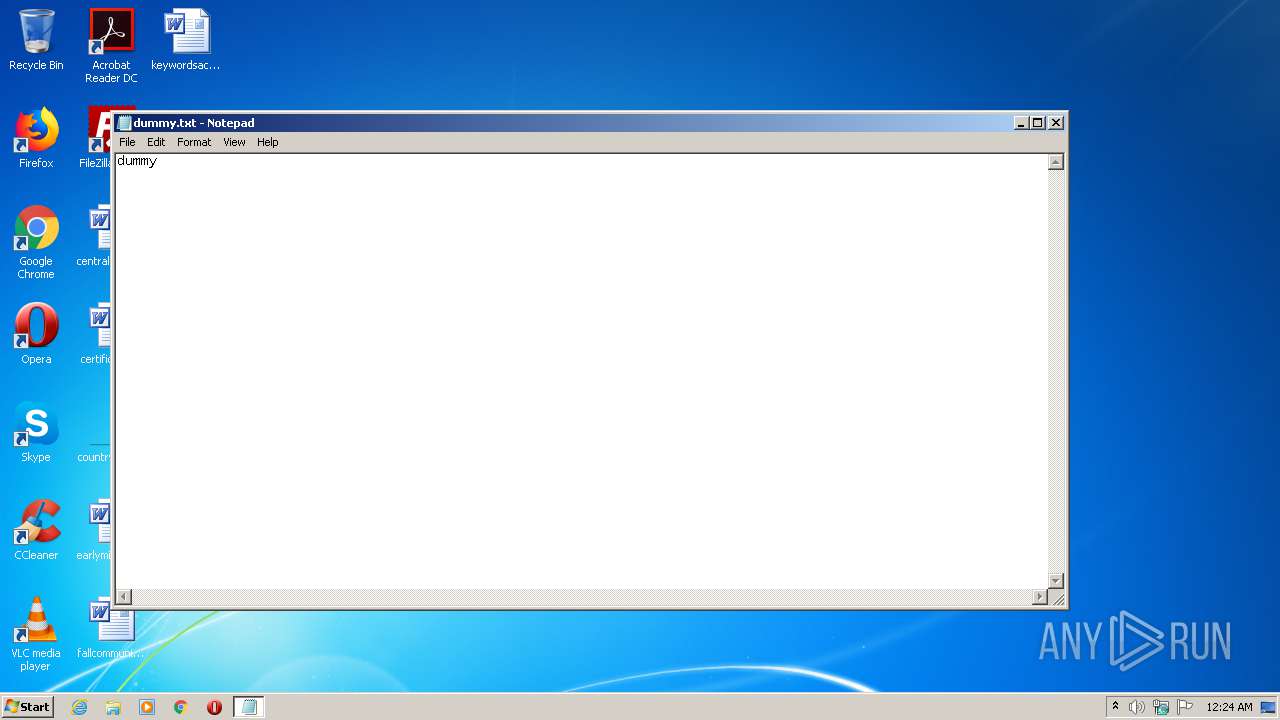
| File name: | dummy.txt |
| Full analysis: | https://app.any.run/tasks/aa05fd4a-2bca-4988-b856-8151e42174f5 |
| Verdict: | Malicious activity |
| Analysis date: | September 12, 2020, 23:24:34 |
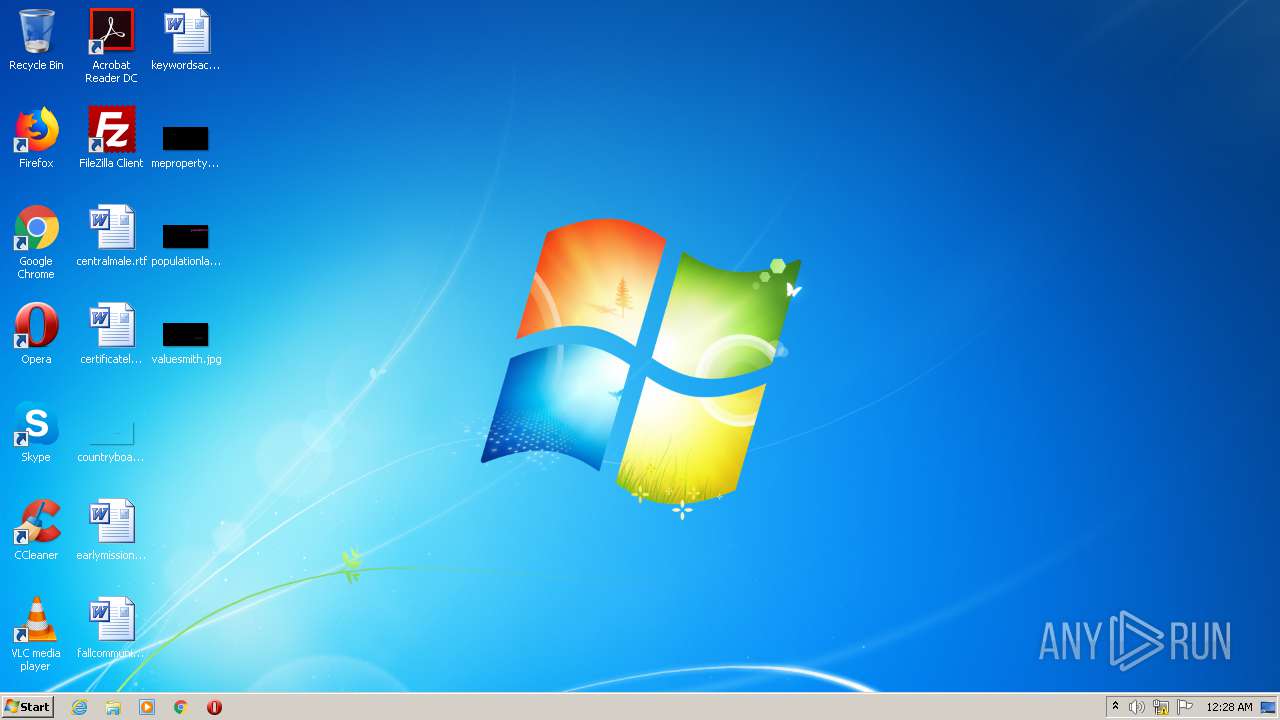
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with no line terminators |
| MD5: | 275876E34CF609DB118F3D84B799A790 |
| SHA1: | 829C3804401B0727F70F73D4415E162400CBE57B |
| SHA256: | B5A2C96250612366EA272FFAC6D9744AAF4B45AACD96AA7CFCB931EE3B558259 |
| SSDEEP: | 3:5n:5n |
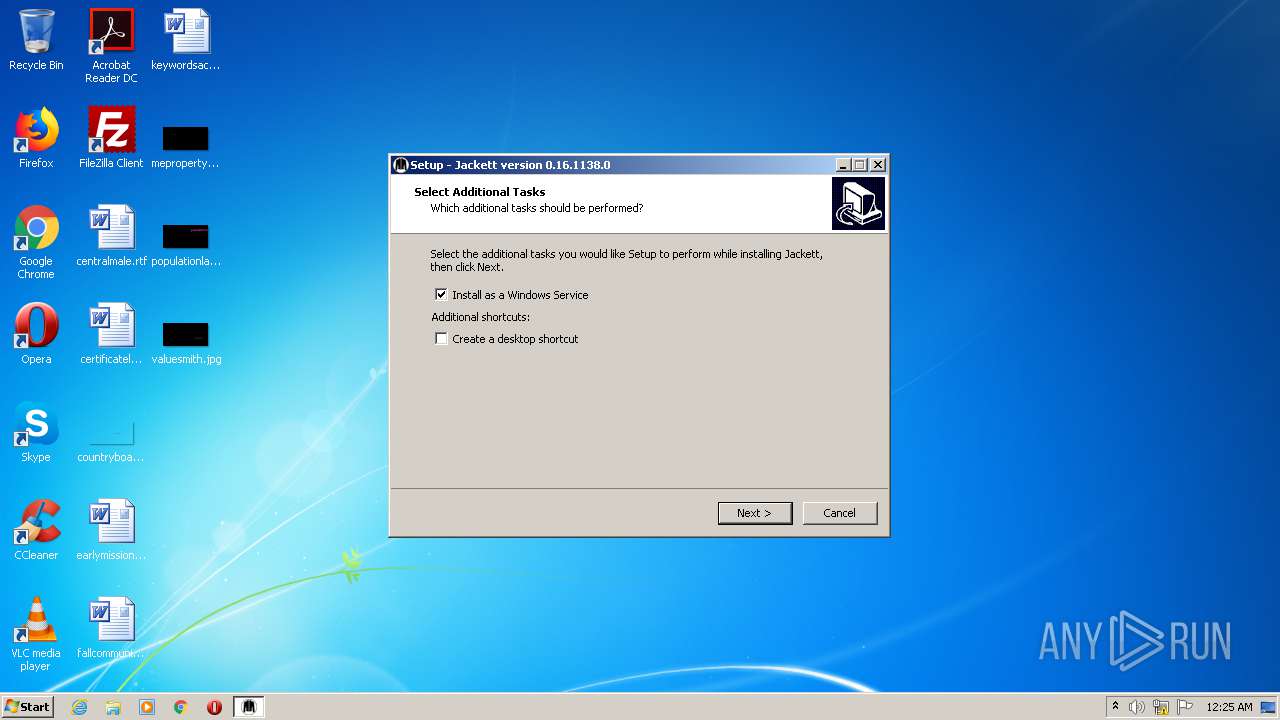
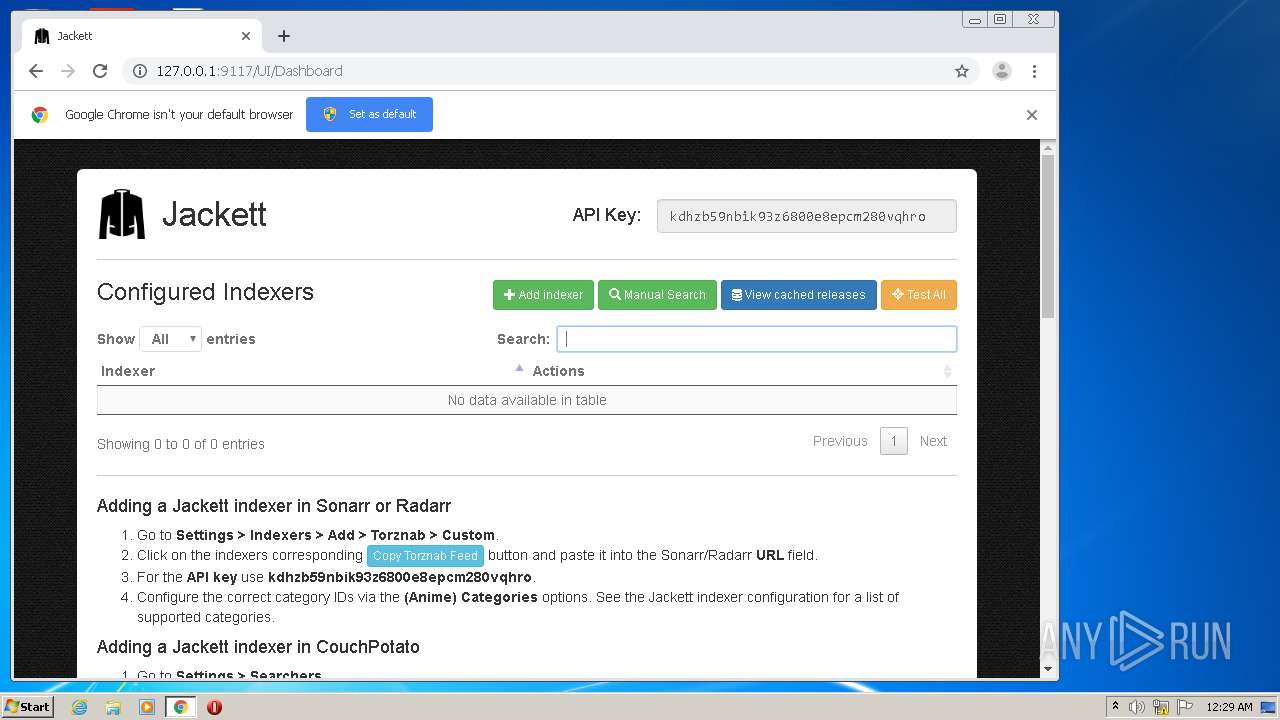
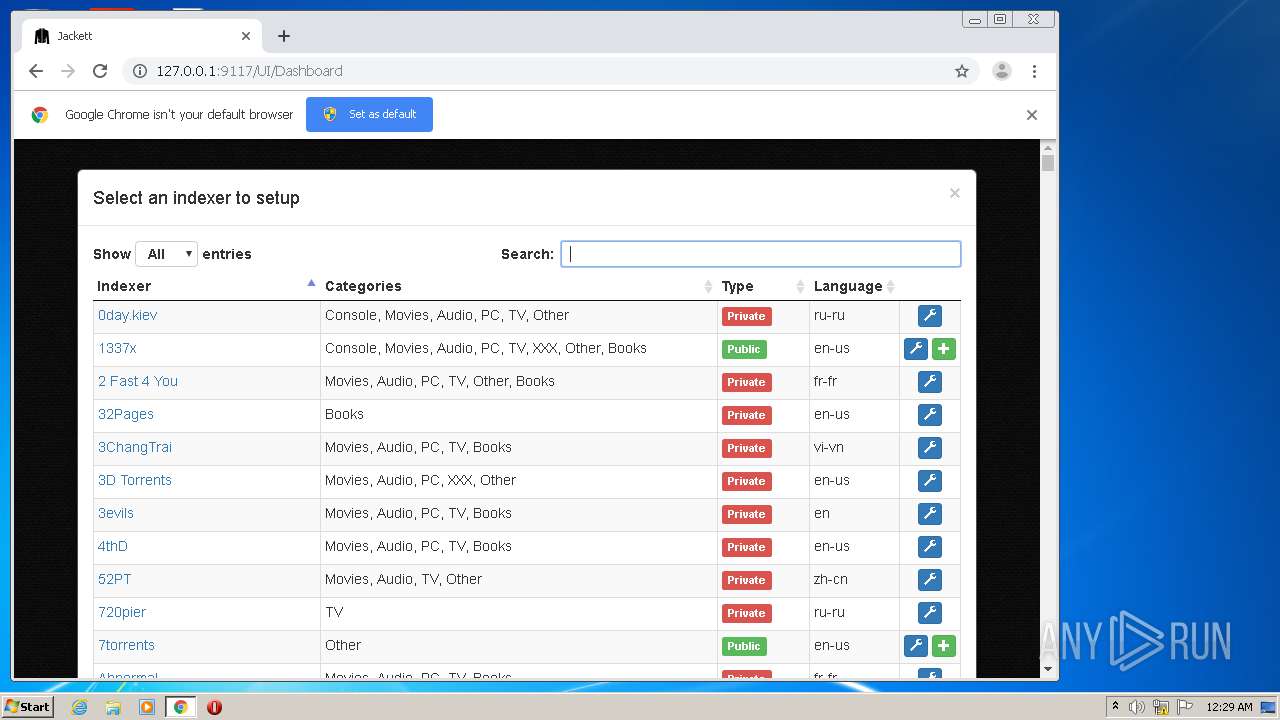
MALICIOUS
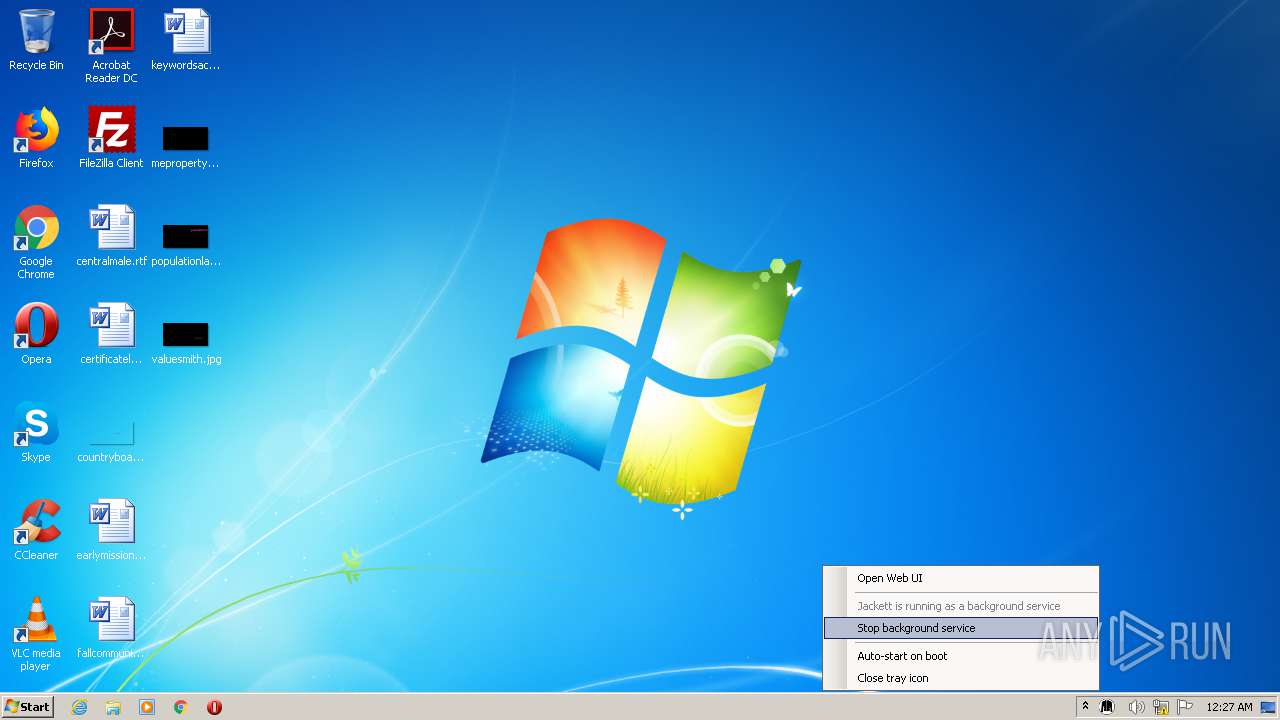
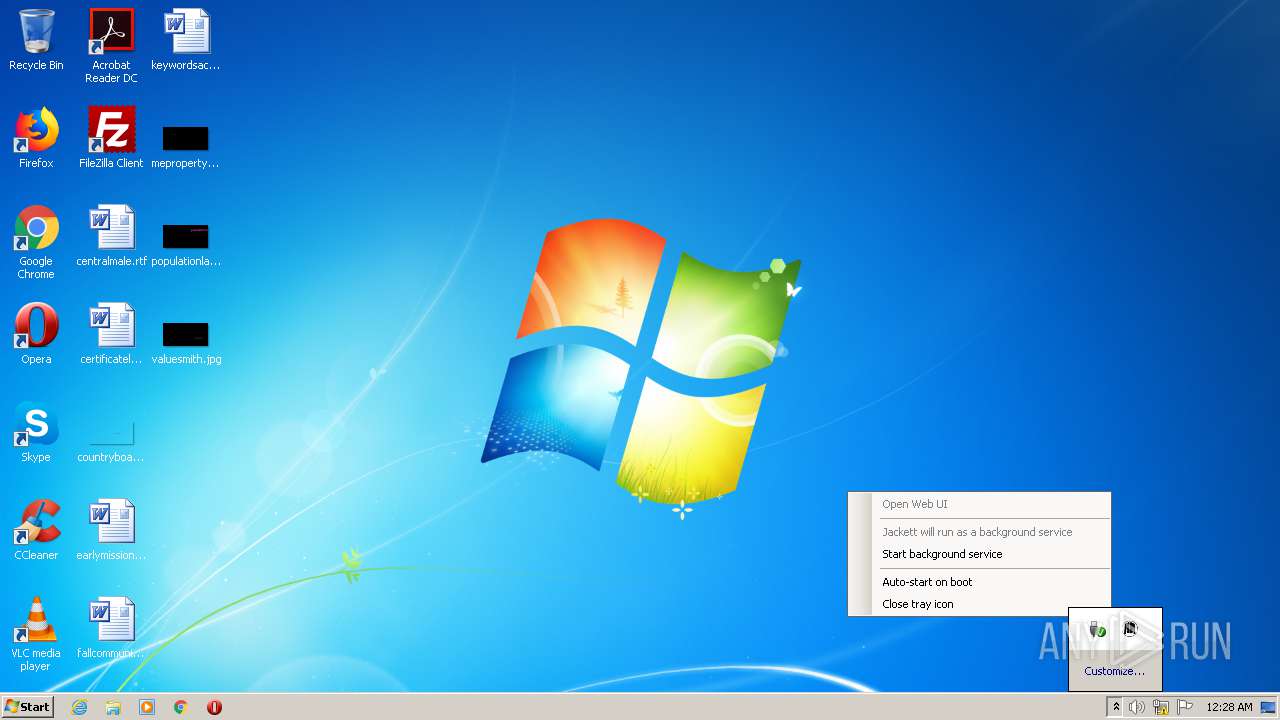
Application was dropped or rewritten from another process
- Jackett.Installer.Windows.exe (PID: 1144)
- Jackett.Installer.Windows.exe (PID: 3064)
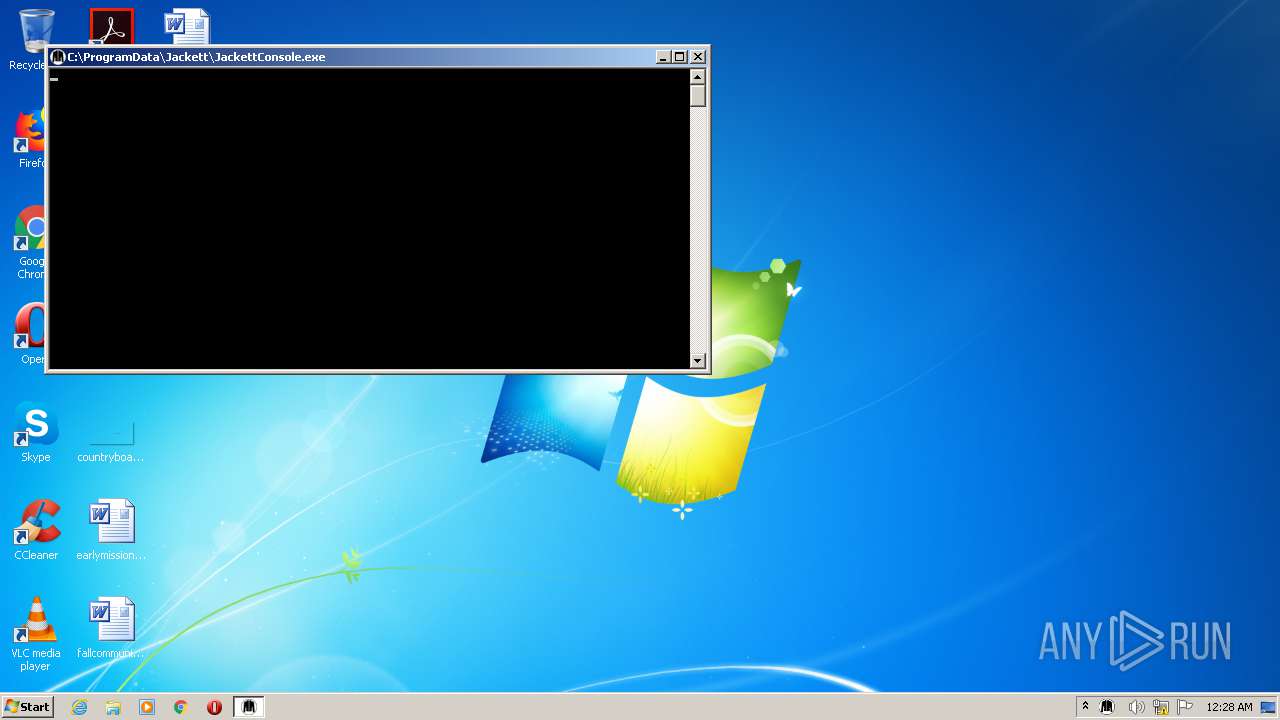
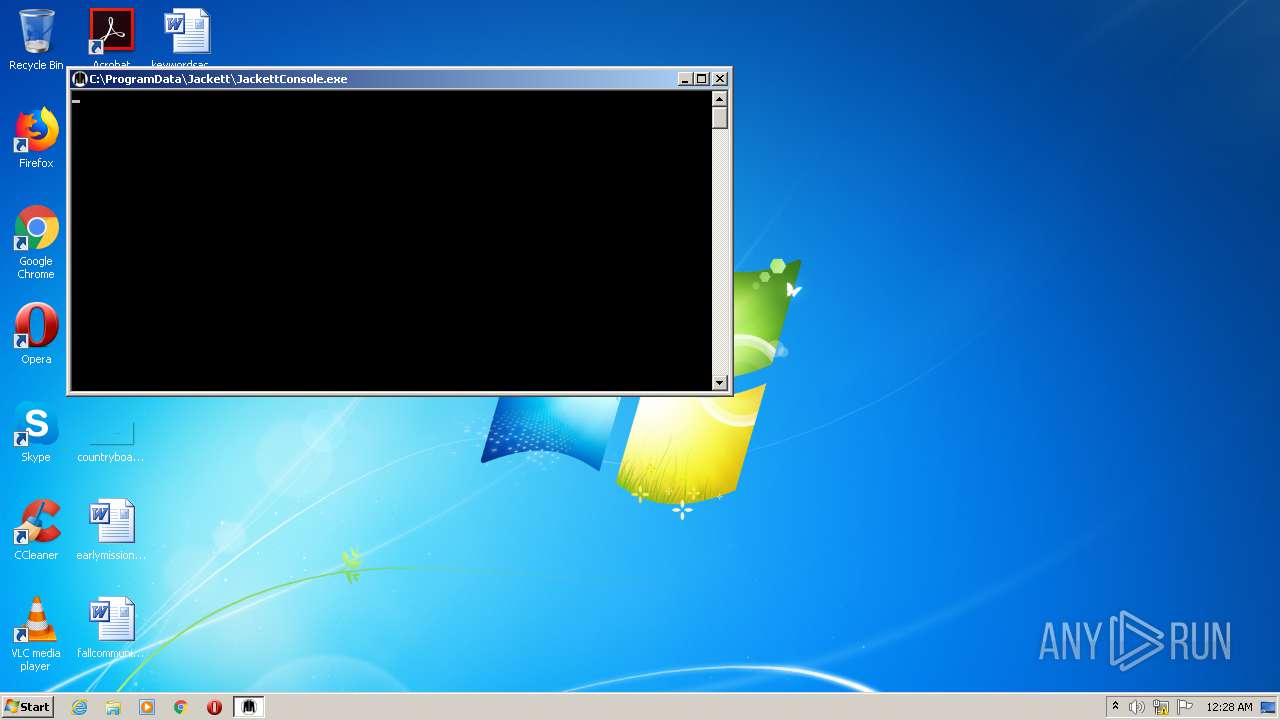
- JackettConsole.exe (PID: 2104)
- JackettConsole.exe (PID: 2100)
- JackettConsole.exe (PID: 2084)
- JackettConsole.exe (PID: 2612)
- JackettService.exe (PID: 3768)
- JackettConsole.exe (PID: 3740)
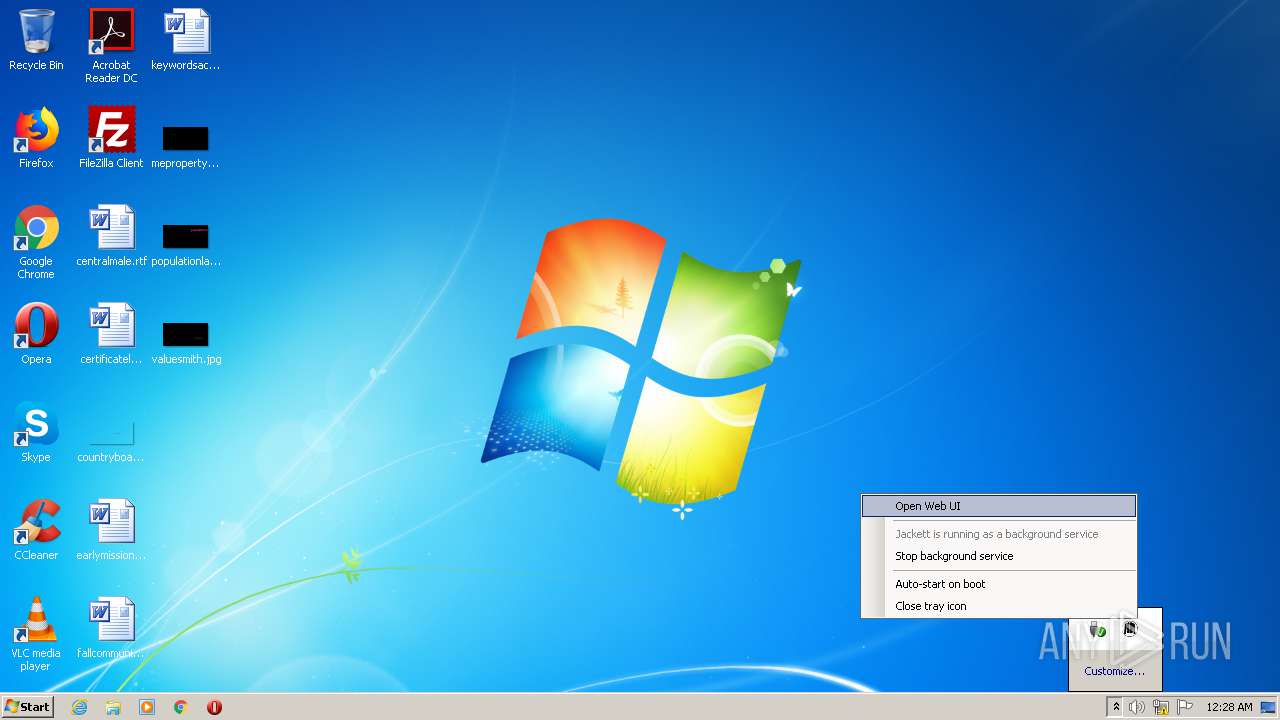
- JackettTray.exe (PID: 2116)
- JackettConsole.exe (PID: 3120)
- JackettConsole.exe (PID: 3712)
- JackettService.exe (PID: 3732)
- JackettConsole.exe (PID: 3796)
Loads dropped or rewritten executable
- JackettConsole.exe (PID: 2084)
- JackettConsole.exe (PID: 2104)
- JackettConsole.exe (PID: 2100)
- JackettConsole.exe (PID: 2612)
- JackettService.exe (PID: 3768)
- JackettConsole.exe (PID: 3740)
- JackettTray.exe (PID: 2116)
- JackettConsole.exe (PID: 3120)
- JackettConsole.exe (PID: 3712)
- JackettConsole.exe (PID: 3796)
- JackettService.exe (PID: 3732)
Changes settings of System certificates
- JackettConsole.exe (PID: 3796)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 3936)
- Jackett.Installer.Windows.exe (PID: 1144)
- Jackett.Installer.Windows.exe (PID: 3064)
- Jackett.Installer.Windows.tmp (PID: 2520)
Cleans NTFS data-stream (Zone Identifier)
- chrome.exe (PID: 3936)
Reads the Windows organization settings
- Jackett.Installer.Windows.tmp (PID: 2520)
Reads Windows owner or organization settings
- Jackett.Installer.Windows.tmp (PID: 2520)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3936)
Starts SC.EXE for service management
- JackettConsole.exe (PID: 2104)
- JackettConsole.exe (PID: 2100)
Executed as Windows Service
- JackettService.exe (PID: 3768)
- JackettService.exe (PID: 3732)
Uses NETSH.EXE for network configuration
- JackettConsole.exe (PID: 2104)
- JackettConsole.exe (PID: 2084)
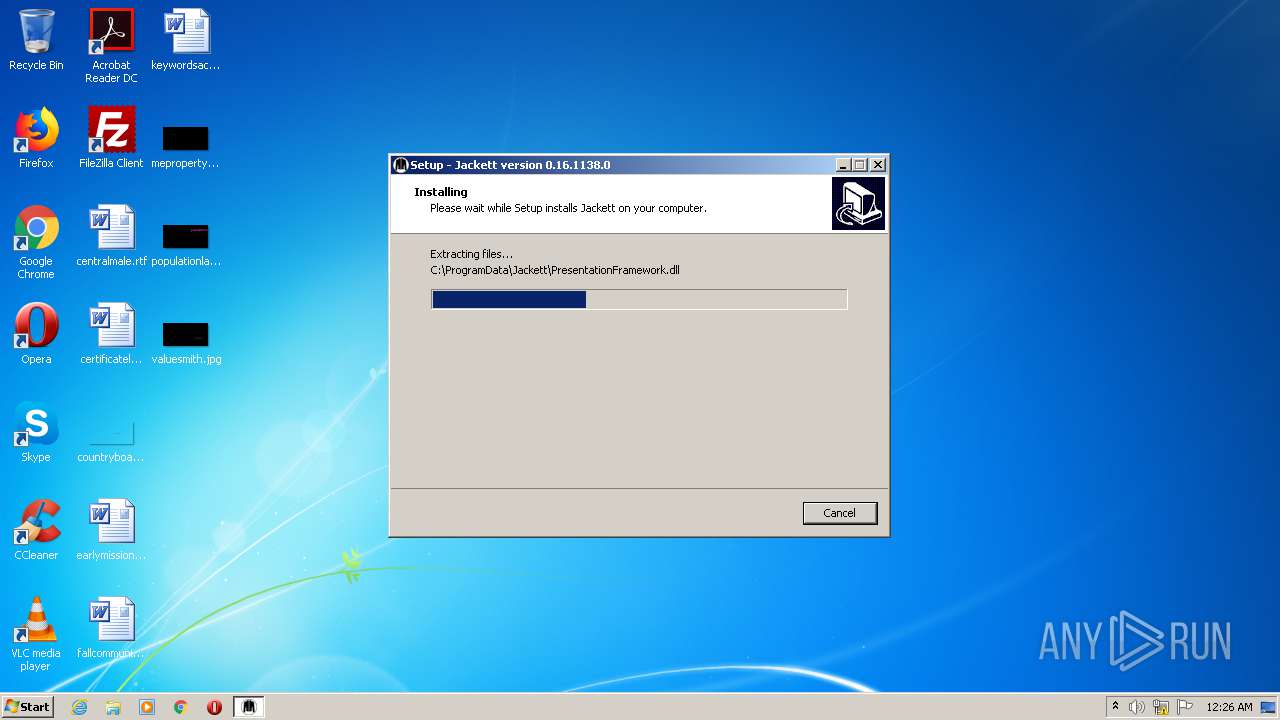
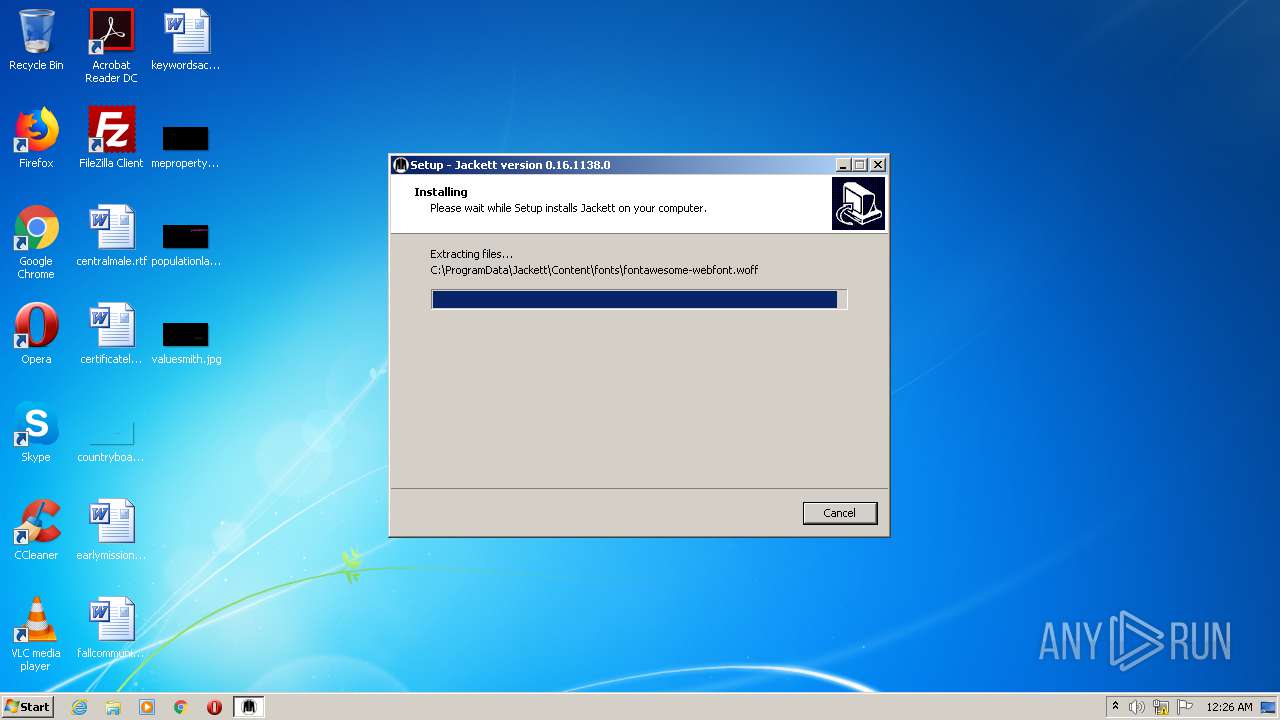
Creates files in the program directory
- JackettService.exe (PID: 3768)
- JackettConsole.exe (PID: 3740)
- JackettTray.exe (PID: 2116)
- JackettConsole.exe (PID: 3796)
- JackettConsole.exe (PID: 2104)
Creates files in the Windows directory
- JackettService.exe (PID: 3768)
- JackettConsole.exe (PID: 3740)
- JackettService.exe (PID: 3732)
- JackettConsole.exe (PID: 3796)
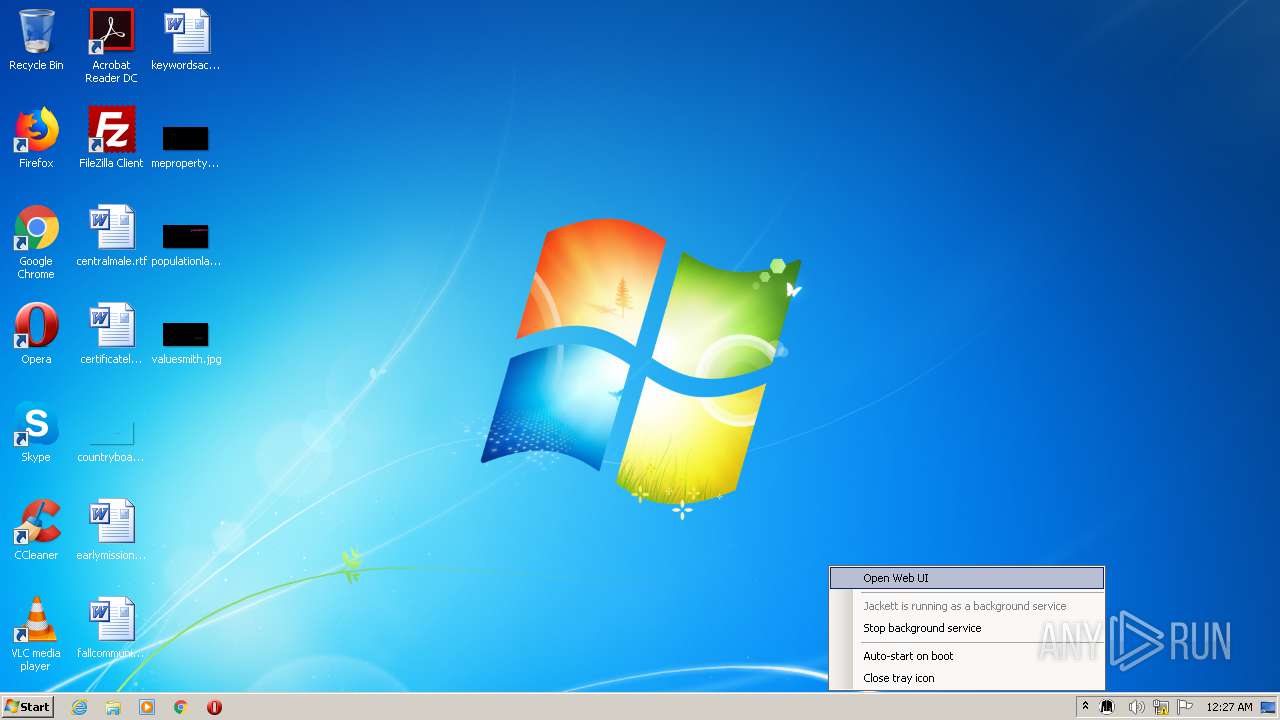
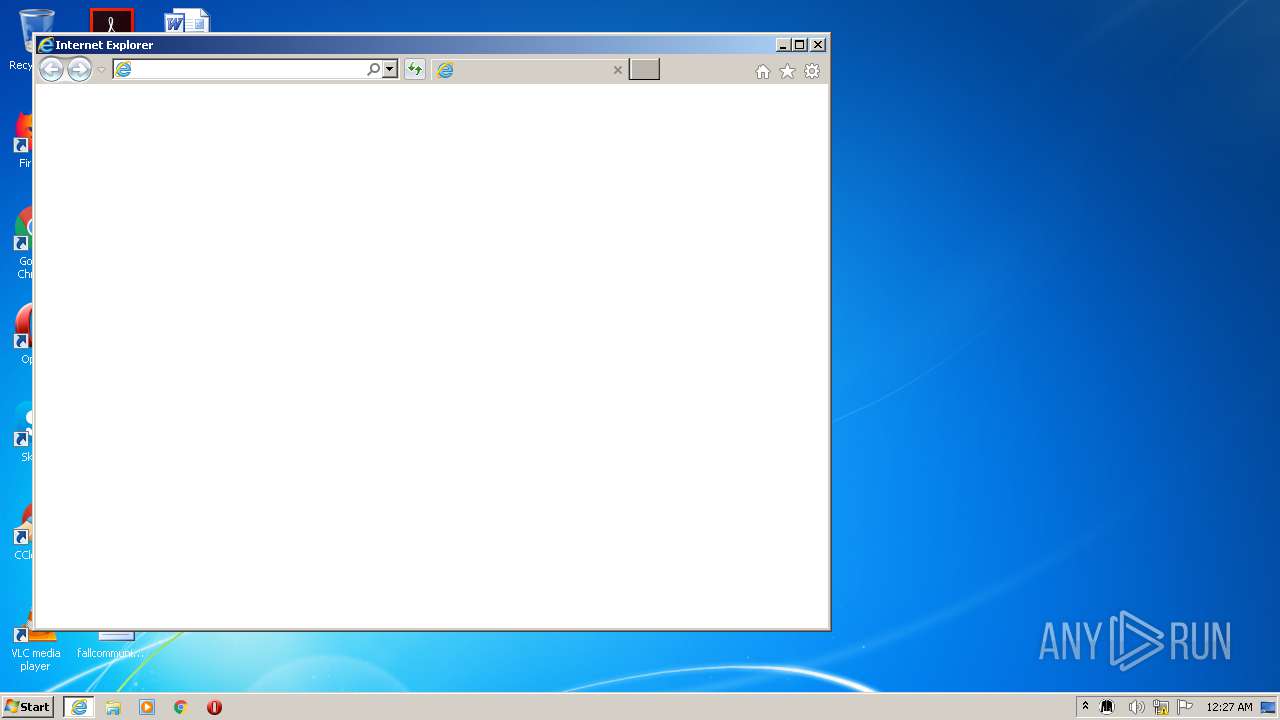
Starts Internet Explorer
- JackettTray.exe (PID: 2116)
Adds / modifies Windows certificates
- JackettConsole.exe (PID: 3796)
INFO
Reads the hosts file
- chrome.exe (PID: 3972)
- chrome.exe (PID: 3936)
- chrome.exe (PID: 1932)
- chrome.exe (PID: 3888)
Reads Internet Cache Settings
- chrome.exe (PID: 3936)
- iexplore.exe (PID: 3560)
- iexplore.exe (PID: 712)
- iexplore.exe (PID: 3912)
- iexplore.exe (PID: 1796)
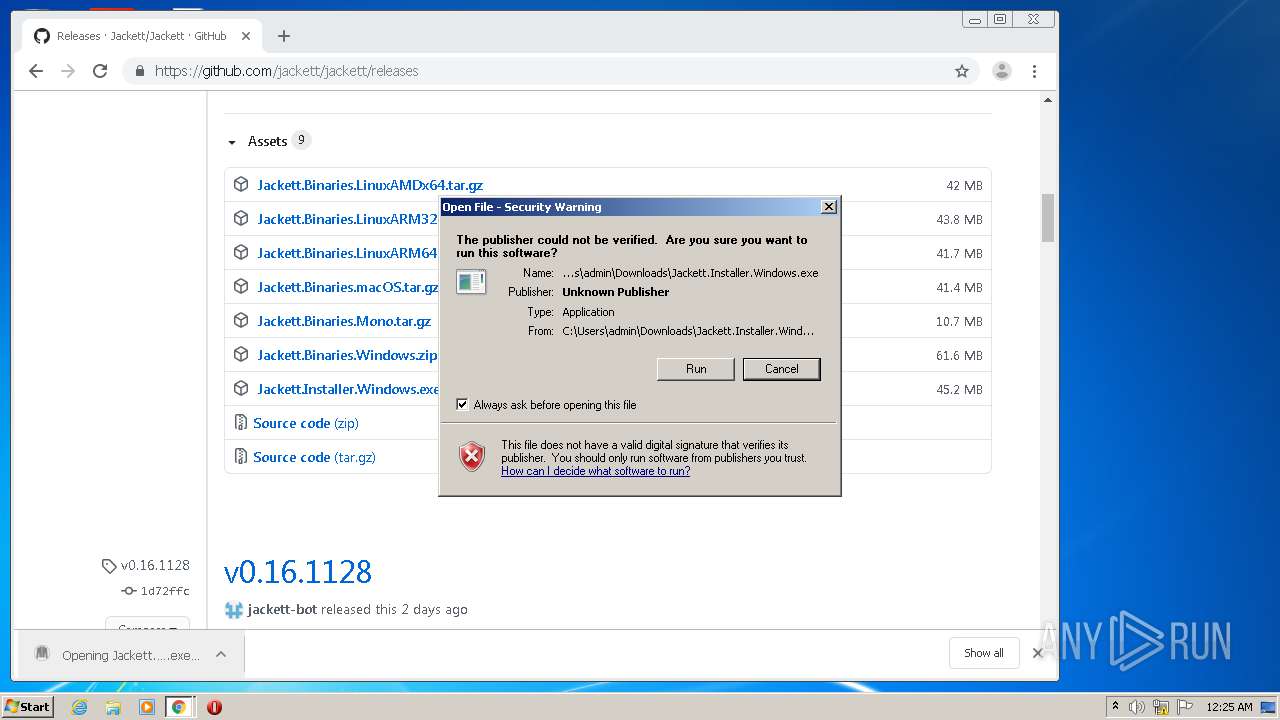
Manual execution by user
- chrome.exe (PID: 3936)
- chrome.exe (PID: 1932)
Application launched itself
- chrome.exe (PID: 3936)
- iexplore.exe (PID: 3560)
- chrome.exe (PID: 1932)
- iexplore.exe (PID: 3912)
Dropped object may contain Bitcoin addresses
- Jackett.Installer.Windows.tmp (PID: 2520)
Application was dropped or rewritten from another process
- Jackett.Installer.Windows.tmp (PID: 3496)
- Jackett.Installer.Windows.tmp (PID: 2520)
Creates a software uninstall entry
- Jackett.Installer.Windows.tmp (PID: 2520)
Creates files in the program directory
- Jackett.Installer.Windows.tmp (PID: 2520)
Creates files in the user directory
- iexplore.exe (PID: 712)
Reads internet explorer settings
- iexplore.exe (PID: 712)
- iexplore.exe (PID: 1796)
Changes internet zones settings
- iexplore.exe (PID: 3560)
- iexplore.exe (PID: 3912)
Reads settings of System Certificates
- iexplore.exe (PID: 3560)
- chrome.exe (PID: 3888)
- JackettConsole.exe (PID: 3796)
Changes settings of System certificates
- iexplore.exe (PID: 3560)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3560)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
138
Monitored processes
70
Malicious processes
16
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,8044618112790646357,9585450534060850497,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15850483617654063120 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3896 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=992,4298036153924893430,3338541156059448940,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=1697524068714293683 --mojo-platform-channel-handle=1012 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,4298036153924893430,3338541156059448940,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=1936842940872119827 --mojo-platform-channel-handle=3572 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 588 | "C:\Windows\System32\sc.exe" delete Jackett | C:\Windows\System32\sc.exe | — | JackettConsole.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 588 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,4298036153924893430,3338541156059448940,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7346921881945691872 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2224 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,4298036153924893430,3338541156059448940,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14377445519173023759 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2084 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 712 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3560 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
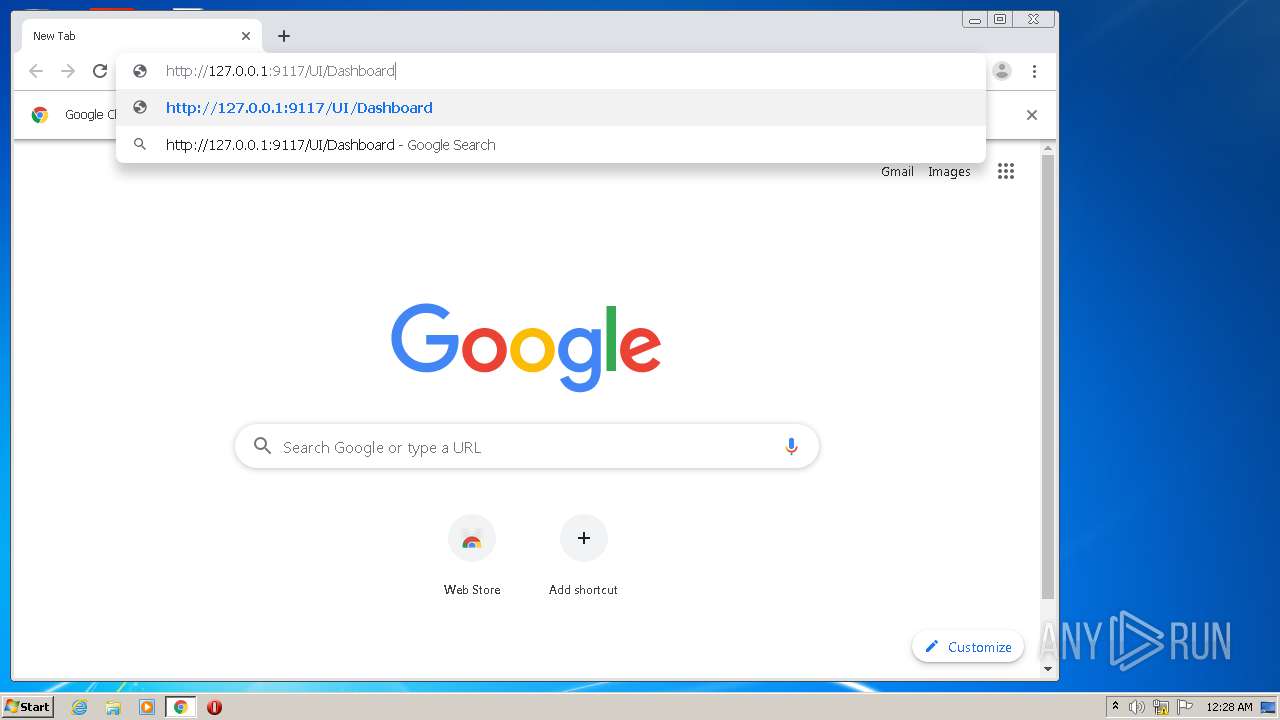
| 956 | "netsh.exe" http add urlacl http://*:9117/ sddl=D:(A;;GX;;;S-1-1-0) | C:\Windows\system32\netsh.exe | — | JackettConsole.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,8044618112790646357,9585450534060850497,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=15141938892898848693 --mojo-platform-channel-handle=3096 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
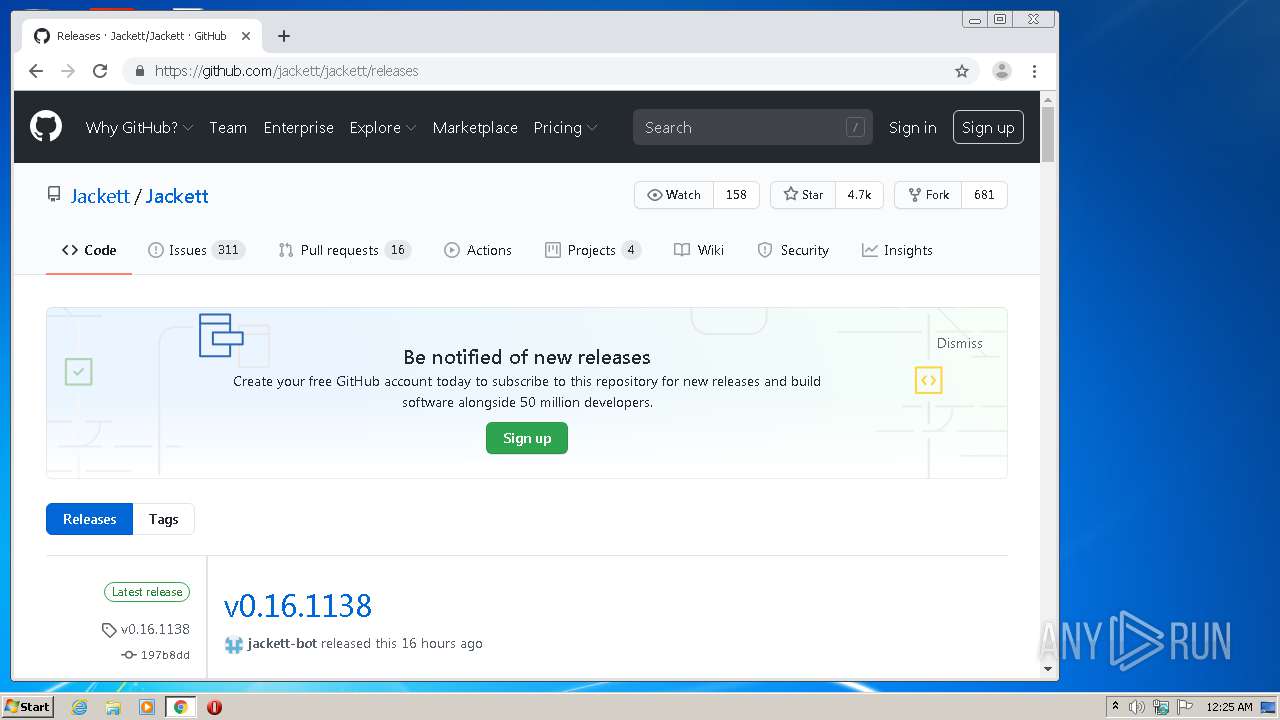
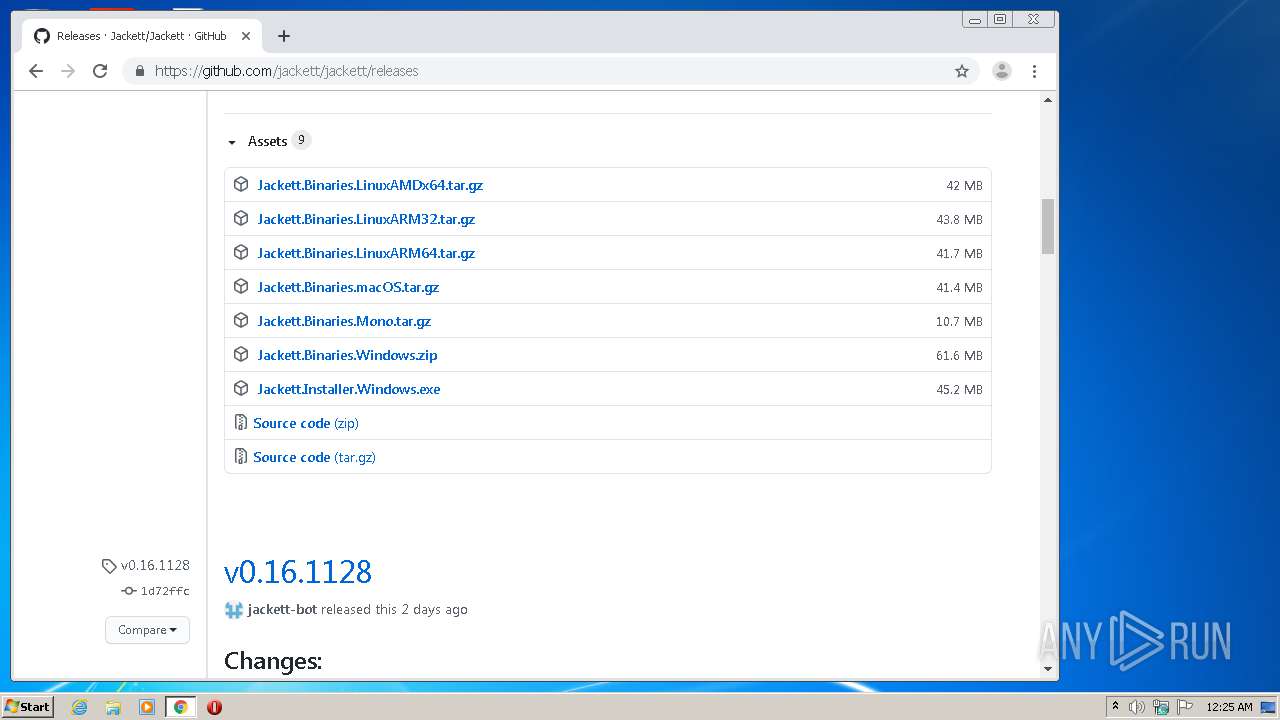
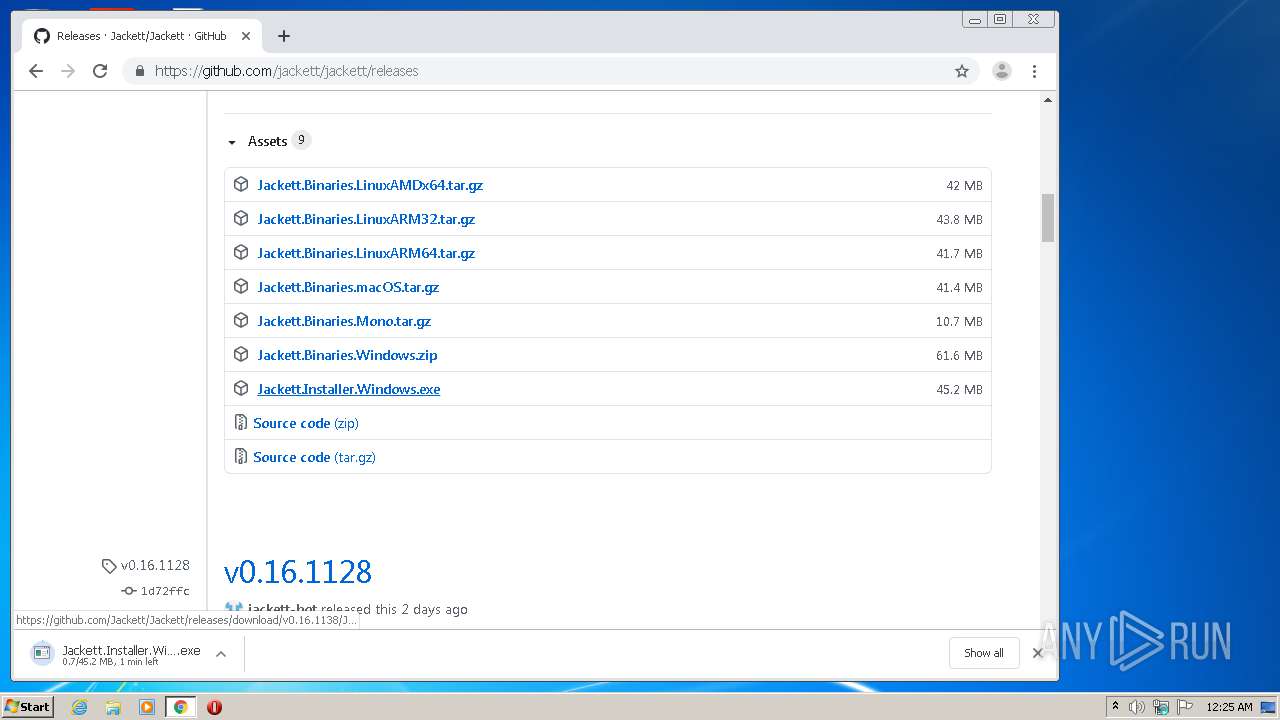
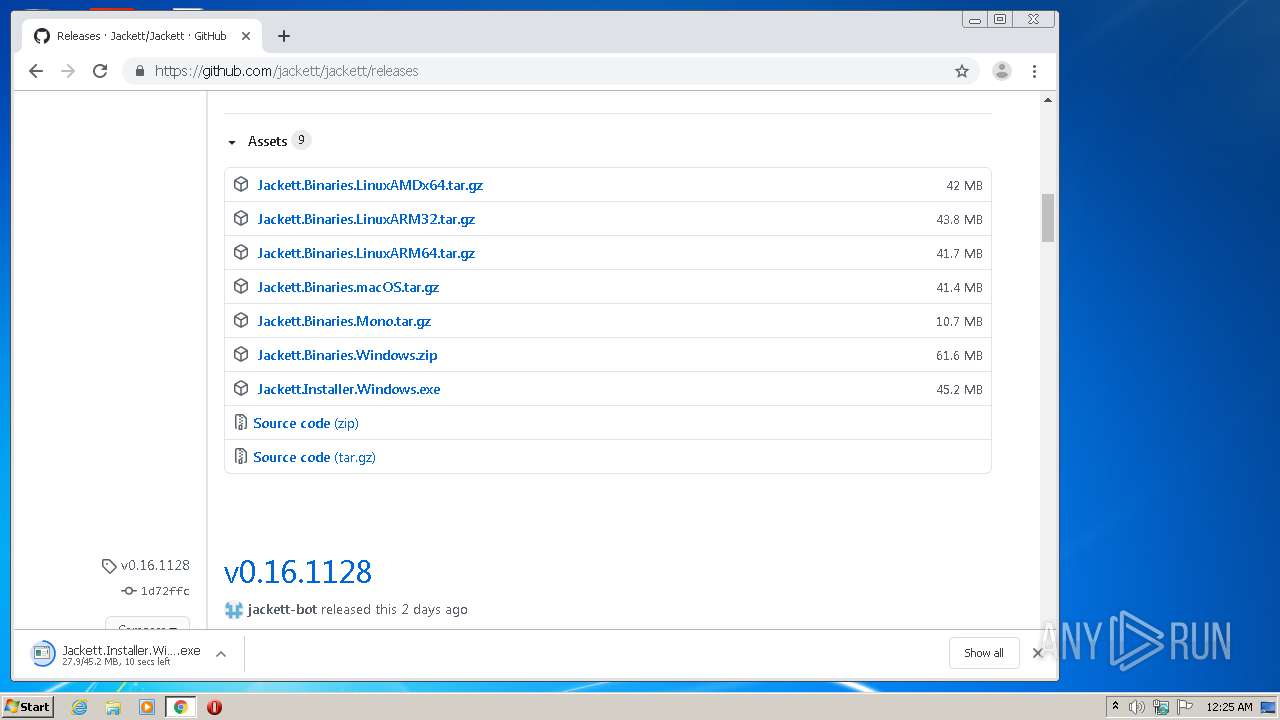
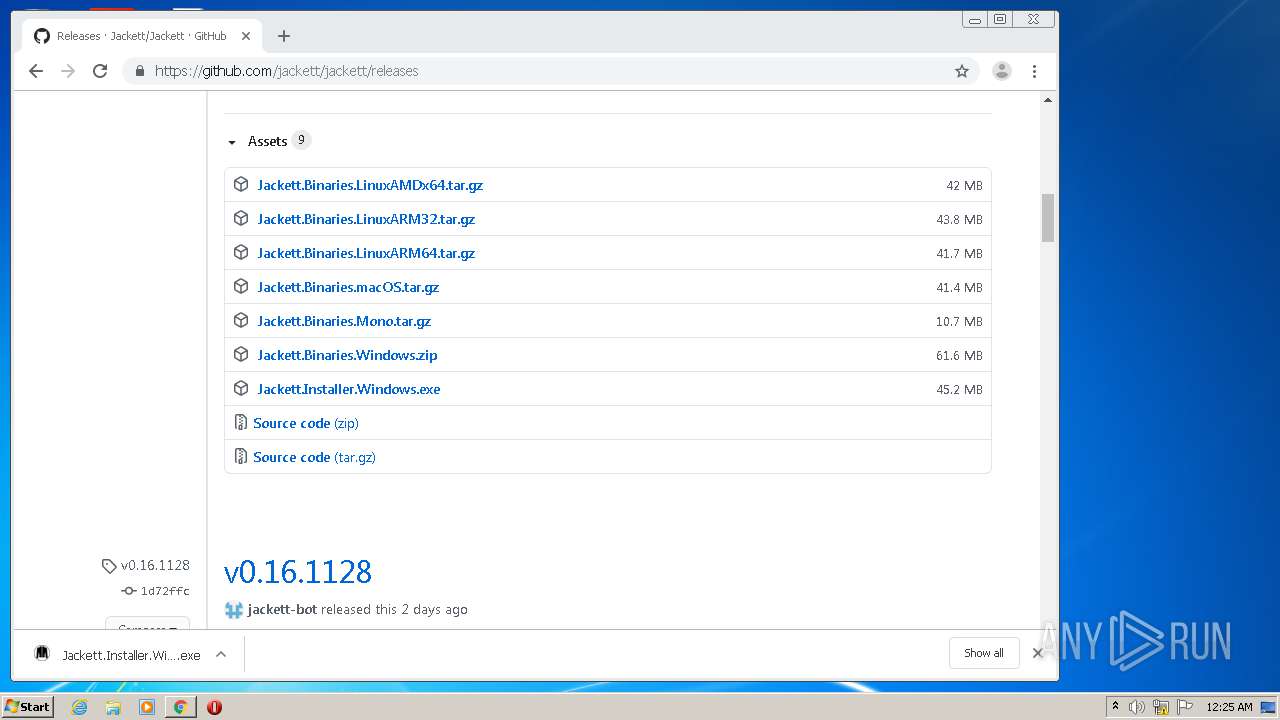
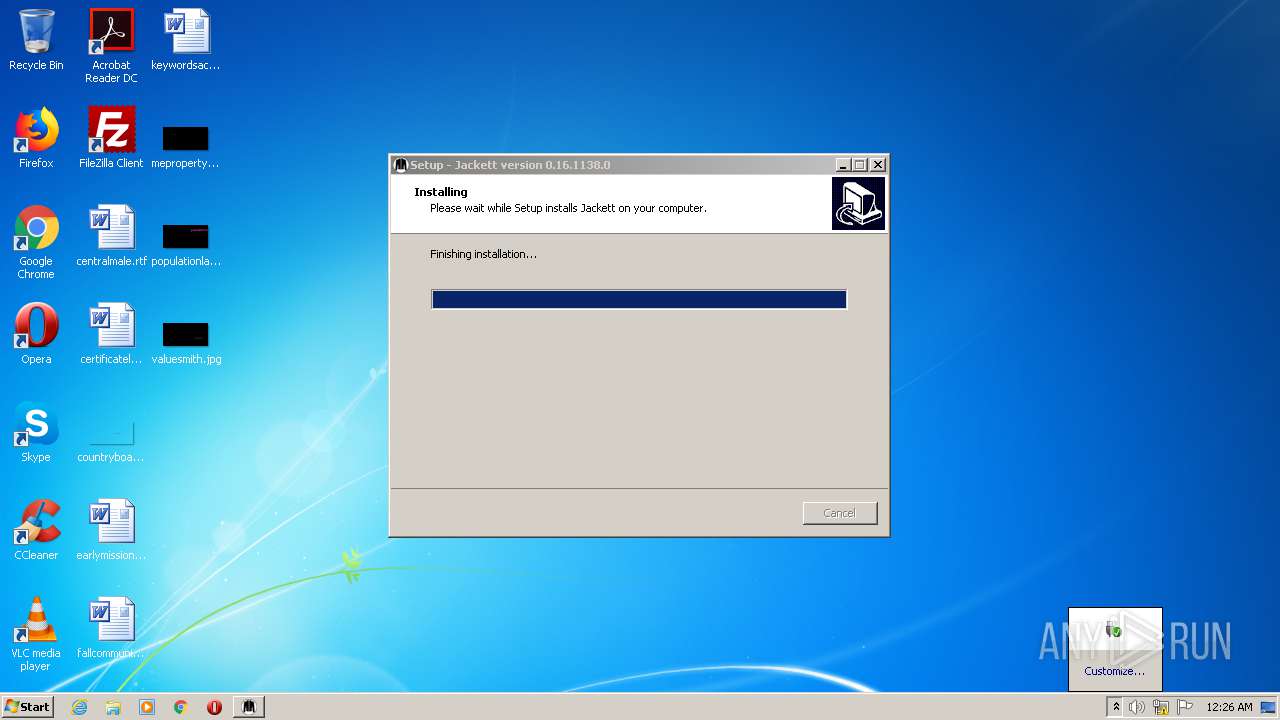
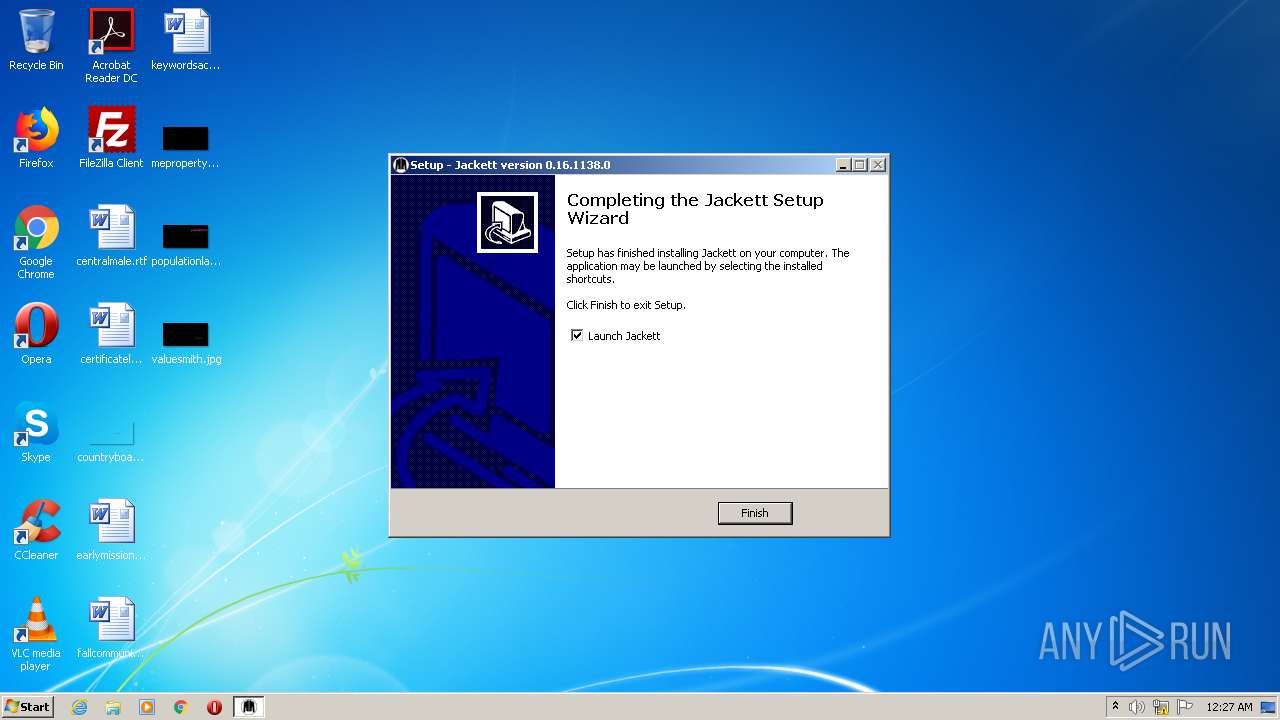
| 1144 | "C:\Users\admin\Downloads\Jackett.Installer.Windows.exe" | C:\Users\admin\Downloads\Jackett.Installer.Windows.exe | chrome.exe | ||||||||||||
User: admin Company: Jackett Integrity Level: MEDIUM Description: Jackett Setup Exit code: 0 Version: 0.16.1138.0 Modules
| |||||||||||||||
Total events
3 695
Read events
3 069
Write events
605
Delete events
21
Modification events
| (PID) Process: | (2208) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosX |
Value: 110 | |||
| (PID) Process: | (2208) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosY |
Value: 110 | |||
| (PID) Process: | (2208) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosDX |
Value: 960 | |||
| (PID) Process: | (2208) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosDY |
Value: 501 | |||
| (PID) Process: | (3936) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3936) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3936) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3936) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3936) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3936-13244426693450625 |
Value: 259 | |||
Executable files
435
Suspicious files
129
Text files
818
Unknown types
33
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\fde3c4fb-5260-420e-a4e7-dc3100a376ec.tmp | — | |
MD5:— | SHA256:— | |||
| 3936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFee8d5.TMP | text | |
MD5:— | SHA256:— | |||
| 3936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFee8d5.TMP | text | |
MD5:— | SHA256:— | |||
| 3936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFee8d5.TMP | text | |
MD5:— | SHA256:— | |||
| 3936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFeea7b.TMP | — | |
MD5:— | SHA256:— | |||
| 3936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
56
DNS requests
120
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
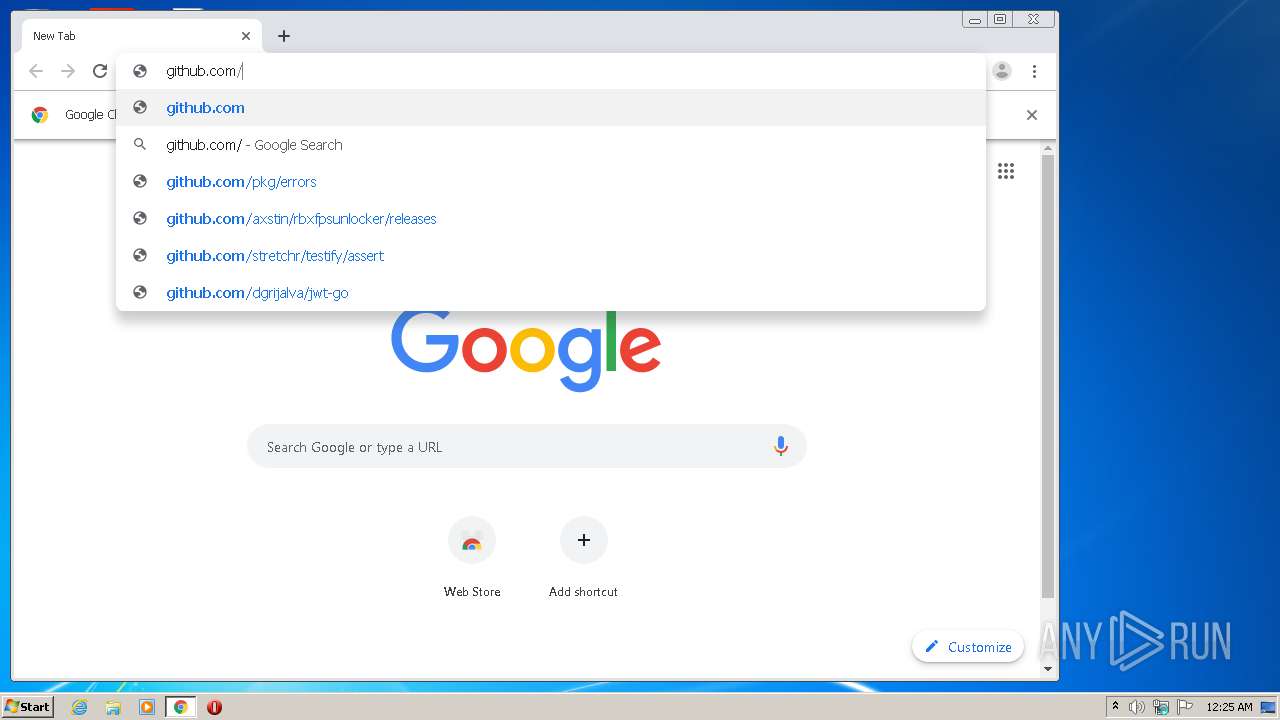
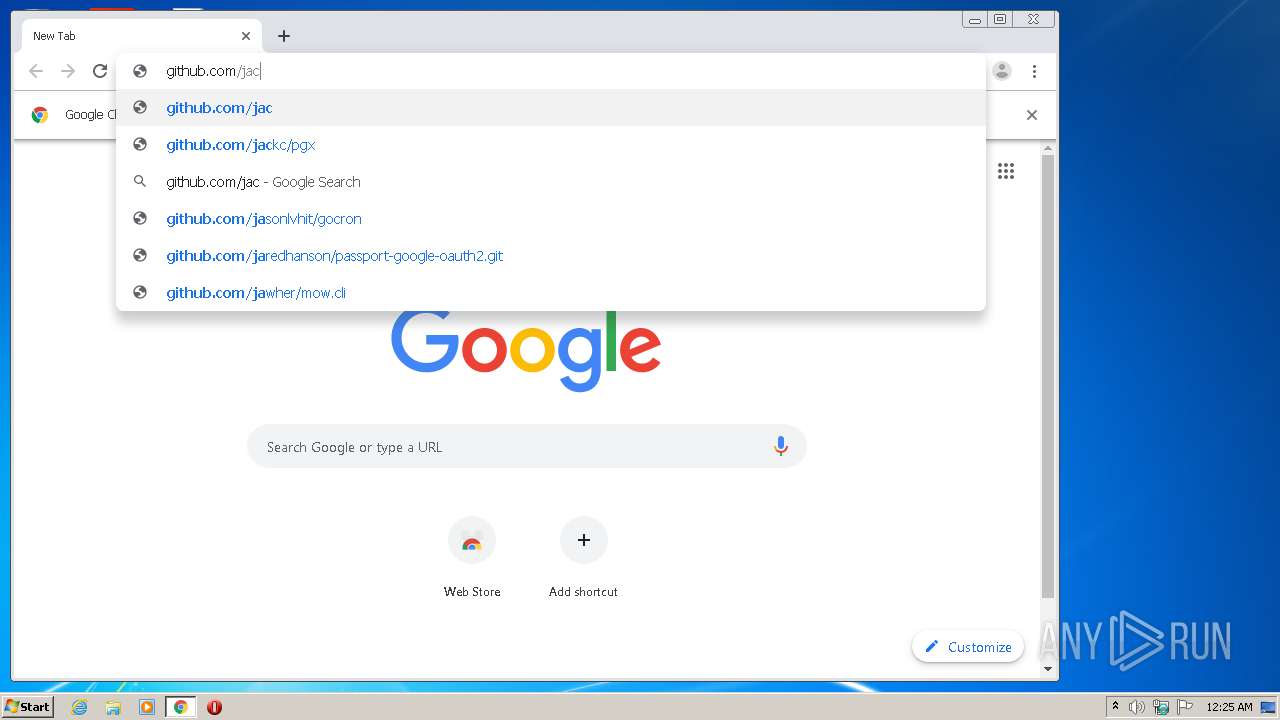
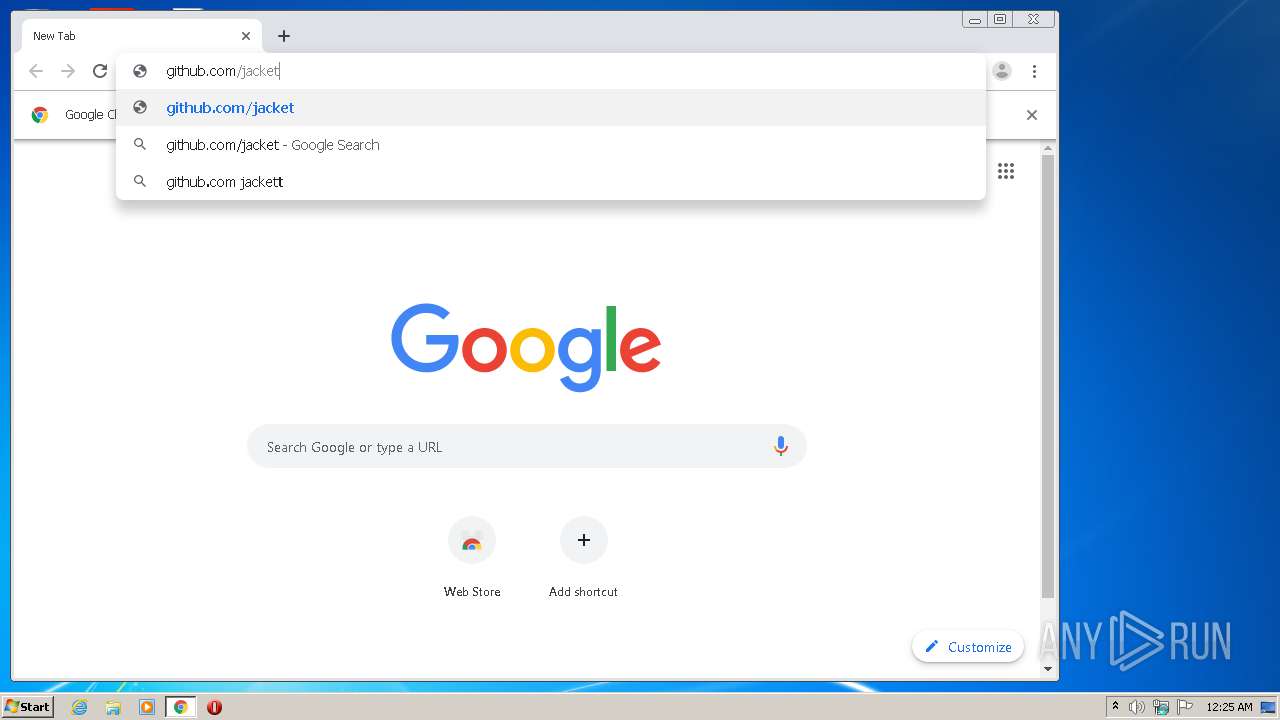
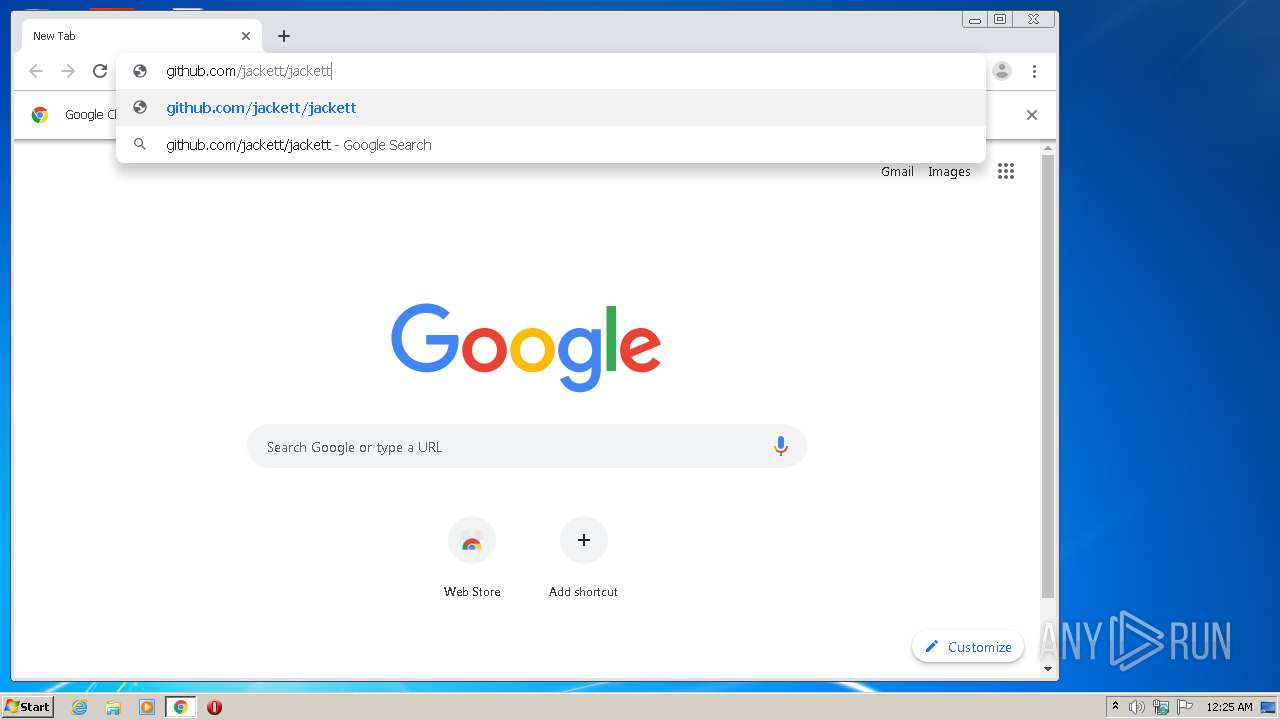
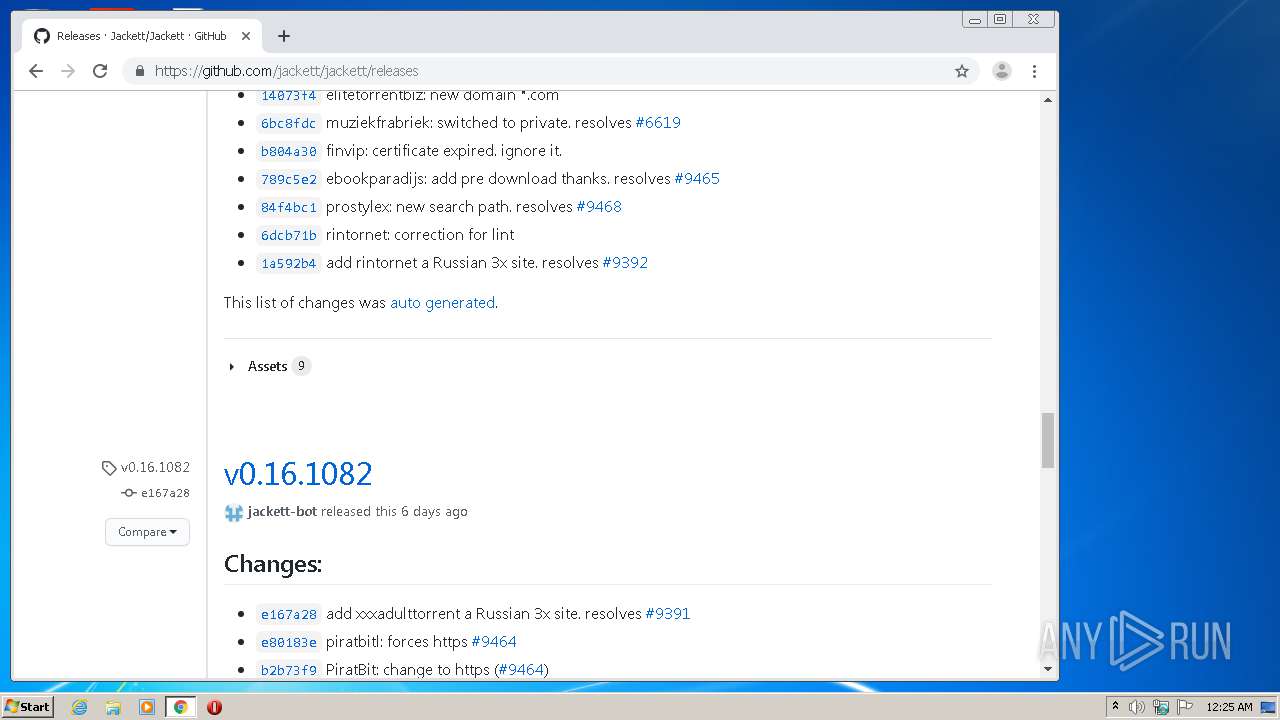
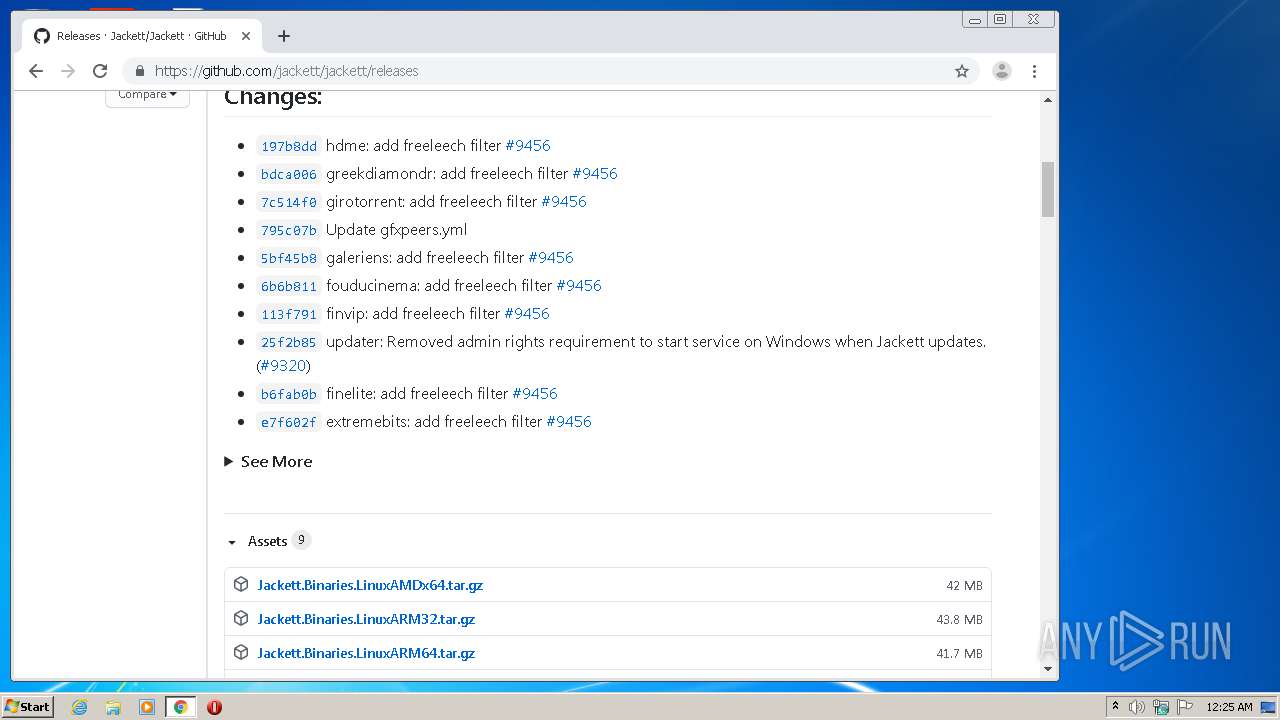
3972 | chrome.exe | GET | 301 | 140.82.121.3:80 | http://github.com/jackett/jackett/releases | US | — | — | malicious |
— | — | GET | — | 67.26.73.254:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | — | — | whitelisted |
— | — | GET | — | 67.26.73.254:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | — | — | whitelisted |
3972 | chrome.exe | GET | 200 | 173.194.5.232:80 | http://r3---sn-aigzrn7l.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWFjQUFXV2lsMkZVdjR5Vk5VZHJTM3E1dw/7919.1028.0.0_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=sX&mip=185.192.70.18&mm=28&mn=sn-aigzrn7l&ms=nvh&mt=1599952939&mv=m&mvi=3&pl=24&shardbypass=yes | US | crx | 834 Kb | whitelisted |
3972 | chrome.exe | GET | 302 | 216.58.208.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWFjQUFXV2lsMkZVdjR5Vk5VZHJTM3E1dw/7919.1028.0.0_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 525 b | whitelisted |
3560 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
3560 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
3560 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
3560 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
— | — | GET | — | 67.26.73.254:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3972 | chrome.exe | 172.217.23.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3972 | chrome.exe | 172.217.22.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
3972 | chrome.exe | 172.217.18.3:443 | www.google.com.ua | Google Inc. | US | whitelisted |
3972 | chrome.exe | 172.217.16.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3972 | chrome.exe | 216.58.212.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3972 | chrome.exe | 172.217.23.110:443 | apis.google.com | Google Inc. | US | whitelisted |
3972 | chrome.exe | 172.217.18.164:443 | www.google.com | Google Inc. | US | whitelisted |
3972 | chrome.exe | 172.217.22.99:443 | www.google.co.uk | Google Inc. | US | whitelisted |
3972 | chrome.exe | 140.82.121.3:80 | github.com | — | US | suspicious |
3972 | chrome.exe | 140.82.121.3:443 | github.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google.com |
| malicious |
www.google.co.uk |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
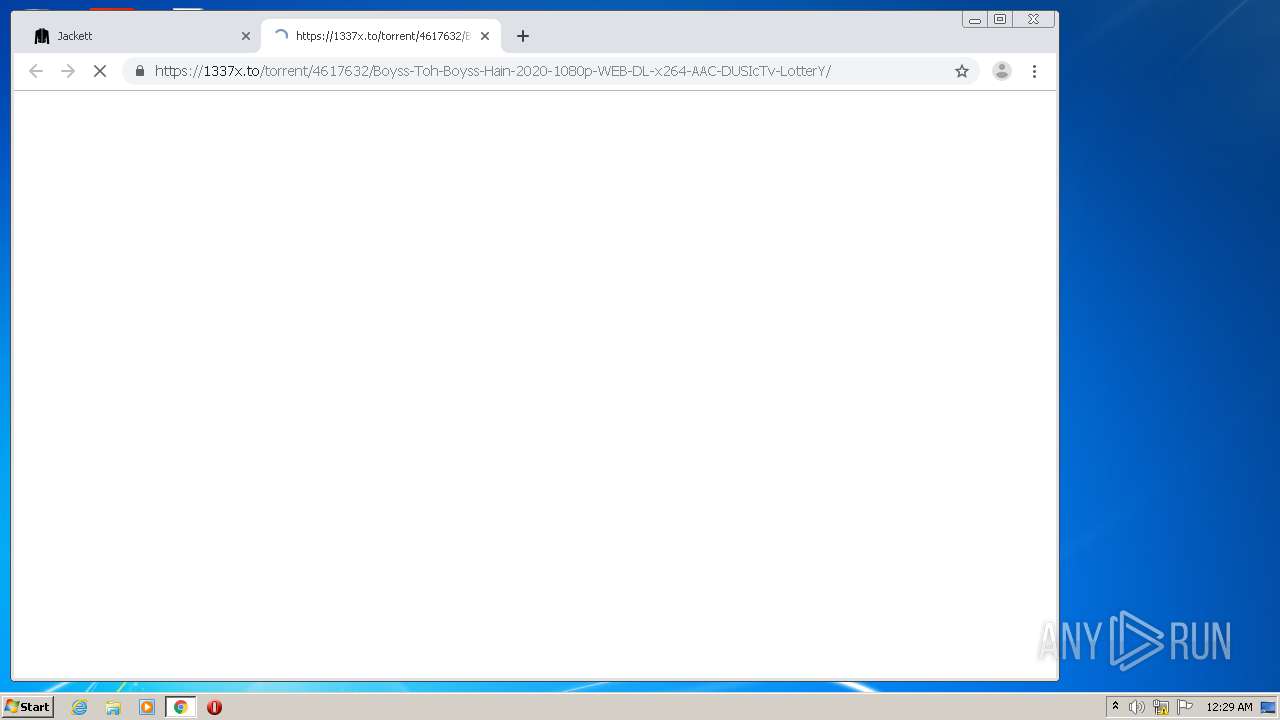
1048 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1048 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1048 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1048 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1048 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1048 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
1048 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1048 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |