E8D8DE486265260D0DF2CB649405E1BBA9F32052 |
| SSDEEP: | 3:N1Kdcr:Cer |
MALICIOUS
No malicious indicators.SUSPICIOUS
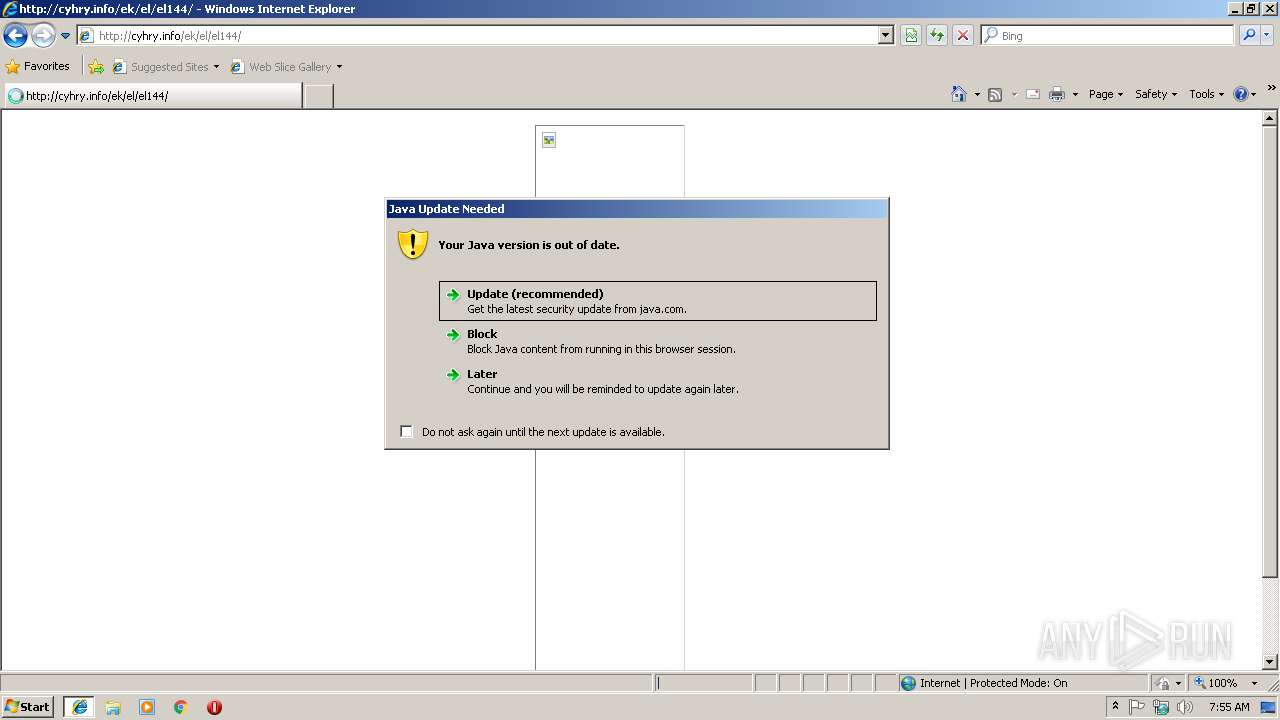
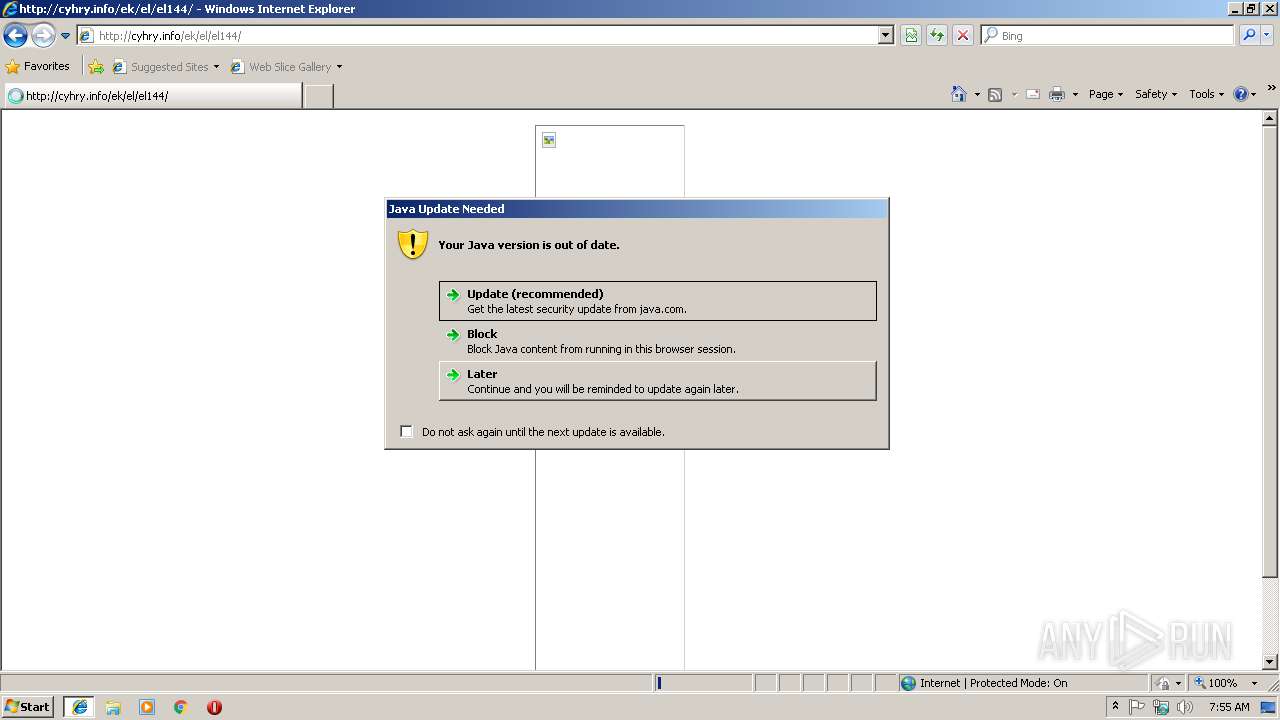
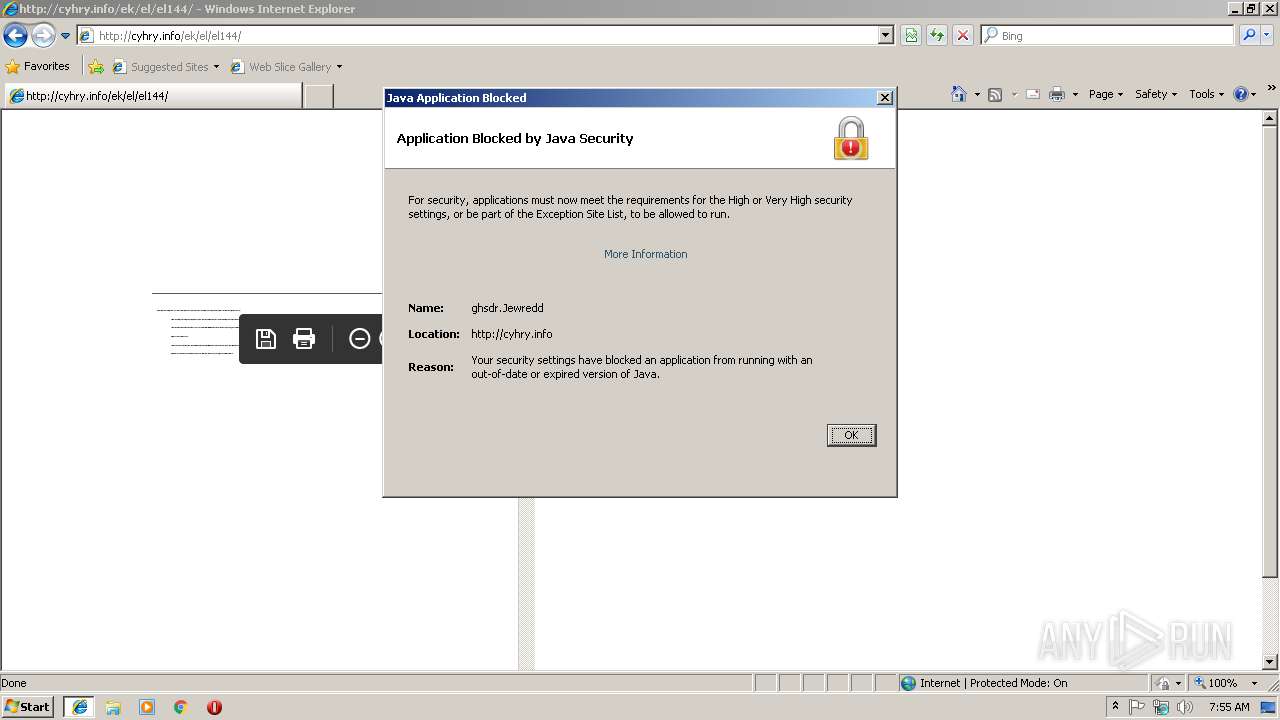
Executes JAVA applets
- iexplore.exe (PID: 1864)
Creates files in the user directory
- jp2launcher.exe (PID: 2724)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2832)
Creates files in the user directory
- iexplore.exe (PID: 2832)
- AcroRd32.exe (PID: 3256)
- AcroRd32.exe (PID: 3364)
- AcroRd32.exe (PID: 2944)
Application launched itself
- AcroRd32.exe (PID: 2944)
- iexplore.exe (PID: 2832)
- AcroRd32.exe (PID: 3256)
- RdrCEF.exe (PID: 2916)
- RdrCEF.exe (PID: 3708)
Reads Internet Cache Settings
- iexplore.exe (PID: 1864)
- iexplore.exe (PID: 2832)
Reads internet explorer settings
- iexplore.exe (PID: 1864)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
53
Monitored processes
22
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1208 | "C:\Program Files\Java\jre1.8.0_92\bin\jp2launcher.exe" -secure -plugin -jre "C:\Program Files\Java\jre1.8.0_92" -vma LURfX2p2bV9sYXVuY2hlZD0xMjA2OTE5MzQ5AC1EX19hcHBsZXRfbGF1bmNoZWQ9MTIwNjkwODY0MAAtRHN1bi5hd3Qud2FybXVwPXRydWUALURqYXZhLnNlY3VyaXR5Lm1hbmFnZXIA -ma cmVhZF9waXBlX25hbWU9anBpMl9waWQxODY0X3BpcGUyLHdyaXRlX3BpcGVfbmFtZT1qcGkyX3BpZDE4NjRfcGlwZTMA | C:\Program Files\Java\jre1.8.0_92\bin\jp2launcher.exe | — | iexplore.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: LOW Description: Java(TM) Web Launcher Exit code: 0 Version: 11.92.2.14 Modules
| |||||||||||||||
| 1864 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2832 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2388 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -cp "C:\PROGRA~1\Java\JRE18~1.0_9\lib\deploy.jar" com.sun.deploy.panel.ControlPanel -userConfig "deployment.expiration.decision.suppression.11.92.2" "false" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | — | iexplore.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: LOW Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 2464 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" --type=renderer /o /eo /l /b /id 1864 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 1 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 2496 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" /o /eo /l /b /id 1864 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | iexplore.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 0 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 2724 | "C:\Program Files\Java\jre1.8.0_92\bin\jp2launcher.exe" -secure -plugin -jre "C:\Program Files\Java\jre1.8.0_92" -vma LURfX2p2bV9sYXVuY2hlZD0xMjA2OTE5MzQ5AC1EX19hcHBsZXRfbGF1bmNoZWQ9MTIwNjkwODY0MAAtRHN1bi5hd3Qud2FybXVwPXRydWUALURqYXZhLnNlY3VyaXR5Lm1hbmFnZXIA -ma cmVhZF9waXBlX25hbWU9anBpMl9waWQxODY0X3BpcGUyLHdyaXRlX3BpcGVfbmFtZT1qcGkyX3BpZDE4NjRfcGlwZTMA | C:\Program Files\Java\jre1.8.0_92\bin\jp2launcher.exe | iexplore.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Web Launcher Exit code: 0 Version: 11.92.2.14 Modules
| |||||||||||||||
| 2832 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2844 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -cp "C:\PROGRA~1\Java\JRE18~1.0_9\lib\deploy.jar" com.sun.deploy.panel.ControlPanel -userConfig "deployment.expiration.decision.11.92.2" "later" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | — | iexplore.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: LOW Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 2860 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" /o /eo /l /b /id 1864 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | iexplore.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 0 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 2908 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" /o /eo /l /b /id 1864 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | iexplore.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 0 Version: 15.23.20070.215641 Modules
| |||||||||||||||
Total events
1 062
Read events
865
Write events
185
Delete events
12
Modification events
| (PID) Process: | (2832) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2832) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2832) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2832) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2832) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2832) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2832) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {4CDDCB25-F92C-11E8-91D7-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2832) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2832) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (2832) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E2070C0004000600070037001F004202 | |||
Executable files
1
Suspicious files
19
Text files
35
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2832 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2832 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1864 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\ek[1].txt | — | |
MD5:— | SHA256:— | |||
| 1864 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PP6KS563\el[1].txt | — | |
MD5:— | SHA256:— | |||
| 1864 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PP6KS563\el144[1].txt | — | |
MD5:— | SHA256:— | |||
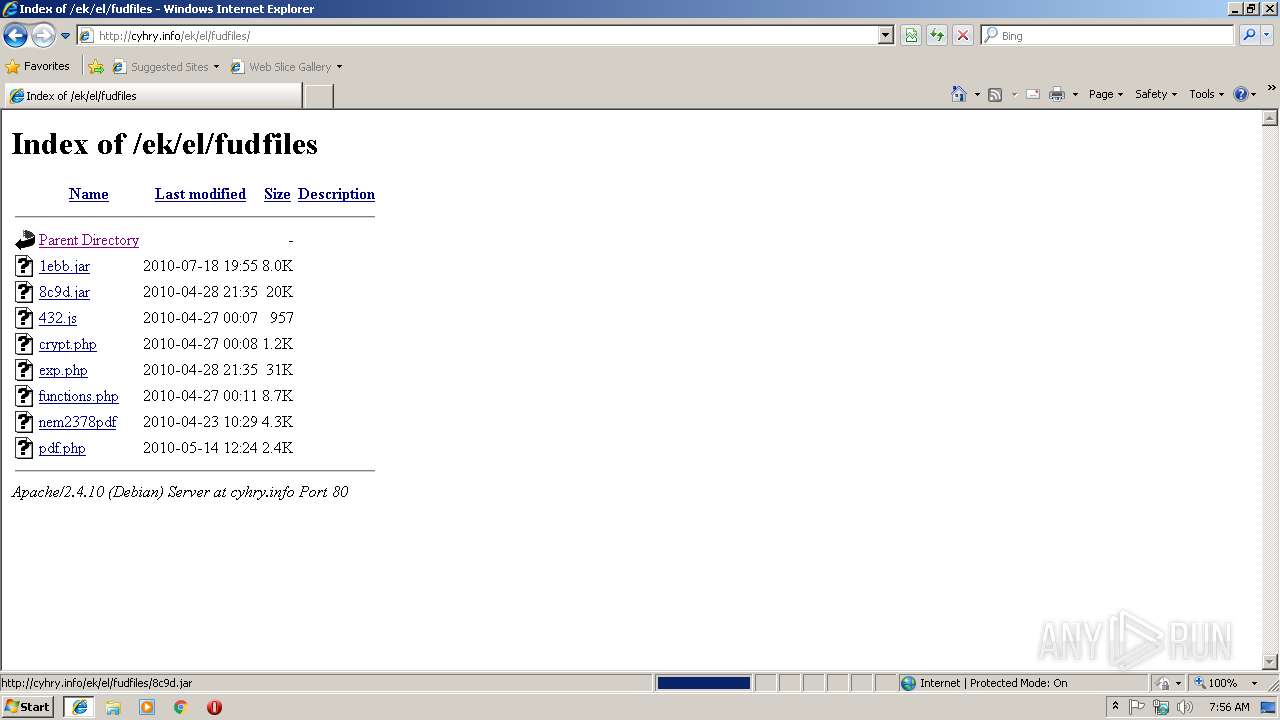
| 2724 | jp2launcher.exe | C:\Users\admin\AppData\Local\Temp\jar_cache168317765517216352.tmp | — | |
MD5:— | SHA256:— | |||
| 2724 | jp2launcher.exe | C:\Users\admin\AppData\LocalLow\Sun\Java\Deployment\cache\6.0\13\74b85cd-16187d26-temp | — | |
MD5:— | SHA256:— | |||
| 3392 | AcroRd32.exe | C:\Users\admin\AppData\LocalLow\Adobe\Acrobat\DC\ReaderMessages-journal | — | |
MD5:— | SHA256:— | |||
| 1864 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\ek[1].htm | html | |
MD5:— | SHA256:— | |||
| 3392 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9Rogh598_czkojh_2m8.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
24
DNS requests
10
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
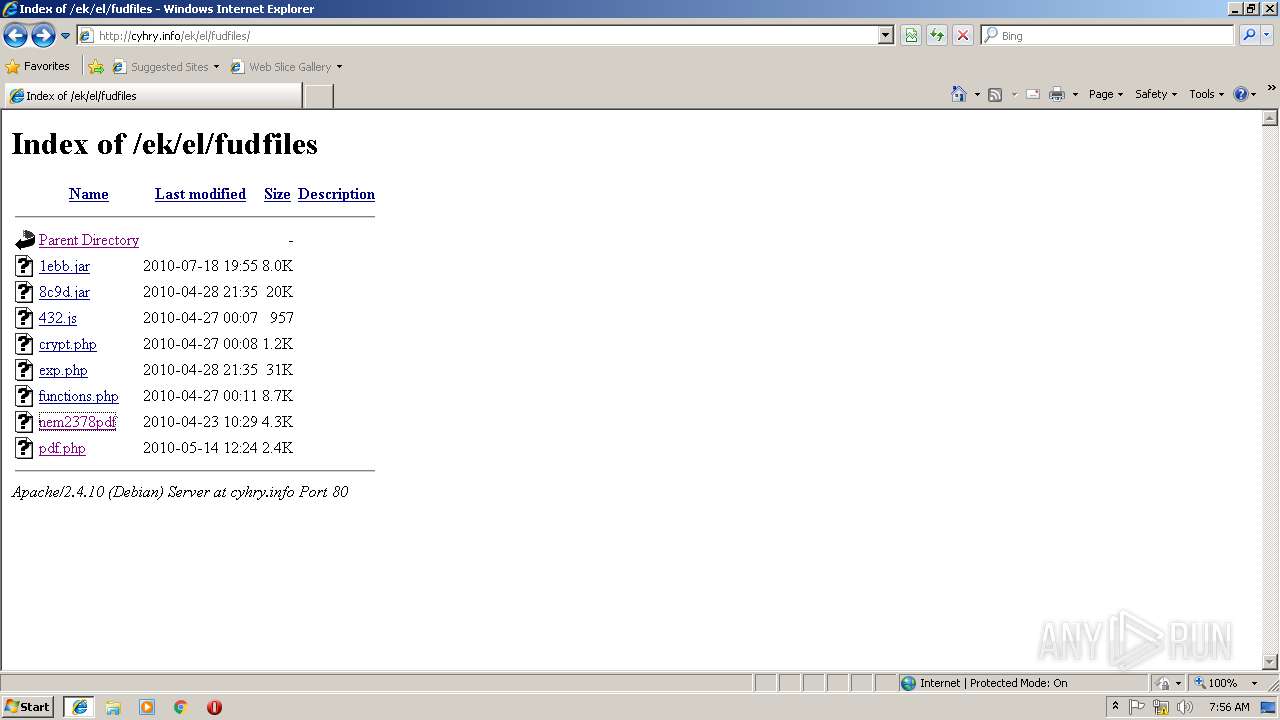
3256 | AcroRd32.exe | GET | 304 | 2.16.186.33:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/284_15_23_20070.zip | unknown | — | — | whitelisted |
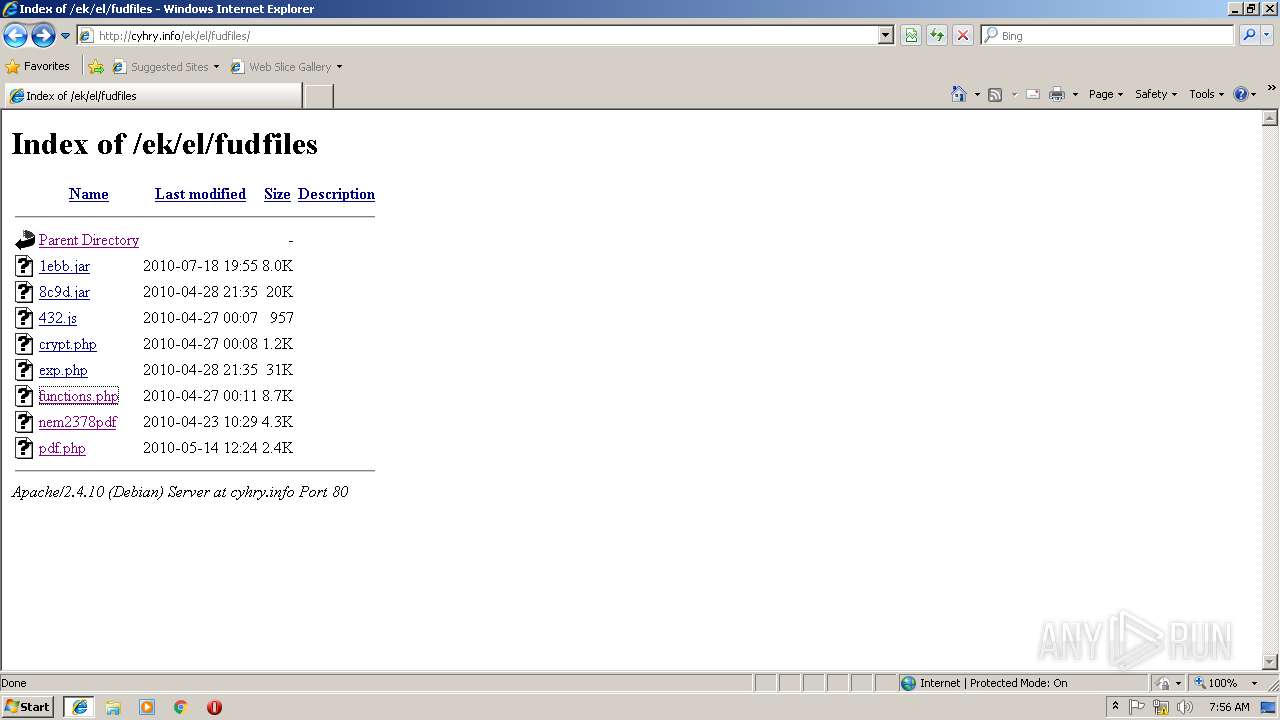
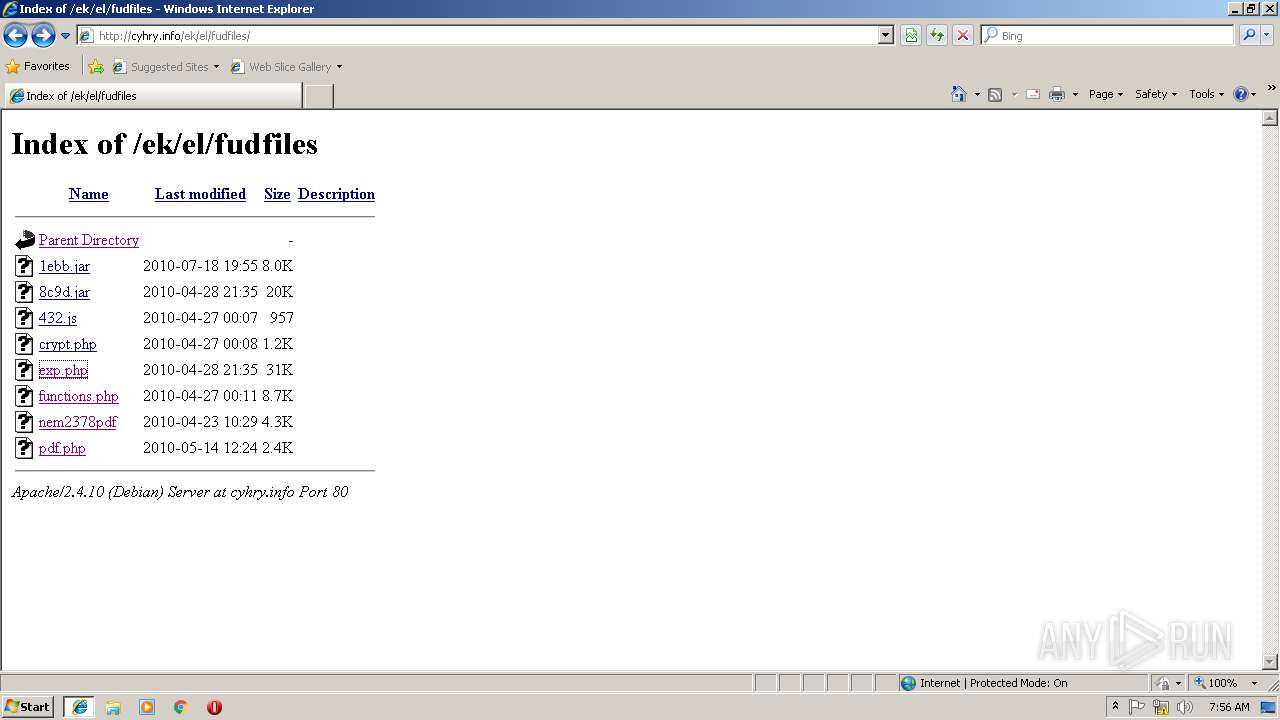
2832 | iexplore.exe | GET | 404 | 185.243.114.215:80 | http://cyhry.info/favicon.ico | unknown | html | 285 b | suspicious |
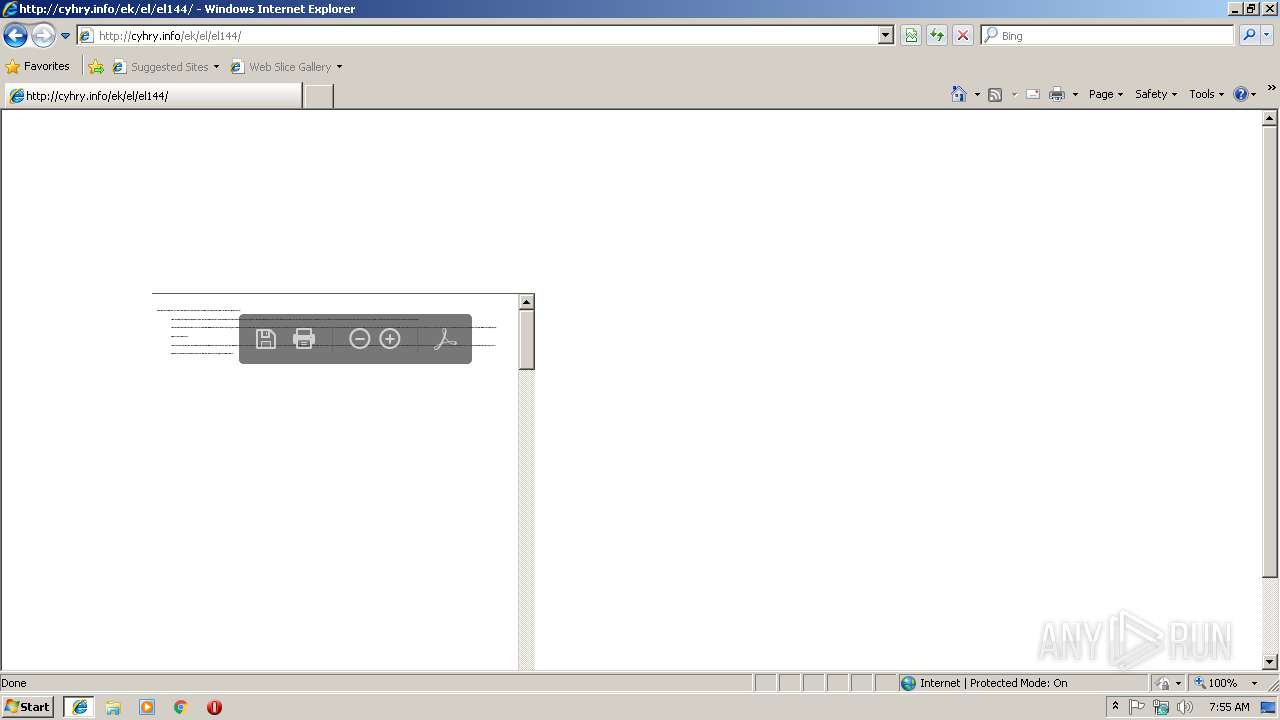
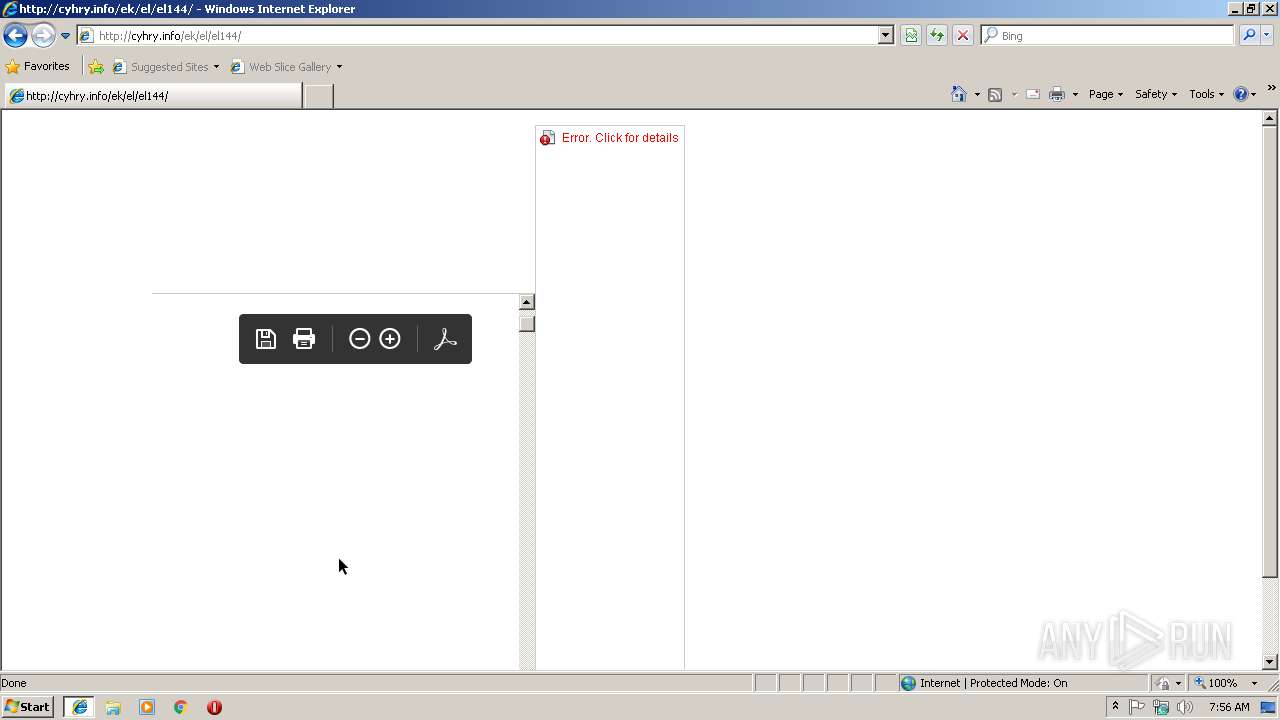
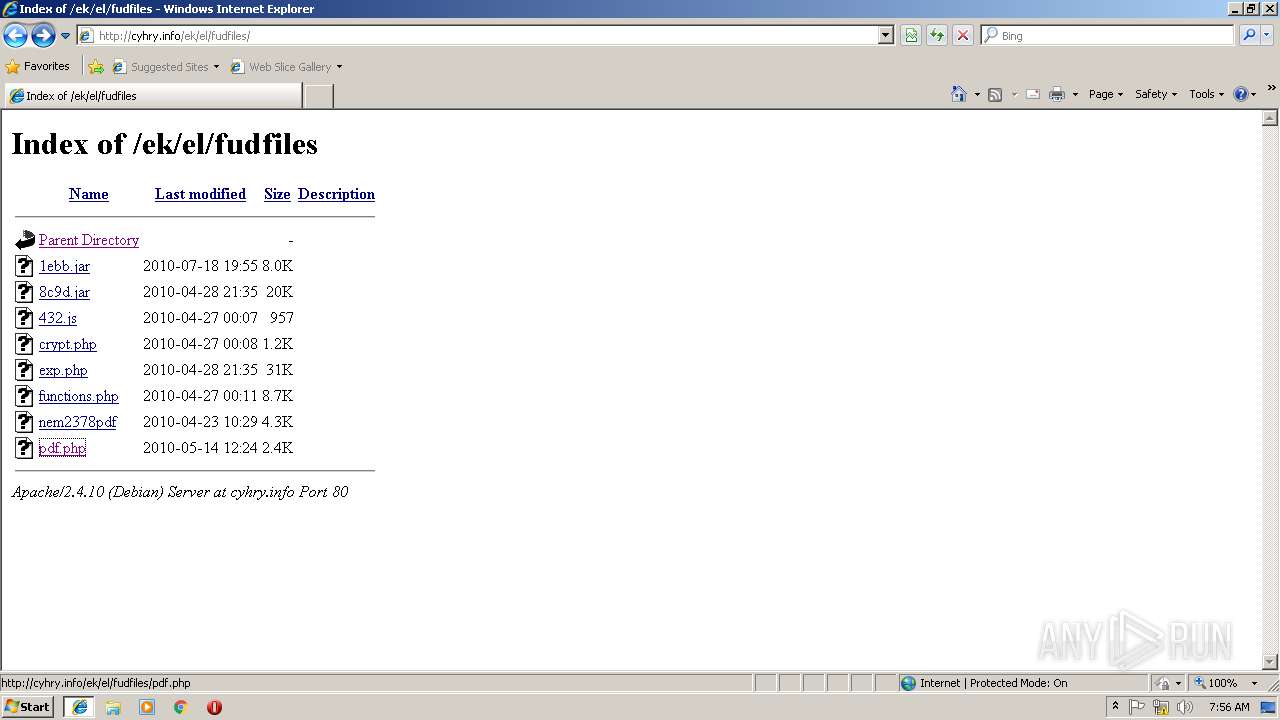
1864 | iexplore.exe | GET | 200 | 185.243.114.215:80 | http://cyhry.info/ek/el/el144/pdf.php | unknown | pdf | 13.3 Kb | suspicious |
3256 | AcroRd32.exe | GET | 304 | 2.16.186.33:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/282_15_23_20070.zip | unknown | — | — | whitelisted |
1864 | iexplore.exe | GET | 301 | 185.243.114.215:80 | http://cyhry.info/ek | unknown | html | 305 b | suspicious |
2832 | iexplore.exe | GET | 404 | 185.243.114.215:80 | http://cyhry.info/favicon.ico | unknown | html | 285 b | suspicious |
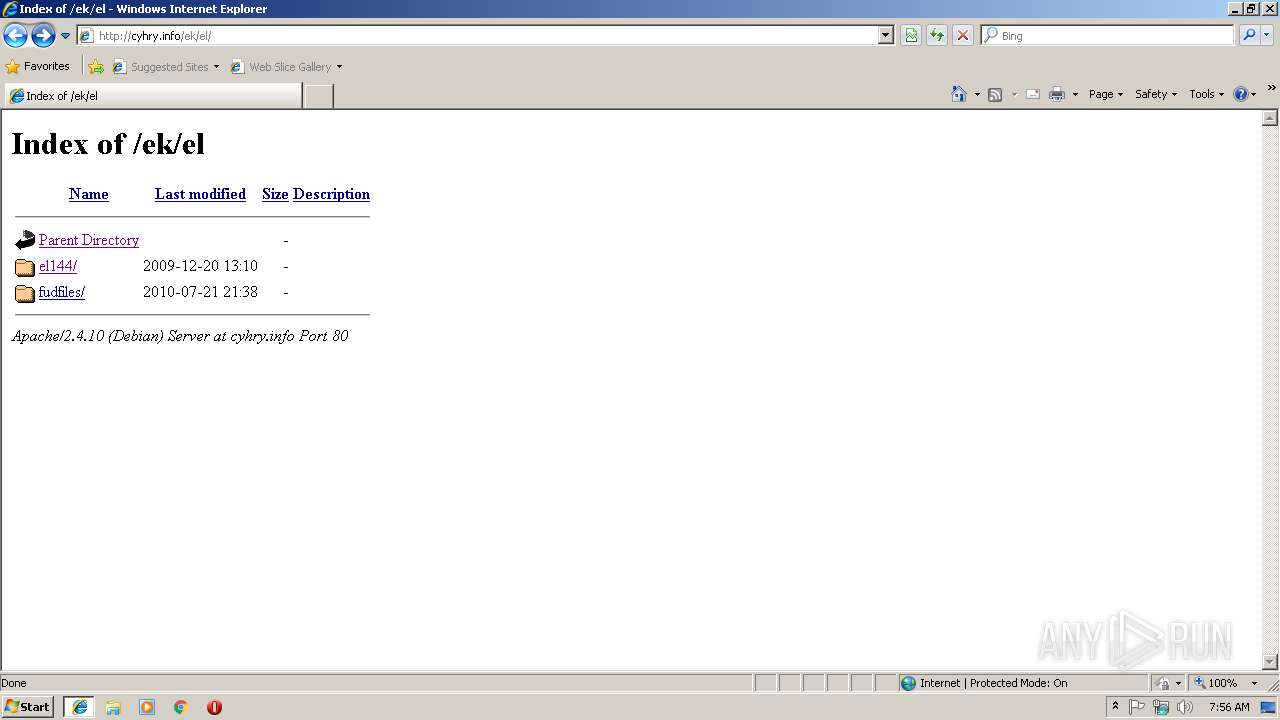
1864 | iexplore.exe | GET | 200 | 185.243.114.215:80 | http://cyhry.info/ek/el/ | unknown | html | 472 b | suspicious |
3256 | AcroRd32.exe | GET | 304 | 2.16.186.33:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/message.zip | unknown | — | — | whitelisted |
2724 | jp2launcher.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
1864 | iexplore.exe | GET | 200 | 185.243.114.215:80 | http://cyhry.info/ek/ | unknown | html | 437 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2832 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1864 | iexplore.exe | 185.243.114.215:80 | cyhry.info | — | — | suspicious |
2832 | iexplore.exe | 185.243.114.215:80 | cyhry.info | — | — | suspicious |
2724 | jp2launcher.exe | 185.243.114.215:80 | cyhry.info | — | — | suspicious |
3256 | AcroRd32.exe | 23.210.248.251:443 | armmf.adobe.com | Akamai International B.V. | NL | whitelisted |
2724 | jp2launcher.exe | 23.38.52.85:443 | javadl-esd-secure.oracle.com | Akamai International B.V. | NL | whitelisted |
2724 | jp2launcher.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2724 | jp2launcher.exe | 23.51.123.27:80 | s2.symcb.com | Akamai Technologies, Inc. | NL | whitelisted |
3256 | AcroRd32.exe | 2.16.186.33:80 | acroipm2.adobe.com | Akamai International B.V. | — | whitelisted |
1864 | iexplore.exe | 205.185.208.52:80 | code.jquery.com | Highwinds Network Group, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
cyhry.info |
| suspicious |
acroipm2.adobe.com |
| whitelisted |
armmf.adobe.com |
| whitelisted |
javadl-esd-secure.oracle.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
status.geotrust.com |
| whitelisted |
s2.symcb.com |
| whitelisted |
sv.symcd.com |
| shared |
code.jquery.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
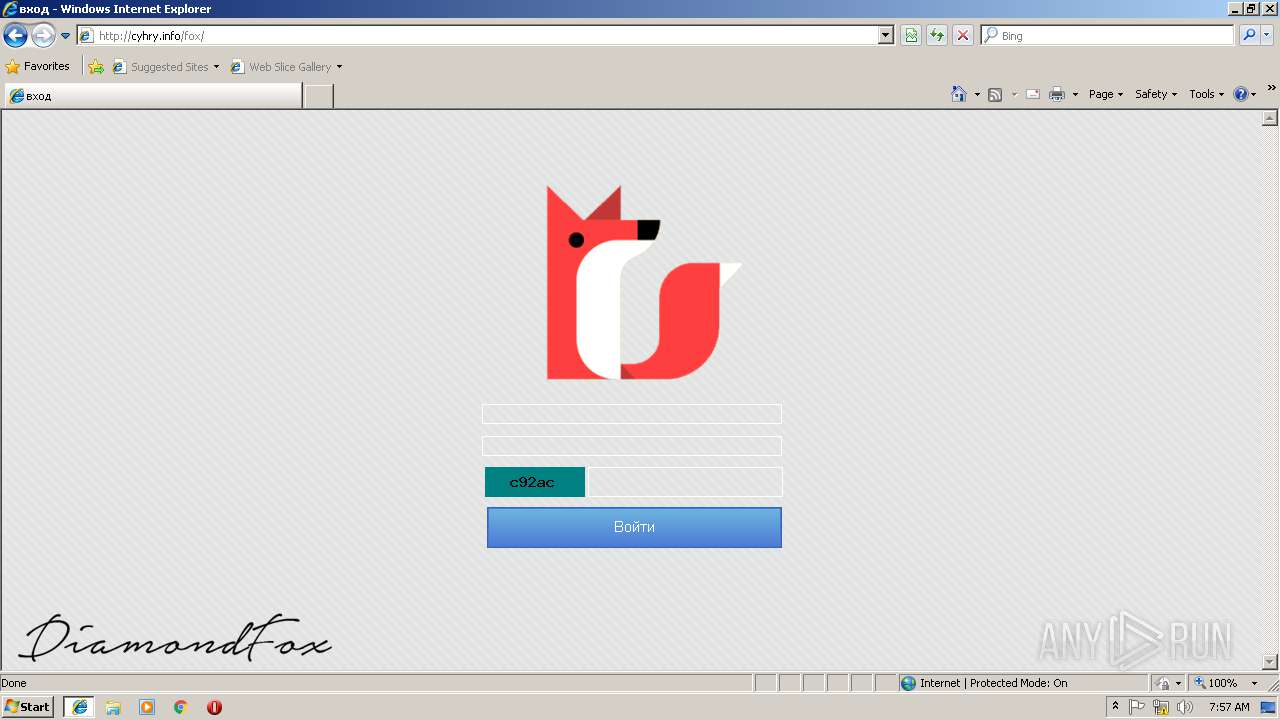
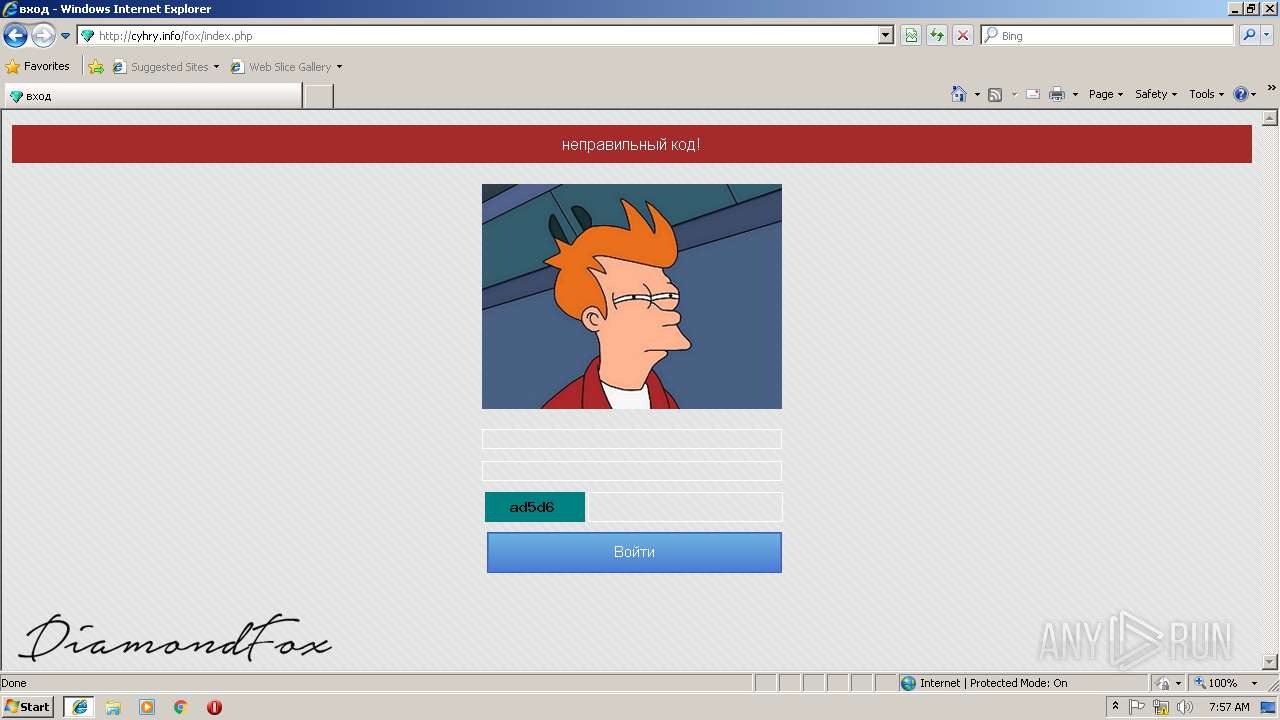
1864 | iexplore.exe | A Network Trojan was detected | ET CURRENT_EVENTS Base64 http argument in applet (Neutrino/Angler) |
2724 | jp2launcher.exe | Potentially Bad Traffic | ET POLICY Vulnerable Java Version 1.8.x Detected |
2724 | jp2launcher.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download By Vulnerable Client |
2724 | jp2launcher.exe | Potentially Bad Traffic | ET INFO JAR Size Under 30K Size - Potentially Hostile |
2724 | jp2launcher.exe | Potentially Bad Traffic | ET POLICY Vulnerable Java Version 1.8.x Detected |
1864 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains pass= in cleartext |
1 ETPRO signatures available at the full report