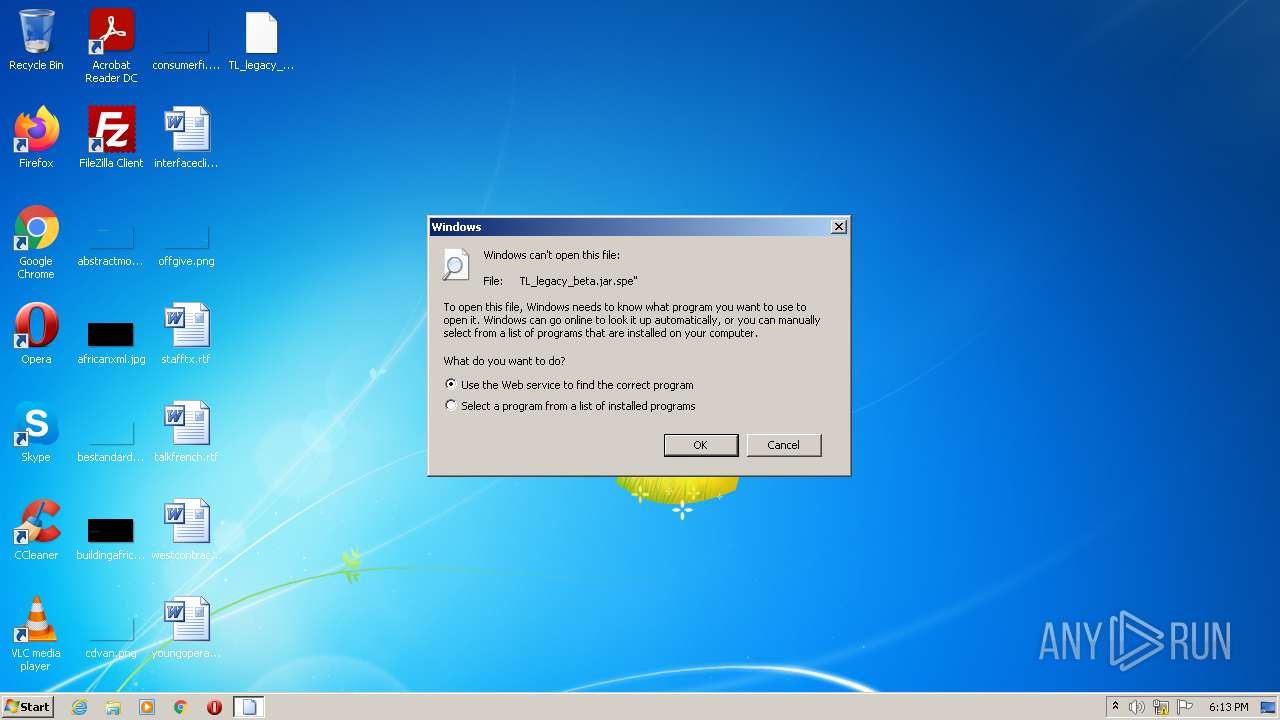
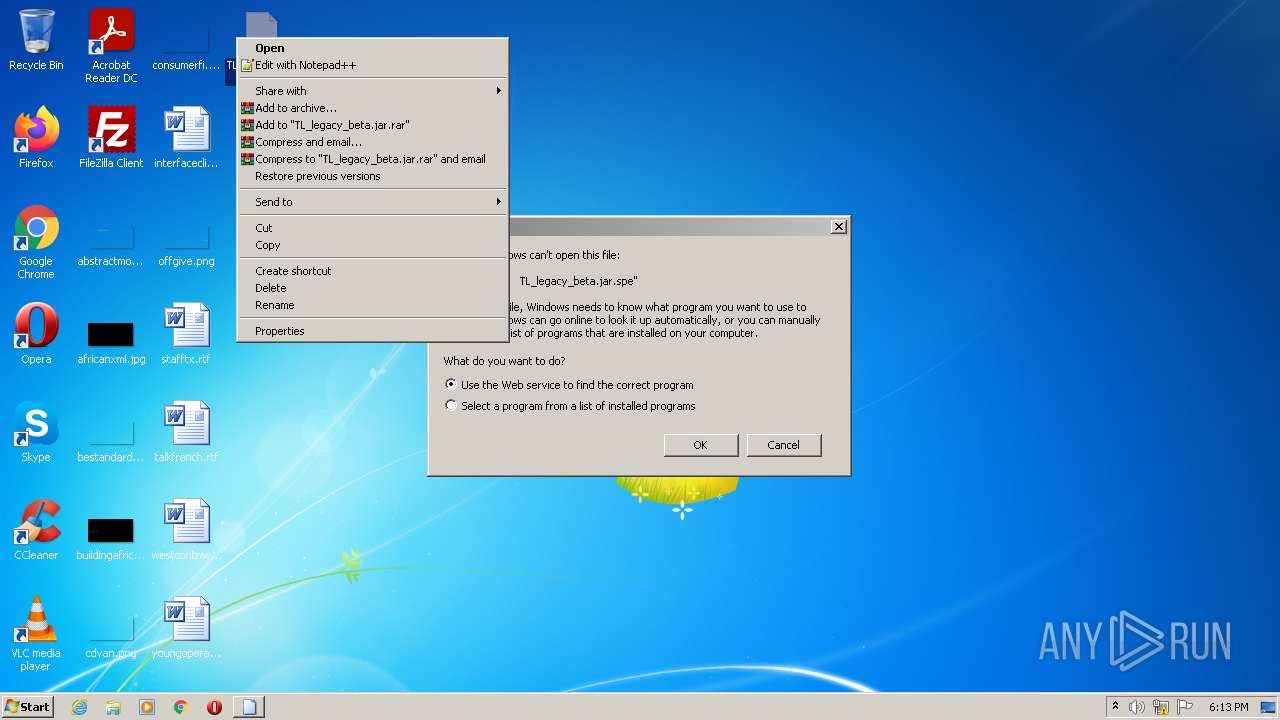
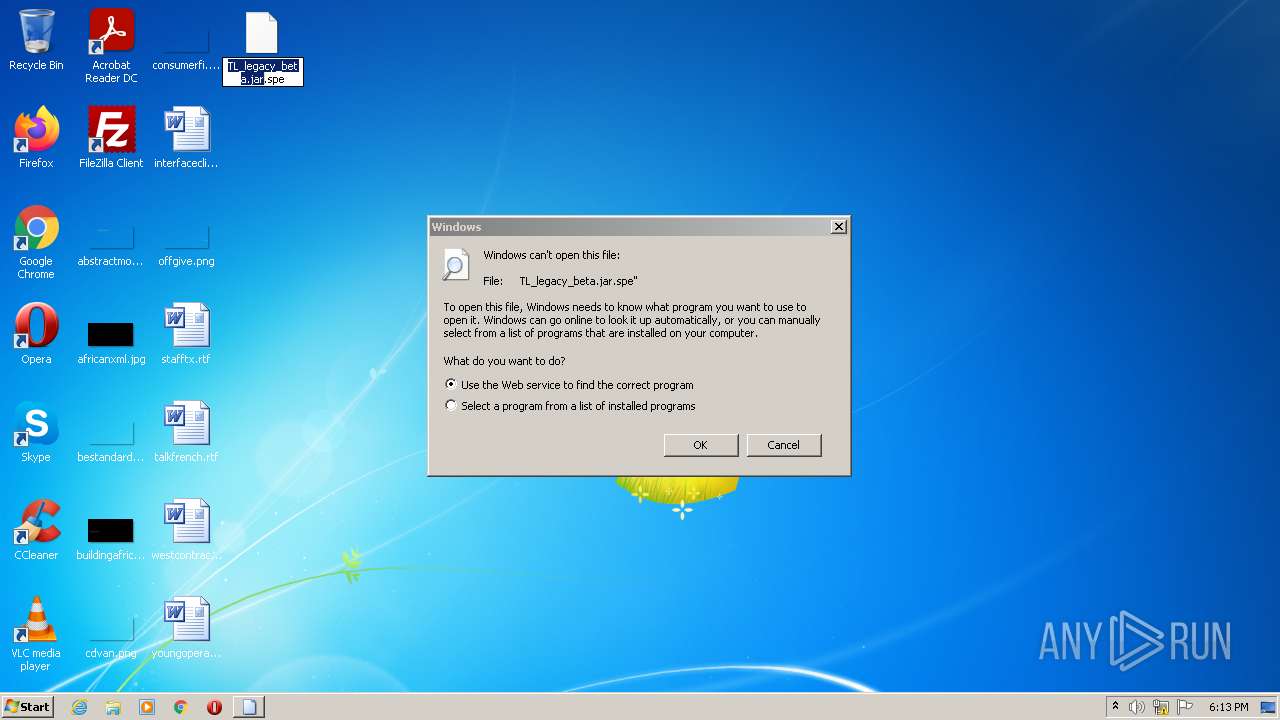
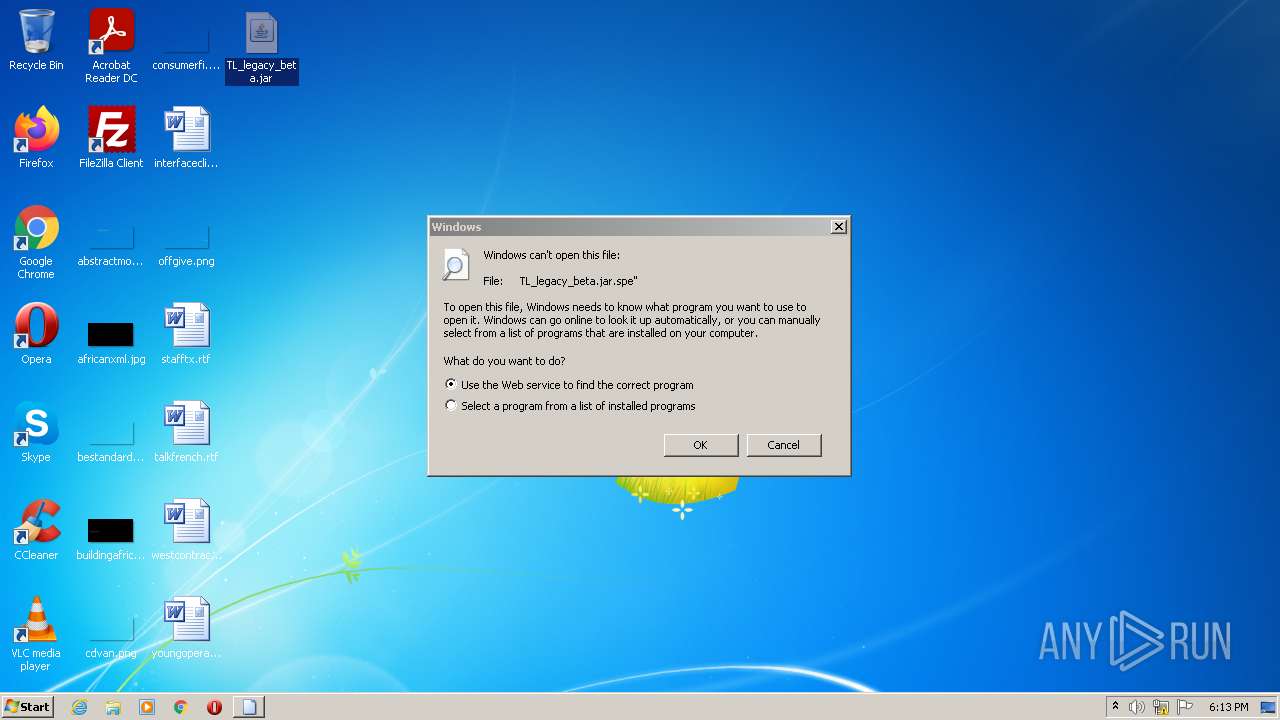
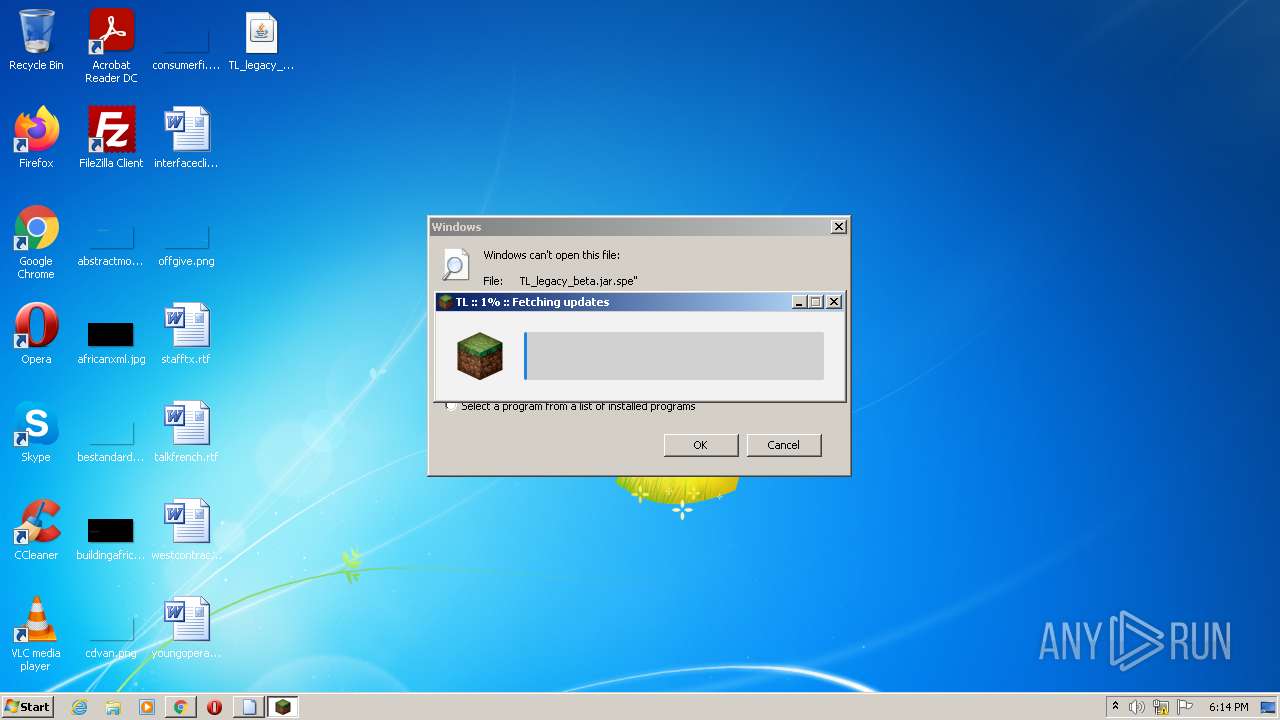
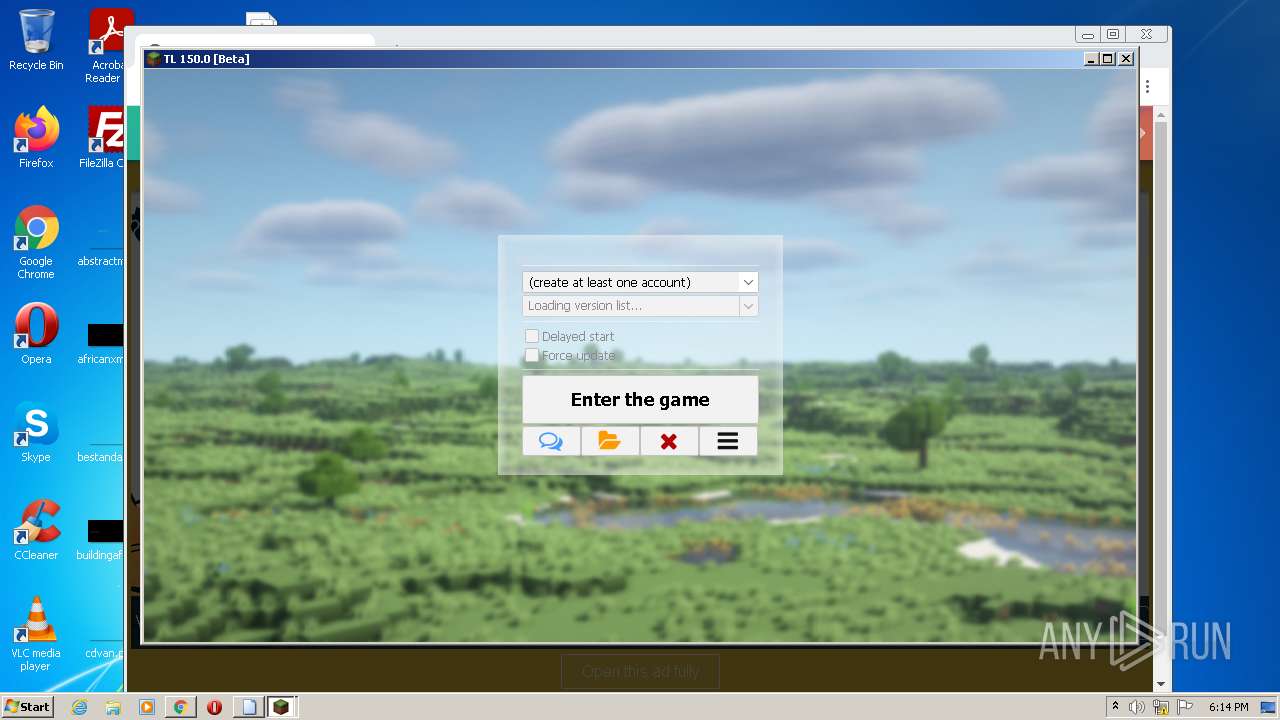
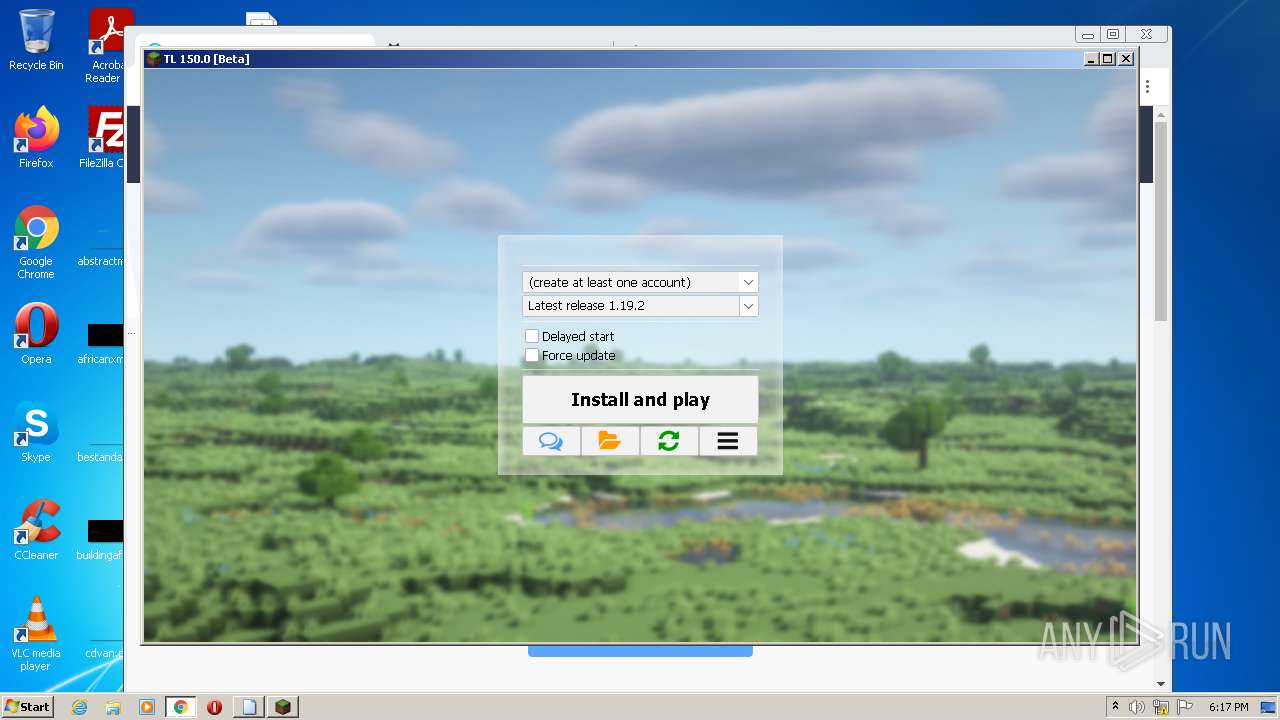
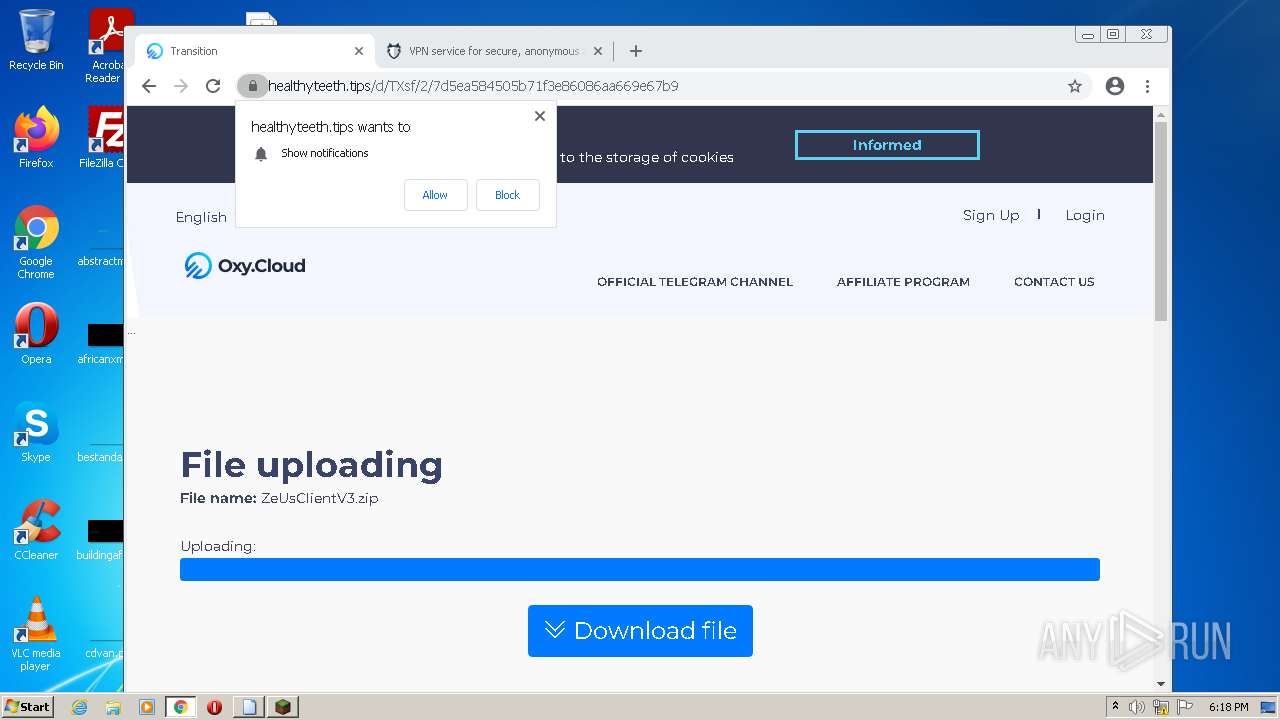
| File name: | TL_legacy_beta.jar |
| Full analysis: | https://app.any.run/tasks/e6ca33d9-9a7c-44d3-8ed8-f03008ba75a7 |
| Verdict: | Malicious activity |
| Analysis date: | August 12, 2022, 17:13:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
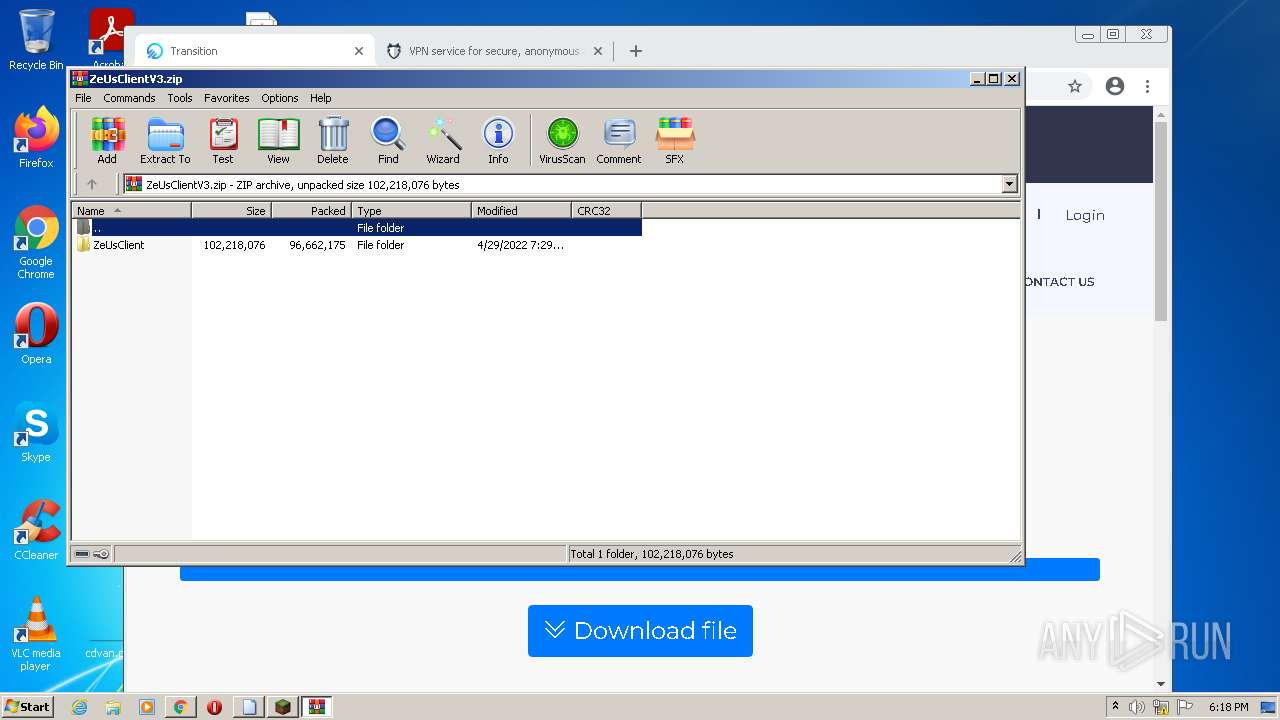
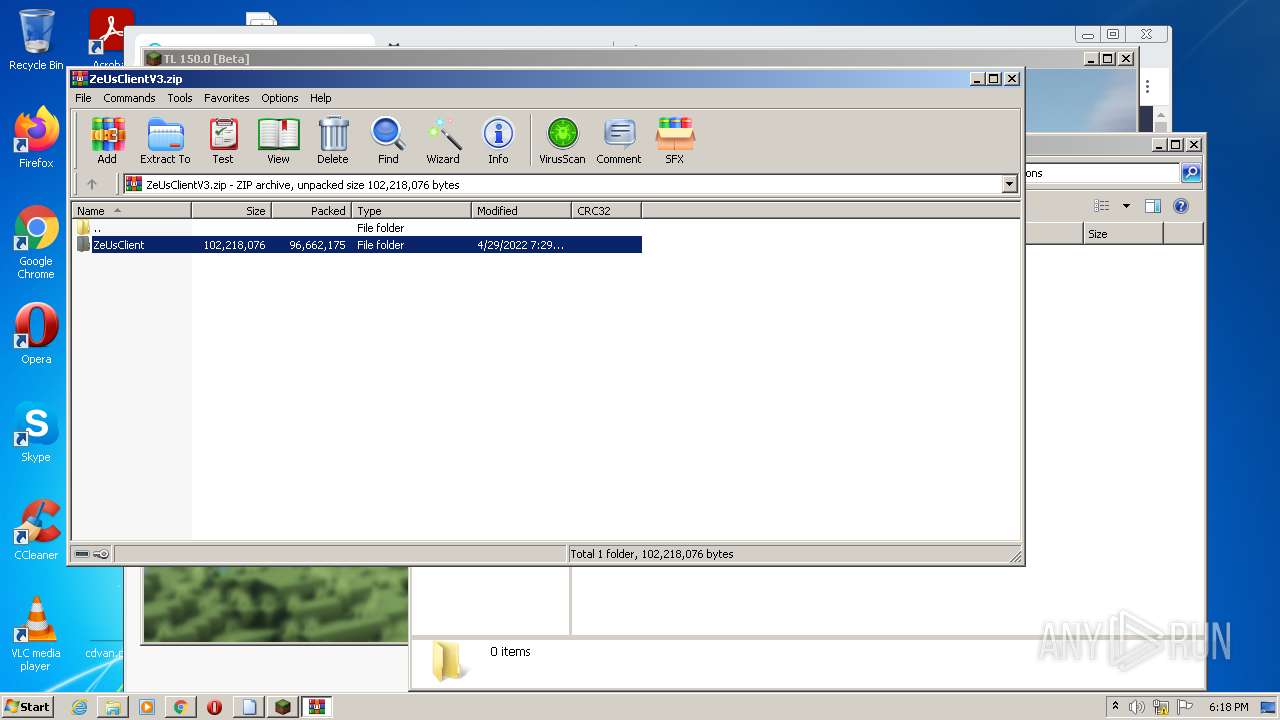
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | 83547D1727806A69E16FE4C6C1417D2C |
| SHA1: | 5655500DC45868B929328A96601807BF81FF2FD2 |
| SHA256: | B59DA929C81B76F2EA1AD1280FEA1D550EFE02FCF89B13E6157E449F51E13617 |
| SSDEEP: | 98304:WfEALdvFlvA8qqrAZfast+9FtMMypuf7qCHPoeefjGlOk:WnhqhJast4zypufmcAfjCOk |
MALICIOUS
Drops executable file immediately after starts
- chrome.exe (PID: 1732)
- chrome.exe (PID: 660)
SUSPICIOUS
Checks supported languages
- javaw.exe (PID: 2948)
- java.exe (PID: 3880)
- WinRAR.exe (PID: 2684)
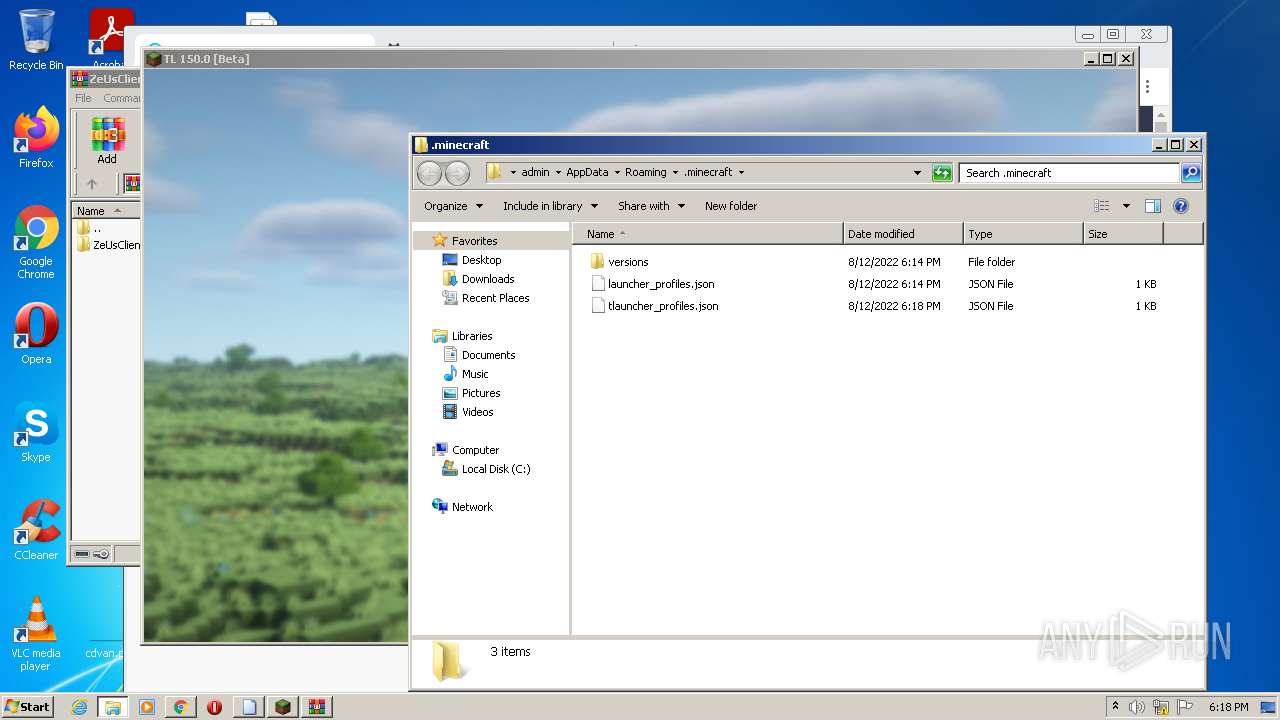
Creates files in the program directory
- javaw.exe (PID: 2948)
Reads the computer name
- java.exe (PID: 3880)
- WinRAR.exe (PID: 2684)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1732)
Drops a file with a compile date too recent
- chrome.exe (PID: 1732)
- chrome.exe (PID: 660)
Executable content was dropped or overwritten
- chrome.exe (PID: 660)
Reads Microsoft Outlook installation path
- chrome.exe (PID: 3600)
INFO
Checks supported languages
- rundll32.exe (PID: 700)
- chrome.exe (PID: 1732)
- chrome.exe (PID: 372)
- chrome.exe (PID: 2700)
- chrome.exe (PID: 3232)
- chrome.exe (PID: 3312)
- chrome.exe (PID: 2664)
- chrome.exe (PID: 3080)
- icacls.exe (PID: 3164)
- chrome.exe (PID: 2376)
- chrome.exe (PID: 3876)
- chrome.exe (PID: 2900)
- chrome.exe (PID: 2584)
- chrome.exe (PID: 2552)
- chrome.exe (PID: 2872)
- chrome.exe (PID: 1072)
- chrome.exe (PID: 3980)
- chrome.exe (PID: 2448)
- chrome.exe (PID: 344)
- chrome.exe (PID: 2612)
- chrome.exe (PID: 2548)
- chrome.exe (PID: 2196)
- chrome.exe (PID: 3352)
- chrome.exe (PID: 3972)
- chrome.exe (PID: 2648)
- chrome.exe (PID: 2760)
- chrome.exe (PID: 1424)
- chrome.exe (PID: 3112)
- chrome.exe (PID: 2232)
- chrome.exe (PID: 1316)
- chrome.exe (PID: 3896)
- chrome.exe (PID: 276)
- chrome.exe (PID: 3804)
- chrome.exe (PID: 2916)
- chrome.exe (PID: 3220)
- chrome.exe (PID: 3000)
- chrome.exe (PID: 660)
- chrome.exe (PID: 1152)
- chrome.exe (PID: 3824)
- chrome.exe (PID: 3020)
- chrome.exe (PID: 2472)
- chrome.exe (PID: 3312)
- chrome.exe (PID: 3220)
- chrome.exe (PID: 1276)
- chrome.exe (PID: 696)
- chrome.exe (PID: 3836)
- chrome.exe (PID: 3548)
- chrome.exe (PID: 3912)
- chrome.exe (PID: 3112)
- chrome.exe (PID: 4068)
- chrome.exe (PID: 808)
- chrome.exe (PID: 1884)
- chrome.exe (PID: 2776)
- chrome.exe (PID: 3572)
- chrome.exe (PID: 2992)
- chrome.exe (PID: 1880)
- chrome.exe (PID: 3748)
- chrome.exe (PID: 2380)
- chrome.exe (PID: 1884)
- chrome.exe (PID: 3604)
- chrome.exe (PID: 3696)
- chrome.exe (PID: 3416)
- chrome.exe (PID: 268)
- chrome.exe (PID: 2784)
- chrome.exe (PID: 3600)
Reads the computer name
- icacls.exe (PID: 3164)
- chrome.exe (PID: 1732)
- chrome.exe (PID: 2664)
- chrome.exe (PID: 2700)
- chrome.exe (PID: 2376)
- chrome.exe (PID: 2612)
- chrome.exe (PID: 3112)
- chrome.exe (PID: 276)
- chrome.exe (PID: 3896)
- chrome.exe (PID: 1152)
- chrome.exe (PID: 1884)
- chrome.exe (PID: 268)
- chrome.exe (PID: 3600)
- chrome.exe (PID: 2784)
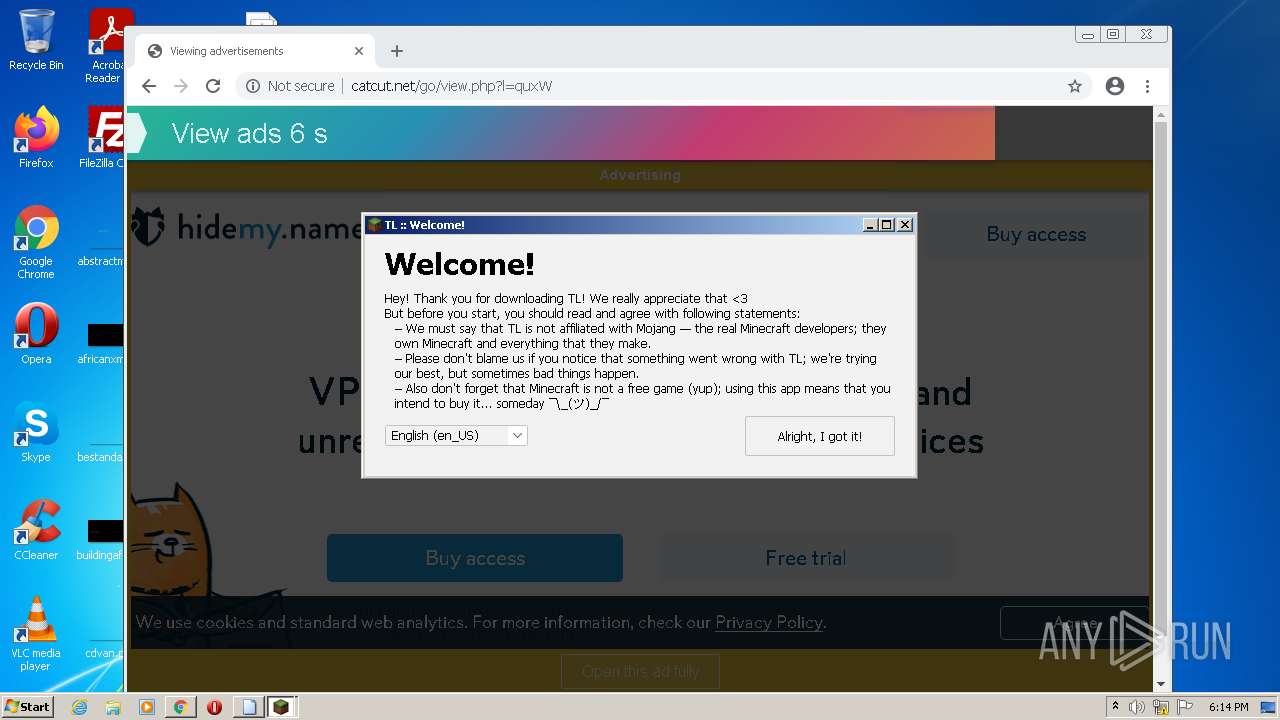
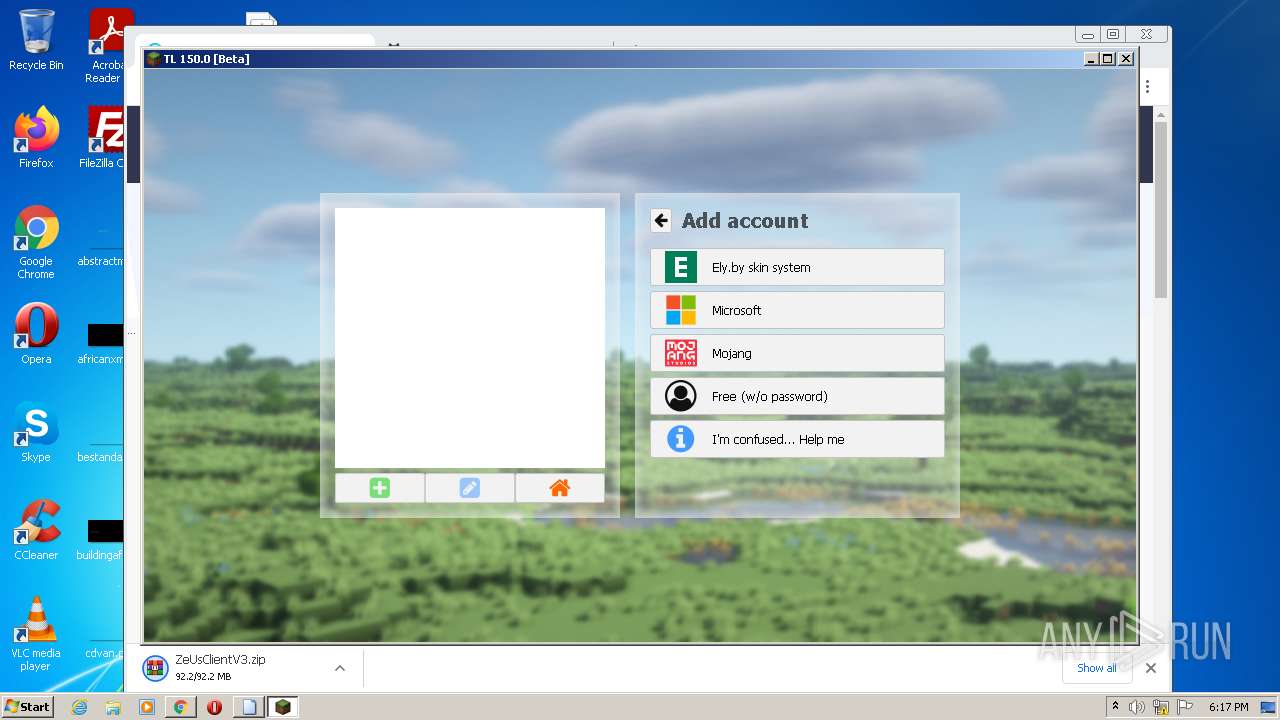
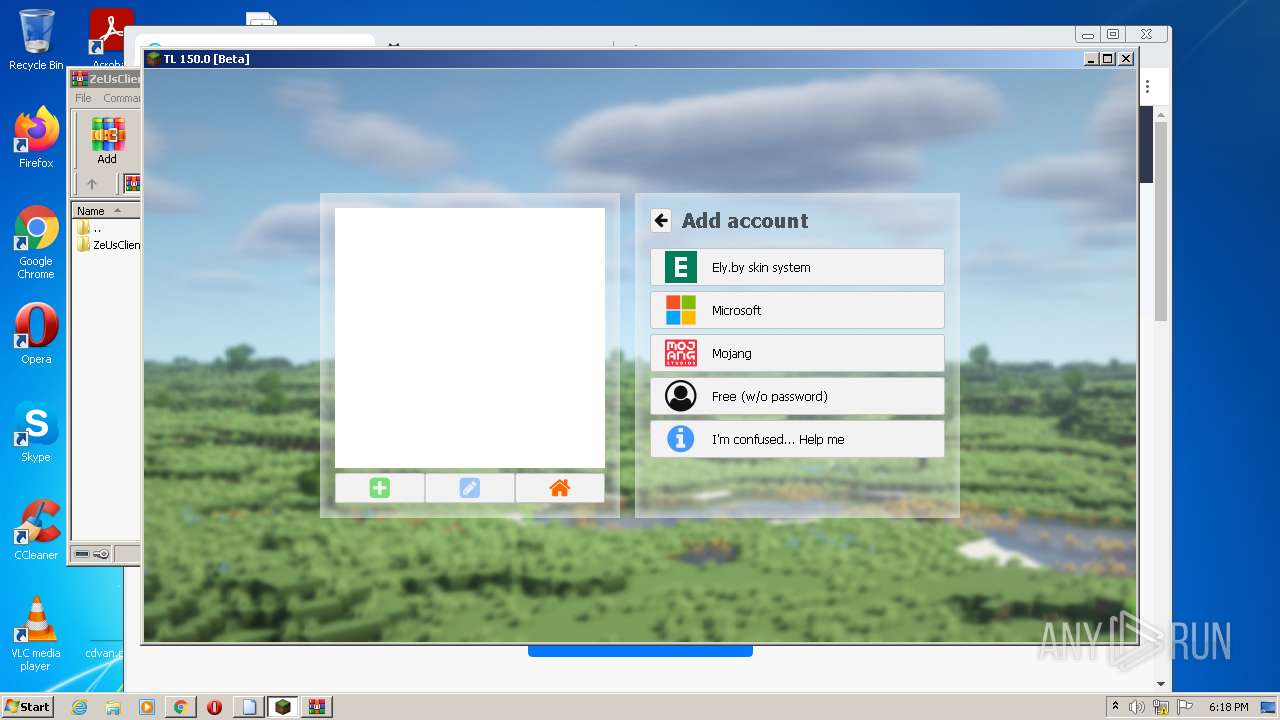
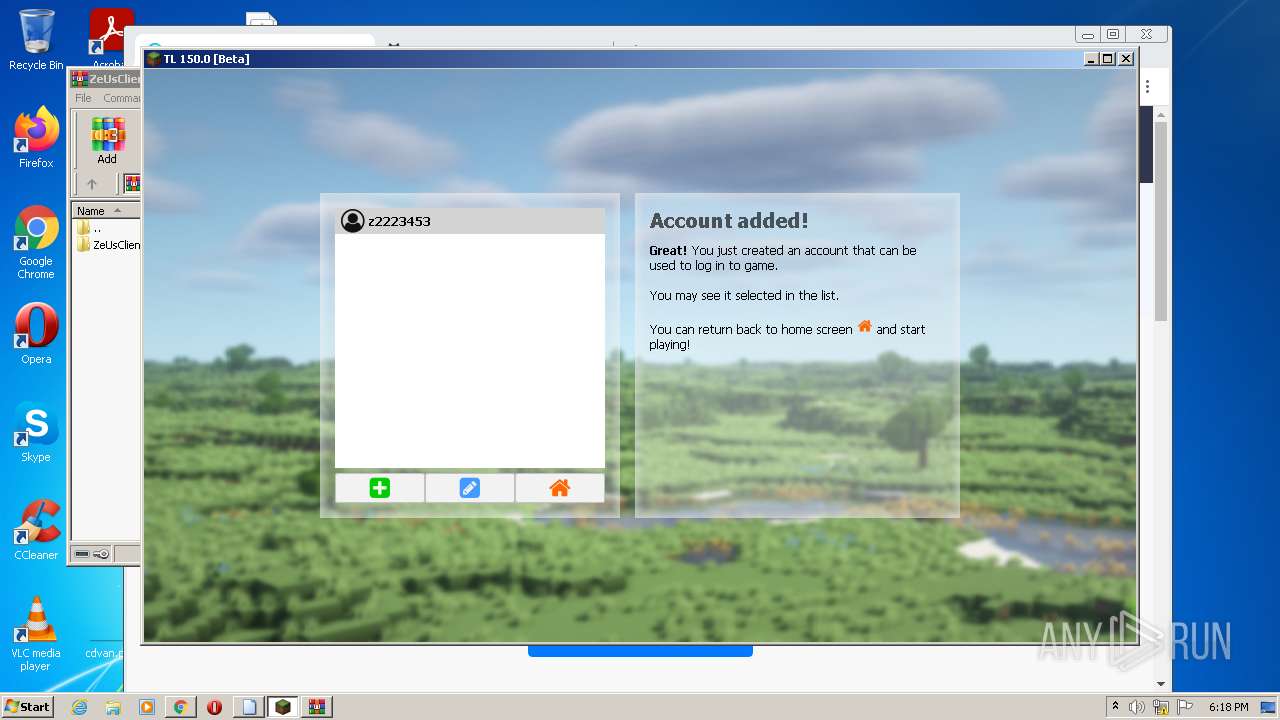
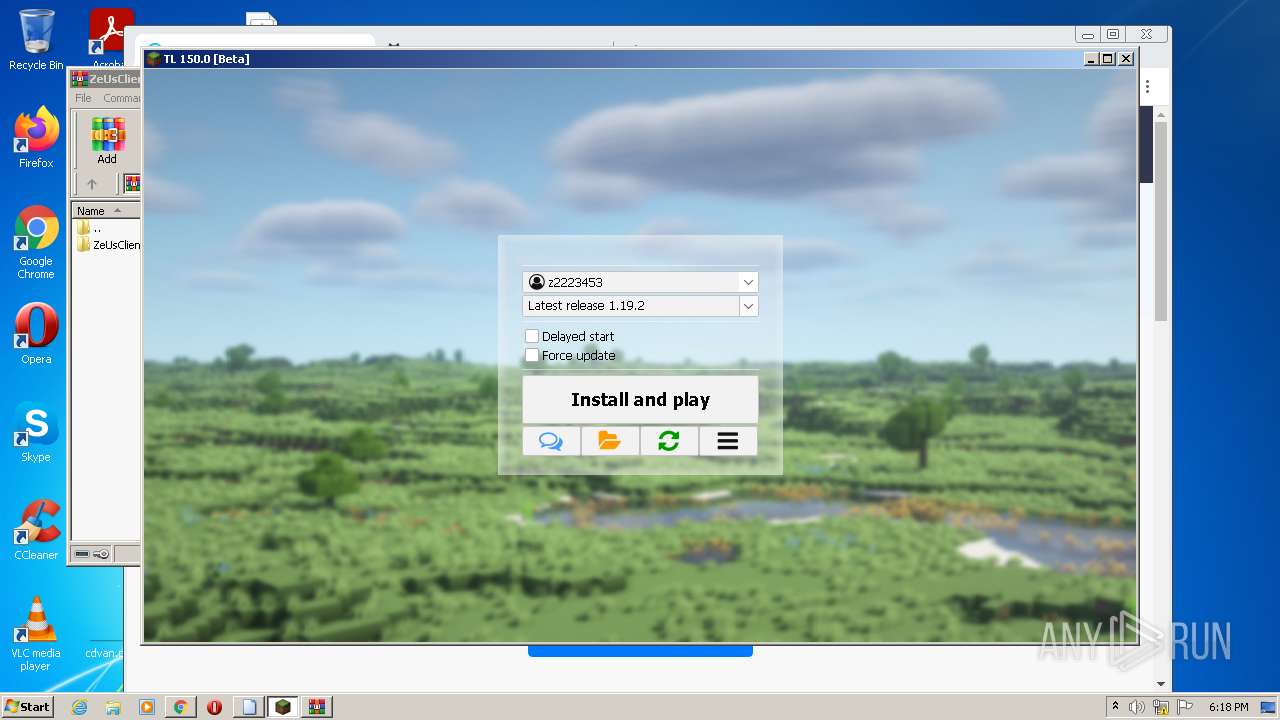
Manual execution by user
- javaw.exe (PID: 2948)
- chrome.exe (PID: 1732)
Application launched itself
- chrome.exe (PID: 1732)
Reads settings of System Certificates
- chrome.exe (PID: 2700)
Reads the date of Windows installation
- chrome.exe (PID: 276)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .spe | | | SPSS Extension (54) |
|---|---|---|
| .jar | | | Java Archive (26.1) |
| .zip | | | ZIP compressed archive (7.2) |
EXIF
ZIP
| ZipFileName: | META-INF/ |
|---|---|
| ZipUncompressedSize: | - |
| ZipCompressedSize: | 2 |
| ZipCRC: | 0x00000000 |
| ZipModifyDate: | 1980:02:01 00:00:00 |
| ZipCompression: | Deflated |
| ZipBitFlag: | 0x0800 |
| ZipRequiredVersion: | 10 |
Total processes
110
Monitored processes
68
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 268 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1040,11933534931536665065,2015693081905396810,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=532 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1040,11933534931536665065,2015693081905396810,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3980 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1040,11933534931536665065,2015693081905396810,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3188 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6dcfd988,0x6dcfd998,0x6dcfd9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1040,11933534931536665065,2015693081905396810,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3260 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 696 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,11933534931536665065,2015693081905396810,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=37 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2076 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 700 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL "C:\Users\admin\Desktop\TL_legacy_beta.jar.spe" | C:\Windows\system32\rundll32.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 808 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,11933534931536665065,2015693081905396810,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=48 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3820 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1072 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1040,11933534931536665065,2015693081905396810,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3564 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1152 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1040,11933534931536665065,2015693081905396810,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3020 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
23 526
Read events
23 294
Write events
224
Delete events
8
Modification events
| (PID) Process: | (3880) java.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: java.exe | |||
| (PID) Process: | (1732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1732) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
21
Suspicious files
320
Text files
251
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-62F68A5C-6C4.pma | — | |
MD5:— | SHA256:— | |||
| 2948 | javaw.exe | C:\ProgramData\Oracle\Java\.oracle_jre_usage\17dfc292991c8061.timestamp | text | |
MD5:— | SHA256:— | |||
| 1732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\8bfd6382-9cfa-4258-9e0a-a0186d0abf97.tmp | text | |
MD5:— | SHA256:— | |||
| 2700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\index | binary | |
MD5:— | SHA256:— | |||
| 1732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 1732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 1732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 1732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF129821.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 1732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
46
TCP/UDP connections
119
DNS requests
103
Threats
9
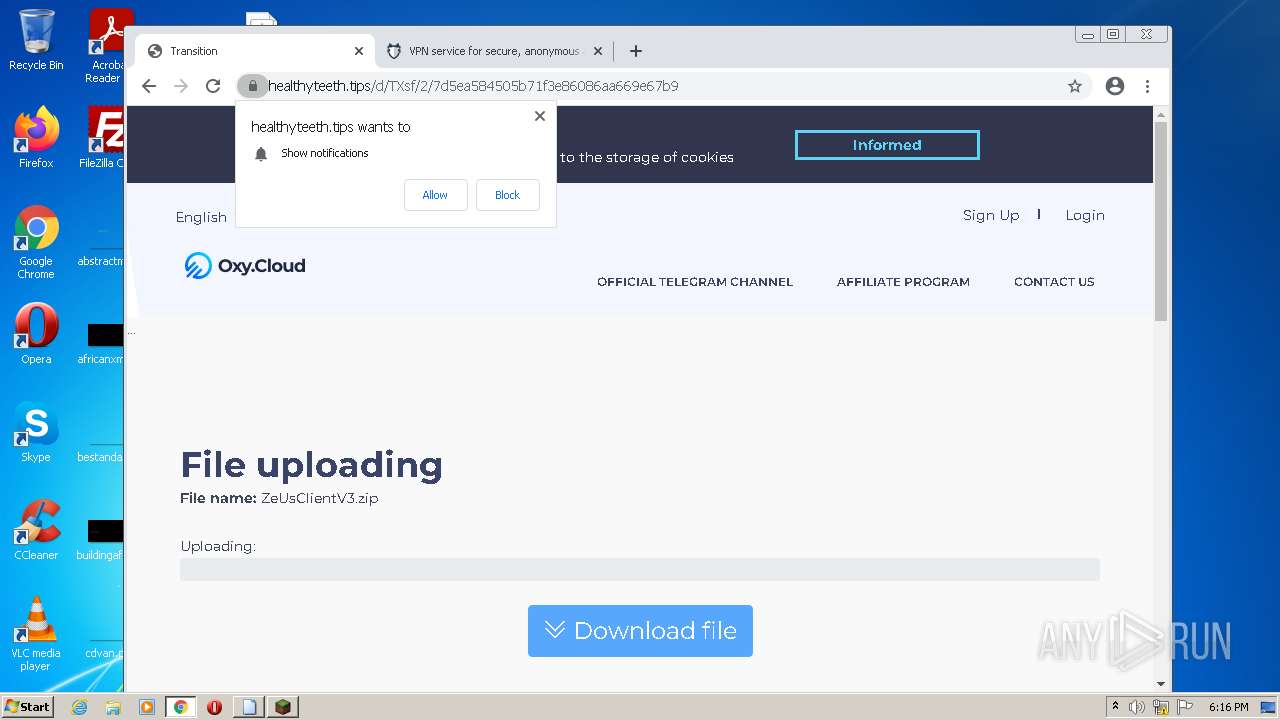
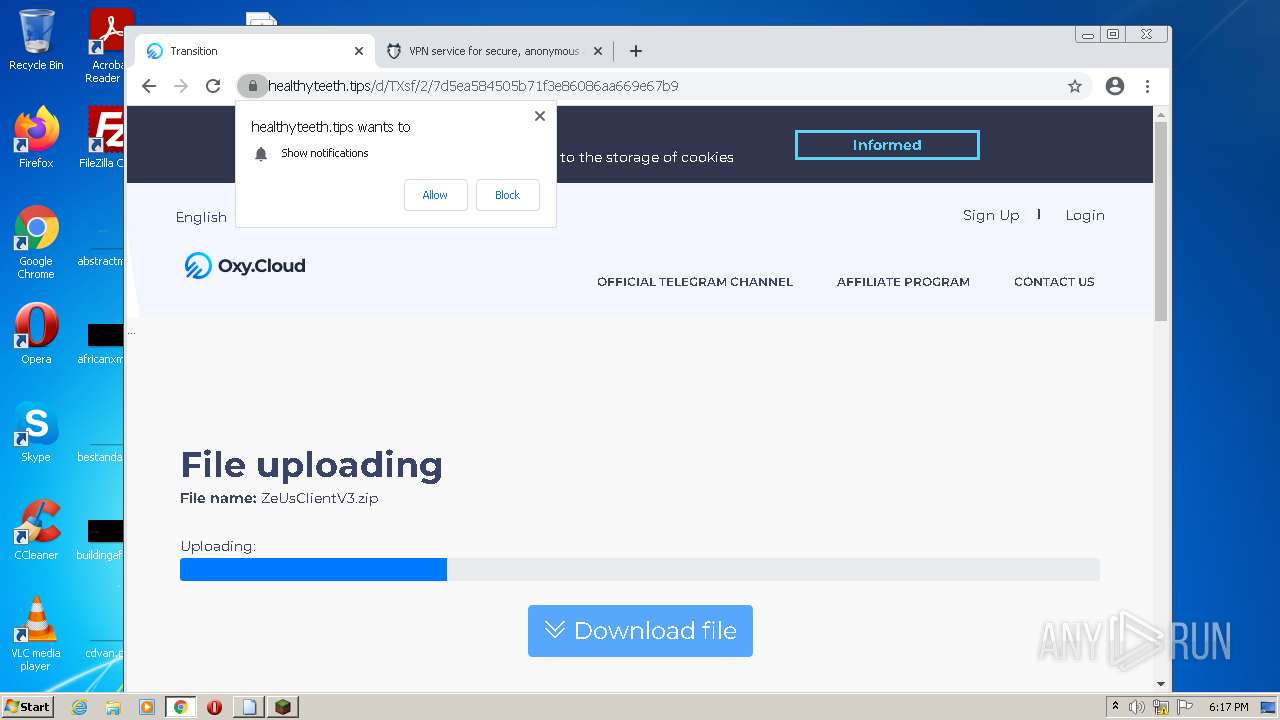
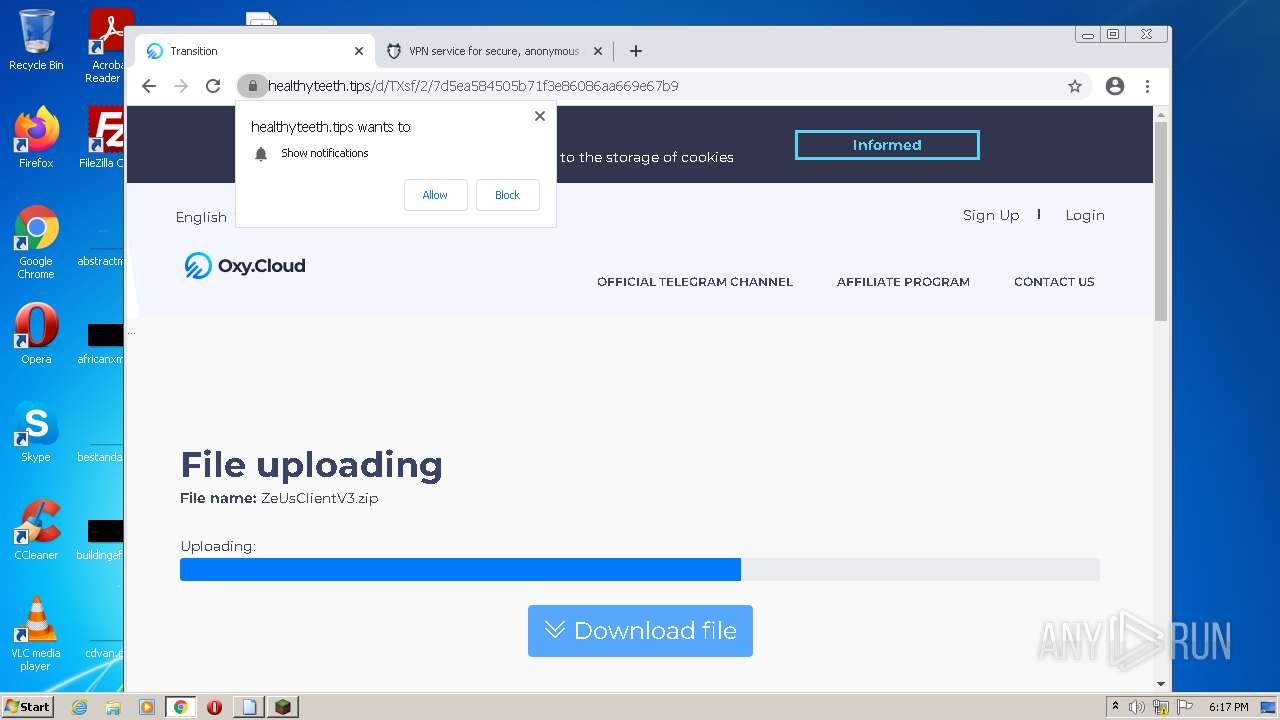
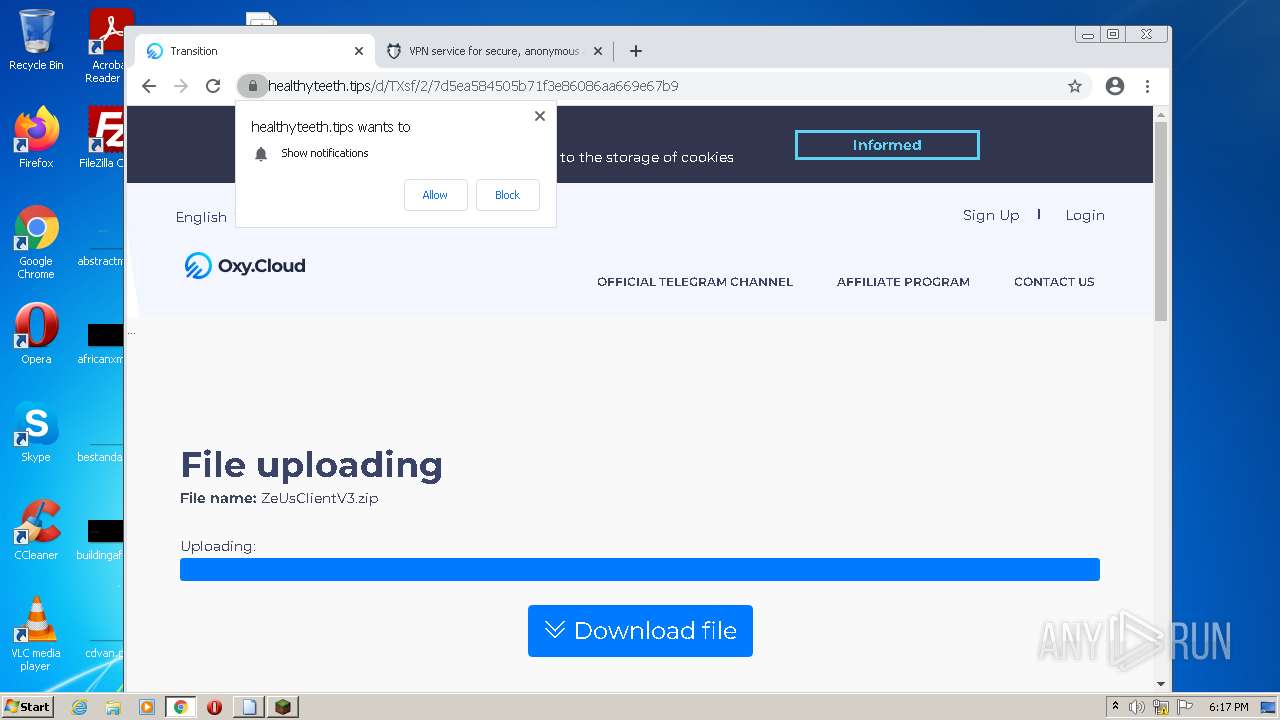
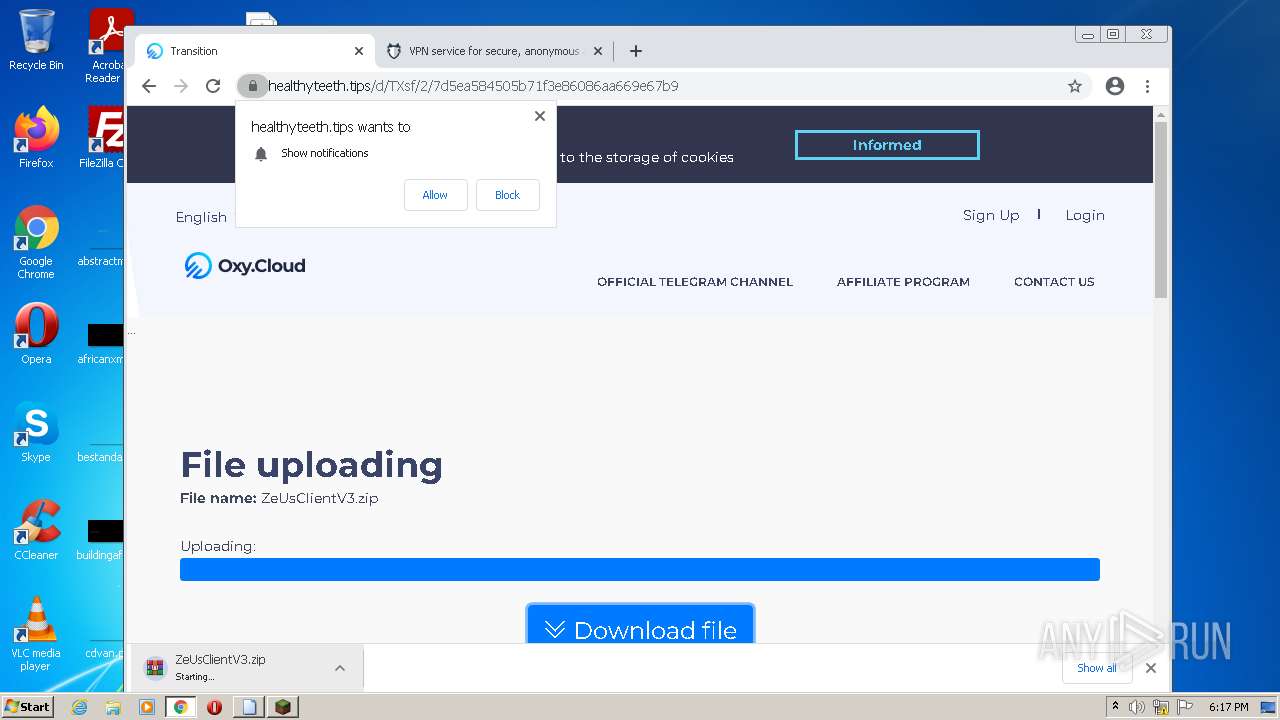
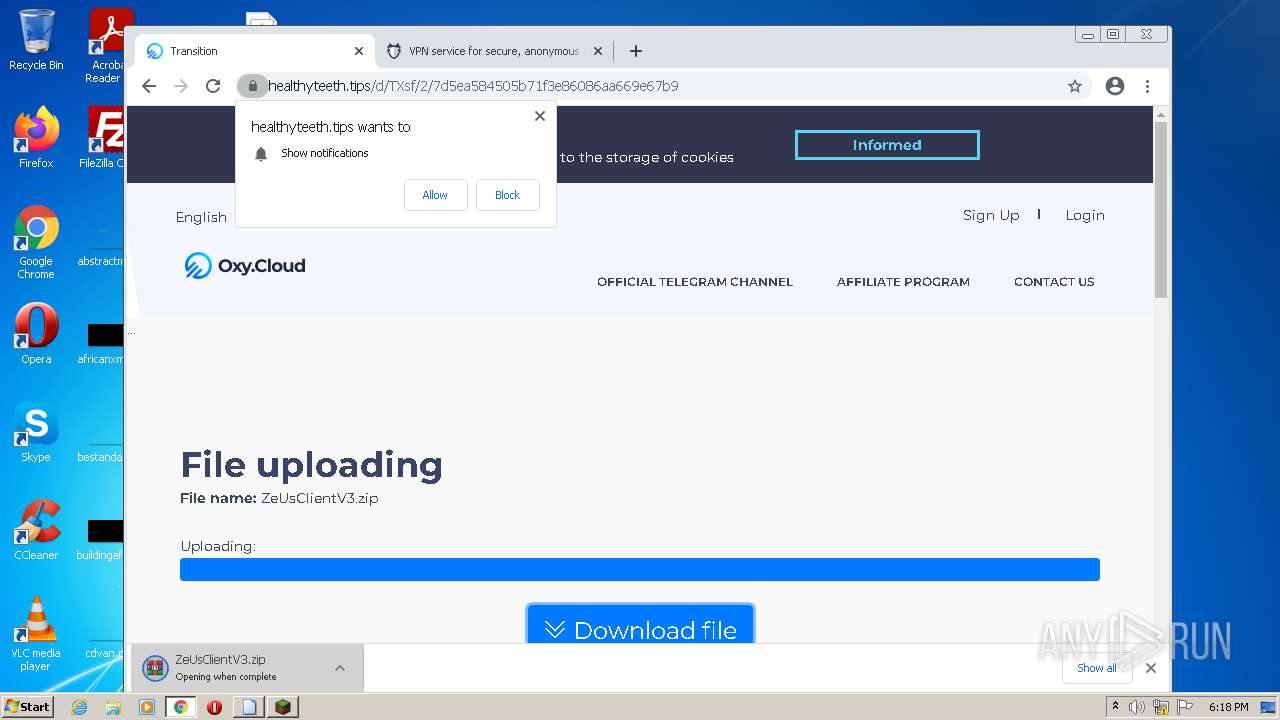
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
892 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | — | — | whitelisted |
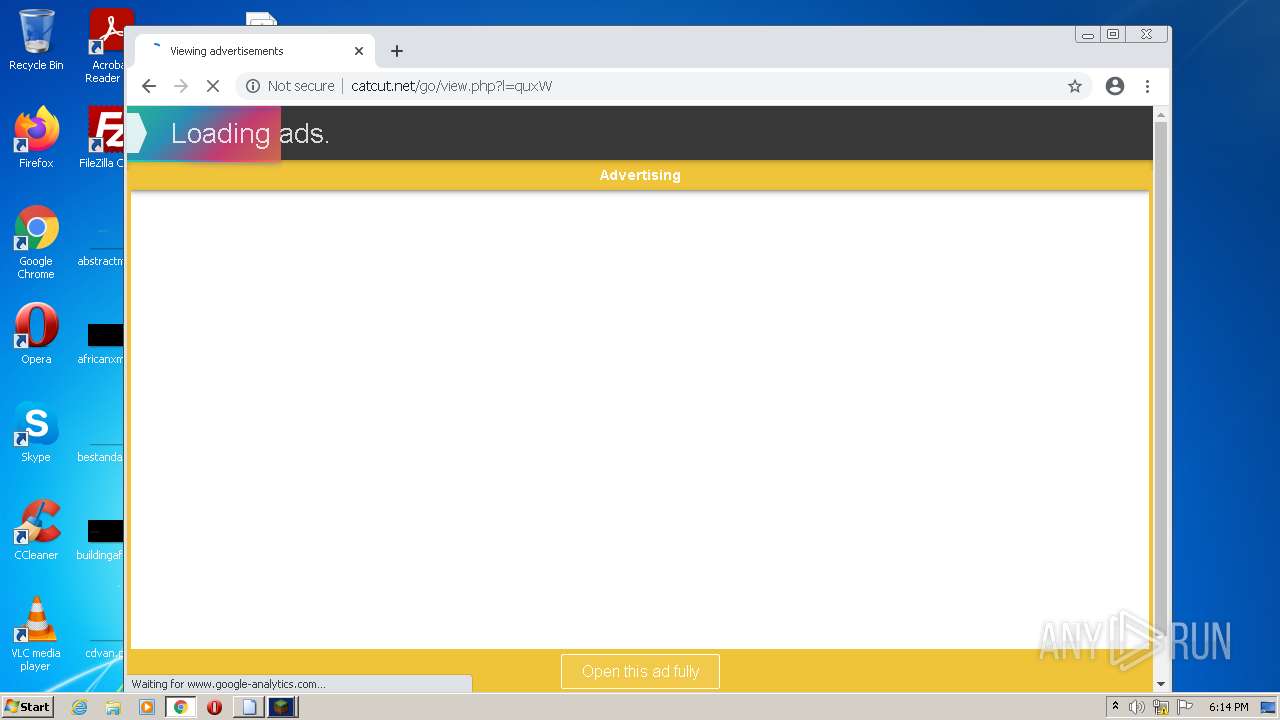
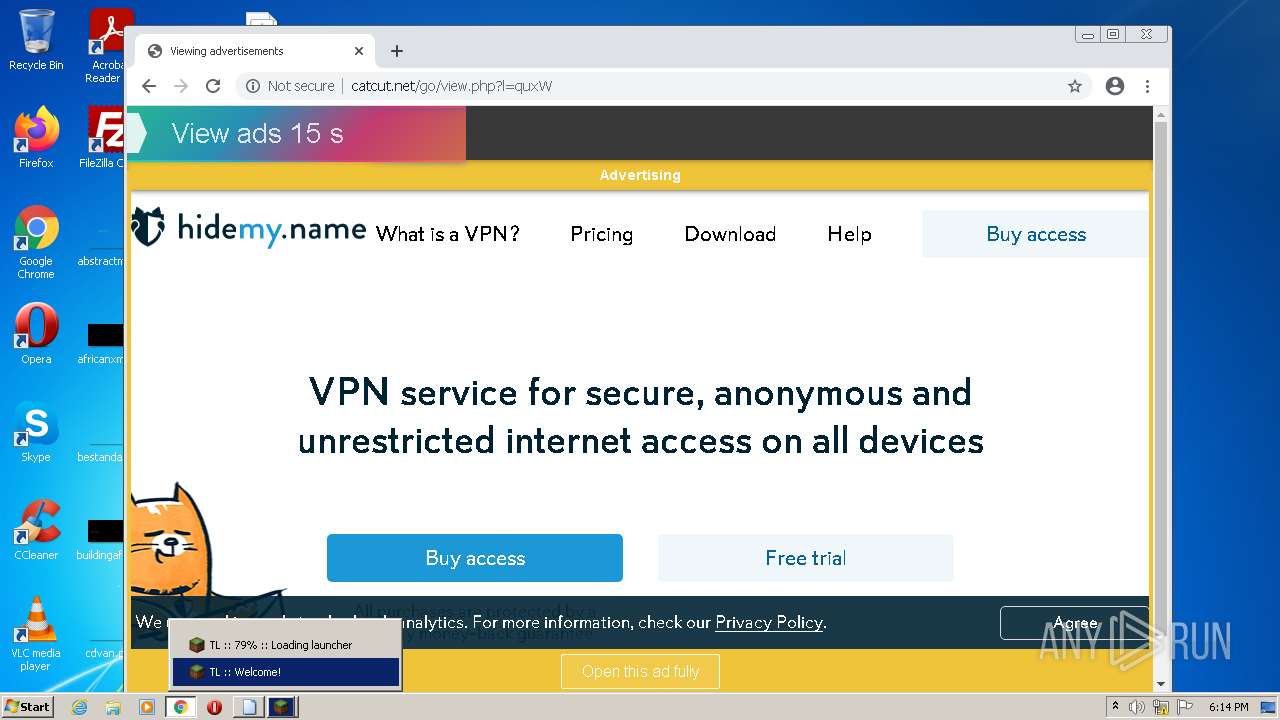
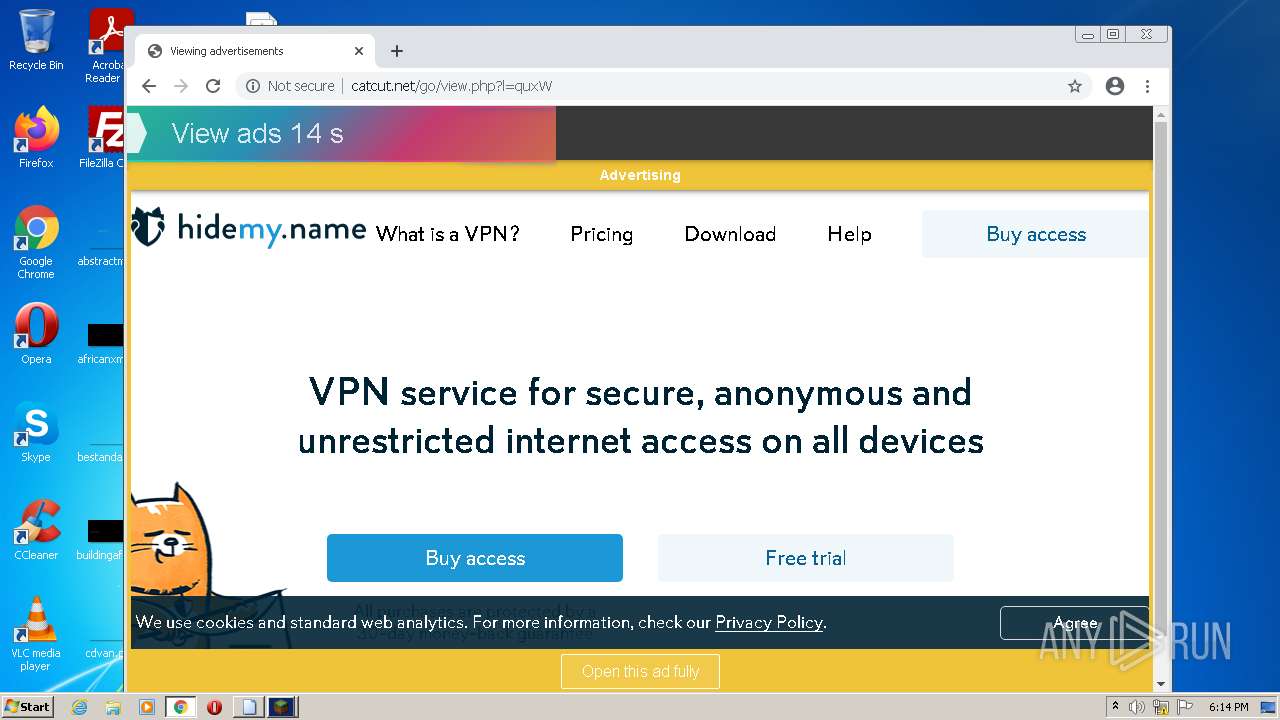
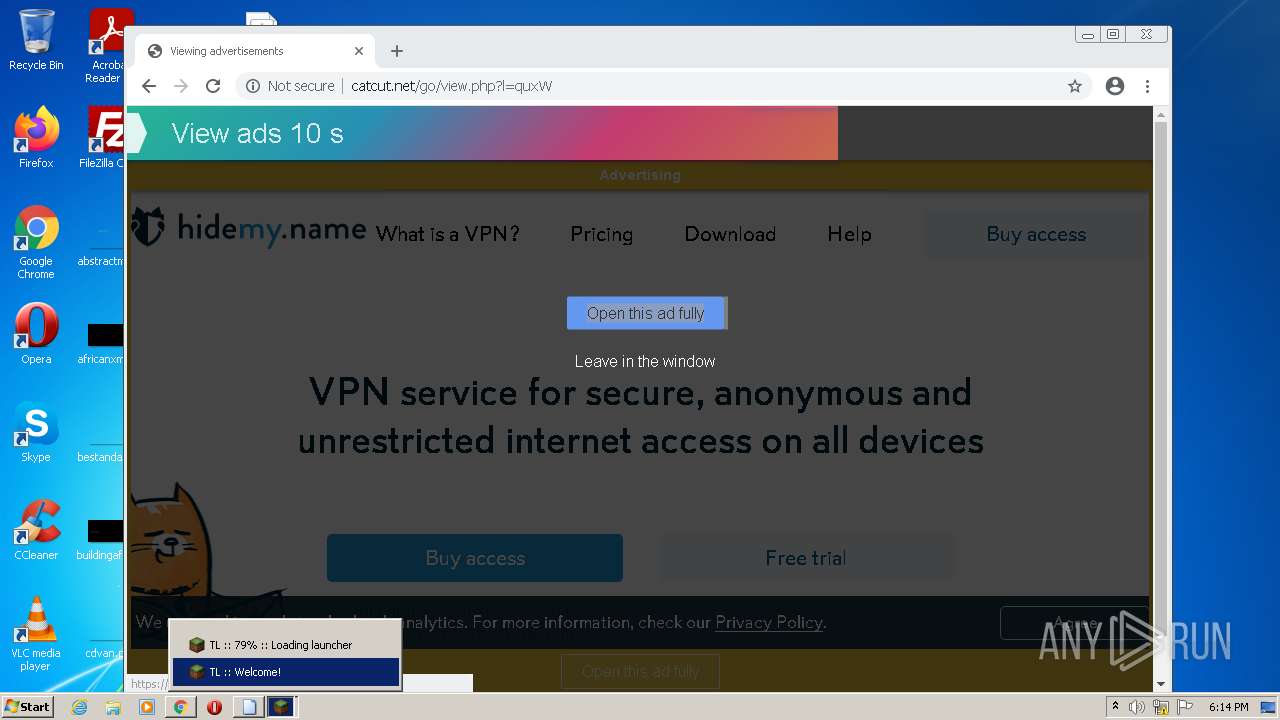
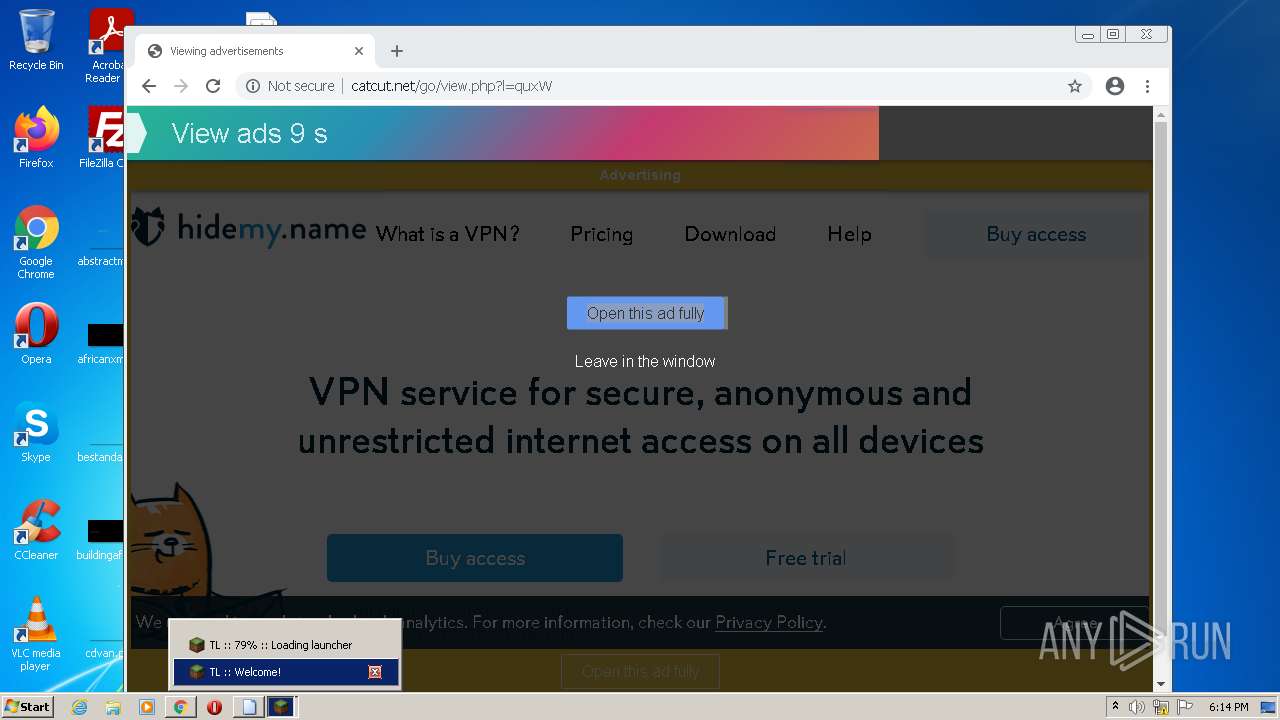
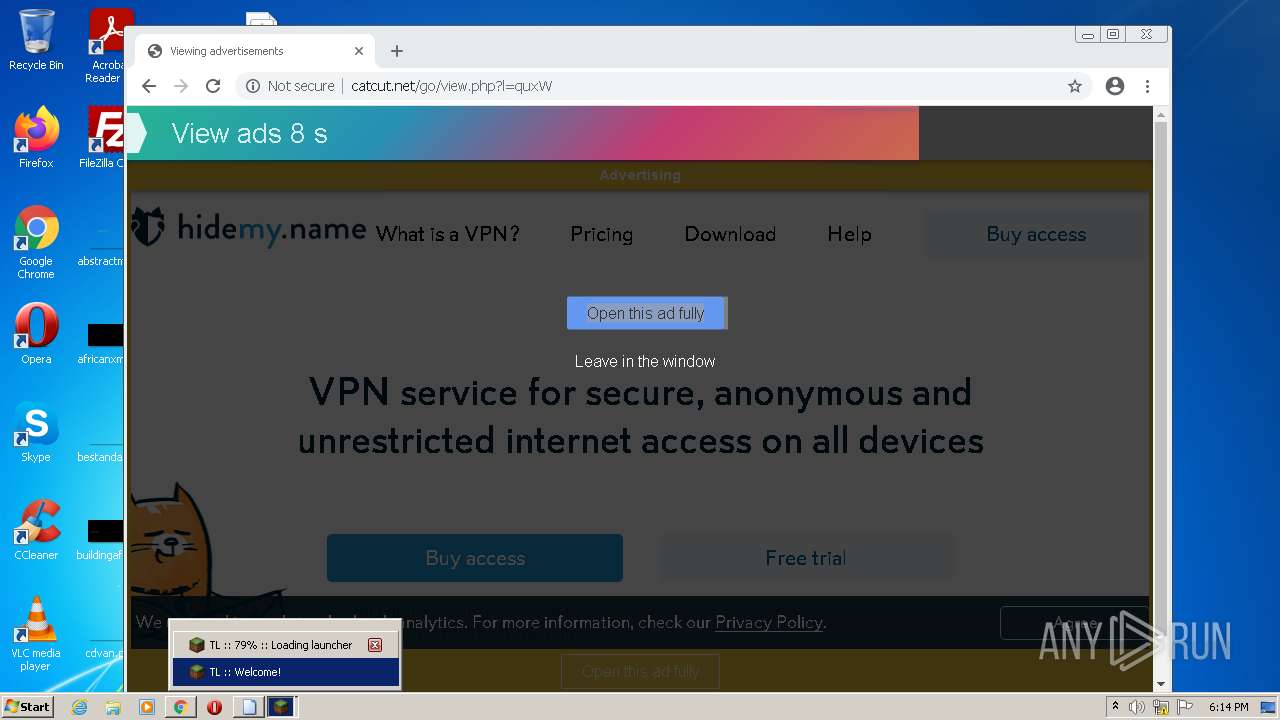
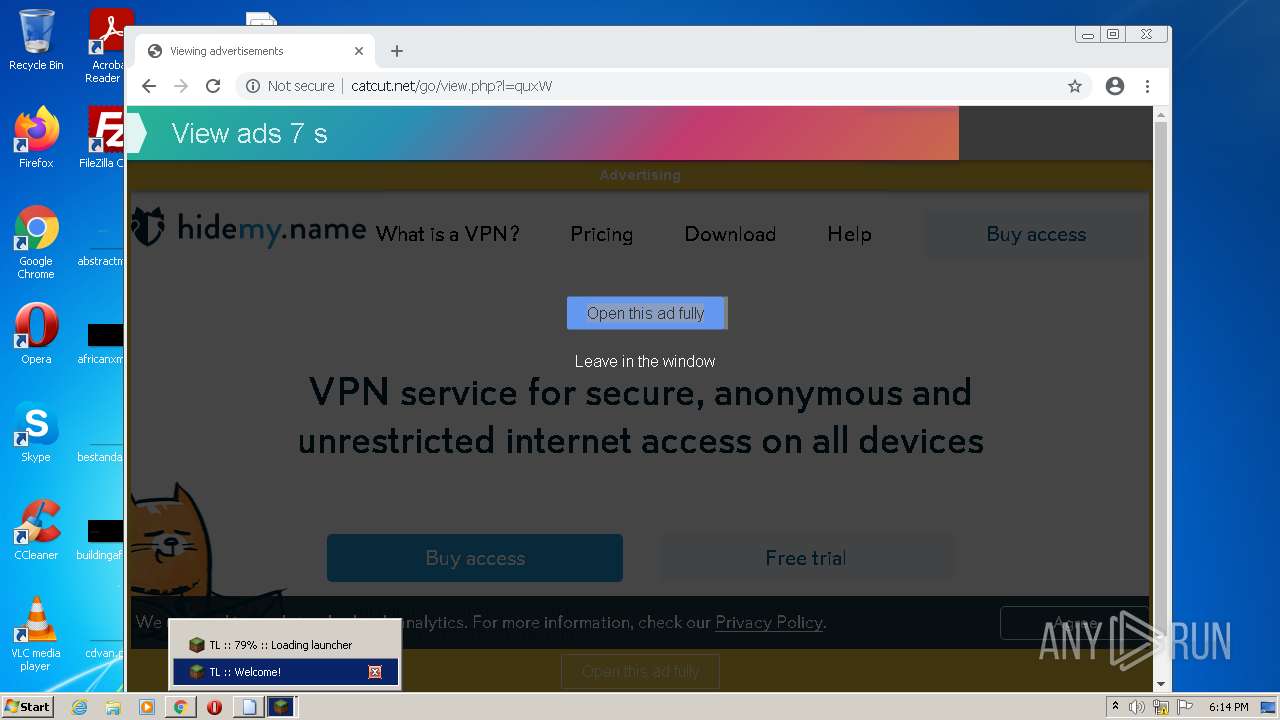
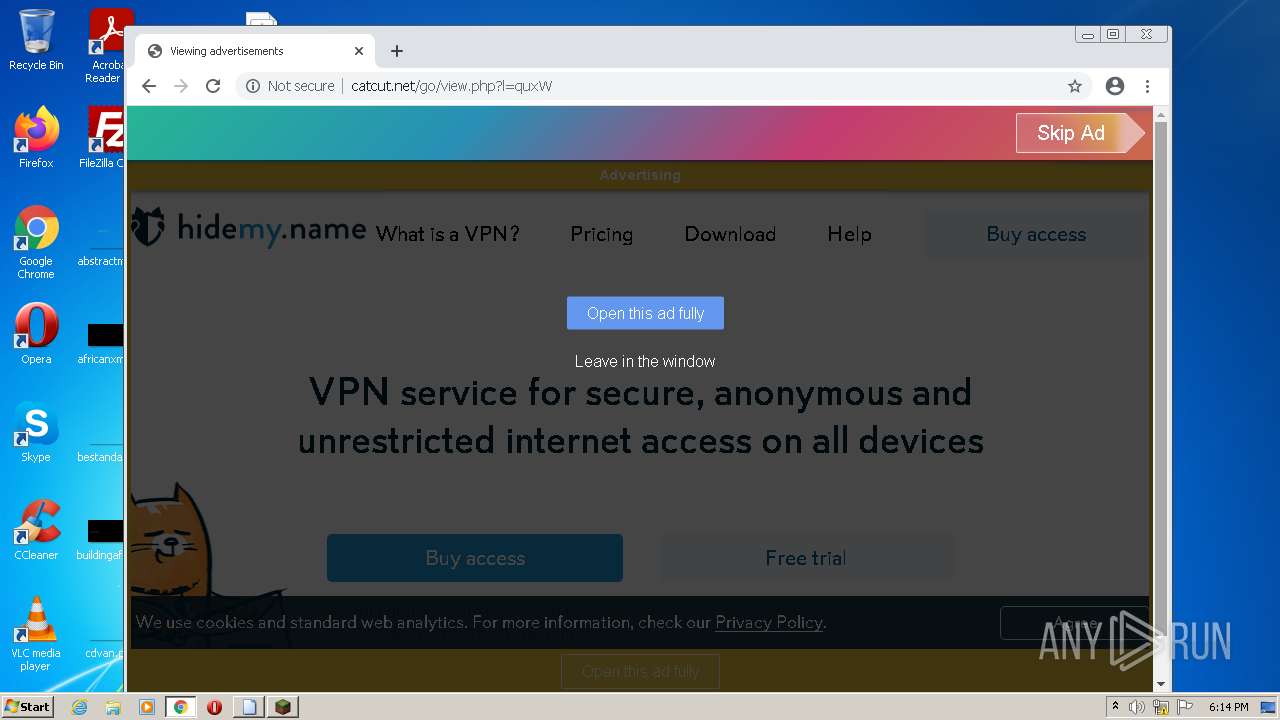
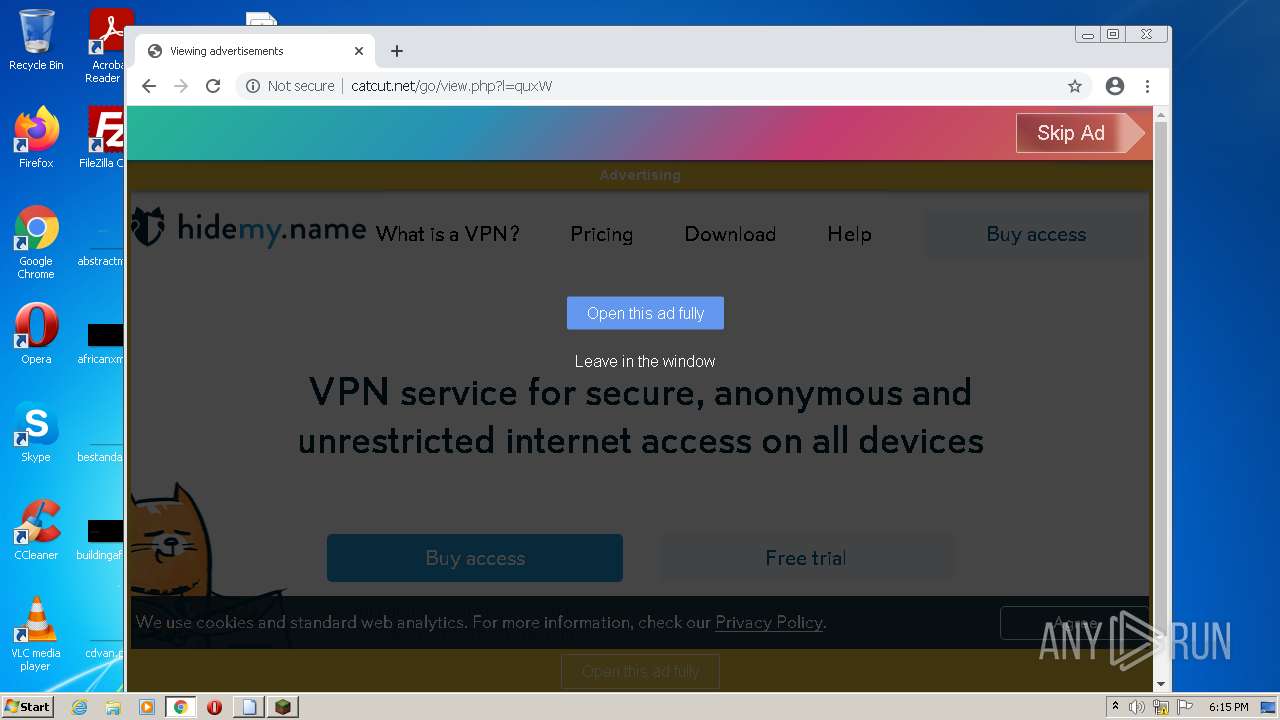
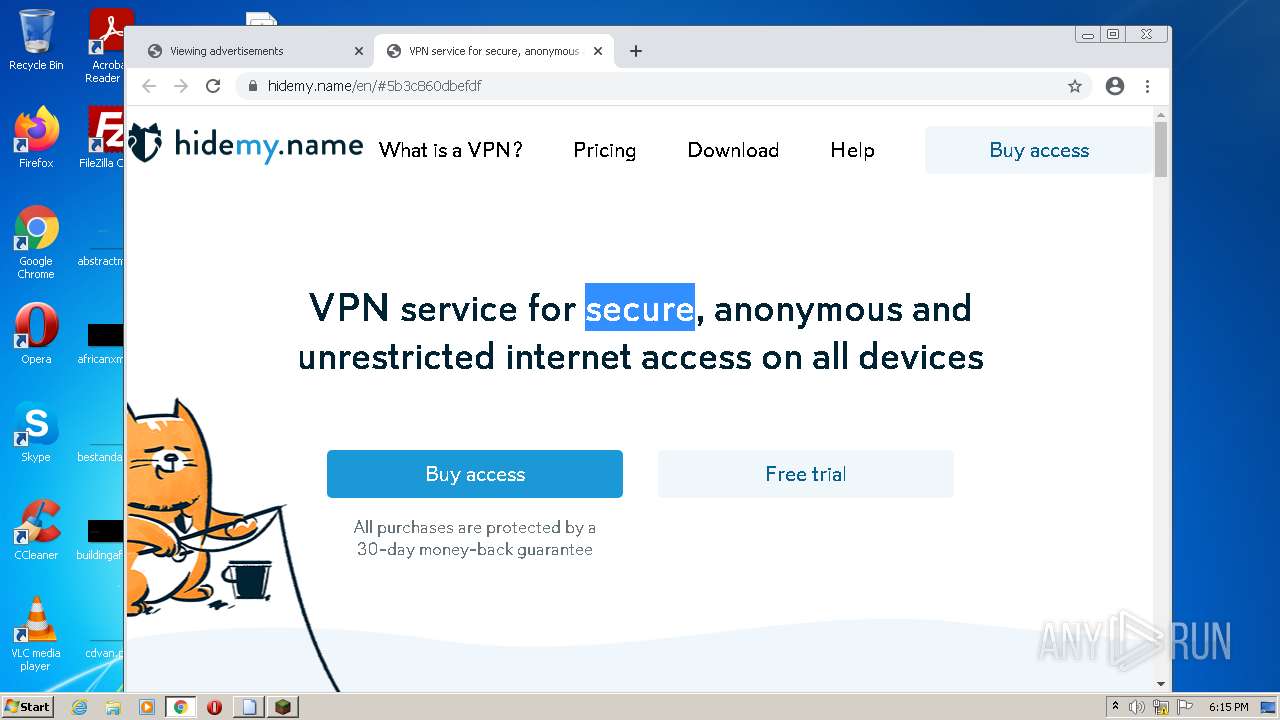
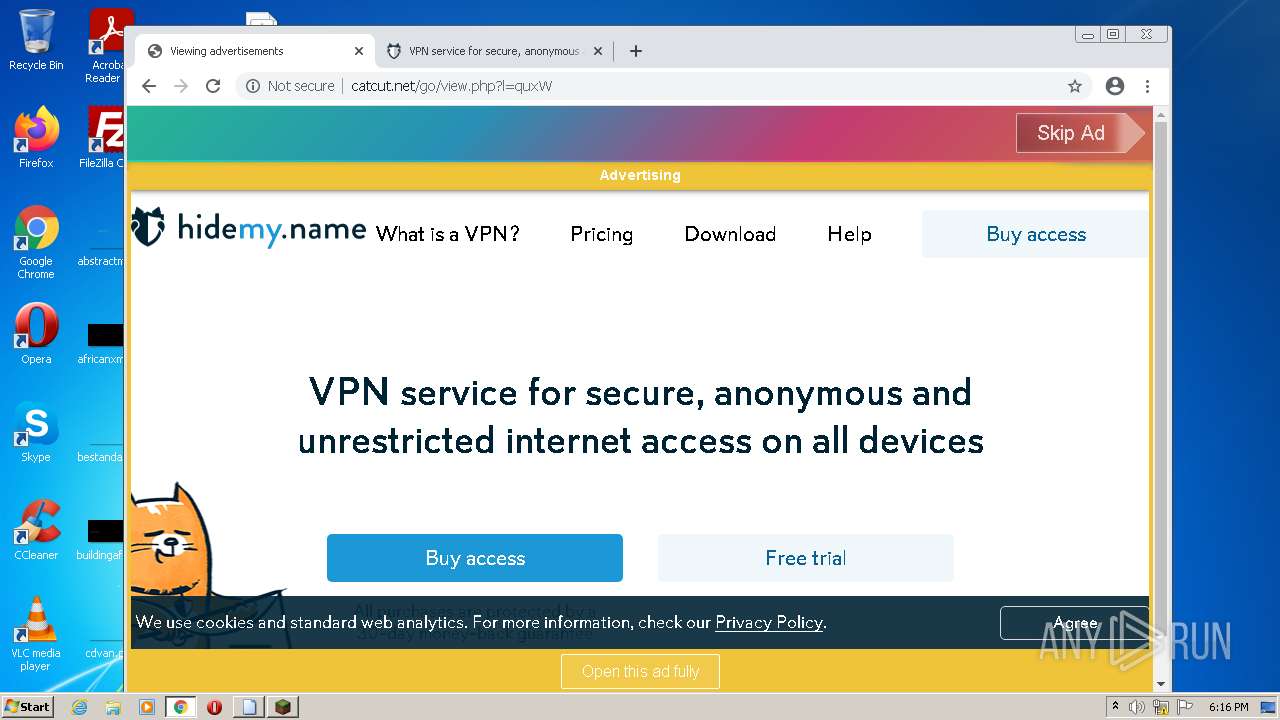
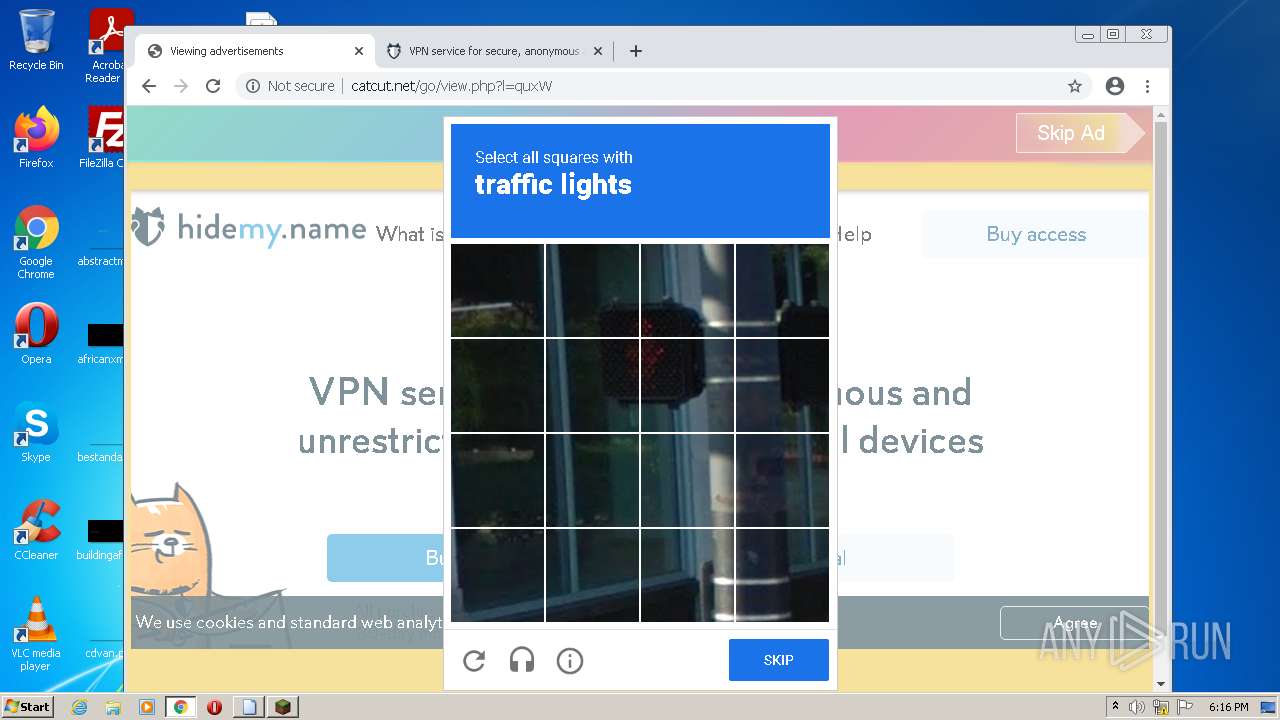
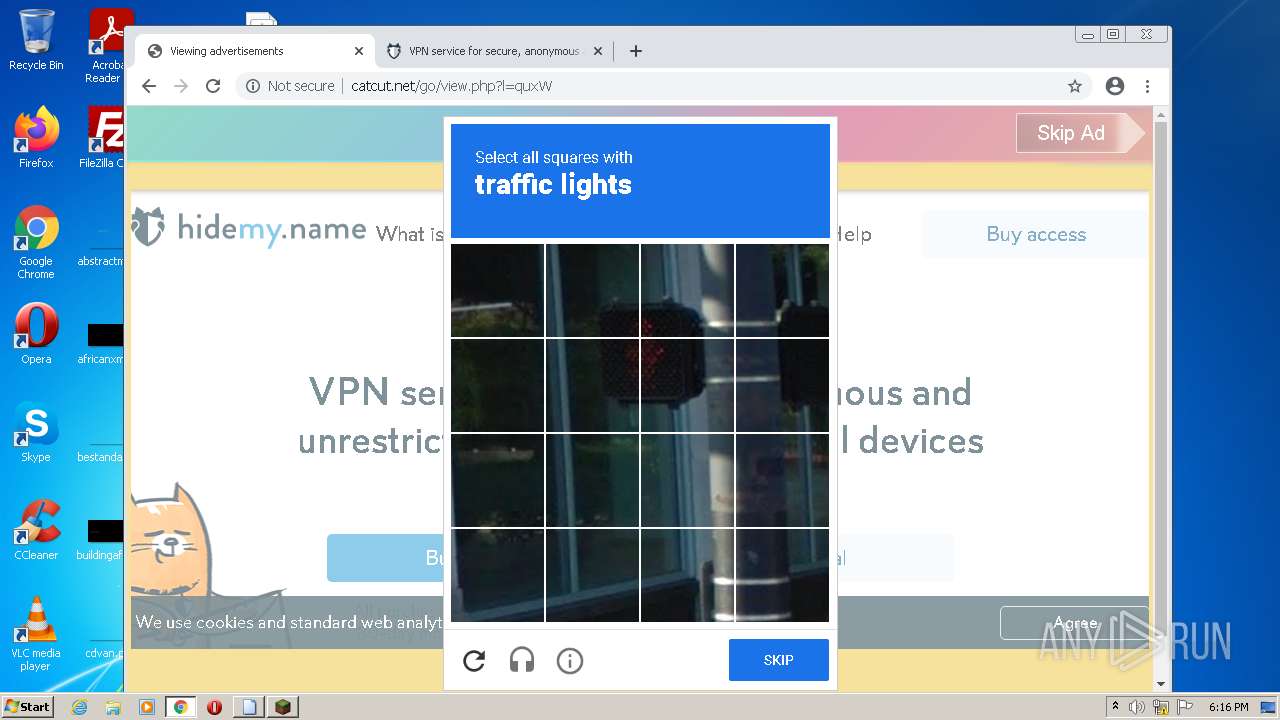
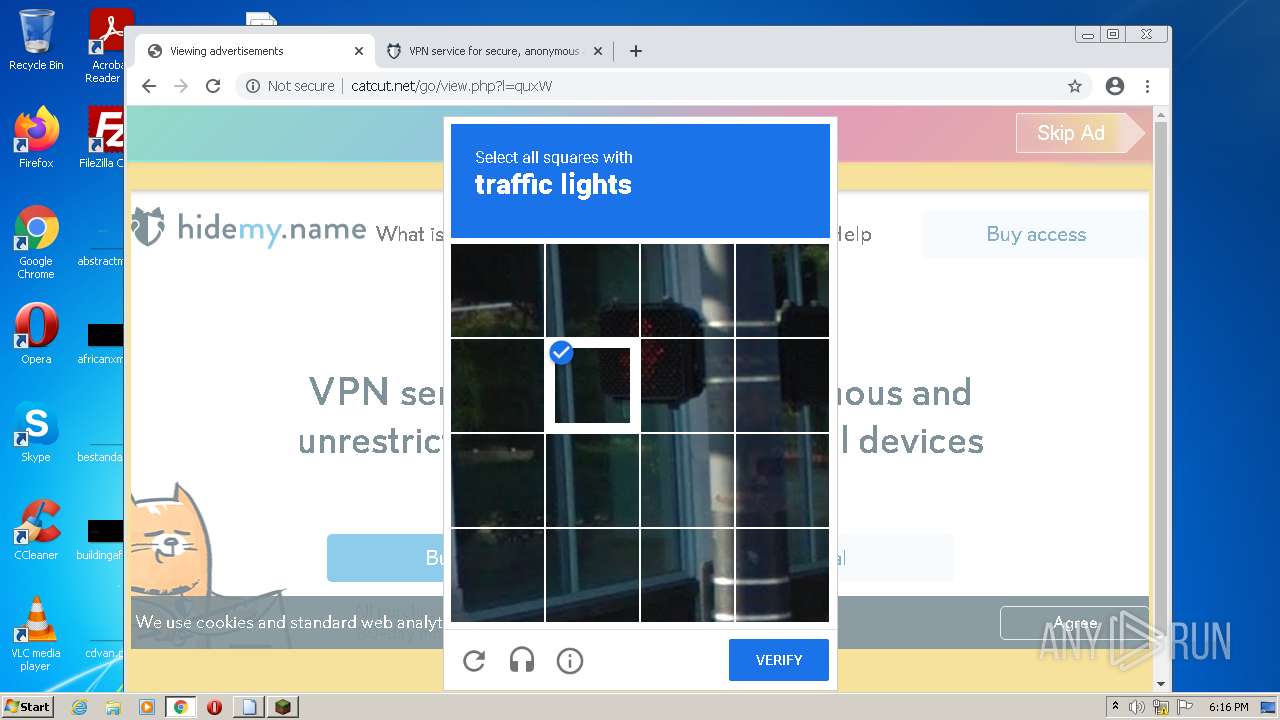
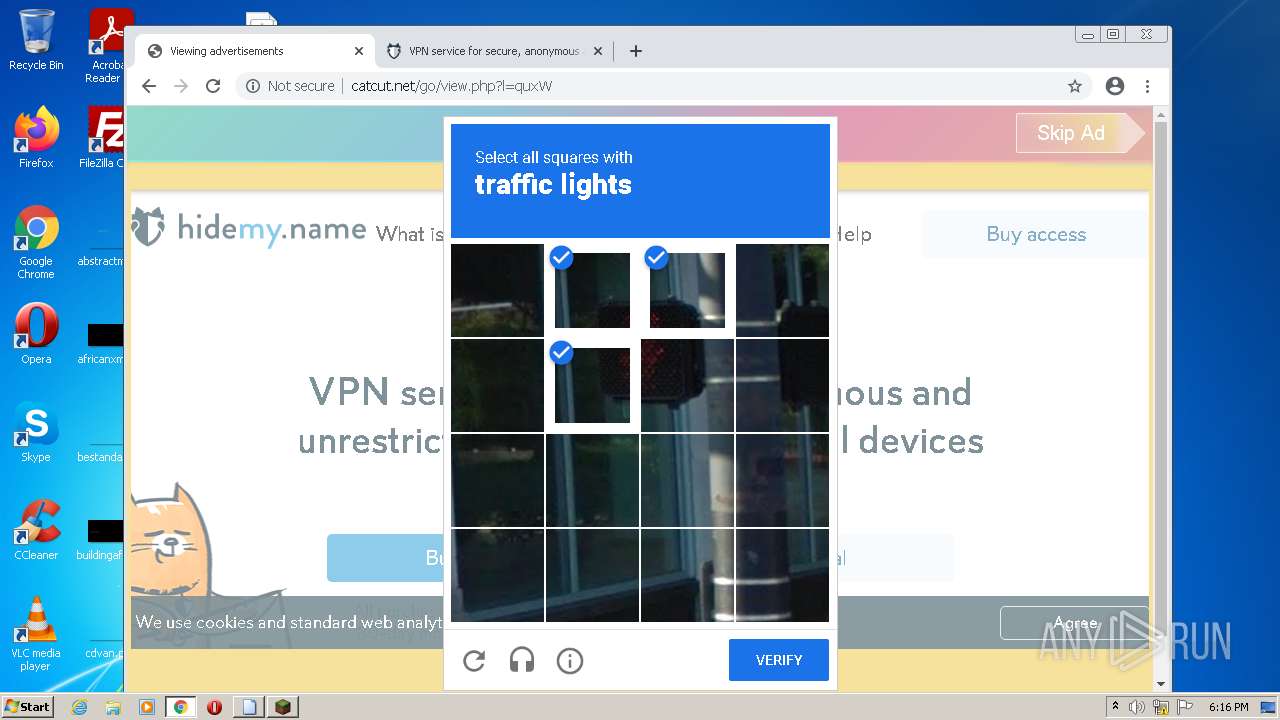
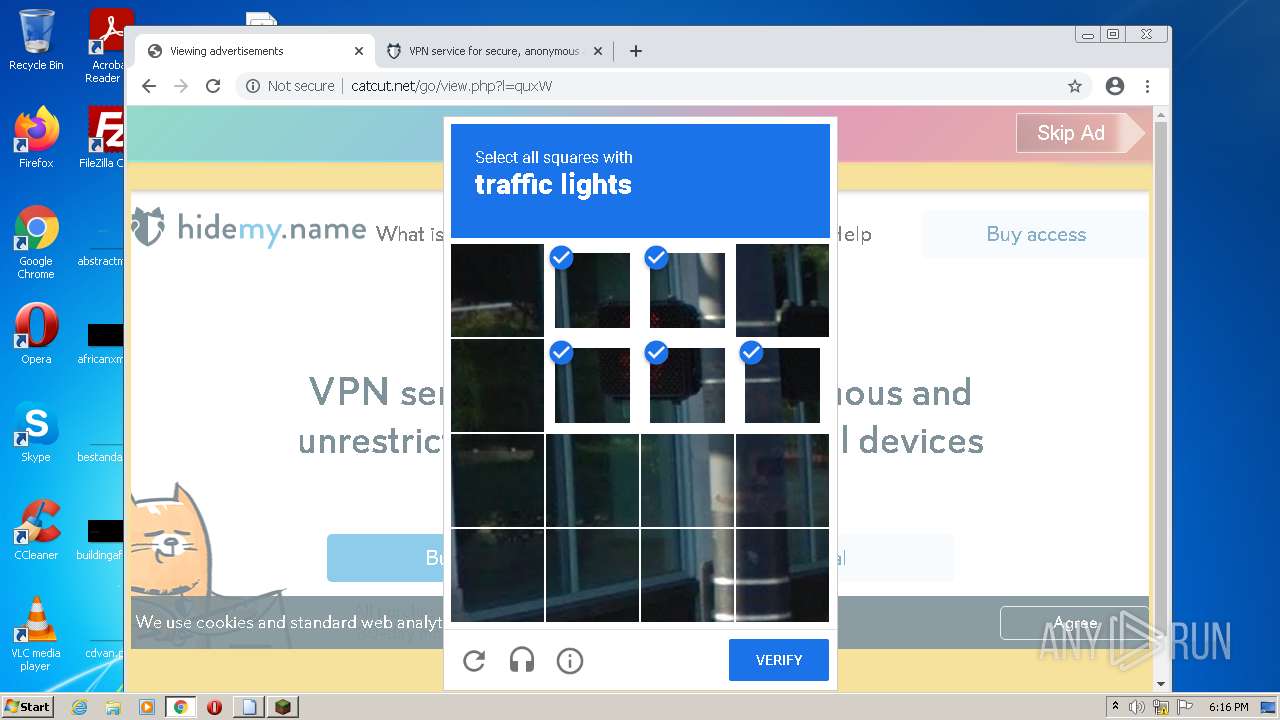
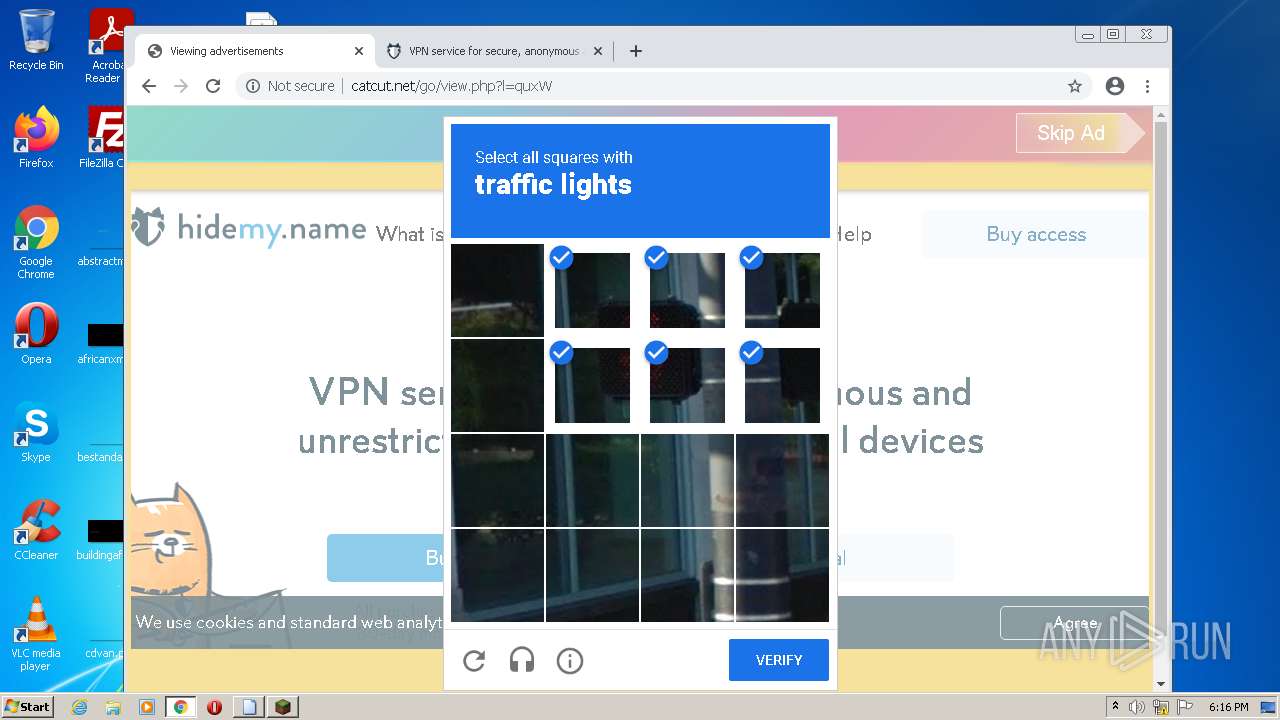
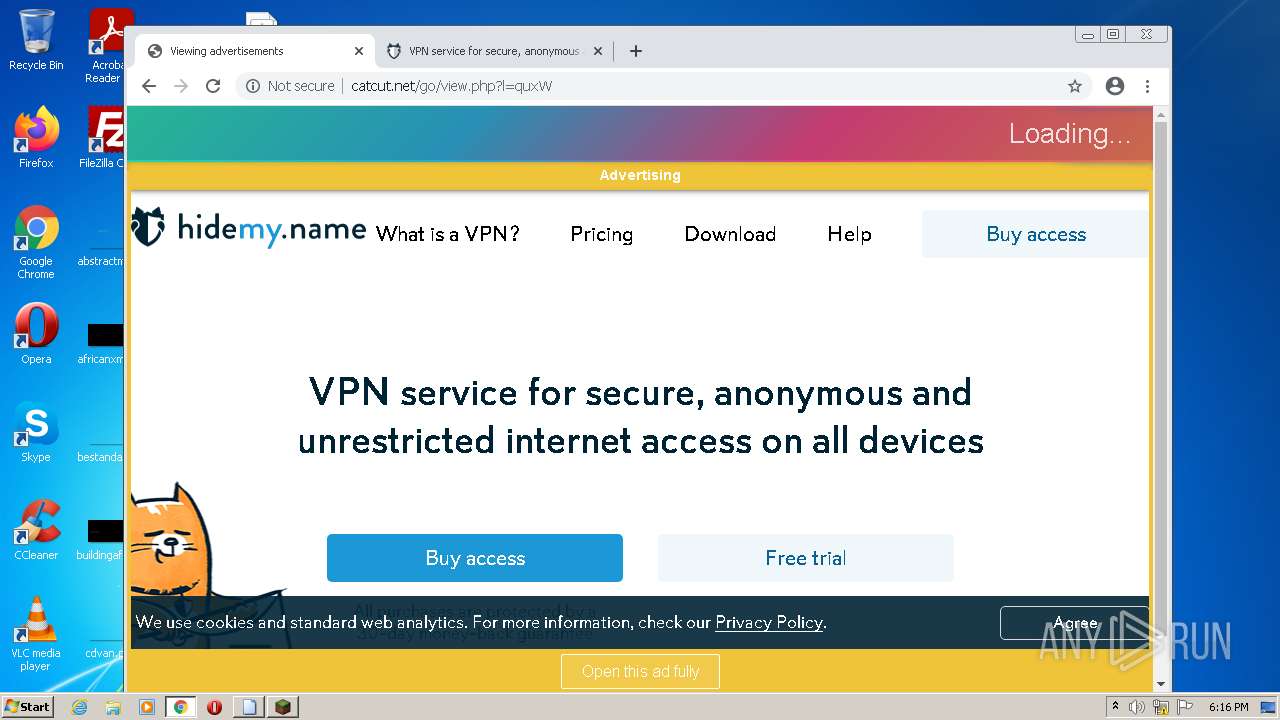
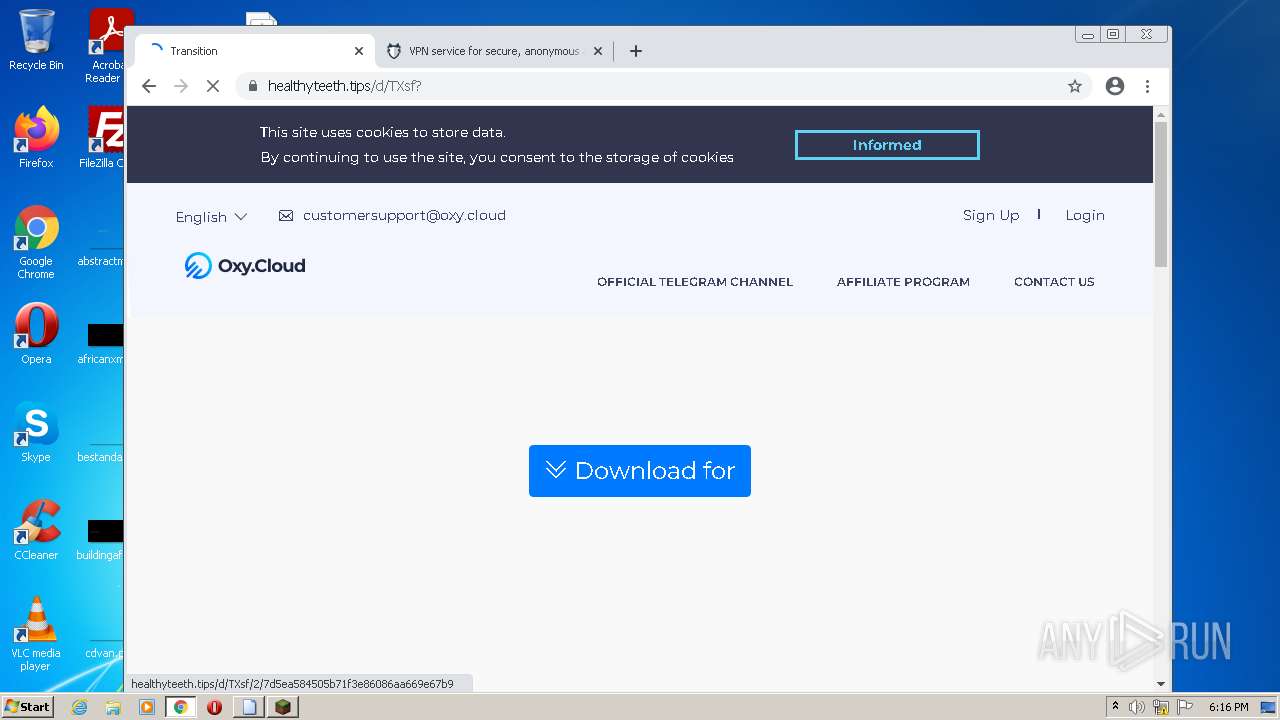
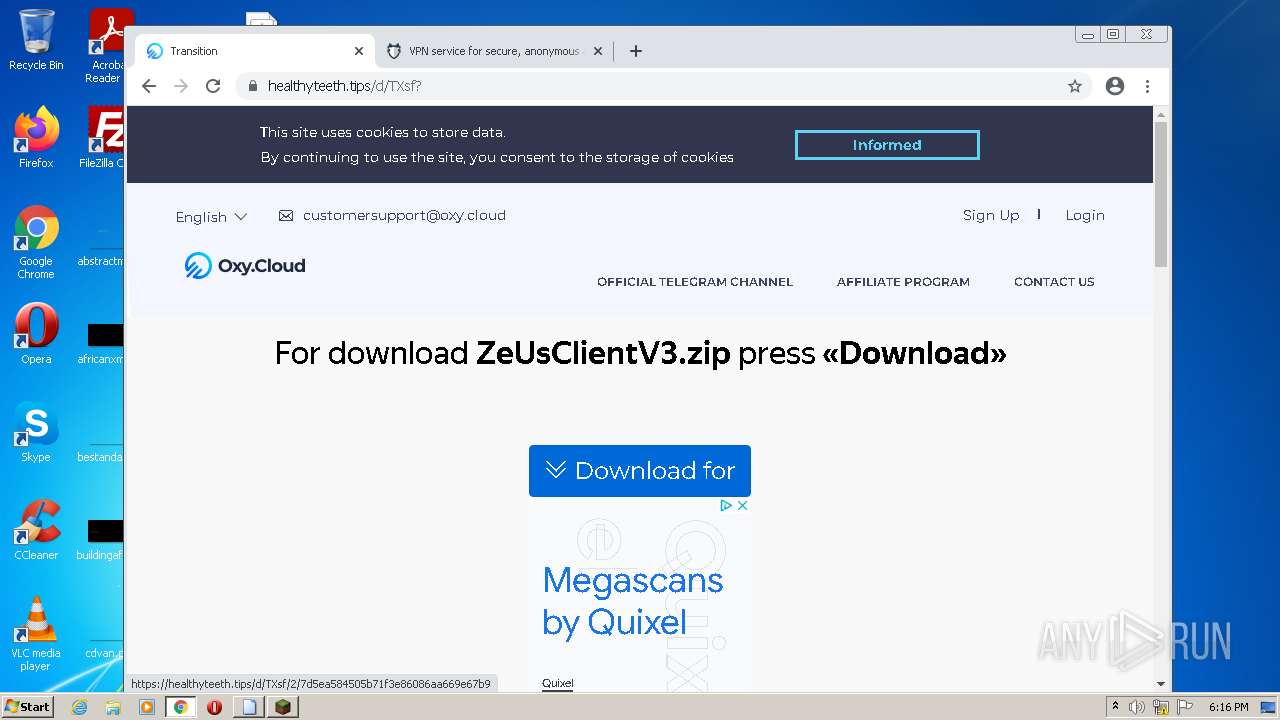
2700 | chrome.exe | GET | 404 | 79.132.136.12:80 | http://catcut.net/favicon.ico | DE | html | 65.4 Kb | suspicious |
892 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 9.70 Kb | whitelisted |
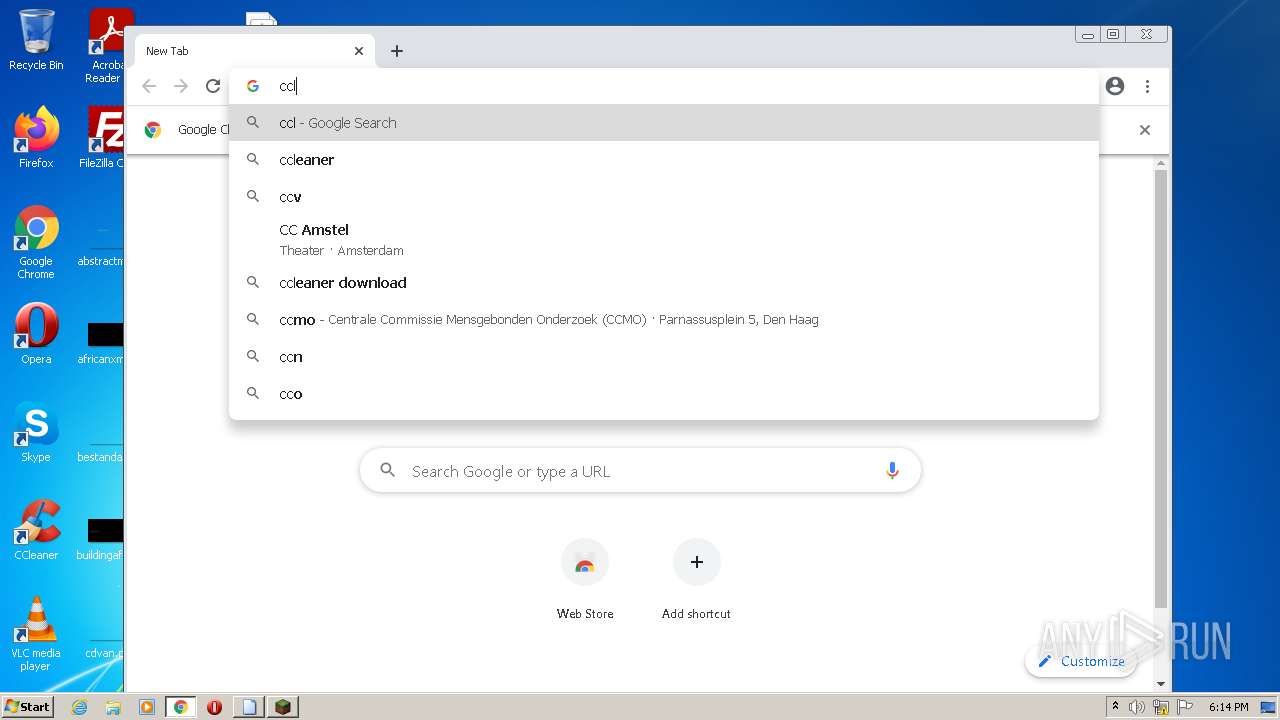
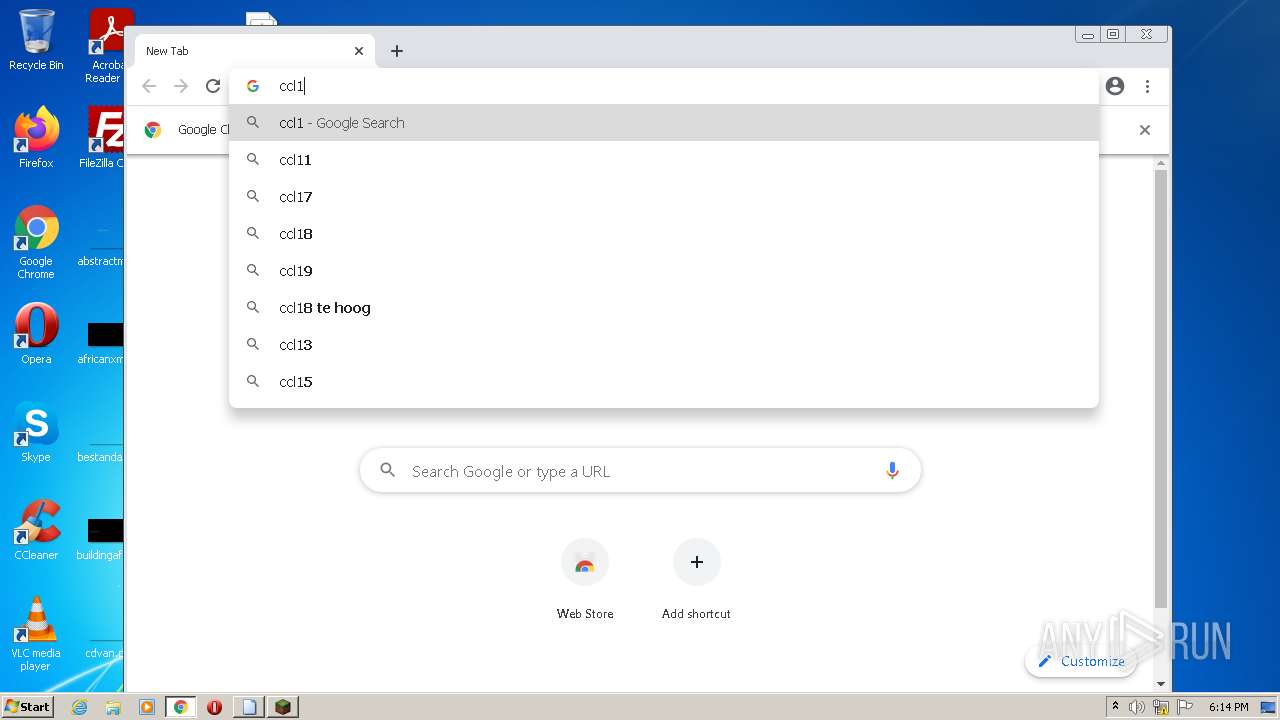
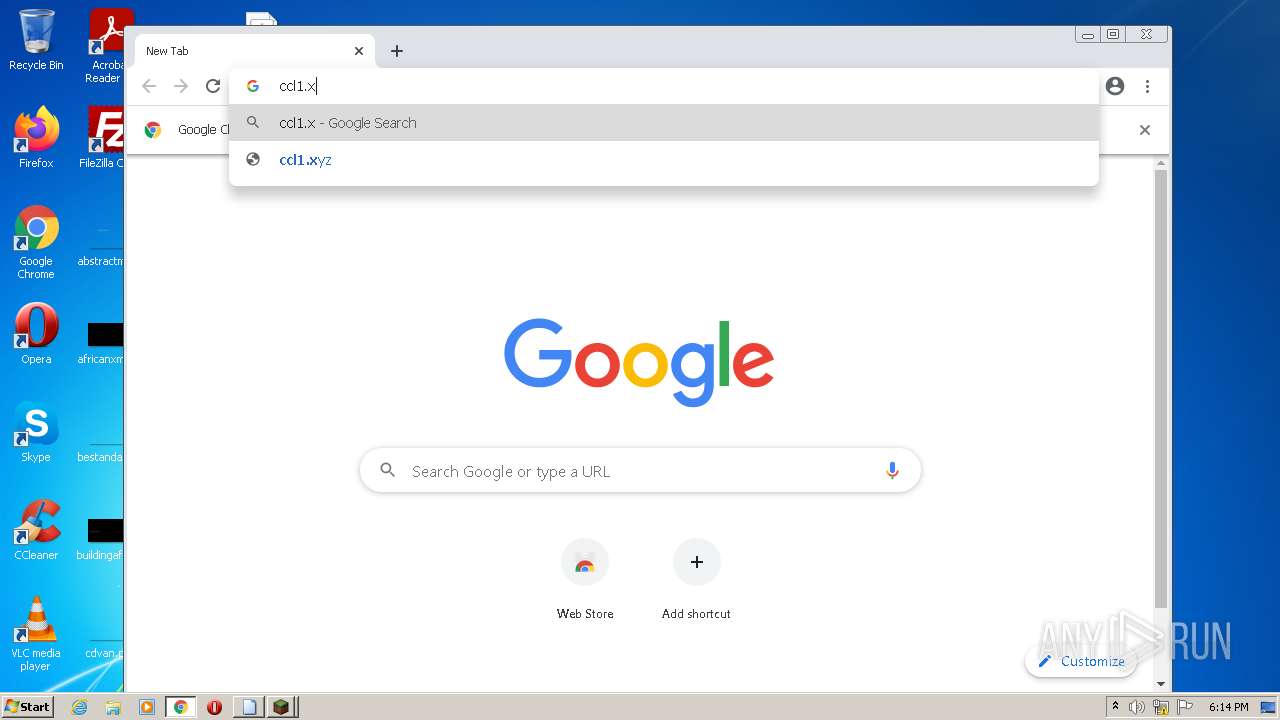
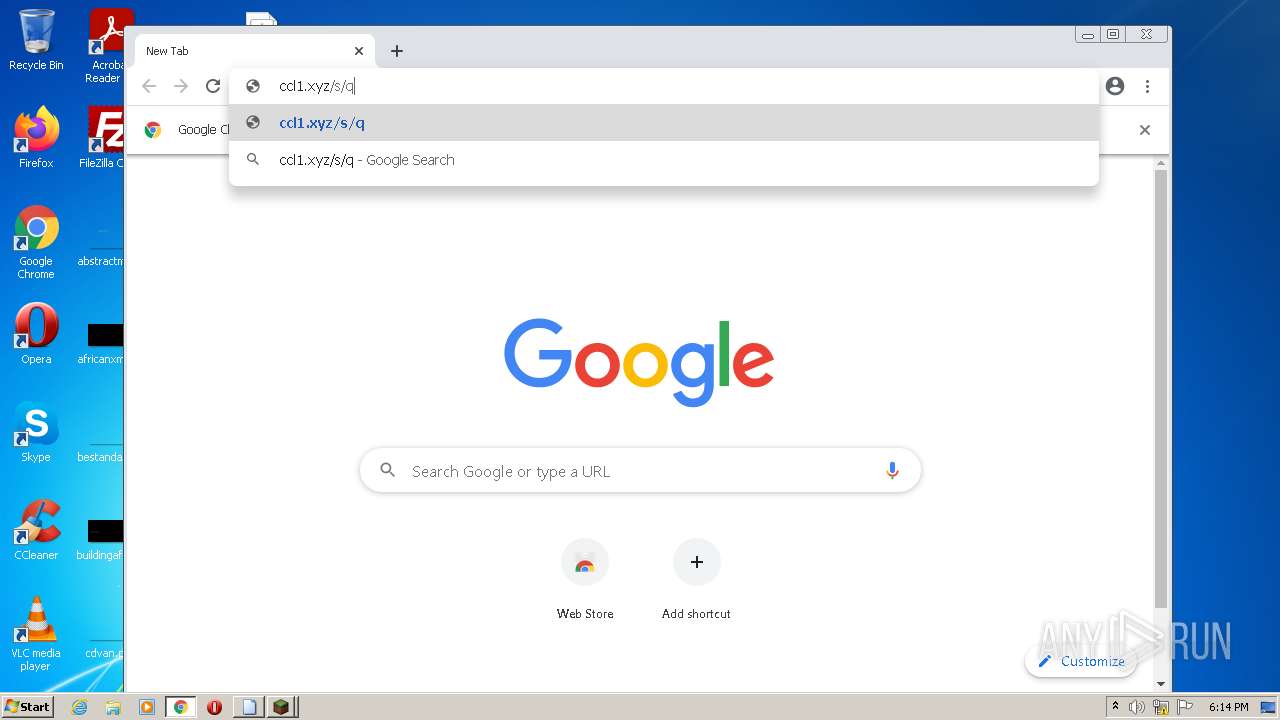
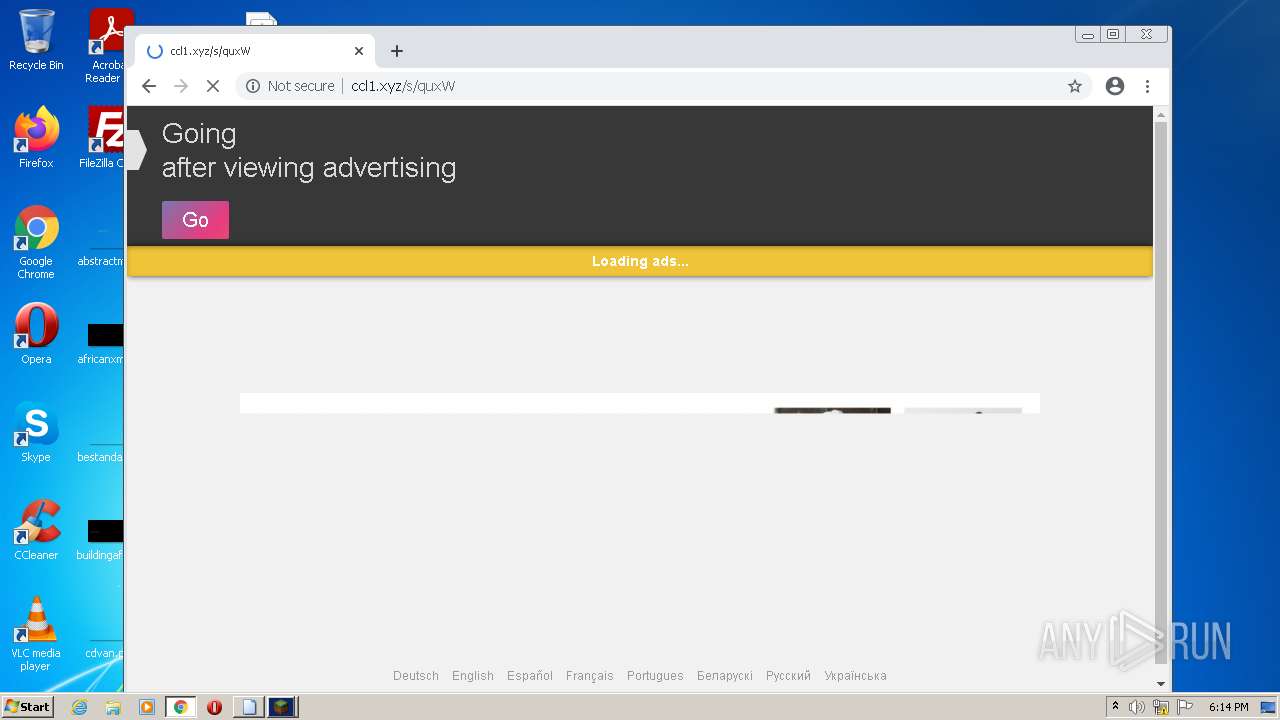
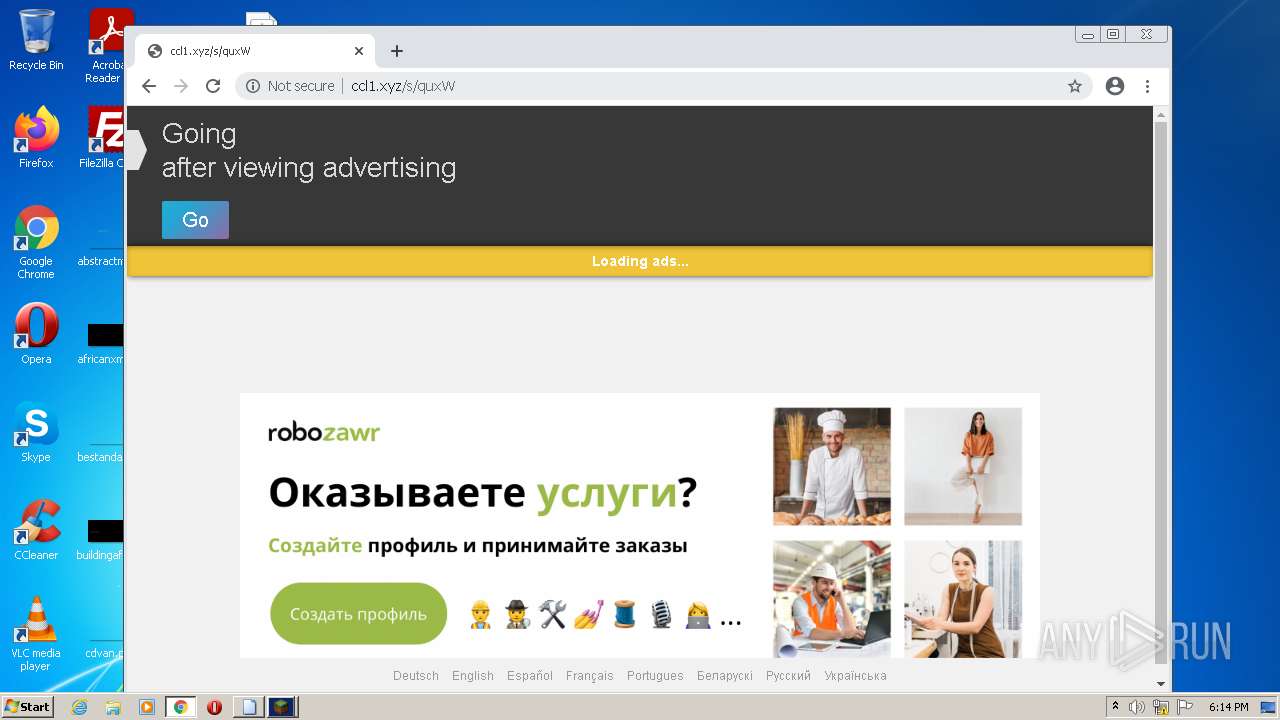
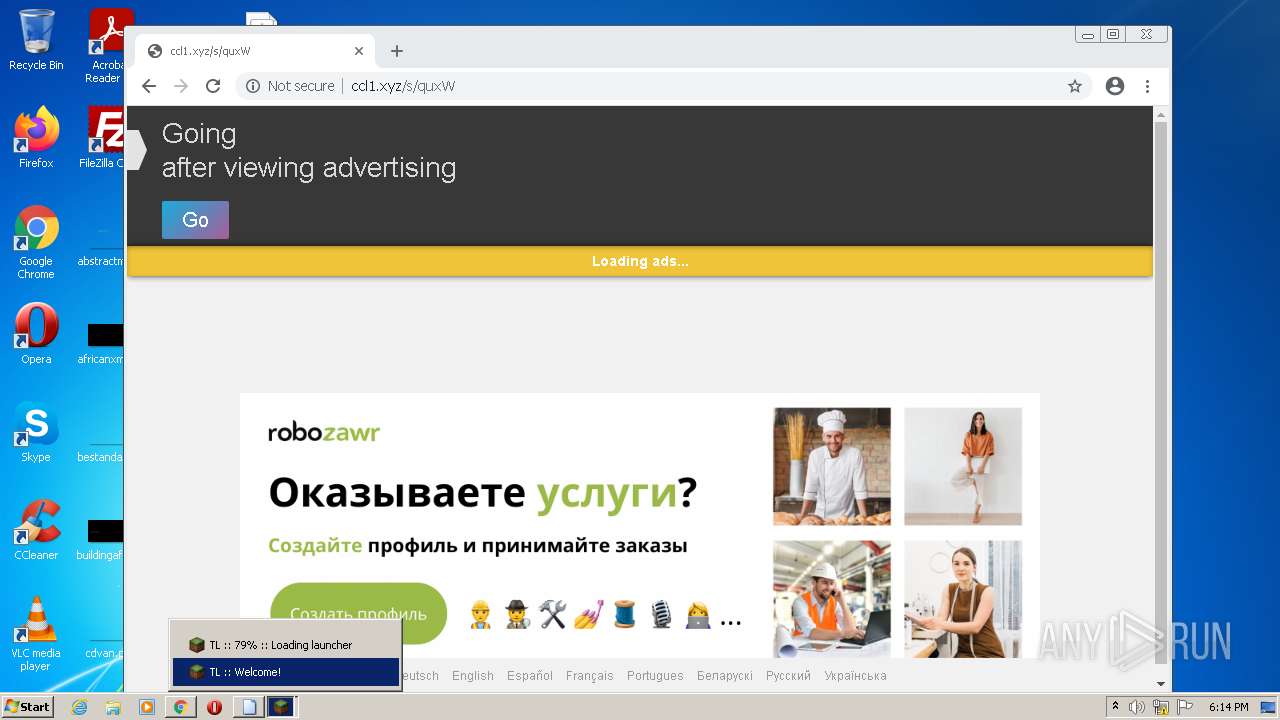
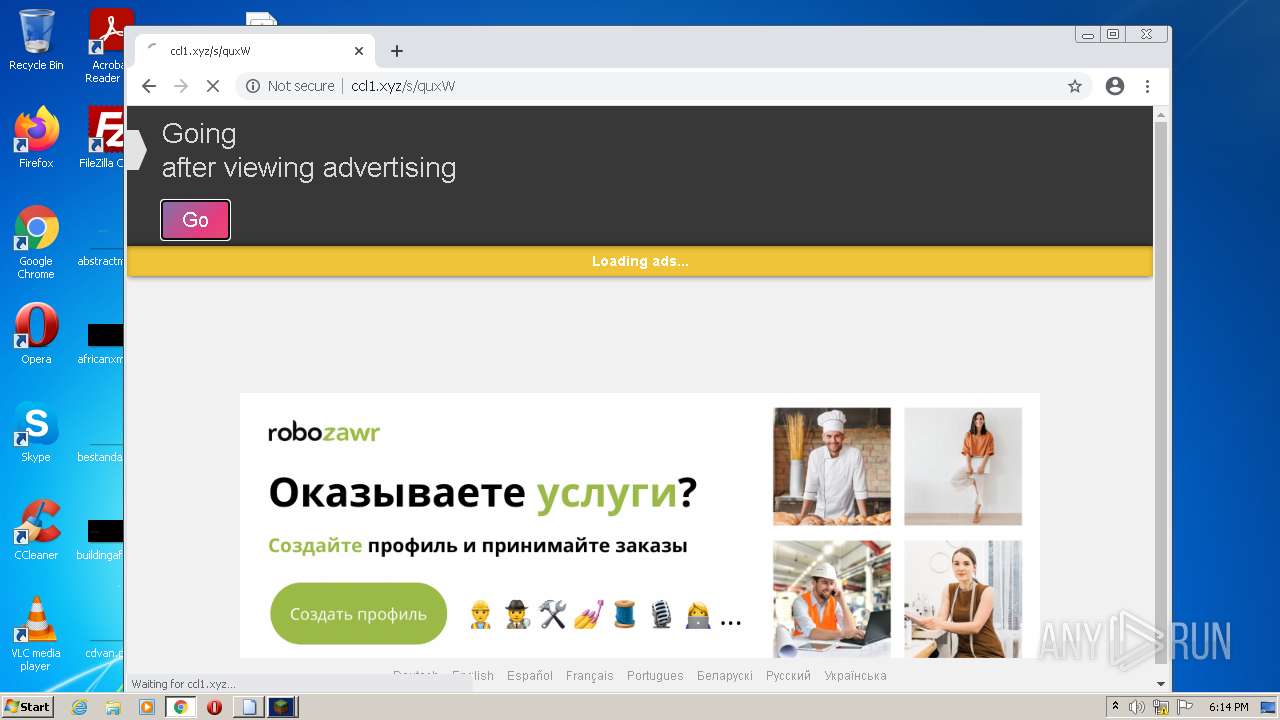
2700 | chrome.exe | GET | 200 | 79.132.136.12:80 | http://ccl1.xyz/s/quxW | DE | html | 7.96 Kb | suspicious |
892 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 9.65 Kb | whitelisted |
892 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 43.4 Kb | whitelisted |
892 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 20.9 Kb | whitelisted |
892 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 9.65 Kb | whitelisted |
2700 | chrome.exe | GET | 302 | 79.132.136.12:80 | http://ccl1.xyz/go.php?to=quxW&a=2922647315&b=&c=1661011078 | DE | — | — | suspicious |
2700 | chrome.exe | GET | 302 | 79.132.136.12:80 | http://ccl1.xyz/go.php?to=quxW&a=2922647315&b=&c=1661011078 | DE | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
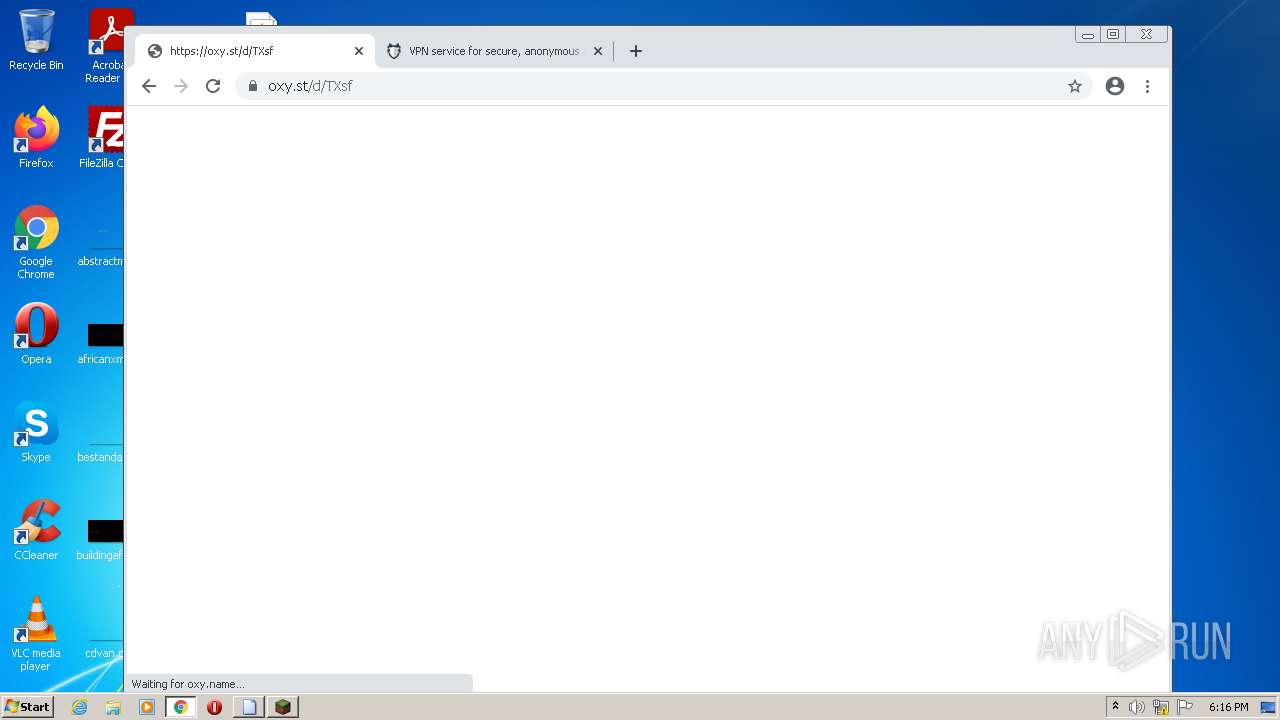
3880 | java.exe | 151.236.118.192:443 | cdn.turikhay.ru | CDNvideo LLC | RU | suspicious |
3880 | java.exe | 104.21.30.156:443 | tlaun.ch | Cloudflare Inc | US | malicious |
3880 | java.exe | 159.223.209.252:443 | eu01-www.tlaun.ch | — | US | unknown |
2700 | chrome.exe | 142.250.186.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
2700 | chrome.exe | 142.250.186.36:443 | www.google.com | Google Inc. | US | whitelisted |
2700 | chrome.exe | 142.250.185.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2700 | chrome.exe | 142.250.184.193:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
2700 | chrome.exe | 216.58.212.174:443 | encrypted-tbn0.gstatic.com | Google Inc. | US | whitelisted |
2700 | chrome.exe | 142.250.184.195:443 | update.googleapis.com | Google Inc. | US | whitelisted |
2700 | chrome.exe | 142.250.186.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cdn.turikhay.ru |
| suspicious |
tlaun.ch |
| unknown |
eu01-www.tlaun.ch |
| unknown |
eu02-www.tlaun.ch |
| unknown |
ru01-www.tlaun.ch |
| suspicious |
ru02-www.tlaun.ch |
| unknown |
eu01-www.tln4.ru |
| unknown |
eu02-www.tln4.ru |
| unknown |
ru01-www.tln4.ru |
| suspicious |
ru02-www.tln4.ru |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2700 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2700 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2700 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2700 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2700 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2700 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2700 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
— | — | Potentially Bad Traffic | ET DNS Query for .to TLD |
— | — | Potentially Bad Traffic | ET DNS Query for .to TLD |