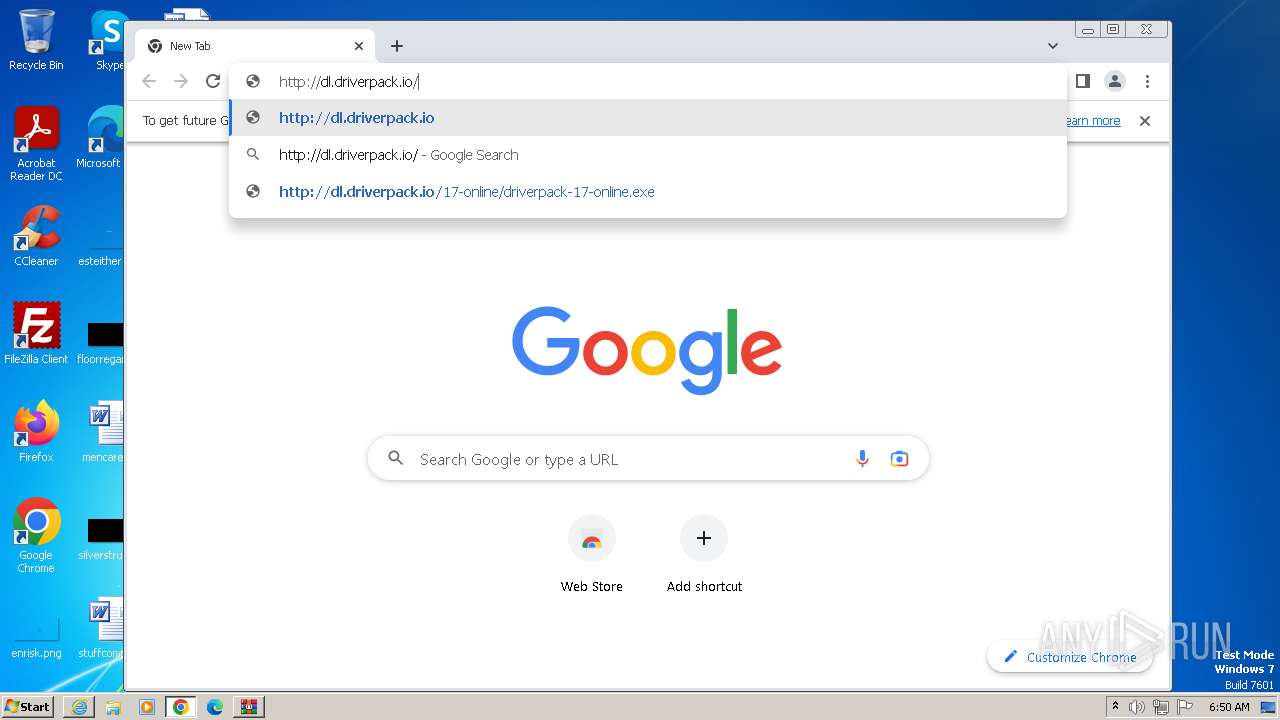
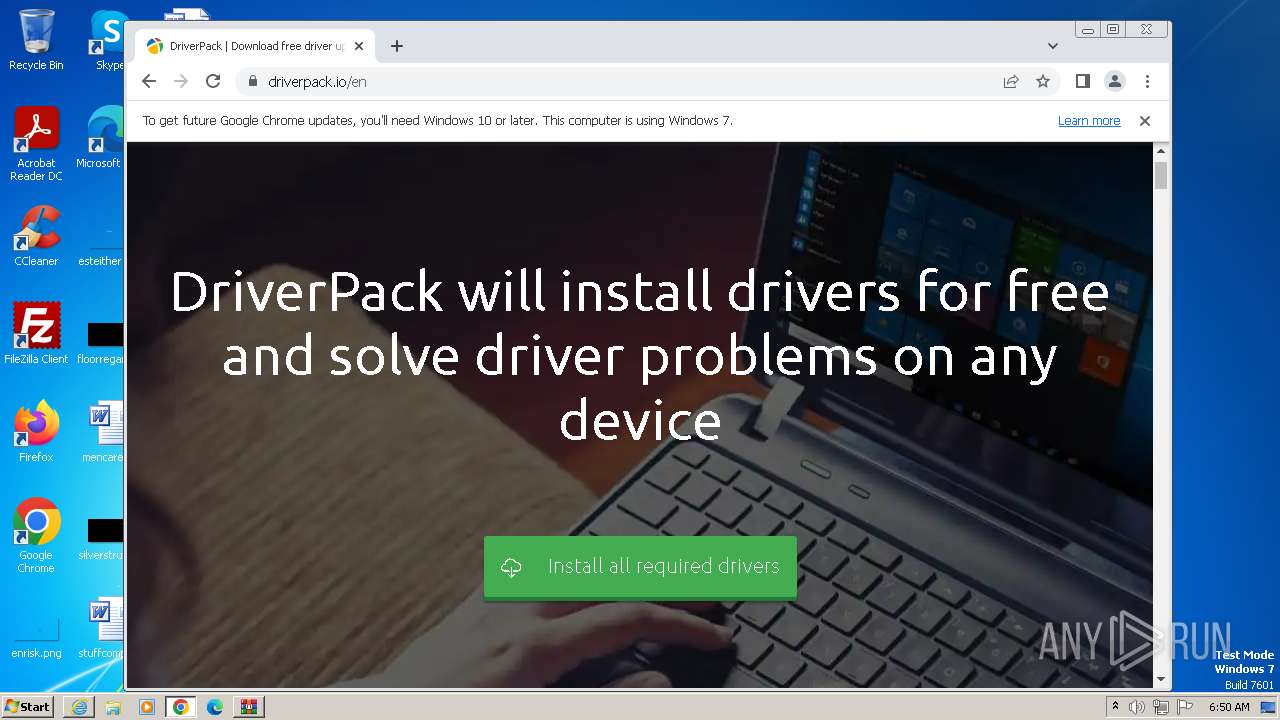
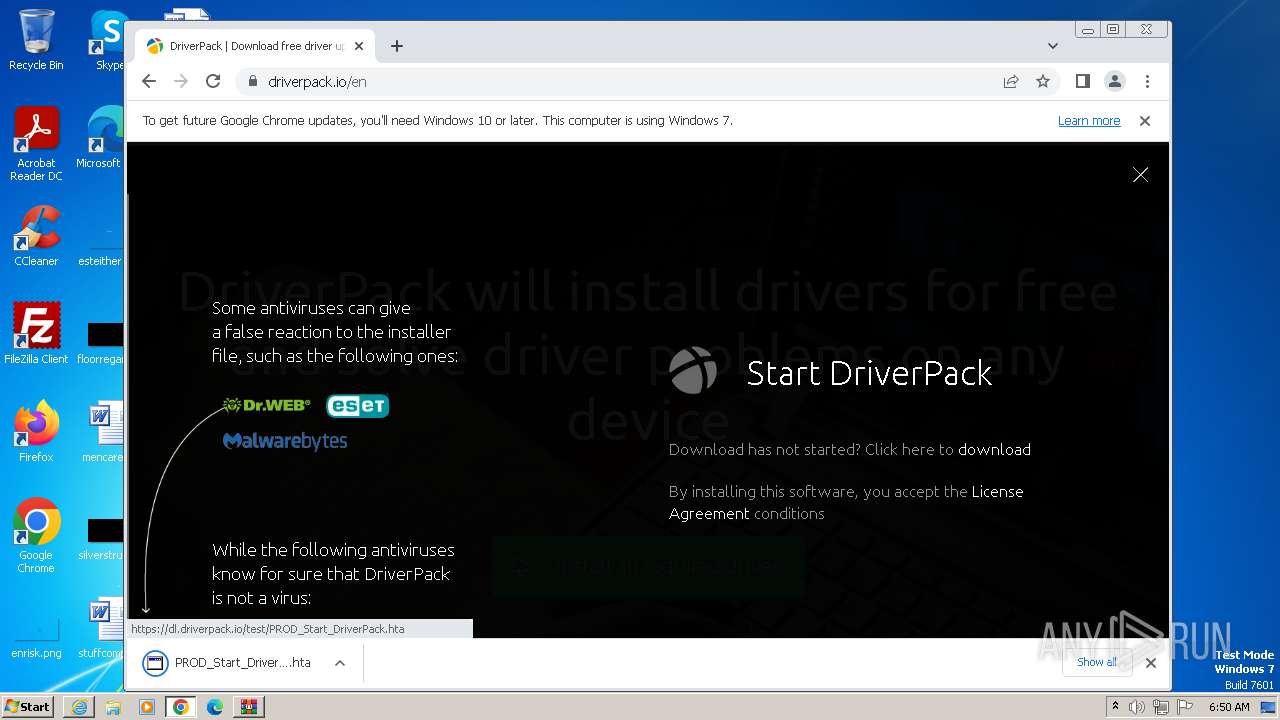
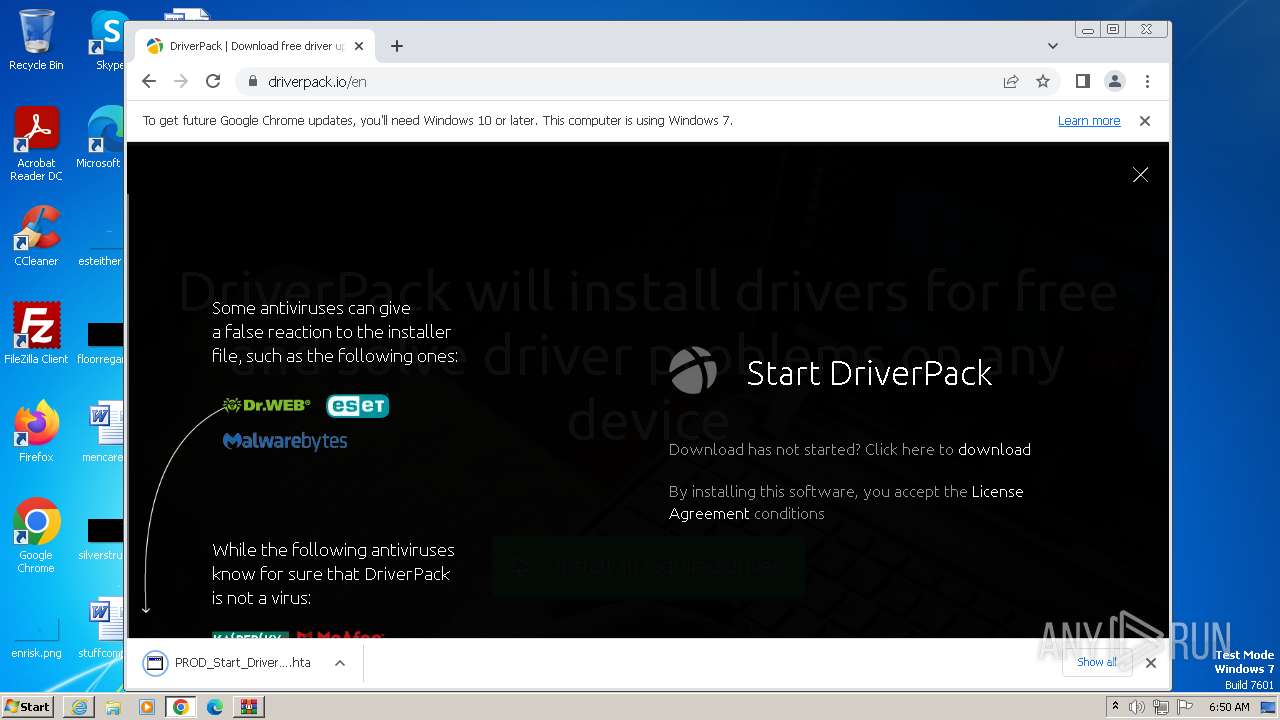
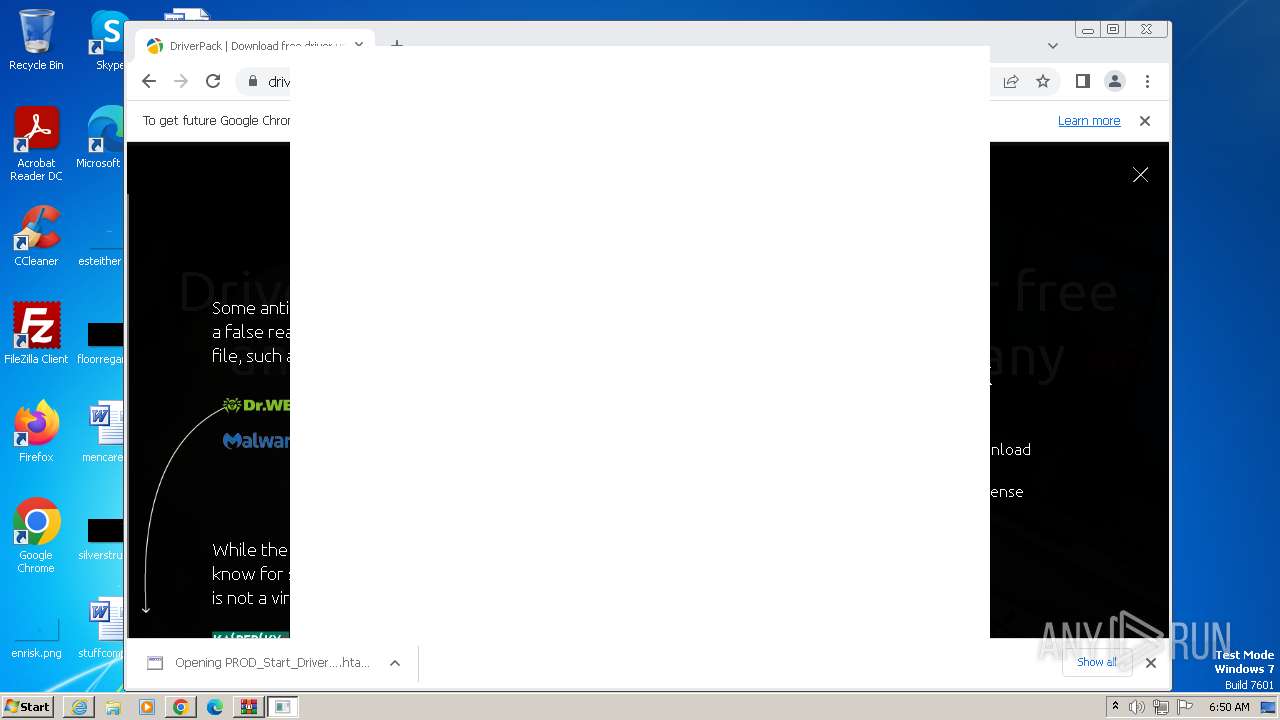
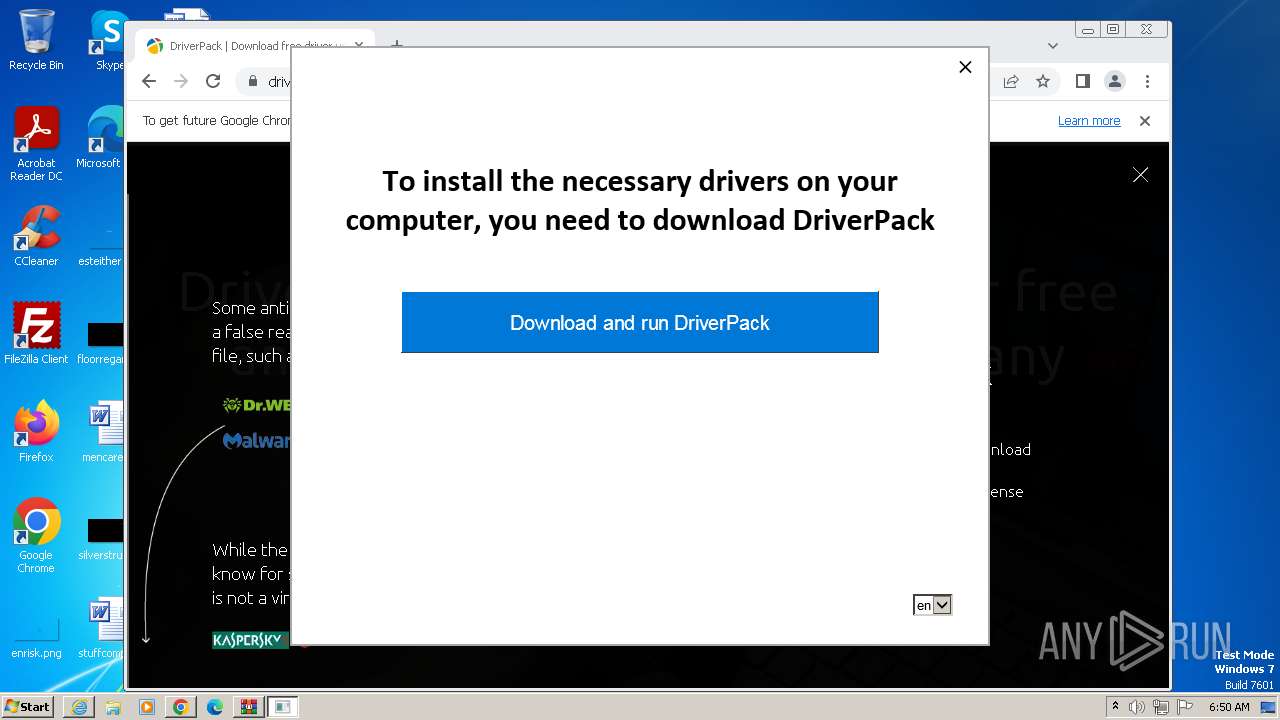
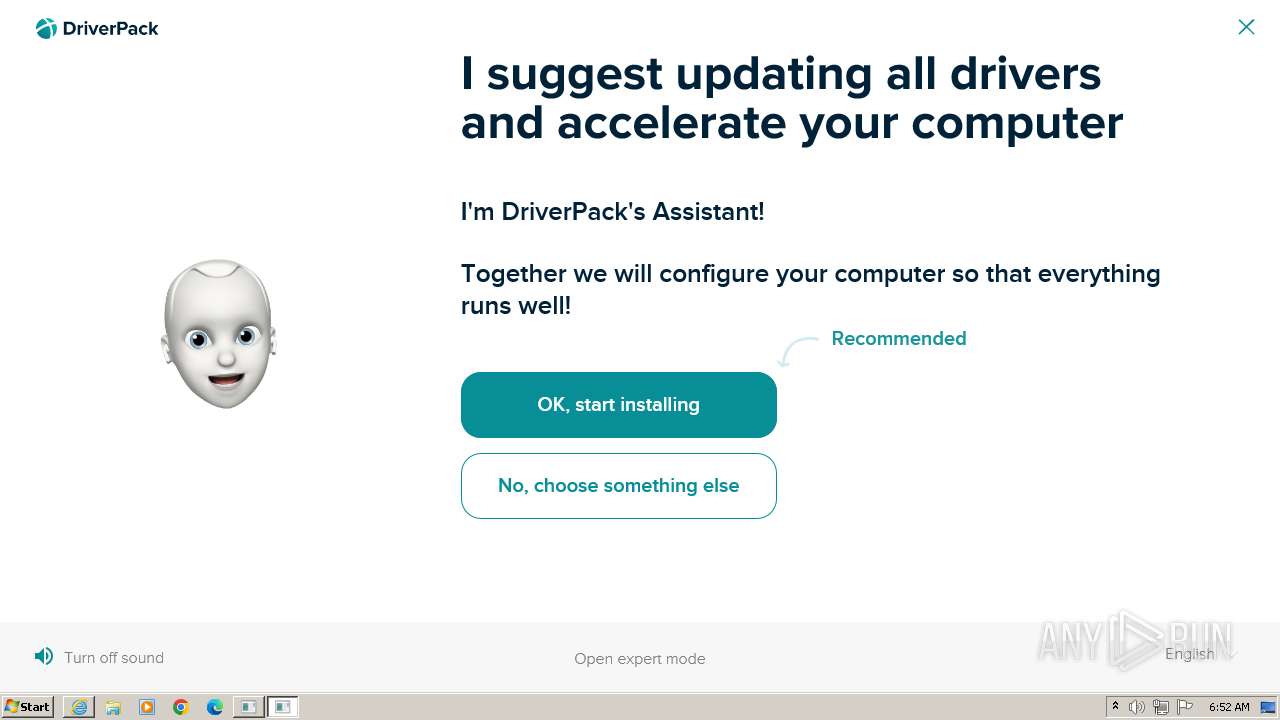
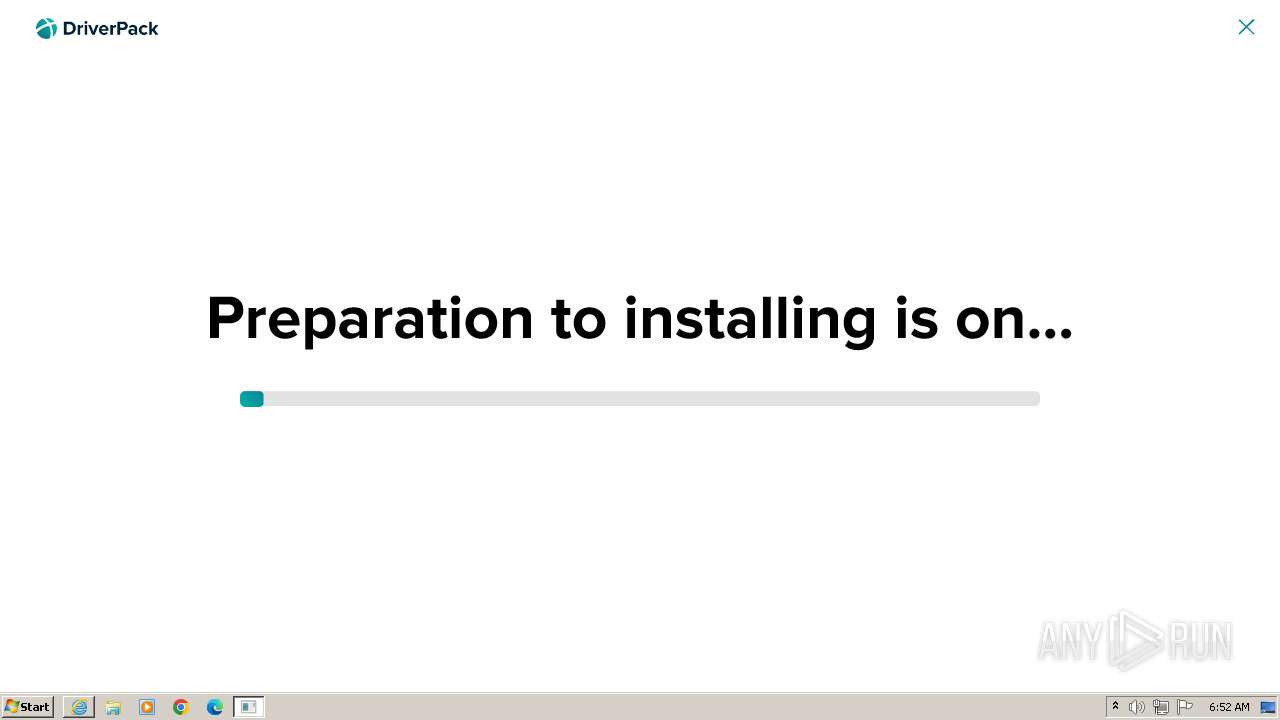
| URL: | dl.driverpack.io |
| Full analysis: | https://app.any.run/tasks/aeaadd3b-3832-4bf6-bec6-828ae1d33425 |
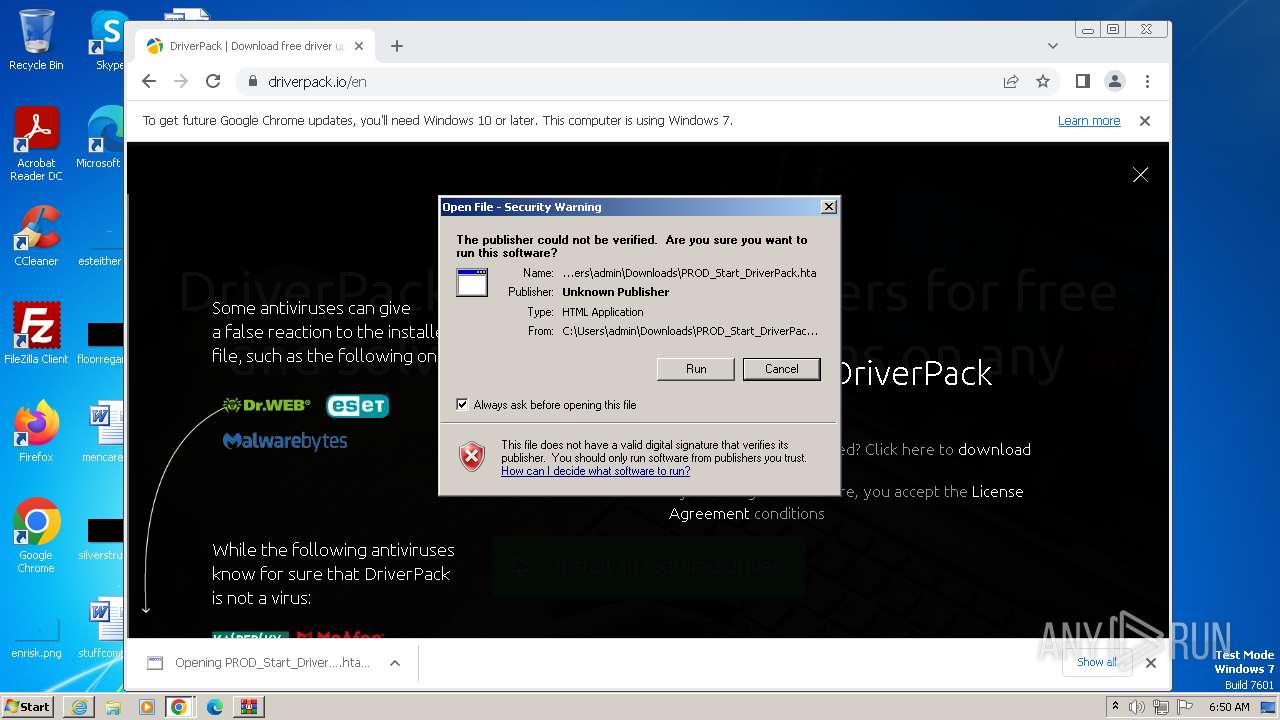
| Verdict: | Malicious activity |
| Analysis date: | October 27, 2023, 05:47:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 3B44F5F9A9A3EE35F425ADDAF8DF9135 |
| SHA1: | E8A04FF9D3EC7916D4204C7C6181235A0BA2E0EE |
| SHA256: | B5C71EF5C9F78307A4D74C45ED00F4C4857C44E2BB86D1183F85DB509000033F |
| SSDEEP: | 3:dXSAXJOLL:kAQH |
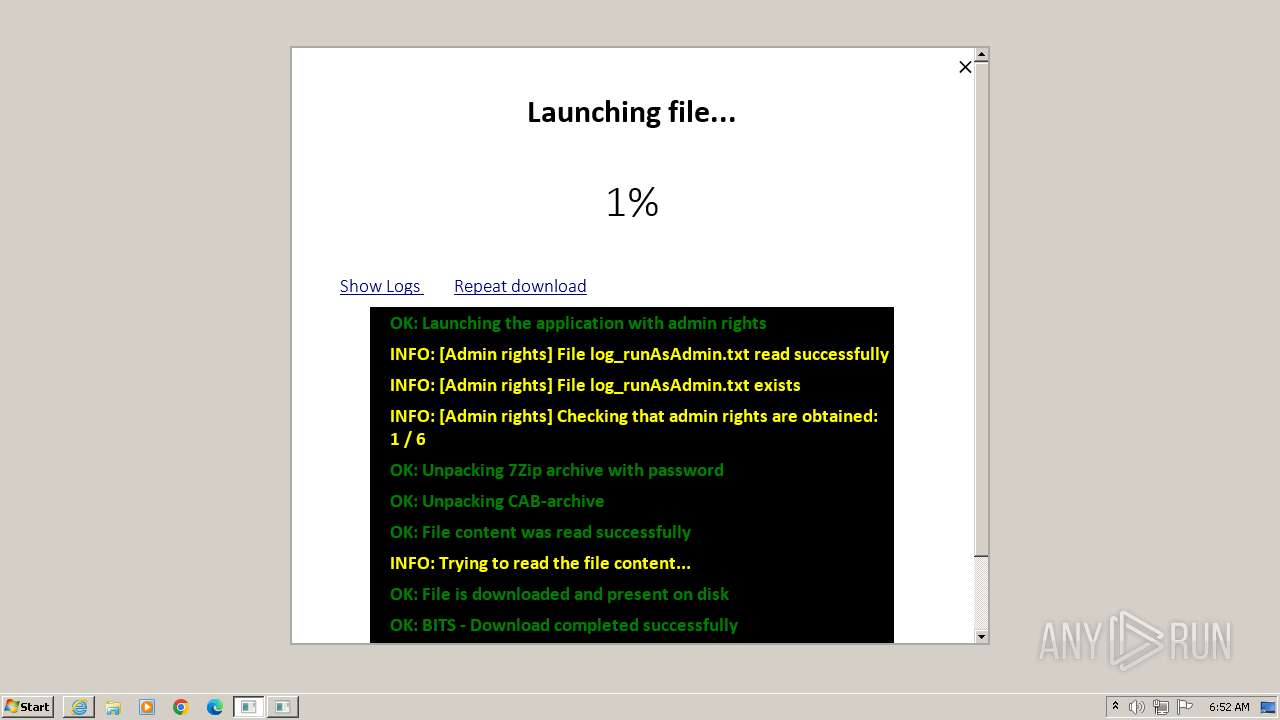
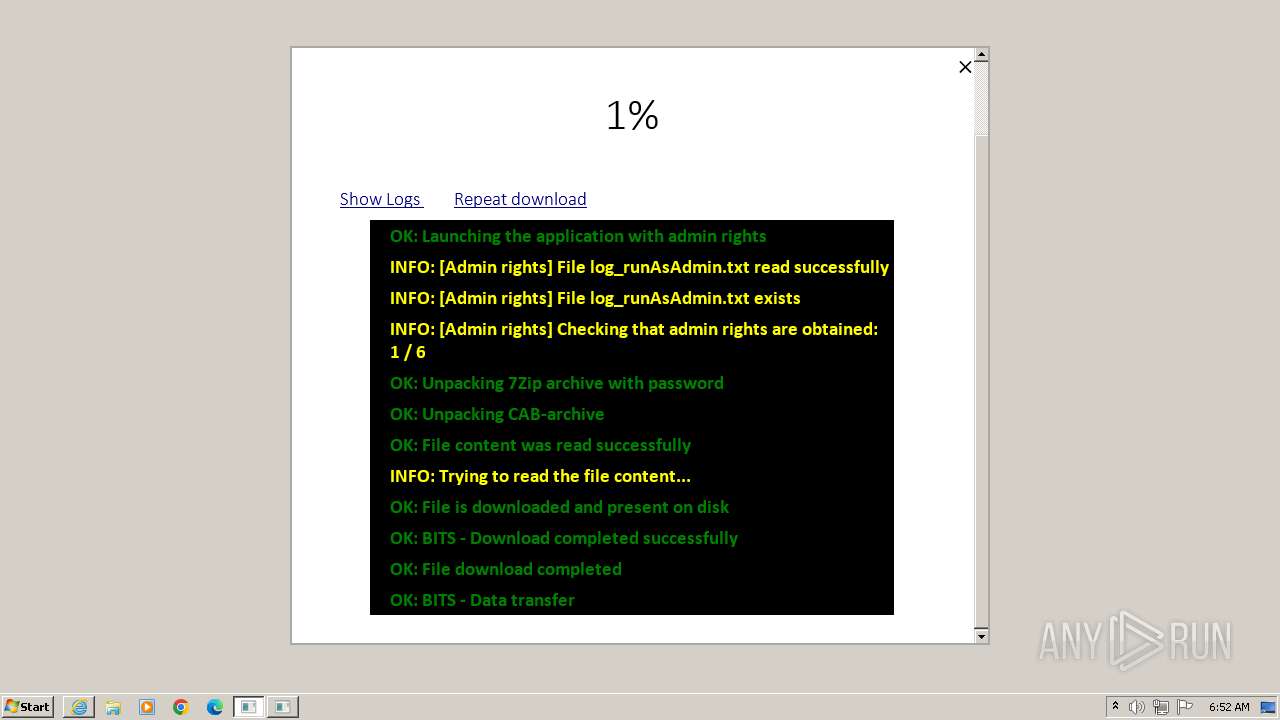
MALICIOUS
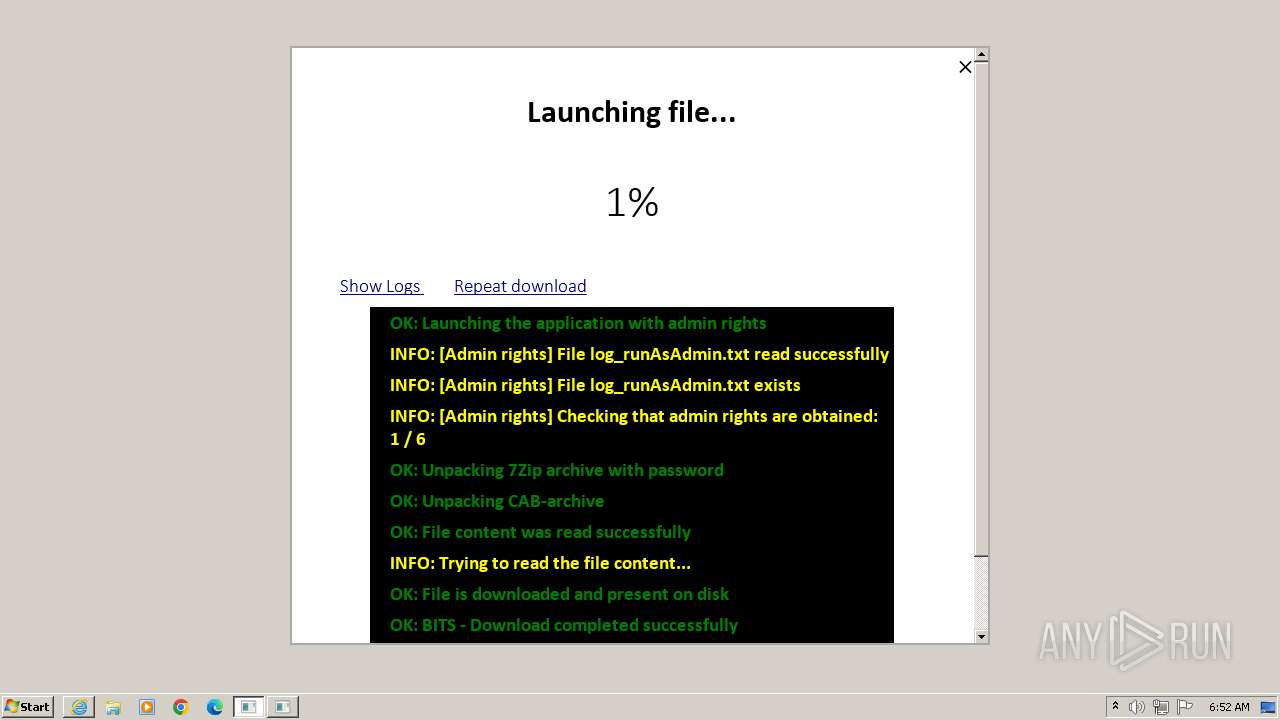
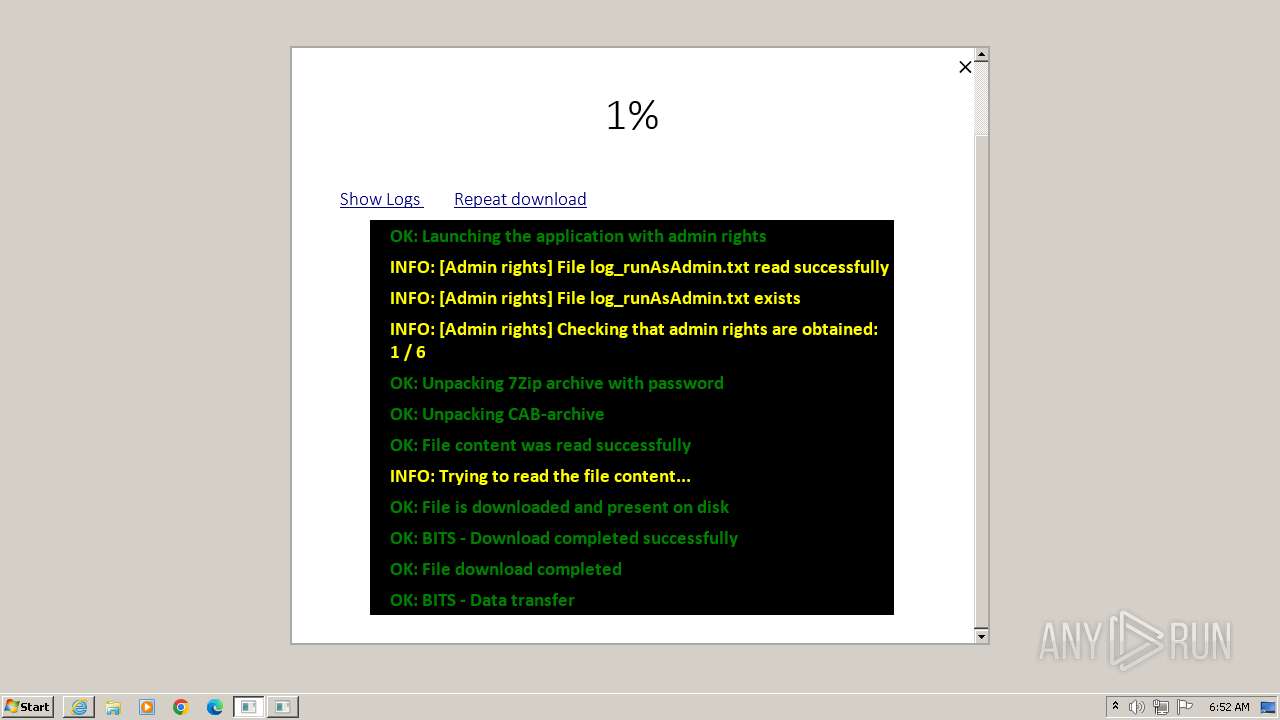
Downloads files via BITSADMIN.EXE
- cmd.exe (PID: 1904)
Application was dropped or rewritten from another process
- 7za.exe (PID: 3096)
- driverpack-wget.exe (PID: 2060)
- driverpack-wget.exe (PID: 1464)
- driverpack-wget.exe (PID: 3752)
- driverpack-wget.exe (PID: 2556)
- driverpack-wget.exe (PID: 3808)
- driverpack-wget.exe (PID: 2300)
- driverpack-wget.exe (PID: 2308)
- driverpack-wget.exe (PID: 3272)
- driverpack-wget.exe (PID: 3916)
- driverpack-wget.exe (PID: 2392)
- driverpack-wget.exe (PID: 3720)
- driverpack-wget.exe (PID: 528)
- driverpack-wget.exe (PID: 3992)
- driverpack-wget.exe (PID: 3660)
- driverpack-wget.exe (PID: 1036)
- driverpack-wget.exe (PID: 1808)
Drops the executable file immediately after the start
- 7za.exe (PID: 3096)
- csc.exe (PID: 4076)
Bypass execution policy to execute commands
- powershell.exe (PID: 3580)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 3712)
Starts Visual C# compiler
- powershell.exe (PID: 3580)
SUSPICIOUS
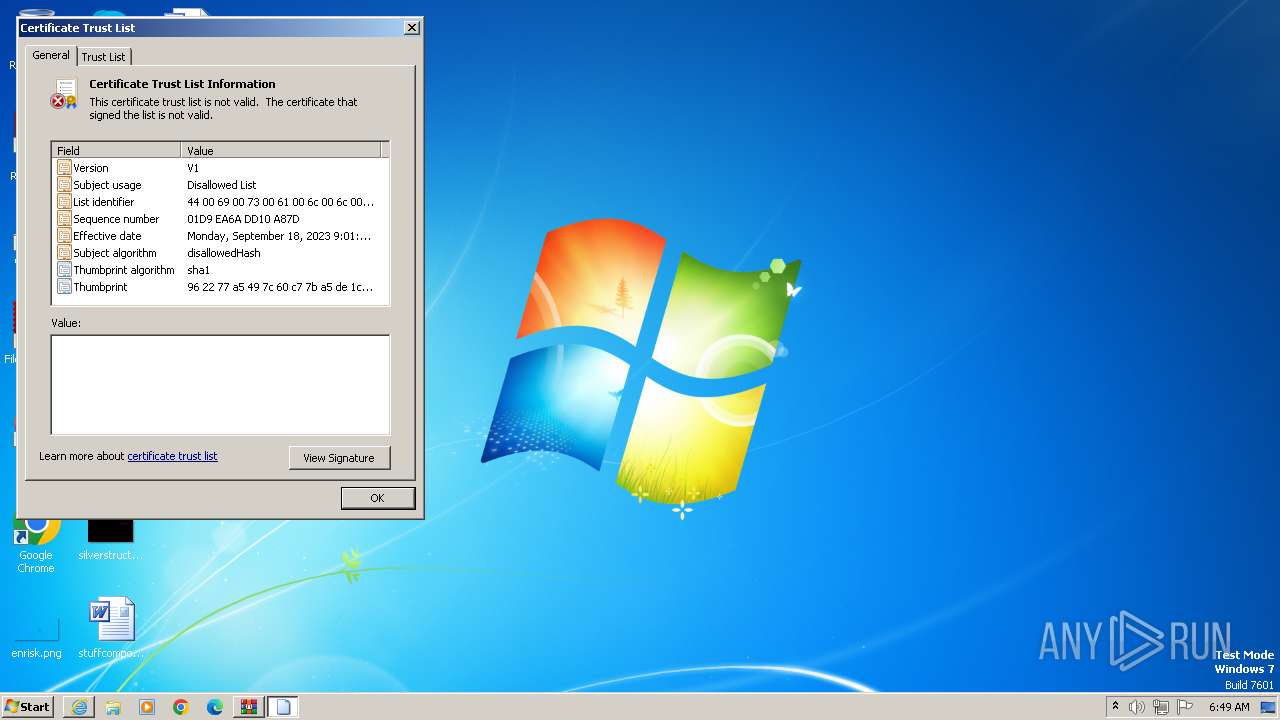
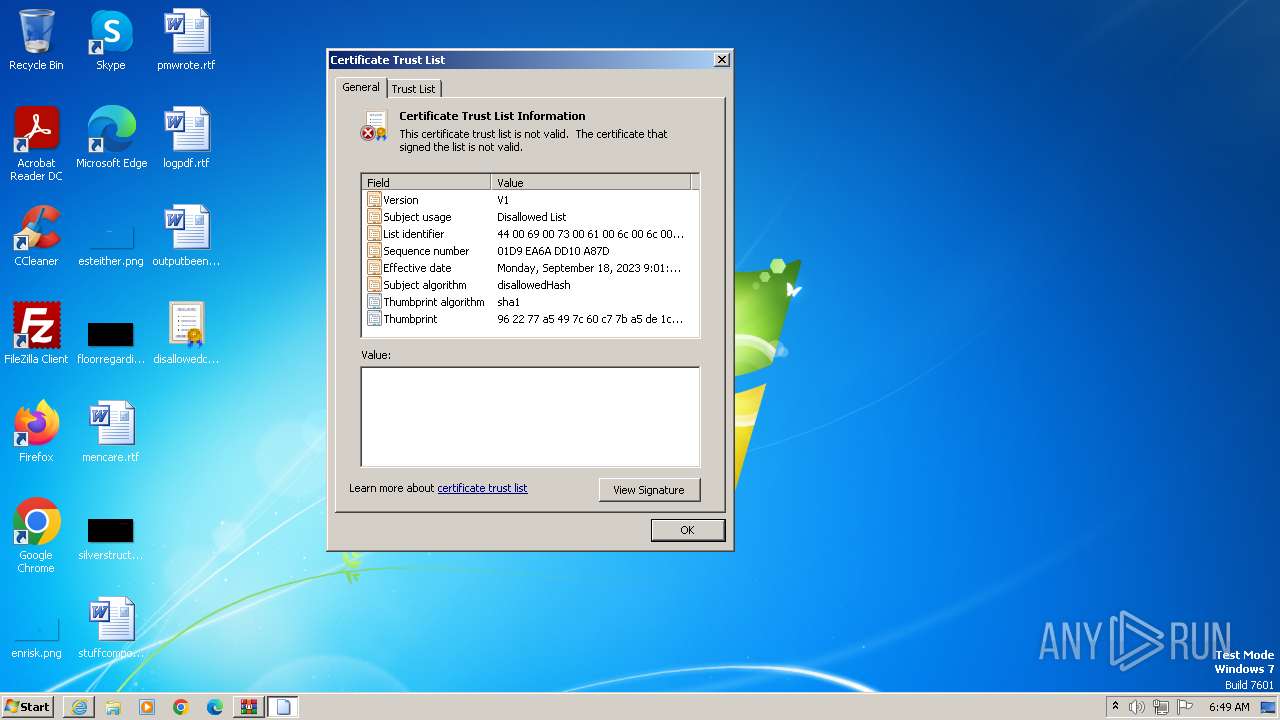
Reads settings of System Certificates
- rundll32.exe (PID: 3880)
- rundll32.exe (PID: 1648)
Uses RUNDLL32.EXE to load library
