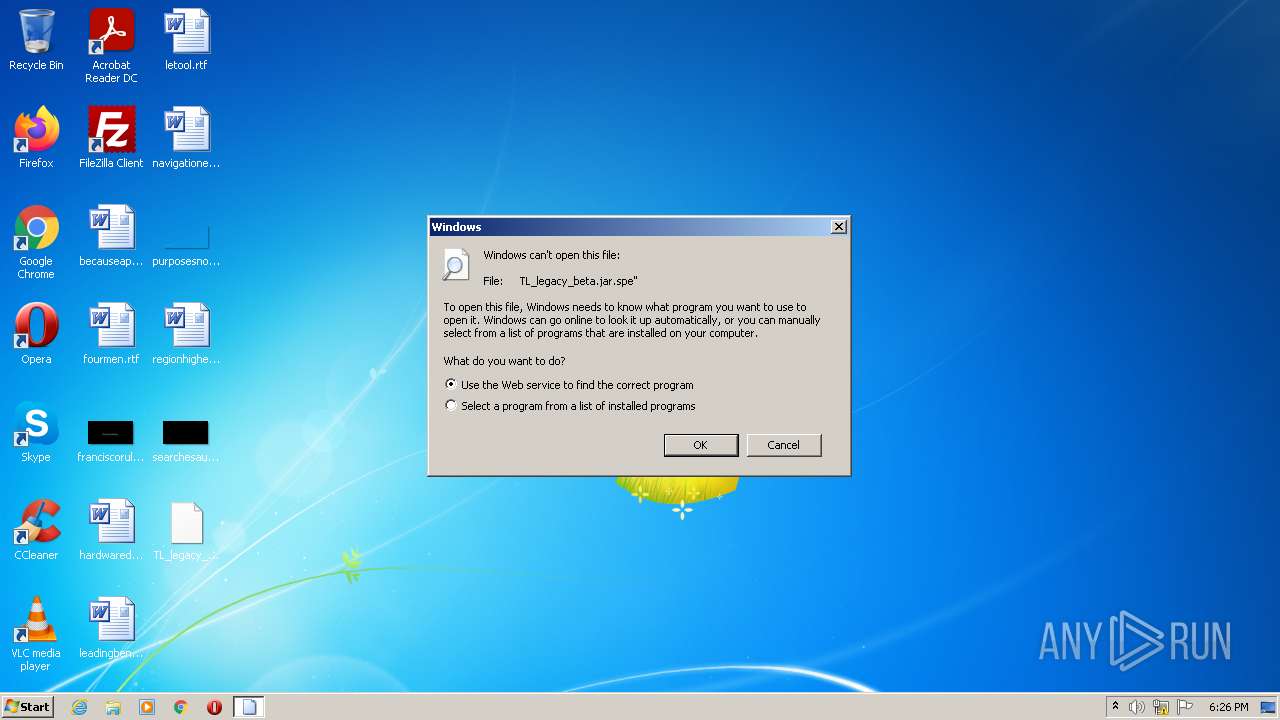
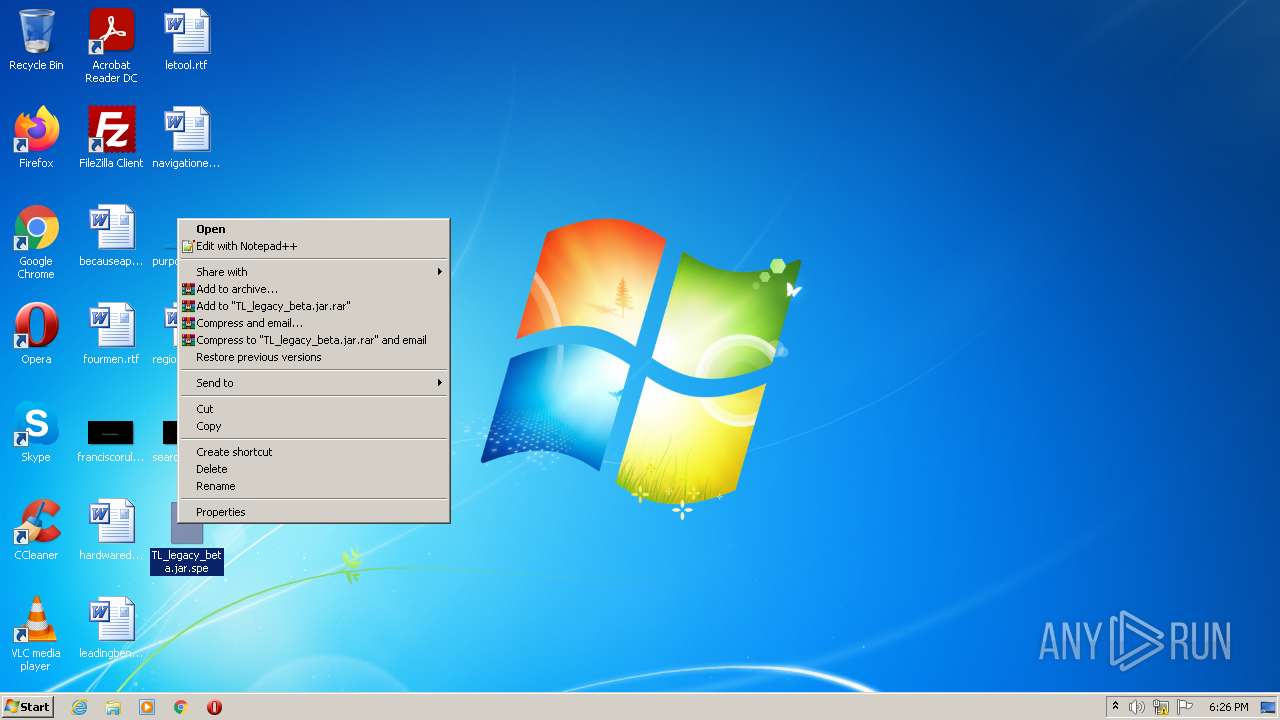
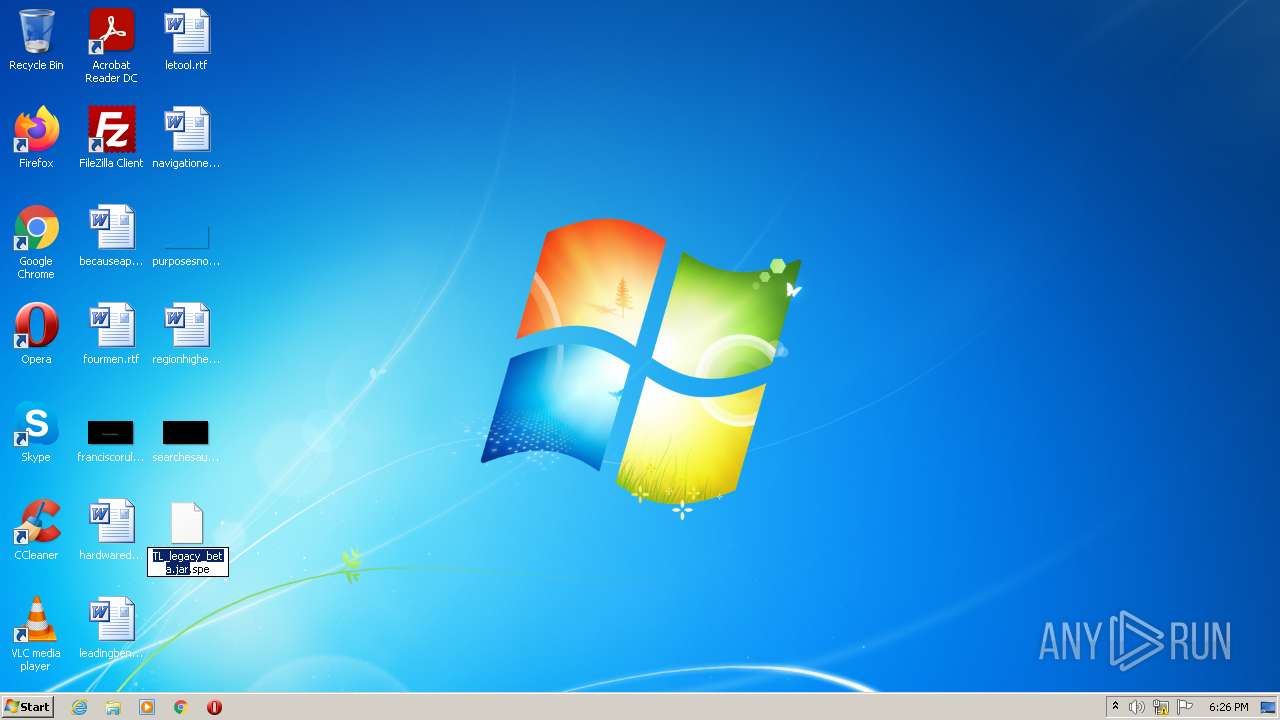
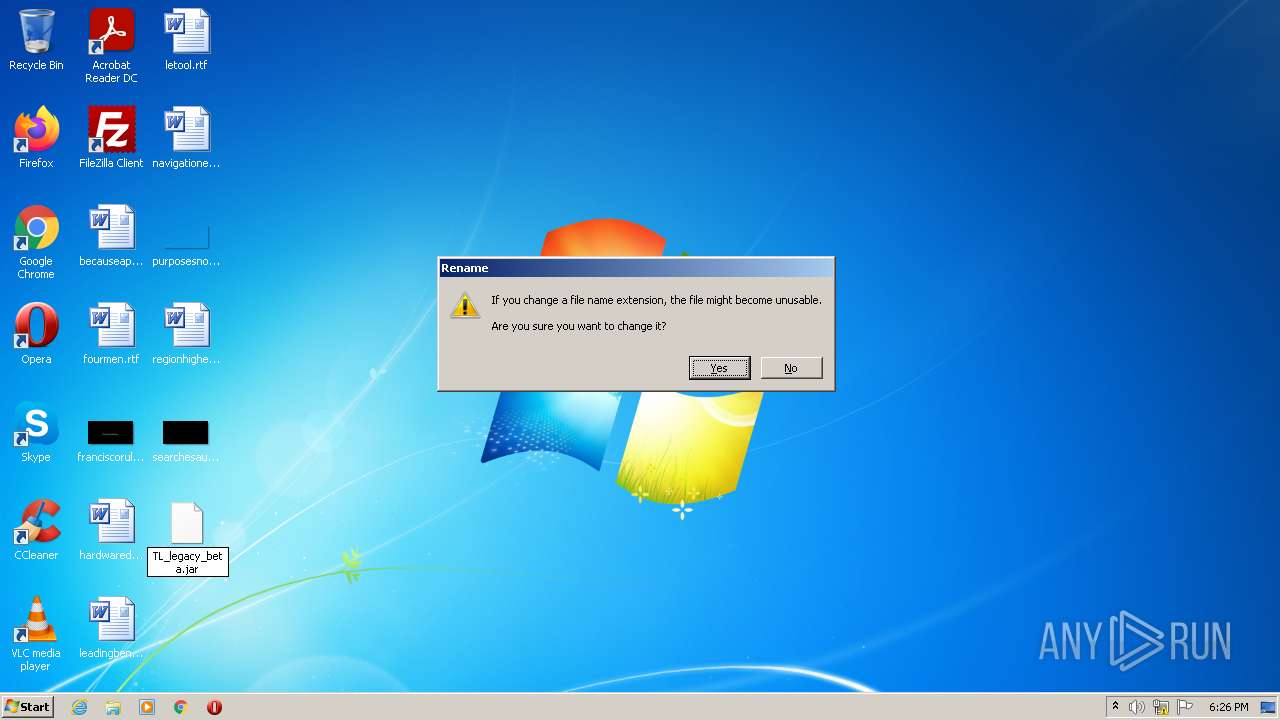
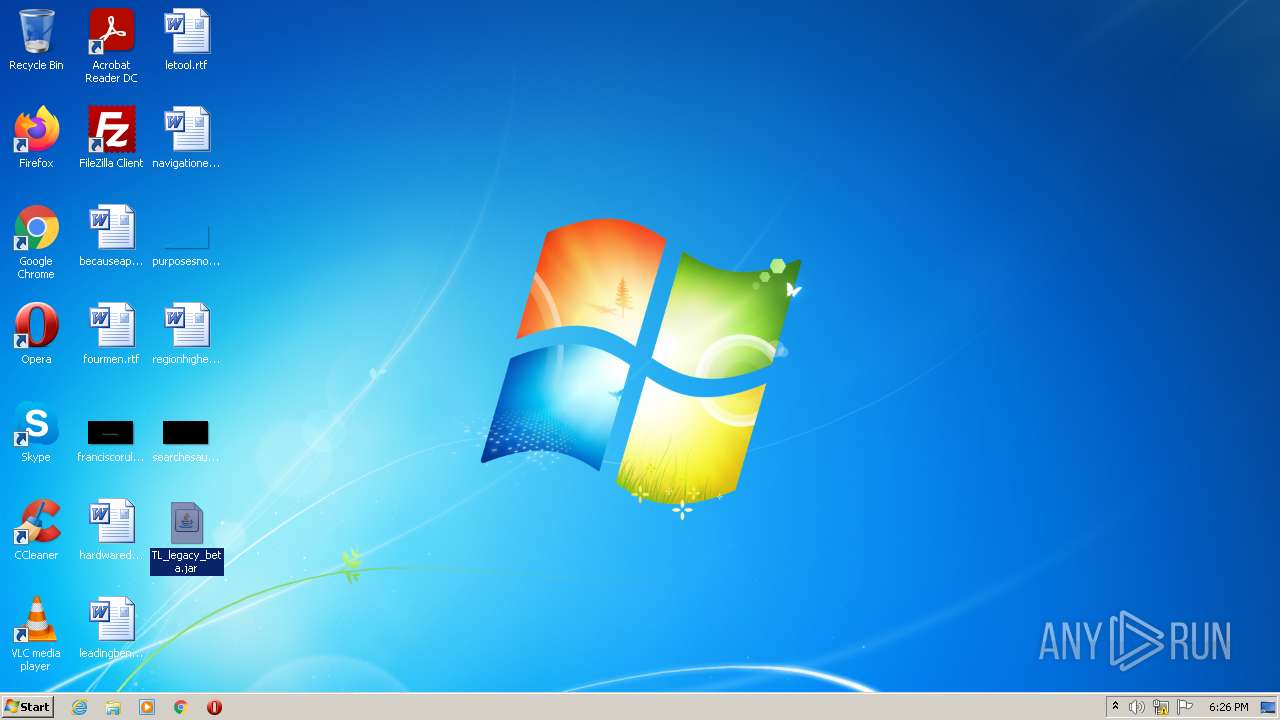
| File name: | TL_legacy_beta.jar |
| Full analysis: | https://app.any.run/tasks/38cd1bd9-7b2e-4b2b-9e6e-49584cc055ec |
| Verdict: | Malicious activity |
| Analysis date: | August 12, 2022, 17:26:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | 83547D1727806A69E16FE4C6C1417D2C |
| SHA1: | 5655500DC45868B929328A96601807BF81FF2FD2 |
| SHA256: | B59DA929C81B76F2EA1AD1280FEA1D550EFE02FCF89B13E6157E449F51E13617 |
| SSDEEP: | 98304:WfEALdvFlvA8qqrAZfast+9FtMMypuf7qCHPoeefjGlOk:WnhqhJast4zypufmcAfjCOk |
MALICIOUS
No malicious indicators.SUSPICIOUS
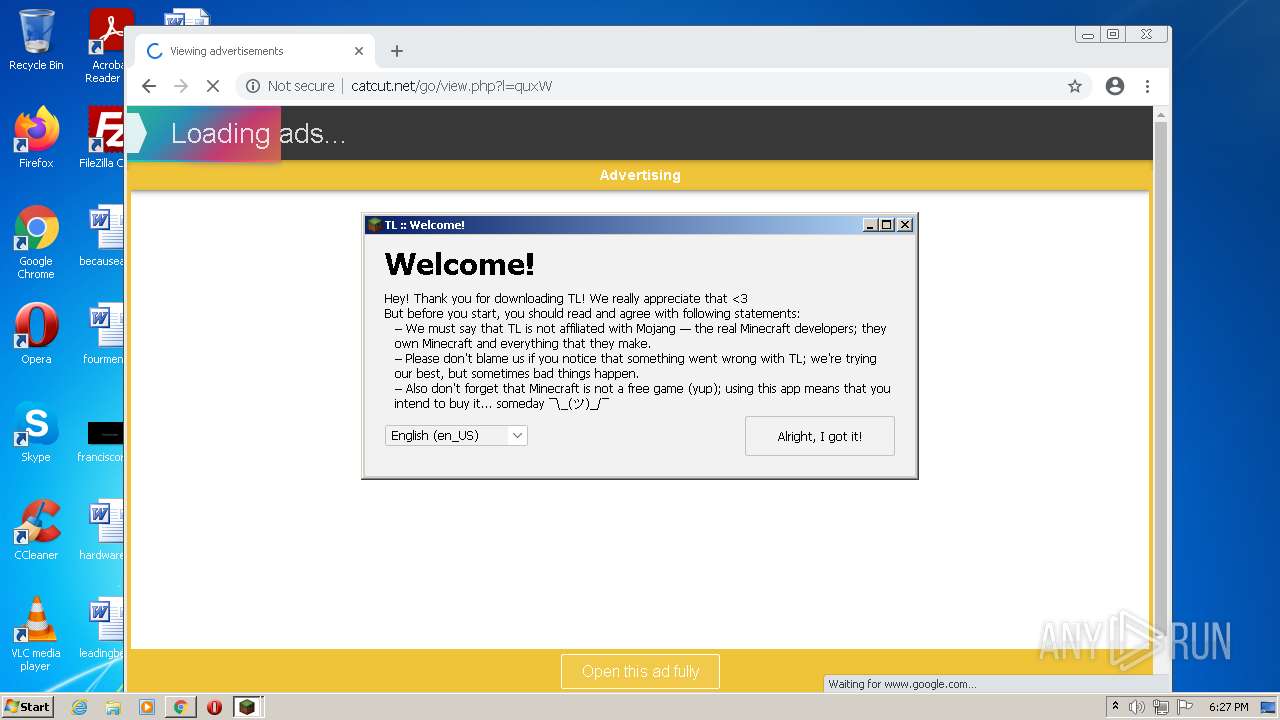
Checks supported languages
- javaw.exe (PID: 2028)
- java.exe (PID: 1568)
- java.exe (PID: 2252)
- javaw.exe (PID: 2532)
Creates files in the program directory
- javaw.exe (PID: 2532)
Reads the computer name
- java.exe (PID: 2252)
- java.exe (PID: 1568)
Modifies files in Chrome extension folder
- chrome.exe (PID: 688)
INFO
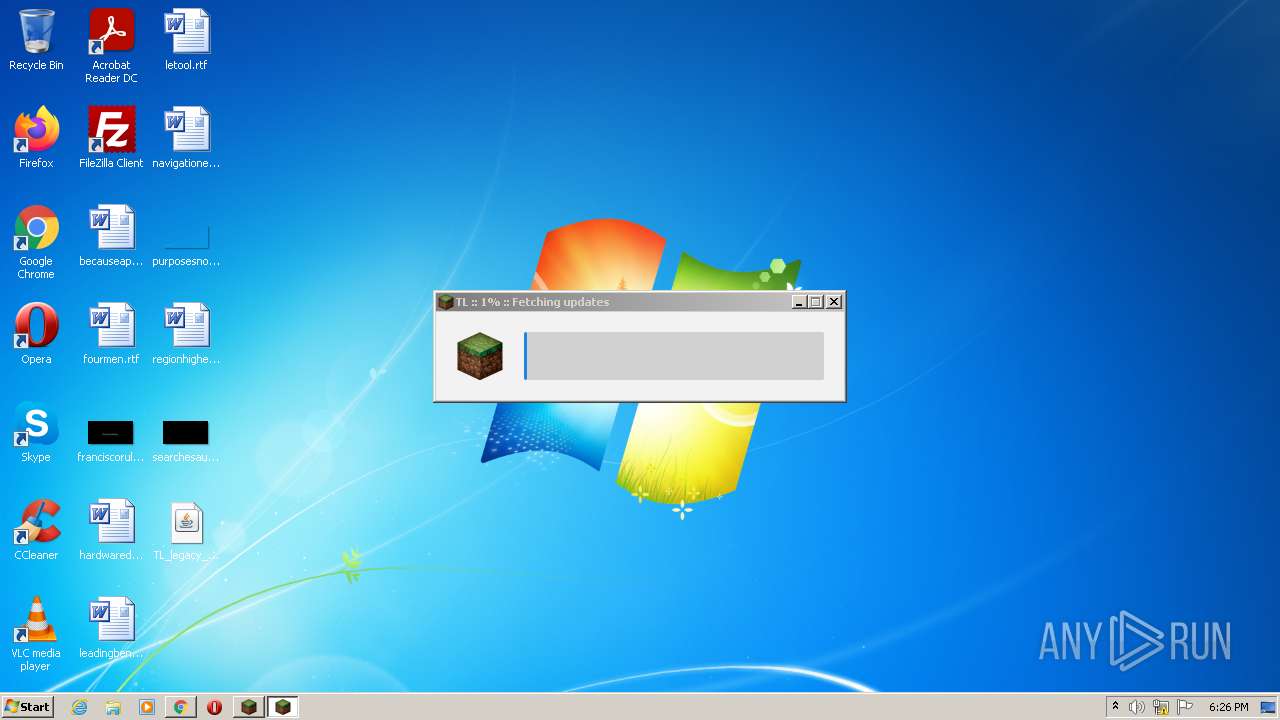
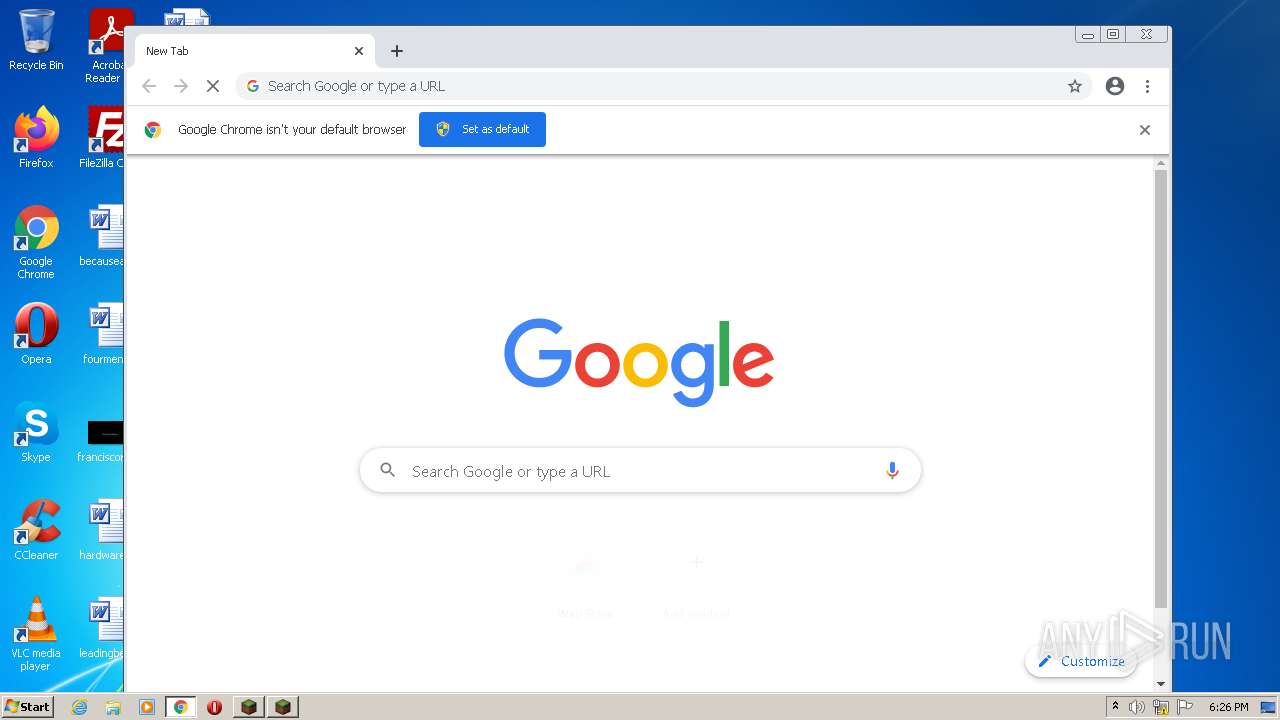
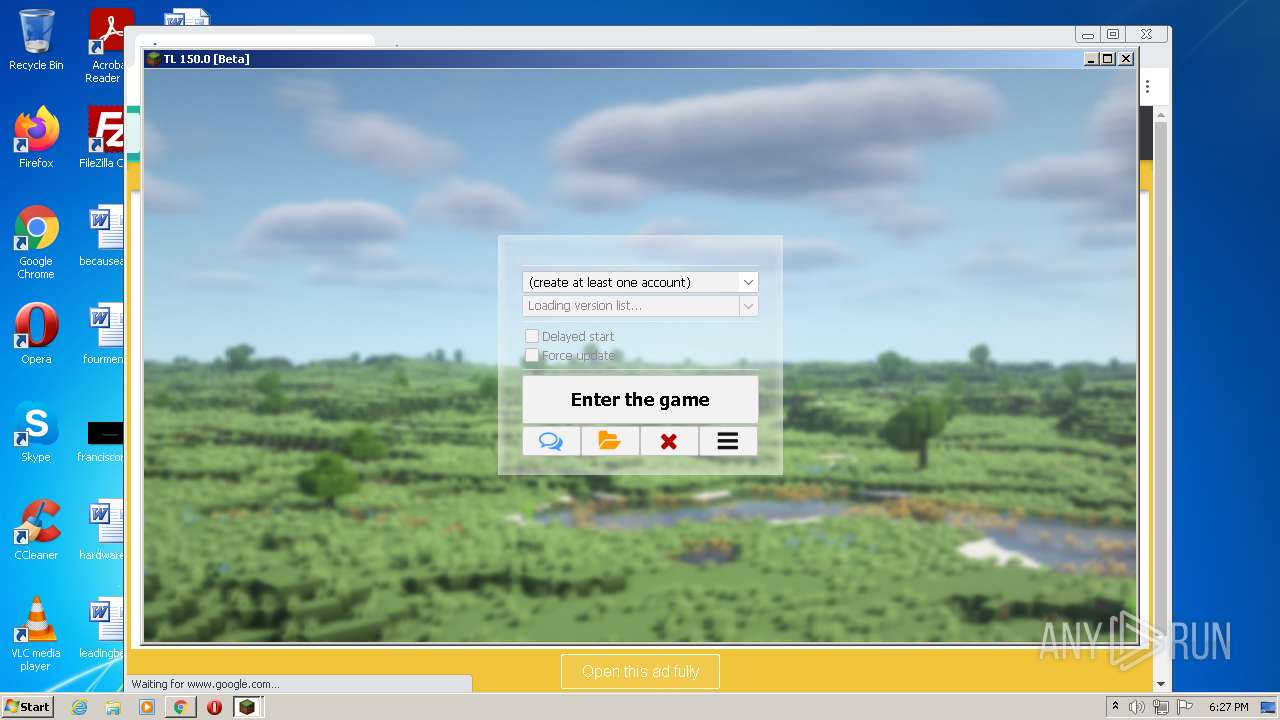
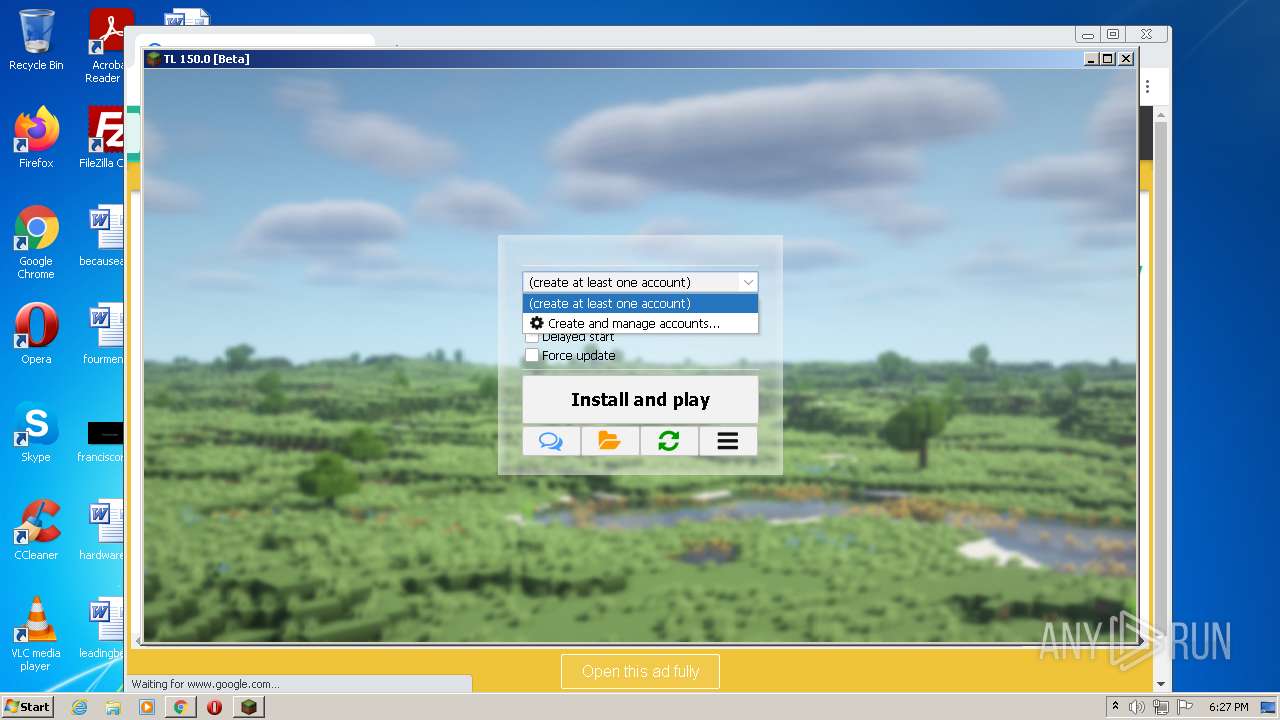
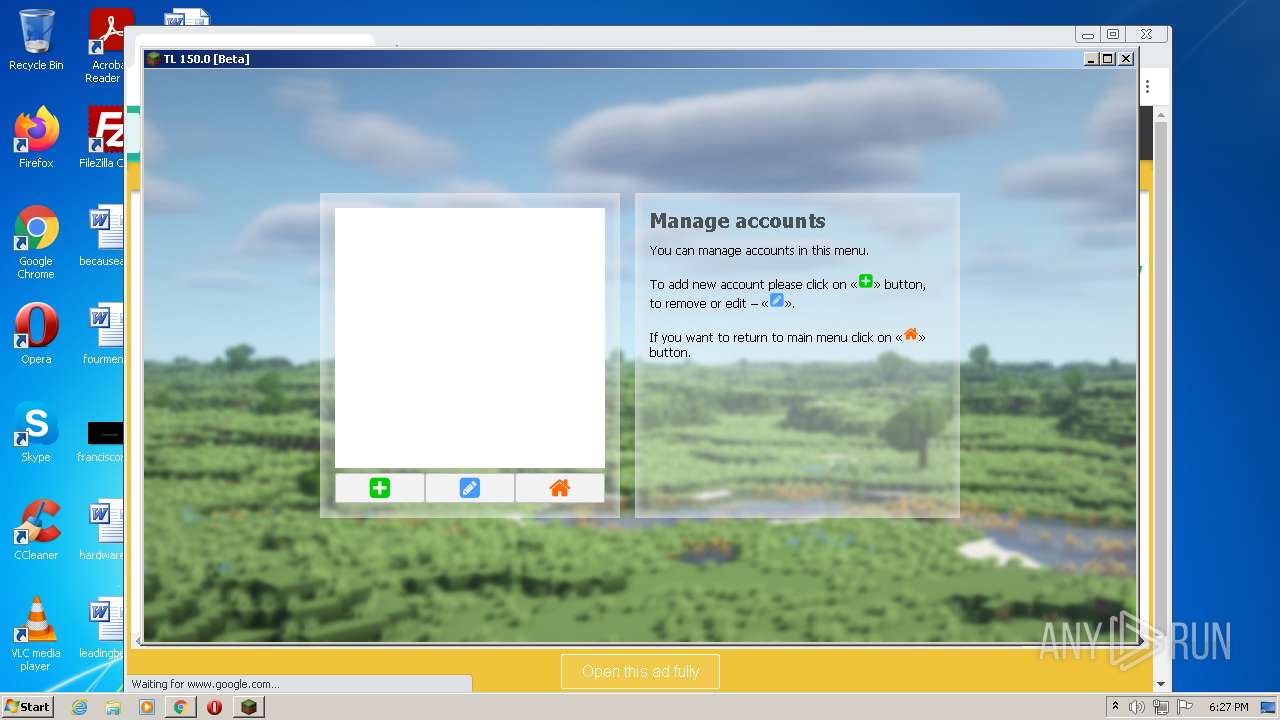
Manual execution by user
- javaw.exe (PID: 2028)
- javaw.exe (PID: 2532)
- chrome.exe (PID: 688)
Checks supported languages
- rundll32.exe (PID: 3088)
- icacls.exe (PID: 1956)
- chrome.exe (PID: 688)
- chrome.exe (PID: 1524)
- chrome.exe (PID: 2352)
- chrome.exe (PID: 1100)
- chrome.exe (PID: 3708)
- chrome.exe (PID: 3696)
- chrome.exe (PID: 2092)
- chrome.exe (PID: 2456)
- chrome.exe (PID: 512)
- chrome.exe (PID: 3420)
- chrome.exe (PID: 2964)
- chrome.exe (PID: 3640)
- chrome.exe (PID: 500)
- chrome.exe (PID: 1928)
- chrome.exe (PID: 452)
- chrome.exe (PID: 4004)
- chrome.exe (PID: 3560)
- chrome.exe (PID: 2636)
- chrome.exe (PID: 4068)
- chrome.exe (PID: 3360)
- chrome.exe (PID: 2632)
- chrome.exe (PID: 3228)
- chrome.exe (PID: 1076)
- chrome.exe (PID: 1264)
- chrome.exe (PID: 2132)
- chrome.exe (PID: 3204)
- chrome.exe (PID: 1608)
- chrome.exe (PID: 3644)
- chrome.exe (PID: 468)
- chrome.exe (PID: 2084)
- chrome.exe (PID: 3384)
- chrome.exe (PID: 3284)
- chrome.exe (PID: 736)
- chrome.exe (PID: 408)
Reads the computer name
- icacls.exe (PID: 1956)
- chrome.exe (PID: 688)
- chrome.exe (PID: 1524)
- chrome.exe (PID: 2352)
- chrome.exe (PID: 2456)
- chrome.exe (PID: 2964)
- chrome.exe (PID: 3228)
- chrome.exe (PID: 3360)
- chrome.exe (PID: 3644)
- chrome.exe (PID: 2084)
Application launched itself
- chrome.exe (PID: 688)
Reads settings of System Certificates
- chrome.exe (PID: 2352)
Reads the date of Windows installation
- chrome.exe (PID: 3228)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .spe | | | SPSS Extension (54) |
|---|---|---|
| .jar | | | Java Archive (26.1) |
| .zip | | | ZIP compressed archive (7.2) |
EXIF
ZIP
| ZipFileName: | META-INF/ |
|---|---|
| ZipUncompressedSize: | - |
| ZipCompressedSize: | 2 |
| ZipCRC: | 0x00000000 |
| ZipModifyDate: | 1980:02:01 00:00:00 |
| ZipCompression: | Deflated |
| ZipBitFlag: | 0x0800 |
| ZipRequiredVersion: | 10 |
Total processes
80
Monitored processes
40
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,9106678284307374459,8086873780355680641,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3188 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1056,9106678284307374459,8086873780355680641,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3108 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1056,9106678284307374459,8086873780355680641,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1940 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 500 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1056,9106678284307374459,8086873780355680641,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3252 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 512 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1056,9106678284307374459,8086873780355680641,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3188 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 688 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,9106678284307374459,8086873780355680641,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=32 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2724 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,9106678284307374459,8086873780355680641,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3720 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1100 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6e6bd988,0x6e6bd998,0x6e6bd9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1264 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1056,9106678284307374459,8086873780355680641,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2500 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
12 620
Read events
12 468
Write events
144
Delete events
8
Modification events
| (PID) Process: | (2252) java.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: java.exe | |||
| (PID) Process: | (1568) java.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: java.exe | |||
| (PID) Process: | (688) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (688) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (688) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (688) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (688) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (688) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (688) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (688) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
20
Suspicious files
193
Text files
165
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 688 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-62F68D4D-2B0.pma | — | |
MD5:— | SHA256:— | |||
| 2352 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\index | binary | |
MD5:— | SHA256:— | |||
| 2532 | javaw.exe | C:\ProgramData\Oracle\Java\.oracle_jre_usage\17dfc292991c8061.timestamp | text | |
MD5:— | SHA256:— | |||
| 688 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\eb7d6f83-93e1-43ef-a265-0739002fca96.tmp | text | |
MD5:— | SHA256:— | |||
| 1100 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 688 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 688 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 688 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFdfca0.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 688 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFdfca0.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 688 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RFdfcbf.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
87
DNS requests
52
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | — | — | whitelisted |
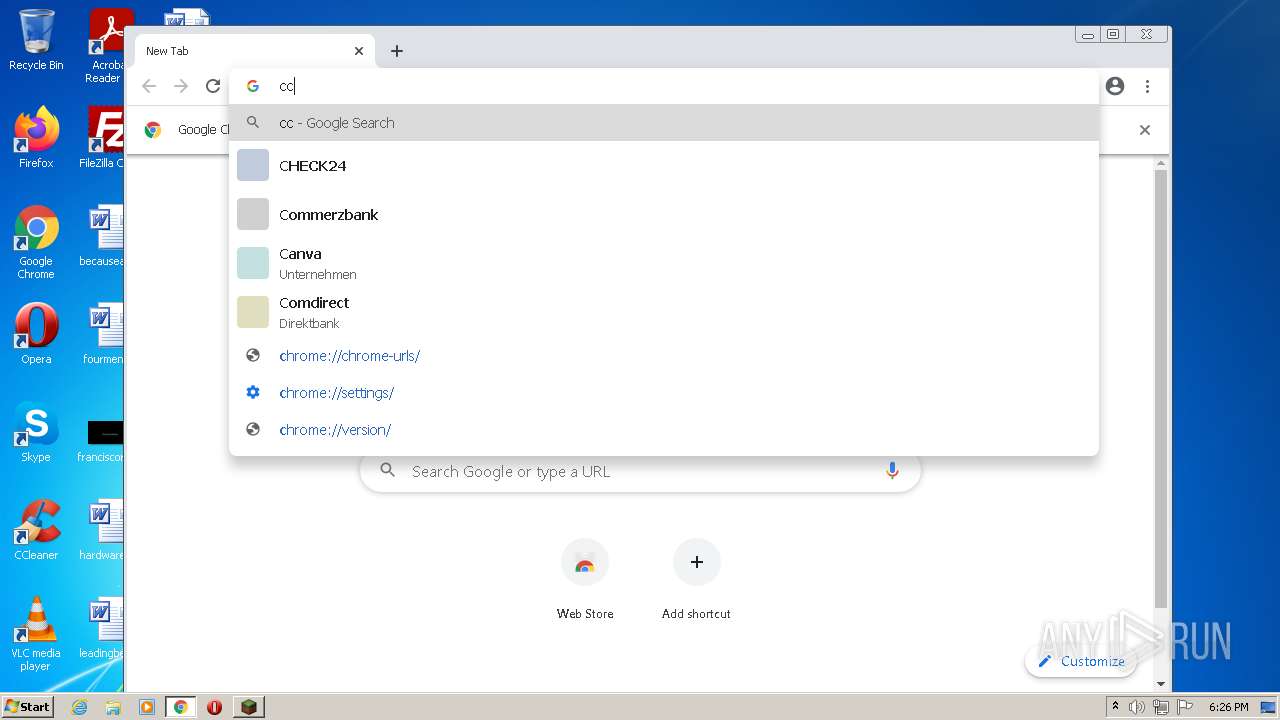
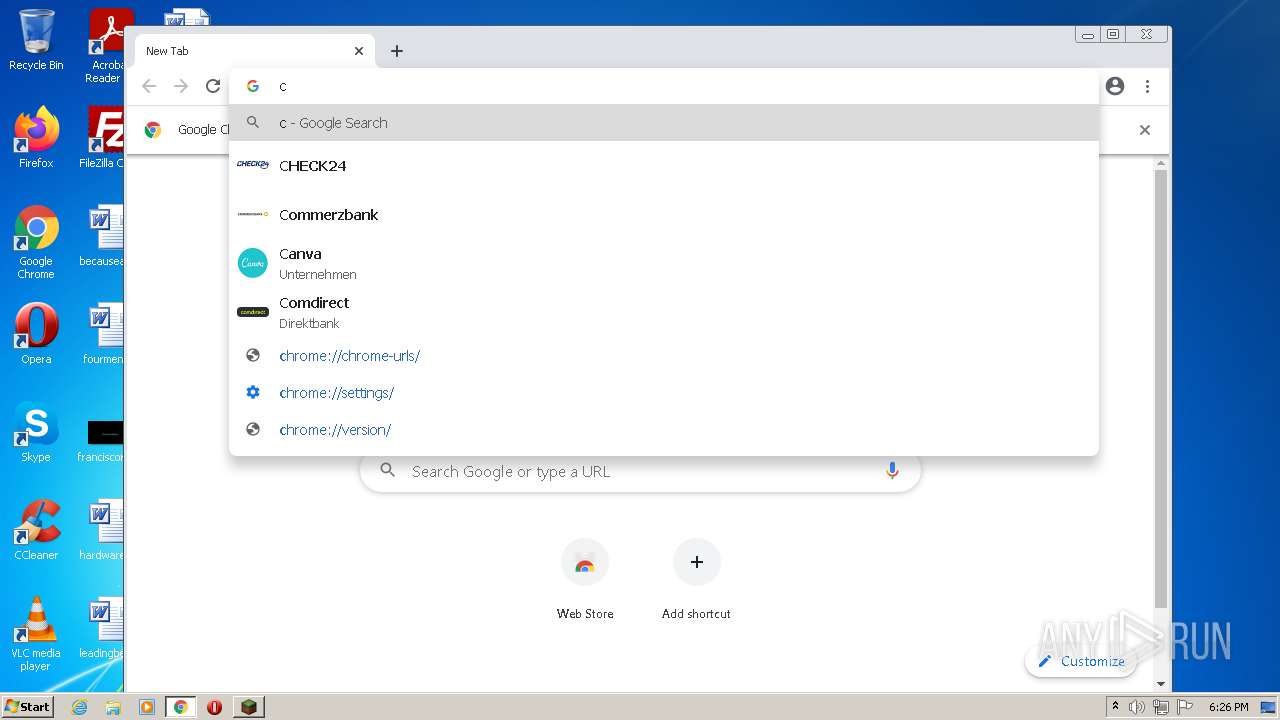
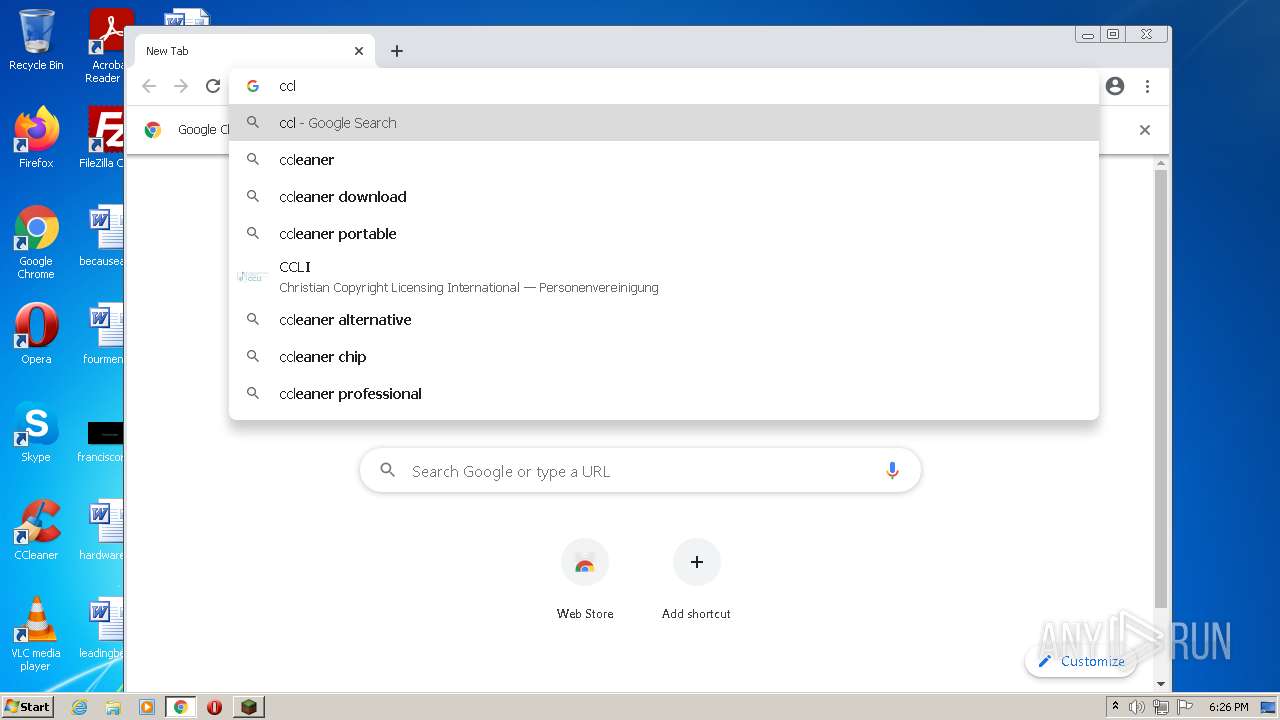
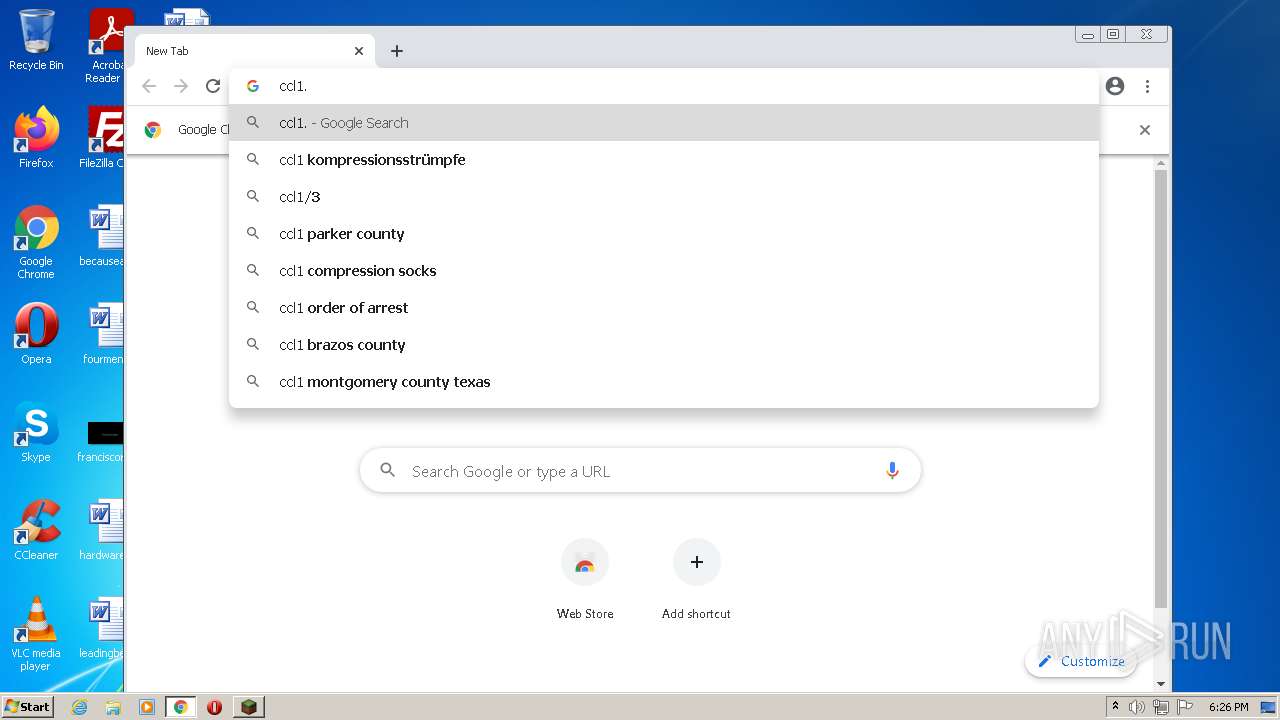
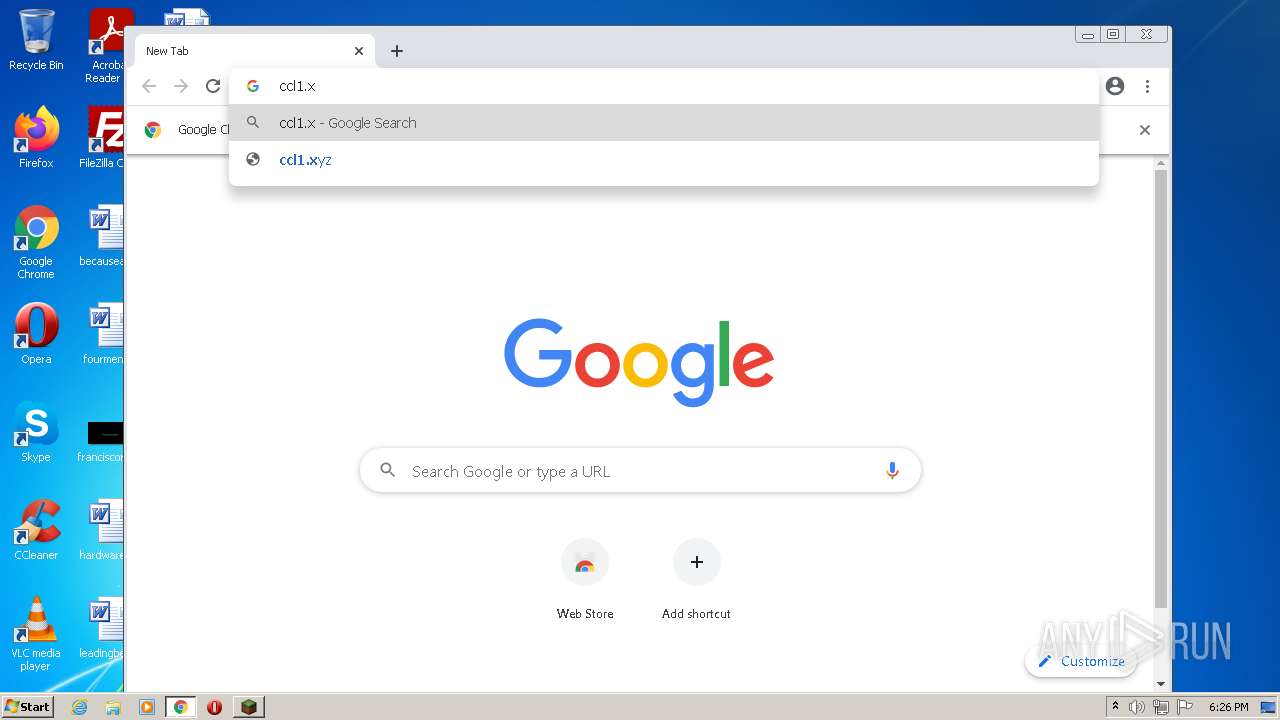
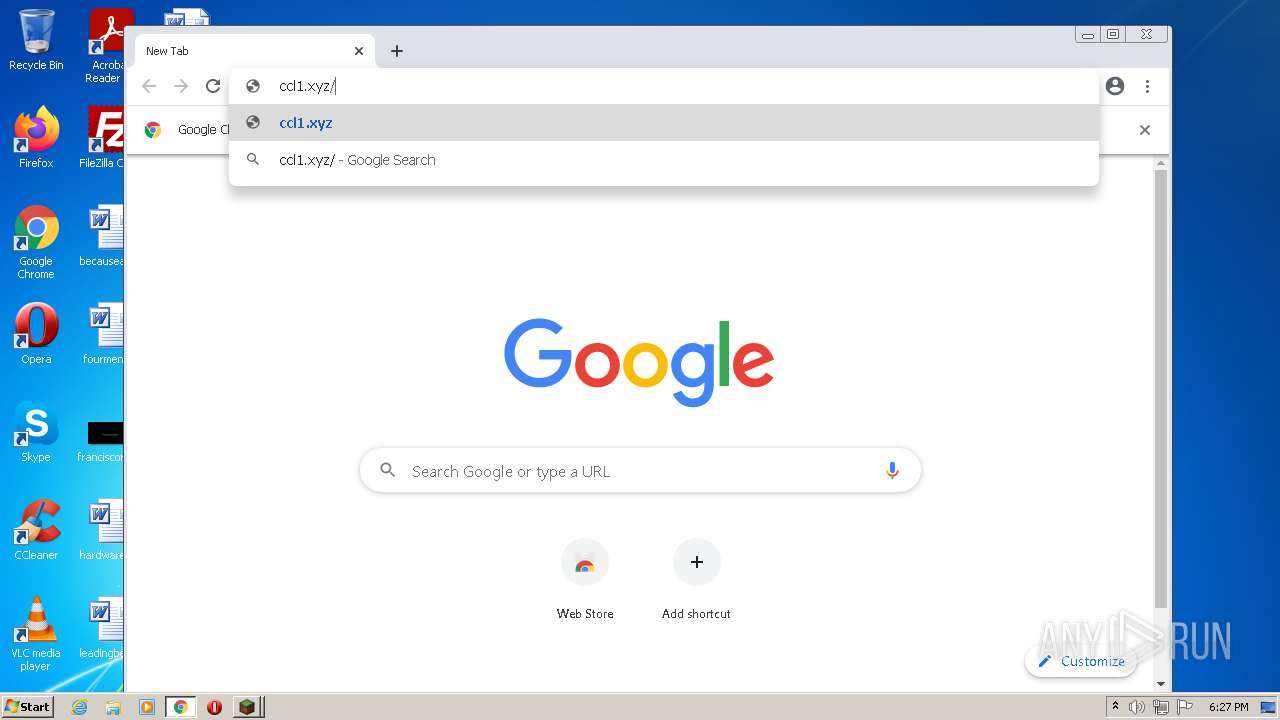
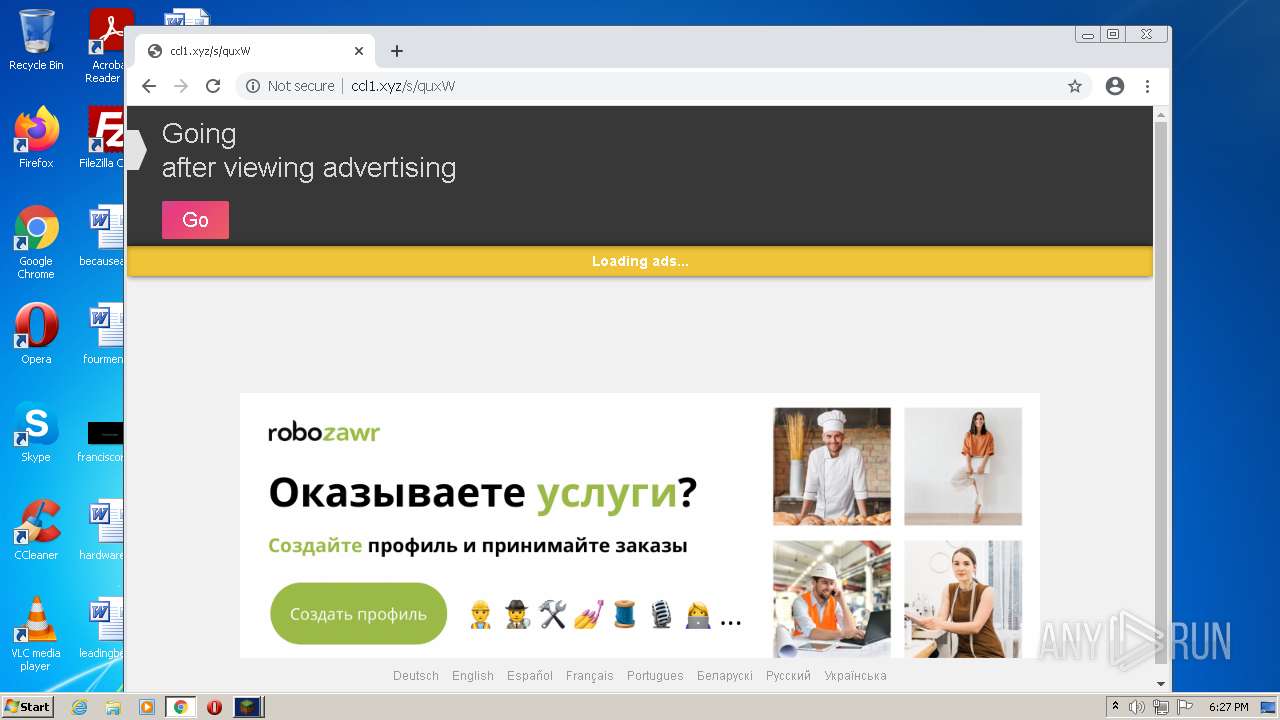
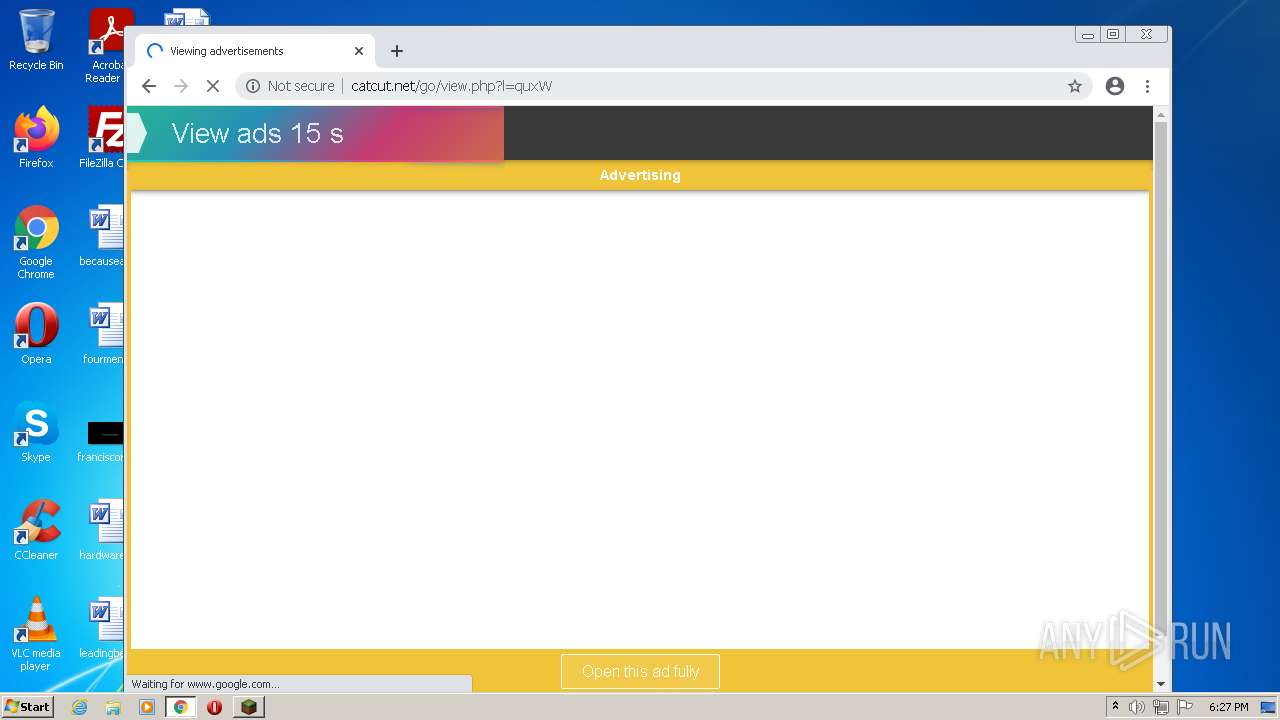
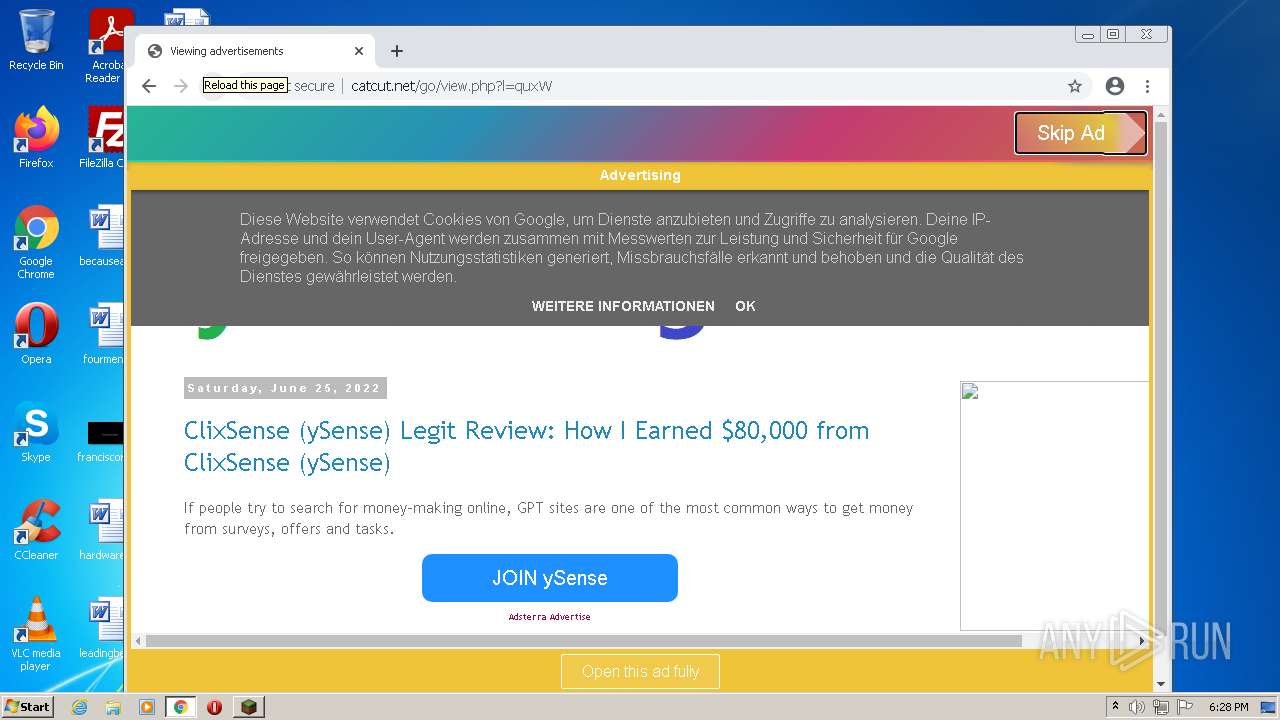
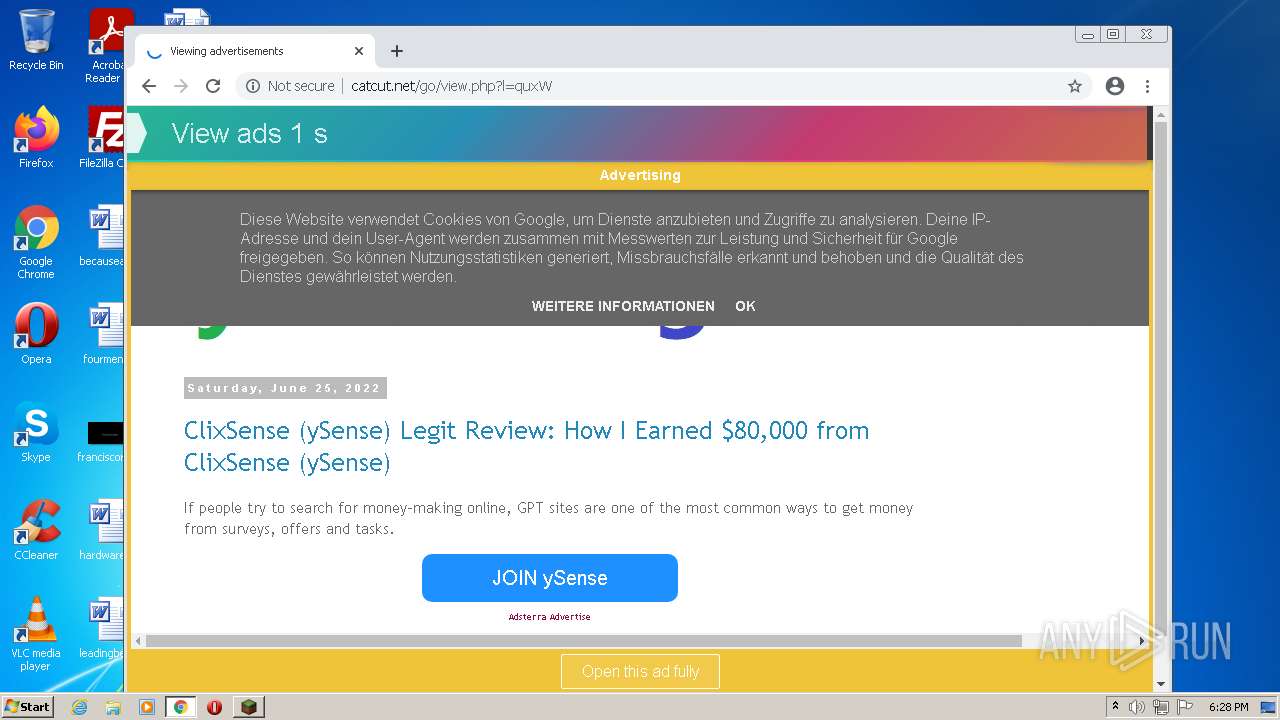
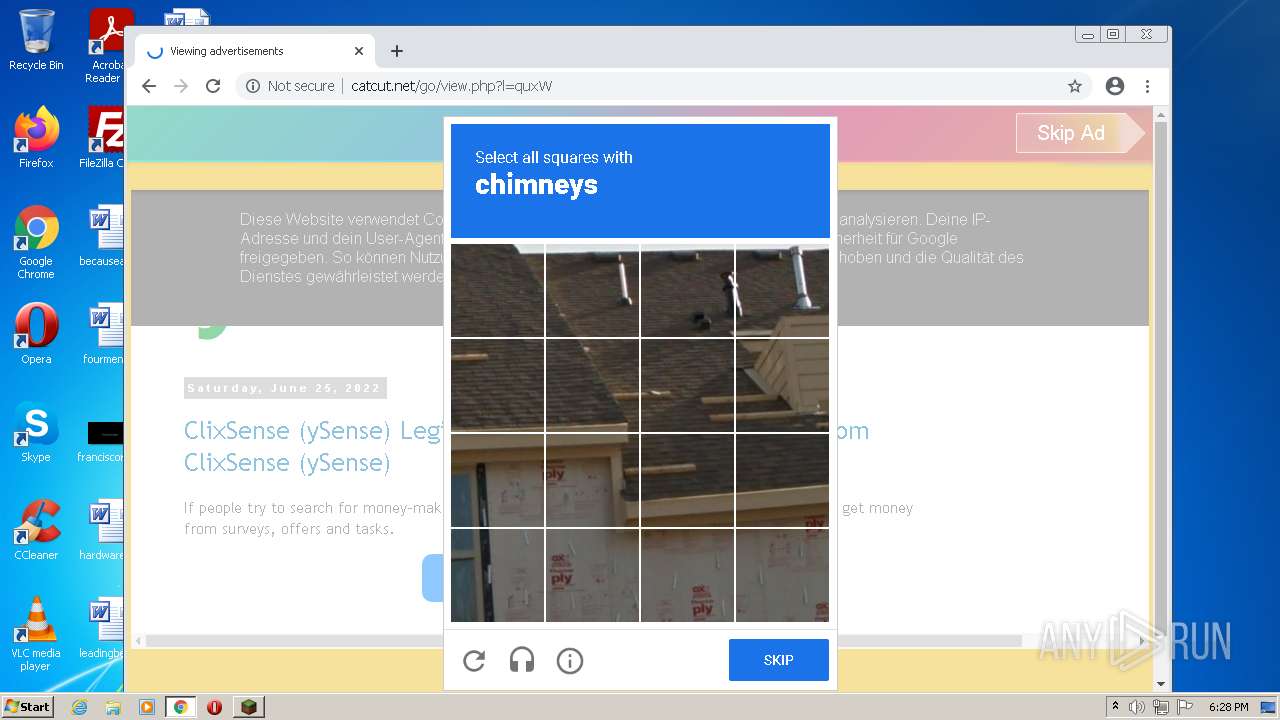
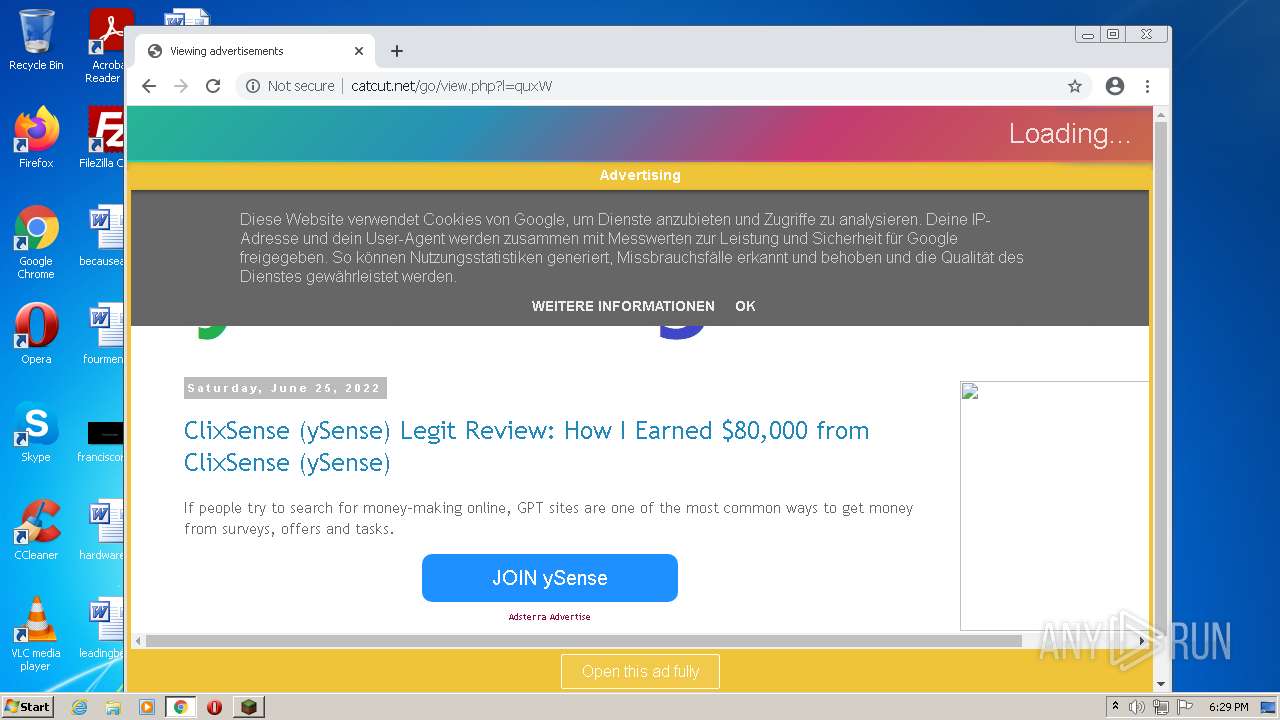
2352 | chrome.exe | GET | 200 | 79.132.136.12:80 | http://ccl1.xyz/s/quxW | DE | html | 7.96 Kb | suspicious |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 9.69 Kb | whitelisted |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 9.69 Kb | whitelisted |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 43.4 Kb | whitelisted |
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvODJiQUFYYVJaZ0k5di1hUFlXS1prX2xDZw/1.0.0.13_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | binary | 45.9 Kb | whitelisted |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 20.9 Kb | whitelisted |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 45.9 Kb | whitelisted |
2352 | chrome.exe | GET | 404 | 79.132.136.12:80 | http://catcut.net/favicon.ico | DE | html | 65.4 Kb | suspicious |
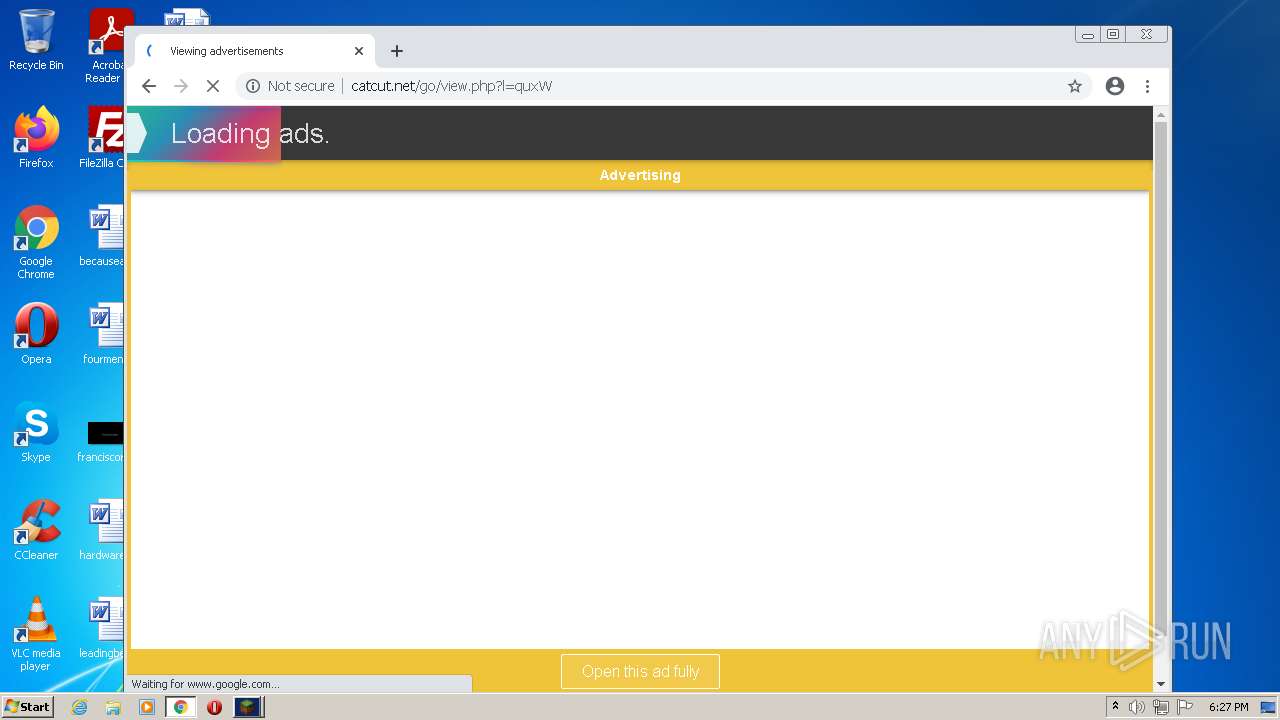
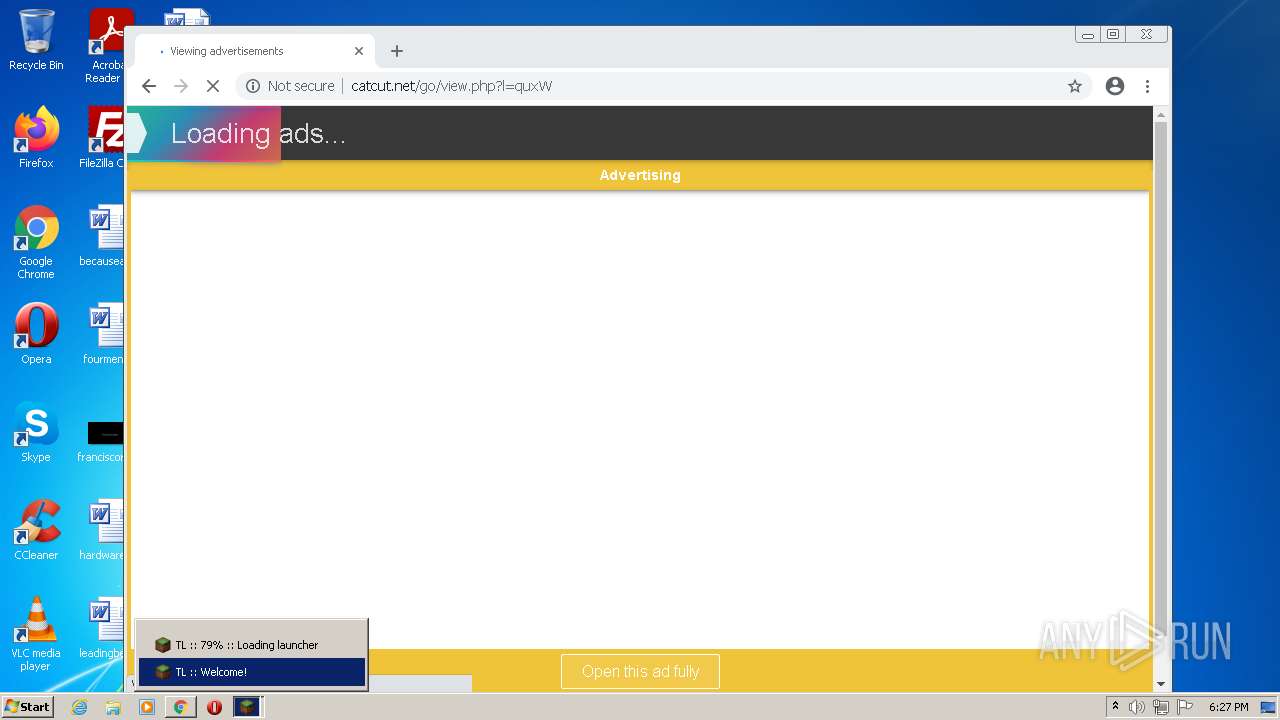
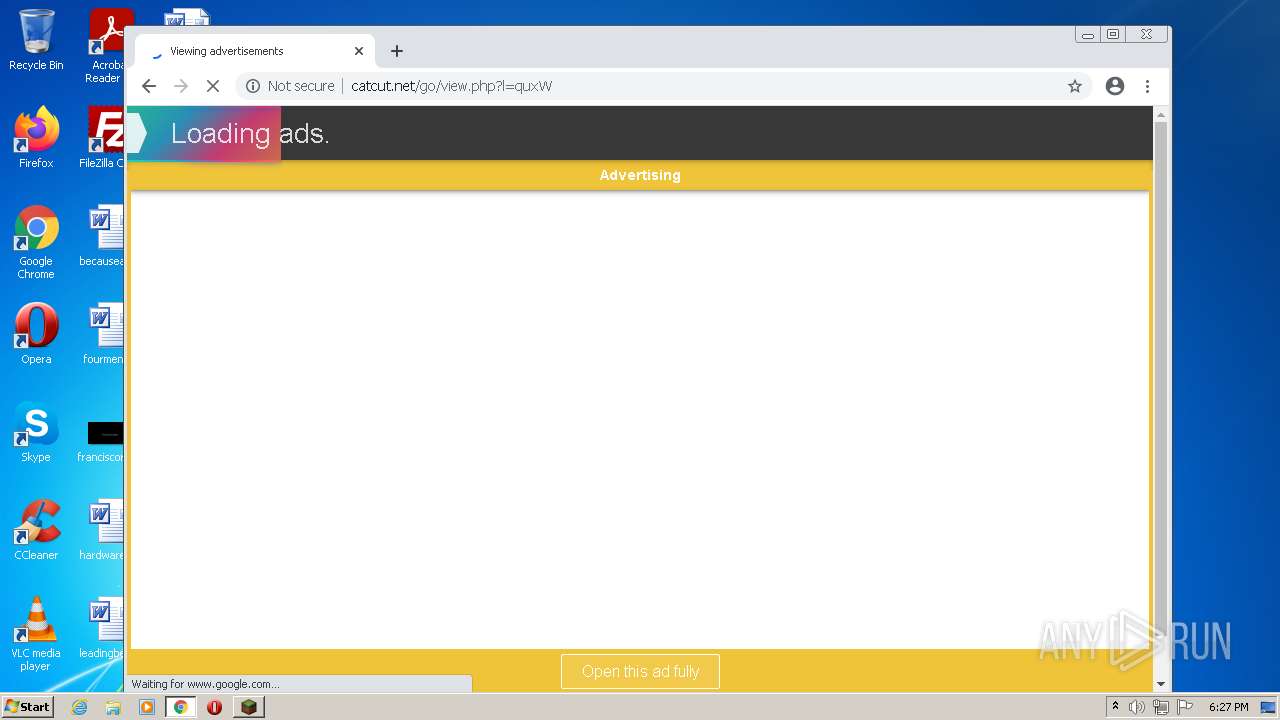
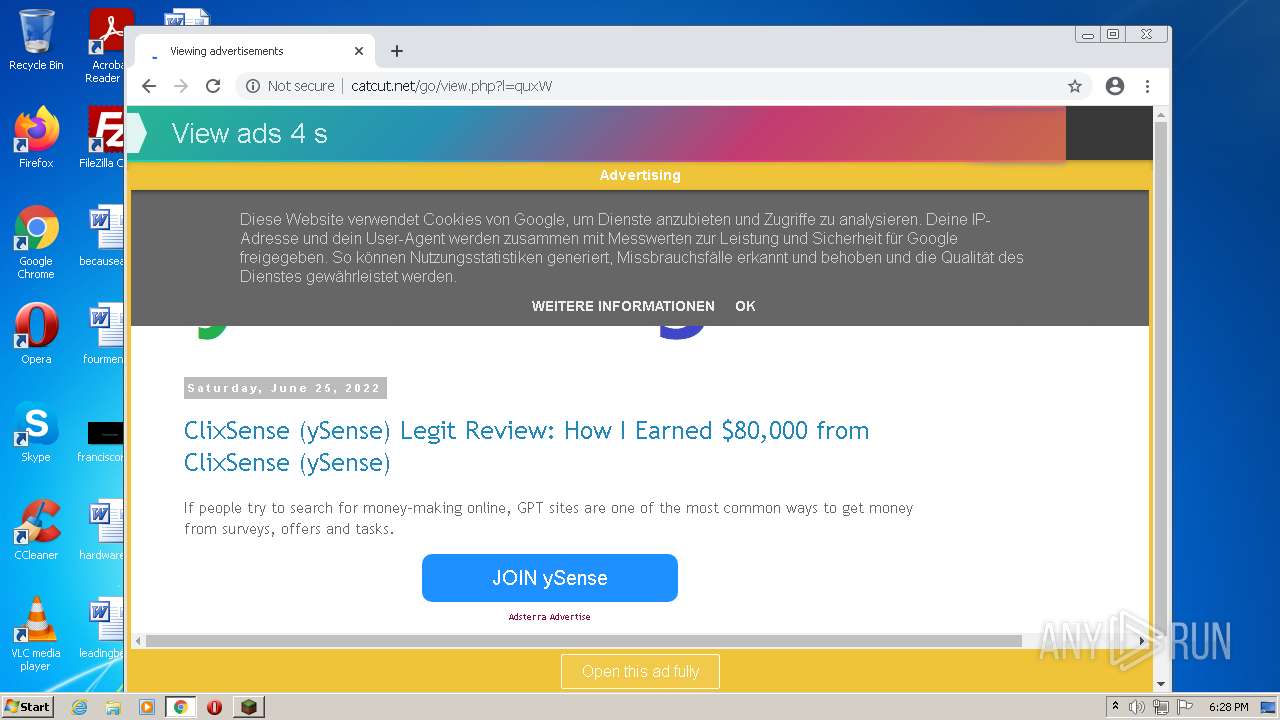
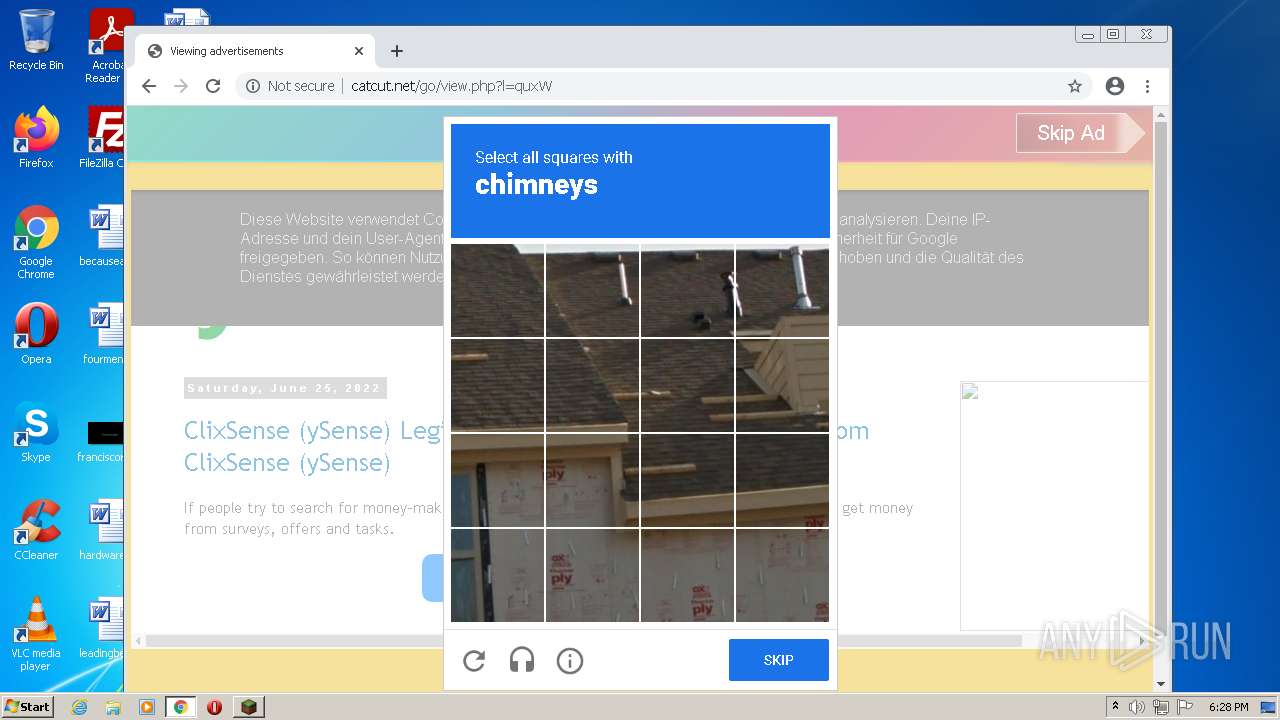
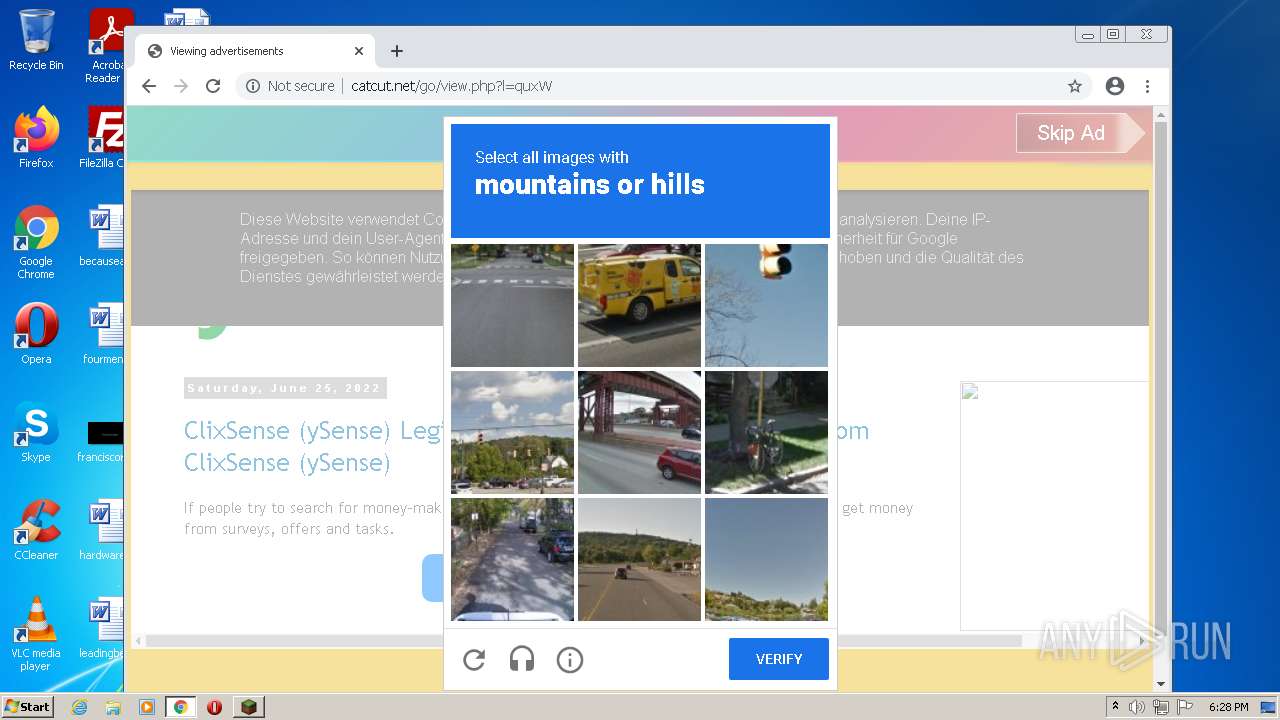
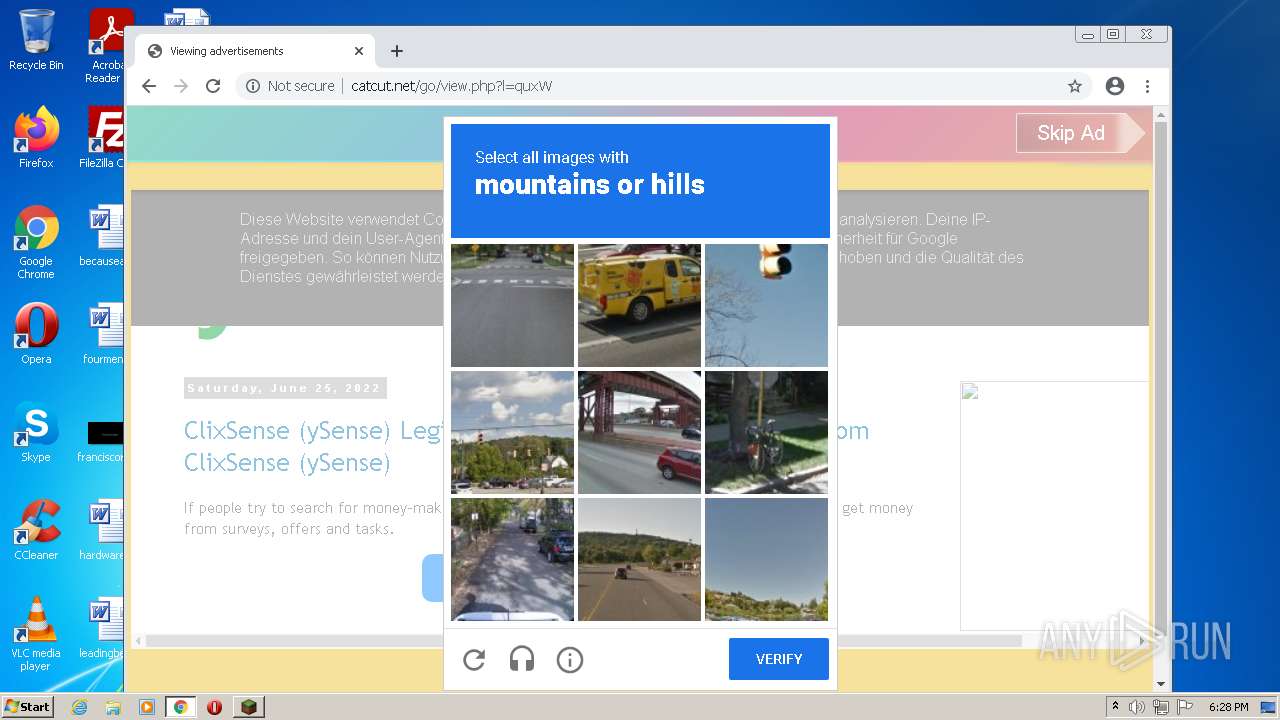
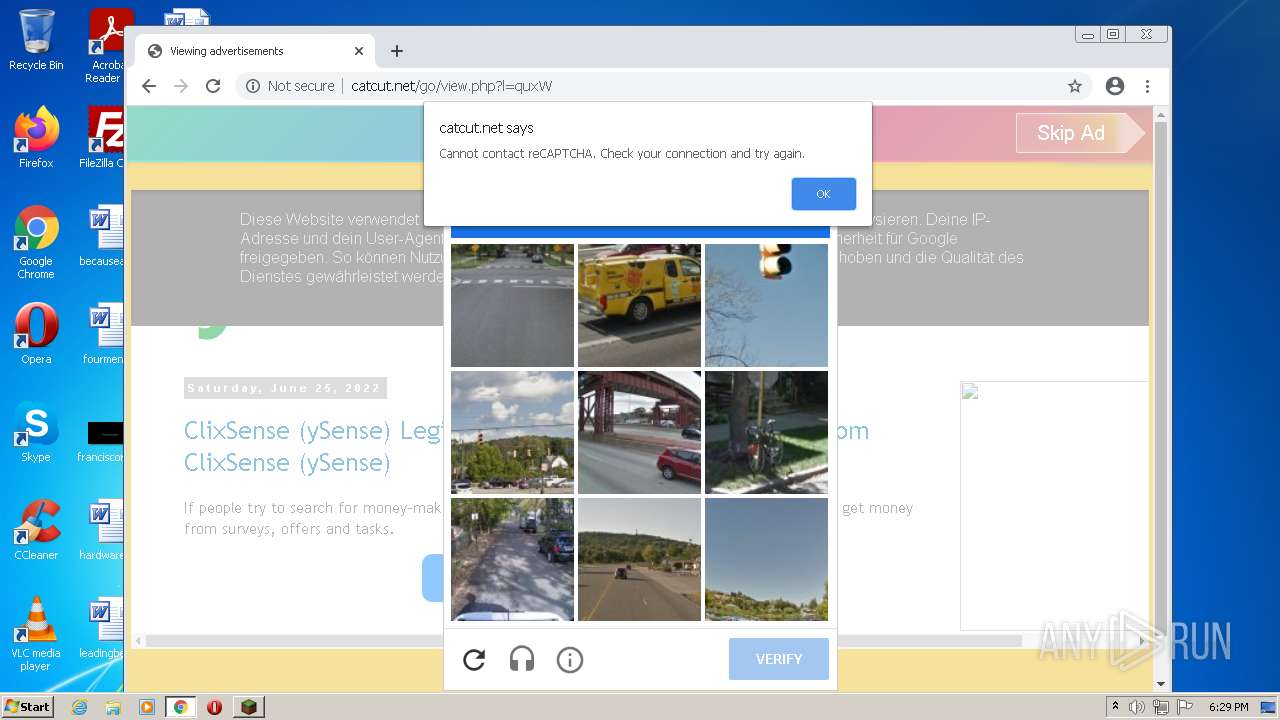
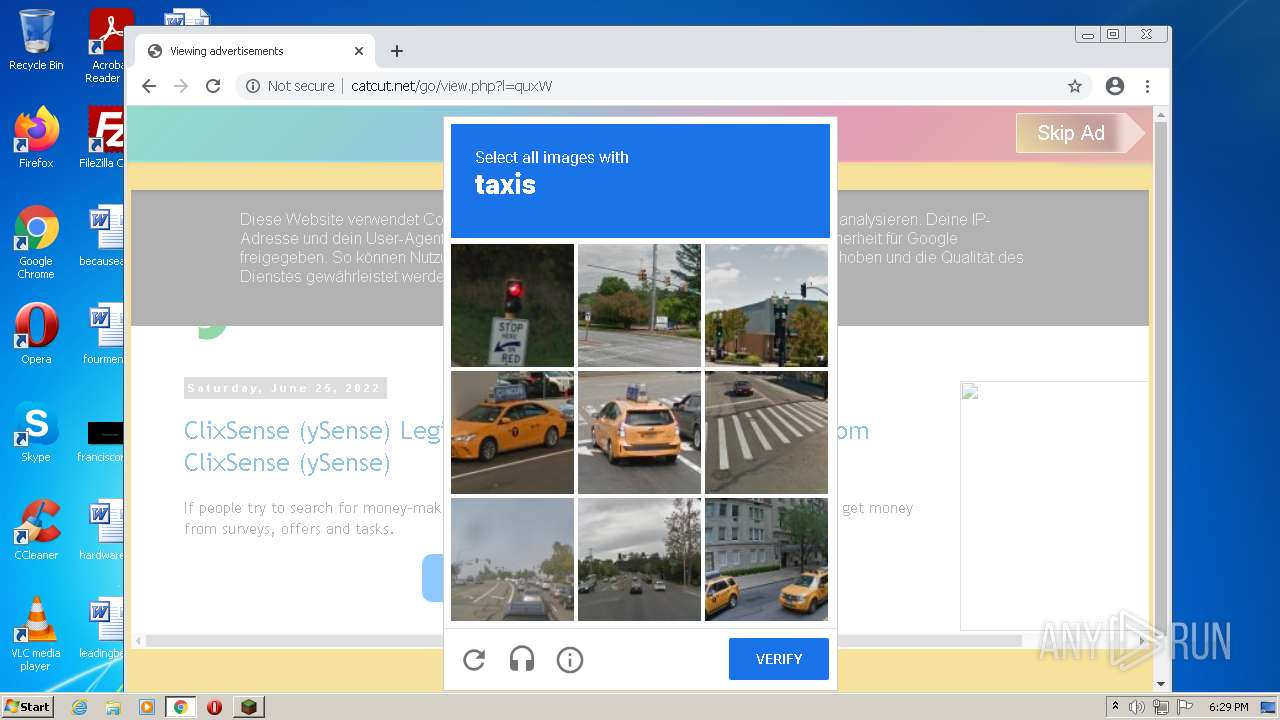
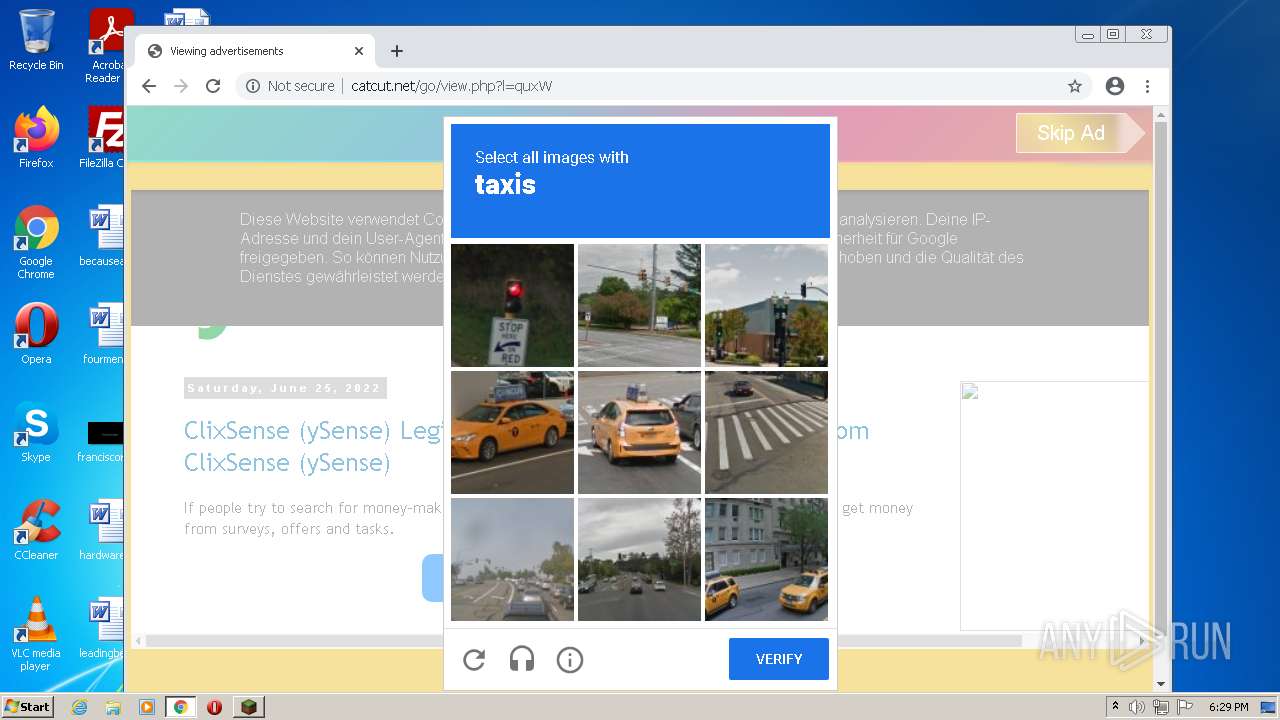
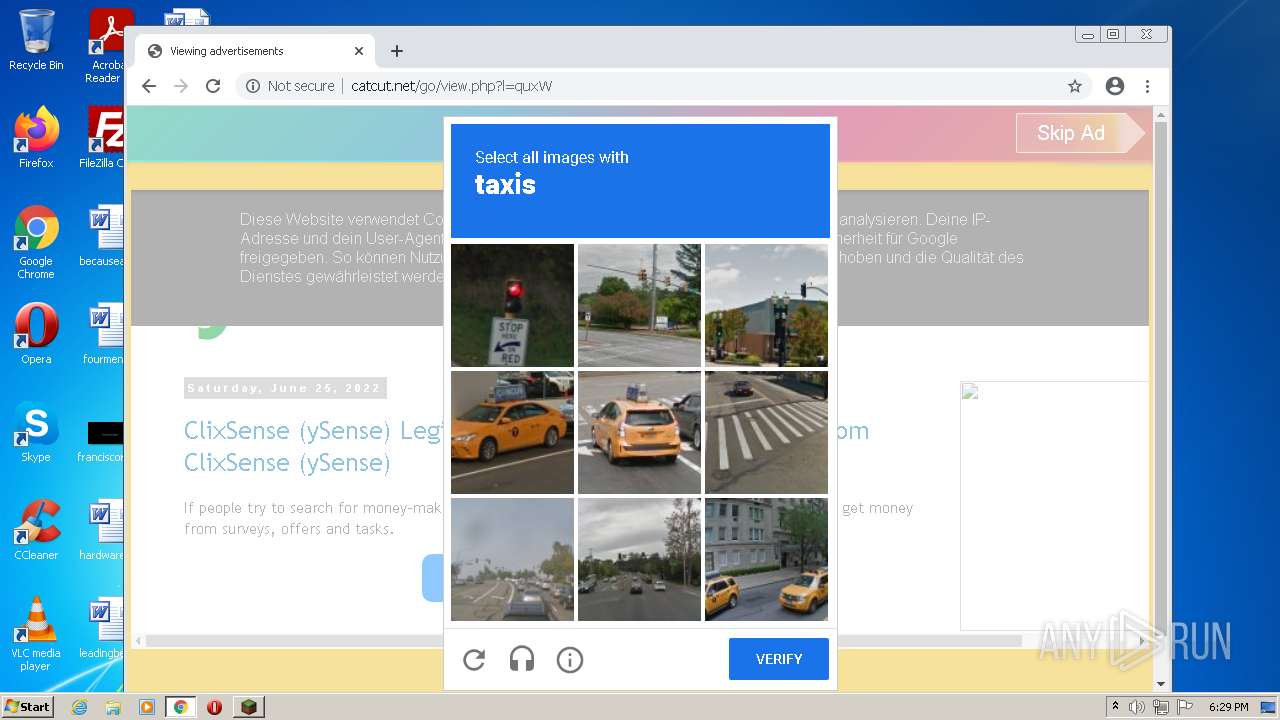
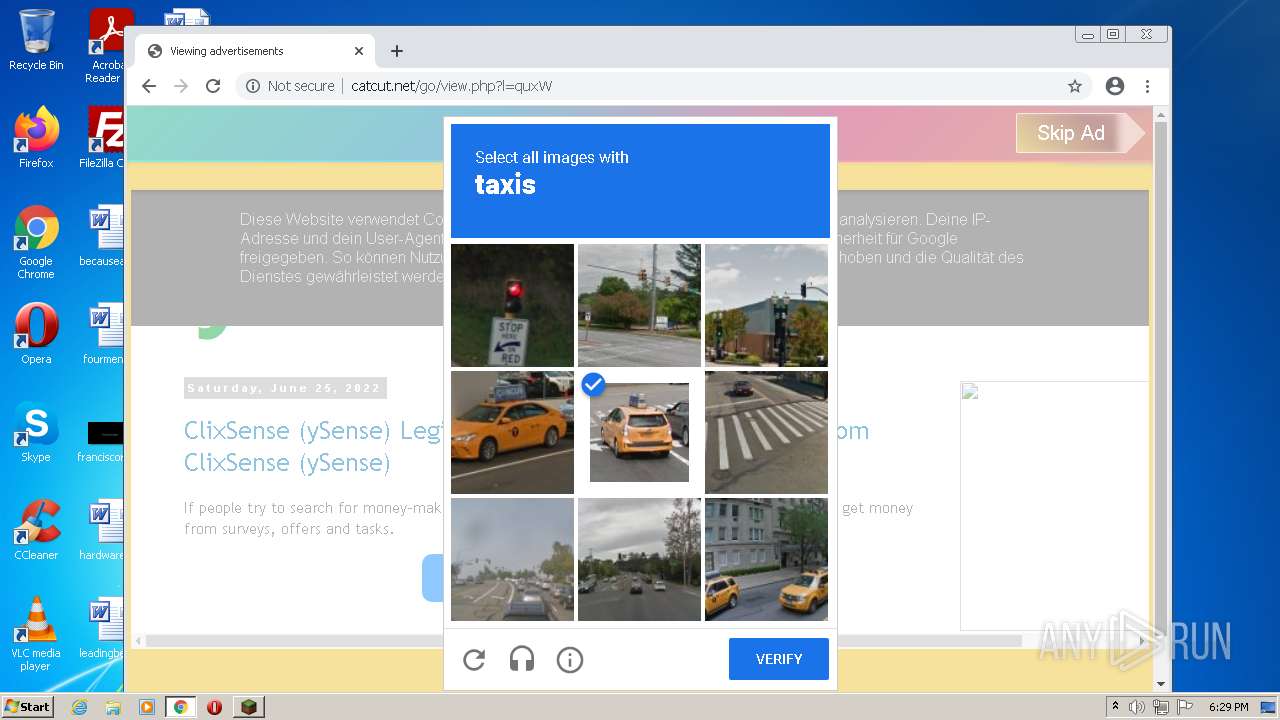
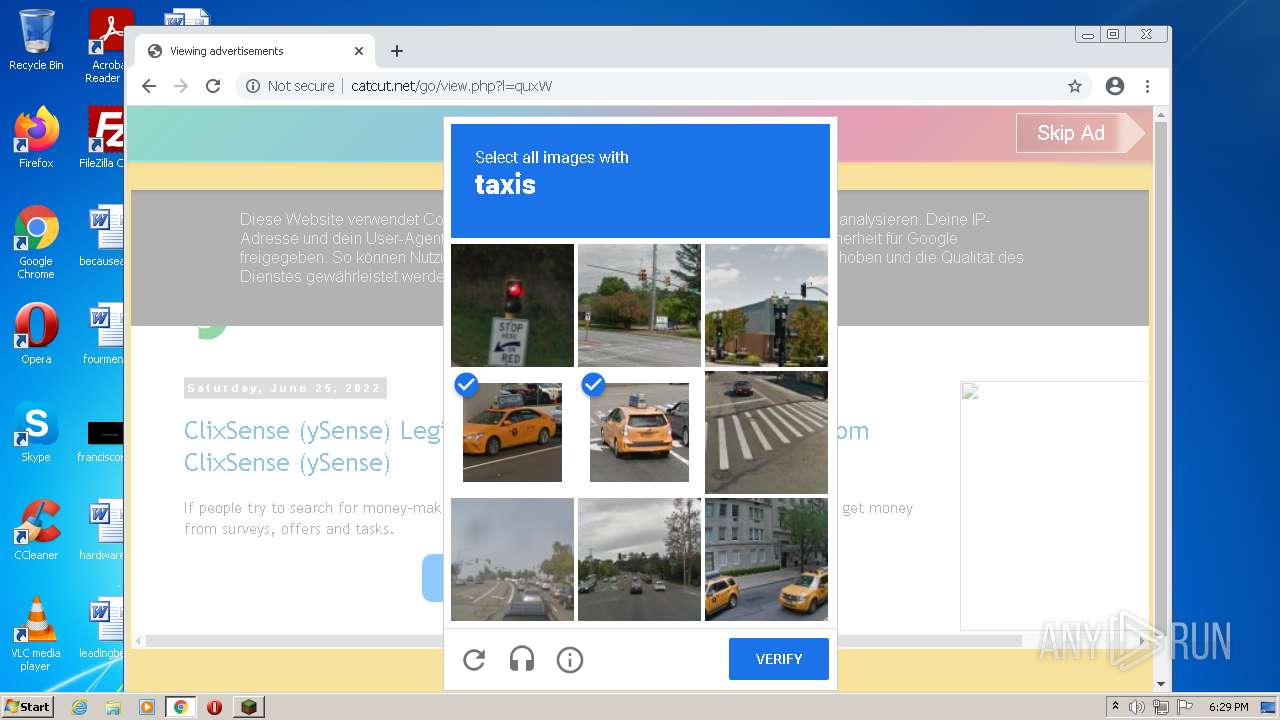
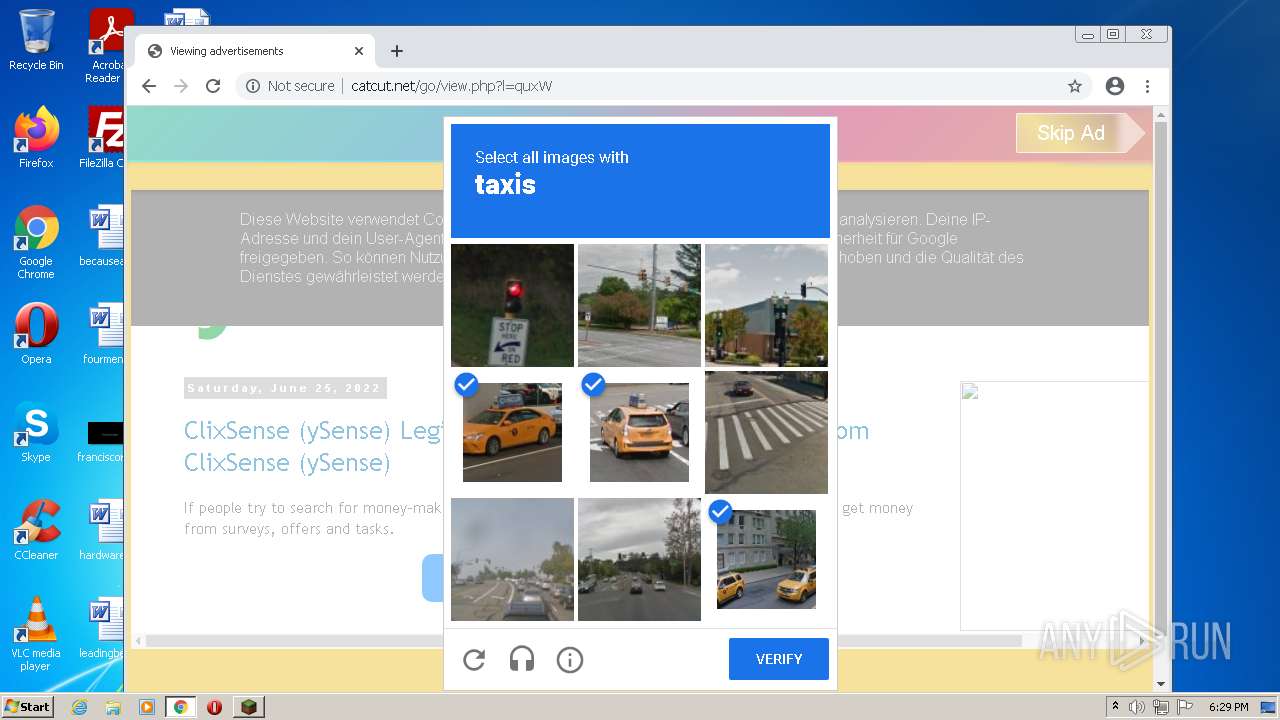
2352 | chrome.exe | GET | 200 | 79.132.136.12:80 | http://catcut.net/go/view.php?l=quxW | DE | html | 20.7 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2252 | java.exe | 151.236.71.1:443 | cdn.turikhay.ru | CDNvideo LLC | RU | suspicious |
2352 | chrome.exe | 142.250.186.164:443 | www.google.com | Google Inc. | US | whitelisted |
2352 | chrome.exe | 142.250.185.109:443 | accounts.google.com | Google Inc. | US | suspicious |
1568 | java.exe | 151.236.105.192:443 | cdn.turikhay.ru | Dataline Ltd | RU | unknown |
2352 | chrome.exe | 142.250.185.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1568 | java.exe | 51.38.188.198:443 | eu02-www.tlaun.ch | — | GB | unknown |
2252 | java.exe | 51.38.188.198:443 | eu02-www.tlaun.ch | — | GB | unknown |
2352 | chrome.exe | 34.104.35.123:80 | edgedl.me.gvt1.com | — | US | whitelisted |
2352 | chrome.exe | 142.250.185.97:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
2252 | java.exe | 159.223.209.252:443 | eu01-www.tlaun.ch | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cdn.turikhay.ru |
| suspicious |
www.google.com |
| malicious |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
eu02-www.tlaun.ch |
| unknown |
clients2.googleusercontent.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
eu02-www.tln4.ru |
| unknown |
eu02-www.4nlt.com |
| unknown |
tlaun.ch |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2352 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2352 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2352 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2352 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2352 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM CLOSEWAIT FIN out of window |