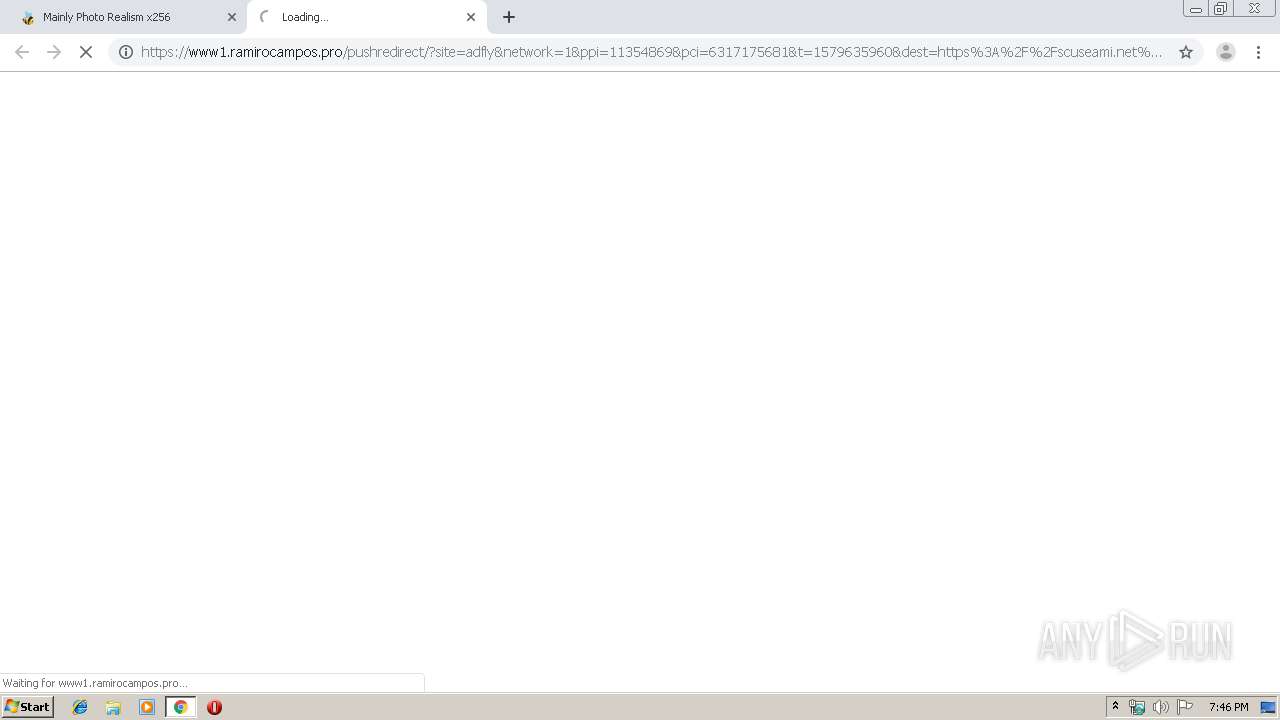
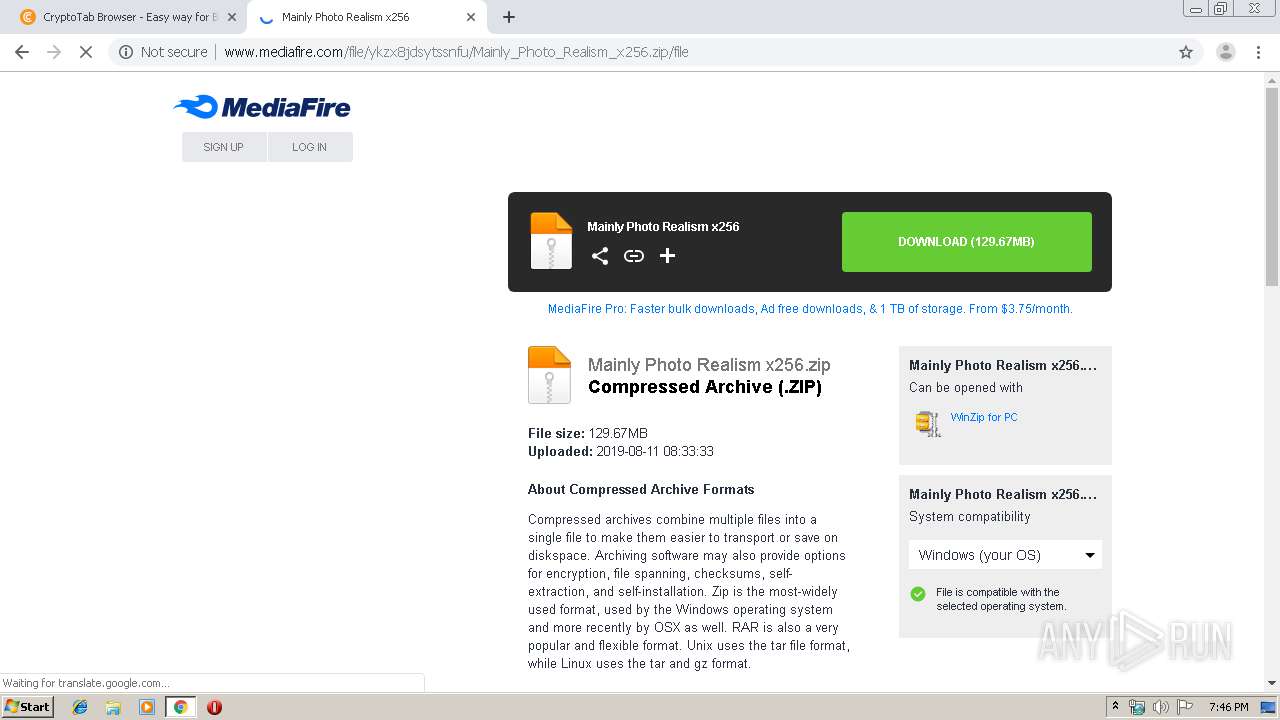
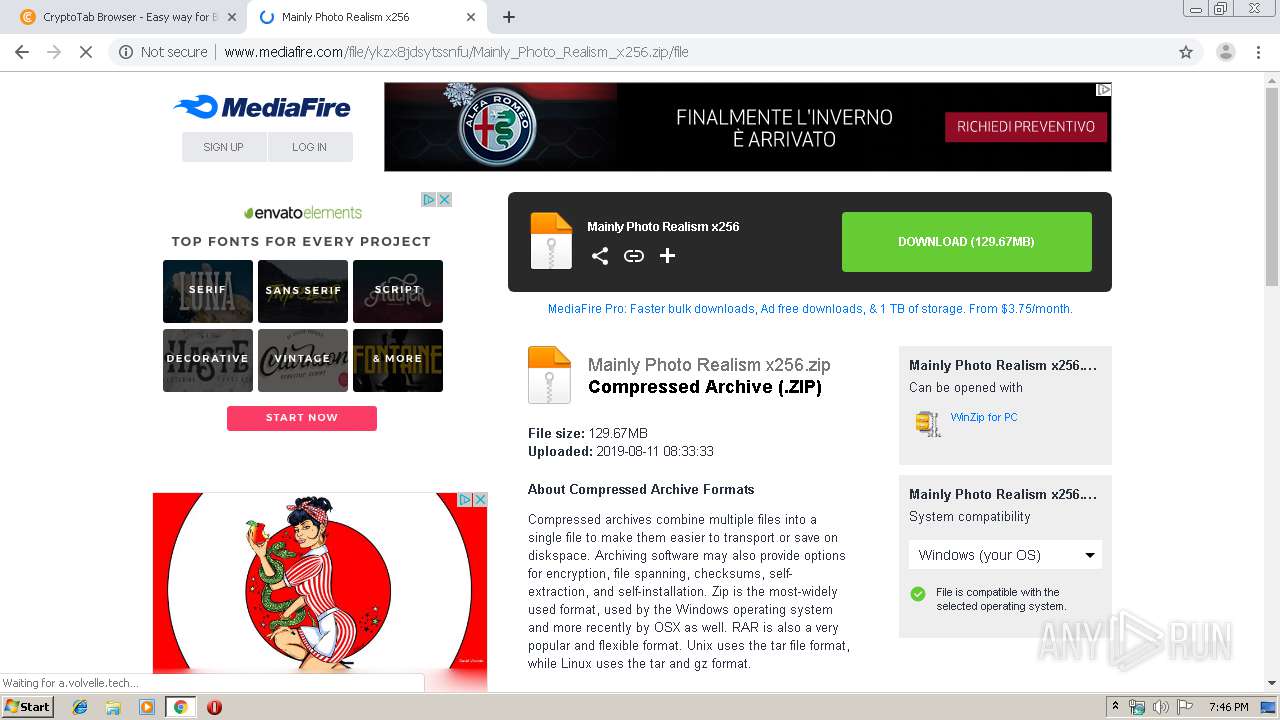
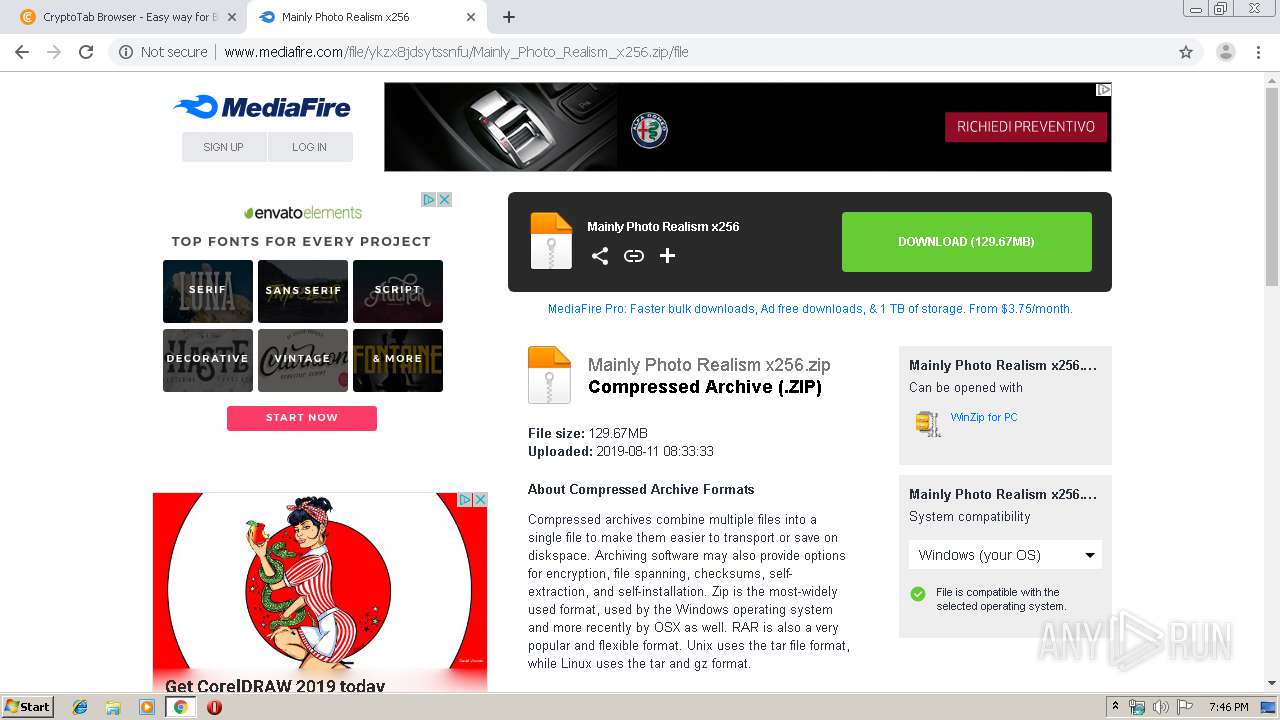
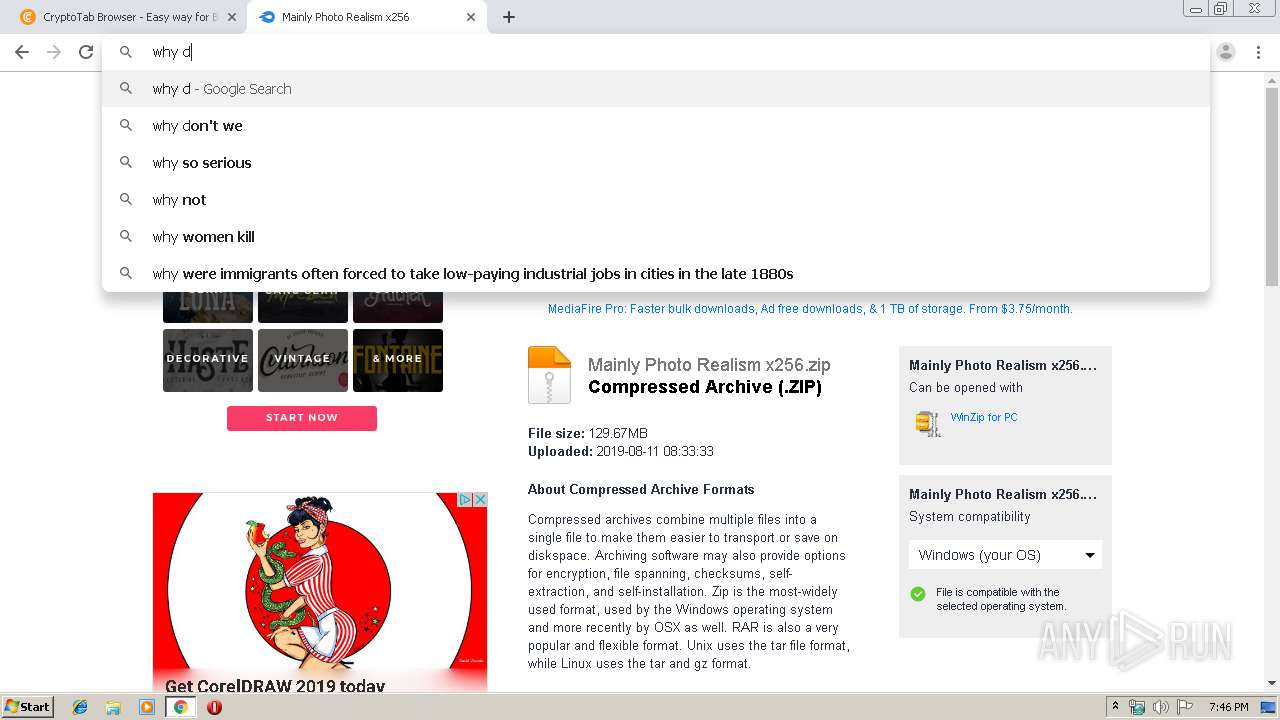
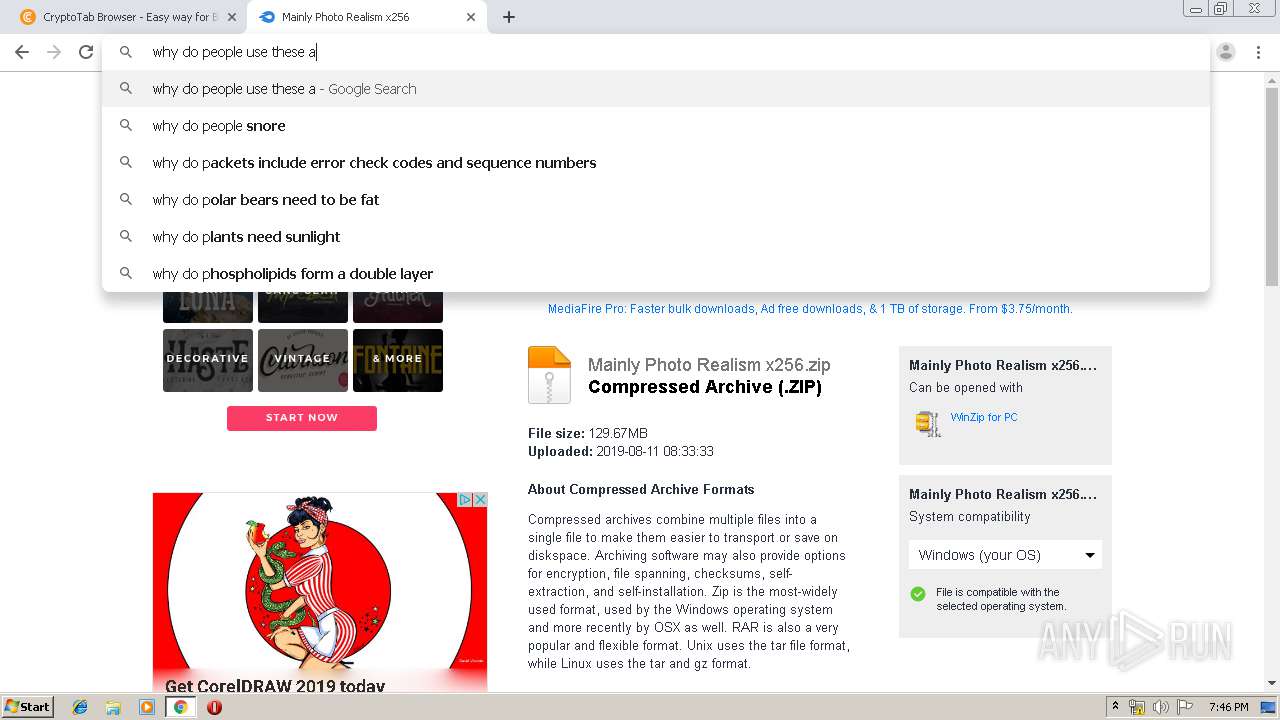
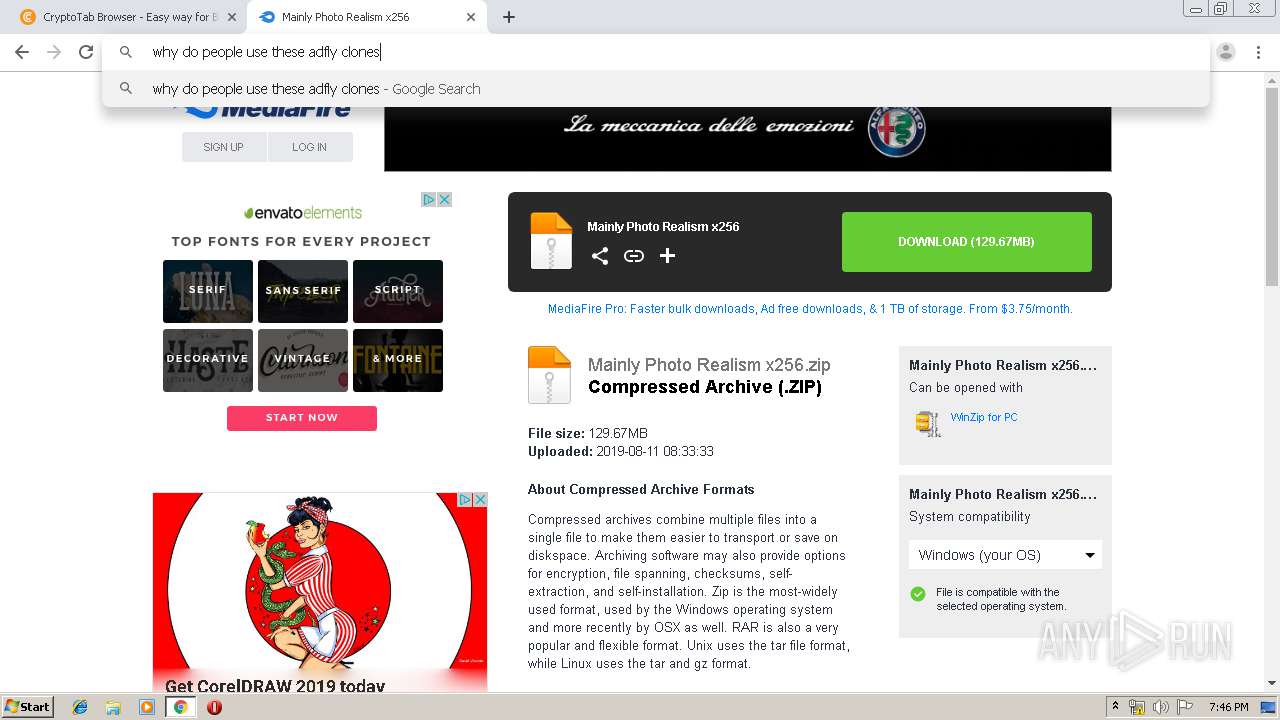
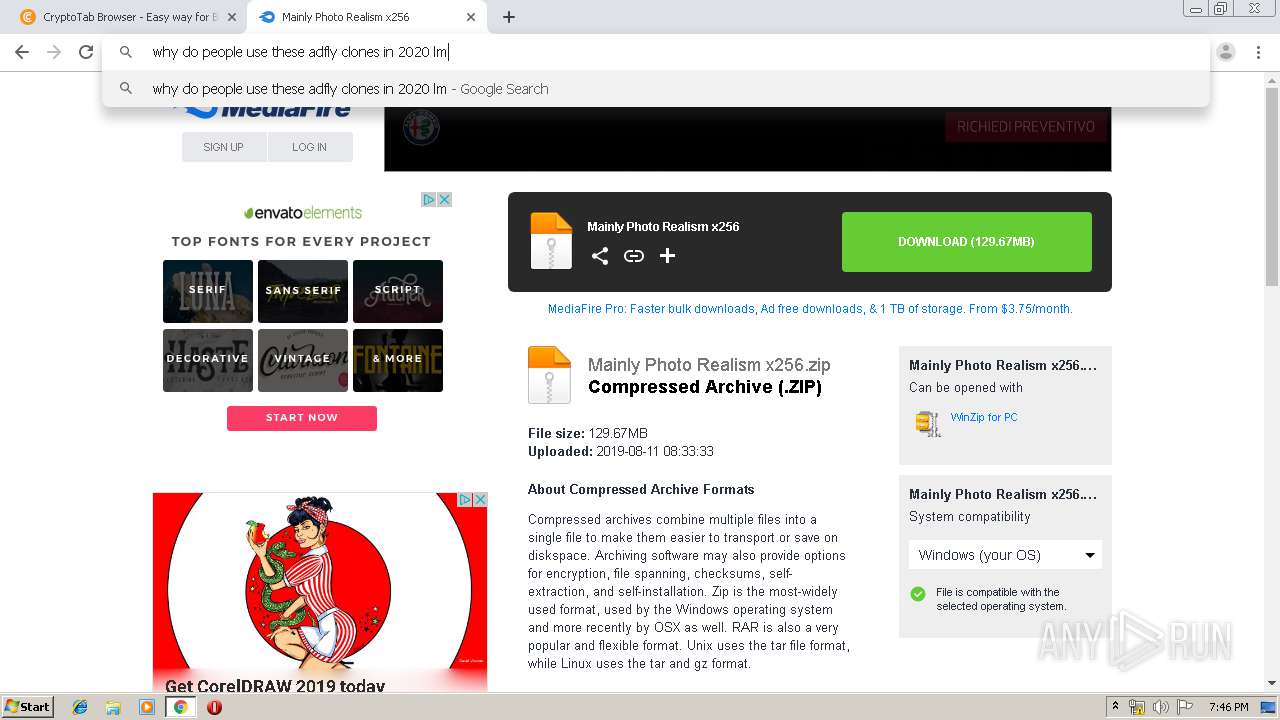
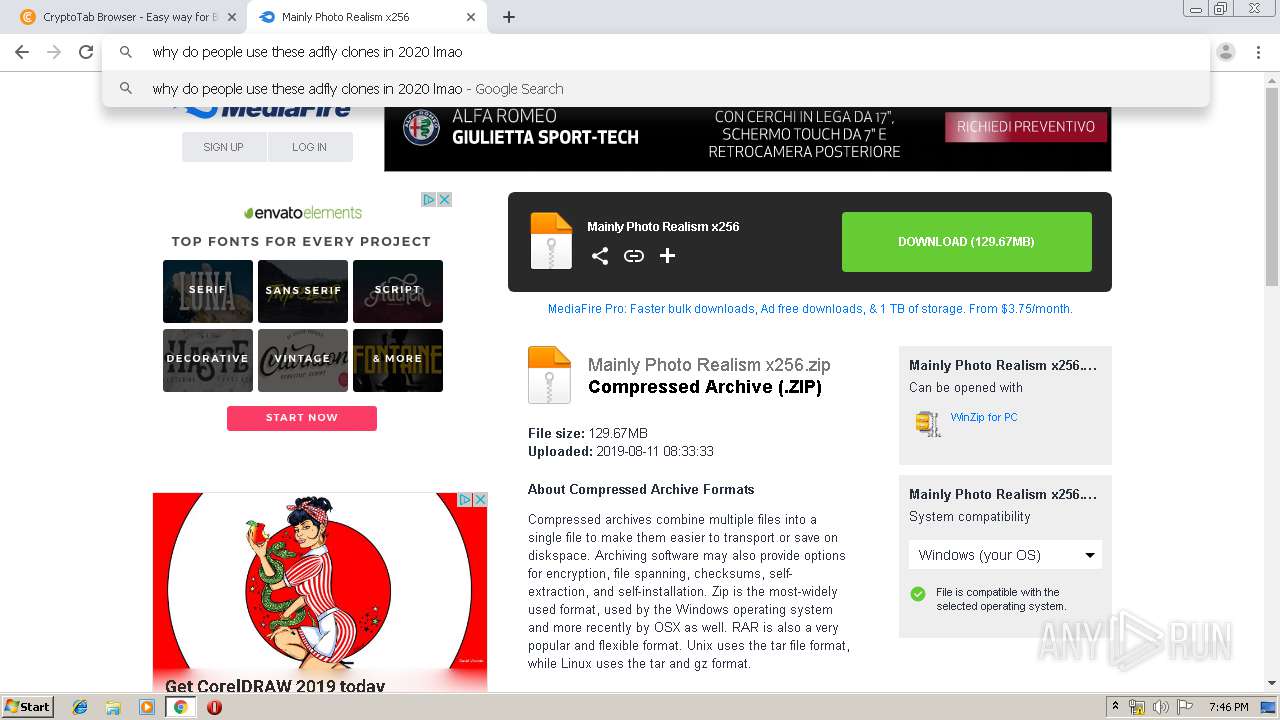
| URL: | http://thacorag.com/11354869/mainly-x256 |
| Full analysis: | https://app.any.run/tasks/146fb261-103e-418e-b08b-76f091b3d7b3 |
| Verdict: | Malicious activity |
| Analysis date: | January 21, 2020, 19:45:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | FF00A195B30C54A0263503EDA4F22915 |
| SHA1: | 17B567F56779258B4FA2C43A46AB58E3438A6EF7 |
| SHA256: | B5A1B4C04CAF019A530A4F59AD7A853EAA9E82DE8F5994D6BD80678F2BFD53D6 |
| SSDEEP: | 3:N1KKNvKeGNW0Tcx9cIVG:CKNvKe1+IVG |
MALICIOUS
No malicious indicators.SUSPICIOUS
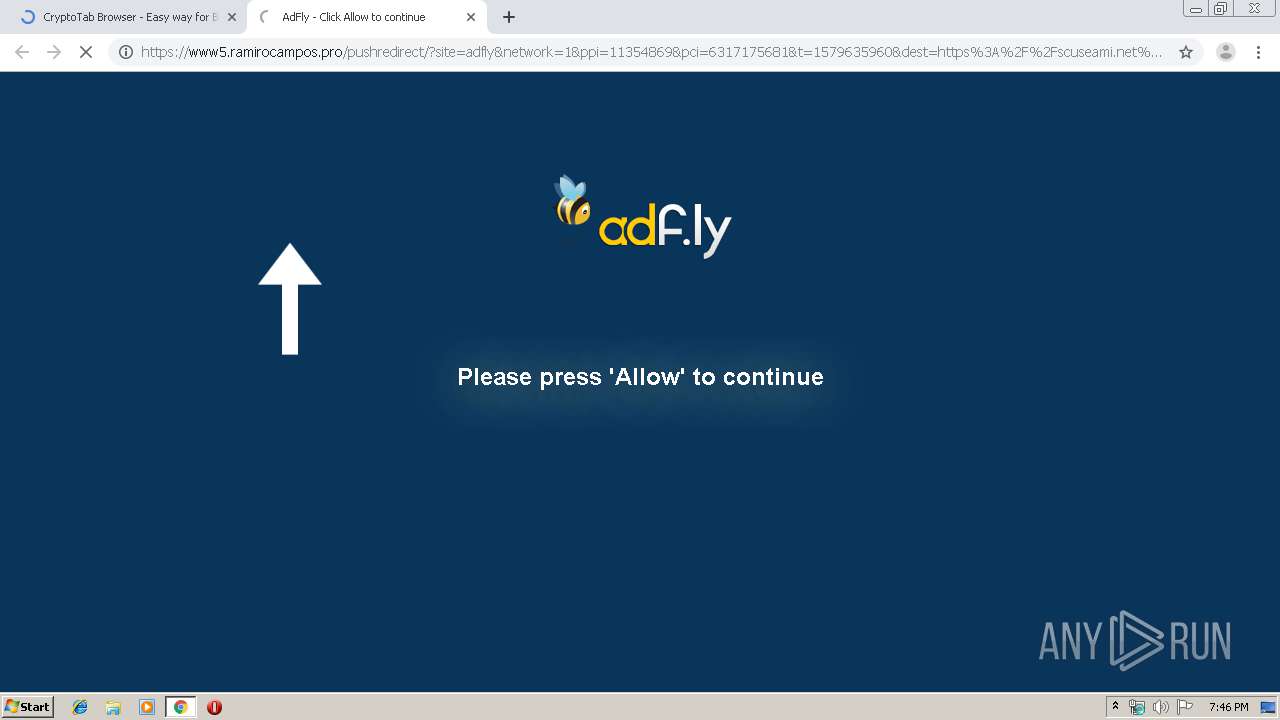
Modifies files in Chrome extension folder
- chrome.exe (PID: 2300)
INFO
Changes settings of System certificates
- chrome.exe (PID: 776)
