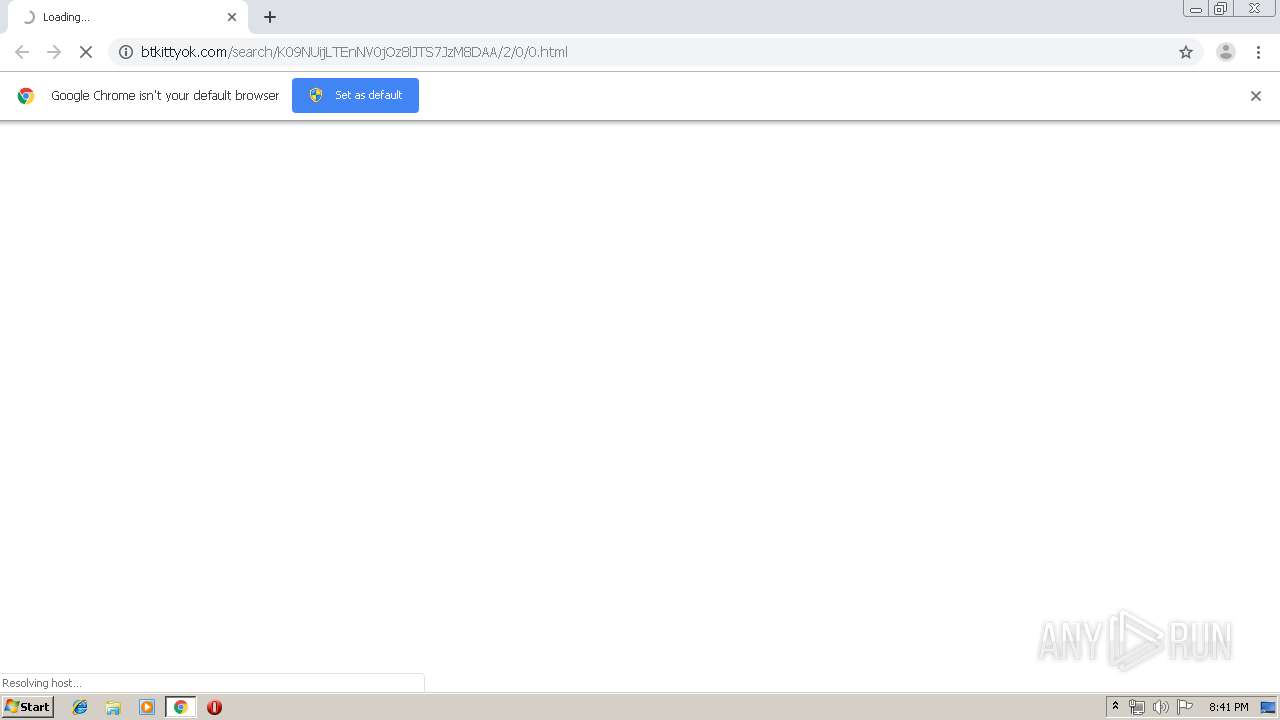
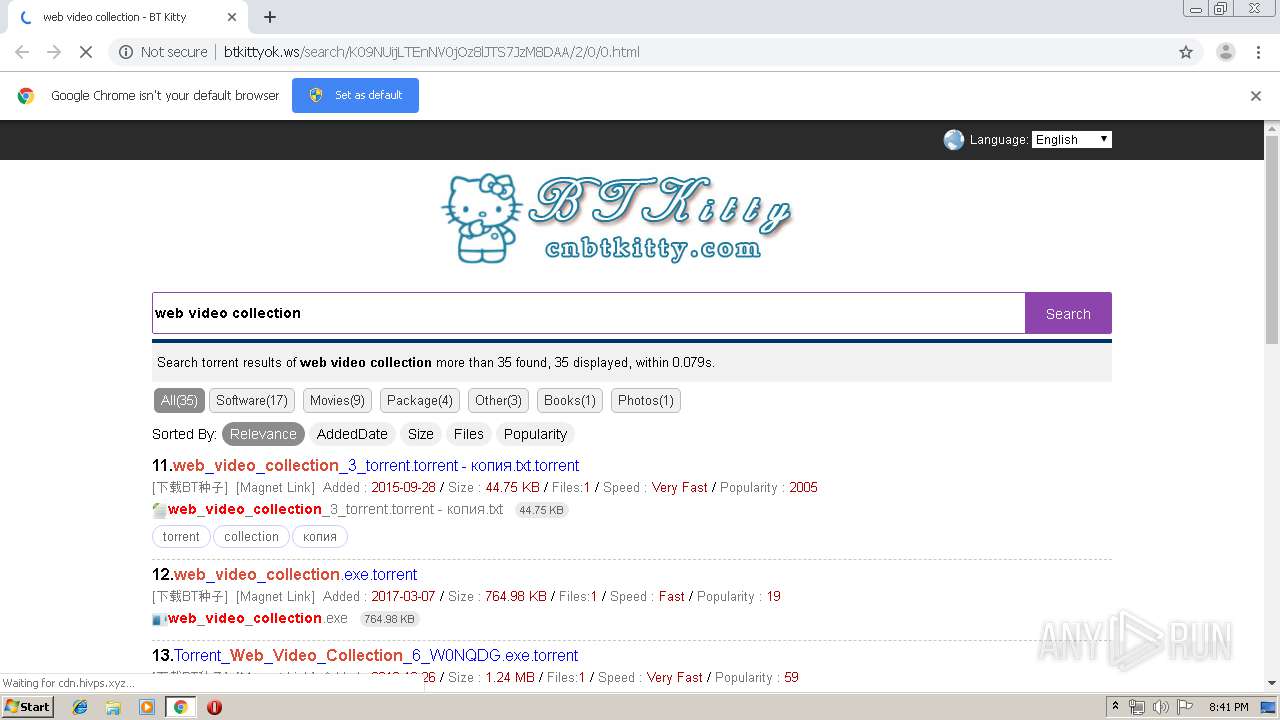
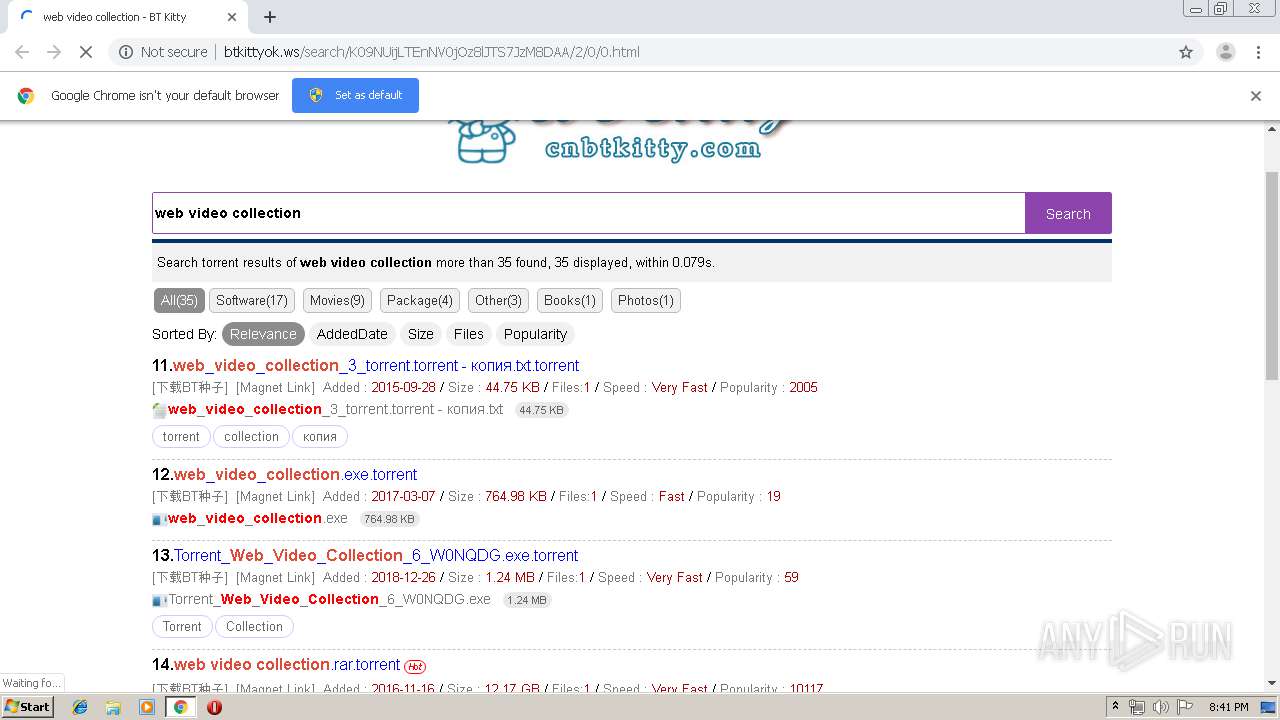
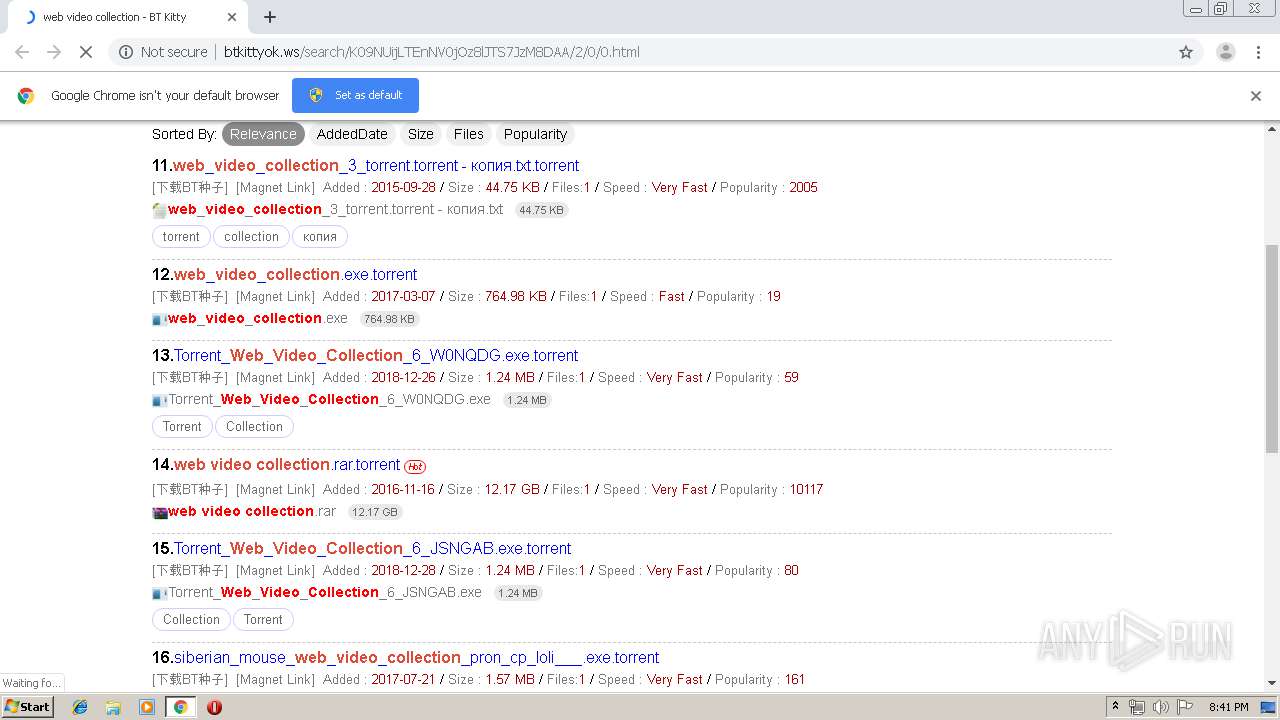
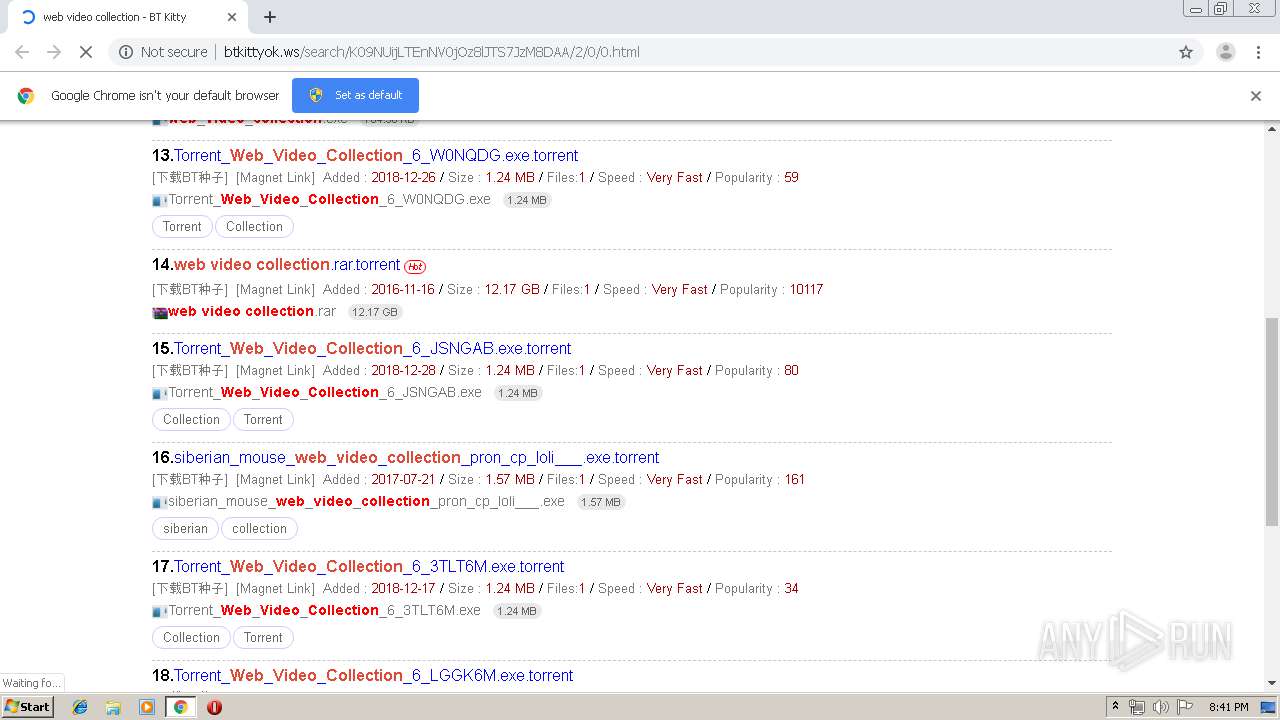
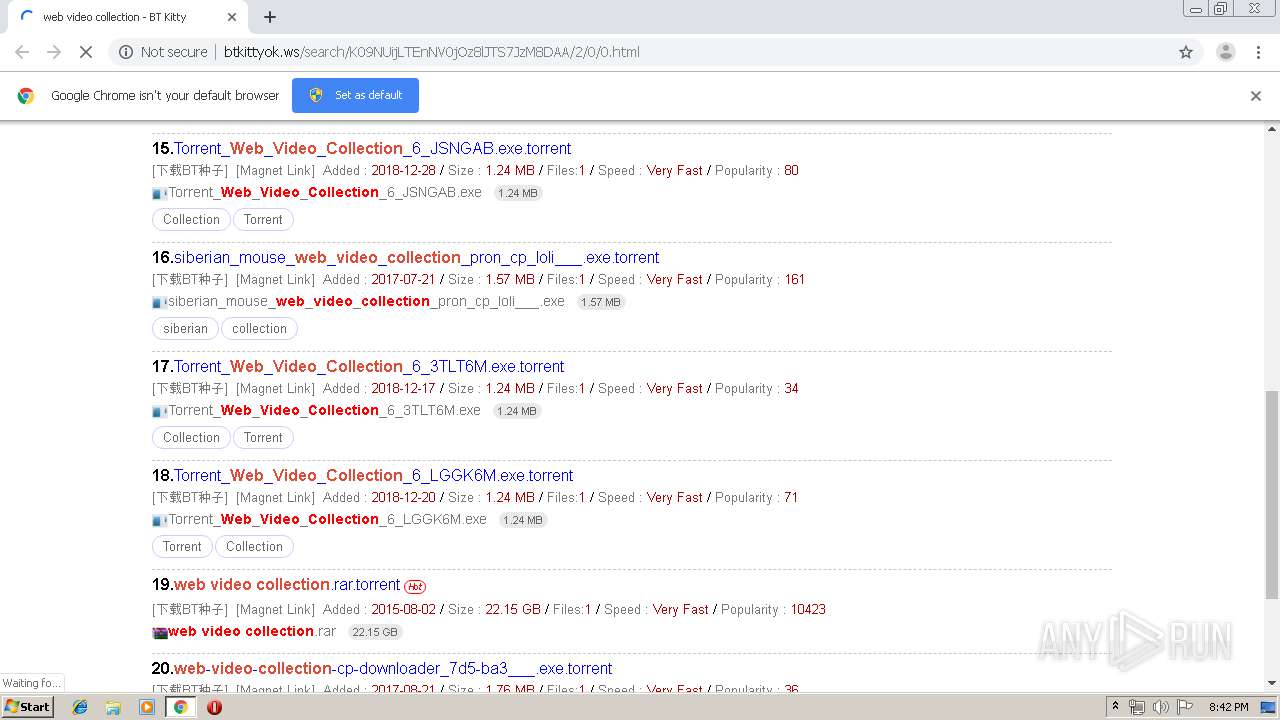
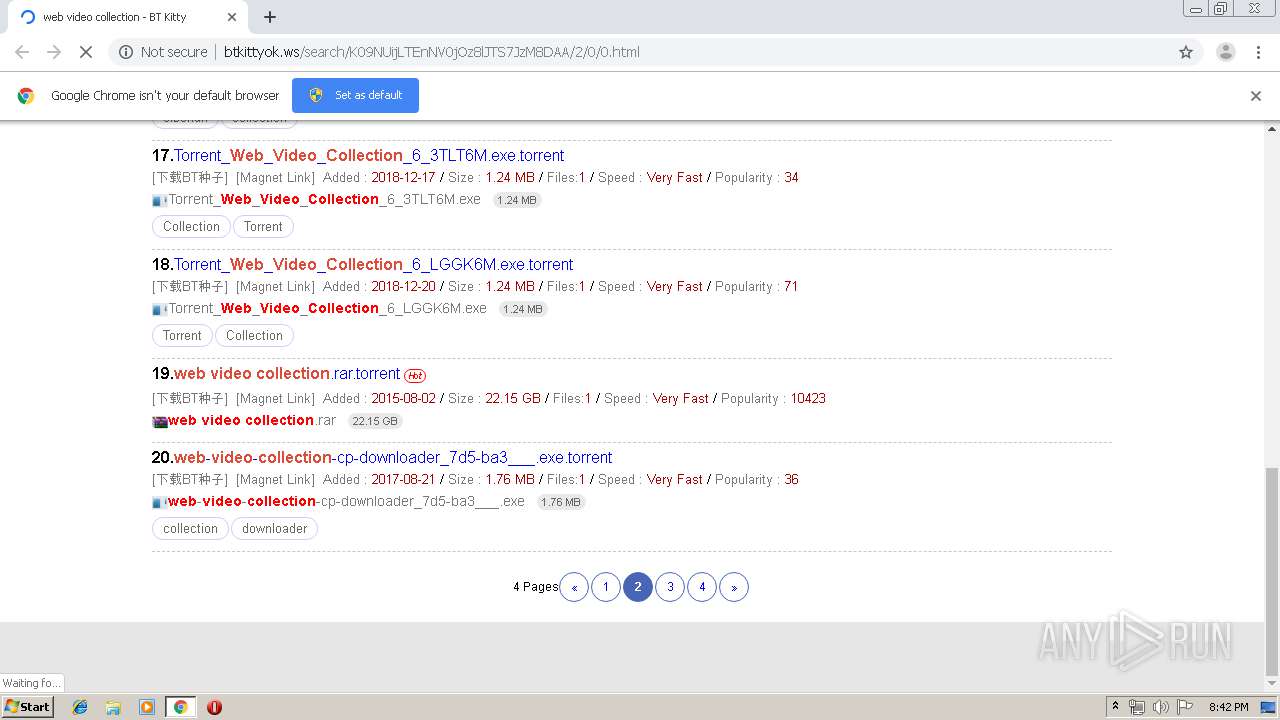
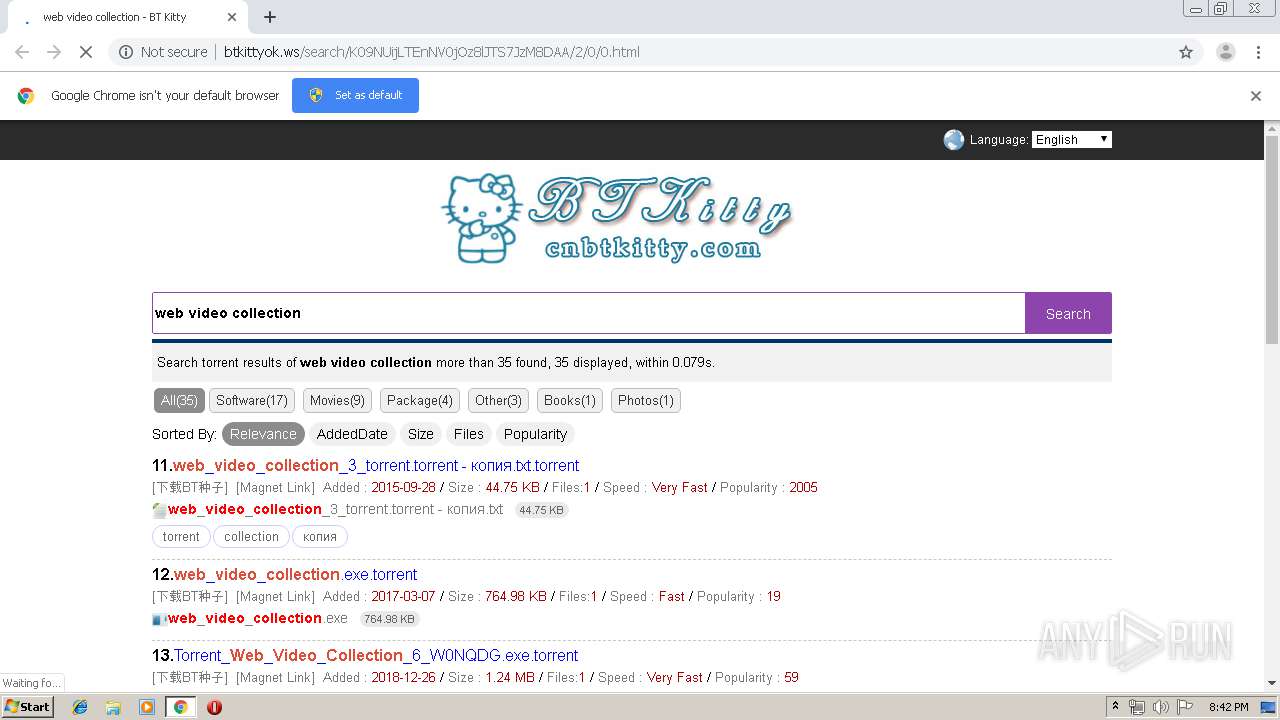
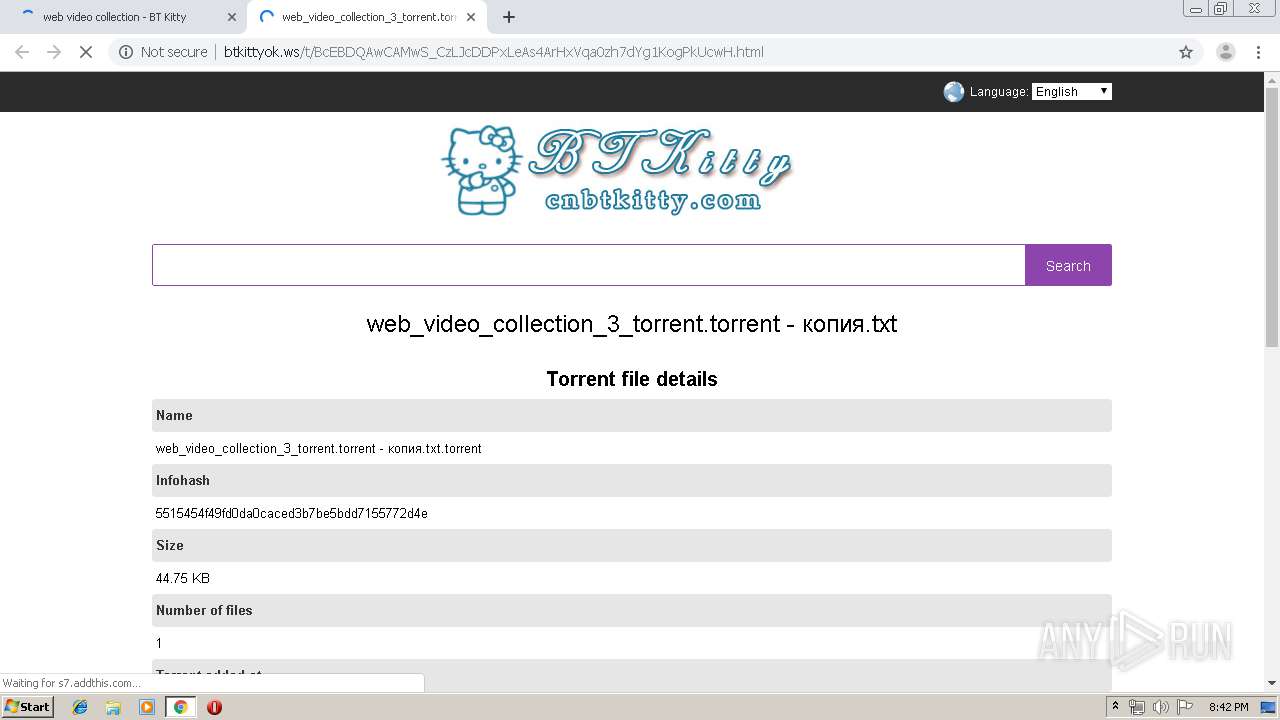
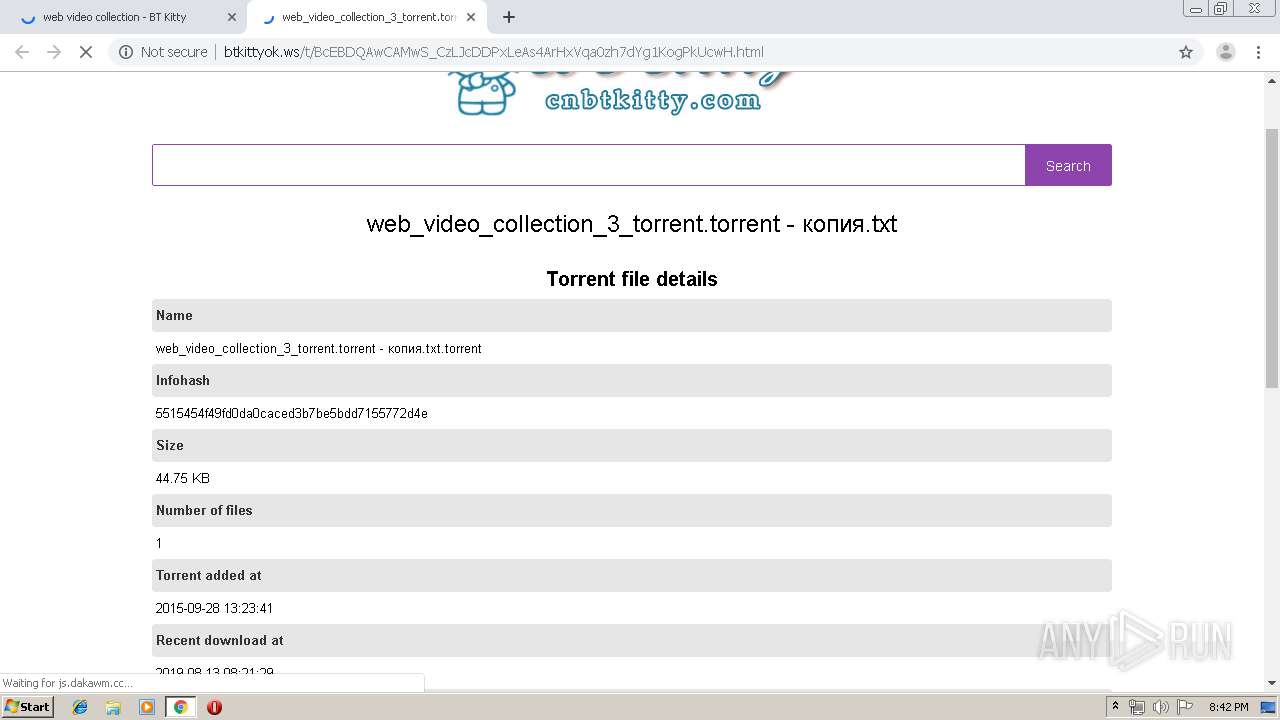
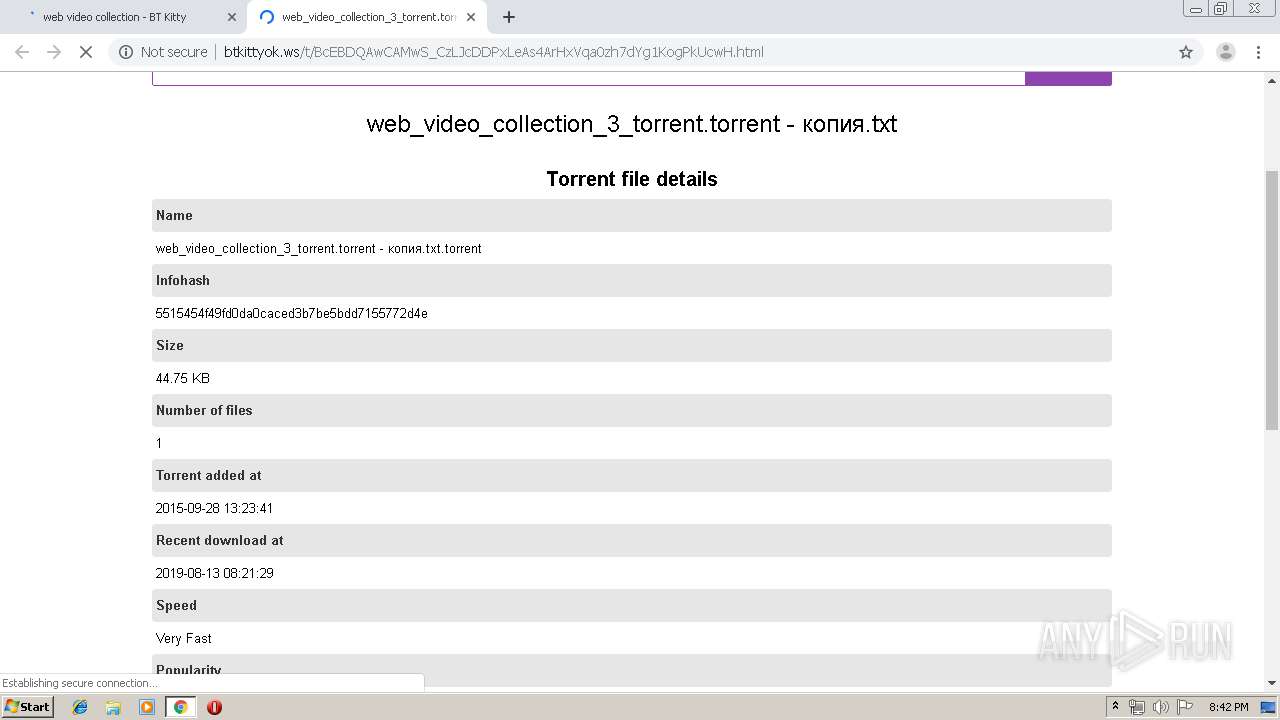
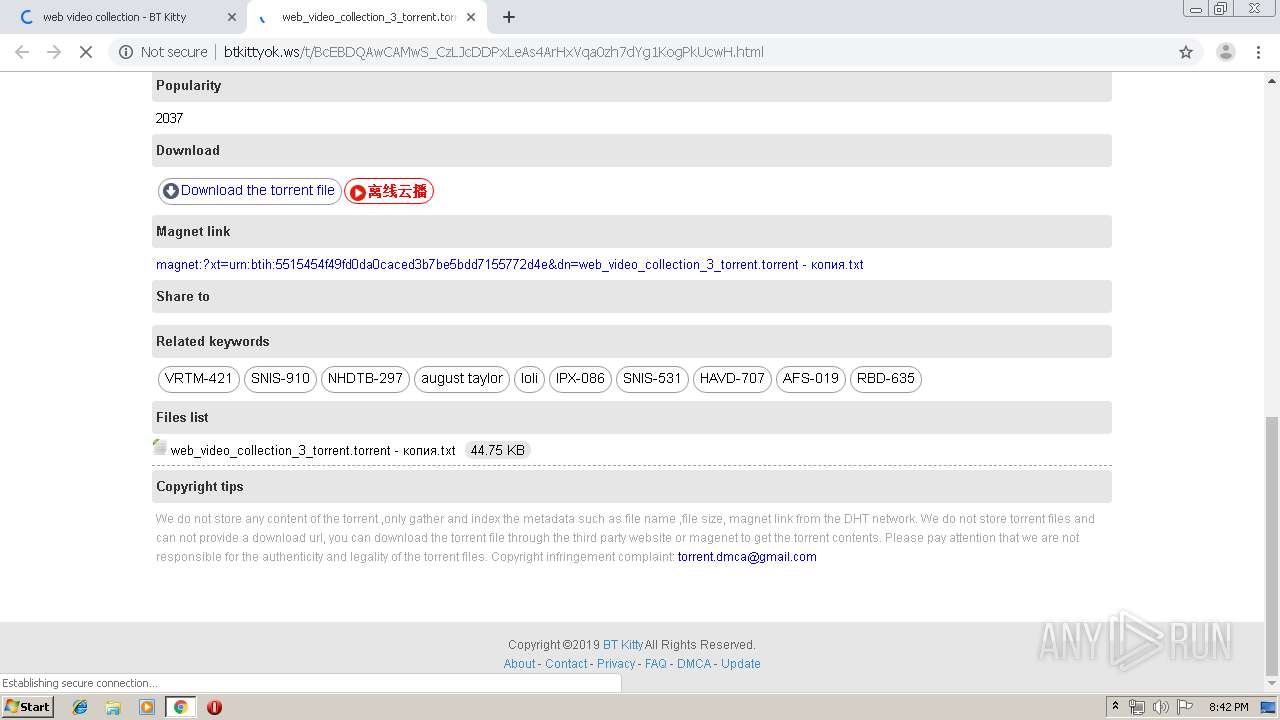
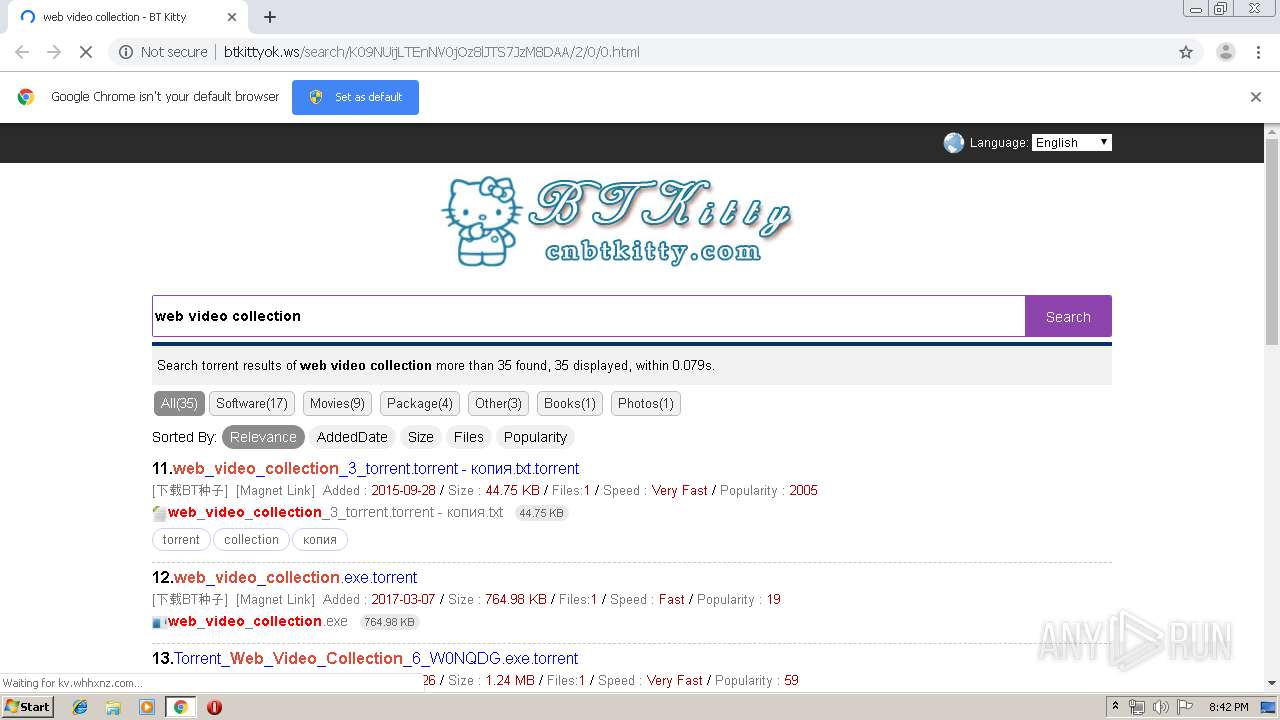
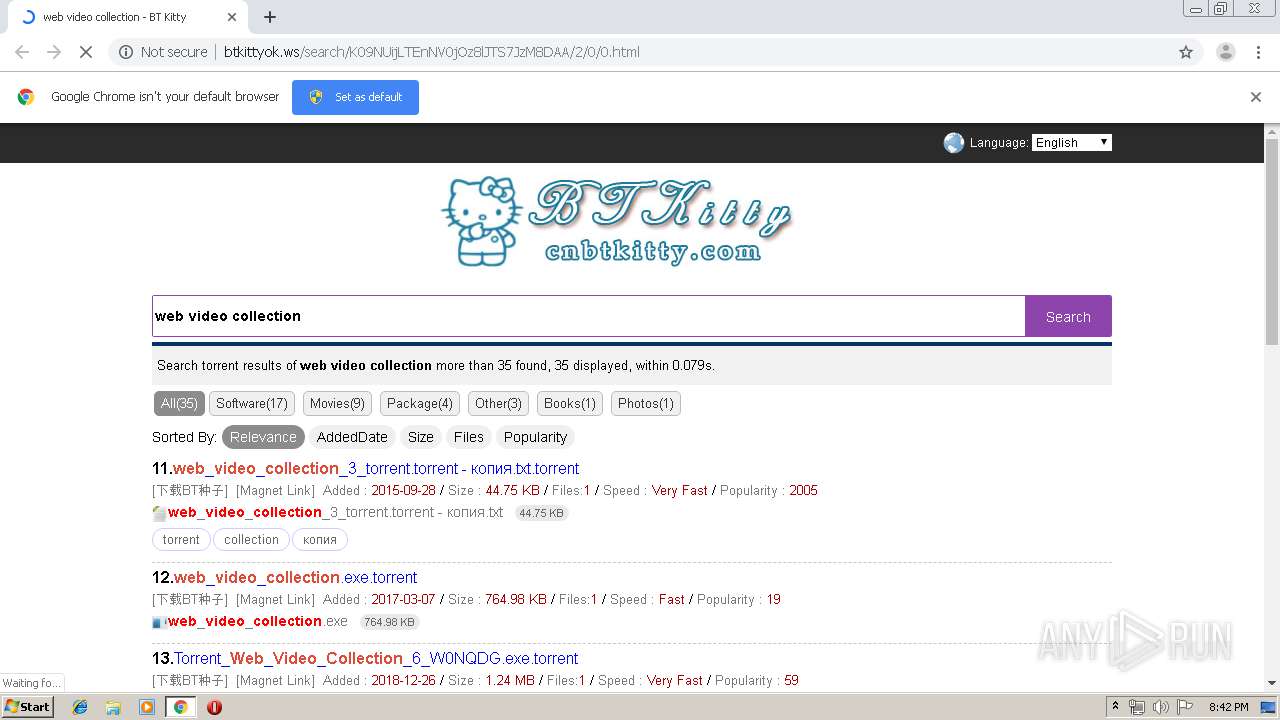
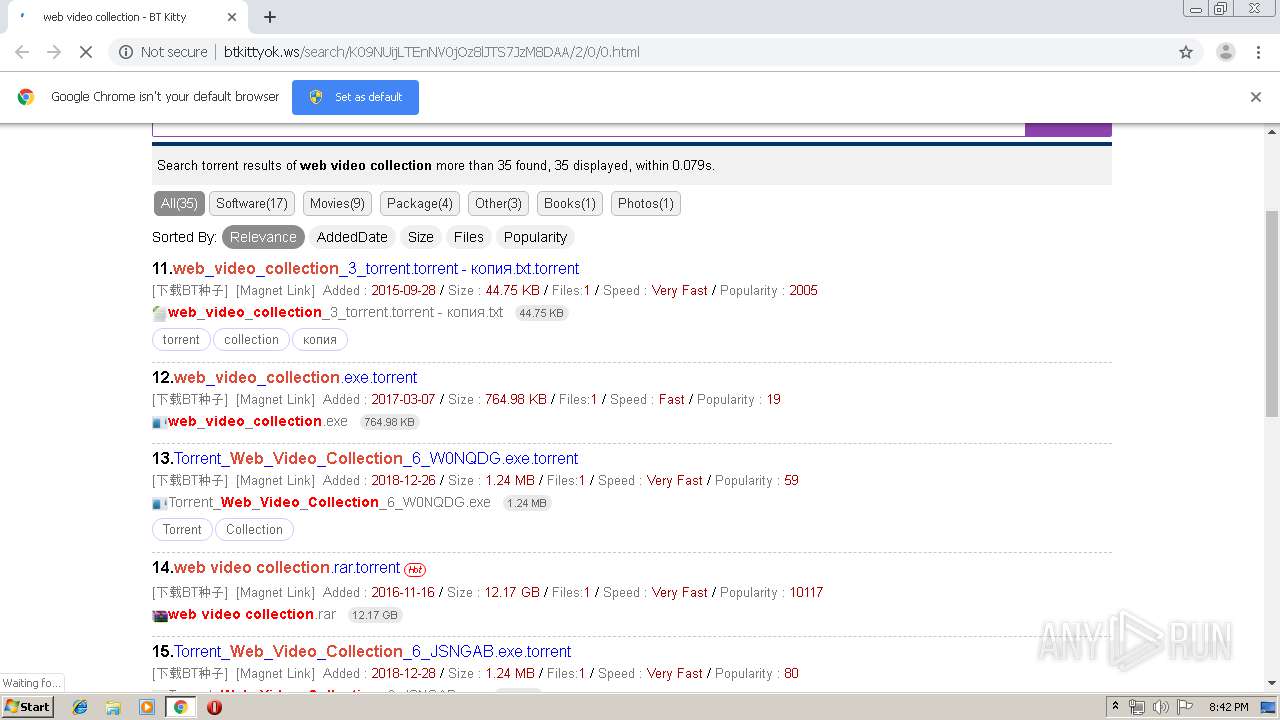
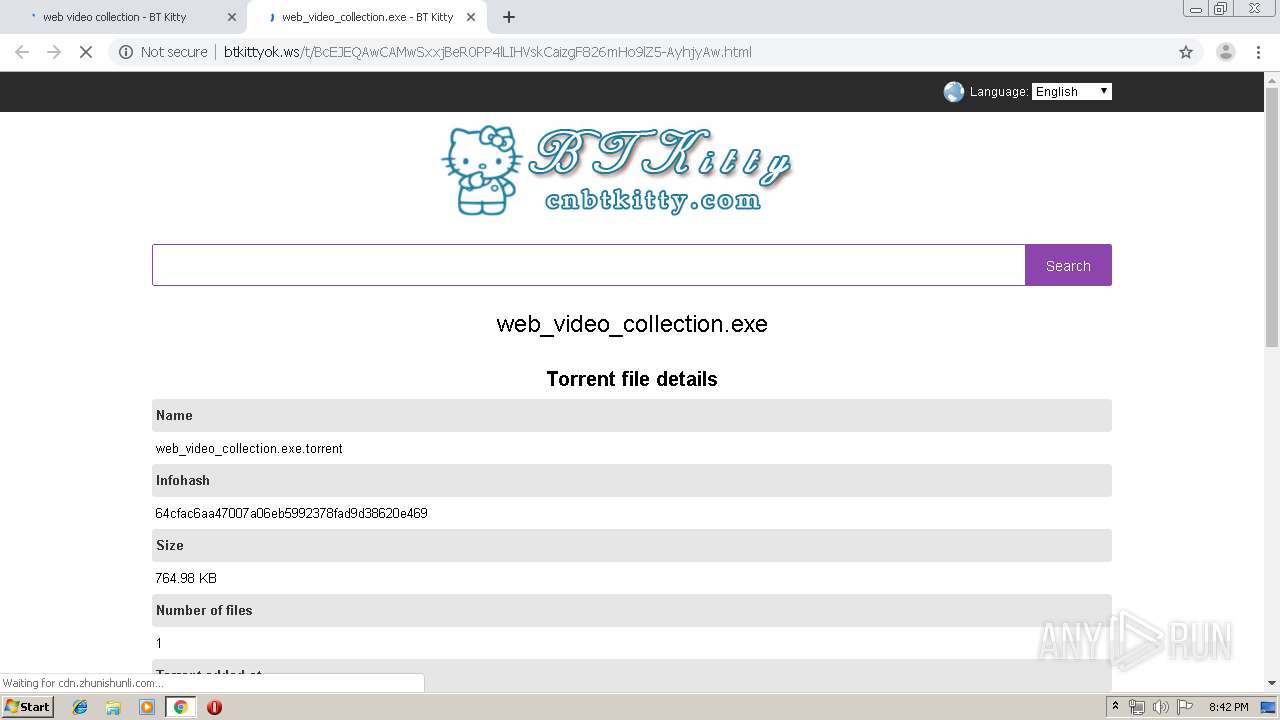
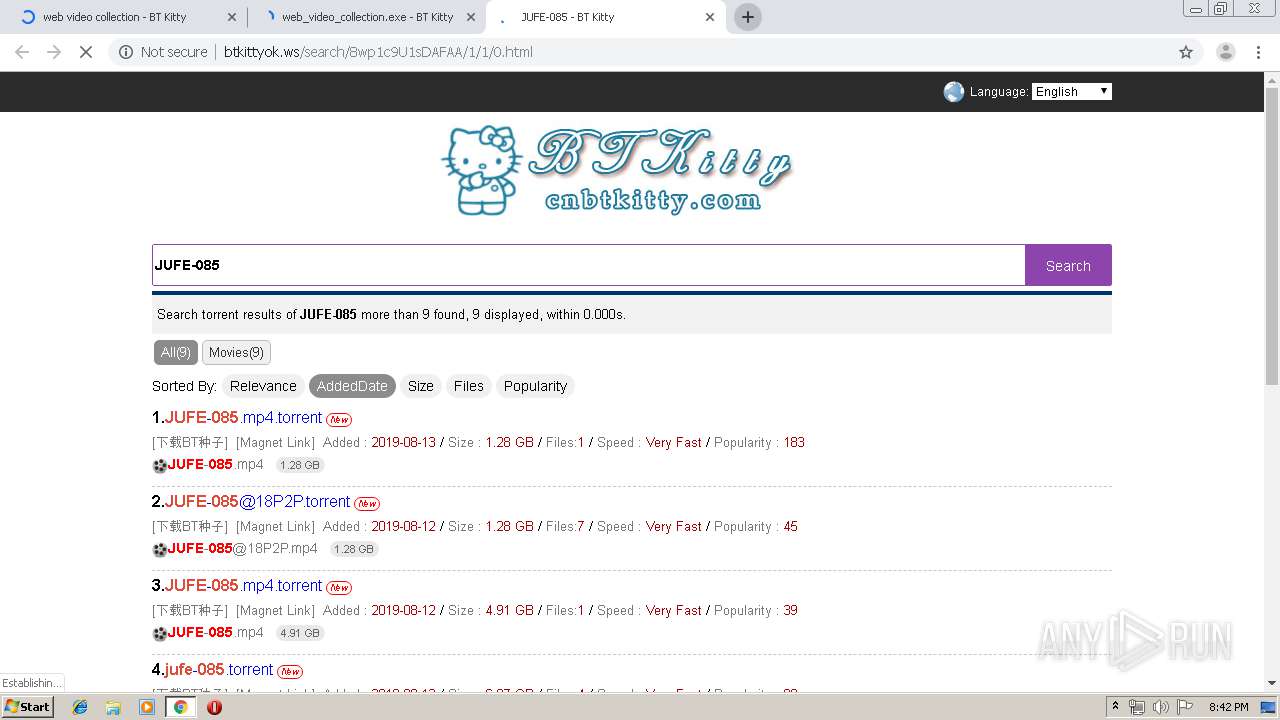
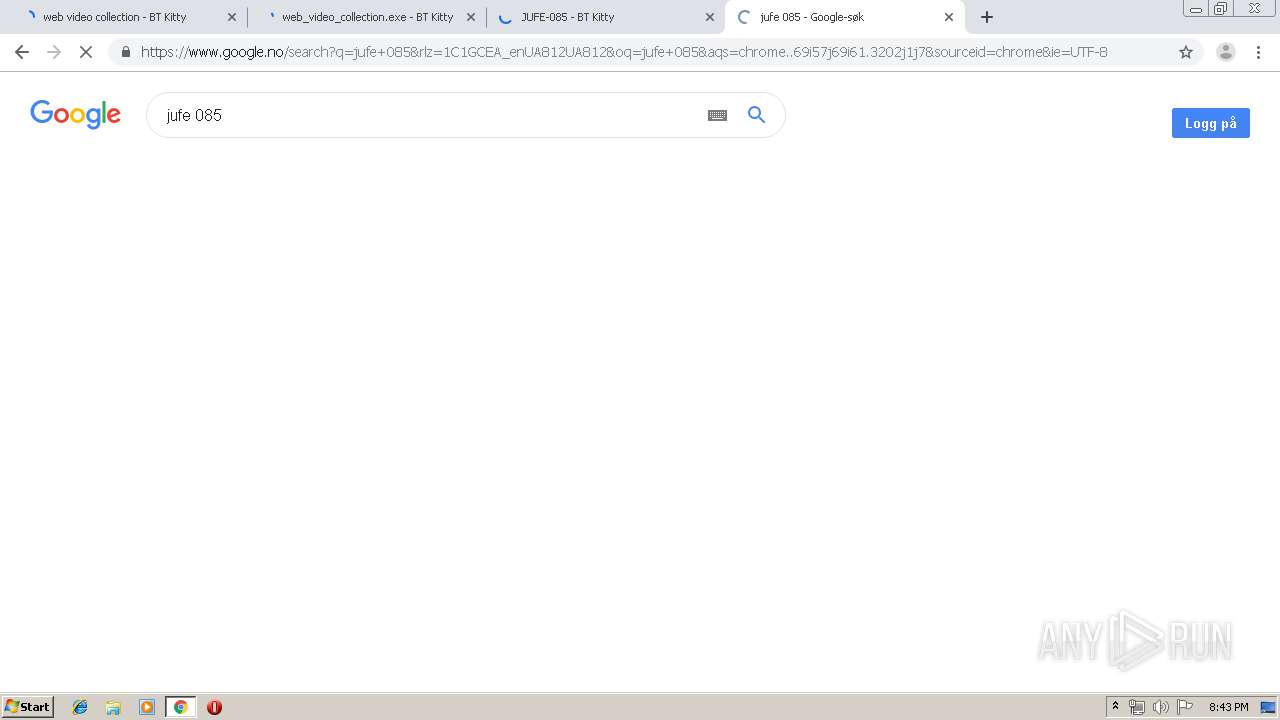
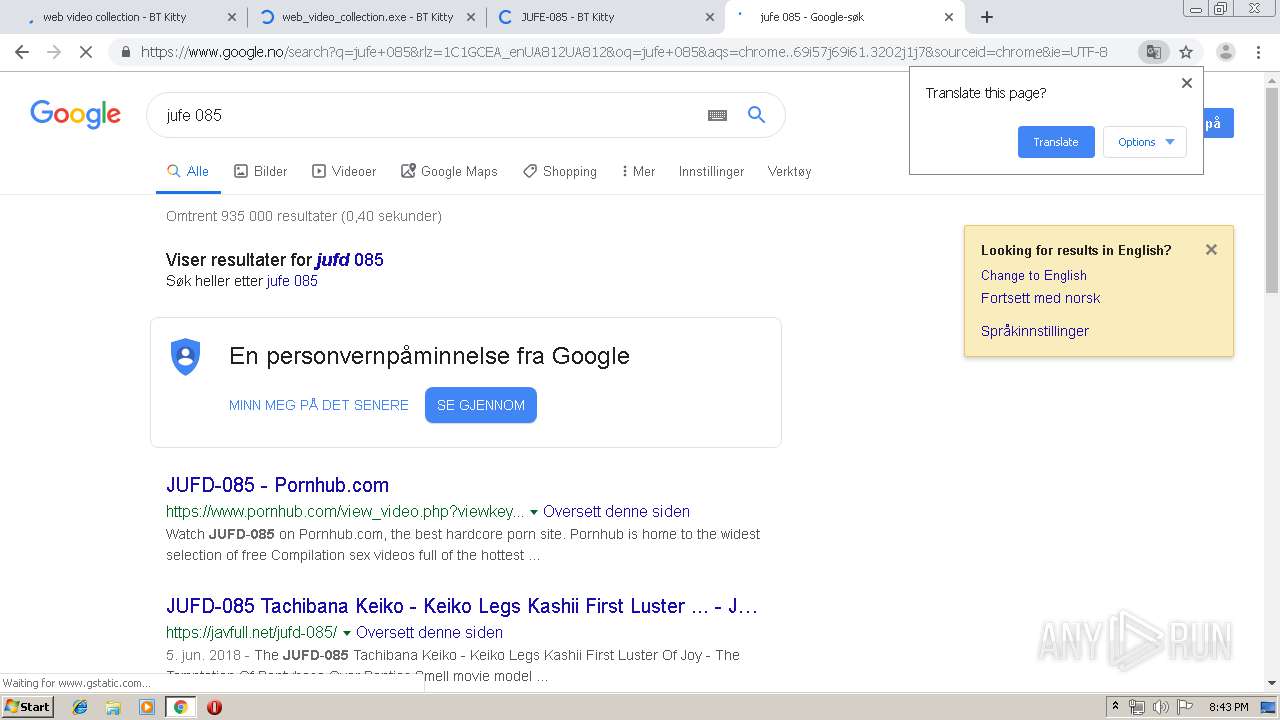
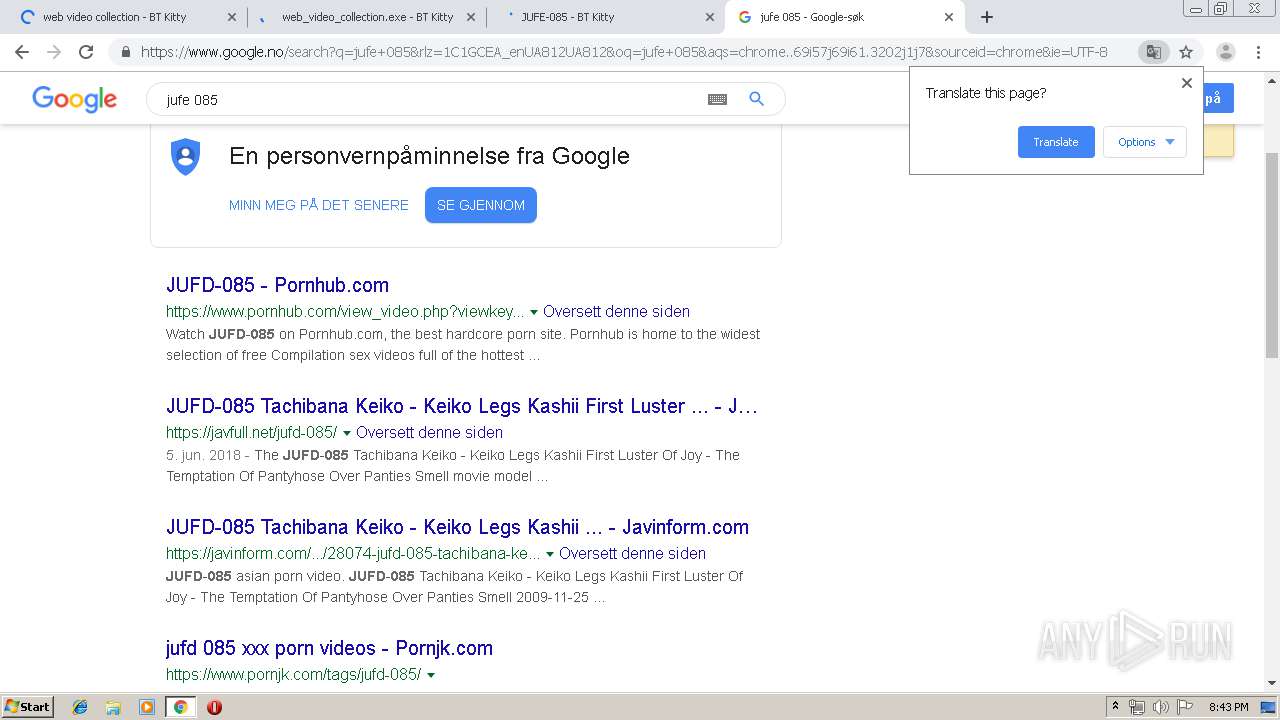
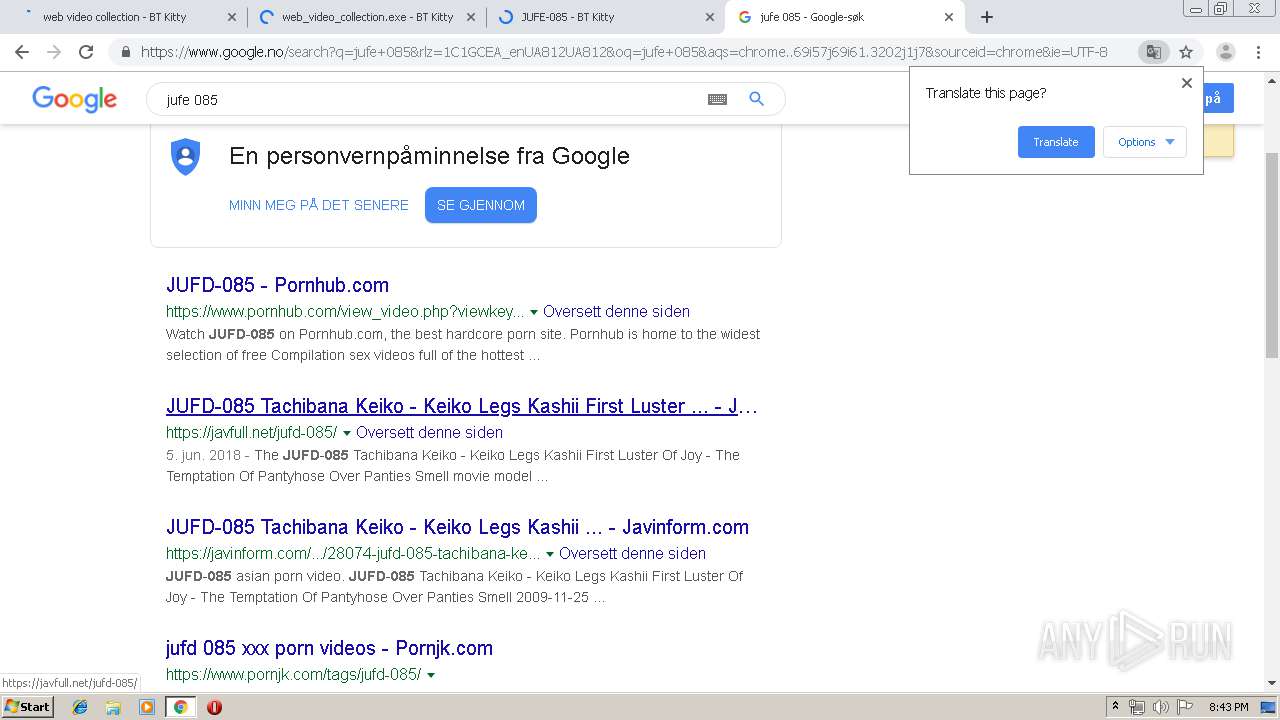
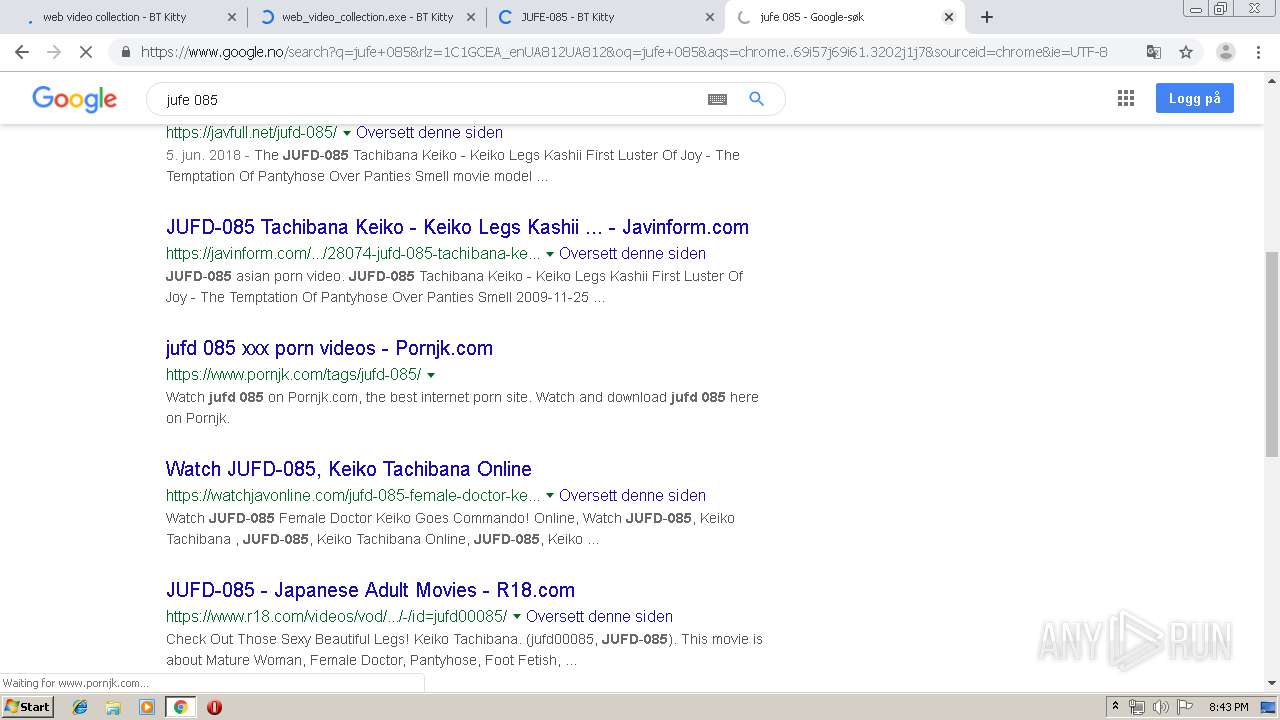
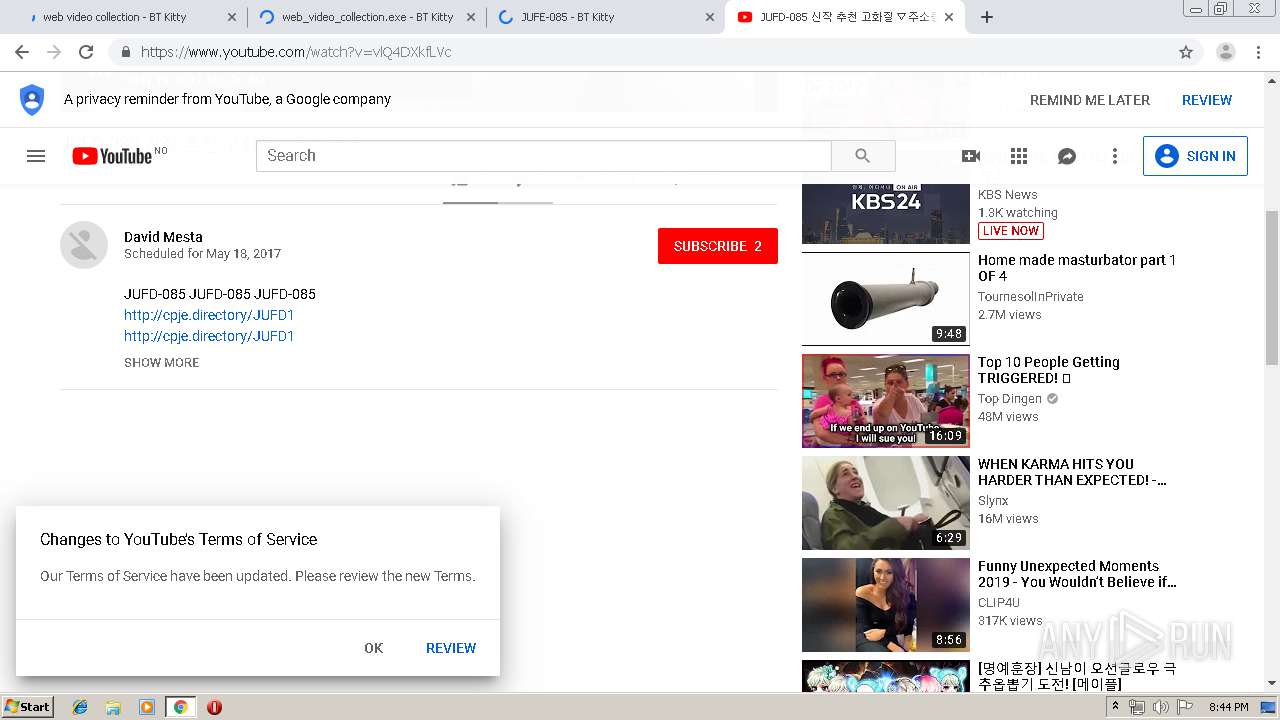
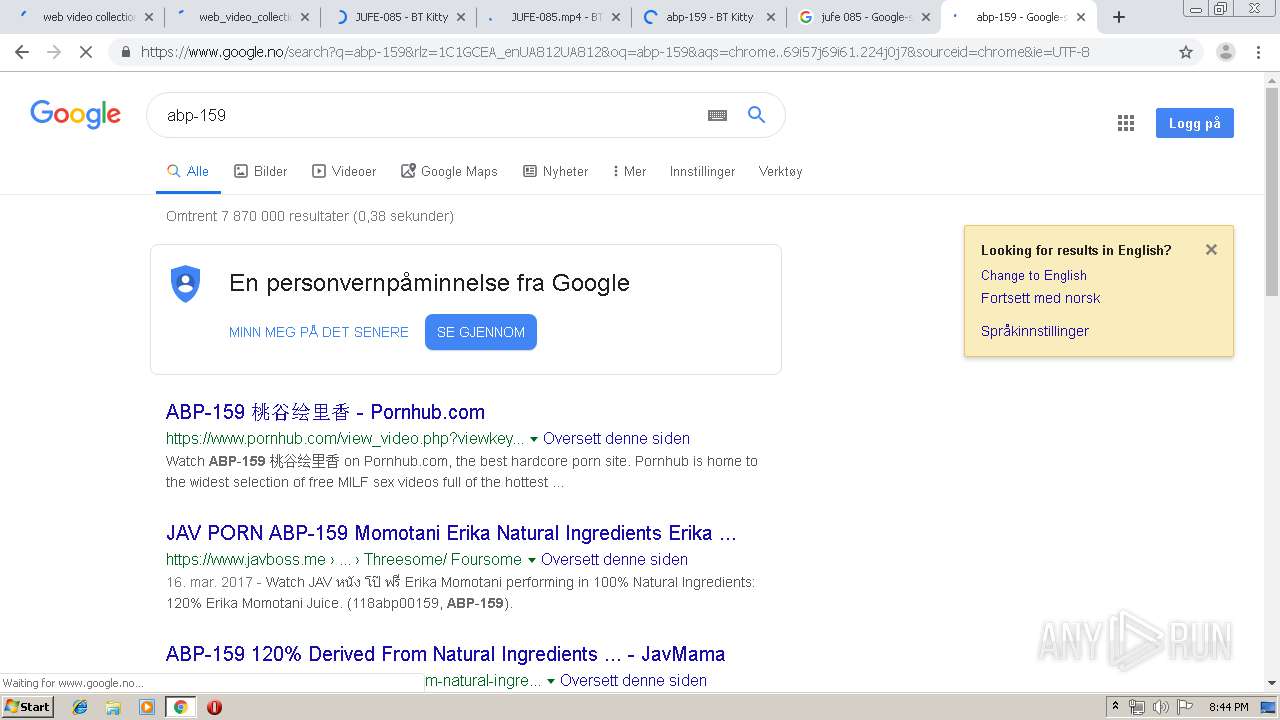
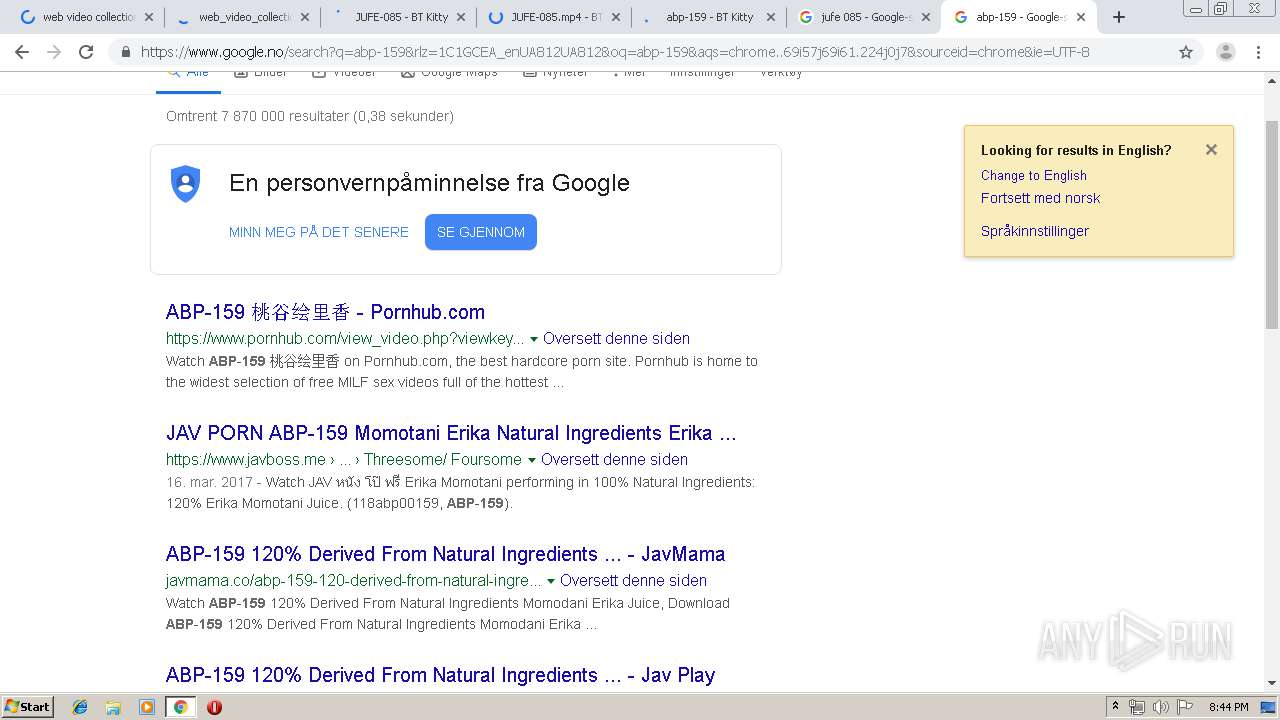
| URL: | http://btkittyok.com/search/K09NUijLTEnNV0jOz8lJTS7JzM8DAA/2/0/0.html |
| Full analysis: | https://app.any.run/tasks/e2028315-48e2-40cf-b104-6bd1b9cde3b9 |
| Verdict: | Malicious activity |
| Analysis date: | August 13, 2019, 19:41:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A0A1200828821F570B3A1825D391F54A |
| SHA1: | 2B70D8772B5A32D25D2E3DB82804CA073E971E53 |
| SHA256: | B599AAEB10DC163A5455D7A1555F2286F9EA3C77E7E95C063BCFB55476147179 |
| SSDEEP: | 3:N1KcKV2SEXGdhPU2cAjYNG:Cco2nGD9csv |
MALICIOUS
No malicious indicators.SUSPICIOUS
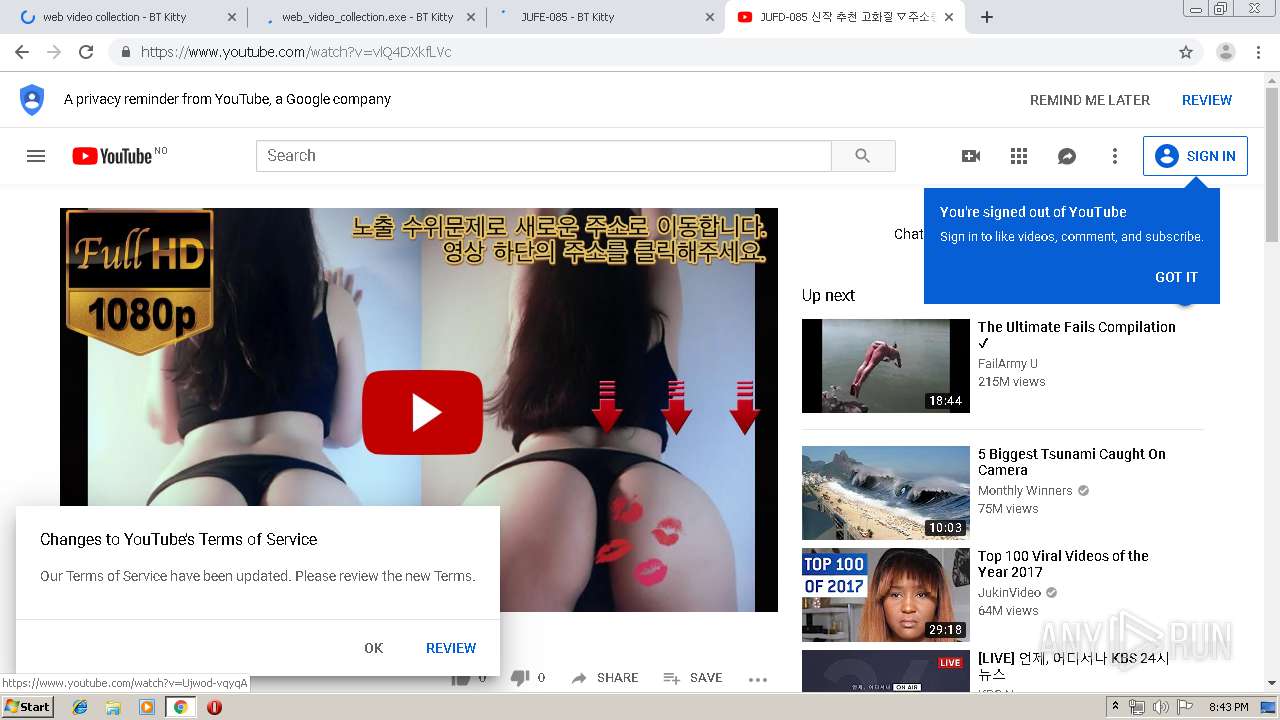
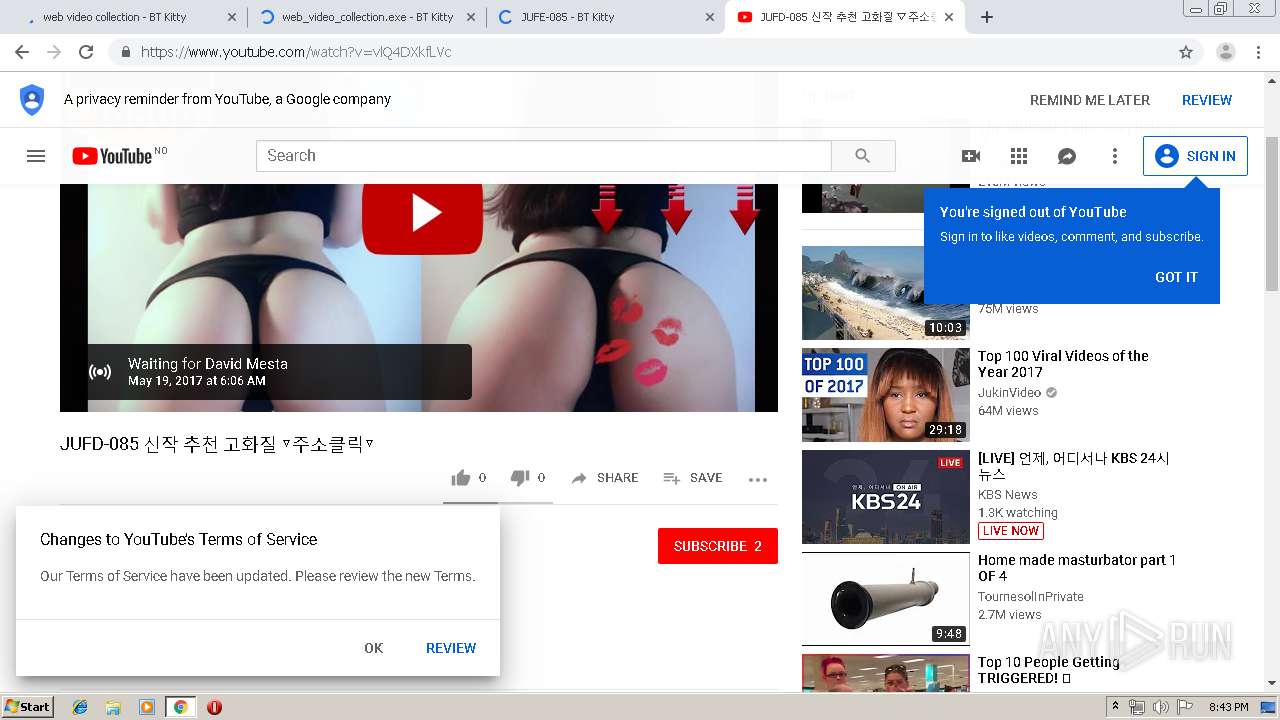
Modifies files in Chrome extension folder
- chrome.exe (PID: 4056)
INFO
Creates files in the user directory
- chrome.exe (PID: 4056)
Application launched itself
- chrome.exe (PID: 4056)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
85
Monitored processes
51
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=980,4741187733243192186,4744935793779468934,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7849732886505301425 --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3248 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=980,4741187733243192186,4744935793779468934,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9470974295693019162 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2448 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,4741187733243192186,4744935793779468934,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11574488388125789891 --mojo-platform-channel-handle=3576 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6eafa9d0,0x6eafa9e0,0x6eafa9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,4741187733243192186,4744935793779468934,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13928869461879718144 --mojo-platform-channel-handle=2148 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=980,4741187733243192186,4744935793779468934,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=634408389607899666 --renderer-client-id=46 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3920 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=980,4741187733243192186,4744935793779468934,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1667563651021208902 --renderer-client-id=39 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3484 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,4741187733243192186,4744935793779468934,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3914855781056168168 --mojo-platform-channel-handle=488 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,4741187733243192186,4744935793779468934,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1488323317994169703 --mojo-platform-channel-handle=2700 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,4741187733243192186,4744935793779468934,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11769061728514994337 --mojo-platform-channel-handle=3596 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
652
Read events
557
Write events
91
Delete events
4
Modification events
| (PID) Process: | (4056) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4056) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4056) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (4056) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (4056) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2156) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 4056-13210198902673750 |
Value: 259 | |||
| (PID) Process: | (4056) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (4056) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (4056) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (4056) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
173
Text files
231
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a26f4335-a263-4f69-9afc-d444f9bc446c.tmp | — | |
MD5:— | SHA256:— | |||
| 4056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 4056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF36d328.TMP | text | |
MD5:— | SHA256:— | |||
| 4056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 4056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF36d356.TMP | text | |
MD5:— | SHA256:— | |||
| 4056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 4056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 4056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 4056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RF36d47f.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
51
TCP/UDP connections
184
DNS requests
129
Threats
71
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
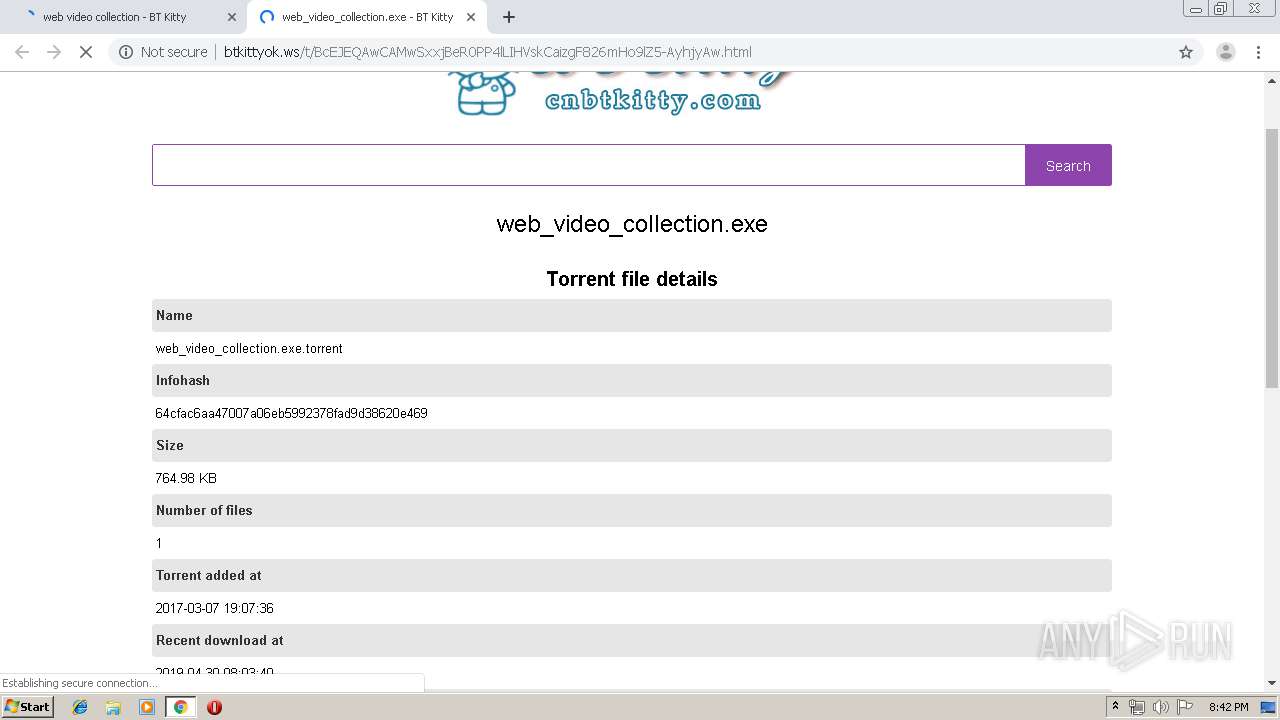
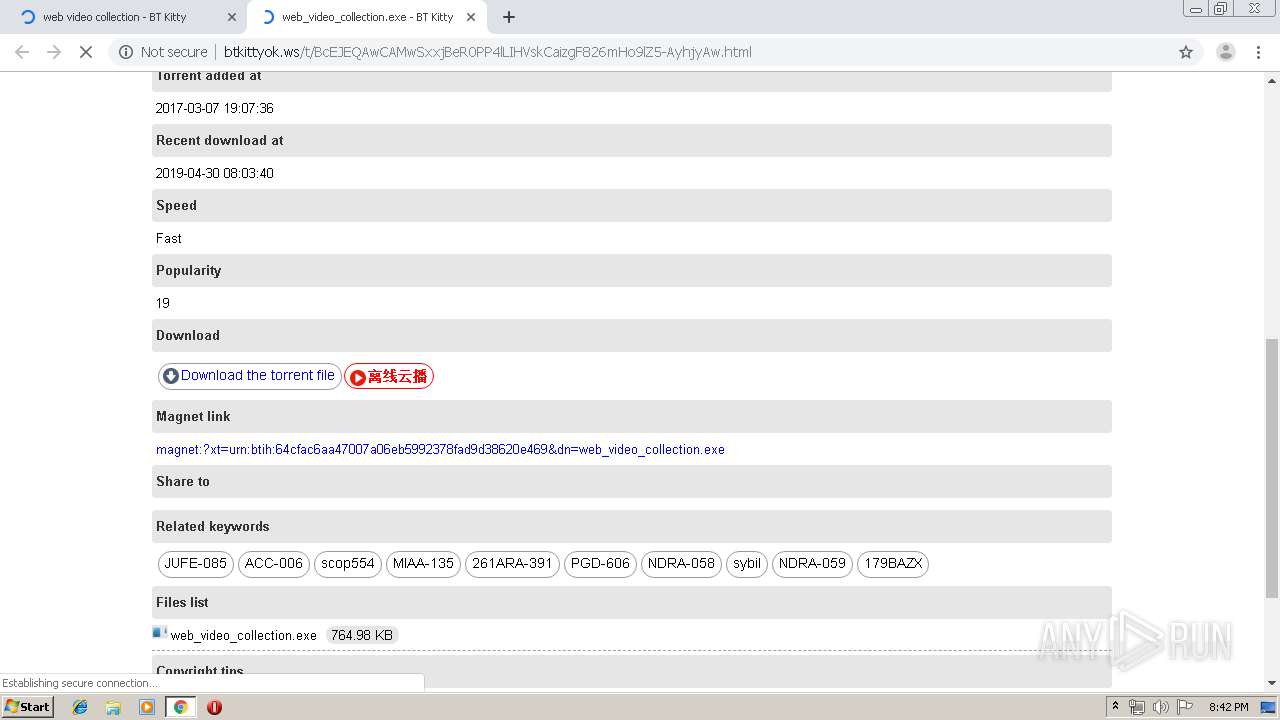
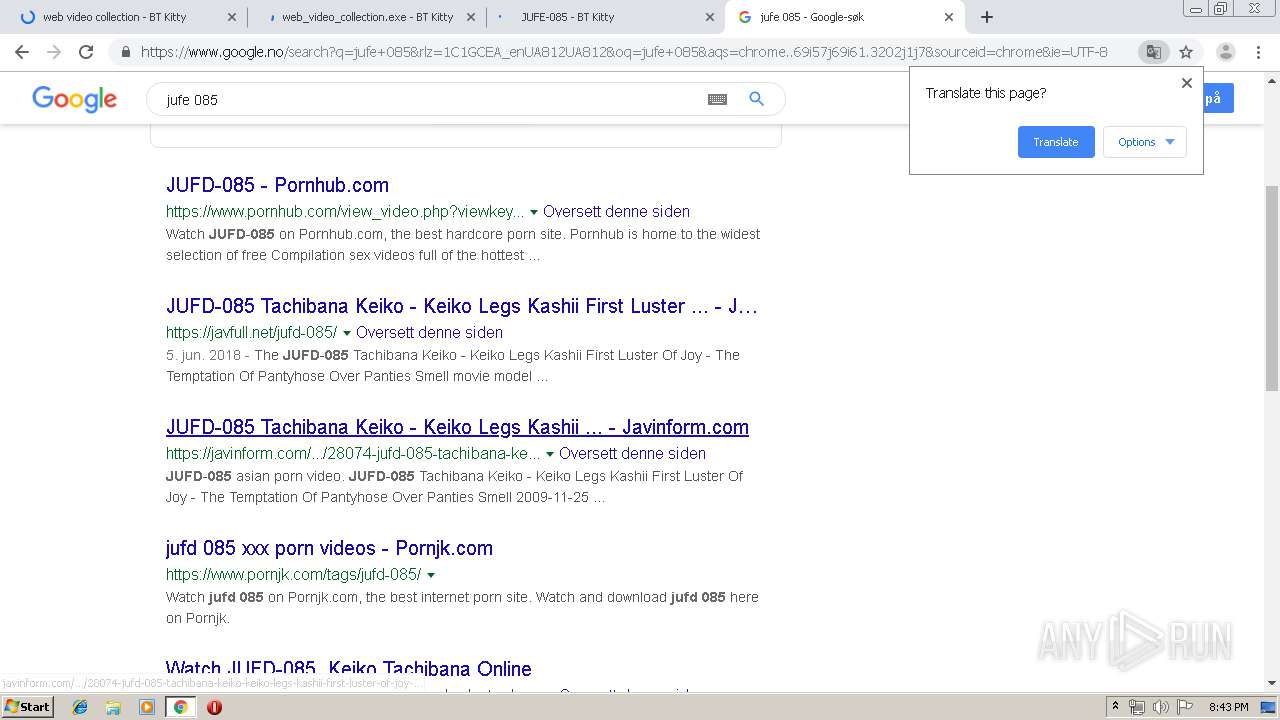
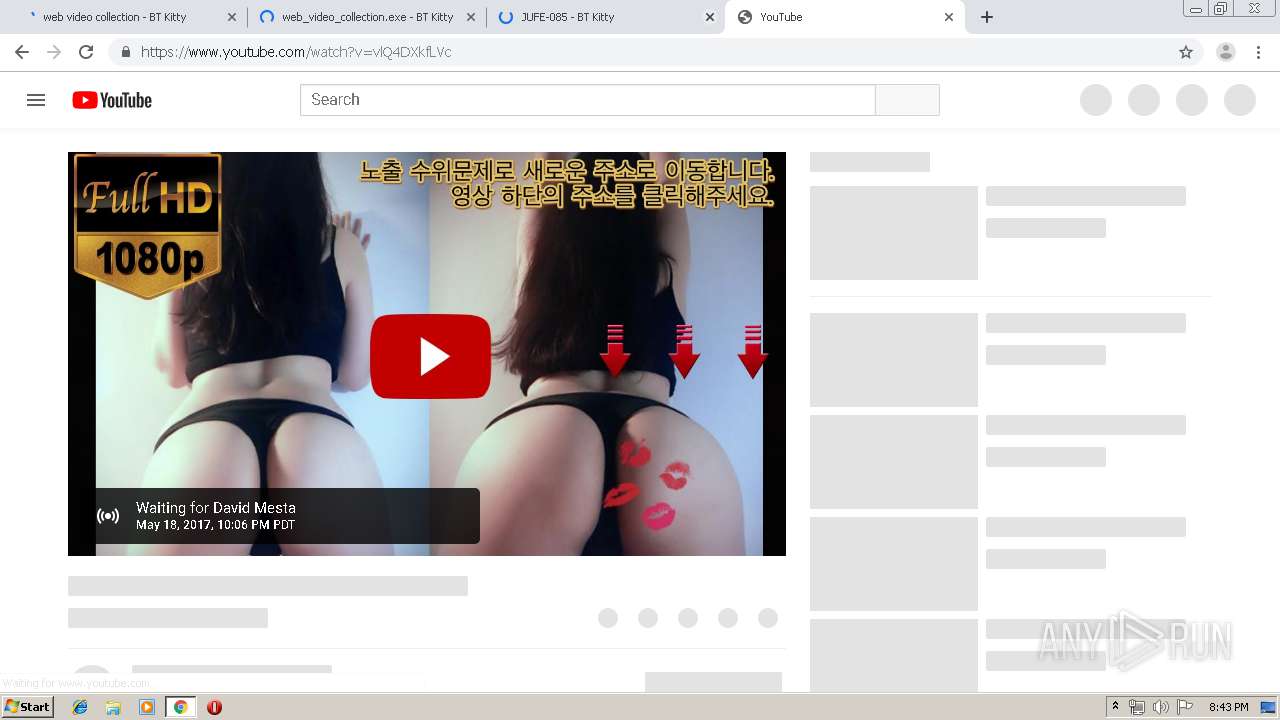
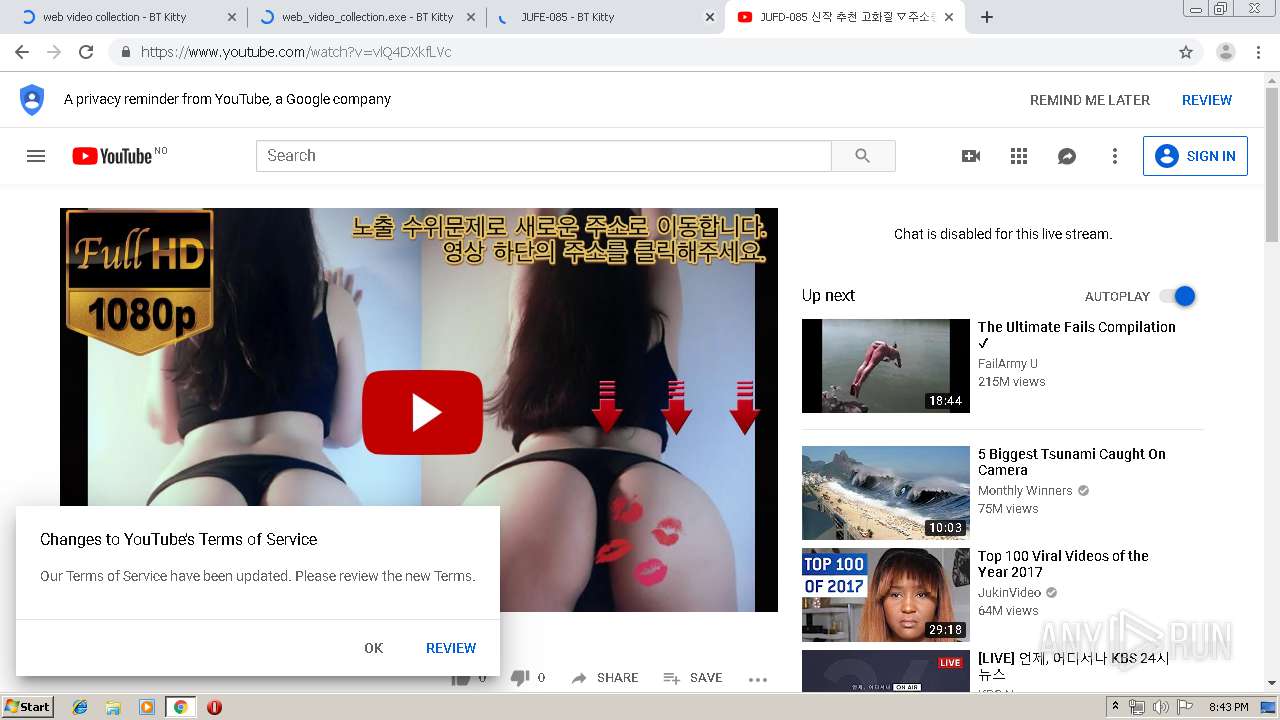
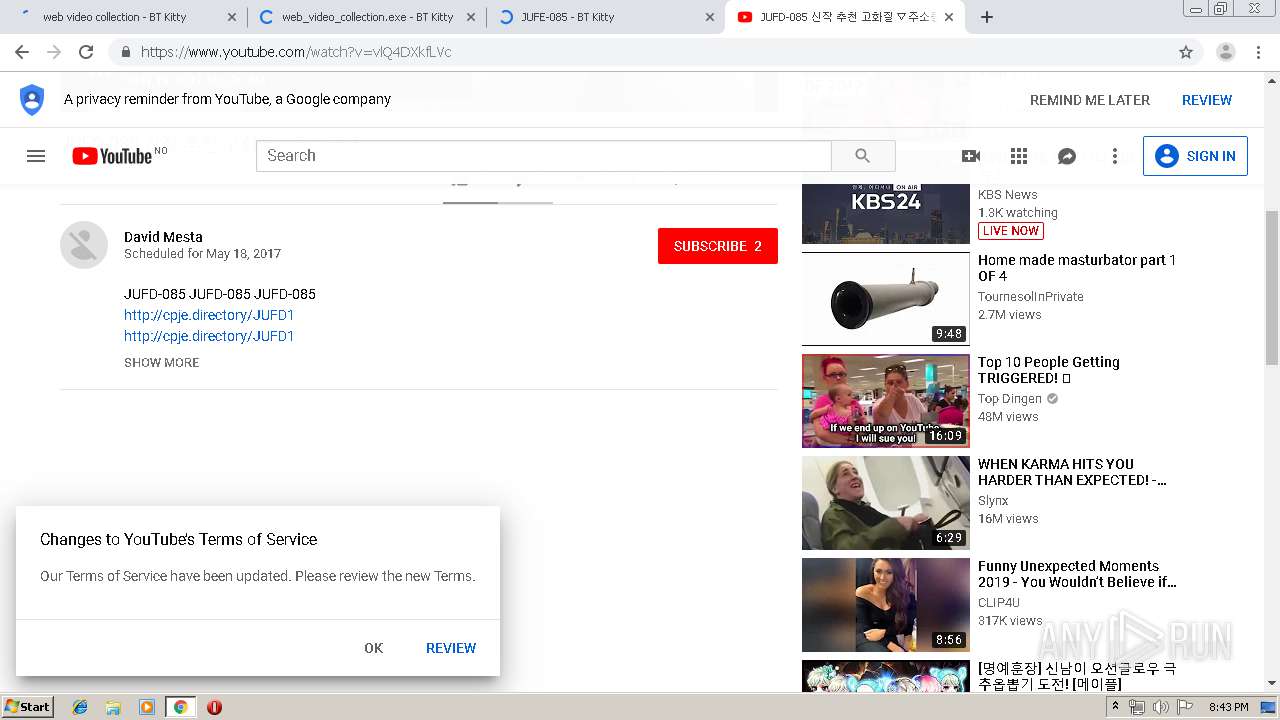
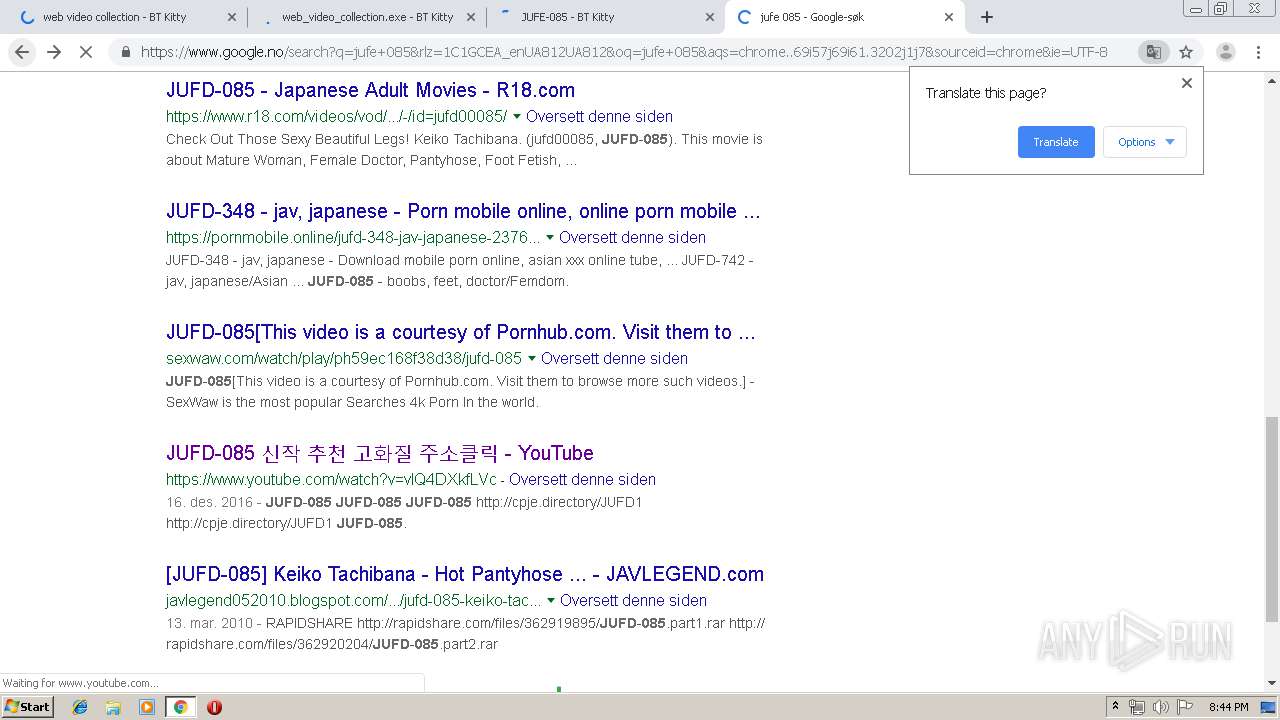
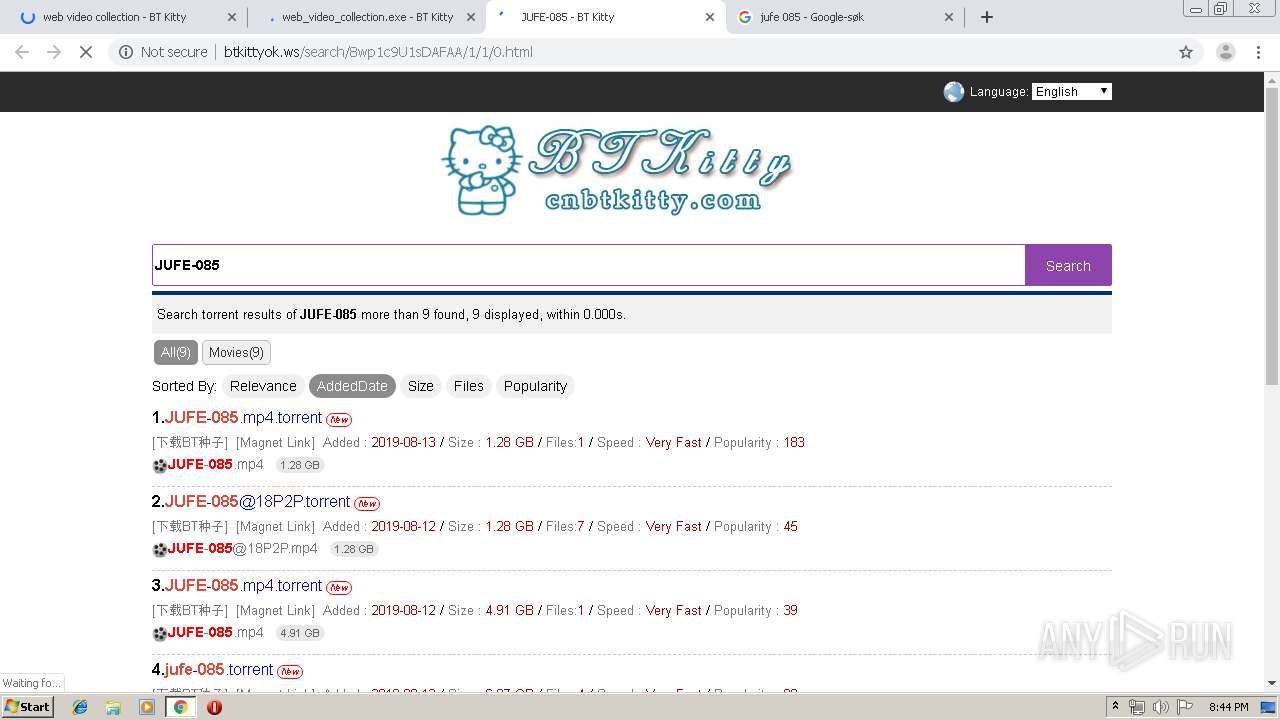
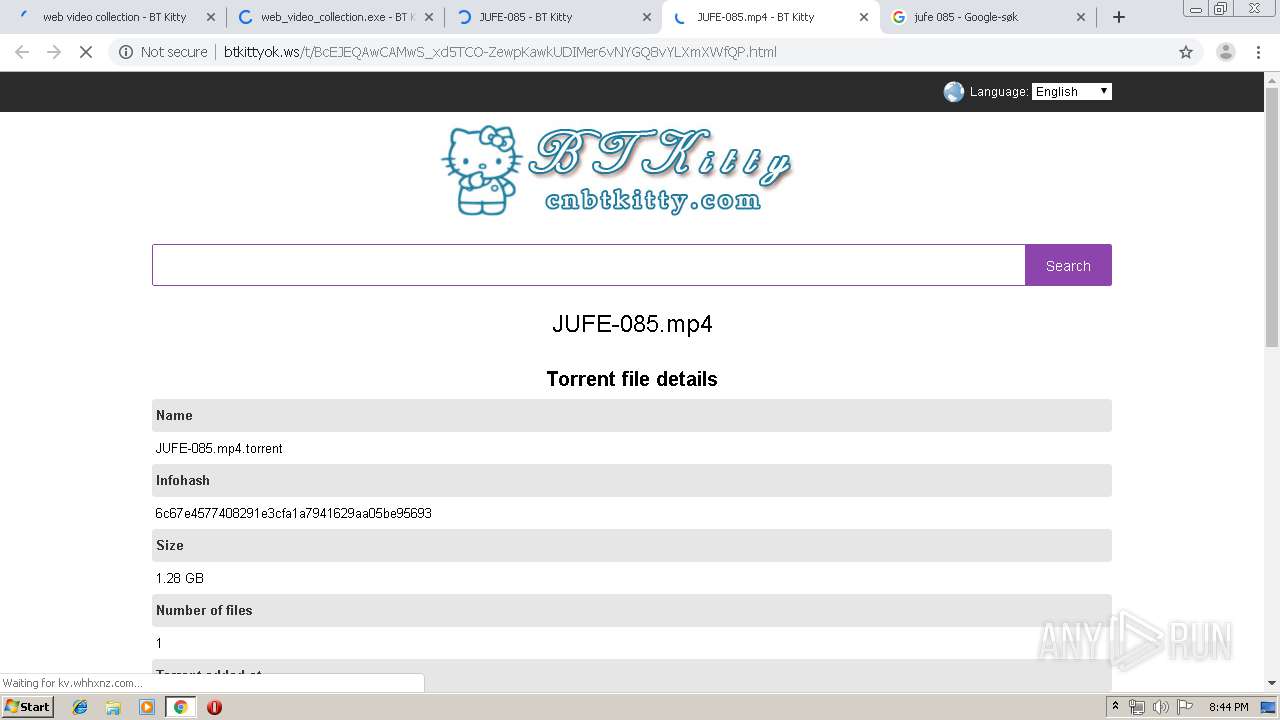
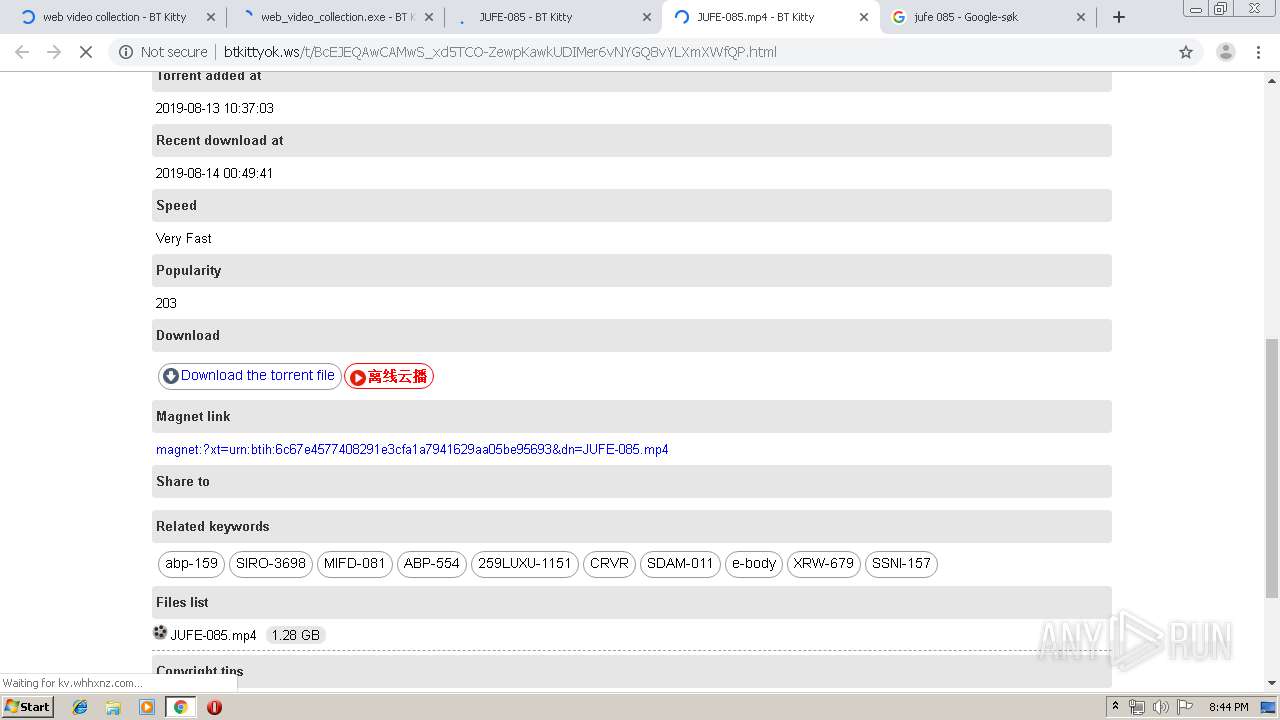
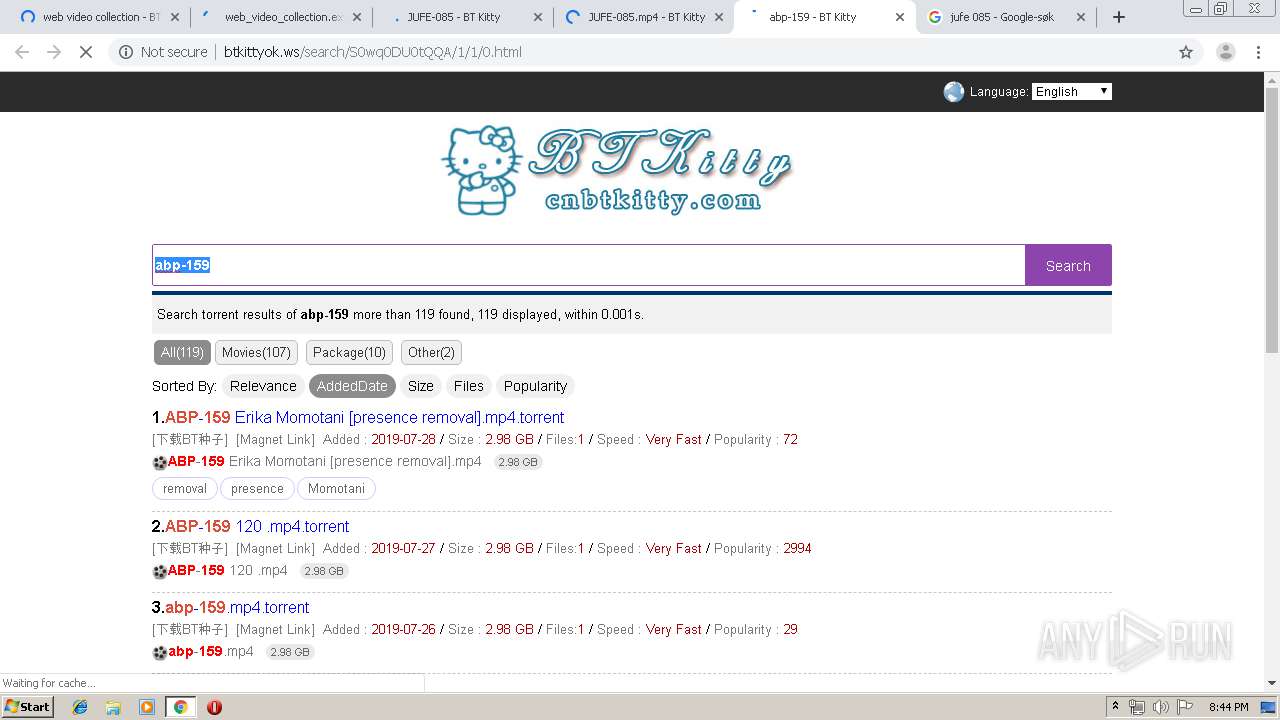
4016 | chrome.exe | GET | 301 | 188.213.49.192:80 | http://btkittyok.com/search/K09NUijLTEnNV0jOz8lJTS7JzM8DAA/2/0/0.html | RO | — | — | unknown |
4016 | chrome.exe | GET | — | 59.80.39.94:80 | http://kv.whhxnz.com/d.php?pid=2461 | CN | — | — | malicious |
4016 | chrome.exe | GET | 200 | 104.27.166.72:80 | http://cdn.hivps.xyz/analytics-btkitty?v=1565725305.651815657253057880.9324650498863283 | US | text | 102 b | suspicious |
4016 | chrome.exe | GET | 200 | 104.27.189.232:80 | http://btkittyok.ws/static/css/css.css?v=147778332323238995522 | US | text | 2.67 Kb | shared |
4016 | chrome.exe | GET | 200 | 104.27.189.232:80 | http://btkittyok.ws/static/images/logo.jpg?version=12321321 | US | image | 16.1 Kb | shared |
4016 | chrome.exe | GET | 200 | 104.27.189.232:80 | http://btkittyok.ws/static/images/filetype/text.png | US | image | 3.55 Kb | shared |
4016 | chrome.exe | GET | 200 | 104.27.189.232:80 | http://btkittyok.ws/static/images/down.png | US | image | 1.56 Kb | shared |
4016 | chrome.exe | GET | 200 | 104.27.189.232:80 | http://btkittyok.ws/search/K09NUijLTEnNV0jOz8lJTS7JzM8DAA/2/0/0.html | US | html | 4.13 Kb | shared |
4016 | chrome.exe | GET | 200 | 104.27.189.232:80 | http://btkittyok.ws/static/images/language.png | US | image | 2.47 Kb | shared |
4016 | chrome.exe | GET | 200 | 104.27.166.72:80 | http://cdn.hivps.xyz/analytics-btkitty?v=1565725327.915915657253276800.43452062546943204 | US | text | 101 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4016 | chrome.exe | 104.27.166.72:80 | cdn.hivps.xyz | Cloudflare Inc | US | shared |
4016 | chrome.exe | 151.101.2.109:443 | cdn.jsdelivr.net | Fastly | US | suspicious |
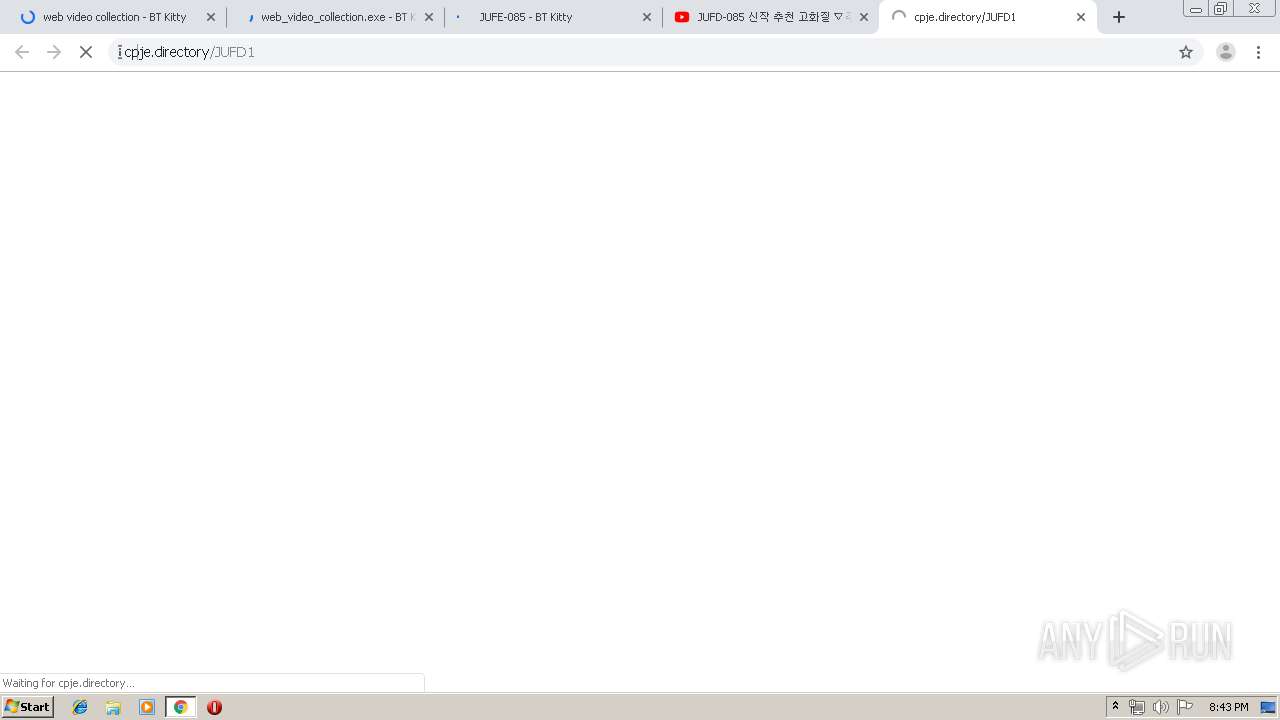
4016 | chrome.exe | 47.246.43.206:443 | www.tuoguang1111.com | — | US | malicious |
4016 | chrome.exe | 59.80.39.94:80 | kv.whhxnz.com | China Unicom IP network | CN | unknown |
4016 | chrome.exe | 116.211.183.234:443 | s4.cnzz.com | CHINANET Hubei province network | CN | suspicious |
4016 | chrome.exe | 104.27.161.240:80 | gotoniubiurl.pw | Cloudflare Inc | US | shared |
4016 | chrome.exe | 23.225.154.19:12443 | js.dakawm.cc | CNSERVERS LLC | US | suspicious |
— | — | 23.210.248.44:80 | s7.addthis.com | Akamai International B.V. | NL | whitelisted |
4016 | chrome.exe | 216.58.207.67:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
4016 | chrome.exe | 172.217.16.132:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
btkittyok.com |
| unknown |
accounts.google.com |
| shared |
btkittyok.ws |
| unknown |
kv.whhxnz.com |
| malicious |
www.tuoguang1111.com |
| malicious |
s4.cnzz.com |
| whitelisted |
cdn.jsdelivr.net |
| whitelisted |
s5.cnzz.com |
| whitelisted |
cdn.hivps.xyz |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4016 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1064 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
1064 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
4016 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.pw domain |
4016 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
4016 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
4016 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
4016 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM CLOSEWAIT FIN out of window |
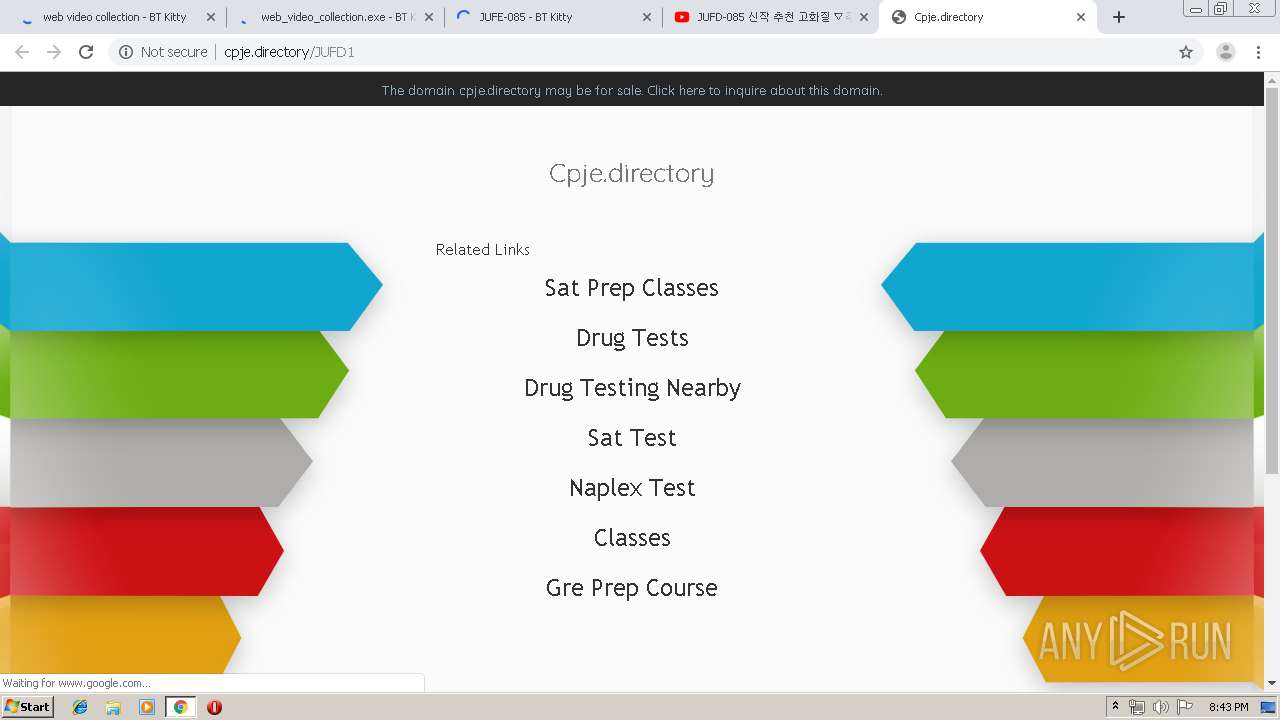
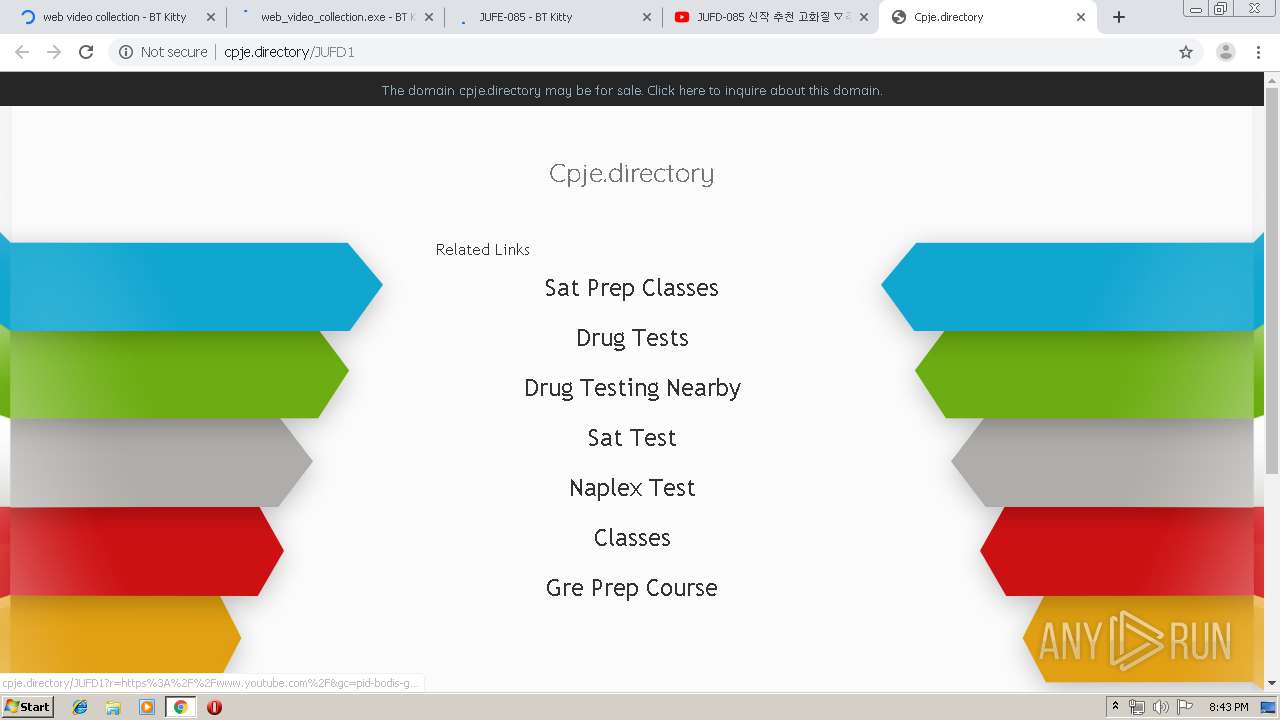
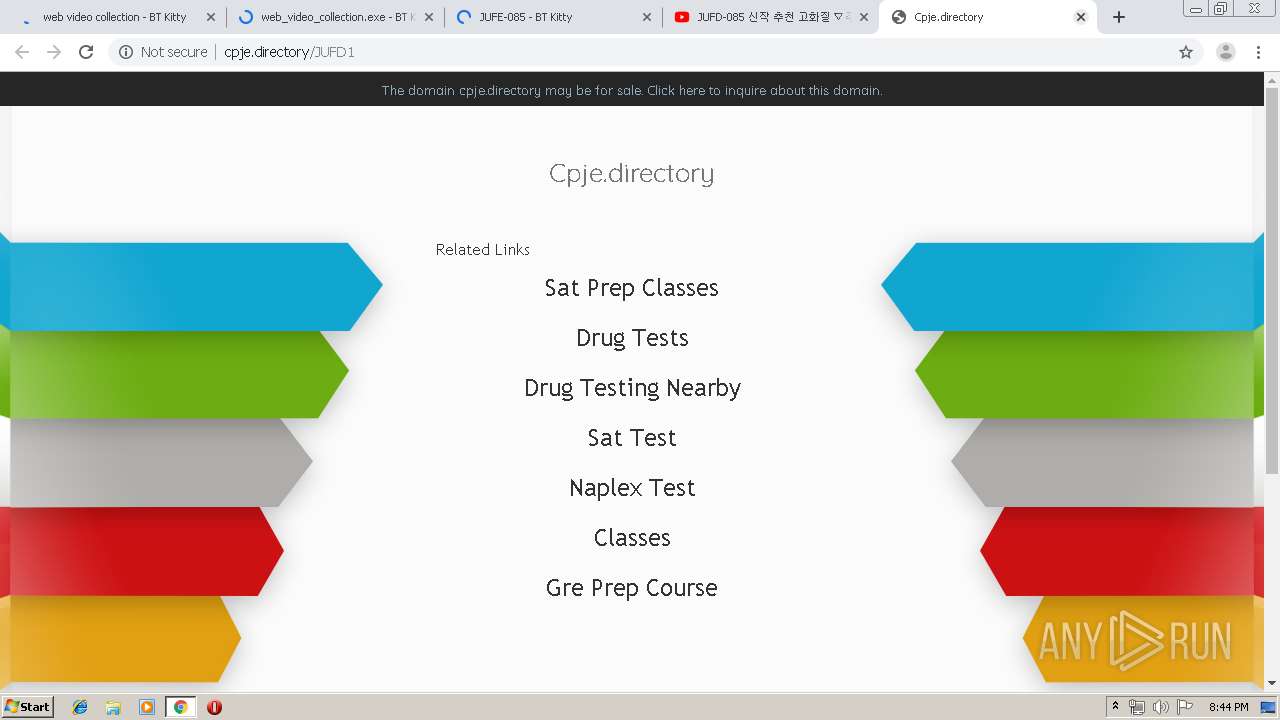
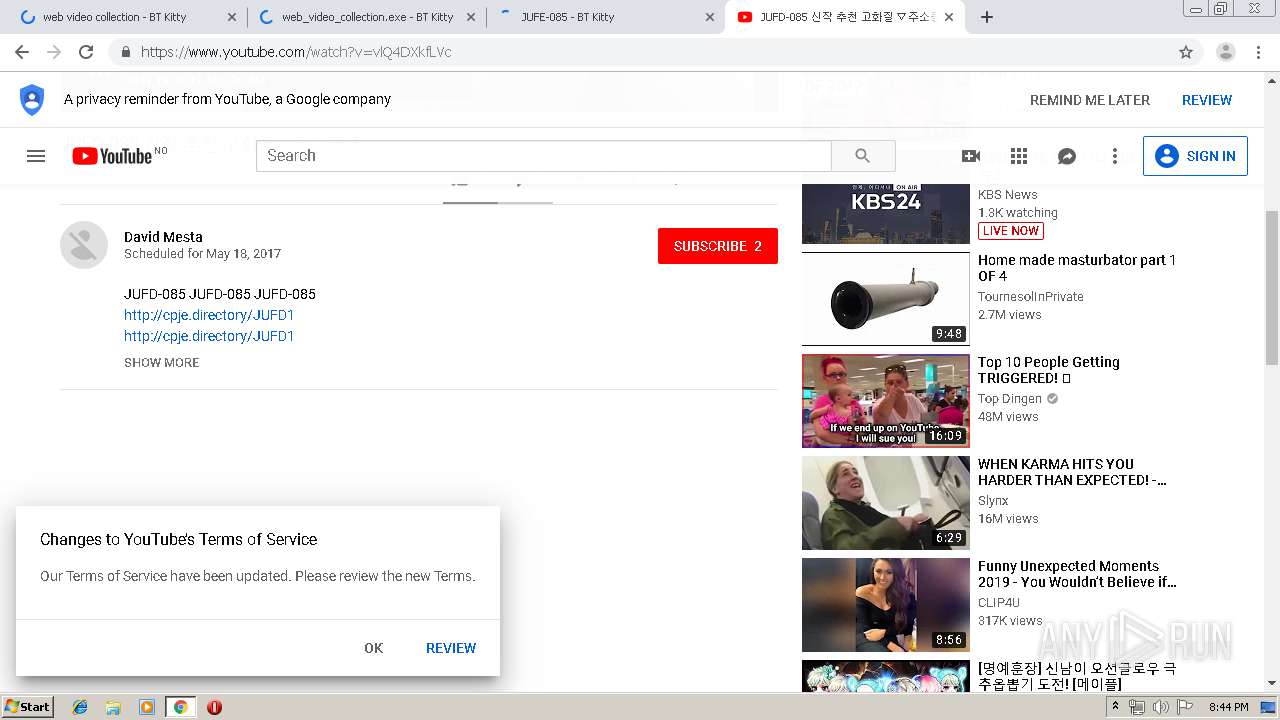
4016 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Drive-by Evil Redirector |
1064 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |