| File name: | epm_free_installer.589.exe |
| Full analysis: | https://app.any.run/tasks/19203130-87bb-4405-a7f5-bbb5f5ac3523 |
| Verdict: | Malicious activity |
| Analysis date: | May 30, 2024, 18:46:02 |
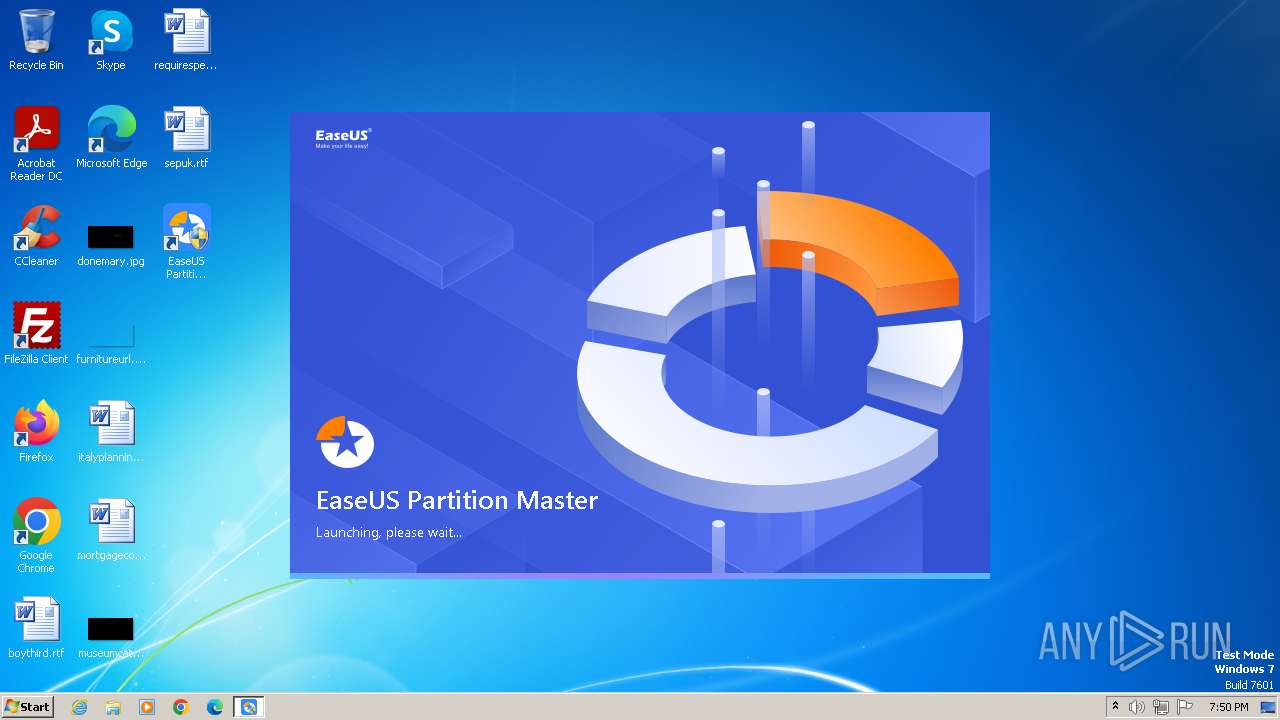
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | F83C51F3E6538A13DEF50E5F20985D29 |
| SHA1: | 921EB4B6CA6147D57B6443171AC7DCB5DBCE31D1 |
| SHA256: | B59A08D26DCF05DEC4FC5AAB69DA4F8F8C3D9F53A8942C5B4C0EF9999BC90211 |
| SSDEEP: | 98304:uxN5Qq0/DGZkAmpgXuC87YNsjyhiLp88E7tf2MCN/i5vsyPGVzj4i6xQPNqjR6R6:obIW+KD |
MALICIOUS
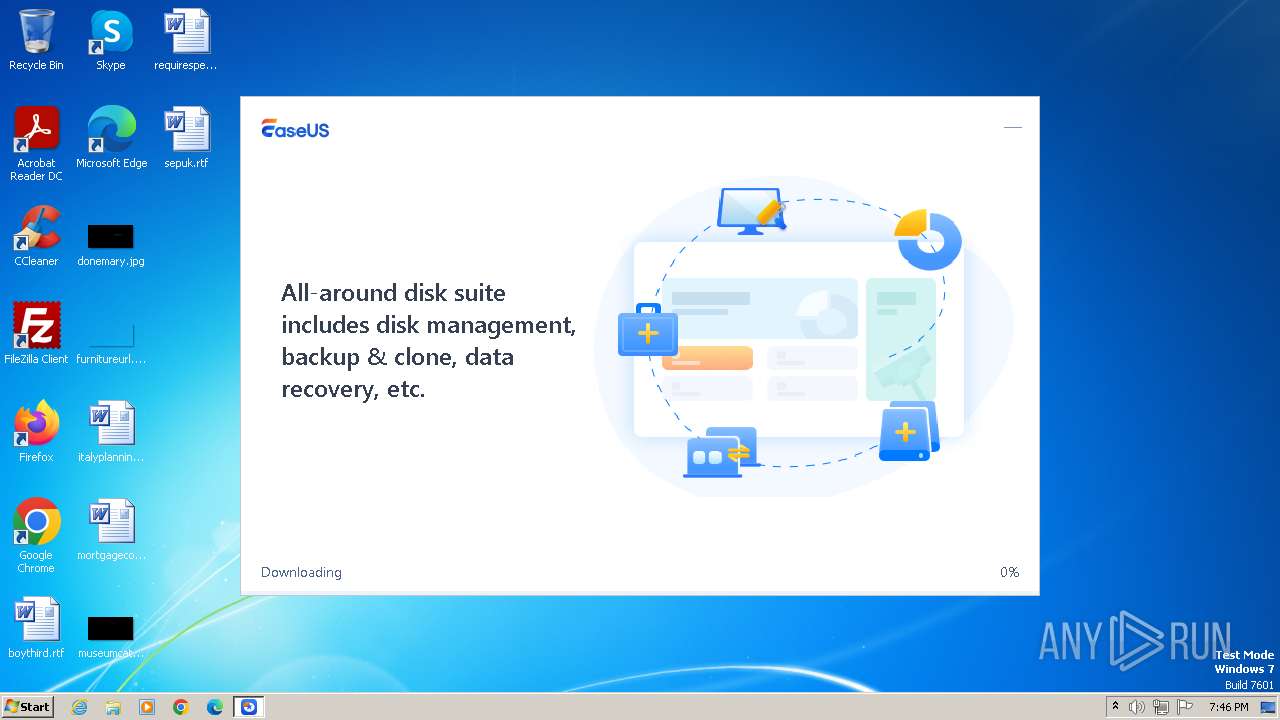
Drops the executable file immediately after the start
- epm_free_installer.589.exe (PID: 1200)
- epm_free_support_16.5.exe (PID: 736)
- DrvSetup.exe (PID: 3100)
- epm_free_support_16.5.tmp (PID: 568)
- EnsUtils.exe (PID: 3296)
Actions looks like stealing of personal data
- epm_free_support_16.5.tmp (PID: 568)
- EUCloneServer.exe (PID: 2012)
Creates a writable file in the system directory
- epm_free_support_16.5.tmp (PID: 568)
- msdtc.exe (PID: 1028)
- DrvSetup.exe (PID: 3100)
- AliyunWrapExe.Exe (PID: 3504)
- ensserver.exe (PID: 3848)
Starts NET.EXE for service management
- cmd.exe (PID: 2588)
- net.exe (PID: 2560)
- net.exe (PID: 1128)
- net.exe (PID: 2684)
Registers / Runs the DLL via REGSVR32.EXE
- cmd.exe (PID: 2588)
SUSPICIOUS
Executable content was dropped or overwritten
- epm_free_installer.589.exe (PID: 1200)
- epm_free_support_16.5.tmp (PID: 568)
- epm_free_support_16.5.exe (PID: 736)
- DrvSetup.exe (PID: 3100)
- EnsUtils.exe (PID: 3296)
Reads security settings of Internet Explorer
- AliyunWrapExe.Exe (PID: 2116)
- AliyunWrapExe.Exe (PID: 3272)
- ensserver.exe (PID: 3848)
- AliyunWrapExe.Exe (PID: 3504)
- AliyunWrapExe.Exe (PID: 3800)
- EDownloader.exe (PID: 820)
- epm_free_support_16.5.tmp (PID: 568)
Reads the Internet Settings
- AliyunWrapExe.Exe (PID: 2116)
- WMIC.exe (PID: 1652)
- AliyunWrapExe.Exe (PID: 3272)
- AliyunWrapExe.Exe (PID: 3800)
- epm_free_support_16.5.tmp (PID: 568)
- EDownloader.exe (PID: 820)
Reads the Windows owner or organization settings
- epm_free_support_16.5.tmp (PID: 568)
Process drops legitimate windows executable
- epm_free_support_16.5.tmp (PID: 568)
- EnsUtils.exe (PID: 3296)
The process drops C-runtime libraries
- epm_free_support_16.5.tmp (PID: 568)
- EnsUtils.exe (PID: 3296)
Drops a system driver (possible attempt to evade defenses)
- epm_free_support_16.5.tmp (PID: 568)
- DrvSetup.exe (PID: 3100)
Changes Internet Explorer settings (feature browser emulation)
- epm_free_support_16.5.tmp (PID: 568)
- EUinApp.exe (PID: 3756)
Creates files in the driver directory
- epm_free_support_16.5.tmp (PID: 568)
- DrvSetup.exe (PID: 3100)
Executing commands from ".cmd" file
- epm_free_support_16.5.tmp (PID: 568)
Process checks presence of unattended files
- epm_free_support_16.5.tmp (PID: 568)
Drops 7-zip archiver for unpacking
- epm_free_support_16.5.tmp (PID: 568)
Uses WMIC.EXE to obtain computer system information
- EDownloader.exe (PID: 820)
Starts CMD.EXE for commands execution
- epm_free_support_16.5.tmp (PID: 568)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 2588)
The process executes VB scripts
- cmd.exe (PID: 2588)
Executes as Windows Service
- dllhost.exe (PID: 2420)
- msdtc.exe (PID: 1028)
- ensserver.exe (PID: 3848)
- VSSVC.exe (PID: 2856)
- vds.exe (PID: 3212)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- cscript.exe (PID: 2848)
Executes WMI query (SCRIPT)
- cscript.exe (PID: 2848)
Creates or modifies Windows services
- DrvSetup.exe (PID: 3100)
- setupepmdrv.exe (PID: 3144)
Searches for installed software
- EDownloader.exe (PID: 820)
Checks Windows Trust Settings
- ensserver.exe (PID: 3848)
Detected use of alternative data streams (AltDS)
- EUCloneServer.exe (PID: 2012)
Creates file in the systems drive root
- EUCloneServer.exe (PID: 2012)
INFO
Checks supported languages
- epm_free_installer.589.exe (PID: 1200)
- EDownloader.exe (PID: 820)
- InfoForSetup.exe (PID: 752)
- AliyunWrapExe.Exe (PID: 2116)
- InfoForSetup.exe (PID: 124)
- InfoForSetup.exe (PID: 1060)
- wmpnscfg.exe (PID: 1236)
- InfoForSetup.exe (PID: 1800)
- epm_free_support_16.5.exe (PID: 736)
- InfoForSetup.exe (PID: 2272)
- InfoForSetup.exe (PID: 2236)
- InfoForSetup.exe (PID: 2260)
- epm_free_support_16.5.tmp (PID: 568)
- InfoForSetup.exe (PID: 1756)
- InfoForSetup.exe (PID: 1944)
- DrvSetup.exe (PID: 3100)
- EnsUtils.exe (PID: 3296)
- setupepmdrv.exe (PID: 3144)
- InfoForSetup.exe (PID: 3568)
- SetupUE.exe (PID: 3552)
- ensserver.exe (PID: 3848)
- InfoForSetup.exe (PID: 3864)
- AliyunWrapExe.Exe (PID: 3800)
- EUinApp.exe (PID: 3756)
- InfoForSetup.exe (PID: 1120)
- AliyunWrapExe.Exe (PID: 3272)
- AliyunWrapExe.Exe (PID: 3504)
- epm0.exe (PID: 308)
- InfoForSetup.exe (PID: 4040)
- InfoForSetup.exe (PID: 2040)
- EUCloneServer.exe (PID: 2012)
- EuDownload.exe (PID: 1604)
- EuDownload.exe (PID: 1236)
- wpn-grant.exe (PID: 2264)
- InfoForSetup.exe (PID: 3700)
- EuDownload.exe (PID: 3156)
- EuDownload.exe (PID: 1412)
- EuDownload.exe (PID: 2688)
- wpn.exe (PID: 1136)
- Main.exe (PID: 316)
Reads the computer name
- epm_free_installer.589.exe (PID: 1200)
- EDownloader.exe (PID: 820)
- AliyunWrapExe.Exe (PID: 2116)
- wmpnscfg.exe (PID: 1236)
- epm_free_support_16.5.tmp (PID: 568)
- DrvSetup.exe (PID: 3100)
- EnsUtils.exe (PID: 3296)
- AliyunWrapExe.Exe (PID: 3272)
- ensserver.exe (PID: 3848)
- AliyunWrapExe.Exe (PID: 3504)
- AliyunWrapExe.Exe (PID: 3800)
- setupepmdrv.exe (PID: 3144)
- Main.exe (PID: 316)
- EuDownload.exe (PID: 1236)
- EuDownload.exe (PID: 1604)
- EUCloneServer.exe (PID: 2012)
- wpn-grant.exe (PID: 2264)
- EuDownload.exe (PID: 3156)
- EuDownload.exe (PID: 1412)
- wpn.exe (PID: 1136)
- EuDownload.exe (PID: 2688)
Create files in a temporary directory
- epm_free_installer.589.exe (PID: 1200)
- EDownloader.exe (PID: 820)
- InfoForSetup.exe (PID: 124)
- AliyunWrapExe.Exe (PID: 2116)
- epm_free_support_16.5.exe (PID: 736)
- epm_free_support_16.5.tmp (PID: 568)
- Main.exe (PID: 316)
- EuDownload.exe (PID: 1604)
- EuDownload.exe (PID: 3156)
Checks proxy server information
- AliyunWrapExe.Exe (PID: 2116)
- AliyunWrapExe.Exe (PID: 3272)
- ensserver.exe (PID: 3848)
- AliyunWrapExe.Exe (PID: 3504)
- AliyunWrapExe.Exe (PID: 3800)
Creates files or folders in the user directory
- AliyunWrapExe.Exe (PID: 2116)
- epm_free_support_16.5.tmp (PID: 568)
- AliyunWrapExe.Exe (PID: 3272)
- AliyunWrapExe.Exe (PID: 3800)
Manual execution by a user
- wmpnscfg.exe (PID: 1236)
- msedge.exe (PID: 2336)
Creates files in the program directory
- epm_free_support_16.5.tmp (PID: 568)
- DrvSetup.exe (PID: 3100)
- EnsUtils.exe (PID: 3296)
- ensserver.exe (PID: 3848)
- AliyunWrapExe.Exe (PID: 3272)
- Main.exe (PID: 316)
- AliyunWrapExe.Exe (PID: 3504)
- AliyunWrapExe.Exe (PID: 3800)
- EUCloneServer.exe (PID: 2012)
- EuDownload.exe (PID: 1236)
- EuDownload.exe (PID: 1412)
- EuDownload.exe (PID: 2688)
Reads the machine GUID from the registry
- AliyunWrapExe.Exe (PID: 2116)
- AliyunWrapExe.Exe (PID: 3272)
- EnsUtils.exe (PID: 3296)
- ensserver.exe (PID: 3848)
- AliyunWrapExe.Exe (PID: 3504)
- AliyunWrapExe.Exe (PID: 3800)
- EuDownload.exe (PID: 1604)
- Main.exe (PID: 316)
- EuDownload.exe (PID: 1236)
- wpn-grant.exe (PID: 2264)
- EUCloneServer.exe (PID: 2012)
- EuDownload.exe (PID: 3156)
- EuDownload.exe (PID: 1412)
- wpn.exe (PID: 1136)
- EuDownload.exe (PID: 2688)
Creates a software uninstall entry
- epm_free_support_16.5.tmp (PID: 568)
Reads security settings of Internet Explorer
- cscript.exe (PID: 2372)
- cscript.exe (PID: 2848)
Checks transactions between databases Windows and Oracle
- dllhost.exe (PID: 2420)
- msdtc.exe (PID: 1028)
- cscript.exe (PID: 2848)
- cscript.exe (PID: 2372)
Reads the software policy settings
- ensserver.exe (PID: 3848)
Application launched itself
- msedge.exe (PID: 3764)
- msedge.exe (PID: 2336)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:01:30 03:57:48+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26624 |
| InitializedDataSize: | 186368 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x338f |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
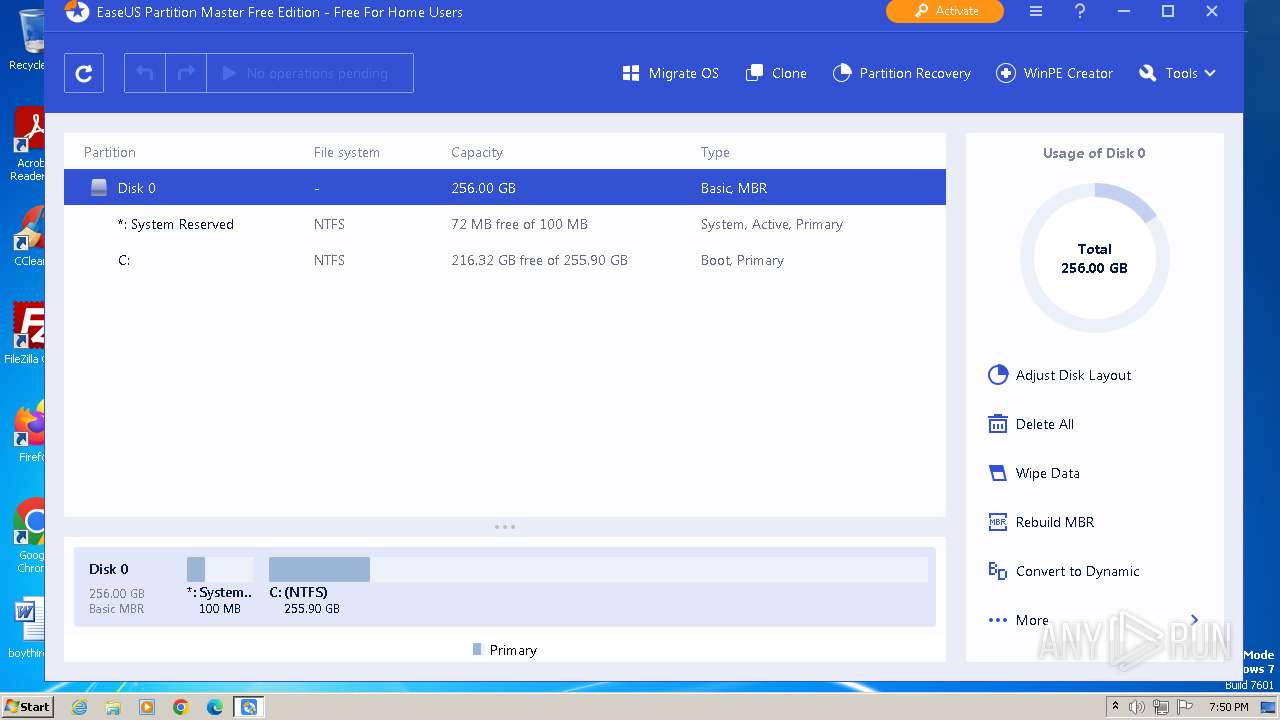
Total processes
134
Monitored processes
80
Malicious processes
12
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | /SendInfo Window "Web_Installer" Activity "Result_Run_Installer" Attribute "{\"Country\":\"United States\",\"Pageid\":\"589\",\"Timezone\":\"GMT-00:00\"}" | C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.2.0\5free\aliyun\InfoForSetup.exe | — | EDownloader.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 308 | "C:\Program Files\EaseUS\EaseUS Partition Master\bin\epm0.exe" | C:\Program Files\EaseUS\EaseUS Partition Master\bin\epm0.exe | — | EDownloader.exe | |||||||||||
User: admin Company: EaseUS Integrity Level: HIGH Description: EaseUS Partition Master Loader Application Version: 16.5.0.0 Modules
| |||||||||||||||
| 316 | Main.exe epm0 | C:\Program Files\EaseUS\EaseUS Partition Master\bin\Main.exe | epm0.exe | ||||||||||||
User: admin Company: EaseUS Integrity Level: HIGH Description: EaseUS Partition Master Version: 16.5.0.0 Modules
| |||||||||||||||
| 568 | "C:\Users\admin\AppData\Local\Temp\is-D9QF5.tmp\epm_free_support_16.5.tmp" /SL5="$4013A,54278452,159744,C:\Users\admin\AppData\Local\Temp\epm_free_support_16.5.exe" /verysilent /norestart /log Installer /DIR="C:\Program Files\EaseUS\EaseUS Partition Master" /LANG=English agreeImprove=true GUID=S-1-5-21-1302019708-1500728564-335382590-1000 xurlID=589 | C:\Users\admin\AppData\Local\Temp\is-D9QF5.tmp\epm_free_support_16.5.tmp | epm_free_support_16.5.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 736 | /verysilent /norestart /log Installer /DIR="C:\Program Files\EaseUS\EaseUS Partition Master" /LANG=English agreeImprove=true GUID=S-1-5-21-1302019708-1500728564-335382590-1000 xurlID=589 | C:\Users\admin\AppData\Local\Temp\epm_free_support_16.5.exe | EDownloader.exe | ||||||||||||
User: admin Company: EaseUS Integrity Level: HIGH Description: EaseUS Partition Master Setup Exit code: 0 Version: 16.5 Modules
| |||||||||||||||
| 752 | /Uid "S-1-5-21-1302019708-1500728564-335382590-1000" | C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.2.0\5free\aliyun\InfoForSetup.exe | — | EDownloader.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 752 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=109.0.5414.149 "--annotation=exe=C:\Program Files\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win32 "--annotation=prod=Microsoft Edge" --annotation=ver=109.0.1518.115 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd8,0x6b56f598,0x6b56f5a8,0x6b56f5b4 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 820 | "C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.2.0\5free\EDownloader.exe" EXEDIR=C:\Users\admin\AppData\Local\Temp ||| EXENAME=epm_free_installer.589.exe ||| DOWNLOAD_VERSION=free ||| PRODUCT_VERSION=2.2.0 ||| INSTALL_TYPE=0 | C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.2.0\5free\EDownloader.exe | epm_free_installer.589.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 936 | C:\Windows\system32\net1 stop vds /Y | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1028 | C:\Windows\System32\msdtc.exe | C:\Windows\System32\msdtc.exe | — | services.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Distributed Transaction Coordinator Service Version: 2001.12.8530.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
29 764
Read events
29 435
Write events
260
Delete events
69
Modification events
| (PID) Process: | (2116) AliyunWrapExe.Exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2116) AliyunWrapExe.Exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2116) AliyunWrapExe.Exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2116) AliyunWrapExe.Exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2116) AliyunWrapExe.Exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2116) AliyunWrapExe.Exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyServer |
Value: | |||
| (PID) Process: | (2116) AliyunWrapExe.Exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyOverride |
Value: | |||
| (PID) Process: | (2116) AliyunWrapExe.Exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoConfigURL |
Value: | |||
| (PID) Process: | (2116) AliyunWrapExe.Exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoDetect |
Value: | |||
| (PID) Process: | (2116) AliyunWrapExe.Exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000005D010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
1 264
Suspicious files
279
Text files
2 278
Unknown types
50
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1200 | epm_free_installer.589.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.2.0\5free\Arabic.ini | text | |
MD5:CBA453F3F4672B54B745DA028B8BF7FA | SHA256:391B8404A5EE90BA3B2C8D4A727B2C9A48A2C9979B895DAB3FE34FF38AF971EB | |||
| 1200 | epm_free_installer.589.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.2.0\5free\Korean.ini | text | |
MD5:C31EC7D64ED0D7B5D596765D597D9F60 | SHA256:E60A751965B230B154FF5B8F6D52E83FFB5443228DFFD55A11DE63936F840EDB | |||
| 1200 | epm_free_installer.589.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.2.0\5free\ChineseTrad.ini | text | |
MD5:802704E820D35785E4CFBE3DD78AE935 | SHA256:DADBC522D6B9C5F9CD25EF32DE2368B6AD35D7E386279B97B9D86BE31B0E7C7A | |||
| 1200 | epm_free_installer.589.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.2.0\5free\InitConfigure.ini | text | |
MD5:0DF699B43B77ADF78A2B817FE02A40CD | SHA256:471A797282CB28BC85F7DC870E5C38307E651844A9F45C4A70DC8BA91919B09A | |||
| 1200 | epm_free_installer.589.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.2.0\5free\InitConfigure_epms.ini | text | |
MD5:398367EFD0613214E3AE77B113EA9D2B | SHA256:C44D56BFD888832B610677426C78211D2811FE3F74FBB4E3E5846DC54EA85B8D | |||
| 1200 | epm_free_installer.589.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.2.0\5free\Japanese.ini | text | |
MD5:1AE5200C2D4E9B39B3390755AEE79E65 | SHA256:4B205FFA191985B93FCE1FDBD964B80459C15C8583AB9B6B4CC8DA8F8F383E65 | |||
| 1200 | epm_free_installer.589.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.2.0\5free\Polish.ini | text | |
MD5:29C977ED855B81F3DAAE700A6754256E | SHA256:9580D1997156ED7584056C53C74FAD54EA8C380856E246CC62C6BA216425D6E6 | |||
| 1200 | epm_free_installer.589.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.2.0\5free\German.ini | text | |
MD5:8D6F85CB9F0F086CE034A1537485483B | SHA256:2210C166999E5766F2D6BBC1F4817A141549D413E5185BD496AEA37031F9F3C0 | |||
| 1200 | epm_free_installer.589.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.2.0\5free\english.ini | text | |
MD5:58121C4A20989A3BF11109405DE2BC89 | SHA256:045F4B07726466541C1007B424E26BB6CE7A994F420E311310B5E4FFE40D26F0 | |||
| 1200 | epm_free_installer.589.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.2.0\5free\Thai.ini | text | |
MD5:8F6B3AA0130153787409FB1231D135C6 | SHA256:A71F2489C40F3E7CF4A0D4914EED54A50BBA27ED871409C319BFAC7B7ACC239B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
42
TCP/UDP connections
115
DNS requests
54
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2116 | AliyunWrapExe.Exe | GET | 200 | 163.171.156.15:80 | http://track.easeus.com/product/index.php?c=main&a=getstatus&pid=19 | unknown | — | — | unknown |
2116 | AliyunWrapExe.Exe | POST | 200 | 47.252.97.13:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_epm_downloader/shards/lb | unknown | — | — | unknown |
820 | EDownloader.exe | POST | 200 | 18.172.112.107:80 | http://download.easeus.com/api2/index.php/Apicp/Drwdl202004/index/ | unknown | — | — | unknown |
2116 | AliyunWrapExe.Exe | POST | 200 | 47.252.97.13:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_epm_downloader/shards/lb | unknown | — | — | unknown |
— | — | POST | 200 | 47.252.97.13:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_epm_downloader/shards/lb | unknown | — | — | unknown |
2116 | AliyunWrapExe.Exe | POST | 200 | 47.252.97.13:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_epm_downloader/shards/lb | unknown | — | — | unknown |
2116 | AliyunWrapExe.Exe | POST | 200 | 47.252.97.13:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_epm_downloader/shards/lb | unknown | — | — | unknown |
2116 | AliyunWrapExe.Exe | POST | 200 | 47.252.97.13:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_epm_downloader/shards/lb | unknown | — | — | unknown |
3800 | AliyunWrapExe.Exe | GET | 200 | 163.171.156.15:80 | http://track.easeus.com/product/index.php?c=main&a=getstatus&pid=0 | unknown | — | — | unknown |
3272 | AliyunWrapExe.Exe | POST | 200 | 47.252.97.8:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_ens_ip/shards/lb | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
820 | EDownloader.exe | 18.172.112.107:80 | download.easeus.com | — | US | unknown |
2116 | AliyunWrapExe.Exe | 163.171.156.15:80 | track.easeus.com | QUANTILNETWORKS | DE | unknown |
2116 | AliyunWrapExe.Exe | 47.252.97.13:80 | easeusinfo.us-east-1.log.aliyuncs.com | Alibaba US Technology Co., Ltd. | US | unknown |
820 | EDownloader.exe | 18.66.112.125:443 | d1.easeus.com | AMAZON-02 | US | unknown |
3272 | AliyunWrapExe.Exe | 163.171.156.15:80 | track.easeus.com | QUANTILNETWORKS | DE | unknown |
3504 | AliyunWrapExe.Exe | 163.171.156.15:80 | track.easeus.com | QUANTILNETWORKS | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.easeus.com |
| unknown |
track.easeus.com |
| unknown |
easeusinfo.us-east-1.log.aliyuncs.com |
| unknown |
d1.easeus.com |
| unknown |
update.easeus.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| shared |
android.clients.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1088 | svchost.exe | Misc activity | ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com) |
Process | Message |
|---|---|
EDownloader.exe | [864]-19:46:14:079 ParseCmdLine param=EXEDIR=C:\Users\admin\AppData\Local\Temp ||| EXENAME=epm_free_installer.589.exe ||| DOWNLOAD_VERSION=free ||| PRODUCT_VERSION=2.2.0 ||| INSTALL_TYPE=0
|
EDownloader.exe | [864]-19:46:14:079 CTools::loadIni configPath=C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.2.0\5free\InitConfigure.ini
|
EDownloader.exe | [2040]-19:46:14:469 Json parse Data Start
|
EDownloader.exe | [2040]-19:46:14:469 PostData Start download url=http://download.easeus.com/api2/index.php/Apicp/Drwdl202004/index/?exeNumber=589&lang=English&pcVersion=home&pid=5&tid=1&version=free
|
EDownloader.exe | [2040]-19:46:14:469 Json url: http://download.easeus.com/api2/index.php/Apicp/Drwdl202004/index/?exeNumber=589&lang=English&pcVersion=home&pid=5&tid=1&version=free
|
EDownloader.exe | [2040]-19:46:15:829 StartPost Error parse tuijian
|
EDownloader.exe | [2040]-19:46:15:829 Json response: {"check":1,"msg":"\u6210\u529f","data":{"pid":"5","download":"https:\/\/d1.easeus.com\/epm\/free\/epm18.5_free.exe","download2":"https:\/\/d2.easeus.com\/epm\/free\/epm18.5_free.exe","download3":"https:\/\/d3.easeus.com\/epm\/free\/epm18.5_free.exe","version":"free","curNum":"18.5","testid":"","url":["https:\/\/d1.easeus.com\/epm\/free\/epm_free_support_16.5.exe"],"md5":"052A86B300616D09DCB41BE5CA52A517","tj_download":"test","referNumber":"1000000","killSwitch":"true","WriteLogSwitch":"false","configid":""},"time":1717094775}
|
EDownloader.exe | [864]-19:46:15:829 CHttpHelper::GetDownloadInfo 56 download info code:0
|
EDownloader.exe | [2040]-19:46:15:829 PostData end
|
EDownloader.exe | [2040]-19:46:15:829 Json parse Data end(code=0)
|