Reads the hosts file
- chrome.exe (PID: 776)
- chrome.exe (PID: 2300)
Application launched itself
- chrome.exe (PID: 2300)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
87
Monitored processes
52
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,14763338659931527132,5489350501673589381,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8242822488153450021 --renderer-client-id=50 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=924 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,14763338659931527132,5489350501673589381,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2671791377120855922 --renderer-client-id=45 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4676 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,14763338659931527132,5489350501673589381,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4467398170348690575 --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3516 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 776 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,14763338659931527132,5489350501673589381,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=153479418195936643 --mojo-platform-channel-handle=1588 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,14763338659931527132,5489350501673589381,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8151515381926170731 --renderer-client-id=35 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,14763338659931527132,5489350501673589381,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3771375027176814860 --mojo-platform-channel-handle=4472 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1216 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,14763338659931527132,5489350501673589381,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15094752523936175302 --mojo-platform-channel-handle=3712 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,14763338659931527132,5489350501673589381,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12459514954984216095 --renderer-client-id=28 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2256 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1428 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,14763338659931527132,5489350501673589381,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15211363936220244247 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2400 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,14763338659931527132,5489350501673589381,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2624055243626687977 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3076 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
666
Read events
546
Write events
115
Delete events
5
Modification events
| (PID) Process: | (2300) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2300) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2300) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2300) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2300) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2300) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2300) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2300) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2300) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2300) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2300-13224109558473375 |