- WinRAR.exe (PID: 1332)
- mshta.exe (PID: 2992)
Reads the Internet Settings
- mshta.exe (PID: 2036)
- cmd.exe (PID: 664)
- mshta.exe (PID: 2992)
- mshta.exe (PID: 3056)
Starts CMD.EXE for commands execution
- mshta.exe (PID: 2036)
- cmd.exe (PID: 4072)
- mshta.exe (PID: 2992)
Process requests binary or script from the Internet
- mshta.exe (PID: 2036)
- mshta.exe (PID: 3056)
Found strings related to reading or modifying Windows Defender settings
- mshta.exe (PID: 2036)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 1904)
- cmd.exe (PID: 3996)
- cmd.exe (PID: 3664)
- cmd.exe (PID: 1896)
- cmd.exe (PID: 2448)
- cmd.exe (PID: 3888)
- cmd.exe (PID: 1884)
- cmd.exe (PID: 3188)
- cmd.exe (PID: 3752)
- cmd.exe (PID: 3900)
- cmd.exe (PID: 3544)
- cmd.exe (PID: 3796)
- cmd.exe (PID: 948)
Cmdlet gets the status of antimalware software installed on the computer
- cmd.exe (PID: 3076)
Query Microsoft Defender status
- mshta.exe (PID: 2036)
- cmd.exe (PID: 3076)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 3076)
- cmd.exe (PID: 3712)
Powershell version downgrade attack
- powershell.exe (PID: 2600)
- powershell.exe (PID: 3580)
Drops 7-zip archiver for unpacking
- expand.exe (PID: 2712)
- 7za.exe (PID: 3096)
Executing commands from a ".bat" file
- mshta.exe (PID: 2036)
- cmd.exe (PID: 4072)
Application launched itself
- cmd.exe (PID: 4072)
- mshta.exe (PID: 2036)
Process drops legitimate windows executable
- 7za.exe (PID: 3096)
Executing commands from ".cmd" file
- mshta.exe (PID: 2992)
The process hides Powershell's copyright startup banner
- cmd.exe (PID: 3712)
Get information on the list of running processes
- cmd.exe (PID: 3712)
The process hide an interactive prompt from the user
- cmd.exe (PID: 3712)
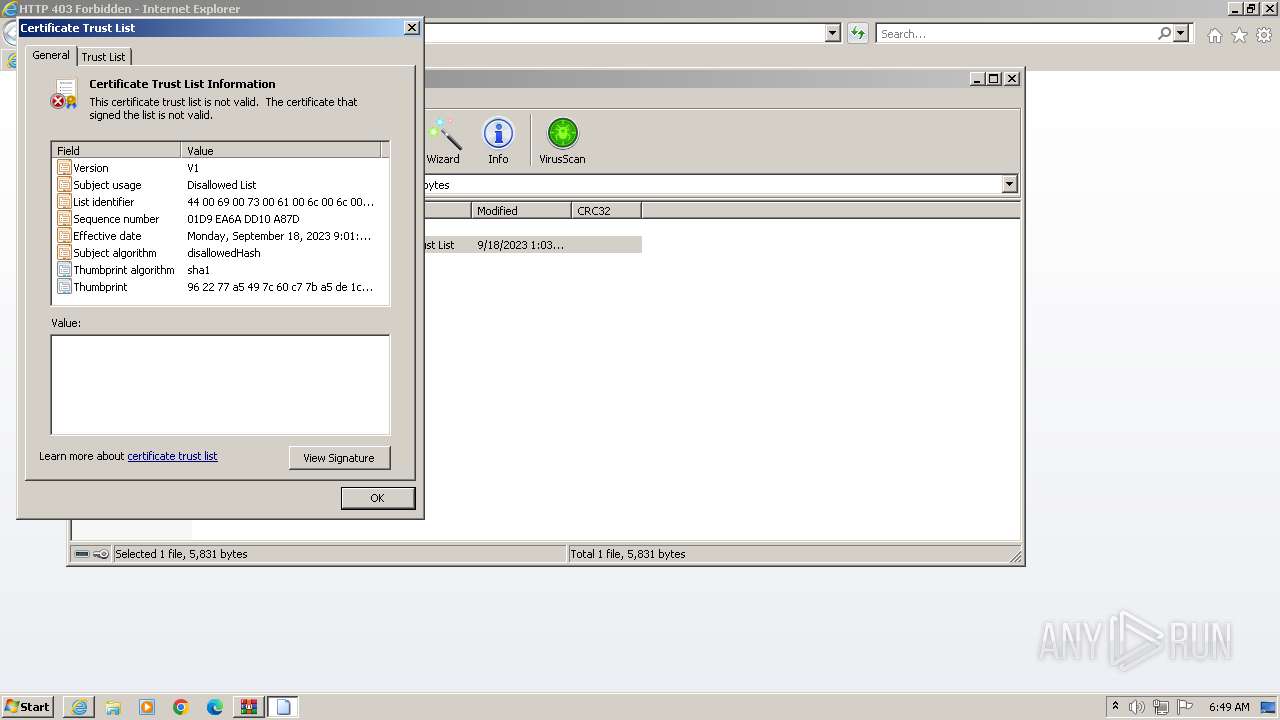
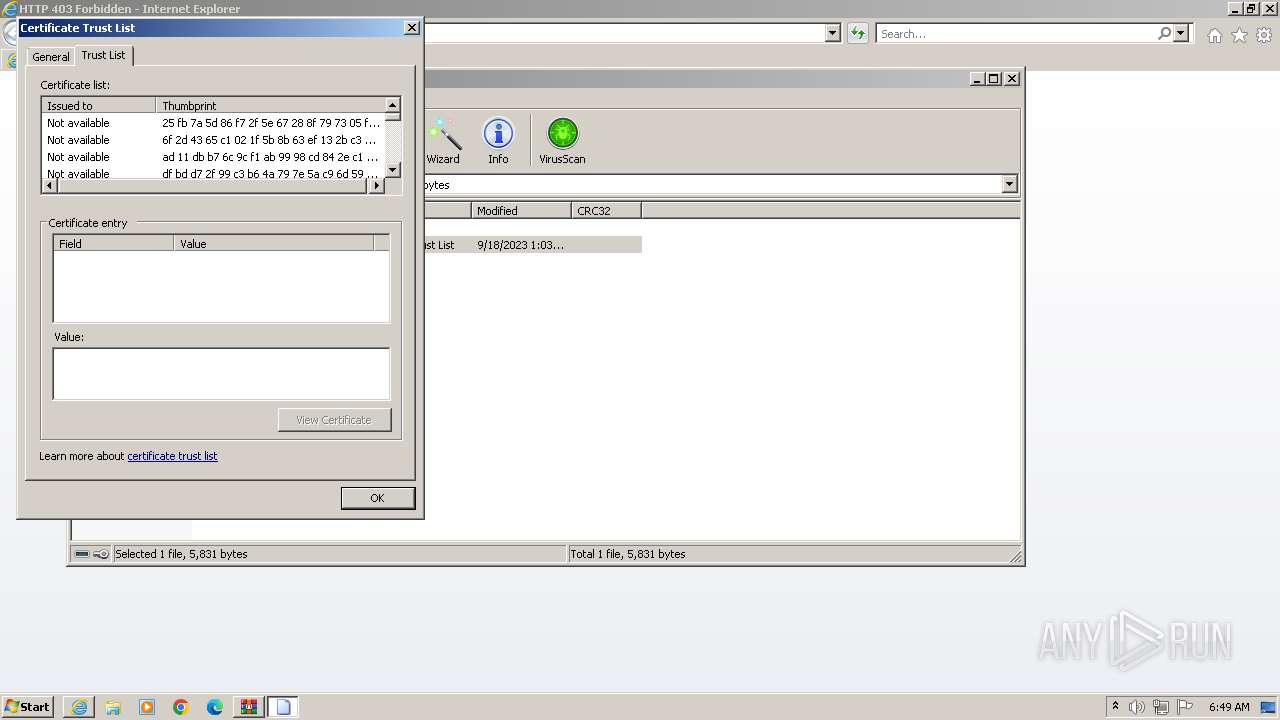
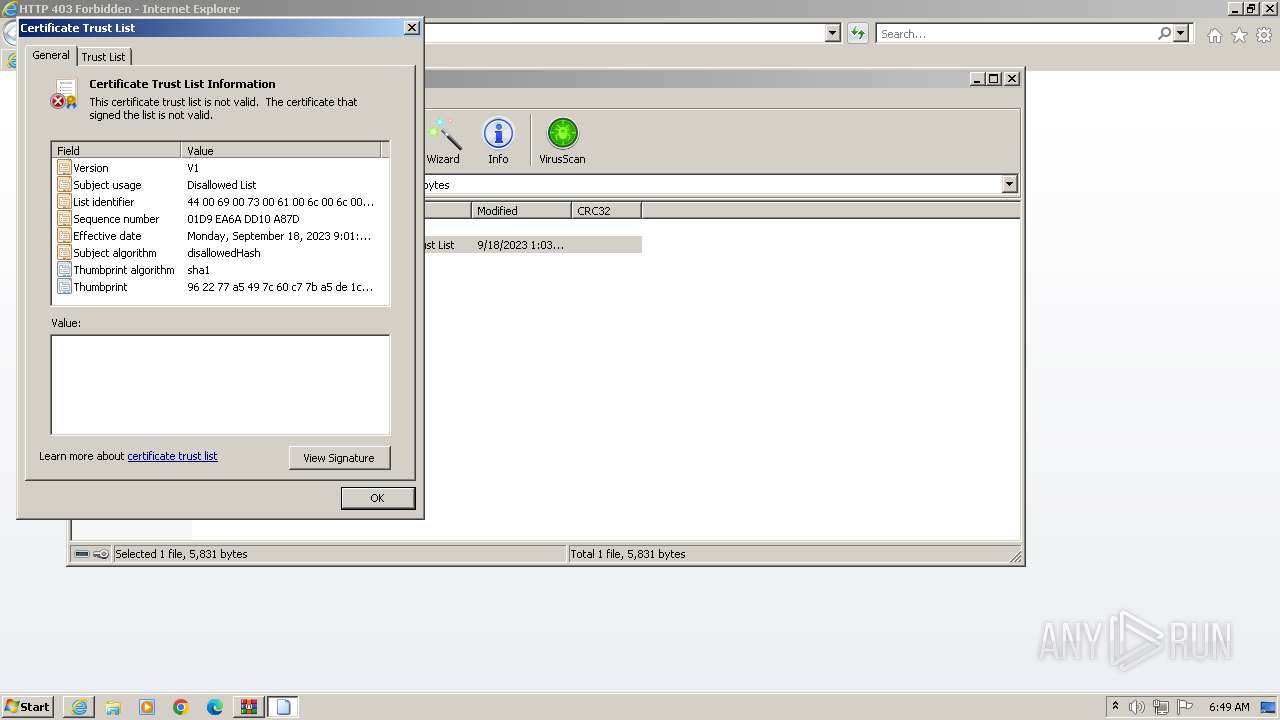
Adds/modifies Windows certificates
- cmd.exe (PID: 664)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- cmd.exe (PID: 3232)
Uses .NET C# to load dll
- powershell.exe (PID: 3580)
Changes internet zones settings
- mshta.exe (PID: 2992)
Uses NETSH.EXE to add a firewall rule or allowed programs
- cmd.exe (PID: 3192)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 3712)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 3712)
INFO
Application launched itself
- iexplore.exe (PID: 852)
- chrome.exe (PID: 2404)
Reads security settings of Internet Explorer
- rundll32.exe (PID: 3880)
- rundll32.exe (PID: 1648)
The process uses the downloaded file
- iexplore.exe (PID: 852)
- WinRAR.exe (PID: 1332)
- chrome.exe (PID: 3328)
- chrome.exe (PID: 3816)
- chrome.exe (PID: 2744)
- chrome.exe (PID: 3336)
- chrome.exe (PID: 2404)
- mshta.exe (PID: 2036)
Manual execution by a user
- chrome.exe (PID: 2404)
- rundll32.exe (PID: 1648)
- wmpnscfg.exe (PID: 4056)
Reads Internet Explorer settings
- mshta.exe (PID: 2036)
- mshta.exe (PID: 2992)
- mshta.exe (PID: 3056)
Checks proxy server information
- mshta.exe (PID: 2036)
- mshta.exe (PID: 2992)
- mshta.exe (PID: 3056)
Uses BITSADMIN.EXE
- cmd.exe (PID: 3664)
- cmd.exe (PID: 3996)
- cmd.exe (PID: 1896)
- cmd.exe (PID: 3888)
- cmd.exe (PID: 2448)
- cmd.exe (PID: 1884)
- cmd.exe (PID: 3188)
- cmd.exe (PID: 3900)
- cmd.exe (PID: 3544)
- cmd.exe (PID: 948)
- cmd.exe (PID: 3752)
- cmd.exe (PID: 3796)
Create files in a temporary directory
- expand.exe (PID: 2712)
- 7za.exe (PID: 3096)
- csc.exe (PID: 4076)
- cvtres.exe (PID: 3316)
- driverpack-wget.exe (PID: 2060)
- driverpack-wget.exe (PID: 2556)
- driverpack-wget.exe (PID: 3752)
- driverpack-wget.exe (PID: 1464)
- driverpack-wget.exe (PID: 3916)
- driverpack-wget.exe (PID: 2392)
- driverpack-wget.exe (PID: 528)
- driverpack-wget.exe (PID: 3272)
- driverpack-wget.exe (PID: 3808)
- driverpack-wget.exe (PID: 2300)
- driverpack-wget.exe (PID: 3720)
- driverpack-wget.exe (PID: 2308)
- driverpack-wget.exe (PID: 1808)
- driverpack-wget.exe (PID: 1036)
- driverpack-wget.exe (PID: 3992)
- driverpack-wget.exe (PID: 3660)
Drops the executable file immediately after the start
- expand.exe (PID: 2712)
Checks supported languages
- 7za.exe (PID: 3096)
- wmpnscfg.exe (PID: 4056)
- csc.exe (PID: 4076)
- cvtres.exe (PID: 3316)
- driverpack-wget.exe (PID: 1464)
- driverpack-wget.exe (PID: 2060)
- driverpack-wget.exe (PID: 3752)
- driverpack-wget.exe (PID: 2556)
- driverpack-wget.exe (PID: 3808)
- driverpack-wget.exe (PID: 2308)
- driverpack-wget.exe (PID: 2300)
- driverpack-wget.exe (PID: 3916)
- driverpack-wget.exe (PID: 2392)
- driverpack-wget.exe (PID: 528)
- driverpack-wget.exe (PID: 3272)
- driverpack-wget.exe (PID: 3720)
- driverpack-wget.exe (PID: 3660)
- driverpack-wget.exe (PID: 1808)
- driverpack-wget.exe (PID: 1036)
- driverpack-wget.exe (PID: 3992)
The executable file from the user directory is run by the CMD process
- 7za.exe (PID: 3096)
- driverpack-wget.exe (PID: 1464)
- driverpack-wget.exe (PID: 2060)
- driverpack-wget.exe (PID: 3752)
- driverpack-wget.exe (PID: 2556)
- driverpack-wget.exe (PID: 3808)
- driverpack-wget.exe (PID: 2308)
- driverpack-wget.exe (PID: 3916)
- driverpack-wget.exe (PID: 3272)
- driverpack-wget.exe (PID: 2300)
- driverpack-wget.exe (PID: 2392)
- driverpack-wget.exe (PID: 528)
- driverpack-wget.exe (PID: 3720)
- driverpack-wget.exe (PID: 3992)
- driverpack-wget.exe (PID: 1036)
- driverpack-wget.exe (PID: 3660)
- driverpack-wget.exe (PID: 1808)
Reads the computer name
- 7za.exe (PID: 3096)
- wmpnscfg.exe (PID: 4056)
- driverpack-wget.exe (PID: 1464)
- driverpack-wget.exe (PID: 2060)
- driverpack-wget.exe (PID: 3752)
- driverpack-wget.exe (PID: 2556)
- driverpack-wget.exe (PID: 3808)
- driverpack-wget.exe (PID: 2300)
- driverpack-wget.exe (PID: 2308)
- driverpack-wget.exe (PID: 3916)
- driverpack-wget.exe (PID: 528)
- driverpack-wget.exe (PID: 2392)
- driverpack-wget.exe (PID: 3272)
- driverpack-wget.exe (PID: 3720)
- driverpack-wget.exe (PID: 3660)
- driverpack-wget.exe (PID: 1808)
- driverpack-wget.exe (PID: 3992)
- driverpack-wget.exe (PID: 1036)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 4056)
- csc.exe (PID: 4076)
- cvtres.exe (PID: 3316)
Creates files or folders in the user directory
- driverpack-wget.exe (PID: 1464)
- driverpack-wget.exe (PID: 3752)
- driverpack-wget.exe (PID: 2060)
- driverpack-wget.exe (PID: 2556)
- driverpack-wget.exe (PID: 3808)
- driverpack-wget.exe (PID: 2308)
- driverpack-wget.exe (PID: 3916)
- driverpack-wget.exe (PID: 2300)
- driverpack-wget.exe (PID: 3720)
- driverpack-wget.exe (PID: 2392)
- driverpack-wget.exe (PID: 3272)
- driverpack-wget.exe (PID: 528)
- driverpack-wget.exe (PID: 3660)
- driverpack-wget.exe (PID: 1036)
- driverpack-wget.exe (PID: 1808)
- driverpack-wget.exe (PID: 3992)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
226
Monitored processes
139
Malicious processes
27
Suspicious processes
16
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | findstr /R /V "^f7f81a39-5f63-5b42-9efd-1f13b5431005quot; | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 120 | findstr /R /V "^f7f81a39-5f63-5b42-9efd-1f13b5431005quot; | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 124 | findstr /R /V "^f7f81a39-5f63-5b42-9efd-1f13b5431005quot; | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --first-renderer-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2032 --field-trial-handle=1152,i,485190327272287705,4754992489620500328,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=4112 --field-trial-handle=1152,i,485190327272287705,4754992489620500328,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 528 | "C:\Windows\System32\cmd.exe" /c ""tools\driverpack-wget.exe" --tries=3 --timeout 5 --retry-connrefused --wait=5 --timestamping --directory-prefix="C:\Users\admin\AppData\Local\Temp\beetle-cab\DriverPack\audio\en" "http://dl.driverpack.io/assistant/beetle/audio/en/intro.mp3" -o "C:\Users\admin\AppData\Roaming\DRPSu\temp\wget_log_43282.log" & echo DONE > "C:\Users\admin\AppData\Roaming\DRPSu\temp\wget_finished_43282.txt"" | C:\Windows\System32\cmd.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 528 | "tools\driverpack-wget.exe" --tries=3 --timeout 5 --retry-connrefused --wait=5 --timestamping --directory-prefix="C:\Users\admin\AppData\Local\Temp\beetle-cab\DriverPack\audio\en" "http://dl.driverpack.io/assistant/beetle/audio/en/TEAM-PROOF-1.mp3" -o "C:\Users\admin\AppData\Roaming\DRPSu\temp\wget_log_52305.log" | C:\Users\admin\AppData\Local\Temp\beetle-cab\DriverPack\Tools\driverpack-wget.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 568 | "C:\Windows\System32\cmd.exe" /c ""tools\driverpack-wget.exe" --tries=3 --timeout 5 --retry-connrefused --wait=5 --timestamping --directory-prefix="C:\Users\admin\AppData\Local\Temp\beetle-cab\DriverPack\audio\en" "http://dl.driverpack.io/assistant/beetle/audio/en/ANTIVIRUS-3.mp3" -o "C:\Users\admin\AppData\Roaming\DRPSu\temp\wget_log_90387.log" & echo DONE > "C:\Users\admin\AppData\Roaming\DRPSu\temp\wget_finished_90387.txt"" | C:\Windows\System32\cmd.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3984 --field-trial-handle=1152,i,485190327272287705,4754992489620500328,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 612 | bitsadmin /info dwnl-task-68346 | C:\Windows\System32\bitsadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: BITS administration utility Exit code: 0 Version: 7.5.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
45 493
Read events
44 782
Write events
705
Delete events
6
Modification events
| (PID) Process: | (852) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (852) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (852) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (852) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (852) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (852) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (852) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (852) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000056010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (852) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (852) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
15
Suspicious files
337
Text files
642
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3968 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\BA429MS2.txt | text | |
MD5:756AEABA2BD976D035C66E3CE66C27A0 | SHA256:C6714545E0D2F55B56381135D21584E32109545297178C3C219CD4D925FEF969 | |||
| 852 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:758CEA855C6382E0D292A1DA032299E7 | SHA256:52CB58C0153F0AF8AF5E5D89D77724E570DD0AFA48B31570D8337C4A00DD5BFF | |||
| 852 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 3968 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\GF72U7JC.txt | text | |
MD5:D31008CEF1D4D5A5054CBCD2E53C61C4 | SHA256:52F8F5A5B2E020424F1B37E14CC1E76C7D4ABD502C25EAF8184B8E87FA7D58E5 | |||
| 3968 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\BW2K5JY3.txt | text | |
MD5:119F44ECF9B226B36F0F49799A14272B | SHA256:E5644737BDE72A566301E06B689A0E334CF06CB6688AD7F3DA8F93993AA7A38C | |||
| 852 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EAF8AA29A62AB29E614331747385D816_F9E4DC0B9D5C777357D7DB8DEF51118A | binary | |
MD5:009986CF548A10670B9D21011E5B1F84 | SHA256:7ADBA08720904F8261C91EA889B5DB84D544CB313F444343D7840AE69FF00D28 | |||
| 852 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 852 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\ver2EBA.tmp | xml | |
MD5:CBD0581678FA40F0EDCBC7C59E0CAD10 | SHA256:159BD4343F344A08F6AF3B716B6FA679859C1BD1D7030D26FF5EF0255B86E1D9 | |||
| 852 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 852 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:A05EDA71D853955B6C049D391795EDA6 | SHA256:63450F694B15F27A76B47D1F13A295AACE1FEE4F034EDFE43E55B88424DB0A64 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
188
TCP/UDP connections
137
DNS requests
99
Threats
77
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
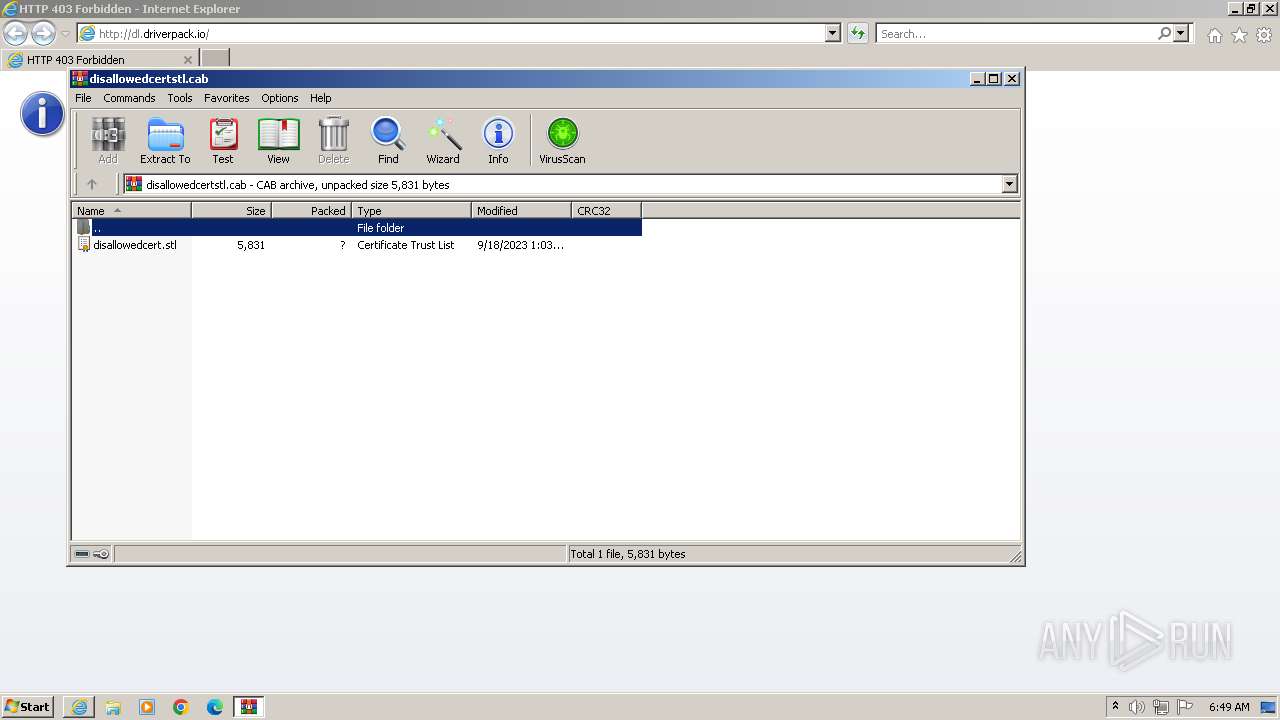
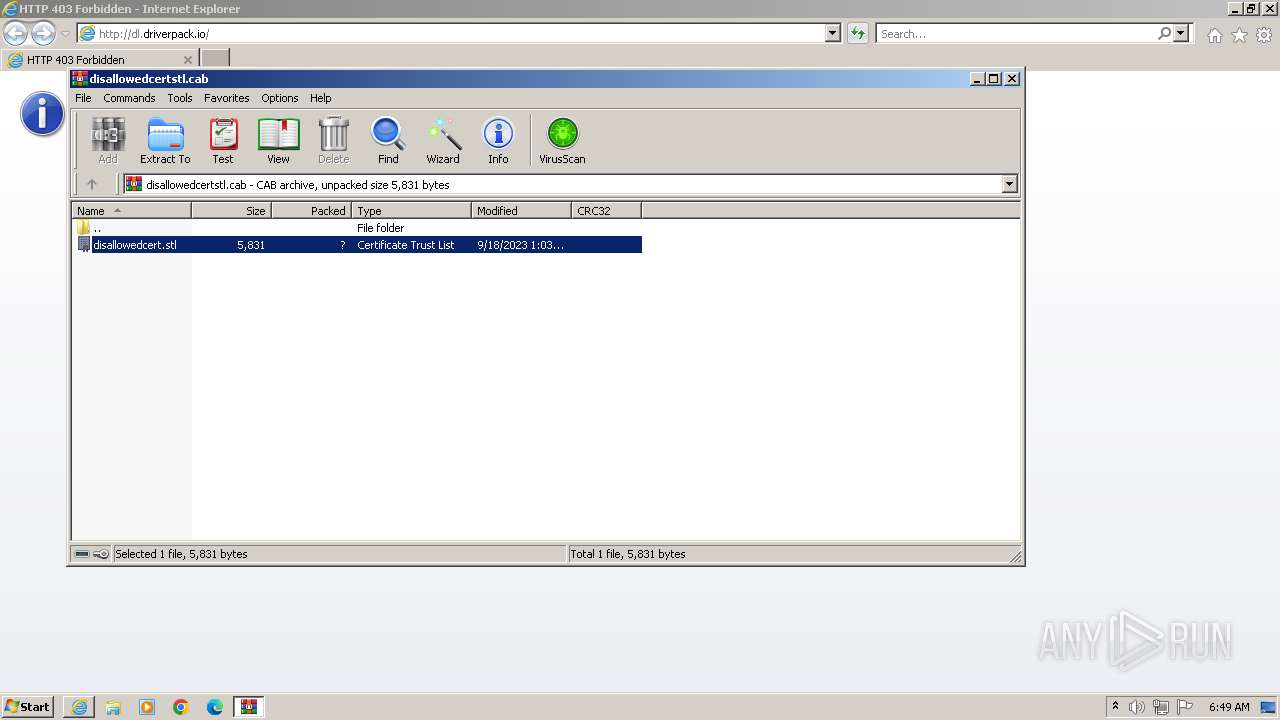
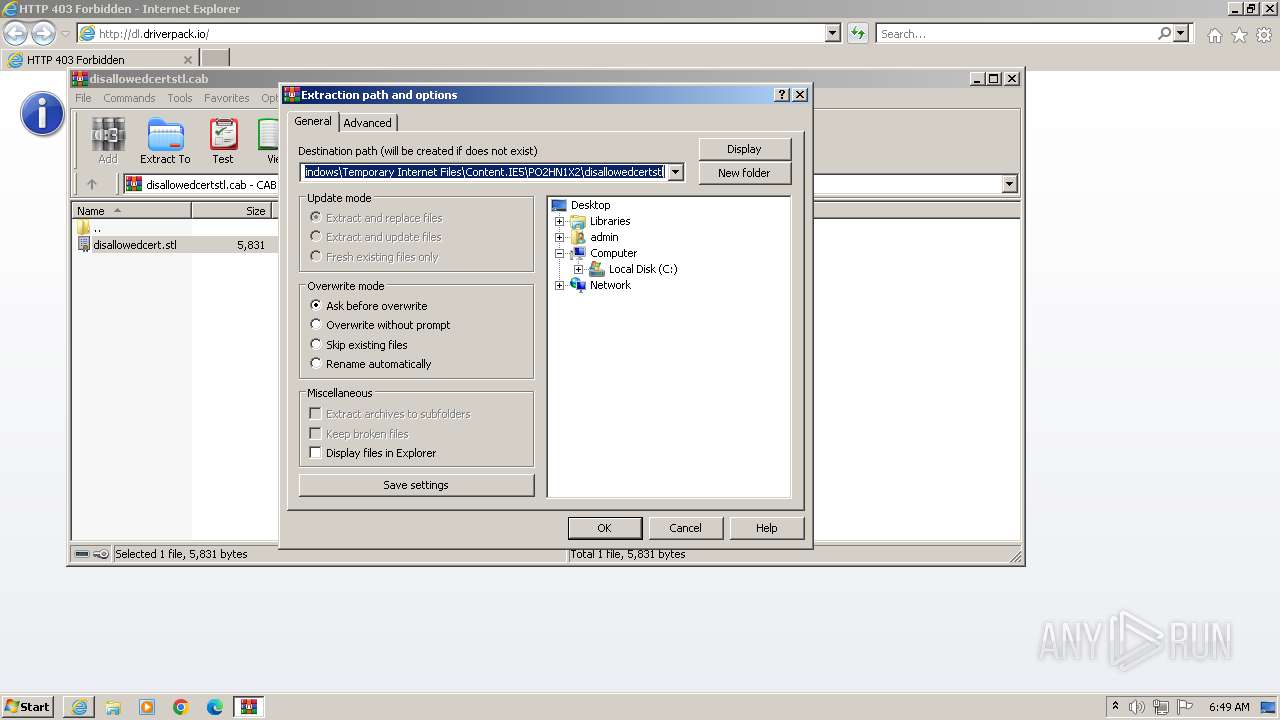
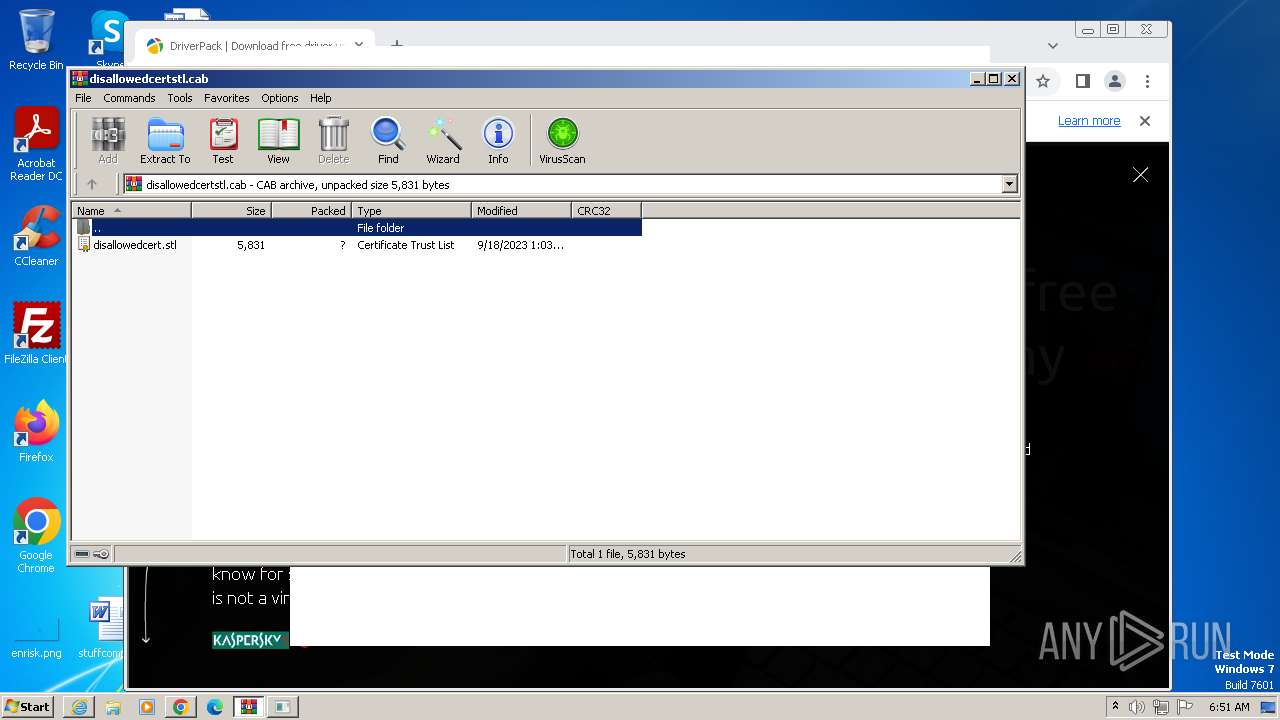
852 | iexplore.exe | GET | 200 | 8.248.141.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?d4c74188198c1b4a | unknown | compressed | 4.66 Kb | unknown |
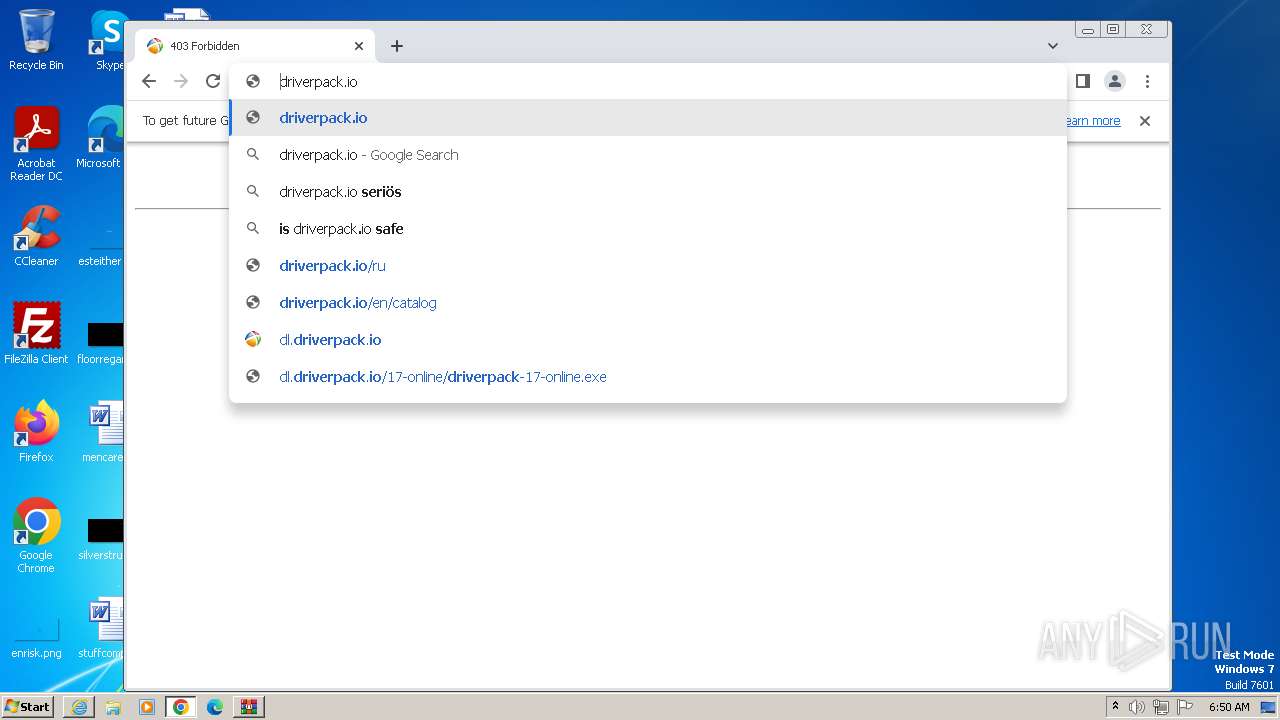
3968 | iexplore.exe | GET | 403 | 87.117.239.150:80 | http://dl.driverpack.io/ | unknown | html | 162 b | unknown |
852 | iexplore.exe | GET | 200 | 8.248.141.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?8a3519f4a6f5722c | unknown | compressed | 4.66 Kb | unknown |
3968 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAqvpsXKY8RRQeo74ffHUxc%3D | unknown | binary | 471 b | unknown |
852 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | unknown | binary | 314 b | unknown |
2748 | chrome.exe | GET | 403 | 87.117.239.150:80 | http://dl.driverpack.io/ | unknown | html | 564 b | unknown |
2748 | chrome.exe | GET | 200 | 95.154.194.108:80 | http://download-storage.driverpack.io/favicon.ico | unknown | image | 2.49 Kb | unknown |
852 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | der | 471 b | unknown |
3968 | iexplore.exe | GET | 200 | 8.248.141.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?d4c74188198c1b4a | unknown | compressed | 4.66 Kb | unknown |
2036 | mshta.exe | GET | 200 | 54.220.192.176:80 | http://dwrapper-prod.herokuapp.com/bin/src/style.css | unknown | text | 3.01 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3968 | iexplore.exe | 87.117.239.150:80 | dl.driverpack.io | Iomart Cloud Services Limited | GB | unknown |
2656 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
852 | iexplore.exe | 104.126.37.130:443 | www.bing.com | Akamai International B.V. | DE | unknown |
852 | iexplore.exe | 8.248.141.254:80 | ctldl.windowsupdate.com | LEVEL3 | US | unknown |
852 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
852 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
3968 | iexplore.exe | 13.107.5.80:443 | api.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dl.driverpack.io |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
www.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2748 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
2748 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
2036 | mshta.exe | A Network Trojan was detected | SUSPICIOUS [ANY.RUN] VBS is used to run Shell |
2036 | mshta.exe | A Network Trojan was detected | SUSPICIOUS [ANY.RUN] VBS is used to run Shell |
2036 | mshta.exe | Potentially Bad Traffic | ET HUNTING PowerShell DownloadFile Command Common In Powershell Stagers |
1088 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
1088 | svchost.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed DNS Query to DriverPack Domain ( .drp .su) |
1088 | svchost.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP DriverPack Domain in DNS Query |
1088 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
1088 | svchost.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP DriverPack Domain in DNS Query |
6 ETPRO signatures available at the full report
Process | Message |
|---|---|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|