Value: 259 | |||
Executable files
0
Suspicious files
192
Text files
346
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\90858c2c-d65c-4a23-b072-43b44b509568.tmp | — | |
MD5:— | SHA256:— | |||
| 2300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF39a86f.TMP | text | |
MD5:— | SHA256:— | |||
| 2300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF39a87f.TMP | text | |
MD5:— | SHA256:— | |||
| 2300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF39a860.TMP | text | |
MD5:— | SHA256:— | |||
| 2300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
74
TCP/UDP connections
181
DNS requests
111
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
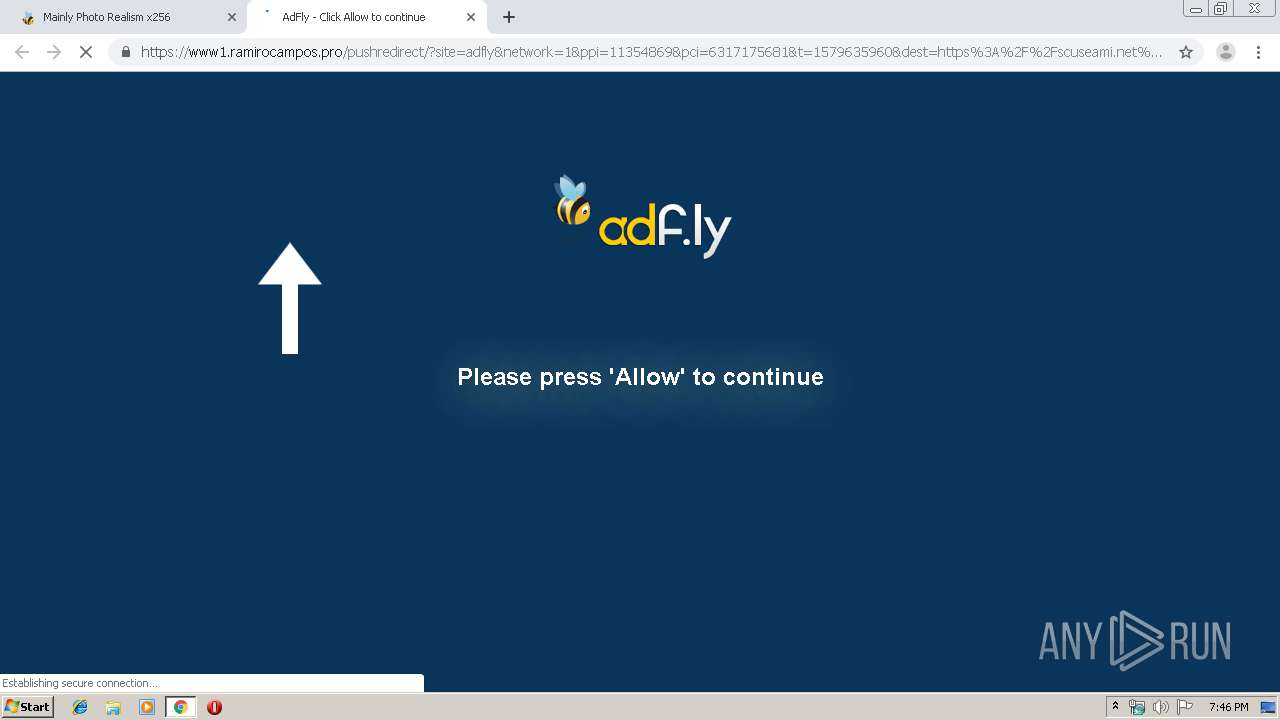
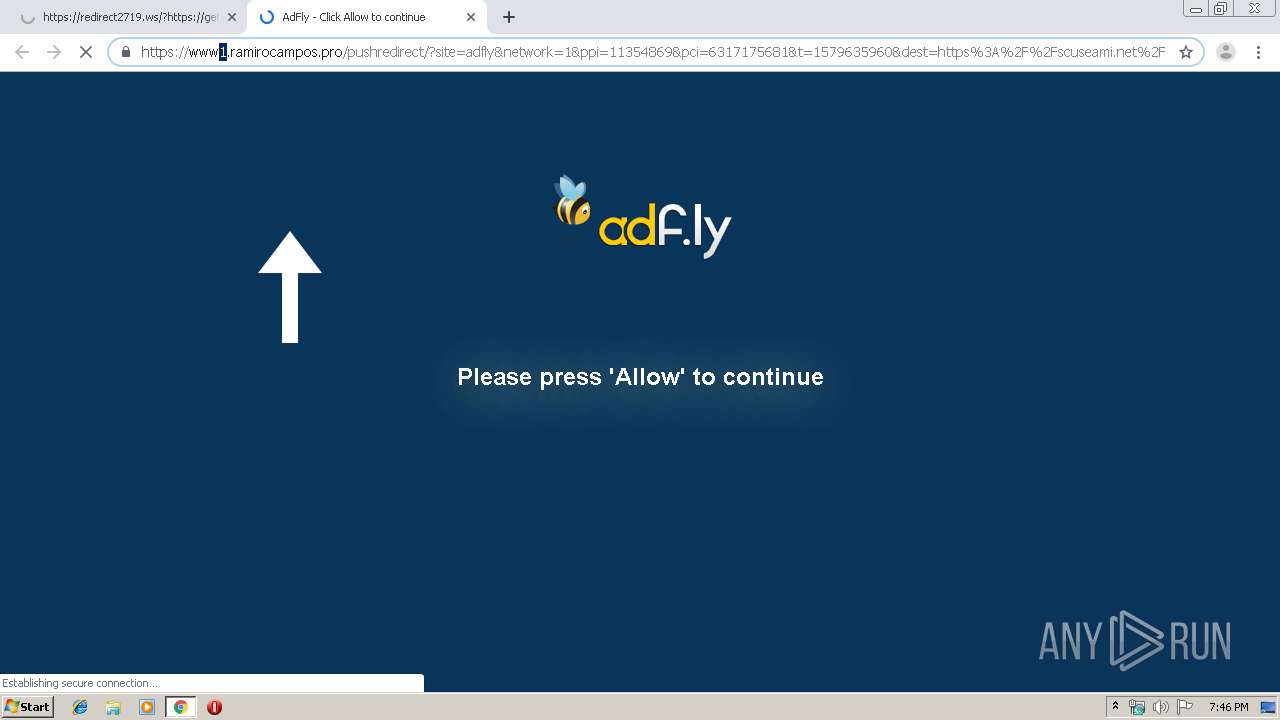
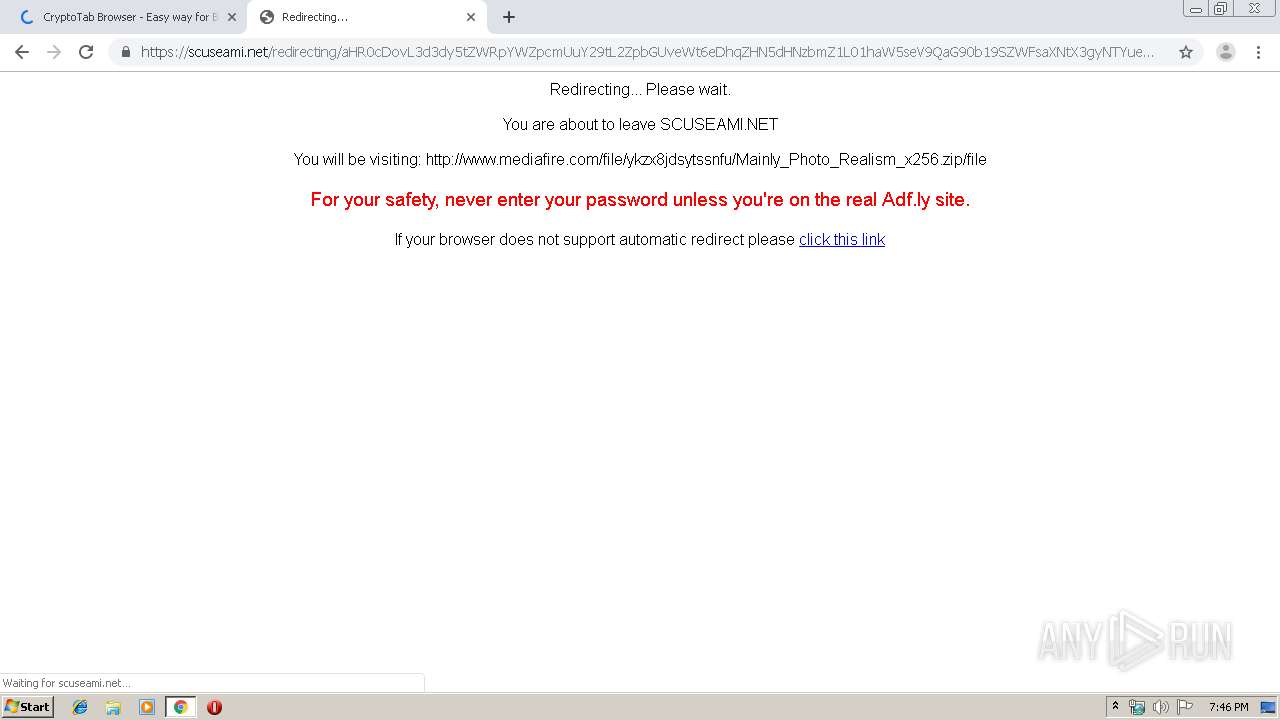
776 | chrome.exe | GET | 301 | 104.31.90.136:80 | http://thacorag.com/11354869/mainly-x256 | US | — | — | suspicious |
776 | chrome.exe | GET | 200 | 172.64.198.39:80 | http://cdn.scuseami.net/static/js/b64.js | US | text | 1.08 Kb | suspicious |
776 | chrome.exe | GET | 200 | 172.64.198.39:80 | http://cdn.scuseami.net/static/js/amvn.js | US | text | 155 Kb | suspicious |
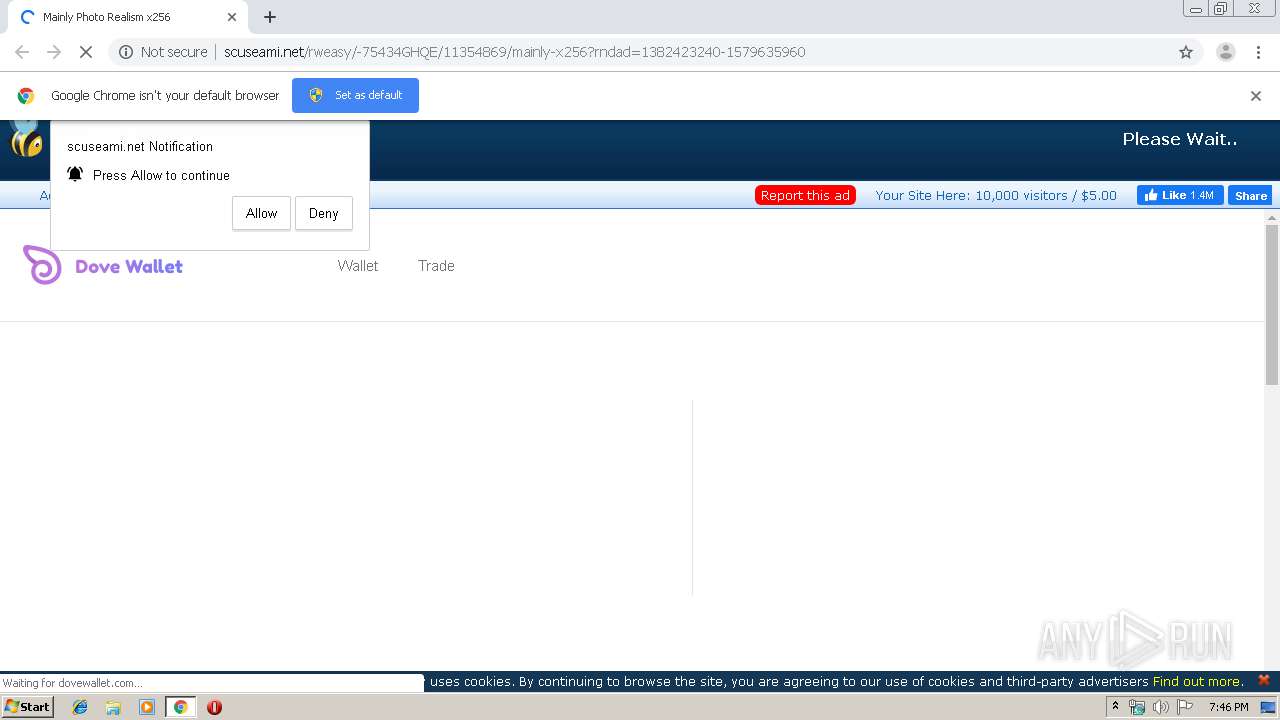
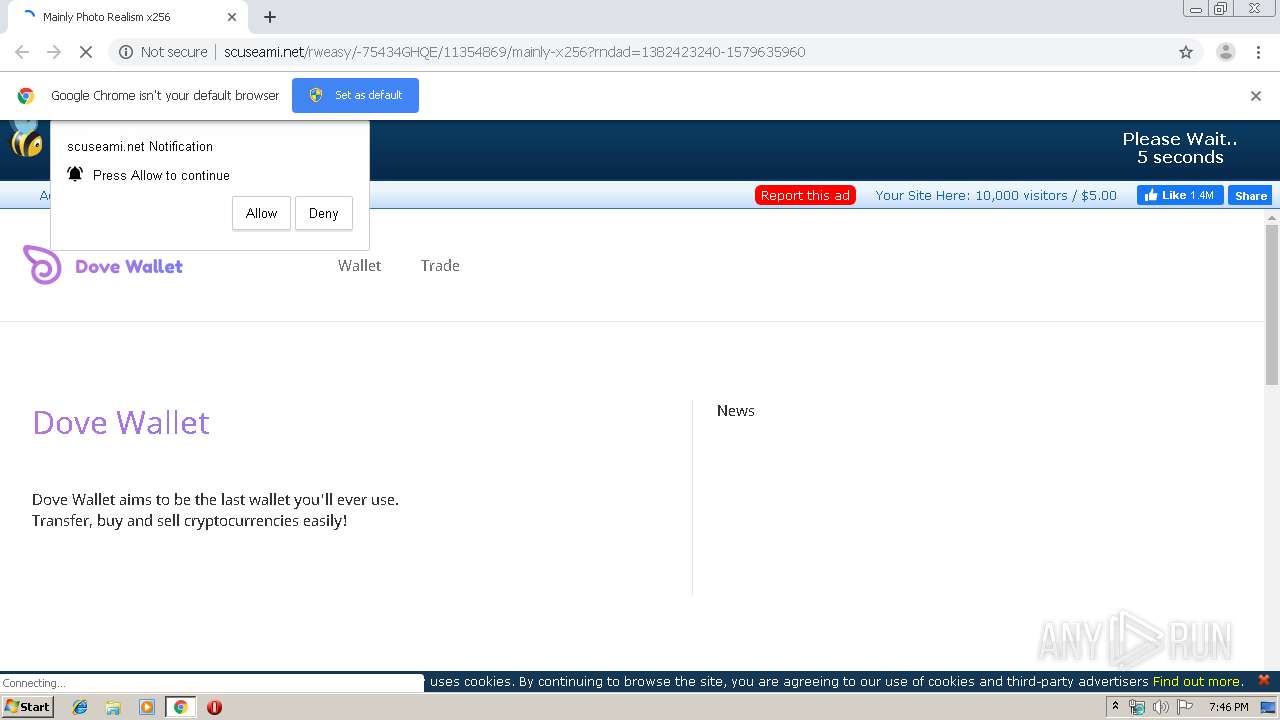
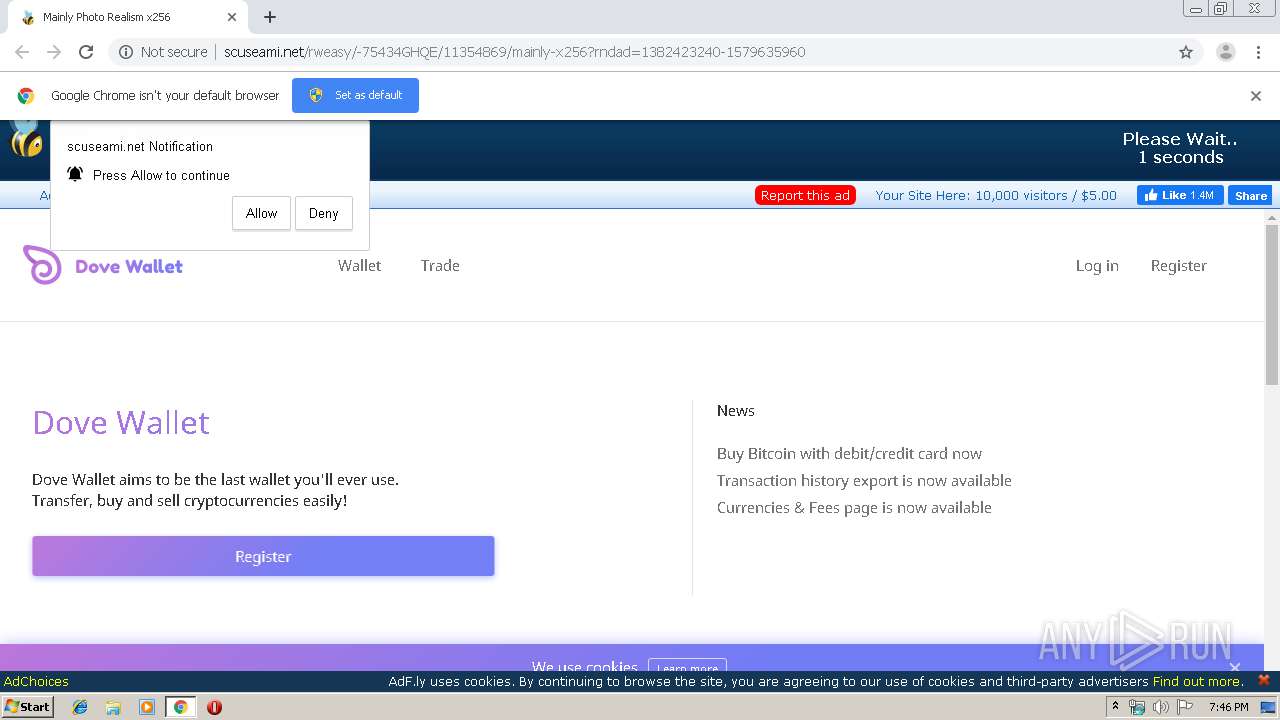
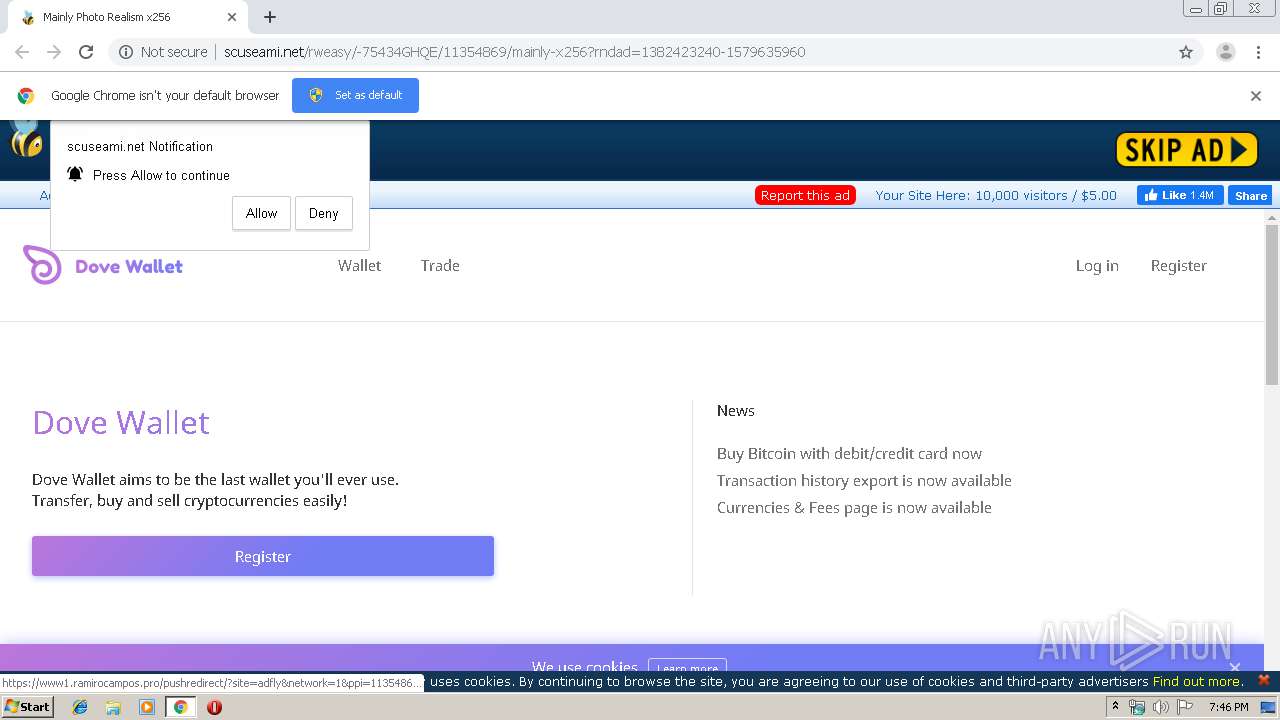
776 | chrome.exe | GET | 200 | 172.64.199.39:80 | http://scuseami.net/rweasy/-75434GHQE/11354869/mainly-x256?rndad=1382423240-1579635960 | US | html | 5.98 Kb | suspicious |
776 | chrome.exe | GET | 200 | 172.64.198.39:80 | http://cdn.scuseami.net/static/js/main.js | US | text | 673 b | suspicious |
776 | chrome.exe | GET | 200 | 172.64.198.39:80 | http://cdn.scuseami.net/static/css/adfly_7.css | US | text | 869 b | suspicious |
776 | chrome.exe | GET | 200 | 172.64.198.39:80 | http://cdn.scuseami.net/static/js/view111.js | US | text | 28.1 Kb | suspicious |
776 | chrome.exe | GET | 200 | 172.64.199.39:80 | http://scuseami.net/funcript1579635964753.php?pub=11354869&v=HaJDvBbSWKUvvtN2zYUludMECI4lztNWzacswBLCjLEMw1MECVBITtYEWKZghYczmMkuvcNzTMM138LCjdMp2tIkiYwliddVWZQsiBOHjcEBxBMSzKUx04OiDNYg5QLlCTJg2MI3jdovyRLmCbJpjdaFyKIg6AdjHLJ118ZSSYwsixcWGaF609IWjToi0oMjiIw0i5YWmZlnuFZmEcVlsNZXWd1ilwbinIQzidO3ibJkz5aW2alXwJXi2OJi1MM3nbRf0Bb32b40itL2CcJloRYmXINsoIIyjboOiJNizOUi4MM3mbJflVMGmbMpwJO2Tbkt0JZCWLIwyoYj2IQlwxOWTakix9NWzbkixwYCjMB6jIZCTaVzjFMGmbUmiJfyQe== | US | text | 62.3 Kb | suspicious |
776 | chrome.exe | GET | 200 | 172.64.199.39:80 | http://scuseami.net/fp.rev11.php?ver=11354869&nocache=8816 | US | text | 12.8 Kb | suspicious |
776 | chrome.exe | GET | 200 | 172.64.199.39:80 | http://scuseami.net/js/display.js | US | text | 12.6 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
776 | chrome.exe | 157.240.20.35:80 | www.facebook.com | Facebook, Inc. | US | whitelisted |
776 | chrome.exe | 37.252.173.38:443 | secure.adnxs.com | AppNexus, Inc | — | unknown |
776 | chrome.exe | 172.217.22.78:443 | clients1.google.com | Google Inc. | US | whitelisted |
776 | chrome.exe | 52.222.149.202:80 | d10lv7w3g0jvk9.cloudfront.net | Amazon.com, Inc. | US | whitelisted |
776 | chrome.exe | 104.18.21.94:443 | resadvantco.info | Cloudflare Inc | US | unknown |
776 | chrome.exe | 172.217.21.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
776 | chrome.exe | 104.31.90.136:80 | thacorag.com | Cloudflare Inc | US | shared |
776 | chrome.exe | 216.58.210.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
776 | chrome.exe | 172.64.199.39:80 | scuseami.net | Cloudflare Inc | US | shared |
776 | chrome.exe | 216.58.207.42:80 | ajax.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
thacorag.com |
| suspicious |
accounts.google.com |
| shared |
scuseami.net |
| suspicious |
ajax.googleapis.com |
| whitelisted |
cdn.scuseami.net |
| suspicious |
d1nmxiiewlx627.cloudfront.net |
| whitelisted |
untypetenthdicket.info |
| unknown |
nielofficieshandl.info |
| suspicious |
nedconstance.info |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
776 | chrome.exe | Attempted User Privilege Gain | AV POLICY Observed Suspicious JScript serving Adware Inbound |
776 | chrome.exe | Attempted User Privilege Gain | AV POLICY Observed Suspicious JScript serving Adware Inbound |